├── .gitignore
├── LICENCE
├── README.md
├── examples
├── dump.py
├── ent-chains.py
├── hunt.md
├── hunt.py
├── image-gui.py
├── image.py
├── keysearch.py
├── mount.py
├── pw-check.py
├── pwcracker.py
├── quick-container.py
└── reserved.py
├── pytruecrypt.py
└── util.py
/.gitignore:
--------------------------------------------------------------------------------
1 | # Byte-compiled / optimized / DLL files
2 | __pycache__/
3 | *.py[cod]
4 |
5 | # C extensions
6 | *.so
7 |
8 | # Distribution / packaging
9 | .Python
10 | env/
11 | bin/
12 | build/
13 | develop-eggs/
14 | dist/
15 | eggs/
16 | lib/
17 | lib64/
18 | parts/
19 | sdist/
20 | var/
21 | *.egg-info/
22 | .installed.cfg
23 | *.egg
24 |
25 | # Installer logs
26 | pip-log.txt
27 | pip-delete-this-directory.txt
28 |
29 | # Unit test / coverage reports
30 | htmlcov/
31 | .tox/
32 | .coverage
33 | .cache
34 | nosetests.xml
35 | coverage.xml
36 |
37 | # Translations
38 | *.mo
39 |
40 | # Mr Developer
41 | .mr.developer.cfg
42 | .project
43 | .pydevproject
44 |
45 | # Rope
46 | .ropeproject
47 |
48 | # Django stuff:
49 | *.log
50 | *.pot
51 |
52 | # Sphinx documentation
53 | docs/_build/
54 |
55 | #cx_freeze script
56 | build.bat
57 |
58 | #
59 | images/
60 | *.dd
61 | *.tc
62 | *.001
63 | *.ico
64 | *.log
65 | *.entropy
66 | *.txt
67 | *.py
68 | !examples/*.py
69 | !pytruecrypt.py
70 | !util.py
71 | dd.exe
--------------------------------------------------------------------------------
/LICENCE:
--------------------------------------------------------------------------------
1 | GNU GENERAL PUBLIC LICENSE
2 | Version 3, 29 June 2007
3 |
4 | Copyright (C) 2007 Free Software Foundation, Inc.
5 | Everyone is permitted to copy and distribute verbatim copies
6 | of this license document, but changing it is not allowed.
7 |
8 | Preamble
9 |
10 | The GNU General Public License is a free, copyleft license for
11 | software and other kinds of works.
12 |
13 | The licenses for most software and other practical works are designed
14 | to take away your freedom to share and change the works. By contrast,
15 | the GNU General Public License is intended to guarantee your freedom to
16 | share and change all versions of a program--to make sure it remains free
17 | software for all its users. We, the Free Software Foundation, use the
18 | GNU General Public License for most of our software; it applies also to
19 | any other work released this way by its authors. You can apply it to
20 | your programs, too.
21 |
22 | When we speak of free software, we are referring to freedom, not
23 | price. Our General Public Licenses are designed to make sure that you
24 | have the freedom to distribute copies of free software (and charge for
25 | them if you wish), that you receive source code or can get it if you
26 | want it, that you can change the software or use pieces of it in new
27 | free programs, and that you know you can do these things.
28 |
29 | To protect your rights, we need to prevent others from denying you
30 | these rights or asking you to surrender the rights. Therefore, you have
31 | certain responsibilities if you distribute copies of the software, or if
32 | you modify it: responsibilities to respect the freedom of others.
33 |
34 | For example, if you distribute copies of such a program, whether
35 | gratis or for a fee, you must pass on to the recipients the same
36 | freedoms that you received. You must make sure that they, too, receive
37 | or can get the source code. And you must show them these terms so they
38 | know their rights.
39 |
40 | Developers that use the GNU GPL protect your rights with two steps:
41 | (1) assert copyright on the software, and (2) offer you this License
42 | giving you legal permission to copy, distribute and/or modify it.
43 |
44 | For the developers' and authors' protection, the GPL clearly explains
45 | that there is no warranty for this free software. For both users' and
46 | authors' sake, the GPL requires that modified versions be marked as
47 | changed, so that their problems will not be attributed erroneously to
48 | authors of previous versions.
49 |
50 | Some devices are designed to deny users access to install or run
51 | modified versions of the software inside them, although the manufacturer
52 | can do so. This is fundamentally incompatible with the aim of
53 | protecting users' freedom to change the software. The systematic
54 | pattern of such abuse occurs in the area of products for individuals to
55 | use, which is precisely where it is most unacceptable. Therefore, we
56 | have designed this version of the GPL to prohibit the practice for those
57 | products. If such problems arise substantially in other domains, we
58 | stand ready to extend this provision to those domains in future versions
59 | of the GPL, as needed to protect the freedom of users.
60 |
61 | Finally, every program is threatened constantly by software patents.
62 | States should not allow patents to restrict development and use of
63 | software on general-purpose computers, but in those that do, we wish to
64 | avoid the special danger that patents applied to a free program could
65 | make it effectively proprietary. To prevent this, the GPL assures that
66 | patents cannot be used to render the program non-free.
67 |
68 | The precise terms and conditions for copying, distribution and
69 | modification follow.
70 |
71 | TERMS AND CONDITIONS
72 |
73 | 0. Definitions.
74 |
75 | "This License" refers to version 3 of the GNU General Public License.
76 |
77 | "Copyright" also means copyright-like laws that apply to other kinds of
78 | works, such as semiconductor masks.
79 |
80 | "The Program" refers to any copyrightable work licensed under this
81 | License. Each licensee is addressed as "you". "Licensees" and
82 | "recipients" may be individuals or organizations.
83 |
84 | To "modify" a work means to copy from or adapt all or part of the work
85 | in a fashion requiring copyright permission, other than the making of an
86 | exact copy. The resulting work is called a "modified version" of the
87 | earlier work or a work "based on" the earlier work.
88 |
89 | A "covered work" means either the unmodified Program or a work based
90 | on the Program.
91 |
92 | To "propagate" a work means to do anything with it that, without
93 | permission, would make you directly or secondarily liable for
94 | infringement under applicable copyright law, except executing it on a
95 | computer or modifying a private copy. Propagation includes copying,
96 | distribution (with or without modification), making available to the
97 | public, and in some countries other activities as well.
98 |
99 | To "convey" a work means any kind of propagation that enables other
100 | parties to make or receive copies. Mere interaction with a user through
101 | a computer network, with no transfer of a copy, is not conveying.
102 |
103 | An interactive user interface displays "Appropriate Legal Notices"
104 | to the extent that it includes a convenient and prominently visible
105 | feature that (1) displays an appropriate copyright notice, and (2)
106 | tells the user that there is no warranty for the work (except to the
107 | extent that warranties are provided), that licensees may convey the
108 | work under this License, and how to view a copy of this License. If
109 | the interface presents a list of user commands or options, such as a
110 | menu, a prominent item in the list meets this criterion.
111 |
112 | 1. Source Code.
113 |
114 | The "source code" for a work means the preferred form of the work
115 | for making modifications to it. "Object code" means any non-source
116 | form of a work.
117 |
118 | A "Standard Interface" means an interface that either is an official
119 | standard defined by a recognized standards body, or, in the case of
120 | interfaces specified for a particular programming language, one that
121 | is widely used among developers working in that language.
122 |
123 | The "System Libraries" of an executable work include anything, other
124 | than the work as a whole, that (a) is included in the normal form of
125 | packaging a Major Component, but which is not part of that Major
126 | Component, and (b) serves only to enable use of the work with that
127 | Major Component, or to implement a Standard Interface for which an
128 | implementation is available to the public in source code form. A
129 | "Major Component", in this context, means a major essential component
130 | (kernel, window system, and so on) of the specific operating system
131 | (if any) on which the executable work runs, or a compiler used to
132 | produce the work, or an object code interpreter used to run it.
133 |
134 | The "Corresponding Source" for a work in object code form means all
135 | the source code needed to generate, install, and (for an executable
136 | work) run the object code and to modify the work, including scripts to
137 | control those activities. However, it does not include the work's
138 | System Libraries, or general-purpose tools or generally available free
139 | programs which are used unmodified in performing those activities but
140 | which are not part of the work. For example, Corresponding Source
141 | includes interface definition files associated with source files for
142 | the work, and the source code for shared libraries and dynamically
143 | linked subprograms that the work is specifically designed to require,
144 | such as by intimate data communication or control flow between those
145 | subprograms and other parts of the work.
146 |
147 | The Corresponding Source need not include anything that users
148 | can regenerate automatically from other parts of the Corresponding
149 | Source.
150 |
151 | The Corresponding Source for a work in source code form is that
152 | same work.
153 |
154 | 2. Basic Permissions.
155 |
156 | All rights granted under this License are granted for the term of
157 | copyright on the Program, and are irrevocable provided the stated
158 | conditions are met. This License explicitly affirms your unlimited
159 | permission to run the unmodified Program. The output from running a
160 | covered work is covered by this License only if the output, given its
161 | content, constitutes a covered work. This License acknowledges your
162 | rights of fair use or other equivalent, as provided by copyright law.
163 |
164 | You may make, run and propagate covered works that you do not
165 | convey, without conditions so long as your license otherwise remains
166 | in force. You may convey covered works to others for the sole purpose
167 | of having them make modifications exclusively for you, or provide you
168 | with facilities for running those works, provided that you comply with
169 | the terms of this License in conveying all material for which you do
170 | not control copyright. Those thus making or running the covered works
171 | for you must do so exclusively on your behalf, under your direction
172 | and control, on terms that prohibit them from making any copies of
173 | your copyrighted material outside their relationship with you.
174 |
175 | Conveying under any other circumstances is permitted solely under
176 | the conditions stated below. Sublicensing is not allowed; section 10
177 | makes it unnecessary.
178 |
179 | 3. Protecting Users' Legal Rights From Anti-Circumvention Law.
180 |
181 | No covered work shall be deemed part of an effective technological
182 | measure under any applicable law fulfilling obligations under article
183 | 11 of the WIPO copyright treaty adopted on 20 December 1996, or
184 | similar laws prohibiting or restricting circumvention of such
185 | measures.
186 |
187 | When you convey a covered work, you waive any legal power to forbid
188 | circumvention of technological measures to the extent such circumvention
189 | is effected by exercising rights under this License with respect to
190 | the covered work, and you disclaim any intention to limit operation or
191 | modification of the work as a means of enforcing, against the work's
192 | users, your or third parties' legal rights to forbid circumvention of
193 | technological measures.
194 |
195 | 4. Conveying Verbatim Copies.
196 |
197 | You may convey verbatim copies of the Program's source code as you
198 | receive it, in any medium, provided that you conspicuously and
199 | appropriately publish on each copy an appropriate copyright notice;
200 | keep intact all notices stating that this License and any
201 | non-permissive terms added in accord with section 7 apply to the code;
202 | keep intact all notices of the absence of any warranty; and give all
203 | recipients a copy of this License along with the Program.
204 |
205 | You may charge any price or no price for each copy that you convey,
206 | and you may offer support or warranty protection for a fee.
207 |
208 | 5. Conveying Modified Source Versions.
209 |
210 | You may convey a work based on the Program, or the modifications to
211 | produce it from the Program, in the form of source code under the
212 | terms of section 4, provided that you also meet all of these conditions:
213 |
214 | a) The work must carry prominent notices stating that you modified
215 | it, and giving a relevant date.
216 |
217 | b) The work must carry prominent notices stating that it is
218 | released under this License and any conditions added under section
219 | 7. This requirement modifies the requirement in section 4 to
220 | "keep intact all notices".
221 |
222 | c) You must license the entire work, as a whole, under this
223 | License to anyone who comes into possession of a copy. This
224 | License will therefore apply, along with any applicable section 7
225 | additional terms, to the whole of the work, and all its parts,
226 | regardless of how they are packaged. This License gives no
227 | permission to license the work in any other way, but it does not
228 | invalidate such permission if you have separately received it.
229 |
230 | d) If the work has interactive user interfaces, each must display
231 | Appropriate Legal Notices; however, if the Program has interactive
232 | interfaces that do not display Appropriate Legal Notices, your
233 | work need not make them do so.
234 |
235 | A compilation of a covered work with other separate and independent
236 | works, which are not by their nature extensions of the covered work,
237 | and which are not combined with it such as to form a larger program,
238 | in or on a volume of a storage or distribution medium, is called an
239 | "aggregate" if the compilation and its resulting copyright are not
240 | used to limit the access or legal rights of the compilation's users
241 | beyond what the individual works permit. Inclusion of a covered work
242 | in an aggregate does not cause this License to apply to the other
243 | parts of the aggregate.
244 |
245 | 6. Conveying Non-Source Forms.
246 |
247 | You may convey a covered work in object code form under the terms
248 | of sections 4 and 5, provided that you also convey the
249 | machine-readable Corresponding Source under the terms of this License,
250 | in one of these ways:
251 |
252 | a) Convey the object code in, or embodied in, a physical product
253 | (including a physical distribution medium), accompanied by the
254 | Corresponding Source fixed on a durable physical medium
255 | customarily used for software interchange.
256 |
257 | b) Convey the object code in, or embodied in, a physical product
258 | (including a physical distribution medium), accompanied by a
259 | written offer, valid for at least three years and valid for as
260 | long as you offer spare parts or customer support for that product
261 | model, to give anyone who possesses the object code either (1) a
262 | copy of the Corresponding Source for all the software in the
263 | product that is covered by this License, on a durable physical
264 | medium customarily used for software interchange, for a price no
265 | more than your reasonable cost of physically performing this
266 | conveying of source, or (2) access to copy the
267 | Corresponding Source from a network server at no charge.
268 |
269 | c) Convey individual copies of the object code with a copy of the
270 | written offer to provide the Corresponding Source. This
271 | alternative is allowed only occasionally and noncommercially, and
272 | only if you received the object code with such an offer, in accord
273 | with subsection 6b.
274 |
275 | d) Convey the object code by offering access from a designated
276 | place (gratis or for a charge), and offer equivalent access to the
277 | Corresponding Source in the same way through the same place at no
278 | further charge. You need not require recipients to copy the
279 | Corresponding Source along with the object code. If the place to
280 | copy the object code is a network server, the Corresponding Source
281 | may be on a different server (operated by you or a third party)
282 | that supports equivalent copying facilities, provided you maintain
283 | clear directions next to the object code saying where to find the
284 | Corresponding Source. Regardless of what server hosts the
285 | Corresponding Source, you remain obligated to ensure that it is
286 | available for as long as needed to satisfy these requirements.
287 |
288 | e) Convey the object code using peer-to-peer transmission, provided
289 | you inform other peers where the object code and Corresponding
290 | Source of the work are being offered to the general public at no
291 | charge under subsection 6d.
292 |
293 | A separable portion of the object code, whose source code is excluded
294 | from the Corresponding Source as a System Library, need not be
295 | included in conveying the object code work.
296 |
297 | A "User Product" is either (1) a "consumer product", which means any
298 | tangible personal property which is normally used for personal, family,
299 | or household purposes, or (2) anything designed or sold for incorporation
300 | into a dwelling. In determining whether a product is a consumer product,
301 | doubtful cases shall be resolved in favor of coverage. For a particular
302 | product received by a particular user, "normally used" refers to a
303 | typical or common use of that class of product, regardless of the status
304 | of the particular user or of the way in which the particular user
305 | actually uses, or expects or is expected to use, the product. A product
306 | is a consumer product regardless of whether the product has substantial
307 | commercial, industrial or non-consumer uses, unless such uses represent
308 | the only significant mode of use of the product.
309 |
310 | "Installation Information" for a User Product means any methods,
311 | procedures, authorization keys, or other information required to install
312 | and execute modified versions of a covered work in that User Product from
313 | a modified version of its Corresponding Source. The information must
314 | suffice to ensure that the continued functioning of the modified object
315 | code is in no case prevented or interfered with solely because
316 | modification has been made.
317 |
318 | If you convey an object code work under this section in, or with, or
319 | specifically for use in, a User Product, and the conveying occurs as
320 | part of a transaction in which the right of possession and use of the
321 | User Product is transferred to the recipient in perpetuity or for a
322 | fixed term (regardless of how the transaction is characterized), the
323 | Corresponding Source conveyed under this section must be accompanied
324 | by the Installation Information. But this requirement does not apply
325 | if neither you nor any third party retains the ability to install
326 | modified object code on the User Product (for example, the work has
327 | been installed in ROM).
328 |
329 | The requirement to provide Installation Information does not include a
330 | requirement to continue to provide support service, warranty, or updates
331 | for a work that has been modified or installed by the recipient, or for
332 | the User Product in which it has been modified or installed. Access to a
333 | network may be denied when the modification itself materially and
334 | adversely affects the operation of the network or violates the rules and
335 | protocols for communication across the network.
336 |
337 | Corresponding Source conveyed, and Installation Information provided,
338 | in accord with this section must be in a format that is publicly
339 | documented (and with an implementation available to the public in
340 | source code form), and must require no special password or key for
341 | unpacking, reading or copying.
342 |
343 | 7. Additional Terms.
344 |
345 | "Additional permissions" are terms that supplement the terms of this
346 | License by making exceptions from one or more of its conditions.
347 | Additional permissions that are applicable to the entire Program shall
348 | be treated as though they were included in this License, to the extent
349 | that they are valid under applicable law. If additional permissions
350 | apply only to part of the Program, that part may be used separately
351 | under those permissions, but the entire Program remains governed by
352 | this License without regard to the additional permissions.
353 |
354 | When you convey a copy of a covered work, you may at your option
355 | remove any additional permissions from that copy, or from any part of
356 | it. (Additional permissions may be written to require their own
357 | removal in certain cases when you modify the work.) You may place
358 | additional permissions on material, added by you to a covered work,
359 | for which you have or can give appropriate copyright permission.
360 |
361 | Notwithstanding any other provision of this License, for material you
362 | add to a covered work, you may (if authorized by the copyright holders of
363 | that material) supplement the terms of this License with terms:
364 |
365 | a) Disclaiming warranty or limiting liability differently from the
366 | terms of sections 15 and 16 of this License; or
367 |
368 | b) Requiring preservation of specified reasonable legal notices or
369 | author attributions in that material or in the Appropriate Legal
370 | Notices displayed by works containing it; or
371 |
372 | c) Prohibiting misrepresentation of the origin of that material, or
373 | requiring that modified versions of such material be marked in
374 | reasonable ways as different from the original version; or
375 |
376 | d) Limiting the use for publicity purposes of names of licensors or
377 | authors of the material; or
378 |
379 | e) Declining to grant rights under trademark law for use of some
380 | trade names, trademarks, or service marks; or
381 |
382 | f) Requiring indemnification of licensors and authors of that
383 | material by anyone who conveys the material (or modified versions of
384 | it) with contractual assumptions of liability to the recipient, for
385 | any liability that these contractual assumptions directly impose on
386 | those licensors and authors.
387 |
388 | All other non-permissive additional terms are considered "further
389 | restrictions" within the meaning of section 10. If the Program as you
390 | received it, or any part of it, contains a notice stating that it is
391 | governed by this License along with a term that is a further
392 | restriction, you may remove that term. If a license document contains
393 | a further restriction but permits relicensing or conveying under this
394 | License, you may add to a covered work material governed by the terms
395 | of that license document, provided that the further restriction does
396 | not survive such relicensing or conveying.
397 |
398 | If you add terms to a covered work in accord with this section, you
399 | must place, in the relevant source files, a statement of the
400 | additional terms that apply to those files, or a notice indicating
401 | where to find the applicable terms.
402 |
403 | Additional terms, permissive or non-permissive, may be stated in the
404 | form of a separately written license, or stated as exceptions;
405 | the above requirements apply either way.
406 |
407 | 8. Termination.
408 |
409 | You may not propagate or modify a covered work except as expressly
410 | provided under this License. Any attempt otherwise to propagate or
411 | modify it is void, and will automatically terminate your rights under
412 | this License (including any patent licenses granted under the third
413 | paragraph of section 11).
414 |
415 | However, if you cease all violation of this License, then your
416 | license from a particular copyright holder is reinstated (a)
417 | provisionally, unless and until the copyright holder explicitly and
418 | finally terminates your license, and (b) permanently, if the copyright
419 | holder fails to notify you of the violation by some reasonable means
420 | prior to 60 days after the cessation.
421 |
422 | Moreover, your license from a particular copyright holder is
423 | reinstated permanently if the copyright holder notifies you of the
424 | violation by some reasonable means, this is the first time you have
425 | received notice of violation of this License (for any work) from that
426 | copyright holder, and you cure the violation prior to 30 days after
427 | your receipt of the notice.
428 |
429 | Termination of your rights under this section does not terminate the
430 | licenses of parties who have received copies or rights from you under
431 | this License. If your rights have been terminated and not permanently
432 | reinstated, you do not qualify to receive new licenses for the same
433 | material under section 10.
434 |
435 | 9. Acceptance Not Required for Having Copies.
436 |
437 | You are not required to accept this License in order to receive or
438 | run a copy of the Program. Ancillary propagation of a covered work
439 | occurring solely as a consequence of using peer-to-peer transmission
440 | to receive a copy likewise does not require acceptance. However,
441 | nothing other than this License grants you permission to propagate or
442 | modify any covered work. These actions infringe copyright if you do
443 | not accept this License. Therefore, by modifying or propagating a
444 | covered work, you indicate your acceptance of this License to do so.
445 |
446 | 10. Automatic Licensing of Downstream Recipients.
447 |
448 | Each time you convey a covered work, the recipient automatically
449 | receives a license from the original licensors, to run, modify and
450 | propagate that work, subject to this License. You are not responsible
451 | for enforcing compliance by third parties with this License.
452 |
453 | An "entity transaction" is a transaction transferring control of an
454 | organization, or substantially all assets of one, or subdividing an
455 | organization, or merging organizations. If propagation of a covered
456 | work results from an entity transaction, each party to that
457 | transaction who receives a copy of the work also receives whatever
458 | licenses to the work the party's predecessor in interest had or could
459 | give under the previous paragraph, plus a right to possession of the
460 | Corresponding Source of the work from the predecessor in interest, if
461 | the predecessor has it or can get it with reasonable efforts.
462 |
463 | You may not impose any further restrictions on the exercise of the
464 | rights granted or affirmed under this License. For example, you may
465 | not impose a license fee, royalty, or other charge for exercise of
466 | rights granted under this License, and you may not initiate litigation
467 | (including a cross-claim or counterclaim in a lawsuit) alleging that
468 | any patent claim is infringed by making, using, selling, offering for
469 | sale, or importing the Program or any portion of it.
470 |
471 | 11. Patents.
472 |
473 | A "contributor" is a copyright holder who authorizes use under this
474 | License of the Program or a work on which the Program is based. The
475 | work thus licensed is called the contributor's "contributor version".
476 |
477 | A contributor's "essential patent claims" are all patent claims
478 | owned or controlled by the contributor, whether already acquired or
479 | hereafter acquired, that would be infringed by some manner, permitted
480 | by this License, of making, using, or selling its contributor version,
481 | but do not include claims that would be infringed only as a
482 | consequence of further modification of the contributor version. For
483 | purposes of this definition, "control" includes the right to grant
484 | patent sublicenses in a manner consistent with the requirements of
485 | this License.
486 |
487 | Each contributor grants you a non-exclusive, worldwide, royalty-free
488 | patent license under the contributor's essential patent claims, to
489 | make, use, sell, offer for sale, import and otherwise run, modify and
490 | propagate the contents of its contributor version.
491 |
492 | In the following three paragraphs, a "patent license" is any express
493 | agreement or commitment, however denominated, not to enforce a patent
494 | (such as an express permission to practice a patent or covenant not to
495 | sue for patent infringement). To "grant" such a patent license to a
496 | party means to make such an agreement or commitment not to enforce a
497 | patent against the party.
498 |
499 | If you convey a covered work, knowingly relying on a patent license,
500 | and the Corresponding Source of the work is not available for anyone
501 | to copy, free of charge and under the terms of this License, through a
502 | publicly available network server or other readily accessible means,
503 | then you must either (1) cause the Corresponding Source to be so
504 | available, or (2) arrange to deprive yourself of the benefit of the
505 | patent license for this particular work, or (3) arrange, in a manner
506 | consistent with the requirements of this License, to extend the patent
507 | license to downstream recipients. "Knowingly relying" means you have
508 | actual knowledge that, but for the patent license, your conveying the
509 | covered work in a country, or your recipient's use of the covered work
510 | in a country, would infringe one or more identifiable patents in that
511 | country that you have reason to believe are valid.
512 |
513 | If, pursuant to or in connection with a single transaction or
514 | arrangement, you convey, or propagate by procuring conveyance of, a
515 | covered work, and grant a patent license to some of the parties
516 | receiving the covered work authorizing them to use, propagate, modify
517 | or convey a specific copy of the covered work, then the patent license
518 | you grant is automatically extended to all recipients of the covered
519 | work and works based on it.
520 |
521 | A patent license is "discriminatory" if it does not include within
522 | the scope of its coverage, prohibits the exercise of, or is
523 | conditioned on the non-exercise of one or more of the rights that are
524 | specifically granted under this License. You may not convey a covered
525 | work if you are a party to an arrangement with a third party that is
526 | in the business of distributing software, under which you make payment
527 | to the third party based on the extent of your activity of conveying
528 | the work, and under which the third party grants, to any of the
529 | parties who would receive the covered work from you, a discriminatory
530 | patent license (a) in connection with copies of the covered work
531 | conveyed by you (or copies made from those copies), or (b) primarily
532 | for and in connection with specific products or compilations that
533 | contain the covered work, unless you entered into that arrangement,
534 | or that patent license was granted, prior to 28 March 2007.
535 |
536 | Nothing in this License shall be construed as excluding or limiting
537 | any implied license or other defenses to infringement that may
538 | otherwise be available to you under applicable patent law.
539 |
540 | 12. No Surrender of Others' Freedom.
541 |
542 | If conditions are imposed on you (whether by court order, agreement or
543 | otherwise) that contradict the conditions of this License, they do not
544 | excuse you from the conditions of this License. If you cannot convey a
545 | covered work so as to satisfy simultaneously your obligations under this
546 | License and any other pertinent obligations, then as a consequence you may
547 | not convey it at all. For example, if you agree to terms that obligate you
548 | to collect a royalty for further conveying from those to whom you convey
549 | the Program, the only way you could satisfy both those terms and this
550 | License would be to refrain entirely from conveying the Program.
551 |
552 | 13. Use with the GNU Affero General Public License.
553 |
554 | Notwithstanding any other provision of this License, you have
555 | permission to link or combine any covered work with a work licensed
556 | under version 3 of the GNU Affero General Public License into a single
557 | combined work, and to convey the resulting work. The terms of this
558 | License will continue to apply to the part which is the covered work,
559 | but the special requirements of the GNU Affero General Public License,
560 | section 13, concerning interaction through a network will apply to the
561 | combination as such.
562 |
563 | 14. Revised Versions of this License.
564 |
565 | The Free Software Foundation may publish revised and/or new versions of
566 | the GNU General Public License from time to time. Such new versions will
567 | be similar in spirit to the present version, but may differ in detail to
568 | address new problems or concerns.
569 |
570 | Each version is given a distinguishing version number. If the
571 | Program specifies that a certain numbered version of the GNU General
572 | Public License "or any later version" applies to it, you have the
573 | option of following the terms and conditions either of that numbered
574 | version or of any later version published by the Free Software
575 | Foundation. If the Program does not specify a version number of the
576 | GNU General Public License, you may choose any version ever published
577 | by the Free Software Foundation.
578 |
579 | If the Program specifies that a proxy can decide which future
580 | versions of the GNU General Public License can be used, that proxy's
581 | public statement of acceptance of a version permanently authorizes you
582 | to choose that version for the Program.
583 |
584 | Later license versions may give you additional or different
585 | permissions. However, no additional obligations are imposed on any
586 | author or copyright holder as a result of your choosing to follow a
587 | later version.
588 |
589 | 15. Disclaimer of Warranty.
590 |
591 | THERE IS NO WARRANTY FOR THE PROGRAM, TO THE EXTENT PERMITTED BY
592 | APPLICABLE LAW. EXCEPT WHEN OTHERWISE STATED IN WRITING THE COPYRIGHT
593 | HOLDERS AND/OR OTHER PARTIES PROVIDE THE PROGRAM "AS IS" WITHOUT WARRANTY
594 | OF ANY KIND, EITHER EXPRESSED OR IMPLIED, INCLUDING, BUT NOT LIMITED TO,
595 | THE IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR
596 | PURPOSE. THE ENTIRE RISK AS TO THE QUALITY AND PERFORMANCE OF THE PROGRAM
597 | IS WITH YOU. SHOULD THE PROGRAM PROVE DEFECTIVE, YOU ASSUME THE COST OF
598 | ALL NECESSARY SERVICING, REPAIR OR CORRECTION.
599 |
600 | 16. Limitation of Liability.
601 |
602 | IN NO EVENT UNLESS REQUIRED BY APPLICABLE LAW OR AGREED TO IN WRITING
603 | WILL ANY COPYRIGHT HOLDER, OR ANY OTHER PARTY WHO MODIFIES AND/OR CONVEYS
604 | THE PROGRAM AS PERMITTED ABOVE, BE LIABLE TO YOU FOR DAMAGES, INCLUDING ANY
605 | GENERAL, SPECIAL, INCIDENTAL OR CONSEQUENTIAL DAMAGES ARISING OUT OF THE
606 | USE OR INABILITY TO USE THE PROGRAM (INCLUDING BUT NOT LIMITED TO LOSS OF
607 | DATA OR DATA BEING RENDERED INACCURATE OR LOSSES SUSTAINED BY YOU OR THIRD
608 | PARTIES OR A FAILURE OF THE PROGRAM TO OPERATE WITH ANY OTHER PROGRAMS),
609 | EVEN IF SUCH HOLDER OR OTHER PARTY HAS BEEN ADVISED OF THE POSSIBILITY OF
610 | SUCH DAMAGES.
611 |
612 | 17. Interpretation of Sections 15 and 16.
613 |
614 | If the disclaimer of warranty and limitation of liability provided
615 | above cannot be given local legal effect according to their terms,
616 | reviewing courts shall apply local law that most closely approximates
617 | an absolute waiver of all civil liability in connection with the
618 | Program, unless a warranty or assumption of liability accompanies a
619 | copy of the Program in return for a fee.
620 |
621 | END OF TERMS AND CONDITIONS
622 |
623 | How to Apply These Terms to Your New Programs
624 |
625 | If you develop a new program, and you want it to be of the greatest
626 | possible use to the public, the best way to achieve this is to make it
627 | free software which everyone can redistribute and change under these terms.
628 |
629 | To do so, attach the following notices to the program. It is safest
630 | to attach them to the start of each source file to most effectively
631 | state the exclusion of warranty; and each file should have at least
632 | the "copyright" line and a pointer to where the full notice is found.
633 |
634 |
635 | Copyright (C)
636 |
637 | This program is free software: you can redistribute it and/or modify
638 | it under the terms of the GNU General Public License as published by
639 | the Free Software Foundation, either version 3 of the License, or
640 | (at your option) any later version.
641 |
642 | This program is distributed in the hope that it will be useful,
643 | but WITHOUT ANY WARRANTY; without even the implied warranty of
644 | MERCHANTABILITY or FITNESS FOR A PARTICULAR PURPOSE. See the
645 | GNU General Public License for more details.
646 |
647 | You should have received a copy of the GNU General Public License
648 | along with this program. If not, see .
649 |
650 | Also add information on how to contact you by electronic and paper mail.
651 |
652 | If the program does terminal interaction, make it output a short
653 | notice like this when it starts in an interactive mode:
654 |
655 | Copyright (C)
656 | This program comes with ABSOLUTELY NO WARRANTY; for details type `show w'.
657 | This is free software, and you are welcome to redistribute it
658 | under certain conditions; type `show c' for details.
659 |
660 | The hypothetical commands `show w' and `show c' should show the appropriate
661 | parts of the General Public License. Of course, your program's commands
662 | might be different; for a GUI interface, you would use an "about box".
663 |
664 | You should also get your employer (if you work as a programmer) or school,
665 | if any, to sign a "copyright disclaimer" for the program, if necessary.
666 | For more information on this, and how to apply and follow the GNU GPL, see
667 | .
668 |
669 | The GNU General Public License does not permit incorporating your program
670 | into proprietary programs. If your program is a subroutine library, you
671 | may consider it more useful to permit linking proprietary applications with
672 | the library. If this is what you want to do, use the GNU Lesser General
673 | Public License instead of this License. But first, please read
674 | .
675 |
--------------------------------------------------------------------------------
/README.md:
--------------------------------------------------------------------------------
1 | pytruecrypt
2 | ===========
3 |
4 | Truecrypt volume parsing library by originally created by [Gareth Owen](https://github.com/drgowen/), University of Portsmouth, with additional features added by [Adam Swann](https://github.com/4144414d/).
5 |
6 | Library status:
7 | - Decrypts header (can dump raw decrypted header)
8 | - Decodes header fields
9 | - Can dump any decrypted sector
10 | - Hidden volume support
11 | - Veracrypt support
12 | - Can decrypt using only recovered keys (no password required)
13 | - Supports all encryption modes and hash functions offered by Truecrypt
14 | - Can decrypt damaged containers if salt and header keys are recoverable
15 | - Easy to use - see example and source code for API
16 |
17 | Examples:
18 | - dump.py: Header and first sector decrypted hex dump
19 | - image.py: Create decrypted dd image of container
20 | - pw-check.py: Checks password against all available Truecrypt options
21 | - pwcracker.py: Password cracker
22 | - quick-container.py: Produces a working Truecrypt container in seconds
23 | - reserved.py: Hides data within the reserved space of a container
24 |
25 | Other Tools
26 | -----------
27 | - tcplay – pretty much fully featured and stable TrueCrypt implementation
28 | - TCHunt – locates allocated containers
29 | - UNTRUE – checking passwords against TrueCrypt encrypted volumes and disks, and/or decrypting the data
30 | - TestCrypt – helps recover lost TrueCrypt partitions
31 | - TCHead – header brute-forcer and hidden volume detection tool
32 | - Hashcat – cracks things
33 | - Passware – cracks things
34 | - Elcomsoft FDD – cracks things
35 | - [tckfc](https://github.com/Octosec/tckfc) - Searches for vaild keyfiles
36 | - [TrueCrypt Search and Decrypt](https://github.com/theevilbit/tcsandd) - Tool created for 2013 DC3 Forensic Challenge
37 |
38 | Example Usage
39 | -------------
40 | Below are examples on how to use the example scripts.
41 | ####dump.py
42 | dump.py will perform a hex dump of the decrypted header and first sector of a container. It also works with hidden volumes if given the -h option.
43 |
44 | > dump
45 | > dump example.tc
46 | > Enter password: password
47 |
48 | HEADER RAW ----------
49 | 0000 54 52 55 45 00 05 07 00 5c 96 e9 4b 00 00 00 00 TRUE.......K....
50 | 0010 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
51 | 0020 00 00 00 00 00 00 00 00 00 0c 00 00 00 00 00 00 ................
52 | 0030 00 02 00 00 00 00 00 00 00 0c 00 00 00 00 00 00 ................
53 | 0040 00 00 02 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
54 | 0050 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
55 | 0060 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
56 | 0070 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
57 | 0080 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
58 | 0090 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
59 | 00a0 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
60 | 00b0 00 00 00 00 00 00 00 00 00 00 00 00 33 73 eb c2 ............3s..
61 | 00c0 12 12 2c ee 8a ff 05 d5 2f ef d3 6e 49 a9 4a bb ..,...../..nI.J.
62 | 00d0 13 0e 08 f1 3a 93 73 2a 71 86 97 7d 40 70 af 62 ....:.s*q..}@p.b
63 | 00e0 05 8e 6f 27 36 0c 64 06 6e 41 23 8f fe f8 33 65 ..o'6.d.nA#...3e
64 | 00f0 6c 34 f9 54 f1 71 96 f9 36 9e f1 ab 62 75 c6 6b l4.T.q..6...bu.k
65 | 0100 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
66 | 0110 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
67 | 0120 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
68 | 0130 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
69 | 0140 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
70 | 0150 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
71 | 0160 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
72 | 0170 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
73 | 0180 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
74 | 0190 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
75 | 01a0 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
76 | 01b0 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
77 |
78 | HEADER ------------
79 | Magic : TRUE
80 | HdrVersion : 5
81 | MinProgVer : 7
82 | CRC : 1553393995
83 | Reserved :
84 | HiddenVolSize : 0
85 | VolSize : 786432
86 | DataStart : 131072
87 | DataSize : 786432
88 | Flags : 0
89 | SectorSize : 512
90 | Reserved2 :
91 | CRC3 : 863235010
92 | Keys : 12122cee8aff05d52fefd36e49a94abb130e08f13a93732a7186977d4070af62058e6f27360c64066e41238ffef833656c34f954f17196f9369ef1ab6275c66b000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000
93 |
94 | FIRST SECTOR-------
95 | 0000 eb 3c 90 4d 53 44 4f 53 35 2e 30 00 02 01 02 00 .<.MSDOS5.0.....
96 | 0010 02 00 02 00 06 f8 05 00 01 00 01 00 00 00 00 00 ................
97 | 0020 00 00 00 00 00 00 29 dc 16 81 6a 4e 4f 20 4e 41 ......)...jNO NA
98 | 0030 4d 45 20 20 20 20 46 41 54 31 32 20 20 20 00 00 ME FAT12 ..
99 | 0040 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
100 | 0050 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
101 | 0060 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
102 | 0070 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
103 | 0080 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
104 | 0090 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
105 | 00a0 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
106 | 00b0 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
107 | 00c0 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
108 | 00d0 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
109 | 00e0 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
110 | 00f0 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
111 | 0100 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
112 | 0110 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
113 | 0120 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
114 | 0130 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
115 | 0140 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
116 | 0150 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
117 | 0160 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
118 | 0170 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
119 | 0180 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
120 | 0190 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
121 | 01a0 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
122 | 01b0 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
123 | 01c0 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
124 | 01d0 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
125 | 01e0 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
126 | 01f0 00 00 00 00 00 00 00 00 00 00 00 00 00 00 55 aa ..............U.
127 |
128 | ###image.py
129 | image is used to image a Truecrypt container for further analysis. The container can be open with a password or with keys extracted from memory.
130 |
131 | Encryption modes can be assigned long or short hand where:
132 |
133 | aes = a
134 | twofish = t
135 | serpent = s
136 |
137 | For example 'aes-twofish' can be shortened to 'at' and aes-twofish-serpent
138 | to ats.
139 |
140 | Similarly hash functions can be assigned long or short hand where:
141 |
142 | ripemd = r
143 | sha-512 = s
144 | whirlpool = w
145 |
146 | ####Example usage:
147 |
148 | > image pwd [] [-vbh] [(-f -oBYTES -dBYTES)]
149 | > image key [-aKEY -tKEY -sKEY] [(-oBYTES -dBYTES)]
150 |
151 | #####Scenario 1:
152 | You wish to image a Truecrypt file "input1.tc" to an image named "output1.dd",
153 | it uses aes and ripemd. The password is "Scenario1". As ripemd is the default
154 | for Truecrypt it does not need to be specified.
155 |
156 | > image pwd input1.tc output1.dd aes Scenario1
157 |
158 | #####Scenario 2:
159 | You wish to image a Truecrypt file "input2.tc" to an image named "output2.dd",
160 | it uses aes-serpent and sha512. The password is "Scenario2". You wish to save
161 | time and use the short hand commands.
162 |
163 | > image pwd input2.tc output2.dd as Scenario2 s
164 |
165 | #####Scenario 3:
166 | You wish to image a Truecrypt file "input3.tc" to an image named "output3.dd",
167 | it uses aes-serpent. You know it contains a hidden volume and the password is
168 | "Scenario3".
169 |
170 | > image pwd input3.tc output3.dd aes-serpent Scenario3 --hidden
171 |
172 | #####Scenario 4:
173 | You wish to image a Truecrypt file "input4.tc" to an image named "output4.dd",
174 | it uses aes. You do not know the password but have extracted AES keys from
175 | memory.
176 |
177 | > image key input4.tc output4.dd aes --aes bac01155a46547f00c3ddf9a4a765159fbe
178 | 1f68d94bf11a3bd6910eedf26d867a63263c949812cd68b7dad91a8dfdacb96942b93cc1b21ffa
179 | feeb4791a0befa4
180 |
181 |
182 | ###pw-check.py
183 | pw-check.py is used to check that a small list of passwords work against a container. It checks all options available in Truecrypt and allows you to confirm that normal and backup headers match. The -d option will print the decoded header to screen if successful, the -v option will also read Veracrypt files.
184 |
185 | > pw-check
186 | > pw-check example.tc password
187 | password appears to be valid for a Truecrypt standard volume using the normal header using aes and ripemd
188 | password appears to be valid for a Truecrypt standard volume using the backup header using aes and ripemd
189 |
190 | ###pwcracker.py
191 | pwcracker.py is an example password cracker for Truecrypt. Simply provide a word list and it will attempt to crack the container.
192 |
193 | > pwcracker
194 | > pwcracker example.tc wordlist.txt
195 | > PW Found: password
196 |
197 | ###quick-container.py
198 | quick-container.py produces a Truecrypt container quickly by skipping the first stage encryption setting. This is therefore similar to 'quick format' full disk encryption whereby the free space is not first encrypted. This means a hidden volume is very obvious and it's possible to track the ammount of encrypted data stored within a container.
199 |
200 | The containers are not formatted and once mounted will require a file system to be created. Containers are always created using AES and ripemd.
201 |
202 | > quick-container
203 | > quick-container example password 1024
204 |
205 | ###reserved.py
206 | reserved.py uses the free space in the Truecrypt header to hide additional data. This data is encrypted with the same password as the container itself.
207 |
208 | To hide a file:
209 |
210 | > reserved hide
211 | > reserved hide example.tc password secret.txt
212 |
213 | To read a hidden file:
214 |
215 | > reserved check
216 | > reserved check example.tc password
217 | > My secret file...
218 |
219 | Prerequisites:
220 | -------------
221 | You must have pycryptoplus installed - https://github.com/doegox/python-cryptoplus
222 |
223 | For many examples you must have docopt installed - http://docopt.org/
224 |
225 | Truecrypt Documentation:
226 | -------------
227 |
228 | Very little as the code is generally compact. See the examples, and pyTruecrypt.py - the comments show how to use it. I am slowly expanding this section.
229 |
230 | ###Truecrypt Basics
231 | Truecrypt works in two main ways either as full disk encryption or using
232 | encrypted containers on Windows, Linux, or OSX. On windows it is also
233 | possible to encrypt the operating system with Truecrypt and boot into
234 | windows. This is not possible on Linux or OSX but it can still use full
235 | disk encryption on non OS disks.
236 |
237 | ###Algorithms
238 | Truecrypt allows the following encryption schemes all working in XTS
239 | mode. Where more than one encryption algorithm is used the data is
240 | encrypted with each algorithm using different master keys.
241 |
242 | - AES (default)
243 | - Serpent
244 | - Twofish
245 | - AES - Twofish
246 | - AES - Twofish - Serpent
247 | - Serpent - AES
248 | - Serpent - Twofish - AES
249 |
250 | Three hash algorithms are available, these are:
251 |
252 | - RIPEMD (default)
253 | - SHA-512
254 | - WHIRLPOOL
255 |
256 |
257 | ###Encryption in Truecrypt
258 |
259 | Truecrypt uses each of the different encryption algorithms in XTS mode.
260 | In short this means that same plain text data encrypted with the same
261 | key but in a different location will produce a different cipher text.
262 | For example a completely zeroed disk encrypted with XTS mode would look
263 | completely random, each sector of zeros produces a different sector of
264 | encrypted data. If ECB mode was used instead you would see a repeating
265 | pattern where each sector of zeros produced the same sector of encrypted
266 | data.
267 |
268 | Truecrypt stores the master keys within the Truecrypt header and these
269 | keys are not generated based on the password chosen for the container.
270 | Instead the master keys are generated randomly when the container is
271 | created and stored in the header, the header is then encrypted using the
272 | password provided for by the user. Only by knowing the password to the
273 | header can you successfully decrypt the header and get to the master
274 | keys to decrypt the data.
275 |
276 | This allows the user to change the password to a container. Rather then
277 | needing to re-encrypt the whole container only the headers need to be
278 | re-encrypted with the new password, the master keys remain the same.
279 |
280 | This raises the obvious risk, if an attacker can decrypt the header at
281 | any point in time they can use the master keys to decrypt data. I.E. A
282 | container is created with a simple password, the attacker cracks this
283 | password and stores the master keys. Later the users changes the password
284 | to the container in an effort to increase security, however the attacker
285 | already has the master keys and as such can decrypt the container.
286 |
287 |
288 | ###Volumes
289 |
290 | TrueCrypt allows the user to have a normal volume and a hidden volume.
291 | The normal volume is designed to be well encrypted but if the TrueCrypt
292 | volume is detected you would not be able to plausibly deny its
293 | existence, and so rubber hose cryptanalysis could be used to get the
294 | password from you. The hidden volume on the other hand is designed to
295 | hide within the normal volume and would look like any other section of
296 | random data, allowing you to plausibly deny it being there.
297 |
298 | The layout of a container is shown in below. The first 256 sectors store
299 | the main headers, while the last 256 sectors store the backup headers
300 | should the main headers be damaged. Everything in-between is the data
301 | section of the container and will store the actual user data.
302 |
303 | Almost everything within the container is encrypted so normal analysis
304 | of the file will simply show ‘random’ data. Only the salts for each of
305 | the headers are store in a decrypted form, however these are simply 64
306 | bits of random data so should be impossible to tell them apart.
307 |
308 | The normal and backup headers contain the same decrypted data however
309 | they are encrypted with different salts. This means they will appear to
310 | be completely different on the binary level.
311 |
312 | The space in the headers (254 sectors in total) is seeded with random
313 | data when the container is first created. This is one of the main
314 | reasons it’s difficult to detect a hidden volume, with or without one
315 | this sector will seemingly contain random data.
316 |
317 | 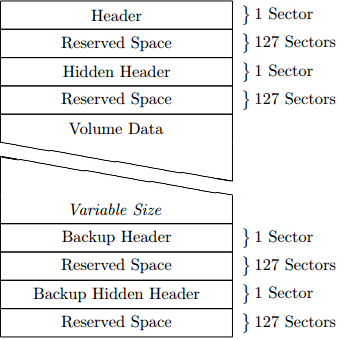
318 |
319 | ###Truecrypt Header v5
320 |
321 | Truecrypt 7.1a uses the header version 5. This header is the same for
322 | normal and hidden volumes and system encryption, the difference is
323 | simply their location and flag bits.
324 |
325 | ####Header Elements
326 |
327 | **1) Salt - 64 Bytes**
328 |
329 | The salt is used when encrypting the header. This is randomly generated data and so will look as if it’s encrypted.
330 |
331 | **2) File Signature - 4 Bytes**
332 |
333 | The ASCII string ‘TRUE’. This is used to check if the header has been decrypted correctly.
334 |
335 | **3) Header Version - 2 Bytes**
336 |
337 | The version of Truecrypt header in use, for 7.1a this will always be \x00\x05.
338 |
339 | **4) Truecrypt Version - 2 Bytes**
340 |
341 | The minimum version of Truecrypt needed to use the volume. For 7.1a this is always be [\\x00\\x07](\x00\x07).
342 |
343 | **5) Key CRC - 4 Bytes**
344 |
345 | CRC32 value for the bytes 256-511 of the header. I.E. the master keys. This is also used to confirm if the Truecrypt header has been decrypted correctly.
346 |
347 | **6) Reserved Space - 16 Bytes**
348 |
349 | 16 Bytes of \x00 which aren’t used in the header.
350 |
351 | **7) Size of Hidden Volume - 8 Bytes**
352 |
353 | The size in bytes of the hidden volume. This is set to zero in a non-hidden volume.
354 |
355 | **8) Size of Hidden Volume - 8 Bytes**
356 |
357 | The size in bytes of the volume.
358 |
359 | **9) Offset to Data - 8 Bytes**
360 |
361 | The is the byte offset from the start of the data. If this header is for a normal (non-hidden) container this should be \x00\x00\x00\x00\x00\x02\x00\x00. This is 131072 bytes, or sector 256.
362 |
363 | **10) Size of Data - 8 Bytes**
364 |
365 | The total size in bytes of the data portion of the container.
366 |
367 | **11) Flag Bits - 4 Bytes**
368 |
369 | Used to determine what type of container is in use. Bit 0 is set for system encryption, while bit 1 is set for non-system in place encryption. The other bits are not used.
370 |
371 | **12) Reserved Space - 120 Bytes**
372 |
373 | Further space in the header which isn’t used.
374 |
375 | **13) Header CRC - 4 Bytes**
376 |
377 | A CRC32 value for the bytes 64-251 of the header.
378 |
379 | **14) Master Keys - 32 Bytes each**
380 |
381 | The remaining space is devoted to the master keys. If multiple encryption algorithms are used then multiple keys will be present. Each 'master key' is comprised of 2 separate 256-bit keys for XTS.
382 |
383 | 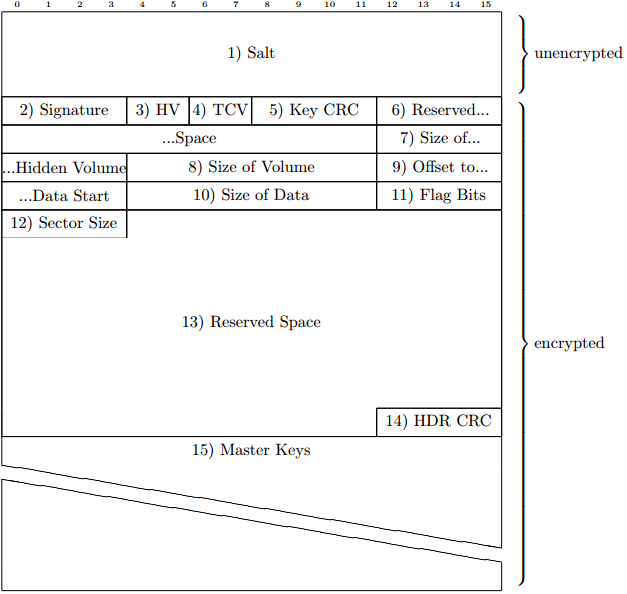
384 |
385 | PyVmMonitor is being used to make this script faster! Check it out http://www.pyvmmonitor.com/
386 |
--------------------------------------------------------------------------------
/examples/dump.py:
--------------------------------------------------------------------------------
1 | # Truecrypt parsing library for Python by Gareth Owen
2 | # https://github.com/drgowen/pytruecrypt/
3 | # See LICENCE for licence details
4 |
5 | # PyTruecrypt is free software: you can redistribute it and/or modify
6 | # it under the terms of the GNU General Public License as published by
7 | # the Free Software Foundation, either version 3 of the License, or
8 | # (at your option) any later version.
9 |
10 | # PyTruecrypt is distributed in the hope that it will be useful,
11 | # but WITHOUT ANY WARRANTY; without even the implied warranty of
12 | # MERCHANTABILITY or FITNESS FOR A PARTICULAR PURPOSE. See the
13 | # GNU General Public License for more details.
14 |
15 | # You should have received a copy of the GNU General Public License
16 | # along with PyTruecrypt. If not, see .
17 |
18 | # Dumps truecrypt header and first sector from volume
19 |
20 | import sys
21 |
22 | sys.path.append("..")
23 |
24 | from pytruecrypt import *
25 | import binascii
26 | import os
27 | from subprocess import *
28 | import stat
29 | import getpass
30 | import getopt
31 |
32 | hidden = False
33 |
34 | args = getopt.getopt(sys.argv[1:], "h")
35 |
36 | # parse cmdline options
37 | for k in args[0]:
38 | if k[0]=='-h':
39 | hidden = True
40 |
41 | if len(args[1]) != 1:
42 | print "Usage: python dump.py [-h] volumepath"
43 | print "Dump truecrypt volume"
44 | print
45 | print " -h\tdump hidden volume"
46 | print
47 | sys.exit(1)
48 |
49 | FILENAME = args[1][0]
50 | PASSWORD = getpass.getpass("Enter password: ")
51 |
52 | #initialise pytruecrypt
53 | tc = PyTruecrypt(FILENAME)
54 |
55 | #open volume (returns false on failure)
56 | if not tc.open(PASSWORD, hidden=hidden):
57 | print "Failed to open volume -maybe incorrect pw"
58 | sys.exit(1)
59 |
60 | #Print header fields
61 | print "HEADER RAW ----------"
62 | print hexdump(tc.getHeaderRaw())
63 |
64 | print "HEADER ------------"
65 | hdr = tc.getHeader()
66 | for k in hdr:
67 | print k, ":",
68 |
69 | if k=="Keys":
70 | print binascii.hexlify(hdr[k])
71 | else:
72 | print hdr[k]
73 |
74 | #Print first sector
75 | print "FIRST SECTOR-------"
76 | print hexdump(tc.getPlainSector(0))
77 |
--------------------------------------------------------------------------------
/examples/ent-chains.py:
--------------------------------------------------------------------------------
1 | """
2 | ent-chains looks for chains of high entropy data.
3 |
4 | GitHub: https://github.com/4144414D/pytruecrypt
5 | Email: adam@nucode.co.uk
6 |
7 | Usage:
8 | ent-chains --chain= [--ent=]
9 |
10 | Options:
11 | -h, --help Show this screen.
12 | -c n, --chain n n is number of sectors in a row required for a chain.
13 | -e x, --ent x x is the value to use as 'high' entropy [default: 7.4].
14 |
15 | """
16 |
17 | from docopt import docopt
18 | import math
19 | from bitarray import bitarray
20 | import os
21 | import numpy as np
22 |
23 | #jaradc - https://gist.github.com/jaradc/eeddf20932c0347928d0da5a09298147
24 | def entropy(data):
25 | """ Computes entropy of label distribution. """
26 | labels = list(data)
27 | n_labels = 512.0
28 |
29 | value,counts = np.unique(labels, return_counts=True)
30 | probs = counts / n_labels
31 |
32 | n_classes = np.count_nonzero(probs)
33 |
34 | ent = 0.
35 |
36 | # Compute entropy
37 | for i in probs:
38 | ent -= i * math.log(i, 2)
39 | return ent
40 |
41 | def chain_search(source_entropy,target):
42 | target = int(target)
43 | chains = []
44 | cur_start = -1
45 | cur_len = -1
46 | tick = 0
47 | for x in range(len(source_entropy)):
48 | tick += 1
49 | if tick == 500:
50 | tick = 0
51 | percentage = (float(100) / len(source_entropy)) * x
52 | print "\rFinding chains... {}%".format(percentage),
53 | if source_entropy[x]:
54 | #contiune chain or start new chain
55 | if cur_len > -1:
56 | #contiune chain
57 | cur_len += 1
58 | else:
59 | #start new chain
60 | cur_start = x
61 | cur_len = 0
62 | else:
63 | #end chain or skip
64 | if cur_len > -1:
65 | #end chain
66 | cur_len += 1
67 | if cur_len >= target:
68 | #append current chain to list
69 | chains.append([cur_start,cur_len])
70 | #reset chaiin stats
71 | cur_start = -1
72 | cur_len = -1
73 | else:
74 | #skip one entropy sector
75 | pass
76 | print "\rFinding chains... 100% "
77 | return chains
78 |
79 | def main(arguments):
80 | f = open(arguments[''], 'rb')
81 | f.seek(0, os.SEEK_END)
82 | size = f.tell()
83 | f.seek(0)
84 |
85 | source_entropy = bitarray()
86 | #run entropy calculations
87 | tick = 0
88 | target = float(arguments['--ent'])
89 | for x in range(0,size,512):
90 | tick += 1
91 | if tick == 1000:
92 | tick = 0
93 | percentage = (float(100) / size) * x
94 | print "\rCalculating source entropy... {}%".format(percentage),
95 | data = f.read(512)
96 | if entropy(data) > target:
97 | source_entropy.append(True)
98 | else:
99 | source_entropy.append(False)
100 | print "\rCalculating source entropy... 100% "
101 |
102 | target = int(arguments['--chain'])
103 |
104 | chains = chain_search(source_entropy,target)
105 | if len(chains) > 0:
106 | print
107 | print "start\tlen"
108 | for chain in chains:
109 | print "{}\t{}".format(chain[0],chain[1])
110 | else:
111 | print "No chains found."
112 |
113 | if __name__ == '__main__':
114 | arguments = docopt(__doc__)
115 | main(arguments)
116 |
--------------------------------------------------------------------------------
/examples/hunt.md:
--------------------------------------------------------------------------------
1 | This tutorial explains how to use [hunt](https://github.com/4144414D/pytruecrypt/blob/master/examples/hunt.py) to locate and recover deleted and/or damaged TrueCrypt containers.
2 |
3 | These techniques will help you locate the containers but you will require either the password or a memory dump containing the container keys.
4 |
5 | Example #1 – a container in unallocated space
6 | =============================================
7 |
8 | The example was generated by creating an NTFS volume, placing the target TrueCrypt container inside the volume, and then reformatting the volume with NTFS again.
9 |
10 | This is a contrived example. There are no other files to cause confusion, there is no fragmentation of the container, and none of the TrueCrypt container has been overwritten. It is possible to simply extract the container just by looking at the image and finding the large section of high entropy data. Nevertheless, this should help provide the basic understanding of the process.
11 |
12 | This tutorial talks about sectors and makes the assumption that they are always 512 bytes in size when you see the word sector think 512 bytes of data.
13 |
14 | [Download the example image here.](https://raw.githubusercontent.com/4144414D/pytruecrypt/gh-pages/resources/example.zip)
15 |
16 | ```
17 | MD5 checksum: f45df1f19969cc9007d11ce742a5f0ad
18 | SHA1 checksum: c5e66174a9b6930138f0918171bcca51ed0a88ed
19 | ```
20 |
21 | How hunt locates the container
22 | ------------------------------
23 |
24 | Before running hunt it is important to understand how hunt is locating the container.
25 |
26 | It provides two options:
27 | - A brute force approach for testing all sectors of the image. This is extremely slow and is only useful if you have already extracted what you think is a TrueCrypt header.
28 | - A chain approach where it looks for sequential sectors of high entropy data.
29 |
30 | This tutorial only discusses the chain approach.
31 |
32 | The diagram below shows the entropy (Shannon entropy) of each sector on the disk. We can see a large section of high entropy data from around sector 27701 to around 48476. This is the container. By looking for sections of continuous high entropy we can target the likely locations of TrueCrypt headers. By checking the sectors around 27701 and 48476 we are able to check a small number of sectors as every check will take some time, particularly on VeraCrypt headers.
33 |
34 | 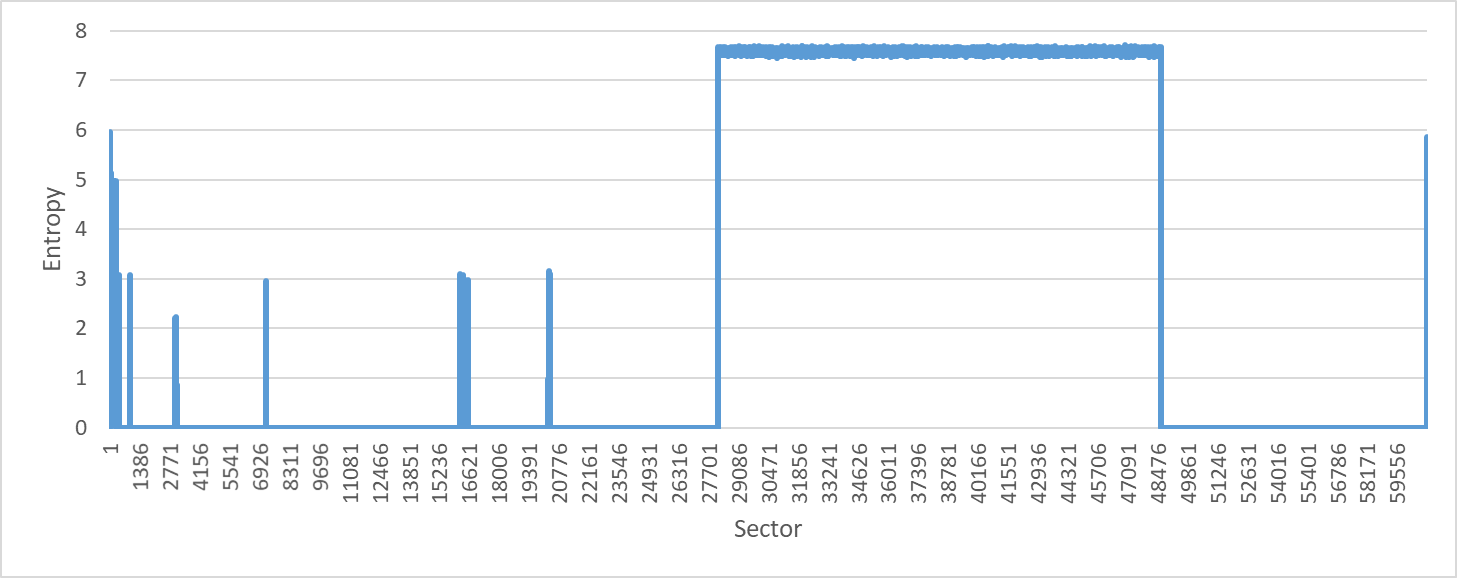
35 |
36 | You are not required to do any of this work yourself. hunt will calculate the entropy and do this targeting for you. This section is just explaining what is happening.
37 |
38 | A few warnings. There will, of course, be high other sections of high entropy on a normal disk. Files such as compressed images or zip files will themselves have high entropy. The time wasted by attempting to decrypt these can be avoided by using a high sector chain count. This works because containers are typically quite large and should stand out against these other files.
39 |
40 | It is possible to create a container with low entropy and with smaller sections of high entropy. This happens if the ‘dynamic’ option is chosen when creating the container. If this is the case you need to look for the header itself which is only 256 sectors in size. This will cause many more false positives as other files with high entropy may be this small.
41 |
42 |
43 | Running hunt
44 | ------------
45 |
46 | For this example hunt is called with the following command:
47 |
48 | ```
49 | hunt example.001 password –chain=256
50 | ```
51 |
52 | The options are as follows:
53 | - example.001 – this is the filename of the example dd image
54 | - password – this is the password for the container
55 | - chain=256 – this is the minimum size of the chain that hunt will look for
56 |
57 | hunt will look like this when it is run. It starts by calculating the entropy of each sector in the image. It will then locate chains of high entropy. Once these chains have been located it will begin testing sectors looking for valid headers.
58 |
59 | We can see that it started checking at sector 28152 and found a fully valid header at sector 28160. This whole process took less than a minute and is much faster than trying brute force and test every sector in the image.
60 |
61 | 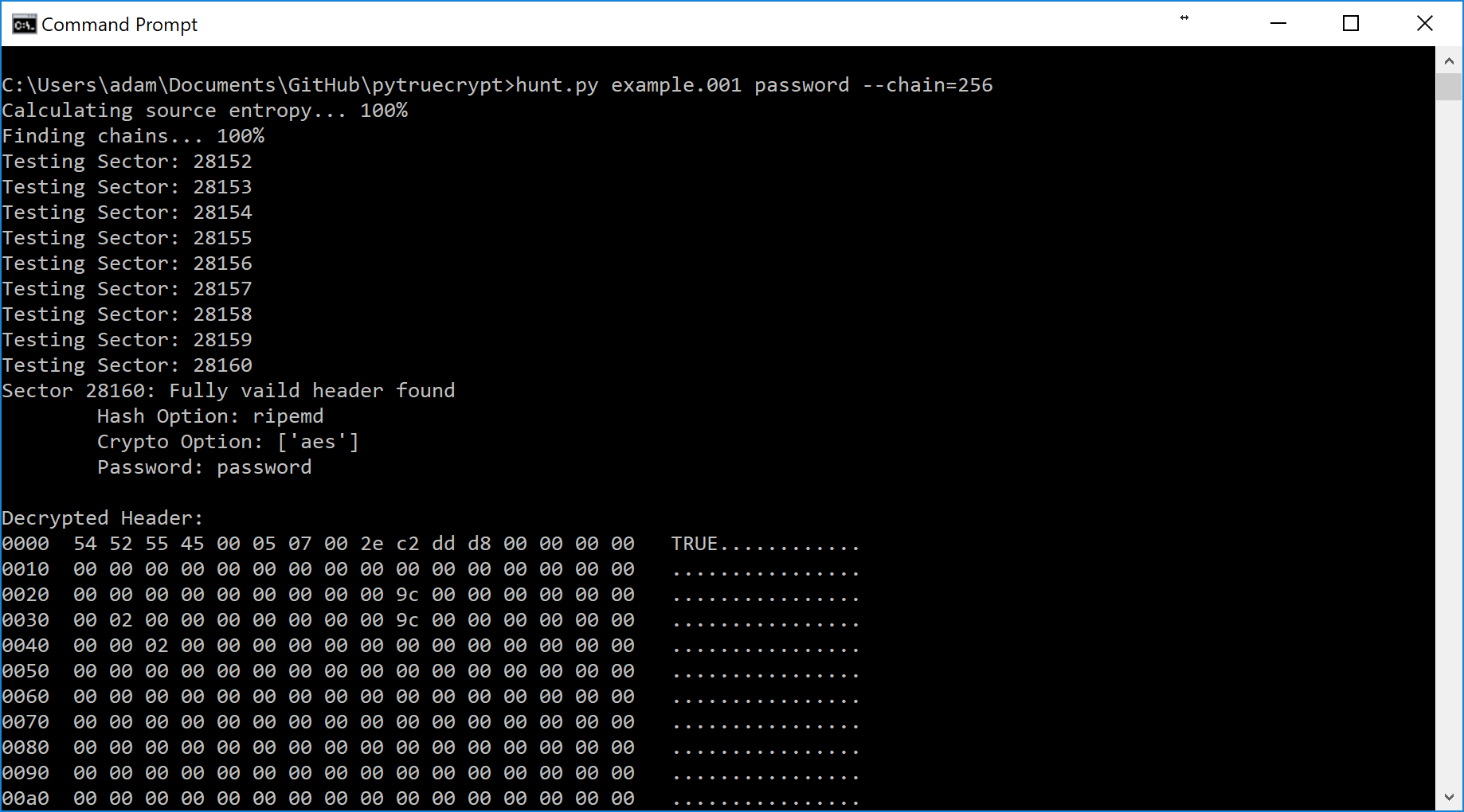
62 |
63 | The headers that have been located are also saved into a text file named results.txt. In this example, two headers were located. This is expected as each container will have a normal header and a backup header. Looking at the decrypted header we can see that they are identical. Please note that they will appear different on the disk as they are encrypted with different salts.
64 |
65 | ```
66 | Sector 28160: Fully valid header found
67 | Hash Option: ripemd
68 | Crypto Option: ['aes']
69 | Password: password
70 |
71 | Decrypted Header:
72 | 0000 54 52 55 45 00 05 07 00 2e c2 dd d8 00 00 00 00 TRUE............
73 | 0010 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
74 | 0020 00 00 00 00 00 00 00 00 00 9c 00 00 00 00 00 00 ................
75 | 0030 00 02 00 00 00 00 00 00 00 9c 00 00 00 00 00 00 ................
76 | 0040 00 00 02 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
77 | 0050 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
78 | 0060 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
79 | 0070 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
80 | 0080 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
81 | 0090 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
82 | 00a0 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
83 | 00b0 00 00 00 00 00 00 00 00 00 00 00 00 b1 2d f8 8c .............-..
84 | 00c0 f3 00 d5 78 08 30 66 2f 17 99 08 27 28 17 c2 20 ...x.0f/...'(..
85 | 00d0 b7 2e 9a 14 79 da 01 77 63 98 37 af 75 da 95 41 ....y..wc.7.u..A
86 | 00e0 93 1f f6 7e 13 d3 b3 c5 de f2 2f cc 00 b5 98 b9 ...~....../.....
87 | 00f0 77 55 00 d4 5b b4 e4 7c 77 7e 5e 65 a3 ec 32 c3 wU..[..|w~^e..2.
88 | 0100 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
89 | 0110 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
90 | 0120 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
91 | 0130 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
92 | 0140 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
93 | 0150 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
94 | 0160 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
95 | 0170 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
96 | 0180 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
97 | 0190 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
98 | 01a0 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
99 | 01b0 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
100 |
101 | Sector 48384: Fully valid header found
102 | Hash Option: ripemd
103 | Crypto Option: ['aes']
104 | Password: password
105 |
106 | Decrypted Header:
107 | 0000 54 52 55 45 00 05 07 00 2e c2 dd d8 00 00 00 00 TRUE............
108 | 0010 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
109 | 0020 00 00 00 00 00 00 00 00 00 9c 00 00 00 00 00 00 ................
110 | 0030 00 02 00 00 00 00 00 00 00 9c 00 00 00 00 00 00 ................
111 | 0040 00 00 02 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
112 | 0050 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
113 | 0060 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
114 | 0070 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
115 | 0080 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
116 | 0090 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
117 | 00a0 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
118 | 00b0 00 00 00 00 00 00 00 00 00 00 00 00 b1 2d f8 8c .............-..
119 | 00c0 f3 00 d5 78 08 30 66 2f 17 99 08 27 28 17 c2 20 ...x.0f/...'(..
120 | 00d0 b7 2e 9a 14 79 da 01 77 63 98 37 af 75 da 95 41 ....y..wc.7.u..A
121 | 00e0 93 1f f6 7e 13 d3 b3 c5 de f2 2f cc 00 b5 98 b9 ...~....../.....
122 | 00f0 77 55 00 d4 5b b4 e4 7c 77 7e 5e 65 a3 ec 32 c3 wU..[..|w~^e..2.
123 | 0100 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
124 | 0110 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
125 | 0120 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
126 | 0130 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
127 | 0140 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
128 | 0150 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
129 | 0160 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
130 | 0170 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
131 | 0180 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
132 | 0190 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
133 | 01a0 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
134 | 01b0 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
135 | ```
136 |
137 |
138 | At this point will know where the headers are and could simply now export the data. However, it is good practice to parse the header and verify our findings. The simplest way to do this is to use the ‘dump.py’ example. Hunt will extract the sectors that are likely to be headers to separate small dd files, in this case, PS28160.dd and PS48384.dd. The names showing they came from physical sector 28160 and 48384 respectively.
139 |
140 | The command is simply dump.py PS28160.dd. You will then be prompted for the password. This will dump the raw header and then they extracted values for convenience.
141 |
142 | 
143 |
144 | The extracted values for this example are:
145 |
146 | ```
147 | Magic : TRUE
148 | HdrVersion : 5
149 | MinProgVer : 7
150 | CRC : 784522712
151 | Reserved :
152 | HiddenVolSize : 0
153 | VolSize : 10223616
154 | DataStart : 131072
155 | DataSize : 10223616
156 | Flags : 0
157 | SectorSize : 512
158 | Reserved2 :
159 | CRC3 : 2972579980
160 | Keys : f300d5780830662f179908272817c220b72e9a1479da0177639837af75da9541931ff67e13d3b3c5def22fcc00b598b9775500d45bb4e47c777e5e65a3ec32c3000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000
161 | ```
162 |
163 | In this example, we are interested in DataStart and DataSize. We will check that the backup header was found in the right location and will help us know that the file is not fragmented.
164 |
165 | To check this the formula we need is:
166 |
167 | ```
168 | header_location + ((DataStart + DataSize) / 512) = backup_location
169 | ```
170 |
171 | Which for this example is:
172 |
173 | ```
174 | 28160 + ((131072 + 10223616) / 512) = 48384
175 | ```
176 |
177 | 48384 is the correct location for the backup header that was located. Therefore we can be reasonably confident that we have located the entire container and there is no fragmentation. If this formula does not point to the backup header then further work will be required, this is not covered here.
178 | We can now extract the entire container and open it with TrueCrypt. dd is one of the many tools that could do this. The dd command for this example is:
179 |
180 | ```
181 | dd if=example.001 of=recovered.tc bs=512 skip=28160 count=20480
182 | ```
183 |
184 | 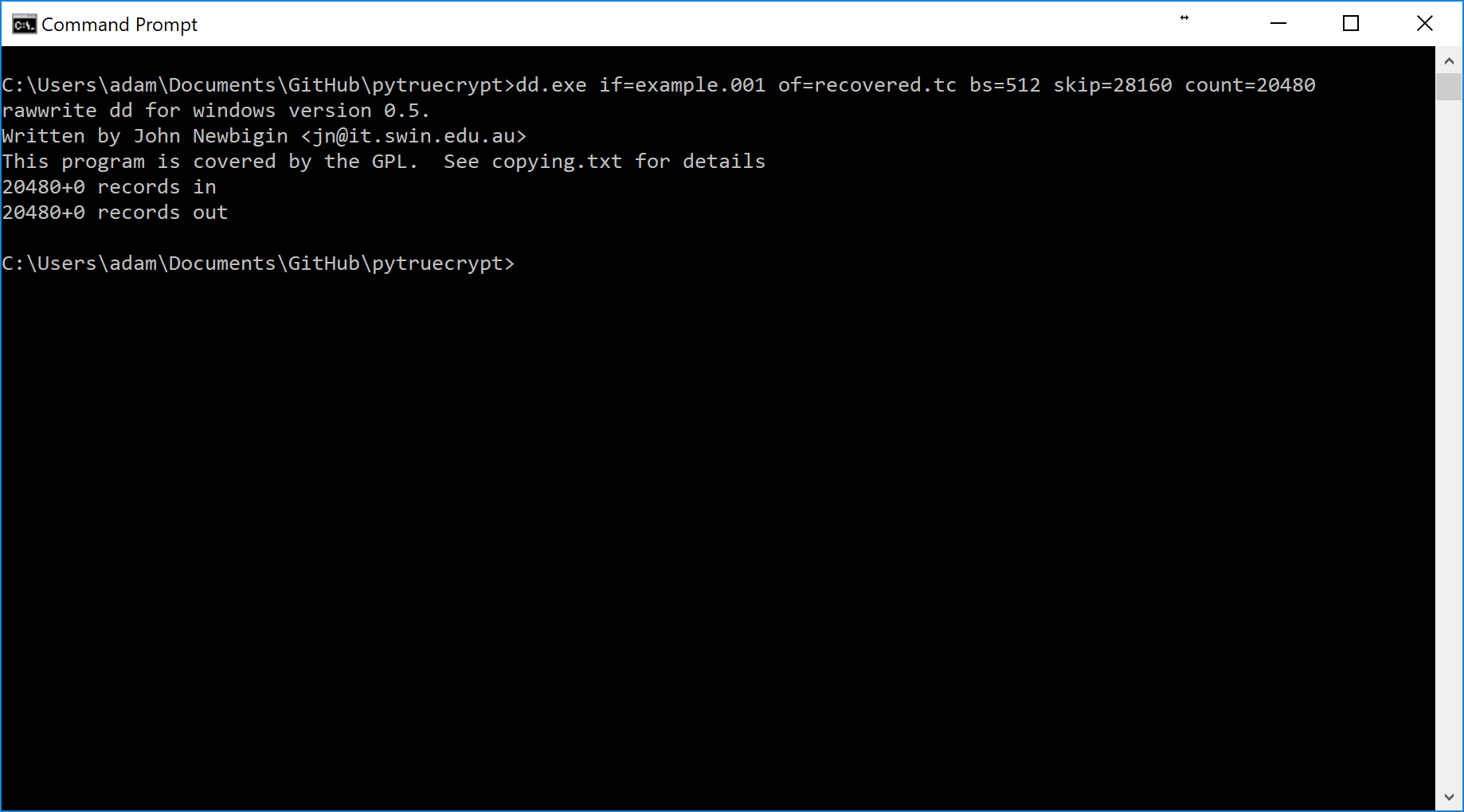
185 |
186 | The resulting container can then be opened in TrueCrypt.
187 |
188 | 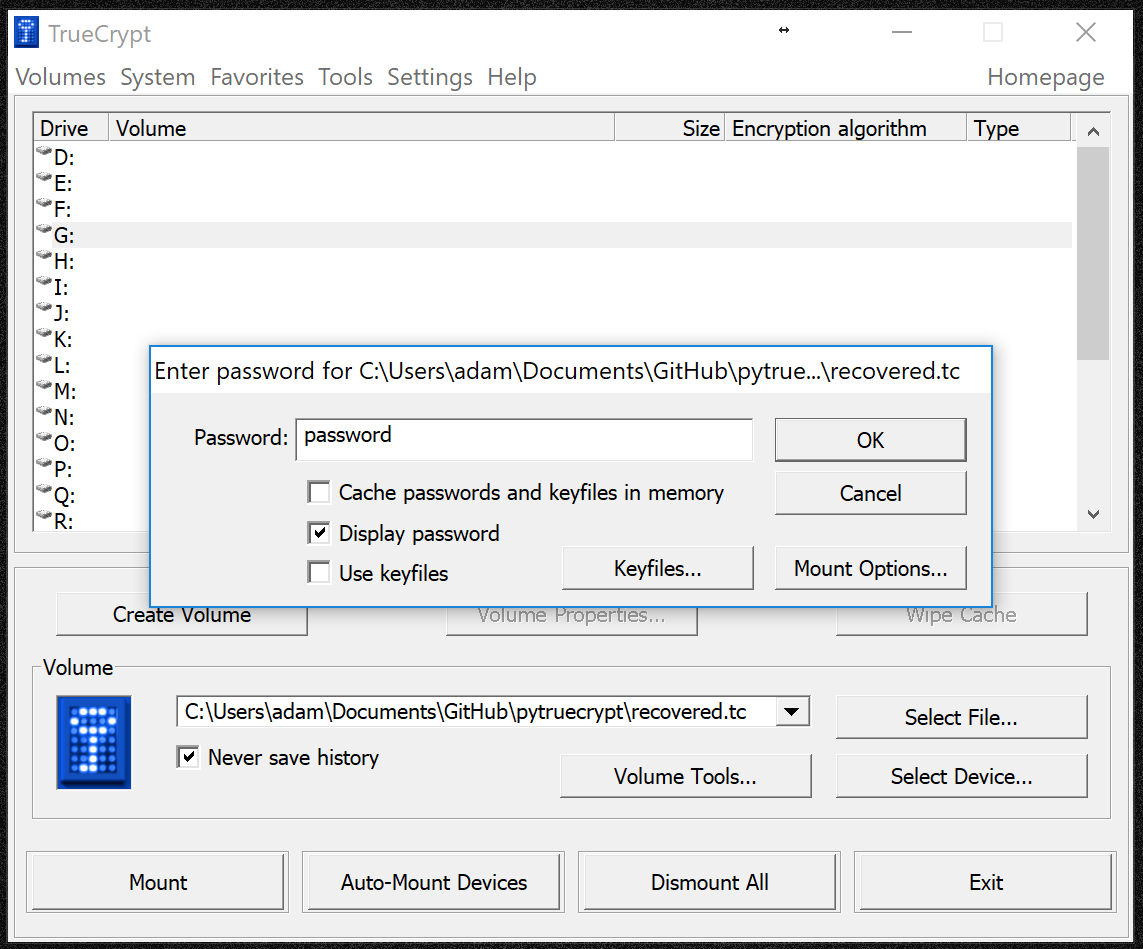
189 |
190 | Once mounted we can use the container in the normal way:
191 |
192 | 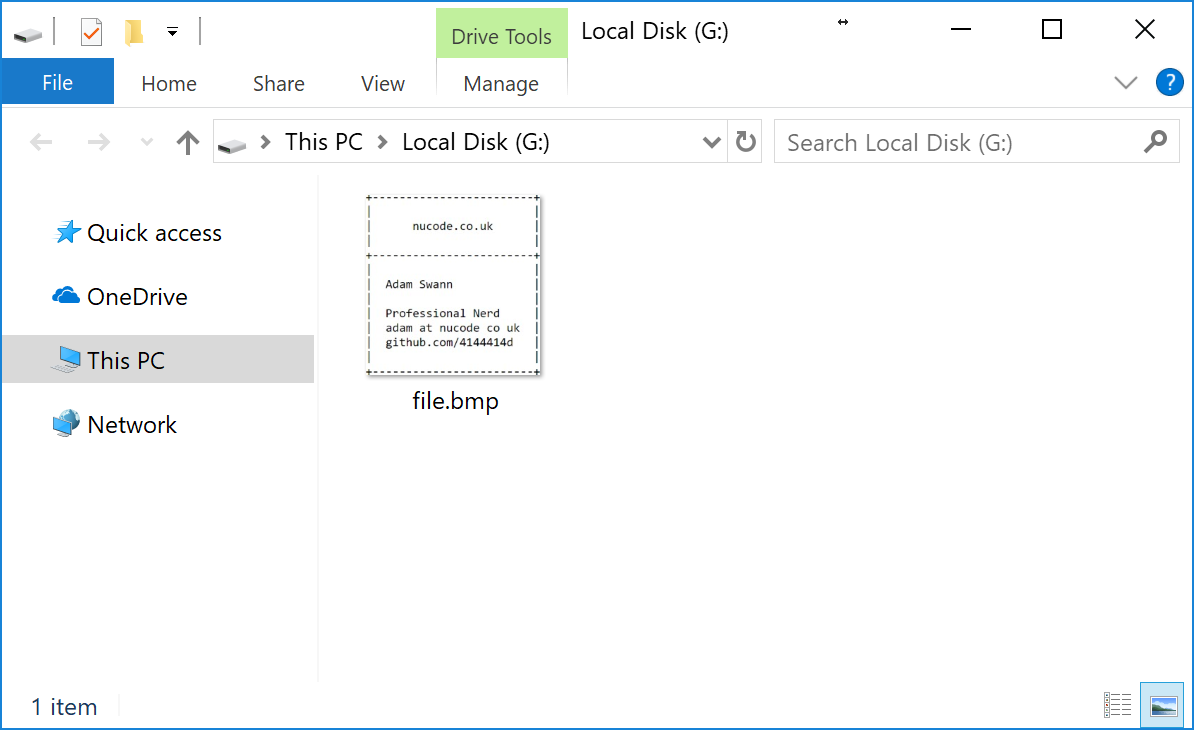
193 |
194 | We can see it simply contains a single image file:
195 |
196 | 
197 |
198 | Example #2 – a damaged container
199 | ================================
200 | This exmaple was created as follows:
201 | - creating a FAT volume
202 | - placing the container on it (password is password)
203 | - reformatting the FAT volume
204 | - copying some images into the FAT volume
205 |
206 | This means that the header of the container has been overwritten by the images. In order to recover this container, we'll need to locate the backup header and work out where the start of the container should have been.
207 |
208 | [Download the example2 image here.](https://raw.githubusercontent.com/4144414D/pytruecrypt/gh-pages/resources/example2.zip)
209 |
210 | ```
211 | MD5 checksum: 3ed9e673027fa14719b00a42bfcef141
212 | SHA1 checksum: a5293105c3fae92168546c493e76ed1547cab117
213 | ```
214 |
215 | Locating the backup header
216 | --------------------------
217 | Looking at the FAT volume we can map out the layout of the files. The layout of the first 1024 sectors is shown below. The process for creating this map is not detailed here, it is for explanatory purposes.
218 |
219 | 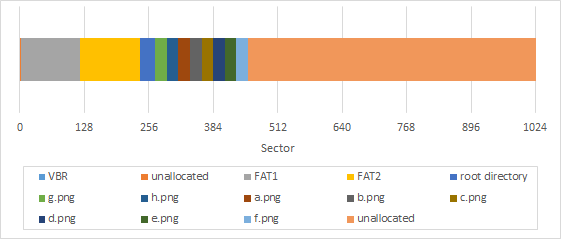
220 |
221 | We can now use hunt to try and locate some headers. hunt is called in exactly the same way as before:
222 | ```
223 | hunt example2.001 password –chain=256
224 | ```
225 |
226 | In this instance, only one header was located at sector 20496.
227 |
228 | ```
229 | Sector 20496: Fully valid header found
230 | Hash Option: ripemd
231 | Crypto Option: ['aes']
232 | Password: password
233 |
234 | Decrypted Header:
235 | 0000 54 52 55 45 00 05 07 00 2e c2 dd d8 00 00 00 00 TRUE............
236 | 0010 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
237 | 0020 00 00 00 00 00 00 00 00 00 9c 00 00 00 00 00 00 ................
238 | 0030 00 02 00 00 00 00 00 00 00 9c 00 00 00 00 00 00 ................
239 | 0040 00 00 02 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
240 | 0050 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
241 | 0060 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
242 | 0070 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
243 | 0080 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
244 | 0090 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
245 | 00a0 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
246 | 00b0 00 00 00 00 00 00 00 00 00 00 00 00 b1 2d f8 8c .............-..
247 | 00c0 f3 00 d5 78 08 30 66 2f 17 99 08 27 28 17 c2 20 ...x.0f/...'(..
248 | 00d0 b7 2e 9a 14 79 da 01 77 63 98 37 af 75 da 95 41 ....y..wc.7.u..A
249 | 00e0 93 1f f6 7e 13 d3 b3 c5 de f2 2f cc 00 b5 98 b9 ...~....../.....
250 | 00f0 77 55 00 d4 5b b4 e4 7c 77 7e 5e 65 a3 ec 32 c3 wU..[..|w~^e..2.
251 | 0100 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
252 | 0110 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
253 | 0120 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
254 | 0130 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
255 | 0140 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
256 | 0150 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
257 | 0160 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
258 | 0170 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
259 | 0180 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
260 | 0190 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
261 | 01a0 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
262 | 01b0 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
263 | ```
264 |
265 | At this point, we cannot be sure if this is a normal header or a backup header. A quick check is to look at the sector that would immediately follow the header. This would be 256 sectors after the header. For this example this would be 20496 + 256 = 20752. Looking at sector 20752 we can see that it is not highly random like we would expect from a container. Therefore we can make the assumption that we have located the backup header.
266 |
267 | ```
268 | Offset 0 1 2 3 4 5 6 7 8 9 A B C D E F
269 |
270 | 00A22000 2E 20 20 20 20 20 20 20 20 20 20 10 00 0E 57 38 . W8
271 | 00A22010 67 4C 67 4C 00 00 58 38 67 4C 02 28 00 00 00 00 gLgL X8gL (
272 | 00A22020 2E 2E 20 20 20 20 20 20 20 20 20 10 00 0E 57 38 .. W8
273 | 00A22030 67 4C 67 4C 00 00 58 38 67 4C 00 00 00 00 00 00 gLgL X8gL
274 | 00A22040 44 45 53 4B 54 4F 50 20 49 4E 49 26 18 0E 57 38 DESKTOP INI& W8
275 | 00A22050 67 4C 67 4C 00 00 58 38 67 4C 03 28 81 00 00 00 gLgL X8gL (
276 | 00A22060 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
277 | 00A22070 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
278 | 00A22080 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
279 | 00A22090 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
280 | 00A220A0 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
281 | 00A220B0 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
282 | 00A220C0 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
283 | 00A220D0 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
284 | 00A220E0 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
285 | 00A220F0 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
286 | 00A22100 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
287 | 00A22110 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
288 | 00A22120 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
289 | 00A22130 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
290 | 00A22140 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
291 | 00A22150 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
292 | 00A22160 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
293 | 00A22170 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
294 | 00A22180 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
295 | 00A22190 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
296 | 00A221A0 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
297 | 00A221B0 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
298 | 00A221C0 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
299 | 00A221D0 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
300 | 00A221E0 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
301 | 00A221F0 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
302 | ```
303 |
304 | Using dump.py we are able to parse the header that has been located.
305 |
306 | ```
307 | Magic : TRUE
308 | HdrVersion : 5
309 | MinProgVer : 7
310 | CRC : 784522712
311 | Reserved :
312 | HiddenVolSize : 0
313 | VolSize : 10223616
314 | DataStart : 131072
315 | DataSize : 10223616
316 | Flags : 0
317 | SectorSize : 512
318 | Reserved2 :
319 | CRC3 : 2972579980
320 | Keys : f300d5780830662f179908272817c220b72e9a1479da0177639837af75da9541931ff67e13d3b3c5def22fcc00b598b9775500d45bb4e47c777e5e65a3ec32c3000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000
321 | ```
322 |
323 | We can use this to work out where the normal header would have been located using the following formula before.
324 |
325 | ```
326 | backup_location - ((DataSize / 512) + 256) = header_location
327 | ```
328 | For our example this is 20496 - ((10223616 / 512) + 256) = 272. If we go to sector 272 we can see the issue, the header has been overwritten by a png. This explains why hunt wansn't able to recover it.
329 |
330 | ```
331 | Offset 0 1 2 3 4 5 6 7 8 9 A B C D E F
332 |
333 | 00022000 89 50 4E 47 0D 0A 1A 0A 00 00 00 0D 49 48 44 52 ‰PNG IHDR
334 | 00022010 00 00 01 72 00 00 01 80 08 06 00 00 00 B0 7E E9 r € °~é
335 | 00022020 1B 00 00 00 01 73 52 47 42 00 AE CE 1C E9 00 00 sRGB ®Î é
336 | 00022030 00 04 67 41 4D 41 00 00 B1 8F 0B FC 61 05 00 00 gAMA ± üa
337 | 00022040 00 09 70 48 59 73 00 00 1D 87 00 00 1D 87 01 8F pHYs ‡ ‡
338 | 00022050 E5 F1 65 00 00 2E B6 49 44 41 54 78 5E ED DD 2D åñe .¶IDATx^íÝ-
339 | 00022060 7B F2 3A 1C C7 F1 BD 8B 4A E4 E4 24 12 89 44 4E {ò: Çñ½‹Jää$ ‰DN
340 | 00022070 22 91 48 5E 02 12 39 89 44 22 91 48 24 12 59 89 "‘H^ 9‰D"‘H$ Y‰
341 | 00022080 AC AC FC 9F A4 4D FA 98 94 52 38 BB 09 FB 7E AE ¬¬üŸ¤Mú˜”R8» û~®
342 | 00022090 2B D7 B9 0F 5B 47 1F D2 5F D3 34 6D 3F C4 E1 B4 +×¹ [G Ò_Ó4m?Äá´
343 | 000220A0 FE 90 8F 8F 0F 99 ED AE E6 13 00 C0 BF 72 DD CD þ ™í®æ À¿rÝÍ
344 | 000220B0 B2 4C FE 58 9F CC 27 75 04 39 00 BC 38 82 1C 00 ²LþXŸÌ'u 9 ¼8‚
345 | 000220C0 02 47 90 03 40 E0 08 72 00 08 DC CD 20 B7 A1 DD G @à r ÜÍ ·¡Ý
346 | 000220D0 B7 B4 C2 FD BA 93 99 E3 F7 6C F1 1F 0C AE B2 9B ·´Âýº“™ã÷lñ ®²›
347 | 000220E0 B9 A7 C9 CA 6C A7 7E C3 AD 7B 9E D7 E2 5E 54 E5 ¹§ÉÊl§~Ã{ž×â^Tå
348 | 000220F0 B4 76 FC 7E 59 3C EB 48 09 68 5E 43 DA 1E 7F A1 ´vü~Y<ëH h^CÚ ¡
349 | 00022100 EE 0C 5E 46 EA CE 5F DD 97 8B D0 EE 5B D4 1F 20 î ^FêÎ_Ý—‹Ðî[Ô
350 | 00022110 C8 2B 25 E4 8D 5F 20 C8 DF 64 7B 50 77 FE EA BE È+%ä _ Èßd{Pwþê¾
351 | 00022120 3C 28 C8 CD B4 35 76 86 BB 2A 19 00 E0 77 D0 47 <(ÈÍ´5v†»* àwÐG
352 | 00022130 0E 00 81 23 C8 01 20 70 04 39 00 04 8E 20 07 80 #È p 9 Ž €
353 | 00022140 C0 0D 0A 72 00 40 38 08 72 00 08 1C 41 0E 00 81 À r @8 r A
354 | 00022150 23 C8 01 20 70 04 39 00 04 8E 20 07 80 C0 11 E4 #È p 9 Ž €À ä
355 | 00022160 00 10 38 82 1C 00 02 47 90 03 40 E0 08 72 00 08 8‚ G @à r
356 | 00022170 1C 41 0E 00 81 73 06 B9 BD AF 9F 67 AD 00 C0 0B A s ¹½¯Ÿg À
357 | 00022180 B0 2F A7 B8 E7 59 2B 04 39 00 BC 10 82 1C 00 02 °/§¸çY+ 9 ¼ ‚
358 | 00022190 47 90 03 40 E0 08 72 00 08 1C 41 0E 00 81 23 C8 G @à r A #È
359 | 000221A0 01 20 70 04 39 00 04 8E 20 07 80 C0 11 E4 00 10 p 9 Ž €À ä
360 | 000221B0 38 82 1C 00 02 47 90 03 40 E0 08 72 00 08 1C 41 8‚ G @à r A
361 | 000221C0 0E 00 81 23 C8 01 20 70 04 39 00 04 8E 20 07 80 #È p 9 Ž €
362 | 000221D0 C0 11 E4 00 10 38 82 1C 00 02 47 90 03 40 E0 08 À ä 8‚ G @à
363 | 000221E0 72 00 08 1C 41 0E 00 81 23 C8 01 20 70 04 39 00 r A #È p 9
364 | 000221F0 04 8E 20 07 80 C0 11 E4 00 10 B8 21 41 0E 00 08 Ž €À ä ¸!A
365 | ```
366 |
367 | Based on the information we have now we can map out where the TrueCrypt container would have been on the disk. Note this is just for explanatory purposes. If we compare this to the current mapping we can see that the images have overwritten most of the header but the data is thankfully the volume data is intact.
368 |
369 | Note that even if parts of the volume data have been overwritten we are still able to decrypt them. It just makes the recovery of data within the container more difficult.
370 |
371 | 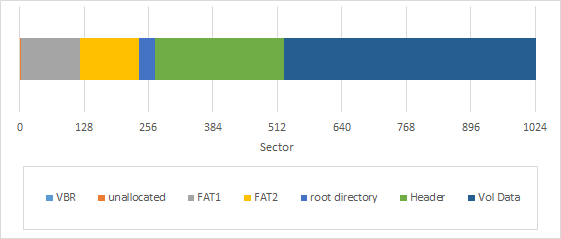
372 |
373 | Using dd we can extract the container, for this example the command is:
374 |
375 | ```
376 | dd if=example2.001 of=recovered.tc bs=512 skip=272 count=20480
377 | ```
378 |
379 | We can then open the container, however, we need to make sure to specify the backup header. If we do not we will get the following error:
380 |
381 | 
382 |
383 | Choosing to use the backup header in mount options will allow us to open the container.
384 |
385 | 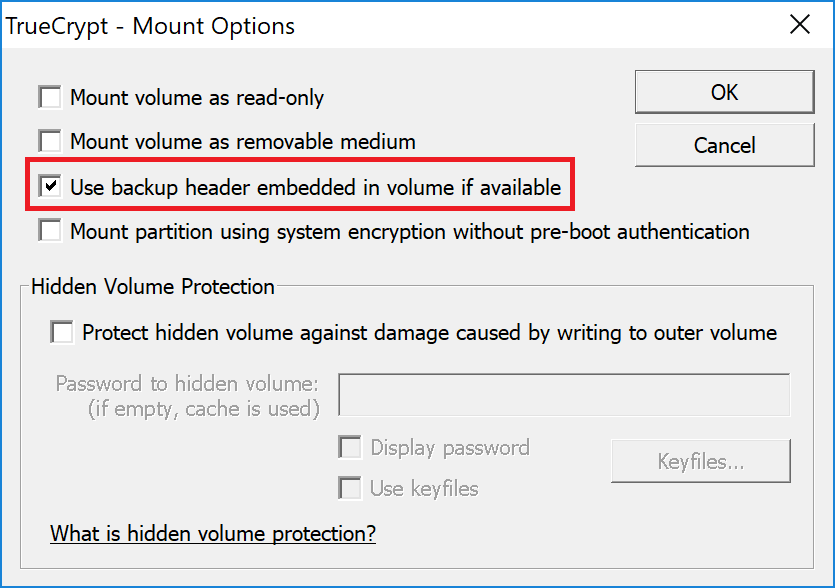
386 |
387 | One slightly interesting note is that if we add the .png extension to the recovered container most imaging tools will render it a normal image without any issues.
388 |
389 | 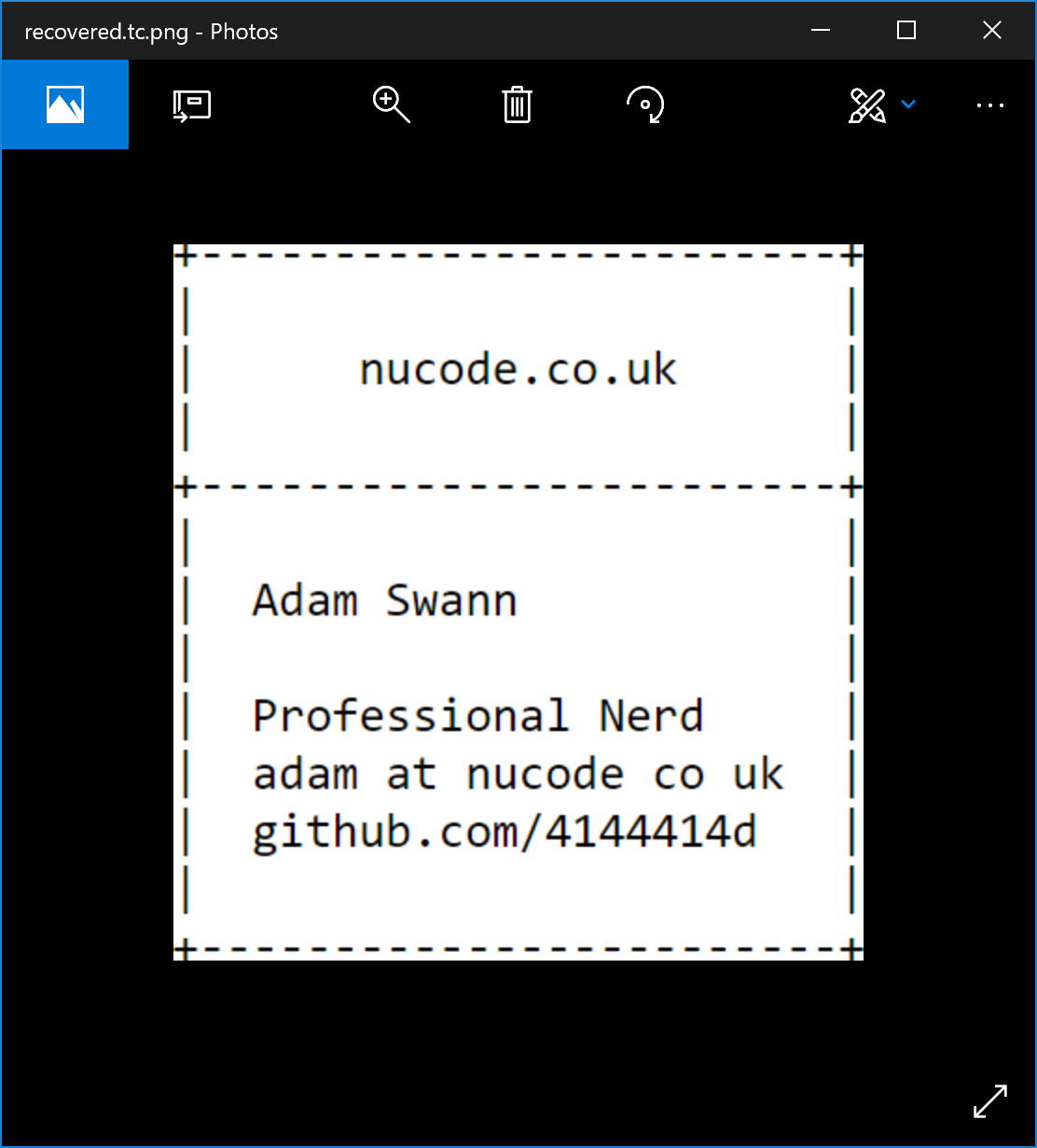
390 |
391 |
392 |
393 |
394 | Example #3 – an unallocated and fragmented container
395 | ====================================================
396 | TBA
397 |
398 |
399 | Example #4 – deleted container with hidden volume
400 | =================================================
401 | TBA
402 |
--------------------------------------------------------------------------------
/examples/hunt.py:
--------------------------------------------------------------------------------
1 | """
2 | hunt will search a file and attempt to decrypt each sector as if it we're a
3 | header. This has not been optimised and will run quite slowly particularly if
4 | the --all option is used. If you are scanning a lot of data and need better
5 | please contact me and I'll do my best to improve this. This is very CPU
6 | intensive and currently only uses a single core.
7 |
8 | This searches for the typical locations of normal containers. It can be modified
9 | to look for hidden containers. Please contact me if needed.
10 |
11 | GitHub: https://github.com/4144414D/pytruecrypt
12 | Email: adam@nucode.co.uk
13 |
14 | Usage:
15 | hunt ... (--chain=|--brute) [-a] [--ent=]
16 |
17 | Options:
18 | -h, --help Show this screen.
19 | -a, --all Search for all TrueCrypt options. Very slow.
20 | -b, --brute Test all sectors. Extremely slow.
21 | -c n, --chain n Search using chain of high entropy, n is number of sectors.
22 | -e log, --ent log Save the full calculated entropy to log file.
23 | """
24 |
25 | from pytruecrypt import *
26 | from util import *
27 | from docopt import docopt
28 | import tempfile
29 | import os
30 | import sys
31 | import time
32 | import math
33 | import pickle
34 | from bitarray import bitarray
35 | import numpy as np
36 |
37 | #jaradc - https://gist.github.com/jaradc/eeddf20932c0347928d0da5a09298147
38 | def entropy(data):
39 | """ Computes entropy of label distribution. """
40 | labels = list(data)
41 | n_labels = 512.0
42 |
43 | value,counts = np.unique(labels, return_counts=True)
44 | probs = counts / n_labels
45 |
46 | n_classes = np.count_nonzero(probs)
47 |
48 | ent = 0.
49 |
50 | # Compute entropy
51 | for i in probs:
52 | ent -= i * math.log(i, 2)
53 | return ent
54 |
55 | def test_sector(hash_options, crypto_options, passwords, data, sector_num):
56 | #create memory backed temp file
57 | t = tempfile.SpooledTemporaryFile(1024)
58 | t.write(data)
59 | for password in passwords:
60 | #loop for each hash option
61 | for hash in hash_options:
62 | #loop for each crypto option
63 | for crypto in crypto_options:
64 | tc = PyTruecrypt(encryption=crypto,hash_func=hash,fd=t)
65 | tc.open(password)
66 | if tc.valid or (entropy(tc.tchdr_plain) < 3):
67 | r = open('results.txt','a')
68 | if tc.valid:
69 | print 'Sector {}: Fully valid header found'.format(sector_num)
70 | r.write('Sector {}: Fully valid header found\n'.format(sector_num))
71 | else:
72 | print 'Sector {}: Low entropy decrypted sector, possible damaged header'.format(sector_num)
73 | r.write('Sector {}: Low entropy decrypted sector, possible damaged header\n'.format(sector_num))
74 | print "\tHash Option: {}".format(hash)
75 | r.write("\tHash Option: {}\n".format(hash))
76 | print "\tCrypto Option: {}".format(crypto)
77 | r.write("\tCrypto Option: {}\n".format(crypto))
78 | print "\tPassword: {}".format(password)
79 | r.write("\tPassword: {}\n".format(password))
80 | print ""
81 | r.write("\n")
82 | print "Decrypted Header:"
83 | r.write("Decrypted Header:\n")
84 | print hexdump(tc.tchdr_plain)
85 | r.write(hexdump(tc.tchdr_plain))
86 | print
87 | r.write('\n')
88 |
89 | s = open("PS{}.dd".format(sector_num),'wb')
90 | s.write(data)
91 | s.close
92 |
93 | def chain_search(source_entropy,target):
94 | target = int(target)
95 | chains = []
96 | cur_start = -1
97 | cur_len = -1
98 | tick = 0
99 | for x in range(len(source_entropy)):
100 | tick += 1
101 | if tick == 500:
102 | tick = 0
103 | percentage = (float(100) / len(source_entropy)) * x
104 | print "\rFinding chains... {}%".format(percentage),
105 | if source_entropy[x]:
106 | #contiune chain or start new chain
107 | if cur_len > -1:
108 | #contiune chain
109 | cur_len += 1
110 | else:
111 | #start new chain
112 | cur_start = x
113 | cur_len = 0
114 | else:
115 | #end chain or skip
116 | if cur_len > -1:
117 | #end chain
118 | cur_len += 1
119 | if cur_len >= target:
120 | #append current chain to list
121 | chains.append([cur_start,cur_len])
122 | #reset chaiin stats
123 | cur_start = -1
124 | cur_len = -1
125 | else:
126 | #skip one entropy sector
127 | pass
128 | print "\rFinding chains... 100% "
129 | return chains
130 |
131 | def search_range(start,end,f,hash_options,crypto_options,passwords):
132 | f.seek(start)
133 | for x in range(start,end,512):
134 | data = f.read(512)
135 | sector_num = x / 512
136 | print "Testing Sector: {}".format(sector_num)
137 | test_sector(hash_options, crypto_options, passwords, data, sector_num)
138 |
139 | def test_chains(chains,f,hash_options,crypto_options,passwords):
140 | search_size = 8
141 |
142 | for chain in chains:
143 | chain_sector = chain[0]
144 | chain_len = chain[1]
145 |
146 | #calc start location
147 | search_start = (chain_sector - search_size) * 512
148 | search_end = (chain_sector + search_size) * 512
149 | search_range(search_start, search_end, f,hash_options,crypto_options,passwords)
150 |
151 | #calc start location, searching for the typical location of a normal
152 | #backup header and not a hidden header. Changing the -256 will change
153 | #this or increasing the search size will aloow it to be found however
154 | #this will be slow
155 | search_start = (chain_sector + chain_len - 256 - search_size) * 512
156 | search_end = (chain_sector + chain_len - 256 + search_size) * 512
157 | search_range(search_start, search_end, f,hash_options,crypto_options,passwords)
158 |
159 | def save(obj, path):
160 | with open(path, 'wb') as f:
161 | pickle.dump(obj, f, pickle.HIGHEST_PROTOCOL)
162 |
163 | def load(path):
164 | with open(path, 'rb') as f:
165 | return pickle.load(f)
166 |
167 | def main(arguments):
168 | arguments = docopt(__doc__)
169 | if arguments['--all']:
170 | hash_options = ['ripemd','sha512','whirlpool']
171 | crypto_options = [["aes"],["aes","twofish"],["aes","twofish","serpent"],
172 | ["serpent"],["serpent","aes"],["serpent","twofish","aes"],["twofish"],
173 | ["twofish","serpent"]]
174 | else:
175 | hash_options = ['ripemd']
176 | crypto_options = [["aes"]]
177 |
178 | #open file and find total size
179 | f = open(arguments[''], 'rb')
180 | f.seek(0, os.SEEK_END)
181 | size = f.tell()
182 | f.seek(0)
183 |
184 | #print "Starting..."
185 | if arguments['--brute']:
186 | search_range(0,size,f,hash_options,crypto_options,arguments[''])
187 | else:
188 | if arguments['--ent']:
189 | entropy_log = open(arguments['--ent'],'w')
190 | pickle_file = arguments['']+'.entropy'
191 | if os.path.isfile(pickle_file):
192 | print "Loading source entropy from {}".format(pickle_file)
193 | source_entropy = load(pickle_file)
194 | else:
195 | source_entropy = bitarray()
196 | #run entropy calculations
197 | tick = 0
198 | for x in range(0,size,512):
199 | tick += 1
200 | if tick == 1000:
201 | tick = 0
202 | percentage = (float(100) / size) * x
203 | print "\rCalculating source entropy... {}%".format(percentage),
204 | data = f.read(512)
205 | sector_entropy = entropy(data)
206 | if sector_entropy > 7:
207 | source_entropy.append(True)
208 | else:
209 | source_entropy.append(False)
210 | if arguments['--ent']:
211 | entropy_log.write("{}\n".format(sector_entropy))
212 |
213 | if arguments['--ent']:
214 | entropy_log.close()
215 | print "\rCalculating source entropy... 100% "
216 | print "Saving {}... ".format(pickle_file),
217 | save(source_entropy, pickle_file)
218 | print "done"
219 |
220 | target = int(arguments['--chain'])
221 |
222 | chains = chain_search(source_entropy,target)
223 | if len(chains) > 0:
224 | test_chains(chains,f,hash_options,crypto_options,arguments[''])
225 | else:
226 | print "No chains found."
227 |
228 | if __name__ == '__main__':
229 | arguments = docopt(__doc__)
230 | main(arguments)
231 |
--------------------------------------------------------------------------------
/examples/image-gui.py:
--------------------------------------------------------------------------------
1 | from Tkinter import *
2 | import tkFileDialog
3 | import os
4 | #from ttk import Frame, Button, Style, Entry, Radiobutton
5 |
6 |
7 | class gui(Frame):
8 | def __init__(self, parent):
9 | Frame.__init__(self, parent)
10 | self.parent = parent
11 | self.createUI()
12 |
13 | def select_container(self):
14 | filename = tkFileDialog.askopenfilename()
15 | if os.path.isfile(filename):
16 | self.container_entry.delete(0,END)
17 | self.container_entry.insert(0,filename)
18 |
19 | def select_vol(self):
20 | filename = tkFileDialog.askopenfilename()
21 | if os.path.isfile(filename):
22 | self.Volatility_entry.delete(0,END)
23 | self.Volatility_entry.insert(0,filename)
24 |
25 | def select_image(self):
26 | filename = tkFileDialog.asksaveasfilename(defaultextension='.dd',filetypes=[('Raw Image', '.dd')])
27 | self.image_entry.delete(0,END)
28 | self.image_entry.insert(0,filename)
29 |
30 | def image(self):
31 | #import image
32 | #run image with options
33 | pass
34 |
35 | def update_options(self):
36 | if self.mode.get() == "key":
37 | #enable key options and disable others
38 | self.password_entry.config(state='disable')
39 | if 'aes' in self.encryption_mode.get():
40 | self.aes_entry.config(state='normal')
41 | else:
42 | self.aes_entry.config(state='disable')
43 | if 'twofish' in self.encryption_mode.get():
44 | self.Twofish_entry.config(state='normal')
45 | else:
46 | self.Twofish_entry.config(state='disable')
47 | if 'serpent' in self.encryption_mode.get():
48 | self.Serpent_entry.config(state='normal')
49 | else:
50 | self.Serpent_entry.config(state='disable')
51 | self.Volatility_entry.config(state='disable')
52 | self.Volatility_button.config(state='disable')
53 | self.hash_mode_ripemd.config(state='disable')
54 | self.hash_mode_sha.config(state='disable')
55 | self.hash_mode_whirlpool.config(state='disable')
56 | self.vera_checkbox.config(state='disable')
57 | self.backup_checkbox.config(state='disable')
58 | self.hidden_checkbox.config(state='disable')
59 | self.force_checkbox.config(state='disable')
60 | self.offset_entry.config(state='normal')
61 | self.datasize_entry.config(state='normal')
62 | elif self.mode.get() == "pwd":
63 | #enable pwd options and disable others
64 | self.password_entry.config(state='normal')
65 | self.aes_entry.config(state='disable')
66 | self.Twofish_entry.config(state='disable')
67 | self.Serpent_entry.config(state='disable')
68 | self.Volatility_entry.config(state='disable')
69 | self.Volatility_button.config(state='disable')
70 | self.hash_mode_ripemd.config(state='normal')
71 | self.hash_mode_sha.config(state='normal')
72 | self.hash_mode_whirlpool.config(state='normal')
73 | self.vera_checkbox.config(state='normal')
74 | self.backup_checkbox.config(state='normal')
75 | self.hidden_checkbox.config(state='normal')
76 | self.force_checkbox.config(state='normal')
77 | if self.force.get() == 1:
78 | self.offset_entry.config(state='normal')
79 | self.datasize_entry.config(state='normal')
80 | else:
81 | self.offset_entry.config(state='disable')
82 | self.datasize_entry.config(state='disable')
83 | else:
84 | #enable vol options and disable others
85 | self.password_entry.config(state='disable')
86 | self.aes_entry.config(state='disable')
87 | self.Twofish_entry.config(state='disable')
88 | self.Serpent_entry.config(state='disable')
89 | self.Volatility_entry.config(state='normal')
90 | self.Volatility_button.config(state='normal')
91 | self.hash_mode_ripemd.config(state='disable')
92 | self.hash_mode_sha.config(state='disable')
93 | self.hash_mode_whirlpool.config(state='disable')
94 | self.vera_checkbox.config(state='disable')
95 | self.backup_checkbox.config(state='disable')
96 | self.hidden_checkbox.config(state='disable')
97 | self.force_checkbox.config(state='disable')
98 | self.offset_entry.config(state='normal')
99 | self.datasize_entry.config(state='normal')
100 |
101 | def createUI(self):
102 | self.parent.title("pytruecrypt image")
103 |
104 | self.pack(fill=BOTH, expand=1)
105 |
106 | #create mode widgets
107 | self.mode_label = Label(self, text="Usage Mode:")
108 | self.mode_label.place(x=15, y=7)
109 | self.mode = StringVar()
110 | self.mode_password = Radiobutton(self, text="Password", variable=self.mode, value="pwd", command=self.update_options)
111 | self.mode_password.place(x=100, y=5)
112 | self.mode_key = Radiobutton(self, text="Key", variable=self.mode, value="key", command=self.update_options)
113 | self.mode_key.place(x=180, y=5)
114 | self.mode_volatility = Radiobutton(self, text="Volatility Key", variable=self.mode, value="vol", command=self.update_options)
115 | self.mode_volatility.place(x=226, y=5)
116 | self.mode.set("pwd")
117 |
118 | #create container entry
119 | self.container_label = Label(self, text="Container:")
120 | self.container_label.place(x=15, y=35)
121 | self.container_entry = Entry(self)
122 | self.container_entry.config(width=41)
123 | self.container_entry.place(x=100, y=35)
124 | self.container_button= Button(self, text="...", height=1, width=1,command=self.select_container)
125 | self.container_button.place(x=353, y=35)
126 |
127 | #create password entry
128 | self.password_label = Label(self, text="Password:")
129 | self.password_label.place(x=15, y=65)
130 | self.password_entry = Entry(self)
131 | self.password_entry.config(width=45)
132 | self.password_entry.place(x=100, y=65)
133 |
134 | #create AES key entry
135 | self.aes_label = Label(self, text="AES Key:")
136 | self.aes_label.place(x=15, y=95)
137 | self.aes_entry = Entry(self)
138 | self.aes_entry.config(width=45)
139 | self.aes_entry.place(x=100, y=95)
140 |
141 | #create Twofish key entry
142 | self.Twofish_label = Label(self, text="Twofish Key:")
143 | self.Twofish_label.place(x=15, y=125)
144 | self.Twofish_entry = Entry(self)
145 | self.Twofish_entry.config(width=45)
146 | self.Twofish_entry.place(x=100, y=125)
147 |
148 | #create Serpent key entry
149 | self.Serpent_label = Label(self, text="Serpent Key:")
150 | self.Serpent_label.place(x=15, y=155)
151 | self.Serpent_entry = Entry(self)
152 | self.Serpent_entry.config(width=45)
153 | self.Serpent_entry.place(x=100, y=155)
154 |
155 | #create Volatility key entry
156 | self.Volatility_label = Label(self, text="Volatility Key:")
157 | self.Volatility_label.place(x=15, y=185)
158 | self.Volatility_entry = Entry(self)
159 | self.Volatility_entry.config(width=41)
160 | self.Volatility_entry.place(x=100, y=185)
161 | self.Volatility_button= Button(self, text="...", height=1, width=1,command=self.select_vol)
162 | self.Volatility_button.place(x=353, y=185)
163 |
164 | #create encryption mode options
165 | self.encryption_mode_label = Label(self, text="Encryption Mode:")
166 | self.encryption_mode_label.place(x=15, y=215)
167 | self.encryption_mode = StringVar()
168 | #create radio buttons
169 | self.encryption_mode_aes = Radiobutton(self, text="AES", variable=self.encryption_mode, value="aes", command=self.update_options)
170 | self.encryption_mode_aes_twofish = Radiobutton(self, text="AES-Twofish", variable=self.encryption_mode, value="aes-twofish", command=self.update_options)
171 | self.encryption_mode_aes_twofish_serpent = Radiobutton(self, text="AES-Twofish-Serpent", variable=self.encryption_mode, value="aes-twofish-serpent", command=self.update_options)
172 | self.encryption_mode_serpent = Radiobutton(self, text="Serpent", variable=self.encryption_mode, value="serpent", command=self.update_options)
173 | self.encryption_mode_serpent_aes = Radiobutton(self, text="Serpent-AES", variable=self.encryption_mode, value="serpent-aes", command=self.update_options)
174 | self.encryption_mode_serpent_twofish_aes = Radiobutton(self, text="Serpent-Twofish-AES", variable=self.encryption_mode, value="serpent-twofish-aes", command=self.update_options)
175 | self.encryption_mode_twofish = Radiobutton(self, text="Twofish", variable=self.encryption_mode, value="twofish", command=self.update_options)
176 | self.encryption_mode_twofish_serpent = Radiobutton(self, text="Twofish-Serpent", variable=self.encryption_mode, value="twofish-serpent", command=self.update_options)
177 | self.encryption_mode.set("aes")
178 | #place radio buttons
179 | self.encryption_mode_aes.place(x=15, y=235)
180 | self.encryption_mode_serpent.place(x=15, y=255)
181 | self.encryption_mode_twofish.place(x=15, y=275)
182 | self.encryption_mode_aes_twofish.place(x=90, y=235)
183 | self.encryption_mode_serpent_aes.place(x=90, y=255)
184 | self.encryption_mode_twofish_serpent.place(x=90, y=275)
185 | self.encryption_mode_serpent_twofish_aes.place(x=205, y=235)
186 | self.encryption_mode_aes_twofish_serpent.place(x=205, y=255)
187 |
188 | #create hash mode options
189 | self.hash_mode_label = Label(self, text="Hash Function:")
190 | self.hash_mode_label.place(x=15, y=300)
191 | self.hash_mode = StringVar()
192 | #radio buttons
193 | self.hash_mode_ripemd = Radiobutton(self, text="RIPEMD", variable=self.hash_mode, value="ripemd", command=self.update_options)
194 | self.hash_mode_sha = Radiobutton(self, text="SHA-512", variable=self.hash_mode, value="sha-512", command=self.update_options)
195 | self.hash_mode_whirlpool = Radiobutton(self, text="Whirlpool", variable=self.hash_mode, value="whirlpool", command=self.update_options)
196 | self.hash_mode.set("ripemd")
197 | #place radio buttons
198 | self.hash_mode_ripemd.place(x=15, y=320)
199 | self.hash_mode_sha.place(x=90, y=320)
200 | self.hash_mode_whirlpool.place(x=164, y=320)
201 |
202 | #option checkboxes
203 | self.option_label = Label(self, text="Password options:")
204 | self.option_label.place(x=15, y=345)
205 | #veracrypt
206 | self.vera = IntVar()
207 | self.vera_checkbox = Checkbutton(self, text="VeraCrypt", variable=self.vera, command=self.update_options)
208 | self.vera_checkbox.place(x=15, y=365)
209 | #backup header
210 | self.backup = IntVar()
211 | self.backup_checkbox = Checkbutton(self, text="Backup Header", variable=self.backup, command=self.update_options)
212 | self.backup_checkbox.place(x=95, y=365)
213 | #hidden header
214 | self.hidden = IntVar()
215 | self.hidden_checkbox = Checkbutton(self, text="Hidden Header", variable=self.hidden, command=self.update_options)
216 | self.hidden_checkbox.place(x=200, y=365)
217 | #force
218 | self.force = IntVar()
219 | self.force_checkbox = Checkbutton(self, text="Force Decryption (requires offset and data size)", variable=self.force, command=self.update_options)
220 | self.force_checkbox.place(x=15, y=390)
221 |
222 | #offset options
223 | self.option_label = Label(self, text="Manual Offsets:")
224 | self.option_label.place(x=15, y=415)
225 | #start offset
226 | self.offset_label = Label(self, text="Offset:")
227 | self.offset_label.place(x=15, y=440)
228 | self.offset_entry = Entry(self)
229 | self.offset_entry.config(width=45)
230 | self.offset_entry.place(x=100, y=440)
231 | #data size
232 | self.offset_label = Label(self, text="Data Size:")
233 | self.offset_label.place(x=15, y=470)
234 | self.datasize_entry = Entry(self)
235 | self.datasize_entry.config(width=45)
236 | self.datasize_entry.place(x=100, y=470)
237 |
238 | #offset options
239 | self.option_label = Label(self, text="Output:")
240 | self.option_label.place(x=15, y=500)
241 | self.image_label = Label(self, text="Image Path:")
242 | self.image_label.place(x=15, y=520)
243 | self.image_entry = Entry(self)
244 | self.image_entry.config(width=41)
245 | self.image_entry.place(x=100, y=520)
246 | self.image_button= Button(self, text="...", height=1, width=1,command=self.select_image)
247 | self.image_button.place(x=353, y=520)
248 |
249 | #create start button
250 | self.go_button= Button(self, text="Decrypt!", command=self.image)
251 | self.go_button.place(x=15, y=550)
252 |
253 | #update the display
254 | self.update_options()
255 |
256 |
257 |
258 | def main():
259 | root = Tk()
260 | root.geometry("400x600")
261 | app = gui(root)
262 | root.resizable(width=False, height=False)
263 | root.mainloop()
264 |
265 |
266 | if __name__ == '__main__':
267 | main()
--------------------------------------------------------------------------------
/examples/image.py:
--------------------------------------------------------------------------------
1 | """
2 | pytruecrypt image is used to image a truecrypt container for further analysis.
3 |
4 | The container can be open with a password or with keys extracted from memory.
5 |
6 | Encryption modes can be assigned long or short hand where:
7 | aes = a
8 | twofish = t
9 | serpent = s
10 |
11 | For example 'aes-twofish' can be shortened to 'at' and aes-twofish-serpent
12 | to ats.
13 |
14 | Similarly hash functions can be assigned long or short hand where:
15 | ripemd = r
16 | sha-512 = s
17 | whirlpool = w
18 |
19 | Example useage:
20 |
21 | Scenario 1:
22 | You wish to image a TrueCrypt file "input1.tc" to an image named "output1.dd",
23 | it uses aes and ripemd. The password is "Scenario1". As ripemd is the default
24 | for TrueCrypt it does not need to be specified.
25 |
26 | > image pwd input1.tc output1.dd aes Scenario1
27 |
28 | Scenario 2:
29 | You wish to image a TrueCrypt file "input2.tc" to an image named "output2.dd",
30 | it uses aes-serpent and sha512. The password is "Scenario2". You wish to save
31 | time and use the short hand commands.
32 |
33 | > image pwd input2.tc output2.dd as Scenario2 s
34 |
35 | Scenario 3:
36 | You wish to image a TrueCrypt file "input3.tc" to an image named "output3.dd",
37 | it uses aes-serpent. You know it contains a hidden volume and the password is
38 | "Scenario3".
39 |
40 | > image pwd input3.tc output3.dd aes-serpent Scenario3 --hidden
41 |
42 | Scenario 4:
43 | You wish to image a TrueCrypt file "input4.tc" to an image named "output4.dd",
44 | it uses aes. You do not know the password but have extracted AES keys from
45 | memory.
46 |
47 | > image key input4.tc output4.dd aes --aes bac01155a46547f00c3ddf9a4a765159fbe
48 | 1f68d94bf11a3bd6910eedf26d867a63263c949812cd68b7dad91a8dfdacb96942b93cc1b21ffa
49 | feeb4791a0befa4
50 |
51 | GitHub: https://github.com/4144414D/pytruecrypt
52 |
53 | Usage:
54 | image pwd [] [-vbh] [(-f -oBYTES -dBYTES)]
55 | image key [-aKEY -tKEY -sKEY] [(-oBYTES -dBYTES)]
56 | image --help
57 |
58 | Options:
59 | --help Show this screen
60 | -a key, --aes key AES Key
61 | -t key, --twofish key TwoFish Key
62 | -s key, --serpent key Serpent Key
63 | -f, --force Continue even if magic number and CRC fail
64 | -o BYTES, --offset BYTES Offset in bytes to start of data area
65 | -d BYTES, --datasize BYTES Size of data area to image
66 | -v, --vera Treat container as Veracrypt
67 | -b, --backup Use backup header
68 | -h, --hidden Use hidden volume
69 | """
70 |
71 | from pytruecrypt import *
72 | from docopt import docopt
73 | import os
74 | import binascii
75 | import time
76 | from util import * #delete after testing
77 |
78 | def checkkey(mode, key,name):
79 | if key != None:
80 | #check if key is required but not supplied
81 | if (name not in mode):
82 | print "ERROR " + name + " key is not required for the selected encryption mode"
83 | #check key is correct length
84 | elif (len(key) == 128):
85 | try:
86 | #try to convert hex to bin
87 | return binascii.unhexlify(key) #good outcome
88 | except TypeError:
89 | print "ERROR " + name + " key invalid and contains non hex characters [0-f]"
90 | #if key is incorrect length give an error
91 | elif (len(key) != 128):
92 | print "ERROR " + name + " key is not the correct length"
93 | else:
94 | #check if key is required but not supplied
95 | if (name in mode):
96 | print "ERROR " + name + " key is required for the selected encryption mode but not supplied"
97 | return False #everything else is a fail
98 |
99 | def percentage(part, whole):
100 | return 100 * float(part)/float(whole)
101 |
102 | def create_log(arguments):
103 | log = open(arguments[''] + '.log','a')
104 | log.write("pytruecrypt - image.py - https://github.com/4144414D/pytruecrypt")
105 | log.write('\n' + '-'*80)
106 | log.write('\nCompleted at: ' + time.strftime("%d/%b/%Y %H:%M:%S"))
107 | log.write('\n\nArguments')
108 | log.write('\nContainer opened with a ' + ('password' if not arguments['key'] else 'key'))
109 | log.write('\nContainer path: ' + arguments[''])
110 | log.write('\nImage path: ' + arguments[''])
111 | log.write('\nEncryption mode: ' + '-'.join(map(str, arguments[''])))
112 | if arguments[''] != 'default':
113 | hash = arguments['']
114 | else:
115 | if arguments['--vera']:
116 | hash = 'sha512'
117 | else:
118 | hash = 'ripemd'
119 | log.write('\nHash Function: ' + hash)
120 | if arguments['key']:
121 | if arguments['--aes']:
122 | log.write('\nAES Key: ' + arguments['--aes'])
123 | if arguments['--serpent']:
124 | log.write('\nSerpent Key: ' + arguments['--serpent'])
125 | if arguments['--twofish']:
126 | log.write('\nTwofish Key: ' + arguments['--twofish'])
127 | else:
128 | log.write('\nPassword: ' + arguments[''])
129 |
130 | log.write('\nForce option: ' + ('Used' if arguments['--force'] else 'Not Used'))
131 | log.write('\nOffset: ' + (str(arguments['--offset']) if arguments['--offset'] else 'Not Used'))
132 | log.write('\nData Size: ' + (str(arguments['--datasize']) if arguments['--datasize'] else 'Not Used'))
133 | log.write('\nHidden Container option: ' + ('Used' if arguments['--hidden'] else 'Not Used'))
134 | log.write('\nBackup Header option: ' + ('Used' if arguments['--backup'] else 'Not Used'))
135 | log.write('\nVeraCrypt option: ' + ('Used' if arguments['--backup'] else 'Not Used'))
136 | log.write('\n' + '-'*80)
137 | log.write('\n\n')
138 |
139 | def create_image(image, tc, DataStart, DataSize,startsec=0):
140 | print '\r',
141 | tick = 0
142 | image_file = open(image,'wb')
143 | for sector in range(0,DataSize/512):
144 | #check timer to see if display needs updating
145 | tock = '%.2f' % time.time()
146 | if tick != tock:
147 | tick = tock
148 | completed = (percentage(sector, DataSize/512))
149 | bars = '=' * (int(completed) / 3)
150 | bar = '[' + bars + ' ' * (33 - len(bars)) + ']'
151 | completed = '%.3f' % completed
152 | print bar + ' ' + str(completed) + '%\r',
153 | image_file.write(tc.getPlainSector(sector,startsec))
154 | print '[' + '=' * 33 + '] 100% '
155 |
156 | if __name__ == '__main__':
157 | arguments = docopt(__doc__)
158 | #check hash function
159 | if not arguments['']:
160 | arguments[''] = 'default'
161 | elif arguments[''] in ['s', 'r', 'w']:
162 | #viable short hand mode chosen, convert to long hand
163 | arguments[''] = arguments[''].replace('w','1').replace('r','2').replace('s','3')
164 | arguments[''] = arguments[''].replace('1','whirlpool').replace('2','ripemd').replace('3','sha512')
165 | elif arguments[''] not in ['sha512','ripemd','whirlpool']:
166 | print "ERROR Please choose a viable hash function: sha512, ripemd, or whirlpool."
167 | exit(1)
168 |
169 | #check crypto options
170 | if arguments[''] in ["a","at","ats","s","sa","sta","t","ts"]:
171 | #viable short hand mode chosen, convert to long hand
172 | arguments[''] = arguments[''].replace('a','1').replace('t','2').replace('s','3')
173 | arguments[''] = arguments[''].replace('1','aes-').replace('2','twofish-').replace('3','serpent-')[:-1]
174 | elif arguments[''] not in ["aes","aes-twofish","aes-twofish-serpent","serpent","serpent-aes","serpent-twofish-aes","twofish","twofish-serpent"]:
175 | print "ERROR Please choose a viable crypto mode:"
176 | for line in ["aes","aes-twofish","aes-twofish-serpent","serpent","serpent-aes","serpent-twofish-aes","twofish","twofish-serpent"]:
177 | print "\t"+line
178 | exit(1)
179 | #split long hand into list
180 | arguments[''] = arguments[''].split('-')
181 |
182 | #check keys are viable if required
183 | key_count = 0
184 | aes_key = None
185 | twofish_key = None
186 | serpent_key = None
187 | if arguments['key']:
188 | aes_key = checkkey(arguments[''],arguments['--aes'],'aes')
189 | twofish_key = checkkey(arguments[''],arguments['--twofish'],'twofish')
190 | serpent_key = checkkey(arguments[''],arguments['--serpent'],'serpent')
191 | if not (aes_key or twofish_key or serpent_key): exit(1)
192 |
193 | #check tc file exists
194 | if not os.path.isfile(arguments['']):
195 | print "ERROR",
196 | print arguments[''],
197 | print "does not exist"
198 | exit(1)
199 |
200 | #check that image file does not already exist
201 | if os.path.isfile(arguments['']):
202 | print "ERROR",
203 | print arguments[''],
204 | print "already exists"
205 | exit(1)
206 |
207 | #use PyTruecrypt to open container
208 | tc = PyTruecrypt(arguments[''], arguments['--vera'], encryption=arguments[''],hash_func=arguments[''])
209 |
210 | if arguments['pwd']:
211 | vaild = tc.open(arguments[''], arguments['--hidden'], True, arguments['--backup'])
212 | if vaild or arguments['--force']:
213 | if not vaild:
214 | tc.vaild = True #force pytruecrypt to decrypt
215 | tc.decodeHeader()
216 | DataStart = int(arguments['--offset'])
217 | DataSize = int(arguments['--datasize'])
218 | offset = int(arguments['--offset']) / 512
219 | else:
220 | header = tc.getHeader()
221 | DataStart = int(header['DataStart'])
222 | DataSize = int(header['DataSize'])
223 | offset = 0
224 | create_image(arguments[''],tc, DataStart, DataSize, offset)
225 | create_log(arguments)
226 | else:
227 | print "ERROR incorrect password"
228 | else:
229 | tc.open_with_key(aes_key,twofish_key,serpent_key)
230 | #if sizes not given calculate sizes for a standard vol
231 | if not arguments['--offset']:
232 | arguments['--offset'] = 131072
233 | if not arguments['--datasize']:
234 | arguments['--datasize'] = tc.size - (131072*2)
235 | create_image(arguments[''],tc, int(arguments['--offset']), int(arguments['--datasize']), int(arguments['--offset']) / 512)
236 | create_log(arguments)
--------------------------------------------------------------------------------
/examples/keysearch.py:
--------------------------------------------------------------------------------
1 | """
2 | keyseaerch helps locate data by attempting to decrypt sectors with supplied
3 | keys and seeing how random the resutls are.
4 |
5 | Encryption modes can be assigned long or short hand where:
6 | aes = a
7 | twofish = t
8 | serpent = s
9 |
10 | For example 'aes-twofish' can be shortened to 'at' and aes-twofish-serpent
11 | to ats.
12 |
13 | GitHub: https://github.com/4144414D/pytruecrypt
14 |
15 | Usage:
16 | image [-mMODE -aKEY -tKEY -sKEY -oNUM]
17 | image --help
18 |
19 | Options:
20 | --help Show this screen
21 | -a key, --aes key AES Key
22 | -t key, --twofish key Twofish Key
23 | -s key, --serpent key Serpent Key
24 | -o num, --offset num Decrypt as offset number num [default: 256]
25 | -m MODE, --mode mode Encryption mode to use [default: aes]
26 | """
27 |
28 | from pytruecrypt import *
29 | from docopt import docopt
30 | import os
31 | import binascii
32 | import time
33 | from util import *
34 | import numpy as np
35 | import math
36 |
37 | def checkkey(mode,key,name):
38 | if key != None:
39 | #check if key is required but not supplied
40 | if (name not in mode):
41 | print "ERROR " + name + " key is not required for the selected encryption mode"
42 | #check key is correct length
43 | elif (len(key) == 128):
44 | try:
45 | #try to convert hex to bin
46 | return binascii.unhexlify(key) #good outcome
47 | except TypeError:
48 | print "ERROR " + name + " key invalid and contains non hex characters [0-f]"
49 | #if key is incorrect length give an error
50 | elif (len(key) != 128):
51 | print "ERROR " + name + " key is not the correct length"
52 | else:
53 | #check if key is required but not supplied
54 | if (name in mode):
55 | print "ERROR " + name + " key is required for the selected encryption mode but not supplied"
56 | return False #everything else is a fail
57 |
58 |
59 | #jaradc - https://gist.github.com/jaradc/eeddf20932c0347928d0da5a09298147
60 | def entropy(data):
61 | """ Computes entropy of label distribution. """
62 | labels = list(data)
63 | n_labels = 512.0
64 |
65 | value,counts = np.unique(labels, return_counts=True)
66 | probs = counts / n_labels
67 |
68 | n_classes = np.count_nonzero(probs)
69 |
70 | ent = 0.
71 |
72 | # Compute entropy
73 | for i in probs:
74 | ent -= i * math.log(i, 2)
75 | return ent
76 |
77 | if __name__ == '__main__':
78 | arguments = docopt(__doc__)
79 |
80 | #check crypto options
81 | if arguments['--mode'] in ["a","at","ats","s","sa","sta","t","ts"]:
82 | #viable short hand mode chosen, convert to long hand, this is dumb
83 | arguments['--mode'] = arguments['--mode'].replace('a','1').replace('t','2').replace('s','3')
84 | arguments['--mode'] = arguments['--mode'].replace('1','aes-').replace('2','twofish-').replace('3','serpent-')[:-1]
85 | elif arguments['--mode'] not in ["aes","aes-twofish","aes-twofish-serpent","serpent","serpent-aes","serpent-twofish-aes","twofish","twofish-serpent"]:
86 | print "ERROR Please choose a viable crypto mode:"
87 | for line in ["aes","aes-twofish","aes-twofish-serpent","serpent","serpent-aes","serpent-twofish-aes","twofish","twofish-serpent"]:
88 | print "\t"+line
89 | exit(1)
90 |
91 | #split long hand into list
92 | arguments['--mode'] = arguments['--mode'].split('-')
93 |
94 | #check keys are viable if required
95 | key_count = 0
96 | aes_key = None
97 | twofish_key = None
98 | serpent_key = None
99 | aes_key = checkkey(arguments['--mode'],arguments['--aes'],'aes')
100 | twofish_key = checkkey(arguments['--mode'],arguments['--twofish'],'twofish')
101 | serpent_key = checkkey(arguments['--mode'],arguments['--serpent'],'serpent')
102 | if not (aes_key or twofish_key or serpent_key): exit(1)
103 |
104 | #check source file exists
105 | if not os.path.isfile(arguments['']):
106 | print "ERROR",
107 | print arguments[''],
108 | print "does not exist"
109 | exit(1)
110 |
111 | #use PyTruecrypt to open source
112 | tc = PyTruecrypt(arguments[''], encryption=arguments['--mode'])
113 |
114 | #open source with keys
115 | tc.open_with_key(aes_key,twofish_key,serpent_key)
116 |
117 | offset = int(arguments['--offset'])
118 | tick = 0
119 |
120 | for x in range(0,tc.size,512):
121 | tc.fd.seek(x)
122 | cipher = tc.fd.read(512)
123 | sector = x/512
124 | plain = tc._decrypt_sector(offset,cipher)
125 | ent = entropy(plain)
126 | if ent < 7:
127 | print
128 | print "Possible result at sector: {}".format(str(sector))
129 | print hexdump(plain)
130 | pause = raw_input("Press enter to contiune...")
131 | tick += 1
132 | if tick == 128:
133 | tick = 0
134 | percentage = (float(100) / tc.size) * x
135 | print "\rSearching... {}%".format(percentage),
136 | print "\rSearching... 100% "
137 |
--------------------------------------------------------------------------------
/examples/mount.py:
--------------------------------------------------------------------------------
1 | # Truecrypt parsing library for Python by Gareth Owen
2 | # https://github.com/drgowen/pytruecrypt/
3 | # See LICENCE for licence details
4 |
5 | # PyTruecrypt is free software: you can redistribute it and/or modify
6 | # it under the terms of the GNU General Public License as published by
7 | # the Free Software Foundation, either version 3 of the License, or
8 | # (at your option) any later version.
9 |
10 | # PyTruecrypt is distributed in the hope that it will be useful,
11 | # but WITHOUT ANY WARRANTY; without even the implied warranty of
12 | # MERCHANTABILITY or FITNESS FOR A PARTICULAR PURPOSE. See the
13 | # GNU General Public License for more details.
14 |
15 | # You should have received a copy of the GNU General Public License
16 | # along with PyTruecrypt. If not, see .
17 |
18 | # Truecrypt volume mounter for Linux
19 |
20 | import sys
21 |
22 | sys.path.append("..")
23 |
24 |
25 | from pytruecrypt import *
26 | import binascii
27 | import os
28 | from subprocess import *
29 | import stat
30 | import getpass
31 | import getopt
32 |
33 | hidden = False
34 | unmount = False
35 |
36 | args = getopt.getopt(sys.argv[1:], "h")
37 |
38 | # parse cmdline options
39 | for k in args[0]:
40 | if k[0]=='-h':
41 | hidden = True
42 | # if k[0]=='-u':
43 | # unmount = True
44 |
45 | if len(args[1]) != 2:
46 | print "Usage: python mount.py [-h] volumepath dmname"
47 | print "Mount truecrypt volume"
48 | print
49 | print " volumepath\tTruecrypt volume file/device"
50 | print " dmname\tDevice mapper name (/dev/mapper/dmname) to map to (e.g. tcrypt)"
51 | print " -h\t\tmount hidden volume"
52 | print
53 | sys.exit(1)
54 |
55 | FILENAME = args[1][0]
56 | PASSWORD = getpass.getpass("Enter password: ")
57 | DMNAME = args[1][1]
58 |
59 | #if unmount:
60 | #todo
61 | # remove loopback
62 | # os.system("losetup -d `sudo losetup -a | grep '%s' | cut -d ':' -f 1`" % (FILENAME))
63 |
64 | #initialise pytruecrypt
65 | tc = PyTruecrypt(FILENAME)
66 |
67 | #open volume (returns false on failure)
68 | if not tc.open(PASSWORD, hidden=hidden):
69 | print "Failed to open volume -maybe incorrect pw"
70 | sys.exit(1)
71 |
72 | #if root - mount it
73 | if os.getuid() == 0:
74 | devName = FILENAME
75 |
76 | # if not block device - use loopback
77 | if not stat.S_ISBLK(os.stat(devName).st_mode):
78 | #find a free loopback device
79 | child = Popen("losetup -f", shell=True, stdout=PIPE)
80 | output, errors = child.communicate();
81 | devName = output.strip()
82 |
83 | #setup loopback
84 | os.system("losetup %s %s" % (devName, FILENAME))
85 |
86 | #setup linux device mapper so can mount volume
87 | dmtable = tc.getDeviceMapperTable(devName)
88 |
89 | #create dm target /dev/mapper/tcrypt
90 | # print "Device mapper table"
91 | # print dmtable
92 |
93 | os.system('echo %s | dmsetup create %s' % (dmtable, DMNAME))
94 |
95 | print "Tcryptdevice on /dev/mapper/"+DMNAME+" - you may now mount it"
96 | #You may now have to mount this manually if your linux doesn't automatically)
97 | # mount /dev/mapper/tcrypt wheretomount
98 |
99 | #to undo
100 | #unmount
101 | #dmsetup remove dmname
102 | #losetup -d /dev/loop0
103 | else:
104 | print "Must be root to mount"
105 |
106 |
--------------------------------------------------------------------------------
/examples/pw-check.py:
--------------------------------------------------------------------------------
1 | """
2 | pw-check will test all passwords given against a file to determine if it would
3 | successfully decode a TrueCrypt/VeraCrypt volume. This also allows you to
4 | see if the standard and backup headers match.
5 |
6 | GitHub: https://github.com/4144414D/pytruecrypt
7 |
8 | Usage:
9 | pw-check ... [-dv]
10 |
11 | Options:
12 | -h, --help Show this screen.
13 | -d, --decode Decode header if successful.
14 | -v, --veracrypt Also check for VeraCrypt.
15 | """
16 |
17 | from pytruecrypt import *
18 | from docopt import docopt
19 | import binascii
20 |
21 | if __name__ == '__main__':
22 | arguments = docopt(__doc__)
23 | for password in arguments['']:
24 | veraoptions = ([False] if not arguments['--veracrypt'] else [False,True])
25 | for vera in veraoptions:
26 | for hidden in [False,True]:
27 | for backup in [False,True]:
28 | for hash in ['ripemd','sha512','whirlpool']:
29 | for crypto in [["aes"],["aes","twofish"],["aes","twofish","serpent"],["serpent"],["serpent","aes"],["serpent","twofish","aes"],["twofish"],["twofish","serpent"]]:
30 | tc = PyTruecrypt(arguments[''], vera, encryption=crypto,hash_func=hash)
31 | if tc.open(password,hidden=hidden,backup=backup):
32 | print password,
33 | print 'appears to be valid for a',
34 | print ('TrueCrypt' if not vera else 'VeraCrypt'),
35 | print ('standard' if not hidden else 'hidden'),
36 | print 'volume using the',
37 | print ('normal' if not backup else 'backup'),
38 | print 'header',
39 | print 'using',
40 | print crypto,
41 | print 'and',
42 | print hash
43 | if arguments['--decode']:
44 | header = tc.getHeader()
45 | for k in header:
46 | print k, ":",
47 | if k=="Keys":
48 | print binascii.hexlify(header[k])
49 | else:
50 | print header[k]
51 | print
--------------------------------------------------------------------------------
/examples/pwcracker.py:
--------------------------------------------------------------------------------
1 | # PyTruecrypt parsing library for Python by Gareth Owen
2 | # https://github.com/drgowen/pytruecrypt/
3 | # See LICENCE for licence details
4 |
5 | # PyTruecrypt is free software: you can redistribute it and/or modify
6 | # it under the terms of the GNU General Public License as published by
7 | # the Free Software Foundation, either version 3 of the License, or
8 | # (at your option) any later version.
9 |
10 | # PyTruecrypt is distributed in the hope that it will be useful,
11 | # but WITHOUT ANY WARRANTY; without even the implied warranty of
12 | # MERCHANTABILITY or FITNESS FOR A PARTICULAR PURPOSE. See the
13 | # GNU General Public License for more details.
14 |
15 | # You should have received a copy of the GNU General Public License
16 | # along with PyTruecrypt. If not, see .
17 |
18 | # Truecrypt password cracker
19 |
20 | import sys
21 |
22 | sys.path.append("..")
23 |
24 | from pytruecrypt import *
25 | import binascii
26 | import os
27 | from subprocess import *
28 | import stat
29 | import getpass
30 | import getopt
31 |
32 | hidden = False
33 |
34 | args = getopt.getopt(sys.argv[1:], "h")
35 |
36 | # parse cmdline options
37 | for k in args[0]:
38 | if k[0]=='-h':
39 | hidden = True
40 |
41 | if len(args[1]) != 2:
42 | print "Usage: python pwcrack.py [-h] volumepath wordlist"
43 | print "Crack truecrypt volume"
44 | print
45 | print " -h\tcrack hidden volume"
46 | print
47 | sys.exit(1)
48 |
49 | FILENAME = args[1][0]
50 |
51 | # open word list
52 | fdwords = open(args[1][1], "r")
53 |
54 | #initialise pytruecrypt
55 | tc = PyTruecrypt(FILENAME)
56 |
57 | # loop through words
58 | for line in fdwords.readlines():
59 | word = line.strip()
60 |
61 | #open volume (returns false on failure)
62 | if tc.open(word, decode=False, hidden=hidden):
63 | print "PW Found: "+word
64 | sys.exit(1)
65 |
66 | print "failed"
67 |
--------------------------------------------------------------------------------
/examples/quick-container.py:
--------------------------------------------------------------------------------
1 | """
2 | quick-container will create a simple TC container very quickly, and
3 | always uses AES and RIPEMD-160.
4 |
5 | While the containers work it should not be considered secure.
6 |
7 | GitHub: https://github.com/4144414D/pytruecrypt
8 |
9 | Usage:
10 | quick-container
11 | """
12 |
13 | import binascii
14 | from docopt import docopt
15 | from Crypto.Random import _UserFriendlyRNG as RNG
16 | from Crypto.Hash import RIPEMD
17 | from Crypto.Cipher import AES
18 | from Crypto.Protocol.KDF import *
19 | from util import *
20 |
21 | def encrypt(enc, encxts, sector, plaintext, offset=0):
22 | # Encrypt IV to produce XTS tweak
23 | ek2n = encxts.encrypt(inttoLE(sector))
24 |
25 | tc_cipher = ''
26 | for i in range(offset, 512, 16):
27 | # Decrypt and apply tweak according to XTS scheme
28 | # pt = Dec(ct ^ ek2n) ^ ek2n
29 | ctext = xor( enc.encrypt( xor(ek2n, plaintext[i:i+16]) ) , ek2n)
30 | tc_cipher += ctext
31 | ek2n = exponentiate_tweak(ek2n)
32 | return tc_cipher
33 |
34 | # exponentiate tweak for next block (multiply by two in finite field)
35 | def exponentiate_tweak(ek2n):
36 | ek2n_i = LEtoint(ek2n) # Little Endian to python int
37 | ek2n_i = (ek2n_i << 1) # multiply by two using left shift
38 | if ek2n_i & (1<<128): # correct for carry
39 | ek2n_i ^= 0x87
40 | return inttoLE(ek2n_i)
41 |
42 | if __name__ == '__main__':
43 | arguments = docopt(__doc__)
44 | file = open(arguments[''],'wb')
45 | size = int(arguments['']) * 1024 * 1024 #get size in bytes
46 |
47 | #create large file
48 | file.truncate(size)
49 |
50 | #create empty header
51 | header = ""
52 |
53 | #create salt for normal header
54 | salt = RNG.get_random_bytes(64)
55 | header += salt
56 |
57 | #ASCII string "TRUE"
58 | header += "TRUE"
59 |
60 | #Volume header format version
61 | header += "\x00\x05" #Same as 7.1a
62 |
63 | #Minimum program version required to open the volume
64 | header += "\x07\x00" #Same as 7.1a
65 |
66 | #CRC-32 checksum of the (decrypted) bytes 256-511 (to be calculated later)
67 | header += "\xAA" * 4
68 |
69 | #Reserved (must contain zeroes)
70 | header += "\x00" * 16
71 |
72 | #Size of hidden volume (set to zero in non-hidden volumes)
73 | header += "\x00" * 8
74 |
75 | #Size of volume
76 | volume_size = size - 262144
77 | header += struct.pack('>Q',volume_size)
78 |
79 | #Byte offset of the start of the master key scope
80 | header += "\x00\x00\x00\x00\x00\x02\x00\x00"
81 |
82 | #Size of the encrypted area within the master key scope
83 | header += "\x00\x00\x00\x00\x00\x0c\x00\x00"
84 |
85 | #Flag bits
86 | header += "\x00" * 4
87 |
88 | #Sector size (in bytes)
89 | header += "\x00\x00\x02\x00"
90 |
91 | #Reserved (must contain zeroes)
92 | header += "\x00" * 120
93 |
94 | #CRC-32 checksum of the (decrypted) bytes 64-251 (to be calculated later)
95 | header += "\xBB" * 4
96 |
97 | #generate password hash
98 | pwhash = PBKDF2(arguments[''], salt, 64, count=2000, prf=lambda p,s: HMAC.new(p,s,RIPEMD).digest())
99 |
100 | #create header pycrypto
101 | hdrkeys = { 'key':pwhash[0:32], 'xtskey':pwhash[32:64] }
102 | hdraes = AES.new(hdrkeys['key'], AES.MODE_ECB)
103 | hdraesxts = AES.new(hdrkeys['xtskey'], AES.MODE_ECB)
104 |
105 | #create container keys
106 | containerkey = PBKDF2(RNG.get_random_bytes(64), RNG.get_random_bytes(64), 64, count=50000, prf=lambda p,s: HMAC.new(p,s,RIPEMD).digest())
107 | header += containerkey
108 |
109 | #fill sector with zeros
110 | header += "\x00" * 192
111 |
112 | #calculate CRC-32 checksum of the (decrypted) bytes 256-511
113 | calculatedCRC = struct.pack('>I',binascii.crc32(header[256:]) & 0xffffffff)
114 | header = header[:72] + calculatedCRC + header[76:]
115 |
116 | #calculate CRC-32 checksum of the (decrypted) bytes 64-251
117 | calculatedCRC = struct.pack('>I',binascii.crc32(header[64:252]) & 0xffffffff)
118 | header = header[:252] + calculatedCRC + header[256:]
119 |
120 | #encrypt header with header keys
121 | encrypted_header = salt + encrypt(hdraes, hdraesxts, 0, header, 64)
122 |
123 | #create backup salt
124 | backup_salt = RNG.get_random_bytes(64)
125 |
126 | #generate backup password hash
127 | pwhash = PBKDF2(arguments[''], backup_salt, 64, count=2000, prf=lambda p,s: HMAC.new(p,s,RIPEMD).digest())
128 |
129 | #create backup header pycrypto
130 | hdrkeys = { 'key':pwhash[0:32], 'xtskey':pwhash[32:64] }
131 | hdraes = AES.new(hdrkeys['key'], AES.MODE_ECB)
132 | hdraesxts = AES.new(hdrkeys['xtskey'], AES.MODE_ECB)
133 |
134 | #encrypt backup header
135 | encrypted_backup_header = backup_salt + encrypt(hdraes, hdraesxts, 0, header, 64)
136 |
137 | #write headers
138 | file.seek(0)
139 | file.write(encrypted_header)
140 | file.seek(size - 131072)
141 | file.write(encrypted_backup_header)
142 | file.close()
--------------------------------------------------------------------------------
/examples/reserved.py:
--------------------------------------------------------------------------------
1 | """
2 | Reserved can be used to both check for data hidden in the reserved sections of a
3 | TrueCrypt container, and to hide data there.
4 |
5 | GitHub: https://github.com/4144414D/pytruecrypt
6 |
7 | Usage:
8 | reserved check [--hidden]
9 | reserved hide [--hidden]
10 |
11 | Options:
12 | -h, --help Show this screen.
13 | --hidden Use the hidden volume space.
14 | """
15 |
16 | from pytruecrypt import *
17 | from docopt import docopt
18 | import sys
19 | import os
20 |
21 | if __name__ == '__main__':
22 | arguments = docopt(__doc__)
23 | tc = PyTruecrypt(arguments[''])
24 | if tc.open(arguments[''],hidden=arguments['--hidden']):
25 | if arguments['check']:
26 | reserved = ''
27 | for i in range(-127,0):
28 | reserved += tc.getPlainSector(i)
29 | sys.stdout.write(reserved)
30 | elif arguments['hide']:
31 | f = open(arguments[''])
32 | f.seek(0, os.SEEK_END)
33 | size = f.tell()
34 | if size > 65024:
35 | print 'File is too big to hide'
36 | exit(1)
37 | f.seek(0)
38 | data = f.read()
39 | while len(data) < 65024: data += '\x00'
40 | for i in range(-127,0):
41 | tc.putCipherSector(i,data[((i + 127) * 512):(((i + 127) * 512) + 512)])
42 | else:
43 | print "Failed to open TrueCrypt volume"
44 | exit(1)
--------------------------------------------------------------------------------
/pytruecrypt.py:
--------------------------------------------------------------------------------
1 | # Truecrypt parsing library for Python by Gareth Owen
2 | # https://github.com/drgowen/pytruecrypt/
3 | # See LICENCE for licence details
4 |
5 | # PyTruecrypt is free software: you can redistribute it and/or modify
6 | # it under the terms of the GNU General Public License as published by
7 | # the Free Software Foundation, either version 3 of the License, or
8 | # (at your option) any later version.
9 |
10 | # PyTruecrypt is distributed in the hope that it will be useful,
11 | # but WITHOUT ANY WARRANTY; without even the implied warranty of
12 | # MERCHANTABILITY or FITNESS FOR A PARTICULAR PURPOSE. See the
13 | # GNU General Public License for more details.
14 |
15 | # You should have received a copy of the GNU General Public License
16 | # along with PyTruecrypt. If not, see .
17 |
18 | from collections import namedtuple
19 | import sys
20 | from Crypto.Protocol.KDF import *
21 | from Crypto.Hash import RIPEMD, SHA512
22 | from CryptoPlus.Hash import python_whirlpool as WHIRLPOOL
23 | from Crypto.Cipher import AES
24 | from CryptoPlus.Cipher import python_Twofish as TwoFish
25 | from CryptoPlus.Cipher import python_Serpent as Serpent
26 | import binascii
27 | import struct
28 | import os
29 | from util import *
30 |
31 | class encObject:
32 | """pycrypto objects used by PyTruecrypt"""
33 | def __init__(self, type):
34 | self.keys = None
35 | self.enc = None
36 | self.encxts = None
37 | self.type = type
38 |
39 | def set_keys(self, key):
40 | #keys = {'key' : binascii.unhexlify(key[:64]),'xtskey' : binascii.unhexlify(key[64:])}
41 | keys = {'key' : key[:32],'xtskey' : key[32:]}
42 | self.keys = keys
43 | self.enc = self._get_encryption_object(self.keys['key'])
44 | self.encxts = self._get_encryption_object(self.keys['xtskey'])
45 |
46 | def _get_encryption_object(self,key):
47 | if self.type == "aes":
48 | return AES.new(key, AES.MODE_ECB)
49 | elif self.type == "serpent":
50 | return Serpent.new(key, Serpent.MODE_ECB)
51 | elif self.type == "twofish":
52 | return TwoFish.new(key, TwoFish.MODE_ECB)
53 | else:
54 | return False
55 |
56 | class PyTruecrypt:
57 | def __init__(self, filename="", veracrypt=False, encryption=["aes"], hash_func="default", fd=None):
58 | self.fn = filename
59 | self.veracrypt = veracrypt
60 | self.valid = False
61 | self.encryption_mode = encryption
62 | self.fd = fd
63 |
64 | #check viable encryption_mode chosen
65 | if self.encryption_mode not in [["aes"],["aes","twofish"],["aes","twofish","serpent"],["serpent"],["serpent","aes"],["serpent","twofish","aes"],["twofish"],["twofish","serpent"]]:
66 | print "Incorrect encryption mode selected"
67 | return False
68 |
69 | #create encryption objects, encryption must be a list of the cipher(s) used in order. Note that the TrueCrypt documentation is incorrect.
70 | self.hdrenc = {}
71 | self.dataenc = {}
72 | for mode in encryption:
73 | if mode in ['aes','twofish','serpent']:
74 | self.hdrenc[mode] = encObject(mode)
75 | self.dataenc[mode] = encObject(mode)
76 |
77 | #set defaults
78 | if hash_func == "default" and not veracrypt:
79 | hash_func = 'ripemd'
80 | elif hash_func == "default" and veracrypt:
81 | hash_func = 'sha512'
82 |
83 | #create pycrypto hash object
84 | if hash_func == 'sha512':
85 | self.hash_func = SHA512
86 | self.hash_func_rounds = (1000 if not self.veracrypt else 500000)
87 | elif hash_func == 'ripemd':
88 | self.hash_func = RIPEMD
89 | self.hash_func_rounds = (2000 if not self.veracrypt else 500000)
90 | elif hash_func == 'whirlpool':
91 | self.hash_func = WHIRLPOOL
92 | self.hash_func_rounds = (1000 if not self.veracrypt else 500000)
93 |
94 | def open_with_key(self, aes_key=None, twofish_key=None, serpent_key=None):
95 | if not self.fd: self.fd = open(self.fn, "r+b")
96 | self.fd.seek(0, os.SEEK_END)
97 | self.size = self.fd.tell()
98 | if aes_key: self.dataenc['aes'].set_keys(aes_key)
99 | if twofish_key: self.dataenc['twofish'].set_keys(twofish_key)
100 | if serpent_key: self.dataenc['serpent'].set_keys(serpent_key)
101 | self.open_with_key = True
102 |
103 | def open(self, password, hidden=False, decode=True, backup=False, keyfiles=None):
104 | if keyfiles:
105 | self.pw = self.keyfile(password,keyfiles)
106 | else:
107 | self.pw = password
108 |
109 | #open container as file object
110 | if not self.fd: self.fd = open(self.fn, "r+b")
111 | self.fd.seek(0, os.SEEK_END)
112 |
113 | #get total size of container
114 | self.size = self.fd.tell()
115 |
116 | #seek to the correct location in the container to read the header
117 | if backup:
118 | self.fd.seek((self.fd.size - 131072) if not hidden else (self.fd.size - 65536))
119 | else:
120 | self.fd.seek(0 if not hidden else 65536)
121 |
122 | #read the encrypted header
123 | self.tchdr_ciphered = self.fd.read(512)
124 |
125 | #get the unencrypted salt for the header key
126 | self.salt = self.tchdr_ciphered[0:64]
127 | self.hdrkeys = None
128 |
129 | # Header key derivation
130 | pwhash = PBKDF2(self.pw, self.salt, 64*len(self.encryption_mode), count=self.hash_func_rounds, prf=lambda p,s: HMAC.new(p,s,self.hash_func).digest())
131 |
132 | #get header crypto keys from pwhash
133 | keys = []
134 | if len(self.encryption_mode) == 1:
135 | keys.append(pwhash[0:64])
136 | elif len(self.encryption_mode) == 2:
137 | keys.append(pwhash[32:64]+pwhash[96:128])
138 | keys.append(pwhash[0:32]+pwhash[64:96])
139 | elif len(self.encryption_mode) == 3:
140 | keys.append(pwhash[64:96]+pwhash[160:192])
141 | keys.append(pwhash[32:64]+pwhash[128:160])
142 | keys.append(pwhash[0:32]+pwhash[96:128])
143 |
144 | #create header crypto objects
145 | i = 0
146 | for mode in self.encryption_mode:
147 | self.hdrenc[mode].set_keys(keys[i])
148 | i = i + 1
149 |
150 | #decrypt header
151 | self.tchdr_plain = self._decrypt_sector(0,self.tchdr_ciphered,64,True)
152 |
153 | #check correct decryption
154 | magic_number = ("TRUE" if not self.veracrypt else "VERA")
155 | if self.tchdr_plain[0:4] != magic_number:
156 | #magic number is incorrect
157 | self.valid = False
158 | else:
159 | #magic number is correct
160 | self.valid = True
161 |
162 | #check crc values
163 | self.checkCRC32()
164 |
165 | if decode:
166 | self.decodeHeader()
167 |
168 | if self.valid and self.valid_HeaderCRC and self.valid_KeyCRC:
169 | return True
170 | else:
171 | return False
172 |
173 | # from "TrueCrypt 7.1a Source\Common\Crc.c"
174 | def truecrypt_crc(self, data, crc):
175 | # /* CRC polynomial 0x04c11db7 */
176 | crc_32_tab = [
177 | 0x00000000, 0x77073096, 0xee0e612c, 0x990951ba, 0x076dc419, 0x706af48f, 0xe963a535, 0x9e6495a3,
178 | 0x0edb8832, 0x79dcb8a4, 0xe0d5e91e, 0x97d2d988, 0x09b64c2b, 0x7eb17cbd, 0xe7b82d07, 0x90bf1d91,
179 | 0x1db71064, 0x6ab020f2, 0xf3b97148, 0x84be41de, 0x1adad47d, 0x6ddde4eb, 0xf4d4b551, 0x83d385c7,
180 | 0x136c9856, 0x646ba8c0, 0xfd62f97a, 0x8a65c9ec, 0x14015c4f, 0x63066cd9, 0xfa0f3d63, 0x8d080df5,
181 | 0x3b6e20c8, 0x4c69105e, 0xd56041e4, 0xa2677172, 0x3c03e4d1, 0x4b04d447, 0xd20d85fd, 0xa50ab56b,
182 | 0x35b5a8fa, 0x42b2986c, 0xdbbbc9d6, 0xacbcf940, 0x32d86ce3, 0x45df5c75, 0xdcd60dcf, 0xabd13d59,
183 | 0x26d930ac, 0x51de003a, 0xc8d75180, 0xbfd06116, 0x21b4f4b5, 0x56b3c423, 0xcfba9599, 0xb8bda50f,
184 | 0x2802b89e, 0x5f058808, 0xc60cd9b2, 0xb10be924, 0x2f6f7c87, 0x58684c11, 0xc1611dab, 0xb6662d3d,
185 | 0x76dc4190, 0x01db7106, 0x98d220bc, 0xefd5102a, 0x71b18589, 0x06b6b51f, 0x9fbfe4a5, 0xe8b8d433,
186 | 0x7807c9a2, 0x0f00f934, 0x9609a88e, 0xe10e9818, 0x7f6a0dbb, 0x086d3d2d, 0x91646c97, 0xe6635c01,
187 | 0x6b6b51f4, 0x1c6c6162, 0x856530d8, 0xf262004e, 0x6c0695ed, 0x1b01a57b, 0x8208f4c1, 0xf50fc457,
188 | 0x65b0d9c6, 0x12b7e950, 0x8bbeb8ea, 0xfcb9887c, 0x62dd1ddf, 0x15da2d49, 0x8cd37cf3, 0xfbd44c65,
189 | 0x4db26158, 0x3ab551ce, 0xa3bc0074, 0xd4bb30e2, 0x4adfa541, 0x3dd895d7, 0xa4d1c46d, 0xd3d6f4fb,
190 | 0x4369e96a, 0x346ed9fc, 0xad678846, 0xda60b8d0, 0x44042d73, 0x33031de5, 0xaa0a4c5f, 0xdd0d7cc9,
191 | 0x5005713c, 0x270241aa, 0xbe0b1010, 0xc90c2086, 0x5768b525, 0x206f85b3, 0xb966d409, 0xce61e49f,
192 | 0x5edef90e, 0x29d9c998, 0xb0d09822, 0xc7d7a8b4, 0x59b33d17, 0x2eb40d81, 0xb7bd5c3b, 0xc0ba6cad,
193 | 0xedb88320, 0x9abfb3b6, 0x03b6e20c, 0x74b1d29a, 0xead54739, 0x9dd277af, 0x04db2615, 0x73dc1683,
194 | 0xe3630b12, 0x94643b84, 0x0d6d6a3e, 0x7a6a5aa8, 0xe40ecf0b, 0x9309ff9d, 0x0a00ae27, 0x7d079eb1,
195 | 0xf00f9344, 0x8708a3d2, 0x1e01f268, 0x6906c2fe, 0xf762575d, 0x806567cb, 0x196c3671, 0x6e6b06e7,
196 | 0xfed41b76, 0x89d32be0, 0x10da7a5a, 0x67dd4acc, 0xf9b9df6f, 0x8ebeeff9, 0x17b7be43, 0x60b08ed5,
197 | 0xd6d6a3e8, 0xa1d1937e, 0x38d8c2c4, 0x4fdff252, 0xd1bb67f1, 0xa6bc5767, 0x3fb506dd, 0x48b2364b,
198 | 0xd80d2bda, 0xaf0a1b4c, 0x36034af6, 0x41047a60, 0xdf60efc3, 0xa867df55, 0x316e8eef, 0x4669be79,
199 | 0xcb61b38c, 0xbc66831a, 0x256fd2a0, 0x5268e236, 0xcc0c7795, 0xbb0b4703, 0x220216b9, 0x5505262f,
200 | 0xc5ba3bbe, 0xb2bd0b28, 0x2bb45a92, 0x5cb36a04, 0xc2d7ffa7, 0xb5d0cf31, 0x2cd99e8b, 0x5bdeae1d,
201 | 0x9b64c2b0, 0xec63f226, 0x756aa39c, 0x026d930a, 0x9c0906a9, 0xeb0e363f, 0x72076785, 0x05005713,
202 | 0x95bf4a82, 0xe2b87a14, 0x7bb12bae, 0x0cb61b38, 0x92d28e9b, 0xe5d5be0d, 0x7cdcefb7, 0x0bdbdf21,
203 | 0x86d3d2d4, 0xf1d4e242, 0x68ddb3f8, 0x1fda836e, 0x81be16cd, 0xf6b9265b, 0x6fb077e1, 0x18b74777,
204 | 0x88085ae6, 0xff0f6a70, 0x66063bca, 0x11010b5c, 0x8f659eff, 0xf862ae69, 0x616bffd3, 0x166ccf45,
205 | 0xa00ae278, 0xd70dd2ee, 0x4e048354, 0x3903b3c2, 0xa7672661, 0xd06016f7, 0x4969474d, 0x3e6e77db,
206 | 0xaed16a4a, 0xd9d65adc, 0x40df0b66, 0x37d83bf0, 0xa9bcae53, 0xdebb9ec5, 0x47b2cf7f, 0x30b5ffe9,
207 | 0xbdbdf21c, 0xcabac28a, 0x53b39330, 0x24b4a3a6, 0xbad03605, 0xcdd70693, 0x54de5729, 0x23d967bf,
208 | 0xb3667a2e, 0xc4614ab8, 0x5d681b02, 0x2a6f2b94, 0xb40bbe37, 0xc30c8ea1, 0x5a05df1b, 0x2d02ef8d]
209 |
210 | # CRC = (CRC >> 8) ^ crc_32_tab[ (CRC ^ *data++) & 0xFF ];
211 | return (crc >> 8) ^ crc_32_tab[(crc ^ ord(data)) & 0xFF]
212 |
213 | def keyfile(self,password,keyfiles):
214 | #pad password with zero bytes until length of 64
215 | while len(password) < 64:
216 | password = password + '\x00'
217 |
218 | #fill keypool with zero bytes
219 | keyfilePool = []
220 | keyfilePoolCursor = 0
221 | for x in range(64):
222 | keyfilePool.append(0)
223 |
224 | total_processed = 0
225 | for keyfile in keyfiles:
226 | keyfilefd = open(keyfile,'rb')
227 | keyfilefd.seek(0)
228 | keyfiledata = keyfilefd.read(1048576) #read first 1MB
229 | keyfilefd.close()
230 |
231 | #stop processing if 1MB has been read
232 | if total_processed == 1048576: break
233 |
234 | #read each byte of keyfile, stopping at 1MB in total
235 | crc = 0xFFFFFFFF
236 | for x in range(len(keyfiledata)):
237 | total_processed += 1
238 |
239 | # from "TrueCrypt 7.1a Source\Common\Keyfiles.c"
240 | crc = self.truecrypt_crc(keyfiledata[x], crc) & 0xFFFFFFFF
241 | #keyPool[writePos++] += (unsigned __int8) (crc >> 24);
242 | keyfilePool[keyfilePoolCursor] = (keyfilePool[keyfilePoolCursor] + ((crc >> 24) & 0xFF)) % 256
243 | #keyPool[writePos++] += (unsigned __int8) (crc >> 16);
244 | keyfilePool[keyfilePoolCursor+1] = (keyfilePool[keyfilePoolCursor+1] + ((crc >> 16) & 0xFF)) % 256
245 | #keyPool[writePos++] += (unsigned __int8) (crc >> 8);
246 | keyfilePool[keyfilePoolCursor+2] = (keyfilePool[keyfilePoolCursor+2] + ((crc >> 8) & 0xFF)) % 256
247 | #keyPool[writePos++] += (unsigned __int8) crc;
248 | keyfilePool[keyfilePoolCursor+3] = (keyfilePool[keyfilePoolCursor+3] + ((crc) & 0xFF)) % 256
249 | keyfilePoolCursor += 4
250 |
251 | #reset cursor if needed
252 | if keyfilePoolCursor == 64: keyfilePoolCursor = 0
253 |
254 | #stop processing if 1MB has been read
255 | if total_processed == 1048576: break
256 |
257 | keyfilePoolString = ""
258 | for x in range(64):
259 | keyfilePoolString = keyfilePoolString + chr((keyfilePool[x] + ord(password[x])) % 256)
260 |
261 | return keyfilePoolString
262 |
263 | def decodeHeader(self):
264 | #Decode header into struct/namedtuple
265 | TCHDR = namedtuple('TCHDR', "Magic HdrVersion MinProgVer CRC Reserved HiddenVolSize VolSize DataStart DataSize Flags SectorSize Reserved2 CRC3 Keys")
266 | self.hdr_decoded = TCHDR._make(struct.unpack(">4sH", self.tchdr_plain[0:6]) + struct.unpack("I16sQQQQII120sI256s", self.tchdr_plain[8:448]))
267 |
268 | #load primary and secondary key for each crypto
269 | keys = []
270 | if len(self.encryption_mode) == 1:
271 | keys.append(self.hdr_decoded.Keys[0:64])
272 | elif len(self.encryption_mode) == 2:
273 | keys.append(self.hdr_decoded.Keys[32:64]+self.hdr_decoded.Keys[96:128])
274 | keys.append(self.hdr_decoded.Keys[0:32]+self.hdr_decoded.Keys[64:96])
275 | elif len(self.encryption_mode) == 3:
276 | keys.append(self.hdr_decoded.Keys[64:96]+self.hdr_decoded.Keys[160:192])
277 | keys.append(self.hdr_decoded.Keys[32:64]+self.hdr_decoded.Keys[128:160])
278 | keys.append(self.hdr_decoded.Keys[0:32]+self.hdr_decoded.Keys[96:128])
279 | i = 0
280 | for mode in self.encryption_mode:
281 | self.dataenc[mode].set_keys(keys[i])
282 | i = i + 1
283 |
284 | #decoded header is python dict
285 | def getHeader(self):
286 | if not self.valid:
287 | return False
288 | return self.hdr_decoded._asdict()
289 |
290 | # Raw plaintext header
291 | def getHeaderRaw(self):
292 | if not self.valid:
293 | return False
294 | return self.tchdr_plain
295 |
296 | # Gets plaintext sector from data section
297 | def getPlainSector(self, sector, secstart=0):
298 | if not (self.valid or (self.open_with_key and secstart > 0)):
299 | return False
300 | if self.valid and secstart == 0:
301 | secstart = self.hdr_decoded.DataStart / 512
302 | self.fd.seek((secstart + sector)*512)
303 | return self._decrypt_sector(secstart + sector, self.fd.read(512))
304 |
305 | # Gets ciphertext sector from data input
306 | def getCipherSector(self, sector, plaintext, secstart=0):
307 | if not (self.valid or (self.open_with_key and secstart > 0)):
308 | return False
309 | if len(plaintext) != 512:
310 | return False
311 | if self.valid and secstart == 0:
312 | secstart = self.hdr_decoded.DataStart / 512
313 | return self._encrypt_sector(secstart + sector, plaintext)
314 |
315 | # Writes ciphertext sector from data input
316 | def putCipherSector(self, sector, plaintext, secstart=0):
317 | if not (self.valid or (self.open_with_key and secstart > 0)):
318 | return False
319 | if len(plaintext) != 512:
320 | return False
321 | if self.valid:
322 | secstart = self.hdr_decoded.DataStart / 512
323 | cipherSector = self.getCipherSector(sector, plaintext, secstart)
324 | self.fd.seek((secstart + sector) * 512)
325 | self.fd.write(cipherSector)
326 |
327 | # checks if the CRC32 of bytes matches the target CRC32
328 | def calculateCRC32(self,bytes,target):
329 | if struct.pack('>I',binascii.crc32(bytes) & 0xffffffff) == target:
330 | return True
331 | else:
332 | return False
333 |
334 | # checks if the store CRC32 in the header matches the calculated CRC32 header
335 | def checkCRC32(self):
336 | self.valid_HeaderCRC = self.calculateCRC32(self.tchdr_plain[:188],self.tchdr_plain[188:192])
337 | self.valid_KeyCRC = self.calculateCRC32(self.tchdr_plain[192:],self.tchdr_plain[8:12])
338 |
339 | # Decrypts a sector, given one or more pycrypto objects for master key plus xts key
340 | # Offset for partial sector decrypts (e.g. hdr)
341 | # internal function, uses _single_decrypt_sector to decrypt data for each pycrypto object
342 | def _decrypt_sector(self, sector, ciphertext, offset=0, header=False):
343 | for mode in self.encryption_mode:
344 | if header:
345 | ciphertext = self._single_decrypt_sector(self.hdrenc[mode].enc, self.hdrenc[mode].encxts,sector,ciphertext,offset)
346 | else:
347 | ciphertext = self._single_decrypt_sector(self.dataenc[mode].enc, self.dataenc[mode].encxts,sector,ciphertext,offset)
348 | return ciphertext[offset:]
349 |
350 | def _encrypt_sector(self, sector, plaintext, offset=0, header=False):
351 | for mode in self.encryption_mode:
352 | if header:
353 | plaintext = self._single_encrypt_sector(self.hdrenc[mode].enc, self.hdrenc[mode].encxts,sector,plaintext,offset)
354 | else:
355 | plaintext = self._single_encrypt_sector(self.dataenc[mode].enc, self.dataenc[mode].encxts,sector,plaintext,offset)
356 | return plaintext[offset:]
357 |
358 | def _single_encrypt_sector(self, enc, encxts, sector, plaintext, offset=0):
359 | # Encrypt IV to produce XTS tweak
360 | ek2n = encxts.encrypt(inttoLE(sector))
361 |
362 | tc_cipher = '\x00' * offset #pad for offset
363 | print hexdump(plaintext)
364 | for i in range(offset, 512, 16):
365 | # Decrypt and apply tweak according to XTS scheme
366 | # pt = Dec(ct ^ ek2n) ^ ek2n
367 | ctext = xor( enc.encrypt( xor(ek2n, plaintext[i:i+16]) ) , ek2n)
368 | tc_cipher += ctext
369 | ek2n = self._exponentiate_tweak(ek2n)
370 | return tc_cipher
371 |
372 | # Decrypt ciphertext with individual crypto object
373 | # Internal function
374 | def _single_decrypt_sector(self, enc, encxts, sector, ciphertext, offset=0):
375 | # Encrypt IV to produce XTS tweak
376 | ek2n = encxts.encrypt(inttoLE(sector))
377 |
378 | tc_plain = '\x00' * offset #pad for offset
379 | for i in range(offset, 512, 16):
380 | # Decrypt and apply tweak according to XTS scheme
381 | # pt = Dec(ct ^ ek2n) ^ ek2n
382 | ptext = xor( enc.decrypt( xor(ek2n, ciphertext[i:i+16]) ) , ek2n)
383 | tc_plain += ptext
384 | ek2n = self._exponentiate_tweak(ek2n)
385 | return tc_plain
386 |
387 | # exponentiate tweak for next block (multiply by two in finite field)
388 | def _exponentiate_tweak(self, ek2n):
389 | ek2n_i = LEtoint(ek2n) # Little Endian to python int
390 | ek2n_i = (ek2n_i << 1) # multiply by two using left shift
391 | if ek2n_i & (1<<128): # correct for carry
392 | ek2n_i ^= 0x87
393 | return inttoLE(ek2n_i)
394 |
--------------------------------------------------------------------------------
/util.py:
--------------------------------------------------------------------------------
1 | # Truecrypt parsing library for Python by Gareth Owen
2 | # https://github.com/drgowen/pytruecrypt/
3 | # See LICENCE for licence details
4 |
5 | # PyTruecrypt is free software: you can redistribute it and/or modify
6 | # it under the terms of the GNU General Public License as published by
7 | # the Free Software Foundation, either version 3 of the License, or
8 | # (at your option) any later version.
9 |
10 | # PyTruecrypt is distributed in the hope that it will be useful,
11 | # but WITHOUT ANY WARRANTY; without even the implied warranty of
12 | # MERCHANTABILITY or FITNESS FOR A PARTICULAR PURPOSE. See the
13 | # GNU General Public License for more details.
14 |
15 | # You should have received a copy of the GNU General Public License
16 | # along with PyTruecrypt. If not, see .
17 |
18 |
19 | # hexdump print function
20 | def hexdump(src, length=16):
21 | FILTER = ''.join([(len(repr(chr(x))) == 3) and chr(x) or '.' for x in range(256)])
22 | lines = []
23 | for c in xrange(0, len(src), length):
24 | chars = src[c:c+length]
25 | hex = ' '.join(["%02x" % ord(x) for x in chars])
26 | printable = ''.join(["%s" % ((ord(x) <= 127 and FILTER[ord(x)]) or '.') for x in chars])
27 | lines.append("%04x %-*s %s\n" % (c, length*3, hex, printable))
28 | return ''.join(lines)
29 |
30 | # Integer to little endian (int array)
31 | # Note: must output 128bit block (ignoring higher significant bytes) otherwise breaks xts code
32 | def inttoLE(x):
33 | str=''
34 | for i in range(16):
35 | str += (chr((x & (0xFF << i*8)) >> i*8))
36 | return str
37 |
38 | # Little endian (int array) to integer
39 | def LEtoint(x):
40 | y = 0
41 | for i in range(16):
42 | y = y + (ord(x[i]) << i*8)
43 | return y
44 |
45 | # Integer array to string
46 | def buftostr(x):
47 | return ''.join(map(chr, x))
48 |
49 | # String to integer array
50 | def strtobuf(x):
51 | return [ord(i) for i in x]
52 |
53 | # XOR two strings
54 | def xor(a,b):
55 | return ''.join([chr(ord(a[i])^ord(b[i])) for i in range(len(a))])
56 |
57 |
--------------------------------------------------------------------------------