', logs)
278 | if grp.mapSettings.triggers:
279 | self.assertInLogs('set hightag to ', logs)
280 | self.assertInLogs('
', logs)
281 | return newMd5s
282 |
283 | def assertInLogs(self, text, logs):
284 | if text.lower() not in logs.lower():
285 | self.fail(text + ' not found in logs')
286 |
287 | def Md5GameFiles(self, testname:str, grp:GrpBase, basepath:Path) -> dict:
288 | with self.subTest('MD5 '+testname):
289 | maps = grp.GetAllFilesEndsWith('.map')
290 | cons = list(grp.gameSettings.conFiles.keys())
291 | return self.Md5Files(basepath, (maps+cons))
292 |
293 | def Md5Files(self, basepath: Path, filenames: list) -> dict:
294 | md5s = {}
295 | for f in filenames:
296 | t = self.Md5File(Path(basepath, f))
297 | md5s[f] = t
298 | trace('Md5Files ', basepath, ': ', md5s)
299 | return md5s
300 |
301 | def Md5File(self, filename:Path):
302 | with open(filename) as file, mmap(file.fileno(), 0, access=ACCESS_READ) as file:
303 | md5sum = md5(file).hexdigest()
304 | return md5sum
305 |
306 | def test_walls(self):
307 | with self.subTest('test PointIsInShape'):
308 | walls = [(0,0), (10,0), (10,10), (0,10)]
309 | self.assertEqual(buildmapbase.PointIsInShape(walls, (5,5), 0) % 2, 1)
310 | self.assertEqual(buildmapbase.PointIsInShape(walls, (15,15), 0) % 2, 0)
311 |
312 | def test_blood_crypt(self):
313 | # ensure it's reversible
314 | data = bytearray(b'123456')
315 | d2 = buildmap.MapCrypt(data, 451)
316 | d2 = buildmap.MapCrypt(d2, 451)
317 | d2 = RffCrypt(d2, 451)
318 | d2 = RffCrypt(d2, 451)
319 | self.assertEqual(data, d2)
320 |
321 | data = bytearray(b'dfgdfghcvbngertguhyrtujityr3456436fdghsdfgxcvb')
322 | d2 = buildmap.MapCrypt(data, 0x7474614d)
323 | d2 = buildmap.MapCrypt(d2, 0x7474614d)
324 | d2 = RffCrypt(d2, 451)
325 | d2 = RffCrypt(d2, 451)
326 | self.assertEqual(data, d2)
327 |
328 | def test_mirror(self):
329 | orig = [12, 11, 10, 9, 8, 7, 6, 5, 4, 3, 2, 1] # verticies are counter-clockwise, right?
330 | desired = [12, 1, 2, 3, 4, 5, 6, 7, 8, 9, 10, 11]
331 | result = buildmapbase.MirrorList(orig)
332 | self.assertListEqual(result, desired, 'mirror')
333 |
334 |
335 |
336 | def CreateGrpFile(frompath: Path, outpath: Path, filenames: list) -> None:
337 | with GrpOutput(outpath, 'test', len(filenames), '', 'GAME.CON', None, 0, 0) as out:
338 | for name in filenames:
339 | with open(Path(frompath, name), 'rb') as f:
340 | d = f.read()
341 | out.write(str(name), d)
342 |
343 | def runtests():
344 | unittest.main(verbosity=9, warnings="error", failfast=True)
345 |
346 |
347 | if __name__ == "__main__":
348 | try:
349 | if os.path.isdir(temp):
350 | shutil.rmtree(temp)
351 | if profiling:
352 | setVerbose(-10)
353 | cProfile.run("runtests()", sort="cumtime")
354 | else:
355 | runtests()
356 | finally:
357 | # if os.path.isdir(temp):
358 | # shutil.rmtree(temp)
359 | pass
360 |
--------------------------------------------------------------------------------
/BuildLibs/buildmapbase.py:
--------------------------------------------------------------------------------
1 | import abc
2 | import binascii
3 | import copy
4 | import random
5 | import struct
6 | from pathlib import Path
7 | from typing import OrderedDict, Union
8 |
9 | from BuildLibs import crc32, error, info, swapobjkey, trace, warning, FancyPacker
10 | import BuildGames
11 |
12 | class CStat:
13 |
14 | def __init__(self, cstat):
15 | self.blocking = bool(cstat & 1)
16 | self.facing = cstat & 0x30
17 | self.onesided = cstat & 0x40
18 | self.blockingHitscan = bool(cstat & 0x800)
19 | self.invisible = bool(cstat & 0x8000)
20 |
21 |
22 | class Sector:
23 |
24 | def __init__(self, data:dict):
25 | self.__dict__ = data
26 |
27 | def defaults(self, data:dict):
28 | self.wallptr: int = data.get('wallptr', 0)
29 | self.wallnum: int = data.get('wallnum', 0)
30 | self.ceilingz: int = data.get('ceilingz', 0)
31 | self.floorz: int = data.get('floorz', 0)
32 | self.ceilingstat: int = data.get('ceilingstat', 0)
33 | self.floorstat: int = data.get('floorstat', 0)
34 | self.ceilingpicnum: int = data.get('ceilingpicnum', 0)
35 | self.ceilingheinum: int = data.get('ceilingheinum', 0)
36 | self.ceilingshade: int = data.get('ceilingshade', 0)
37 | self.ceiling_palette: int = data.get('ceiling_palette', 0)
38 | self.ceiling_texcoords: list = data.get('ceiling_texcoords', [0, 0])
39 | self.floorpicnum: int = data.get('floorpicnum', 0)
40 | self.floorheinum: int = data.get('floorheinum', 0)
41 | self.floorshade: int = data.get('floorshade', 0)
42 | self.floor_palette: int = data.get('floor_palette', 0)
43 | self.floor_texcoords: list = data.get('floor_texcoords', [0, 0])
44 | self.visibility: int = data.get('visibility', 0)
45 | self.filler: int = data.get('filler', 0)
46 | self.lowtag: int = data.get('lowtag', 0)
47 | self.hightag: int = data.get('hightag', 0)
48 | self.extra: int = data.get('extra', -1)
49 | self.length: int = data.get('length', 0)
50 | self.ceilingxpanning: int = data.get('ceilingxpanning', 0)
51 | self.floorxpanning: int = data.get('floorxpanning', 0)
52 | self.ceilingypanning: int = data.get('ceilingypanning', 0)
53 | self.floorypanning: int = data.get('floorypanning', 0)
54 |
55 | self.walls: Union[list, None] = data.get('walls', None)
56 | self.nearbySectors: Union[set, None] = data.get('nearbySectors', None)
57 | self.shapes: Union[list, None] = data.get('shapes', None)
58 |
59 |
60 | class Wall:
61 |
62 | def __init__(self, data:dict):
63 | self.__dict__ = data
64 |
65 | def defaults(self, data:dict):
66 | self.pos: list = data.get('pos', [0, 0])
67 | self.next_wall: int = data.get('next_wall', 0)
68 | self.next_sector_wall: int = data.get('next_sector_wall', -1)
69 | self.next_sector: int = data.get('next_sector', -1)
70 | self.cstat: int = data.get('cstat', 0)
71 | self.picnum: int = data.get('picnum', 0)
72 | self.overpicnum: int = data.get('overpicnum', 0)
73 | self.shade: int = data.get('shade', 0)
74 | self.palette: int = data.get('palette', 0)
75 | self.texcoords: list = data.get('texcoords', [0, 0, 0, 0])
76 | self.lowtag: int = data.get('lowtag', 0)
77 | self.hightag: int = data.get('hightag', 0)
78 | self.extra: int = data.get('extra', -1)
79 | self.length: int = data.get('length', 0)
80 |
81 |
82 | class Sprite:
83 |
84 | def __init__(self, data:dict):
85 | self.__dict__ = data
86 |
87 | def defaults(self, data:dict):
88 | self.pos: list = data.get('pos', [0, 0, 0])
89 | self.cstat: int = data.get('cstat', 0)
90 | self.picnum: int = data.get('picnum', 0)
91 | self.shade: int = data.get('shade', 0)
92 | self.palette: int = data.get('palette', 0)
93 | self.clipdist: int = data.get('clipdist', 0)
94 | self.filler: int = data.get('filler', 0)
95 | self.texcoords: list = data.get('texcoords', [0, 0, 0, 0])
96 | self.sectnum: int = data.get('sectnum', 0)
97 | self.statnum: int = data.get('statnum', 0)
98 | self.angle: int = data.get('angle', 0)
99 | self.owner: int = data.get('owner', 0)
100 | self.velocity: list = data.get('velocity', [0, 0, 0])
101 | self.lowtag: int = data.get('lowtag', 0)
102 | self.hightag: int = data.get('hightag', 0)
103 | self.extra: int = data.get('extra', -1)
104 | self.extraData = data.get('extraData')
105 | self.length: int = data.get('length', 0)
106 |
107 | def __copy__(self) -> 'Sprite':
108 | cls = self.__class__
109 | copied = cls.__new__(cls)
110 | copied.__dict__.update(self.__dict__)
111 | copied.pos = copied.pos[:]
112 | copied.texcoords = copied.texcoords[:]
113 | copied.velocity = copied.velocity[:]
114 | return copied
115 |
116 |
117 | class MapFileBase(metaclass=abc.ABCMeta):
118 |
119 | """
120 | https://moddingwiki.shikadi.net/wiki/MAP_Format_(Build)
121 |
122 | """
123 |
124 | def __init__(self, gameName, name, data: bytearray = None):
125 | self.full_rewrite:bool = False
126 | self.gameSettings = BuildGames.GetGameMapSettings(gameName)
127 | self.name = name
128 | self.data = data
129 | info('\n', name, len(data) if data is not None else None)
130 |
131 | self.version = 0
132 | self.startPos = [0, 0, 0]
133 | self.startAngle = 0
134 | self.startSect = 0
135 | self.num_sectors = 0
136 | self.num_sprites = 0
137 | self.num_walls = 0
138 |
139 | self.crypt = 0
140 |
141 | self.header2Len = 0
142 | self.x_sector_size = 0
143 | self.x_wall_size = 0
144 | self.x_sprite_size = 0
145 |
146 | self.CreateHeaderPacker()
147 | self.CreateSectorPacker()
148 | self.CreateWallPacker()
149 | self.CreateSpritePacker()
150 |
151 | assert self.HEADER_SIZE == self.headerPacker.calcsize()
152 | assert self.SECTOR_SIZE == self.sectorPacker.calcsize()
153 | assert self.WALL_SIZE == self.wallPacker.calcsize()
154 | assert self.SPRITE_SIZE == self.spritePacker.calcsize()
155 |
156 | self.sectors = []
157 | self.walls = []
158 | self.items = []
159 | self.enemies = []
160 | self.triggers = []
161 | self.other_sprites = []
162 | self.sectorCache = {}
163 |
164 | if self.gameSettings.idType == 'lowtag':
165 | self.AppendSprite = self.AppendSpriteLowtag
166 | self.GetSpriteType = self.GetSpriteTypeLowtag
167 | elif self.gameSettings.swappableItems or self.gameSettings.swappableEnemies:
168 | self.AppendSprite = self.AppendSpriteId
169 | self.GetSpriteType = self.GetSpriteTypeId
170 | else:
171 | self.AppendSprite = self.BasicAppendSprite
172 | self.GetSpriteType = self.BasicGetSpriteType
173 | warning('using fallback sprite identification methods!')
174 |
175 | if data is not None:
176 | self.ReadData()
177 | assert len(self.sectors) > 0
178 | assert len(self.walls) > 0
179 | if name != 'maps/null.map':
180 | assert len(self.sprites) > 0
181 |
182 | def __str__(self):
183 | lines = []
184 | lines.append(f'MapFile: {self.name}')
185 |
186 | lines.append(f' version: {self.version}')
187 | lines.append(f' startPos: {self.startPos}')
188 | lines.append(f' startAngle: {self.startAngle}')
189 | lines.append(f' startSect: {self.startSect}')
190 |
191 | lines.append(f' num sectors: {self.num_sectors}')
192 | lines.append(f' num walls: {self.num_walls}')
193 | lines.append(f' num sprites: {self.num_sprites}')
194 | lines.append(f' len sectors: {len(self.sectors)}')
195 | lines.append(f' len walls: {len(self.walls)}')
196 | lines.append(f' len sprites: {len(self.sprites)}')
197 | lines.append(f' len data: {len(self.data) if self.data is not None else None}')
198 |
199 | return '\n'.join(lines)
200 |
201 | @property
202 | def sprites(self):
203 | return self.items + self.enemies + self.triggers + self.other_sprites
204 |
205 | def Randomize(self, seed:int, settings:dict, spoilerlog):
206 | try:
207 | spoilerlog.SetFilename(Path(self.name))
208 | spoilerlog.SetGameMapSettings(self.gameSettings)
209 | self.spoilerlog = spoilerlog
210 | self._Randomize(seed, settings)
211 | except:
212 | error('Randomize', self.name)
213 | raise
214 | finally:
215 | self.spoilerlog = None
216 | spoilerlog.FinishRandomizingFile()
217 |
218 | def _Randomize(self, seed:int, settings:dict):
219 | self.spoilerlog.write('before: '
220 | + 'items: ' + str(len(self.items)) + ', enemies: ' + str(len(self.enemies))
221 | + ', triggers: ' + str(len(self.triggers)) + ', other_sprites: ' + str(len(self.other_sprites))
222 | )
223 |
224 | chanceDupeItem:float = settings['MapFile.chanceDupeItem']
225 | chanceDeleteItem:float = settings['MapFile.chanceDeleteItem']
226 |
227 | chanceDupeEnemy:float = settings['MapFile.chanceDupeEnemy']
228 | chanceDeleteEnemy:float = settings['MapFile.chanceDeleteEnemy']
229 |
230 | itemVariety:float = settings['MapFile.itemVariety']
231 | enemyVariety:float = settings['MapFile.enemyVariety']
232 |
233 | rng = random.Random(crc32('map dupe items', self.name, seed))
234 | self.DupeSprites(rng, self.items, chanceDupeItem, 1, self.gameSettings.swappableItems, itemVariety, 'item')
235 |
236 | rng = random.Random(crc32('map shuffle items', self.name, seed))
237 | self.SwapAllSprites(rng, self.items, 'item')
238 |
239 | rng = random.Random(crc32('map reduce items', self.name, seed))
240 | self.ReduceSprites(rng, self.items, chanceDeleteItem, 'item')
241 | trace('\n')
242 |
243 | if self.gameSettings.gameName == 'Blood':
244 | # TODO: need to parse the extraData to determine if an enemy is important
245 | chanceDupeEnemy = max(chanceDupeEnemy - chanceDeleteEnemy, 0)
246 | chanceDeleteEnemy = 0
247 |
248 | rng = random.Random(crc32('map dupe enemies', self.name, seed))
249 | enemiesReplacements = {}
250 | for i in self.gameSettings.addableEnemies:
251 | enemiesReplacements[i] = self.gameSettings.swappableEnemies[i]
252 | self.DupeSprites(rng, self.enemies, chanceDupeEnemy, 2, enemiesReplacements, enemyVariety, 'enemy')
253 |
254 | rng = random.Random(crc32('map shuffle enemies', self.name, seed))
255 | self.SwapAllSprites(rng, self.enemies, 'enemy')
256 |
257 | rng = random.Random(crc32('map reduce enemies', self.name, seed))
258 | self.ReduceSprites(rng, self.enemies, chanceDeleteEnemy, 'enemy')
259 | trace('\n')
260 |
261 | rng = random.Random(crc32('map rando triggers', self.name, seed))
262 | self.RandomizeTriggers(rng, self.triggers, self.gameSettings.triggers)
263 |
264 | rng = random.Random(crc32('map additions', self.name, seed))
265 | for add in self.gameSettings.additions.get(self.name.lower(), []):
266 | self.AddSprite(rng, add)
267 |
268 | #self.MirrorMap()
269 | self.WriteData()
270 |
271 | self.spoilerlog.ListSprites('item', self.items)
272 | self.spoilerlog.ListSprites('enemy', self.enemies)
273 |
274 | self.spoilerlog.write('after: '
275 | + 'items: ' + str(len(self.items)) + ', enemies: ' + str(len(self.enemies))
276 | + ', triggers: ' + str(len(self.triggers)) + ', other_sprites: ' + str(len(self.other_sprites))
277 | )
278 |
279 | def IsItem(self, sprite:Sprite, cstat: CStat) -> bool:
280 | if self.gameSettings.swappableItems and sprite.picnum not in self.gameSettings.swappableItems:
281 | return False
282 | elif (not self.gameSettings.swappableItems) and sprite.picnum < 10:
283 | return False
284 | #elif (self.game_name == 'Ion Fury' and not cstat.blocking) or cstat.blockingHitscan or cstat.invisible or cstat.onesided or cstat.facing != 0:
285 | elif cstat.blockingHitscan or cstat.invisible or cstat.onesided or cstat.facing != 0:
286 | return False
287 | return True
288 |
289 | def SwapSprites(self, spritetype:str, a:Sprite, b:Sprite):
290 | self.spoilerlog.SwapSprites(spritetype, a, b)
291 |
292 | swapobjkey(a, b, 'pos')
293 | swapobjkey(a, b, 'sectnum')
294 | swapobjkey(a, b, 'angle')
295 | #swapobjkey(a, b, 'hightag')
296 | #swapobjkey(a, b, 'lowtag')# this seems to cause problems with shadow warrior enemies changing types?
297 | a.length, b.length = b.length, a.length
298 | a.extra, b.extra = b.extra, a.extra
299 | a.extraData, b.extraData = b.extraData, a.extraData
300 |
301 | def DupeSprite(self, rng: random.Random, sprite:Sprite, spacing: float, possibleReplacements:dict, replacementChance:float, spritetype: str) -> Union[Sprite,None]:
302 | sprite = copy.copy(sprite)
303 | if rng.random() < replacementChance:
304 | replace = rng.choice((*possibleReplacements.keys(), sprite.picnum))
305 | if replace != sprite.picnum:
306 | r = possibleReplacements[replace]
307 | sprite.lowtag = r.get('lowtag', sprite.lowtag)
308 | xrepeat = r.get('xrepeat', sprite.texcoords[0])
309 | yrepeat = r.get('yrepeat', sprite.texcoords[1])
310 | palettes = r.get('palettes', [0])
311 | sprite.palette = rng.choice(palettes)
312 | sprite.texcoords = [xrepeat, yrepeat, 0, 0]
313 | sprite.picnum = replace
314 | for i in range(20):
315 | x = rng.choice([-350, -250, -150, 0, 150, 250, 350])
316 | y = rng.choice([-350, -250, -150, 0, 150, 250, 350])
317 | if x == 0 and y == 0:
318 | continue
319 | sprite.pos[0] += x * spacing
320 | sprite.pos[1] += y * spacing
321 | newsect = self.GetContainingSectorNearby(sprite.sectnum, sprite.pos)
322 | if newsect is not None:
323 | sprite.sectnum = newsect
324 | self.spoilerlog.AddSprite(spritetype, sprite)
325 | return sprite
326 | return None
327 |
328 | def SwapAllSprites(self, rng, toSwap, spritetype:str):
329 | for a in range(len(toSwap)):
330 | b = rng.randrange(0, len(toSwap))
331 | if a == b:
332 | continue
333 | a = toSwap[a]
334 | b = toSwap[b]
335 | self.SwapSprites(spritetype, a, b)
336 |
337 | def DupeSprites(self, rng: random.Random, items: list, rate: float, spacing: float, possibleReplacements:dict, replacementChance:float, spritetype: str):
338 | for sprite in items.copy():
339 | if rng.random() > rate:
340 | continue
341 | newsprite = self.DupeSprite(rng, sprite, spacing, possibleReplacements, replacementChance, spritetype)
342 | if newsprite:
343 | items.append(newsprite)
344 |
345 | def ReduceSprites(self, rng: random.Random, items: list, rate: float, spritetype: str):
346 | for i in range(len(items)-1, -1, -1):
347 | if rng.random() > rate:
348 | continue
349 | self.spoilerlog.DelSprite(spritetype, items[i])
350 | items[i] = items[-1]
351 | items.pop()
352 |
353 | def RandomizeTriggers(self, rng: random.Random, sprites: list, triggerSettings: dict) -> None:
354 | if not triggerSettings:
355 | return
356 | sprite:Sprite
357 | for sprite in sprites:
358 | settings = triggerSettings.get(sprite.picnum)
359 | if not settings:
360 | continue
361 | if sprite.hightag in settings.get('not_hightags', []):
362 | continue
363 | hightags = settings.get('hightags')
364 | if hightags:
365 | sprite.hightag = rng.choice([*hightags, sprite.hightag])
366 | self.spoilerlog.SpriteChangedTag('hightag', sprite, sprite.hightag)
367 | lowtags = settings.get('lowtags')
368 | if lowtags:
369 | sprite.lowtag = rng.choice([*lowtags, sprite.lowtag])
370 | self.spoilerlog.SpriteChangedTag('lowtag', sprite, sprite.lowtag)
371 |
372 | def AddSprite(self, rng: random.Random, add: dict) -> None:
373 | # keep up to date with CreateSpritePacker
374 | add = {
375 | 'picnum': rng.choice(add['choices']),
376 | 'cstat': 0,
377 | 'shade': 0,
378 | 'palette': 0,
379 | 'clipdist': 32,
380 | 'filler': 0,
381 | 'texcoords': [32,32,0,0],
382 | 'statnum': 0,
383 | 'angle': 1536,
384 | 'owner': -1,
385 | 'velocity': [0,0,0],
386 | 'lowtag': 0,
387 | 'hightag': 0,
388 | 'extra': -1,
389 | 'length': self.SPRITE_SIZE,
390 | **add.copy()
391 | }
392 | del add['choices']
393 |
394 | sprite = Sprite(add)
395 | self.AppendSprite(sprite)
396 | spritetype = self.GetSpriteType(sprite)
397 | self.spoilerlog.AddSprite(spritetype, sprite)
398 |
399 |
400 | def MirrorMap(self):
401 | # TODO, need to figure out re-ordering of walls, they need to be counterclockwise
402 | # probably need to compare coordinates and do some sorting
403 | # actually reversing the list might be good enough, maybe the issue is with all the pointer/index dependencies?
404 | self.full_rewrite = True
405 | x=1
406 | y=-1
407 |
408 | self.startPos[0] *= x
409 | self.startPos[1] *= y
410 |
411 | for w in self.walls:
412 | w.pos[0] *= x
413 | w.pos[1] *= y
414 |
415 | for sect in self.sectors:
416 | shapes = [[]]
417 | wallptr = sect.wallptr
418 | numwalls = sect.wallnum
419 | for i in range(wallptr, wallptr + numwalls):
420 | shapes[-1].append(i)
421 | if self.walls[i].next_wall != -1:
422 | shapes.append([])
423 |
424 | for shape in shapes:
425 | #rev = shape.copy()
426 | #rev.reverse()
427 | rev = MirrorList(shape)
428 | for a, b in zip(shape, rev):
429 | if a >= b:
430 | break
431 | walla:Wall = self.walls[a]
432 | wallb:Wall = self.walls[b]
433 |
434 | next_wall_a = walla.next_wall
435 | next_sector_wall_a = walla.next_sector_wall
436 | next_sector_a = walla.next_sector
437 |
438 | next_wall_b = wallb.next_wall
439 | next_sector_wall_b = wallb.next_sector_wall
440 | next_sector_b = wallb.next_sector
441 |
442 | walla.next_wall = next_wall_b
443 | walla.next_sector_wall = next_sector_wall_b
444 | walla.next_sector = next_sector_b
445 |
446 | wallb.next_wall = next_wall_a
447 | wallb.next_sector_wall = next_sector_wall_a
448 | wallb.next_sector = next_sector_a
449 |
450 | self.walls[a] = wallb
451 | self.walls[b] = walla
452 |
453 | # need to fix all the references to these points...
454 |
455 | for s in self.sprites:
456 | s.pos[0] *= x
457 | s.pos[1] *= y
458 |
459 | def AppendSector(self, sector: Sector) -> None:
460 | self.sectors.append(sector)
461 |
462 | def AppendWall(self, wall: Wall) -> None:
463 | self.walls.append(wall)
464 |
465 | def BasicAppendSprite(self, sprite: Sprite) -> None:
466 | cstat = CStat(sprite.cstat)
467 | if self.IsItem(sprite, cstat):
468 | self.items.append(sprite)
469 | else:
470 | self.other_sprites.append(sprite)
471 |
472 | def AppendSpriteId(self, sprite: Sprite) -> None:
473 | if sprite.picnum in self.gameSettings.swappableItems:
474 | self.items.append(sprite)
475 | elif sprite.picnum in self.gameSettings.triggers:
476 | self.triggers.append(sprite)
477 | elif sprite.picnum in self.gameSettings.swappableEnemies and not CStat(sprite.cstat).invisible:
478 | self.enemies.append(sprite)
479 | else:
480 | self.other_sprites.append(sprite)
481 |
482 | def AppendSpriteLowtag(self, sprite: Sprite) -> None:
483 | if sprite.lowtag in self.gameSettings.swappableItems:
484 | self.items.append(sprite)
485 | elif sprite.lowtag in self.gameSettings.triggers:
486 | self.triggers.append(sprite)
487 | elif sprite.lowtag in self.gameSettings.swappableEnemies and not CStat(sprite.cstat).invisible:
488 | self.enemies.append(sprite)
489 | else:
490 | self.other_sprites.append(sprite)
491 |
492 | def BasicGetSpriteType(self, sprite:Sprite) -> str:
493 | cstat = CStat(sprite.cstat)
494 | if self.IsItem(sprite, cstat):
495 | return 'item'
496 | else:
497 | return 'other'
498 |
499 | def GetSpriteTypeId(self, sprite:Sprite) -> str:
500 | if sprite.picnum in self.gameSettings.swappableItems:
501 | return 'item'
502 | elif sprite.picnum in self.gameSettings.triggers:
503 | return 'trigger'
504 | elif sprite.picnum in self.gameSettings.swappableEnemies and not CStat(sprite.cstat).invisible:
505 | return 'enemy'
506 | else:
507 | return 'other'
508 |
509 | def GetSpriteTypeLowtag(self, sprite:Sprite) -> str:
510 | if sprite.lowtag in self.gameSettings.swappableItems:
511 | return 'item'
512 | elif sprite.lowtag in self.gameSettings.triggers:
513 | return 'trigger'
514 | elif sprite.lowtag in self.gameSettings.swappableEnemies and not CStat(sprite.cstat).invisible:
515 | return 'enemy'
516 | else:
517 | return 'other'
518 |
519 | def GetSector(self, pos) -> Sector:
520 | data = self.data[pos:pos + self.SECTOR_SIZE]
521 |
522 | if self.crypt and self.version == 7:
523 | data = MapCrypt(data, self.mapRevision * self.SECTOR_SIZE)
524 |
525 | sector = Sector(self.sectorPacker.unpack(data))
526 | sector.length = self.SECTOR_SIZE
527 | if sector.extra > 0:
528 | pos += self.SECTOR_SIZE
529 | sector.extraData = self.data[pos:pos + self.x_sector_size]
530 | sector.length += self.x_sector_size
531 | return sector
532 |
533 | def GetWall(self, pos) -> Wall:
534 | data = self.data[pos:pos + self.WALL_SIZE]
535 |
536 | if self.crypt and self.version == 7:
537 | data = MapCrypt(data, (self.mapRevision * self.SECTOR_SIZE) | 0x7474614d)
538 |
539 | wall = Wall(self.wallPacker.unpack(data))
540 | wall.length = self.WALL_SIZE
541 | if wall.extra > 0:
542 | pos += self.WALL_SIZE
543 | wall.extraData = self.data[pos:pos + self.x_wall_size]
544 | wall.length += self.x_wall_size
545 | return wall
546 |
547 | def GetSprite(self, pos) -> Sprite:
548 | data = self.data[pos:pos + self.SPRITE_SIZE]
549 |
550 | if self.crypt and self.version == 7:
551 | data = MapCrypt(data, (self.mapRevision * self.SPRITE_SIZE) | 0x7474614d)
552 |
553 | sprite = Sprite(self.spritePacker.unpack(data))
554 | sprite.length = self.SPRITE_SIZE
555 | sprite.extraData = None
556 | if sprite.extra > 0:
557 | pos += self.SPRITE_SIZE
558 | sprite.extraData = self.data[pos:pos + self.x_sprite_size]
559 | sprite.length += self.x_sprite_size
560 | return sprite
561 |
562 | @abc.abstractmethod
563 | def CreateHeaderPacker(self):
564 | return
565 |
566 | @abc.abstractmethod
567 | def CreateSectorPacker(self):
568 | # keep AddSector up to date with this
569 | return
570 |
571 | @abc.abstractmethod
572 | def CreateWallPacker(self):
573 | # keep AddWall up to date with this
574 | return
575 |
576 | @abc.abstractmethod
577 | def CreateSpritePacker(self):
578 | # keep AddSprite up to date with this
579 | return
580 |
581 | def ReadHeaders(self) -> int:
582 | self.__dict__.update(self.headerPacker.unpack(self.data[:self.HEADER_SIZE]))
583 | return self.HEADER_SIZE
584 |
585 | def WriteHeaders(self) -> int:
586 | # TODO: Create header object
587 | newdata = self.headerPacker.pack(self.__dict__)
588 | self.data.extend(newdata)
589 | return len(newdata)
590 |
591 | def ReadNumSectors(self, start) -> int:
592 | stop = start + 2
593 | (self.num_sectors,) = struct.unpack(' int:
597 | new_data = struct.pack(' int:
602 | stop = start + 2
603 | (self.num_walls, ) = struct.unpack(' int:
607 | new_data = struct.pack(' int:
612 | stop = start + 2
613 | (self.num_sprites, ) = struct.unpack(' int:
617 | new_data = struct.pack(' int:
622 | GetSector = self.GetSector
623 | AppendSector = self.AppendSector
624 | for i in range(self.num_sectors):
625 | sector = GetSector(pos)
626 | AppendSector(sector)
627 | pos += sector.length
628 | return pos
629 |
630 | def WriteSector(self, sector: Sector):
631 | newdata = self.sectorPacker.pack(sector.__dict__)
632 |
633 | if self.crypt and self.version == 7:
634 | newdata = bytearray(newdata)
635 | newdata = MapCrypt(newdata, self.mapRevision * self.SECTOR_SIZE)
636 |
637 | if sector.extra > 0:
638 | newdata += sector.extraData
639 | self.data.extend(newdata)
640 |
641 | def WriteSectors(self, pos) -> int:
642 | WriteSector = self.WriteSector
643 | for sector in self.sectors:
644 | WriteSector(sector)
645 | pos += sector.length
646 | return pos
647 |
648 | def ReadWalls(self, pos) -> int:
649 | GetWall = self.GetWall
650 | AppendWall = self.AppendWall
651 | for i in range(self.num_walls):
652 | wall = GetWall(pos)
653 | AppendWall(wall)
654 | pos += wall.length
655 | return pos
656 |
657 | def WriteWall(self, wall: Wall):
658 | newdata = self.wallPacker.pack(wall.__dict__)
659 |
660 | if self.crypt and self.version == 7:
661 | newdata = bytearray(newdata)
662 | newdata = MapCrypt(newdata, (self.mapRevision * self.SECTOR_SIZE) | 0x7474614d)
663 |
664 | if wall.extra > 0:
665 | newdata += wall.extraData
666 | self.data.extend(newdata)
667 |
668 | def WriteWalls(self, pos) -> int:
669 | for wall in self.walls:
670 | self.WriteWall(wall)
671 | pos += wall.length
672 | return pos
673 |
674 | def ReadSprites(self, pos) -> int:
675 | GetSprite = self.GetSprite
676 | AppendSprite = self.AppendSprite
677 | for i in range(self.num_sprites):
678 | sprite = GetSprite(pos)
679 | AppendSprite(sprite)
680 | pos += sprite.length
681 | return pos
682 |
683 | def WriteSprite(self, sprite: Sprite):
684 | newdata = self.spritePacker.pack(sprite.__dict__)
685 |
686 | newdata = bytearray(newdata)
687 | if self.crypt and self.version == 7:
688 | newdata = MapCrypt(newdata, (self.mapRevision * self.SPRITE_SIZE) | 0x7474614d)
689 |
690 | if sprite.extra > 0:
691 | newdata.extend(sprite.extraData)
692 | self.data.extend(newdata)
693 |
694 | def WriteSprites(self, pos) -> int:
695 | WriteSprite = self.WriteSprite
696 | for sprite in self.sprites:
697 | WriteSprite(sprite)
698 | pos += sprite.length
699 | return pos
700 |
701 | @abc.abstractmethod
702 | def ReadData(self):
703 | return
704 |
705 | @abc.abstractmethod
706 | def WriteData(self):
707 | return
708 |
709 | def GetSectorInfo(self, sector:int) -> Sector:
710 | if sector in self.sectorCache:
711 | return self.sectorCache[sector]
712 |
713 | assert sector >= 0
714 | assert sector < len(self.sectors)
715 |
716 | wallptr = self.sectors[sector].wallptr
717 | numwalls = self.sectors[sector].wallnum
718 |
719 | walls = {}
720 | nearbySectors = set()
721 | shapes = [[]]
722 | for i in range(numwalls):
723 | w = self.walls[wallptr]
724 | nearbySectors.add(w.next_sector)
725 | walls[wallptr] = w.pos
726 | shapes[-1].append(w.pos)
727 | if w.next_wall in walls:
728 | shapes.append([])
729 | wallptr += 1
730 |
731 | shapes.pop(-1)
732 | nearbySectors.discard(-1)
733 | nearbySectors.discard(sector)
734 | sect = Sector({'walls': walls, 'nearbySectors': nearbySectors, 'shapes': shapes})
735 | self.sectorCache[sector] = sect
736 | return sect
737 |
738 | def GetContainingSectorNearby(self, sector:int, point) -> Union[int,None]:
739 | sectorInfo:Sector = self.GetSectorInfo(sector)
740 | if PointIsInSector(sectorInfo, point):
741 | return sector
742 | for sect2 in sectorInfo.nearbySectors:
743 | sectorInfo2:Sector = self.GetSectorInfo(sect2)
744 | if PointIsInSector(sectorInfo2, point):
745 | return sect2
746 | return None
747 |
748 |
749 |
750 | def PointIsInSector(sect:Sector, testpos:list) -> bool:
751 | intersects = 0
752 | for shape in sect.shapes:
753 | intersects = PointIsInShape(shape, testpos, intersects)
754 | return (intersects%2)==1
755 |
756 |
757 | def PointIsInShape(walls, p, intersects) -> int:
758 | # https://stackoverflow.com/a/2922778
759 | i=0
760 | n=len(walls)
761 | j=n-1
762 | while i < n:
763 | # ensure the wall straddles the point on the Y axis
764 | if ((walls[i][1] > p[1]) != (walls[j][1] > p[1])):
765 | # check slope?
766 | wallXSize = walls[j][0]-walls[i][0]
767 | wallYSize = walls[j][1]-walls[i][1]
768 | pointYDist = p[1]-walls[i][1]
769 | if p[0] < wallXSize * pointYDist / wallYSize + walls[i][0]:
770 | intersects += 1
771 | j=i
772 | i+=1
773 | return intersects
774 |
775 |
776 | def MapCrypt(data:bytearray, key:int) -> bytearray:
777 | # reversible/symmetrical
778 | for i in range(len(data)):
779 | data[i] = data[i] ^ (key & 0xff)
780 | key += 1
781 | return data
782 |
783 | def MirrorList(l):
784 | # ensure proper vertex order
785 | return l[0:1] + l[-1:0:-1]
786 |
--------------------------------------------------------------------------------
/LICENSE:
--------------------------------------------------------------------------------
1 | GNU AFFERO GENERAL PUBLIC LICENSE
2 | Version 3, 19 November 2007
3 |
4 | Copyright (C) 2007 Free Software Foundation, Inc.
5 | Everyone is permitted to copy and distribute verbatim copies
6 | of this license document, but changing it is not allowed.
7 |
8 | Preamble
9 |
10 | The GNU Affero General Public License is a free, copyleft license for
11 | software and other kinds of works, specifically designed to ensure
12 | cooperation with the community in the case of network server software.
13 |
14 | The licenses for most software and other practical works are designed
15 | to take away your freedom to share and change the works. By contrast,
16 | our General Public Licenses are intended to guarantee your freedom to
17 | share and change all versions of a program--to make sure it remains free
18 | software for all its users.
19 |
20 | When we speak of free software, we are referring to freedom, not
21 | price. Our General Public Licenses are designed to make sure that you
22 | have the freedom to distribute copies of free software (and charge for
23 | them if you wish), that you receive source code or can get it if you
24 | want it, that you can change the software or use pieces of it in new
25 | free programs, and that you know you can do these things.
26 |
27 | Developers that use our General Public Licenses protect your rights
28 | with two steps: (1) assert copyright on the software, and (2) offer
29 | you this License which gives you legal permission to copy, distribute
30 | and/or modify the software.
31 |
32 | A secondary benefit of defending all users' freedom is that
33 | improvements made in alternate versions of the program, if they
34 | receive widespread use, become available for other developers to
35 | incorporate. Many developers of free software are heartened and
36 | encouraged by the resulting cooperation. However, in the case of
37 | software used on network servers, this result may fail to come about.
38 | The GNU General Public License permits making a modified version and
39 | letting the public access it on a server without ever releasing its
40 | source code to the public.
41 |
42 | The GNU Affero General Public License is designed specifically to
43 | ensure that, in such cases, the modified source code becomes available
44 | to the community. It requires the operator of a network server to
45 | provide the source code of the modified version running there to the
46 | users of that server. Therefore, public use of a modified version, on
47 | a publicly accessible server, gives the public access to the source
48 | code of the modified version.
49 |
50 | An older license, called the Affero General Public License and
51 | published by Affero, was designed to accomplish similar goals. This is
52 | a different license, not a version of the Affero GPL, but Affero has
53 | released a new version of the Affero GPL which permits relicensing under
54 | this license.
55 |
56 | The precise terms and conditions for copying, distribution and
57 | modification follow.
58 |
59 | TERMS AND CONDITIONS
60 |
61 | 0. Definitions.
62 |
63 | "This License" refers to version 3 of the GNU Affero General Public License.
64 |
65 | "Copyright" also means copyright-like laws that apply to other kinds of
66 | works, such as semiconductor masks.
67 |
68 | "The Program" refers to any copyrightable work licensed under this
69 | License. Each licensee is addressed as "you". "Licensees" and
70 | "recipients" may be individuals or organizations.
71 |
72 | To "modify" a work means to copy from or adapt all or part of the work
73 | in a fashion requiring copyright permission, other than the making of an
74 | exact copy. The resulting work is called a "modified version" of the
75 | earlier work or a work "based on" the earlier work.
76 |
77 | A "covered work" means either the unmodified Program or a work based
78 | on the Program.
79 |
80 | To "propagate" a work means to do anything with it that, without
81 | permission, would make you directly or secondarily liable for
82 | infringement under applicable copyright law, except executing it on a
83 | computer or modifying a private copy. Propagation includes copying,
84 | distribution (with or without modification), making available to the
85 | public, and in some countries other activities as well.
86 |
87 | To "convey" a work means any kind of propagation that enables other
88 | parties to make or receive copies. Mere interaction with a user through
89 | a computer network, with no transfer of a copy, is not conveying.
90 |
91 | An interactive user interface displays "Appropriate Legal Notices"
92 | to the extent that it includes a convenient and prominently visible
93 | feature that (1) displays an appropriate copyright notice, and (2)
94 | tells the user that there is no warranty for the work (except to the
95 | extent that warranties are provided), that licensees may convey the
96 | work under this License, and how to view a copy of this License. If
97 | the interface presents a list of user commands or options, such as a
98 | menu, a prominent item in the list meets this criterion.
99 |
100 | 1. Source Code.
101 |
102 | The "source code" for a work means the preferred form of the work
103 | for making modifications to it. "Object code" means any non-source
104 | form of a work.
105 |
106 | A "Standard Interface" means an interface that either is an official
107 | standard defined by a recognized standards body, or, in the case of
108 | interfaces specified for a particular programming language, one that
109 | is widely used among developers working in that language.
110 |
111 | The "System Libraries" of an executable work include anything, other
112 | than the work as a whole, that (a) is included in the normal form of
113 | packaging a Major Component, but which is not part of that Major
114 | Component, and (b) serves only to enable use of the work with that
115 | Major Component, or to implement a Standard Interface for which an
116 | implementation is available to the public in source code form. A
117 | "Major Component", in this context, means a major essential component
118 | (kernel, window system, and so on) of the specific operating system
119 | (if any) on which the executable work runs, or a compiler used to
120 | produce the work, or an object code interpreter used to run it.
121 |
122 | The "Corresponding Source" for a work in object code form means all
123 | the source code needed to generate, install, and (for an executable
124 | work) run the object code and to modify the work, including scripts to
125 | control those activities. However, it does not include the work's
126 | System Libraries, or general-purpose tools or generally available free
127 | programs which are used unmodified in performing those activities but
128 | which are not part of the work. For example, Corresponding Source
129 | includes interface definition files associated with source files for
130 | the work, and the source code for shared libraries and dynamically
131 | linked subprograms that the work is specifically designed to require,
132 | such as by intimate data communication or control flow between those
133 | subprograms and other parts of the work.
134 |
135 | The Corresponding Source need not include anything that users
136 | can regenerate automatically from other parts of the Corresponding
137 | Source.
138 |
139 | The Corresponding Source for a work in source code form is that
140 | same work.
141 |
142 | 2. Basic Permissions.
143 |
144 | All rights granted under this License are granted for the term of
145 | copyright on the Program, and are irrevocable provided the stated
146 | conditions are met. This License explicitly affirms your unlimited
147 | permission to run the unmodified Program. The output from running a
148 | covered work is covered by this License only if the output, given its
149 | content, constitutes a covered work. This License acknowledges your
150 | rights of fair use or other equivalent, as provided by copyright law.
151 |
152 | You may make, run and propagate covered works that you do not
153 | convey, without conditions so long as your license otherwise remains
154 | in force. You may convey covered works to others for the sole purpose
155 | of having them make modifications exclusively for you, or provide you
156 | with facilities for running those works, provided that you comply with
157 | the terms of this License in conveying all material for which you do
158 | not control copyright. Those thus making or running the covered works
159 | for you must do so exclusively on your behalf, under your direction
160 | and control, on terms that prohibit them from making any copies of
161 | your copyrighted material outside their relationship with you.
162 |
163 | Conveying under any other circumstances is permitted solely under
164 | the conditions stated below. Sublicensing is not allowed; section 10
165 | makes it unnecessary.
166 |
167 | 3. Protecting Users' Legal Rights From Anti-Circumvention Law.
168 |
169 | No covered work shall be deemed part of an effective technological
170 | measure under any applicable law fulfilling obligations under article
171 | 11 of the WIPO copyright treaty adopted on 20 December 1996, or
172 | similar laws prohibiting or restricting circumvention of such
173 | measures.
174 |
175 | When you convey a covered work, you waive any legal power to forbid
176 | circumvention of technological measures to the extent such circumvention
177 | is effected by exercising rights under this License with respect to
178 | the covered work, and you disclaim any intention to limit operation or
179 | modification of the work as a means of enforcing, against the work's
180 | users, your or third parties' legal rights to forbid circumvention of
181 | technological measures.
182 |
183 | 4. Conveying Verbatim Copies.
184 |
185 | You may convey verbatim copies of the Program's source code as you
186 | receive it, in any medium, provided that you conspicuously and
187 | appropriately publish on each copy an appropriate copyright notice;
188 | keep intact all notices stating that this License and any
189 | non-permissive terms added in accord with section 7 apply to the code;
190 | keep intact all notices of the absence of any warranty; and give all
191 | recipients a copy of this License along with the Program.
192 |
193 | You may charge any price or no price for each copy that you convey,
194 | and you may offer support or warranty protection for a fee.
195 |
196 | 5. Conveying Modified Source Versions.
197 |
198 | You may convey a work based on the Program, or the modifications to
199 | produce it from the Program, in the form of source code under the
200 | terms of section 4, provided that you also meet all of these conditions:
201 |
202 | a) The work must carry prominent notices stating that you modified
203 | it, and giving a relevant date.
204 |
205 | b) The work must carry prominent notices stating that it is
206 | released under this License and any conditions added under section
207 | 7. This requirement modifies the requirement in section 4 to
208 | "keep intact all notices".
209 |
210 | c) You must license the entire work, as a whole, under this
211 | License to anyone who comes into possession of a copy. This
212 | License will therefore apply, along with any applicable section 7
213 | additional terms, to the whole of the work, and all its parts,
214 | regardless of how they are packaged. This License gives no
215 | permission to license the work in any other way, but it does not
216 | invalidate such permission if you have separately received it.
217 |
218 | d) If the work has interactive user interfaces, each must display
219 | Appropriate Legal Notices; however, if the Program has interactive
220 | interfaces that do not display Appropriate Legal Notices, your
221 | work need not make them do so.
222 |
223 | A compilation of a covered work with other separate and independent
224 | works, which are not by their nature extensions of the covered work,
225 | and which are not combined with it such as to form a larger program,
226 | in or on a volume of a storage or distribution medium, is called an
227 | "aggregate" if the compilation and its resulting copyright are not
228 | used to limit the access or legal rights of the compilation's users
229 | beyond what the individual works permit. Inclusion of a covered work
230 | in an aggregate does not cause this License to apply to the other
231 | parts of the aggregate.
232 |
233 | 6. Conveying Non-Source Forms.
234 |
235 | You may convey a covered work in object code form under the terms
236 | of sections 4 and 5, provided that you also convey the
237 | machine-readable Corresponding Source under the terms of this License,
238 | in one of these ways:
239 |
240 | a) Convey the object code in, or embodied in, a physical product
241 | (including a physical distribution medium), accompanied by the
242 | Corresponding Source fixed on a durable physical medium
243 | customarily used for software interchange.
244 |
245 | b) Convey the object code in, or embodied in, a physical product
246 | (including a physical distribution medium), accompanied by a
247 | written offer, valid for at least three years and valid for as
248 | long as you offer spare parts or customer support for that product
249 | model, to give anyone who possesses the object code either (1) a
250 | copy of the Corresponding Source for all the software in the
251 | product that is covered by this License, on a durable physical
252 | medium customarily used for software interchange, for a price no
253 | more than your reasonable cost of physically performing this
254 | conveying of source, or (2) access to copy the
255 | Corresponding Source from a network server at no charge.
256 |
257 | c) Convey individual copies of the object code with a copy of the
258 | written offer to provide the Corresponding Source. This
259 | alternative is allowed only occasionally and noncommercially, and
260 | only if you received the object code with such an offer, in accord
261 | with subsection 6b.
262 |
263 | d) Convey the object code by offering access from a designated
264 | place (gratis or for a charge), and offer equivalent access to the
265 | Corresponding Source in the same way through the same place at no
266 | further charge. You need not require recipients to copy the
267 | Corresponding Source along with the object code. If the place to
268 | copy the object code is a network server, the Corresponding Source
269 | may be on a different server (operated by you or a third party)
270 | that supports equivalent copying facilities, provided you maintain
271 | clear directions next to the object code saying where to find the
272 | Corresponding Source. Regardless of what server hosts the
273 | Corresponding Source, you remain obligated to ensure that it is
274 | available for as long as needed to satisfy these requirements.
275 |
276 | e) Convey the object code using peer-to-peer transmission, provided
277 | you inform other peers where the object code and Corresponding
278 | Source of the work are being offered to the general public at no
279 | charge under subsection 6d.
280 |
281 | A separable portion of the object code, whose source code is excluded
282 | from the Corresponding Source as a System Library, need not be
283 | included in conveying the object code work.
284 |
285 | A "User Product" is either (1) a "consumer product", which means any
286 | tangible personal property which is normally used for personal, family,
287 | or household purposes, or (2) anything designed or sold for incorporation
288 | into a dwelling. In determining whether a product is a consumer product,
289 | doubtful cases shall be resolved in favor of coverage. For a particular
290 | product received by a particular user, "normally used" refers to a
291 | typical or common use of that class of product, regardless of the status
292 | of the particular user or of the way in which the particular user
293 | actually uses, or expects or is expected to use, the product. A product
294 | is a consumer product regardless of whether the product has substantial
295 | commercial, industrial or non-consumer uses, unless such uses represent
296 | the only significant mode of use of the product.
297 |
298 | "Installation Information" for a User Product means any methods,
299 | procedures, authorization keys, or other information required to install
300 | and execute modified versions of a covered work in that User Product from
301 | a modified version of its Corresponding Source. The information must
302 | suffice to ensure that the continued functioning of the modified object
303 | code is in no case prevented or interfered with solely because
304 | modification has been made.
305 |
306 | If you convey an object code work under this section in, or with, or
307 | specifically for use in, a User Product, and the conveying occurs as
308 | part of a transaction in which the right of possession and use of the
309 | User Product is transferred to the recipient in perpetuity or for a
310 | fixed term (regardless of how the transaction is characterized), the
311 | Corresponding Source conveyed under this section must be accompanied
312 | by the Installation Information. But this requirement does not apply
313 | if neither you nor any third party retains the ability to install
314 | modified object code on the User Product (for example, the work has
315 | been installed in ROM).
316 |
317 | The requirement to provide Installation Information does not include a
318 | requirement to continue to provide support service, warranty, or updates
319 | for a work that has been modified or installed by the recipient, or for
320 | the User Product in which it has been modified or installed. Access to a
321 | network may be denied when the modification itself materially and
322 | adversely affects the operation of the network or violates the rules and
323 | protocols for communication across the network.
324 |
325 | Corresponding Source conveyed, and Installation Information provided,
326 | in accord with this section must be in a format that is publicly
327 | documented (and with an implementation available to the public in
328 | source code form), and must require no special password or key for
329 | unpacking, reading or copying.
330 |
331 | 7. Additional Terms.
332 |
333 | "Additional permissions" are terms that supplement the terms of this
334 | License by making exceptions from one or more of its conditions.
335 | Additional permissions that are applicable to the entire Program shall
336 | be treated as though they were included in this License, to the extent
337 | that they are valid under applicable law. If additional permissions
338 | apply only to part of the Program, that part may be used separately
339 | under those permissions, but the entire Program remains governed by
340 | this License without regard to the additional permissions.
341 |
342 | When you convey a copy of a covered work, you may at your option
343 | remove any additional permissions from that copy, or from any part of
344 | it. (Additional permissions may be written to require their own
345 | removal in certain cases when you modify the work.) You may place
346 | additional permissions on material, added by you to a covered work,
347 | for which you have or can give appropriate copyright permission.
348 |
349 | Notwithstanding any other provision of this License, for material you
350 | add to a covered work, you may (if authorized by the copyright holders of
351 | that material) supplement the terms of this License with terms:
352 |
353 | a) Disclaiming warranty or limiting liability differently from the
354 | terms of sections 15 and 16 of this License; or
355 |
356 | b) Requiring preservation of specified reasonable legal notices or
357 | author attributions in that material or in the Appropriate Legal
358 | Notices displayed by works containing it; or
359 |
360 | c) Prohibiting misrepresentation of the origin of that material, or
361 | requiring that modified versions of such material be marked in
362 | reasonable ways as different from the original version; or
363 |
364 | d) Limiting the use for publicity purposes of names of licensors or
365 | authors of the material; or
366 |
367 | e) Declining to grant rights under trademark law for use of some
368 | trade names, trademarks, or service marks; or
369 |
370 | f) Requiring indemnification of licensors and authors of that
371 | material by anyone who conveys the material (or modified versions of
372 | it) with contractual assumptions of liability to the recipient, for
373 | any liability that these contractual assumptions directly impose on
374 | those licensors and authors.
375 |
376 | All other non-permissive additional terms are considered "further
377 | restrictions" within the meaning of section 10. If the Program as you
378 | received it, or any part of it, contains a notice stating that it is
379 | governed by this License along with a term that is a further
380 | restriction, you may remove that term. If a license document contains
381 | a further restriction but permits relicensing or conveying under this
382 | License, you may add to a covered work material governed by the terms
383 | of that license document, provided that the further restriction does
384 | not survive such relicensing or conveying.
385 |
386 | If you add terms to a covered work in accord with this section, you
387 | must place, in the relevant source files, a statement of the
388 | additional terms that apply to those files, or a notice indicating
389 | where to find the applicable terms.
390 |
391 | Additional terms, permissive or non-permissive, may be stated in the
392 | form of a separately written license, or stated as exceptions;
393 | the above requirements apply either way.
394 |
395 | 8. Termination.
396 |
397 | You may not propagate or modify a covered work except as expressly
398 | provided under this License. Any attempt otherwise to propagate or
399 | modify it is void, and will automatically terminate your rights under
400 | this License (including any patent licenses granted under the third
401 | paragraph of section 11).
402 |
403 | However, if you cease all violation of this License, then your
404 | license from a particular copyright holder is reinstated (a)
405 | provisionally, unless and until the copyright holder explicitly and
406 | finally terminates your license, and (b) permanently, if the copyright
407 | holder fails to notify you of the violation by some reasonable means
408 | prior to 60 days after the cessation.
409 |
410 | Moreover, your license from a particular copyright holder is
411 | reinstated permanently if the copyright holder notifies you of the
412 | violation by some reasonable means, this is the first time you have
413 | received notice of violation of this License (for any work) from that
414 | copyright holder, and you cure the violation prior to 30 days after
415 | your receipt of the notice.
416 |
417 | Termination of your rights under this section does not terminate the
418 | licenses of parties who have received copies or rights from you under
419 | this License. If your rights have been terminated and not permanently
420 | reinstated, you do not qualify to receive new licenses for the same
421 | material under section 10.
422 |
423 | 9. Acceptance Not Required for Having Copies.
424 |
425 | You are not required to accept this License in order to receive or
426 | run a copy of the Program. Ancillary propagation of a covered work
427 | occurring solely as a consequence of using peer-to-peer transmission
428 | to receive a copy likewise does not require acceptance. However,
429 | nothing other than this License grants you permission to propagate or
430 | modify any covered work. These actions infringe copyright if you do
431 | not accept this License. Therefore, by modifying or propagating a
432 | covered work, you indicate your acceptance of this License to do so.
433 |
434 | 10. Automatic Licensing of Downstream Recipients.
435 |
436 | Each time you convey a covered work, the recipient automatically
437 | receives a license from the original licensors, to run, modify and
438 | propagate that work, subject to this License. You are not responsible
439 | for enforcing compliance by third parties with this License.
440 |
441 | An "entity transaction" is a transaction transferring control of an
442 | organization, or substantially all assets of one, or subdividing an
443 | organization, or merging organizations. If propagation of a covered
444 | work results from an entity transaction, each party to that
445 | transaction who receives a copy of the work also receives whatever
446 | licenses to the work the party's predecessor in interest had or could
447 | give under the previous paragraph, plus a right to possession of the
448 | Corresponding Source of the work from the predecessor in interest, if
449 | the predecessor has it or can get it with reasonable efforts.
450 |
451 | You may not impose any further restrictions on the exercise of the
452 | rights granted or affirmed under this License. For example, you may
453 | not impose a license fee, royalty, or other charge for exercise of
454 | rights granted under this License, and you may not initiate litigation
455 | (including a cross-claim or counterclaim in a lawsuit) alleging that
456 | any patent claim is infringed by making, using, selling, offering for
457 | sale, or importing the Program or any portion of it.
458 |
459 | 11. Patents.
460 |
461 | A "contributor" is a copyright holder who authorizes use under this
462 | License of the Program or a work on which the Program is based. The
463 | work thus licensed is called the contributor's "contributor version".
464 |
465 | A contributor's "essential patent claims" are all patent claims
466 | owned or controlled by the contributor, whether already acquired or
467 | hereafter acquired, that would be infringed by some manner, permitted
468 | by this License, of making, using, or selling its contributor version,
469 | but do not include claims that would be infringed only as a
470 | consequence of further modification of the contributor version. For
471 | purposes of this definition, "control" includes the right to grant
472 | patent sublicenses in a manner consistent with the requirements of
473 | this License.
474 |
475 | Each contributor grants you a non-exclusive, worldwide, royalty-free
476 | patent license under the contributor's essential patent claims, to
477 | make, use, sell, offer for sale, import and otherwise run, modify and
478 | propagate the contents of its contributor version.
479 |
480 | In the following three paragraphs, a "patent license" is any express
481 | agreement or commitment, however denominated, not to enforce a patent
482 | (such as an express permission to practice a patent or covenant not to
483 | sue for patent infringement). To "grant" such a patent license to a
484 | party means to make such an agreement or commitment not to enforce a
485 | patent against the party.
486 |
487 | If you convey a covered work, knowingly relying on a patent license,
488 | and the Corresponding Source of the work is not available for anyone
489 | to copy, free of charge and under the terms of this License, through a
490 | publicly available network server or other readily accessible means,
491 | then you must either (1) cause the Corresponding Source to be so
492 | available, or (2) arrange to deprive yourself of the benefit of the
493 | patent license for this particular work, or (3) arrange, in a manner
494 | consistent with the requirements of this License, to extend the patent
495 | license to downstream recipients. "Knowingly relying" means you have
496 | actual knowledge that, but for the patent license, your conveying the
497 | covered work in a country, or your recipient's use of the covered work
498 | in a country, would infringe one or more identifiable patents in that
499 | country that you have reason to believe are valid.
500 |
501 | If, pursuant to or in connection with a single transaction or
502 | arrangement, you convey, or propagate by procuring conveyance of, a
503 | covered work, and grant a patent license to some of the parties
504 | receiving the covered work authorizing them to use, propagate, modify
505 | or convey a specific copy of the covered work, then the patent license
506 | you grant is automatically extended to all recipients of the covered
507 | work and works based on it.
508 |
509 | A patent license is "discriminatory" if it does not include within
510 | the scope of its coverage, prohibits the exercise of, or is
511 | conditioned on the non-exercise of one or more of the rights that are
512 | specifically granted under this License. You may not convey a covered
513 | work if you are a party to an arrangement with a third party that is
514 | in the business of distributing software, under which you make payment
515 | to the third party based on the extent of your activity of conveying
516 | the work, and under which the third party grants, to any of the
517 | parties who would receive the covered work from you, a discriminatory
518 | patent license (a) in connection with copies of the covered work
519 | conveyed by you (or copies made from those copies), or (b) primarily
520 | for and in connection with specific products or compilations that
521 | contain the covered work, unless you entered into that arrangement,
522 | or that patent license was granted, prior to 28 March 2007.
523 |
524 | Nothing in this License shall be construed as excluding or limiting
525 | any implied license or other defenses to infringement that may
526 | otherwise be available to you under applicable patent law.
527 |
528 | 12. No Surrender of Others' Freedom.
529 |
530 | If conditions are imposed on you (whether by court order, agreement or
531 | otherwise) that contradict the conditions of this License, they do not
532 | excuse you from the conditions of this License. If you cannot convey a
533 | covered work so as to satisfy simultaneously your obligations under this
534 | License and any other pertinent obligations, then as a consequence you may
535 | not convey it at all. For example, if you agree to terms that obligate you
536 | to collect a royalty for further conveying from those to whom you convey
537 | the Program, the only way you could satisfy both those terms and this
538 | License would be to refrain entirely from conveying the Program.
539 |
540 | 13. Remote Network Interaction; Use with the GNU General Public License.
541 |
542 | Notwithstanding any other provision of this License, if you modify the
543 | Program, your modified version must prominently offer all users
544 | interacting with it remotely through a computer network (if your version
545 | supports such interaction) an opportunity to receive the Corresponding
546 | Source of your version by providing access to the Corresponding Source
547 | from a network server at no charge, through some standard or customary
548 | means of facilitating copying of software. This Corresponding Source
549 | shall include the Corresponding Source for any work covered by version 3
550 | of the GNU General Public License that is incorporated pursuant to the
551 | following paragraph.
552 |
553 | Notwithstanding any other provision of this License, you have
554 | permission to link or combine any covered work with a work licensed
555 | under version 3 of the GNU General Public License into a single
556 | combined work, and to convey the resulting work. The terms of this
557 | License will continue to apply to the part which is the covered work,
558 | but the work with which it is combined will remain governed by version
559 | 3 of the GNU General Public License.
560 |
561 | 14. Revised Versions of this License.
562 |
563 | The Free Software Foundation may publish revised and/or new versions of
564 | the GNU Affero General Public License from time to time. Such new versions
565 | will be similar in spirit to the present version, but may differ in detail to
566 | address new problems or concerns.
567 |
568 | Each version is given a distinguishing version number. If the
569 | Program specifies that a certain numbered version of the GNU Affero General
570 | Public License "or any later version" applies to it, you have the
571 | option of following the terms and conditions either of that numbered
572 | version or of any later version published by the Free Software
573 | Foundation. If the Program does not specify a version number of the
574 | GNU Affero General Public License, you may choose any version ever published
575 | by the Free Software Foundation.
576 |
577 | If the Program specifies that a proxy can decide which future
578 | versions of the GNU Affero General Public License can be used, that proxy's
579 | public statement of acceptance of a version permanently authorizes you
580 | to choose that version for the Program.
581 |
582 | Later license versions may give you additional or different
583 | permissions. However, no additional obligations are imposed on any
584 | author or copyright holder as a result of your choosing to follow a
585 | later version.
586 |
587 | 15. Disclaimer of Warranty.
588 |
589 | THERE IS NO WARRANTY FOR THE PROGRAM, TO THE EXTENT PERMITTED BY
590 | APPLICABLE LAW. EXCEPT WHEN OTHERWISE STATED IN WRITING THE COPYRIGHT
591 | HOLDERS AND/OR OTHER PARTIES PROVIDE THE PROGRAM "AS IS" WITHOUT WARRANTY
592 | OF ANY KIND, EITHER EXPRESSED OR IMPLIED, INCLUDING, BUT NOT LIMITED TO,
593 | THE IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR
594 | PURPOSE. THE ENTIRE RISK AS TO THE QUALITY AND PERFORMANCE OF THE PROGRAM
595 | IS WITH YOU. SHOULD THE PROGRAM PROVE DEFECTIVE, YOU ASSUME THE COST OF
596 | ALL NECESSARY SERVICING, REPAIR OR CORRECTION.
597 |
598 | 16. Limitation of Liability.
599 |
600 | IN NO EVENT UNLESS REQUIRED BY APPLICABLE LAW OR AGREED TO IN WRITING
601 | WILL ANY COPYRIGHT HOLDER, OR ANY OTHER PARTY WHO MODIFIES AND/OR CONVEYS
602 | THE PROGRAM AS PERMITTED ABOVE, BE LIABLE TO YOU FOR DAMAGES, INCLUDING ANY
603 | GENERAL, SPECIAL, INCIDENTAL OR CONSEQUENTIAL DAMAGES ARISING OUT OF THE
604 | USE OR INABILITY TO USE THE PROGRAM (INCLUDING BUT NOT LIMITED TO LOSS OF
605 | DATA OR DATA BEING RENDERED INACCURATE OR LOSSES SUSTAINED BY YOU OR THIRD
606 | PARTIES OR A FAILURE OF THE PROGRAM TO OPERATE WITH ANY OTHER PROGRAMS),
607 | EVEN IF SUCH HOLDER OR OTHER PARTY HAS BEEN ADVISED OF THE POSSIBILITY OF
608 | SUCH DAMAGES.
609 |
610 | 17. Interpretation of Sections 15 and 16.
611 |
612 | If the disclaimer of warranty and limitation of liability provided
613 | above cannot be given local legal effect according to their terms,
614 | reviewing courts shall apply local law that most closely approximates
615 | an absolute waiver of all civil liability in connection with the
616 | Program, unless a warranty or assumption of liability accompanies a
617 | copy of the Program in return for a fee.
618 |
619 | END OF TERMS AND CONDITIONS
620 |
621 | How to Apply These Terms to Your New Programs
622 |
623 | If you develop a new program, and you want it to be of the greatest
624 | possible use to the public, the best way to achieve this is to make it
625 | free software which everyone can redistribute and change under these terms.
626 |
627 | To do so, attach the following notices to the program. It is safest
628 | to attach them to the start of each source file to most effectively
629 | state the exclusion of warranty; and each file should have at least
630 | the "copyright" line and a pointer to where the full notice is found.
631 |
632 |
633 | Copyright (C)
634 |
635 | This program is free software: you can redistribute it and/or modify
636 | it under the terms of the GNU Affero General Public License as published
637 | by the Free Software Foundation, either version 3 of the License, or
638 | (at your option) any later version.
639 |
640 | This program is distributed in the hope that it will be useful,
641 | but WITHOUT ANY WARRANTY; without even the implied warranty of
642 | MERCHANTABILITY or FITNESS FOR A PARTICULAR PURPOSE. See the
643 | GNU Affero General Public License for more details.
644 |
645 | You should have received a copy of the GNU Affero General Public License
646 | along with this program. If not, see .
647 |
648 | Also add information on how to contact you by electronic and paper mail.
649 |
650 | If your software can interact with users remotely through a computer
651 | network, you should also make sure that it provides a way for users to
652 | get its source. For example, if your program is a web application, its
653 | interface could display a "Source" link that leads users to an archive
654 | of the code. There are many ways you could offer source, and different
655 | solutions will be better for different programs; see section 13 for the
656 | specific requirements.
657 |
658 | You should also get your employer (if you work as a programmer) or school,
659 | if any, to sign a "copyright disclaimer" for the program, if necessary.
660 | For more information on this, and how to apply and follow the GNU AGPL, see
661 | .
662 |
--------------------------------------------------------------------------------
 15 |
16 | "Damn, I'm lookin' good!"
17 |
18 |
15 |
16 | "Damn, I'm lookin' good!"
17 |
18 | 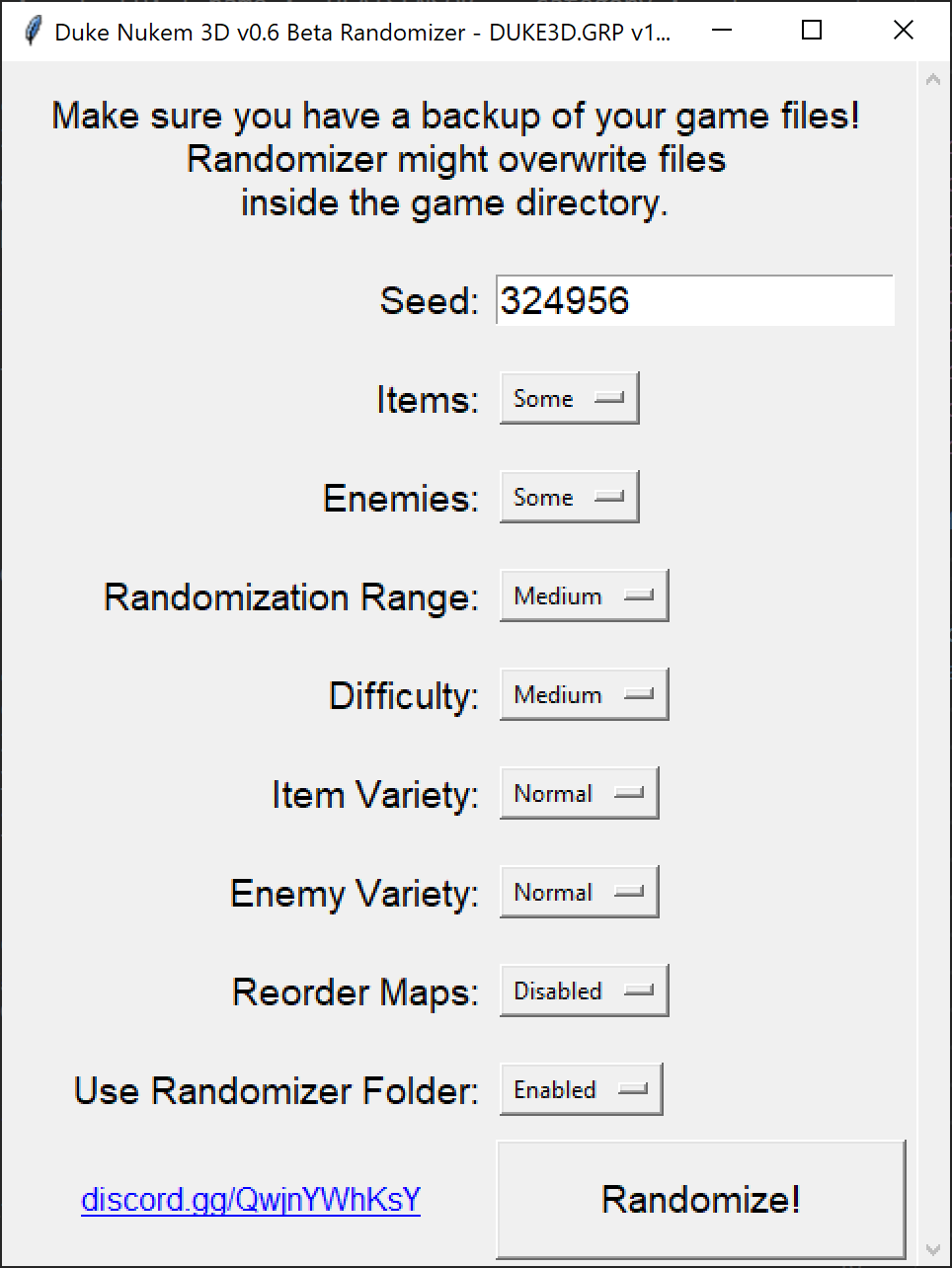 19 |
19 |  8 |
9 | Download build-engine-randomizer.exe from [the Assets section on the Releases page](https://github.com/Die4Ever/build-engine-randomizer/releases). Put eduke32.exe/nblood.exe/etc into the game's folder. Run the Randomizer it, point it to the game's GRP file, choose your settings, and click Randomize! Make sure you have a backup of your game files first just in case. On Windows the Randomizer will generate a bat file for you to play, and then you can just play the game as normal, choose which episode and which difficulty, and it will automatically use the new map files. You do NOT select "USER MAP" in the game menus. If you don't get a bat file, then [see the wiki](https://github.com/Die4Ever/build-engine-randomizer/wiki#how-to-use) for how to play.
10 |
11 | For info on where to get the games and how to run them, [check out our wiki here](https://github.com/Die4Ever/build-engine-randomizer/wiki).
12 |
13 |
8 |
9 | Download build-engine-randomizer.exe from [the Assets section on the Releases page](https://github.com/Die4Ever/build-engine-randomizer/releases). Put eduke32.exe/nblood.exe/etc into the game's folder. Run the Randomizer it, point it to the game's GRP file, choose your settings, and click Randomize! Make sure you have a backup of your game files first just in case. On Windows the Randomizer will generate a bat file for you to play, and then you can just play the game as normal, choose which episode and which difficulty, and it will automatically use the new map files. You do NOT select "USER MAP" in the game menus. If you don't get a bat file, then [see the wiki](https://github.com/Die4Ever/build-engine-randomizer/wiki#how-to-use) for how to play.
10 |
11 | For info on where to get the games and how to run them, [check out our wiki here](https://github.com/Die4Ever/build-engine-randomizer/wiki).
12 |
13 |  14 |
15 | "Damn, I'm lookin' good!"
16 |
17 |
14 |
15 | "Damn, I'm lookin' good!"
16 |
17 |  18 |
19 | Randomizes enemies and items. For games that use CON files (Duke Nukem 3D and Ion Fury so far) it also randomizes values like maximum health and ammo values, and enemy strengths. Also supports randomizing the map order. Be warned that putting every setting to maximum will make the game nearly impossible. I suggest you start with the default settings. Also check out the Randomizer.html file that gets created in the output directory to see what's changed.
20 |
21 | [Join our Discord here!](https://discord.gg/QwjnYWhKsY)
22 |
23 | Also check out [our new website, Mods4Ever.com](https://Mods4Ever.com/)
24 |
--------------------------------------------------------------------------------
/.github/release_template.md:
--------------------------------------------------------------------------------
1 | Build Engine Randomizer currently supports: Duke Nukem 3D, Ion Fury, Shadow Warrior (1997), Blood, and PowerSlave/Exhumed (and maybe more in the future!)
2 |
3 | # Trailer
4 |
5 |
6 |
18 |
19 | Randomizes enemies and items. For games that use CON files (Duke Nukem 3D and Ion Fury so far) it also randomizes values like maximum health and ammo values, and enemy strengths. Also supports randomizing the map order. Be warned that putting every setting to maximum will make the game nearly impossible. I suggest you start with the default settings. Also check out the Randomizer.html file that gets created in the output directory to see what's changed.
20 |
21 | [Join our Discord here!](https://discord.gg/QwjnYWhKsY)
22 |
23 | Also check out [our new website, Mods4Ever.com](https://Mods4Ever.com/)
24 |
--------------------------------------------------------------------------------
/.github/release_template.md:
--------------------------------------------------------------------------------
1 | Build Engine Randomizer currently supports: Duke Nukem 3D, Ion Fury, Shadow Warrior (1997), Blood, and PowerSlave/Exhumed (and maybe more in the future!)
2 |
3 | # Trailer
4 |
5 |
6 |  7 |
8 | Download build-engine-randomizer.exe from the Assets section below. Put eduke32.exe/nblood.exe/etc into the game's folder. Run the Randomizer it, point it to the game's GRP file, choose your settings, and click Randomize! Make sure you have a backup of your game files first just in case. On Windows the Randomizer will generate a bat file for you to play, and then you can just play the game as normal, choose which episode and which difficulty, and it will automatically use the new map files. You do NOT select "USER MAP" in the game menus. If you don't get a bat file, then [see the wiki](https://github.com/Die4Ever/build-engine-randomizer/wiki#how-to-use) for how to play.
9 |
10 | For info on where to get the games and how to run them, [check out our wiki here](https://github.com/Die4Ever/build-engine-randomizer/wiki).
11 |
12 |
7 |
8 | Download build-engine-randomizer.exe from the Assets section below. Put eduke32.exe/nblood.exe/etc into the game's folder. Run the Randomizer it, point it to the game's GRP file, choose your settings, and click Randomize! Make sure you have a backup of your game files first just in case. On Windows the Randomizer will generate a bat file for you to play, and then you can just play the game as normal, choose which episode and which difficulty, and it will automatically use the new map files. You do NOT select "USER MAP" in the game menus. If you don't get a bat file, then [see the wiki](https://github.com/Die4Ever/build-engine-randomizer/wiki#how-to-use) for how to play.
9 |
10 | For info on where to get the games and how to run them, [check out our wiki here](https://github.com/Die4Ever/build-engine-randomizer/wiki).
11 |
12 |  15 |
16 | "Damn, I'm lookin' good!"
17 |
18 |
15 |
16 | "Damn, I'm lookin' good!"
17 |
18 |  19 |
19 |