├── .gitattributes
├── COPYING.TXT
├── README.md
├── _config.yml
├── cve.csv
├── exploitdb.csv
├── logo.png
├── openvas.csv
├── osvdb.csv
├── scipvuldb.csv
├── securityfocus.csv
├── securitytracker.csv
├── utilities
├── docker
│ ├── Dockerfile
│ └── Dockerfile_README.md
└── updater
│ └── updateFiles.sh
├── vulscan.nse
└── xforce.csv
/.gitattributes:
--------------------------------------------------------------------------------
1 | # Auto detect text files and perform LF normalization
2 | * text=auto
3 |
4 | # Custom for Visual Studio
5 | *.cs diff=csharp
6 |
7 | # Standard to msysgit
8 | *.doc diff=astextplain
9 | *.DOC diff=astextplain
10 | *.docx diff=astextplain
11 | *.DOCX diff=astextplain
12 | *.dot diff=astextplain
13 | *.DOT diff=astextplain
14 | *.pdf diff=astextplain
15 | *.PDF diff=astextplain
16 | *.rtf diff=astextplain
17 | *.RTF diff=astextplain
18 |
--------------------------------------------------------------------------------
/COPYING.TXT:
--------------------------------------------------------------------------------
1 | <<<<<<< HEAD
2 | GNU GENERAL PUBLIC LICENSE
3 | Version 3, 29 June 2007
4 |
5 | Copyright (C) 2007 Free Software Foundation, Inc.
6 | Everyone is permitted to copy and distribute verbatim copies
7 | of this license document, but changing it is not allowed.
8 |
9 | Preamble
10 |
11 | The GNU General Public License is a free, copyleft license for
12 | software and other kinds of works.
13 |
14 | The licenses for most software and other practical works are designed
15 | to take away your freedom to share and change the works. By contrast,
16 | the GNU General Public License is intended to guarantee your freedom to
17 | share and change all versions of a program--to make sure it remains free
18 | software for all its users. We, the Free Software Foundation, use the
19 | GNU General Public License for most of our software; it applies also to
20 | any other work released this way by its authors. You can apply it to
21 | your programs, too.
22 |
23 | When we speak of free software, we are referring to freedom, not
24 | price. Our General Public Licenses are designed to make sure that you
25 | have the freedom to distribute copies of free software (and charge for
26 | them if you wish), that you receive source code or can get it if you
27 | want it, that you can change the software or use pieces of it in new
28 | free programs, and that you know you can do these things.
29 |
30 | To protect your rights, we need to prevent others from denying you
31 | these rights or asking you to surrender the rights. Therefore, you have
32 | certain responsibilities if you distribute copies of the software, or if
33 | you modify it: responsibilities to respect the freedom of others.
34 |
35 | For example, if you distribute copies of such a program, whether
36 | gratis or for a fee, you must pass on to the recipients the same
37 | freedoms that you received. You must make sure that they, too, receive
38 | or can get the source code. And you must show them these terms so they
39 | know their rights.
40 |
41 | Developers that use the GNU GPL protect your rights with two steps:
42 | (1) assert copyright on the software, and (2) offer you this License
43 | giving you legal permission to copy, distribute and/or modify it.
44 |
45 | For the developers' and authors' protection, the GPL clearly explains
46 | that there is no warranty for this free software. For both users' and
47 | authors' sake, the GPL requires that modified versions be marked as
48 | changed, so that their problems will not be attributed erroneously to
49 | authors of previous versions.
50 |
51 | Some devices are designed to deny users access to install or run
52 | modified versions of the software inside them, although the manufacturer
53 | can do so. This is fundamentally incompatible with the aim of
54 | protecting users' freedom to change the software. The systematic
55 | pattern of such abuse occurs in the area of products for individuals to
56 | use, which is precisely where it is most unacceptable. Therefore, we
57 | have designed this version of the GPL to prohibit the practice for those
58 | products. If such problems arise substantially in other domains, we
59 | stand ready to extend this provision to those domains in future versions
60 | of the GPL, as needed to protect the freedom of users.
61 |
62 | Finally, every program is threatened constantly by software patents.
63 | States should not allow patents to restrict development and use of
64 | software on general-purpose computers, but in those that do, we wish to
65 | avoid the special danger that patents applied to a free program could
66 | make it effectively proprietary. To prevent this, the GPL assures that
67 | patents cannot be used to render the program non-free.
68 |
69 | The precise terms and conditions for copying, distribution and
70 | modification follow.
71 |
72 | TERMS AND CONDITIONS
73 |
74 | 0. Definitions.
75 |
76 | "This License" refers to version 3 of the GNU General Public License.
77 |
78 | "Copyright" also means copyright-like laws that apply to other kinds of
79 | works, such as semiconductor masks.
80 |
81 | "The Program" refers to any copyrightable work licensed under this
82 | License. Each licensee is addressed as "you". "Licensees" and
83 | "recipients" may be individuals or organizations.
84 |
85 | To "modify" a work means to copy from or adapt all or part of the work
86 | in a fashion requiring copyright permission, other than the making of an
87 | exact copy. The resulting work is called a "modified version" of the
88 | earlier work or a work "based on" the earlier work.
89 |
90 | A "covered work" means either the unmodified Program or a work based
91 | on the Program.
92 |
93 | To "propagate" a work means to do anything with it that, without
94 | permission, would make you directly or secondarily liable for
95 | infringement under applicable copyright law, except executing it on a
96 | computer or modifying a private copy. Propagation includes copying,
97 | distribution (with or without modification), making available to the
98 | public, and in some countries other activities as well.
99 |
100 | To "convey" a work means any kind of propagation that enables other
101 | parties to make or receive copies. Mere interaction with a user through
102 | a computer network, with no transfer of a copy, is not conveying.
103 |
104 | An interactive user interface displays "Appropriate Legal Notices"
105 | to the extent that it includes a convenient and prominently visible
106 | feature that (1) displays an appropriate copyright notice, and (2)
107 | tells the user that there is no warranty for the work (except to the
108 | extent that warranties are provided), that licensees may convey the
109 | work under this License, and how to view a copy of this License. If
110 | the interface presents a list of user commands or options, such as a
111 | menu, a prominent item in the list meets this criterion.
112 |
113 | 1. Source Code.
114 |
115 | The "source code" for a work means the preferred form of the work
116 | for making modifications to it. "Object code" means any non-source
117 | form of a work.
118 |
119 | A "Standard Interface" means an interface that either is an official
120 | standard defined by a recognized standards body, or, in the case of
121 | interfaces specified for a particular programming language, one that
122 | is widely used among developers working in that language.
123 |
124 | The "System Libraries" of an executable work include anything, other
125 | than the work as a whole, that (a) is included in the normal form of
126 | packaging a Major Component, but which is not part of that Major
127 | Component, and (b) serves only to enable use of the work with that
128 | Major Component, or to implement a Standard Interface for which an
129 | implementation is available to the public in source code form. A
130 | "Major Component", in this context, means a major essential component
131 | (kernel, window system, and so on) of the specific operating system
132 | (if any) on which the executable work runs, or a compiler used to
133 | produce the work, or an object code interpreter used to run it.
134 |
135 | The "Corresponding Source" for a work in object code form means all
136 | the source code needed to generate, install, and (for an executable
137 | work) run the object code and to modify the work, including scripts to
138 | control those activities. However, it does not include the work's
139 | System Libraries, or general-purpose tools or generally available free
140 | programs which are used unmodified in performing those activities but
141 | which are not part of the work. For example, Corresponding Source
142 | includes interface definition files associated with source files for
143 | the work, and the source code for shared libraries and dynamically
144 | linked subprograms that the work is specifically designed to require,
145 | such as by intimate data communication or control flow between those
146 | subprograms and other parts of the work.
147 |
148 | The Corresponding Source need not include anything that users
149 | can regenerate automatically from other parts of the Corresponding
150 | Source.
151 |
152 | The Corresponding Source for a work in source code form is that
153 | same work.
154 |
155 | 2. Basic Permissions.
156 |
157 | All rights granted under this License are granted for the term of
158 | copyright on the Program, and are irrevocable provided the stated
159 | conditions are met. This License explicitly affirms your unlimited
160 | permission to run the unmodified Program. The output from running a
161 | covered work is covered by this License only if the output, given its
162 | content, constitutes a covered work. This License acknowledges your
163 | rights of fair use or other equivalent, as provided by copyright law.
164 |
165 | You may make, run and propagate covered works that you do not
166 | convey, without conditions so long as your license otherwise remains
167 | in force. You may convey covered works to others for the sole purpose
168 | of having them make modifications exclusively for you, or provide you
169 | with facilities for running those works, provided that you comply with
170 | the terms of this License in conveying all material for which you do
171 | not control copyright. Those thus making or running the covered works
172 | for you must do so exclusively on your behalf, under your direction
173 | and control, on terms that prohibit them from making any copies of
174 | your copyrighted material outside their relationship with you.
175 |
176 | Conveying under any other circumstances is permitted solely under
177 | the conditions stated below. Sublicensing is not allowed; section 10
178 | makes it unnecessary.
179 |
180 | 3. Protecting Users' Legal Rights From Anti-Circumvention Law.
181 |
182 | No covered work shall be deemed part of an effective technological
183 | measure under any applicable law fulfilling obligations under article
184 | 11 of the WIPO copyright treaty adopted on 20 December 1996, or
185 | similar laws prohibiting or restricting circumvention of such
186 | measures.
187 |
188 | When you convey a covered work, you waive any legal power to forbid
189 | circumvention of technological measures to the extent such circumvention
190 | is effected by exercising rights under this License with respect to
191 | the covered work, and you disclaim any intention to limit operation or
192 | modification of the work as a means of enforcing, against the work's
193 | users, your or third parties' legal rights to forbid circumvention of
194 | technological measures.
195 |
196 | 4. Conveying Verbatim Copies.
197 |
198 | You may convey verbatim copies of the Program's source code as you
199 | receive it, in any medium, provided that you conspicuously and
200 | appropriately publish on each copy an appropriate copyright notice;
201 | keep intact all notices stating that this License and any
202 | non-permissive terms added in accord with section 7 apply to the code;
203 | keep intact all notices of the absence of any warranty; and give all
204 | recipients a copy of this License along with the Program.
205 |
206 | You may charge any price or no price for each copy that you convey,
207 | and you may offer support or warranty protection for a fee.
208 |
209 | 5. Conveying Modified Source Versions.
210 |
211 | You may convey a work based on the Program, or the modifications to
212 | produce it from the Program, in the form of source code under the
213 | terms of section 4, provided that you also meet all of these conditions:
214 |
215 | a) The work must carry prominent notices stating that you modified
216 | it, and giving a relevant date.
217 |
218 | b) The work must carry prominent notices stating that it is
219 | released under this License and any conditions added under section
220 | 7. This requirement modifies the requirement in section 4 to
221 | "keep intact all notices".
222 |
223 | c) You must license the entire work, as a whole, under this
224 | License to anyone who comes into possession of a copy. This
225 | License will therefore apply, along with any applicable section 7
226 | additional terms, to the whole of the work, and all its parts,
227 | regardless of how they are packaged. This License gives no
228 | permission to license the work in any other way, but it does not
229 | invalidate such permission if you have separately received it.
230 |
231 | d) If the work has interactive user interfaces, each must display
232 | Appropriate Legal Notices; however, if the Program has interactive
233 | interfaces that do not display Appropriate Legal Notices, your
234 | work need not make them do so.
235 |
236 | A compilation of a covered work with other separate and independent
237 | works, which are not by their nature extensions of the covered work,
238 | and which are not combined with it such as to form a larger program,
239 | in or on a volume of a storage or distribution medium, is called an
240 | "aggregate" if the compilation and its resulting copyright are not
241 | used to limit the access or legal rights of the compilation's users
242 | beyond what the individual works permit. Inclusion of a covered work
243 | in an aggregate does not cause this License to apply to the other
244 | parts of the aggregate.
245 |
246 | 6. Conveying Non-Source Forms.
247 |
248 | You may convey a covered work in object code form under the terms
249 | of sections 4 and 5, provided that you also convey the
250 | machine-readable Corresponding Source under the terms of this License,
251 | in one of these ways:
252 |
253 | a) Convey the object code in, or embodied in, a physical product
254 | (including a physical distribution medium), accompanied by the
255 | Corresponding Source fixed on a durable physical medium
256 | customarily used for software interchange.
257 |
258 | b) Convey the object code in, or embodied in, a physical product
259 | (including a physical distribution medium), accompanied by a
260 | written offer, valid for at least three years and valid for as
261 | long as you offer spare parts or customer support for that product
262 | model, to give anyone who possesses the object code either (1) a
263 | copy of the Corresponding Source for all the software in the
264 | product that is covered by this License, on a durable physical
265 | medium customarily used for software interchange, for a price no
266 | more than your reasonable cost of physically performing this
267 | conveying of source, or (2) access to copy the
268 | Corresponding Source from a network server at no charge.
269 |
270 | c) Convey individual copies of the object code with a copy of the
271 | written offer to provide the Corresponding Source. This
272 | alternative is allowed only occasionally and noncommercially, and
273 | only if you received the object code with such an offer, in accord
274 | with subsection 6b.
275 |
276 | d) Convey the object code by offering access from a designated
277 | place (gratis or for a charge), and offer equivalent access to the
278 | Corresponding Source in the same way through the same place at no
279 | further charge. You need not require recipients to copy the
280 | Corresponding Source along with the object code. If the place to
281 | copy the object code is a network server, the Corresponding Source
282 | may be on a different server (operated by you or a third party)
283 | that supports equivalent copying facilities, provided you maintain
284 | clear directions next to the object code saying where to find the
285 | Corresponding Source. Regardless of what server hosts the
286 | Corresponding Source, you remain obligated to ensure that it is
287 | available for as long as needed to satisfy these requirements.
288 |
289 | e) Convey the object code using peer-to-peer transmission, provided
290 | you inform other peers where the object code and Corresponding
291 | Source of the work are being offered to the general public at no
292 | charge under subsection 6d.
293 |
294 | A separable portion of the object code, whose source code is excluded
295 | from the Corresponding Source as a System Library, need not be
296 | included in conveying the object code work.
297 |
298 | A "User Product" is either (1) a "consumer product", which means any
299 | tangible personal property which is normally used for personal, family,
300 | or household purposes, or (2) anything designed or sold for incorporation
301 | into a dwelling. In determining whether a product is a consumer product,
302 | doubtful cases shall be resolved in favor of coverage. For a particular
303 | product received by a particular user, "normally used" refers to a
304 | typical or common use of that class of product, regardless of the status
305 | of the particular user or of the way in which the particular user
306 | actually uses, or expects or is expected to use, the product. A product
307 | is a consumer product regardless of whether the product has substantial
308 | commercial, industrial or non-consumer uses, unless such uses represent
309 | the only significant mode of use of the product.
310 |
311 | "Installation Information" for a User Product means any methods,
312 | procedures, authorization keys, or other information required to install
313 | and execute modified versions of a covered work in that User Product from
314 | a modified version of its Corresponding Source. The information must
315 | suffice to ensure that the continued functioning of the modified object
316 | code is in no case prevented or interfered with solely because
317 | modification has been made.
318 |
319 | If you convey an object code work under this section in, or with, or
320 | specifically for use in, a User Product, and the conveying occurs as
321 | part of a transaction in which the right of possession and use of the
322 | User Product is transferred to the recipient in perpetuity or for a
323 | fixed term (regardless of how the transaction is characterized), the
324 | Corresponding Source conveyed under this section must be accompanied
325 | by the Installation Information. But this requirement does not apply
326 | if neither you nor any third party retains the ability to install
327 | modified object code on the User Product (for example, the work has
328 | been installed in ROM).
329 |
330 | The requirement to provide Installation Information does not include a
331 | requirement to continue to provide support service, warranty, or updates
332 | for a work that has been modified or installed by the recipient, or for
333 | the User Product in which it has been modified or installed. Access to a
334 | network may be denied when the modification itself materially and
335 | adversely affects the operation of the network or violates the rules and
336 | protocols for communication across the network.
337 |
338 | Corresponding Source conveyed, and Installation Information provided,
339 | in accord with this section must be in a format that is publicly
340 | documented (and with an implementation available to the public in
341 | source code form), and must require no special password or key for
342 | unpacking, reading or copying.
343 |
344 | 7. Additional Terms.
345 |
346 | "Additional permissions" are terms that supplement the terms of this
347 | License by making exceptions from one or more of its conditions.
348 | Additional permissions that are applicable to the entire Program shall
349 | be treated as though they were included in this License, to the extent
350 | that they are valid under applicable law. If additional permissions
351 | apply only to part of the Program, that part may be used separately
352 | under those permissions, but the entire Program remains governed by
353 | this License without regard to the additional permissions.
354 |
355 | When you convey a copy of a covered work, you may at your option
356 | remove any additional permissions from that copy, or from any part of
357 | it. (Additional permissions may be written to require their own
358 | removal in certain cases when you modify the work.) You may place
359 | additional permissions on material, added by you to a covered work,
360 | for which you have or can give appropriate copyright permission.
361 |
362 | Notwithstanding any other provision of this License, for material you
363 | add to a covered work, you may (if authorized by the copyright holders of
364 | that material) supplement the terms of this License with terms:
365 |
366 | a) Disclaiming warranty or limiting liability differently from the
367 | terms of sections 15 and 16 of this License; or
368 |
369 | b) Requiring preservation of specified reasonable legal notices or
370 | author attributions in that material or in the Appropriate Legal
371 | Notices displayed by works containing it; or
372 |
373 | c) Prohibiting misrepresentation of the origin of that material, or
374 | requiring that modified versions of such material be marked in
375 | reasonable ways as different from the original version; or
376 |
377 | d) Limiting the use for publicity purposes of names of licensors or
378 | authors of the material; or
379 |
380 | e) Declining to grant rights under trademark law for use of some
381 | trade names, trademarks, or service marks; or
382 |
383 | f) Requiring indemnification of licensors and authors of that
384 | material by anyone who conveys the material (or modified versions of
385 | it) with contractual assumptions of liability to the recipient, for
386 | any liability that these contractual assumptions directly impose on
387 | those licensors and authors.
388 |
389 | All other non-permissive additional terms are considered "further
390 | restrictions" within the meaning of section 10. If the Program as you
391 | received it, or any part of it, contains a notice stating that it is
392 | governed by this License along with a term that is a further
393 | restriction, you may remove that term. If a license document contains
394 | a further restriction but permits relicensing or conveying under this
395 | License, you may add to a covered work material governed by the terms
396 | of that license document, provided that the further restriction does
397 | not survive such relicensing or conveying.
398 |
399 | If you add terms to a covered work in accord with this section, you
400 | must place, in the relevant source files, a statement of the
401 | additional terms that apply to those files, or a notice indicating
402 | where to find the applicable terms.
403 |
404 | Additional terms, permissive or non-permissive, may be stated in the
405 | form of a separately written license, or stated as exceptions;
406 | the above requirements apply either way.
407 |
408 | 8. Termination.
409 |
410 | You may not propagate or modify a covered work except as expressly
411 | provided under this License. Any attempt otherwise to propagate or
412 | modify it is void, and will automatically terminate your rights under
413 | this License (including any patent licenses granted under the third
414 | paragraph of section 11).
415 |
416 | However, if you cease all violation of this License, then your
417 | license from a particular copyright holder is reinstated (a)
418 | provisionally, unless and until the copyright holder explicitly and
419 | finally terminates your license, and (b) permanently, if the copyright
420 | holder fails to notify you of the violation by some reasonable means
421 | prior to 60 days after the cessation.
422 |
423 | Moreover, your license from a particular copyright holder is
424 | reinstated permanently if the copyright holder notifies you of the
425 | violation by some reasonable means, this is the first time you have
426 | received notice of violation of this License (for any work) from that
427 | copyright holder, and you cure the violation prior to 30 days after
428 | your receipt of the notice.
429 |
430 | Termination of your rights under this section does not terminate the
431 | licenses of parties who have received copies or rights from you under
432 | this License. If your rights have been terminated and not permanently
433 | reinstated, you do not qualify to receive new licenses for the same
434 | material under section 10.
435 |
436 | 9. Acceptance Not Required for Having Copies.
437 |
438 | You are not required to accept this License in order to receive or
439 | run a copy of the Program. Ancillary propagation of a covered work
440 | occurring solely as a consequence of using peer-to-peer transmission
441 | to receive a copy likewise does not require acceptance. However,
442 | nothing other than this License grants you permission to propagate or
443 | modify any covered work. These actions infringe copyright if you do
444 | not accept this License. Therefore, by modifying or propagating a
445 | covered work, you indicate your acceptance of this License to do so.
446 |
447 | 10. Automatic Licensing of Downstream Recipients.
448 |
449 | Each time you convey a covered work, the recipient automatically
450 | receives a license from the original licensors, to run, modify and
451 | propagate that work, subject to this License. You are not responsible
452 | for enforcing compliance by third parties with this License.
453 |
454 | An "entity transaction" is a transaction transferring control of an
455 | organization, or substantially all assets of one, or subdividing an
456 | organization, or merging organizations. If propagation of a covered
457 | work results from an entity transaction, each party to that
458 | transaction who receives a copy of the work also receives whatever
459 | licenses to the work the party's predecessor in interest had or could
460 | give under the previous paragraph, plus a right to possession of the
461 | Corresponding Source of the work from the predecessor in interest, if
462 | the predecessor has it or can get it with reasonable efforts.
463 |
464 | You may not impose any further restrictions on the exercise of the
465 | rights granted or affirmed under this License. For example, you may
466 | not impose a license fee, royalty, or other charge for exercise of
467 | rights granted under this License, and you may not initiate litigation
468 | (including a cross-claim or counterclaim in a lawsuit) alleging that
469 | any patent claim is infringed by making, using, selling, offering for
470 | sale, or importing the Program or any portion of it.
471 |
472 | 11. Patents.
473 |
474 | A "contributor" is a copyright holder who authorizes use under this
475 | License of the Program or a work on which the Program is based. The
476 | work thus licensed is called the contributor's "contributor version".
477 |
478 | A contributor's "essential patent claims" are all patent claims
479 | owned or controlled by the contributor, whether already acquired or
480 | hereafter acquired, that would be infringed by some manner, permitted
481 | by this License, of making, using, or selling its contributor version,
482 | but do not include claims that would be infringed only as a
483 | consequence of further modification of the contributor version. For
484 | purposes of this definition, "control" includes the right to grant
485 | patent sublicenses in a manner consistent with the requirements of
486 | this License.
487 |
488 | Each contributor grants you a non-exclusive, worldwide, royalty-free
489 | patent license under the contributor's essential patent claims, to
490 | make, use, sell, offer for sale, import and otherwise run, modify and
491 | propagate the contents of its contributor version.
492 |
493 | In the following three paragraphs, a "patent license" is any express
494 | agreement or commitment, however denominated, not to enforce a patent
495 | (such as an express permission to practice a patent or covenant not to
496 | sue for patent infringement). To "grant" such a patent license to a
497 | party means to make such an agreement or commitment not to enforce a
498 | patent against the party.
499 |
500 | If you convey a covered work, knowingly relying on a patent license,
501 | and the Corresponding Source of the work is not available for anyone
502 | to copy, free of charge and under the terms of this License, through a
503 | publicly available network server or other readily accessible means,
504 | then you must either (1) cause the Corresponding Source to be so
505 | available, or (2) arrange to deprive yourself of the benefit of the
506 | patent license for this particular work, or (3) arrange, in a manner
507 | consistent with the requirements of this License, to extend the patent
508 | license to downstream recipients. "Knowingly relying" means you have
509 | actual knowledge that, but for the patent license, your conveying the
510 | covered work in a country, or your recipient's use of the covered work
511 | in a country, would infringe one or more identifiable patents in that
512 | country that you have reason to believe are valid.
513 |
514 | If, pursuant to or in connection with a single transaction or
515 | arrangement, you convey, or propagate by procuring conveyance of, a
516 | covered work, and grant a patent license to some of the parties
517 | receiving the covered work authorizing them to use, propagate, modify
518 | or convey a specific copy of the covered work, then the patent license
519 | you grant is automatically extended to all recipients of the covered
520 | work and works based on it.
521 |
522 | A patent license is "discriminatory" if it does not include within
523 | the scope of its coverage, prohibits the exercise of, or is
524 | conditioned on the non-exercise of one or more of the rights that are
525 | specifically granted under this License. You may not convey a covered
526 | work if you are a party to an arrangement with a third party that is
527 | in the business of distributing software, under which you make payment
528 | to the third party based on the extent of your activity of conveying
529 | the work, and under which the third party grants, to any of the
530 | parties who would receive the covered work from you, a discriminatory
531 | patent license (a) in connection with copies of the covered work
532 | conveyed by you (or copies made from those copies), or (b) primarily
533 | for and in connection with specific products or compilations that
534 | contain the covered work, unless you entered into that arrangement,
535 | or that patent license was granted, prior to 28 March 2007.
536 |
537 | Nothing in this License shall be construed as excluding or limiting
538 | any implied license or other defenses to infringement that may
539 | otherwise be available to you under applicable patent law.
540 |
541 | 12. No Surrender of Others' Freedom.
542 |
543 | If conditions are imposed on you (whether by court order, agreement or
544 | otherwise) that contradict the conditions of this License, they do not
545 | excuse you from the conditions of this License. If you cannot convey a
546 | covered work so as to satisfy simultaneously your obligations under this
547 | License and any other pertinent obligations, then as a consequence you may
548 | not convey it at all. For example, if you agree to terms that obligate you
549 | to collect a royalty for further conveying from those to whom you convey
550 | the Program, the only way you could satisfy both those terms and this
551 | License would be to refrain entirely from conveying the Program.
552 |
553 | 13. Use with the GNU Affero General Public License.
554 |
555 | Notwithstanding any other provision of this License, you have
556 | permission to link or combine any covered work with a work licensed
557 | under version 3 of the GNU Affero General Public License into a single
558 | combined work, and to convey the resulting work. The terms of this
559 | License will continue to apply to the part which is the covered work,
560 | but the special requirements of the GNU Affero General Public License,
561 | section 13, concerning interaction through a network will apply to the
562 | combination as such.
563 |
564 | 14. Revised Versions of this License.
565 |
566 | The Free Software Foundation may publish revised and/or new versions of
567 | the GNU General Public License from time to time. Such new versions will
568 | be similar in spirit to the present version, but may differ in detail to
569 | address new problems or concerns.
570 |
571 | Each version is given a distinguishing version number. If the
572 | Program specifies that a certain numbered version of the GNU General
573 | Public License "or any later version" applies to it, you have the
574 | option of following the terms and conditions either of that numbered
575 | version or of any later version published by the Free Software
576 | Foundation. If the Program does not specify a version number of the
577 | GNU General Public License, you may choose any version ever published
578 | by the Free Software Foundation.
579 |
580 | If the Program specifies that a proxy can decide which future
581 | versions of the GNU General Public License can be used, that proxy's
582 | public statement of acceptance of a version permanently authorizes you
583 | to choose that version for the Program.
584 |
585 | Later license versions may give you additional or different
586 | permissions. However, no additional obligations are imposed on any
587 | author or copyright holder as a result of your choosing to follow a
588 | later version.
589 |
590 | 15. Disclaimer of Warranty.
591 |
592 | THERE IS NO WARRANTY FOR THE PROGRAM, TO THE EXTENT PERMITTED BY
593 | APPLICABLE LAW. EXCEPT WHEN OTHERWISE STATED IN WRITING THE COPYRIGHT
594 | HOLDERS AND/OR OTHER PARTIES PROVIDE THE PROGRAM "AS IS" WITHOUT WARRANTY
595 | OF ANY KIND, EITHER EXPRESSED OR IMPLIED, INCLUDING, BUT NOT LIMITED TO,
596 | THE IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR
597 | PURPOSE. THE ENTIRE RISK AS TO THE QUALITY AND PERFORMANCE OF THE PROGRAM
598 | IS WITH YOU. SHOULD THE PROGRAM PROVE DEFECTIVE, YOU ASSUME THE COST OF
599 | ALL NECESSARY SERVICING, REPAIR OR CORRECTION.
600 |
601 | 16. Limitation of Liability.
602 |
603 | IN NO EVENT UNLESS REQUIRED BY APPLICABLE LAW OR AGREED TO IN WRITING
604 | WILL ANY COPYRIGHT HOLDER, OR ANY OTHER PARTY WHO MODIFIES AND/OR CONVEYS
605 | THE PROGRAM AS PERMITTED ABOVE, BE LIABLE TO YOU FOR DAMAGES, INCLUDING ANY
606 | GENERAL, SPECIAL, INCIDENTAL OR CONSEQUENTIAL DAMAGES ARISING OUT OF THE
607 | USE OR INABILITY TO USE THE PROGRAM (INCLUDING BUT NOT LIMITED TO LOSS OF
608 | DATA OR DATA BEING RENDERED INACCURATE OR LOSSES SUSTAINED BY YOU OR THIRD
609 | PARTIES OR A FAILURE OF THE PROGRAM TO OPERATE WITH ANY OTHER PROGRAMS),
610 | EVEN IF SUCH HOLDER OR OTHER PARTY HAS BEEN ADVISED OF THE POSSIBILITY OF
611 | SUCH DAMAGES.
612 |
613 | 17. Interpretation of Sections 15 and 16.
614 |
615 | If the disclaimer of warranty and limitation of liability provided
616 | above cannot be given local legal effect according to their terms,
617 | reviewing courts shall apply local law that most closely approximates
618 | an absolute waiver of all civil liability in connection with the
619 | Program, unless a warranty or assumption of liability accompanies a
620 | copy of the Program in return for a fee.
621 |
622 | END OF TERMS AND CONDITIONS
623 |
624 | How to Apply These Terms to Your New Programs
625 |
626 | If you develop a new program, and you want it to be of the greatest
627 | possible use to the public, the best way to achieve this is to make it
628 | free software which everyone can redistribute and change under these terms.
629 |
630 | To do so, attach the following notices to the program. It is safest
631 | to attach them to the start of each source file to most effectively
632 | state the exclusion of warranty; and each file should have at least
633 | the "copyright" line and a pointer to where the full notice is found.
634 |
635 |
636 | Copyright (C)
637 |
638 | This program is free software: you can redistribute it and/or modify
639 | it under the terms of the GNU General Public License as published by
640 | the Free Software Foundation, either version 3 of the License, or
641 | (at your option) any later version.
642 |
643 | This program is distributed in the hope that it will be useful,
644 | but WITHOUT ANY WARRANTY; without even the implied warranty of
645 | MERCHANTABILITY or FITNESS FOR A PARTICULAR PURPOSE. See the
646 | GNU General Public License for more details.
647 |
648 | You should have received a copy of the GNU General Public License
649 | along with this program. If not, see .
650 |
651 | Also add information on how to contact you by electronic and paper mail.
652 |
653 | If the program does terminal interaction, make it output a short
654 | notice like this when it starts in an interactive mode:
655 |
656 | Copyright (C)
657 | This program comes with ABSOLUTELY NO WARRANTY; for details type `show w'.
658 | This is free software, and you are welcome to redistribute it
659 | under certain conditions; type `show c' for details.
660 |
661 | The hypothetical commands `show w' and `show c' should show the appropriate
662 | parts of the General Public License. Of course, your program's commands
663 | might be different; for a GUI interface, you would use an "about box".
664 |
665 | You should also get your employer (if you work as a programmer) or school,
666 | if any, to sign a "copyright disclaimer" for the program, if necessary.
667 | For more information on this, and how to apply and follow the GNU GPL, see
668 | .
669 |
670 | The GNU General Public License does not permit incorporating your program
671 | into proprietary programs. If your program is a subroutine library, you
672 | may consider it more useful to permit linking proprietary applications with
673 | the library. If this is what you want to do, use the GNU Lesser General
674 | Public License instead of this License. But first, please read
675 | .
676 | =======
677 | GNU GENERAL PUBLIC LICENSE
678 | Version 3, 29 June 2007
679 |
680 | Copyright (C) 2007 Free Software Foundation, Inc.
681 | Everyone is permitted to copy and distribute verbatim copies
682 | of this license document, but changing it is not allowed.
683 |
684 | Preamble
685 |
686 | The GNU General Public License is a free, copyleft license for
687 | software and other kinds of works.
688 |
689 | The licenses for most software and other practical works are designed
690 | to take away your freedom to share and change the works. By contrast,
691 | the GNU General Public License is intended to guarantee your freedom to
692 | share and change all versions of a program--to make sure it remains free
693 | software for all its users. We, the Free Software Foundation, use the
694 | GNU General Public License for most of our software; it applies also to
695 | any other work released this way by its authors. You can apply it to
696 | your programs, too.
697 |
698 | When we speak of free software, we are referring to freedom, not
699 | price. Our General Public Licenses are designed to make sure that you
700 | have the freedom to distribute copies of free software (and charge for
701 | them if you wish), that you receive source code or can get it if you
702 | want it, that you can change the software or use pieces of it in new
703 | free programs, and that you know you can do these things.
704 |
705 | To protect your rights, we need to prevent others from denying you
706 | these rights or asking you to surrender the rights. Therefore, you have
707 | certain responsibilities if you distribute copies of the software, or if
708 | you modify it: responsibilities to respect the freedom of others.
709 |
710 | For example, if you distribute copies of such a program, whether
711 | gratis or for a fee, you must pass on to the recipients the same
712 | freedoms that you received. You must make sure that they, too, receive
713 | or can get the source code. And you must show them these terms so they
714 | know their rights.
715 |
716 | Developers that use the GNU GPL protect your rights with two steps:
717 | (1) assert copyright on the software, and (2) offer you this License
718 | giving you legal permission to copy, distribute and/or modify it.
719 |
720 | For the developers' and authors' protection, the GPL clearly explains
721 | that there is no warranty for this free software. For both users' and
722 | authors' sake, the GPL requires that modified versions be marked as
723 | changed, so that their problems will not be attributed erroneously to
724 | authors of previous versions.
725 |
726 | Some devices are designed to deny users access to install or run
727 | modified versions of the software inside them, although the manufacturer
728 | can do so. This is fundamentally incompatible with the aim of
729 | protecting users' freedom to change the software. The systematic
730 | pattern of such abuse occurs in the area of products for individuals to
731 | use, which is precisely where it is most unacceptable. Therefore, we
732 | have designed this version of the GPL to prohibit the practice for those
733 | products. If such problems arise substantially in other domains, we
734 | stand ready to extend this provision to those domains in future versions
735 | of the GPL, as needed to protect the freedom of users.
736 |
737 | Finally, every program is threatened constantly by software patents.
738 | States should not allow patents to restrict development and use of
739 | software on general-purpose computers, but in those that do, we wish to
740 | avoid the special danger that patents applied to a free program could
741 | make it effectively proprietary. To prevent this, the GPL assures that
742 | patents cannot be used to render the program non-free.
743 |
744 | The precise terms and conditions for copying, distribution and
745 | modification follow.
746 |
747 | TERMS AND CONDITIONS
748 |
749 | 0. Definitions.
750 |
751 | "This License" refers to version 3 of the GNU General Public License.
752 |
753 | "Copyright" also means copyright-like laws that apply to other kinds of
754 | works, such as semiconductor masks.
755 |
756 | "The Program" refers to any copyrightable work licensed under this
757 | License. Each licensee is addressed as "you". "Licensees" and
758 | "recipients" may be individuals or organizations.
759 |
760 | To "modify" a work means to copy from or adapt all or part of the work
761 | in a fashion requiring copyright permission, other than the making of an
762 | exact copy. The resulting work is called a "modified version" of the
763 | earlier work or a work "based on" the earlier work.
764 |
765 | A "covered work" means either the unmodified Program or a work based
766 | on the Program.
767 |
768 | To "propagate" a work means to do anything with it that, without
769 | permission, would make you directly or secondarily liable for
770 | infringement under applicable copyright law, except executing it on a
771 | computer or modifying a private copy. Propagation includes copying,
772 | distribution (with or without modification), making available to the
773 | public, and in some countries other activities as well.
774 |
775 | To "convey" a work means any kind of propagation that enables other
776 | parties to make or receive copies. Mere interaction with a user through
777 | a computer network, with no transfer of a copy, is not conveying.
778 |
779 | An interactive user interface displays "Appropriate Legal Notices"
780 | to the extent that it includes a convenient and prominently visible
781 | feature that (1) displays an appropriate copyright notice, and (2)
782 | tells the user that there is no warranty for the work (except to the
783 | extent that warranties are provided), that licensees may convey the
784 | work under this License, and how to view a copy of this License. If
785 | the interface presents a list of user commands or options, such as a
786 | menu, a prominent item in the list meets this criterion.
787 |
788 | 1. Source Code.
789 |
790 | The "source code" for a work means the preferred form of the work
791 | for making modifications to it. "Object code" means any non-source
792 | form of a work.
793 |
794 | A "Standard Interface" means an interface that either is an official
795 | standard defined by a recognized standards body, or, in the case of
796 | interfaces specified for a particular programming language, one that
797 | is widely used among developers working in that language.
798 |
799 | The "System Libraries" of an executable work include anything, other
800 | than the work as a whole, that (a) is included in the normal form of
801 | packaging a Major Component, but which is not part of that Major
802 | Component, and (b) serves only to enable use of the work with that
803 | Major Component, or to implement a Standard Interface for which an
804 | implementation is available to the public in source code form. A
805 | "Major Component", in this context, means a major essential component
806 | (kernel, window system, and so on) of the specific operating system
807 | (if any) on which the executable work runs, or a compiler used to
808 | produce the work, or an object code interpreter used to run it.
809 |
810 | The "Corresponding Source" for a work in object code form means all
811 | the source code needed to generate, install, and (for an executable
812 | work) run the object code and to modify the work, including scripts to
813 | control those activities. However, it does not include the work's
814 | System Libraries, or general-purpose tools or generally available free
815 | programs which are used unmodified in performing those activities but
816 | which are not part of the work. For example, Corresponding Source
817 | includes interface definition files associated with source files for
818 | the work, and the source code for shared libraries and dynamically
819 | linked subprograms that the work is specifically designed to require,
820 | such as by intimate data communication or control flow between those
821 | subprograms and other parts of the work.
822 |
823 | The Corresponding Source need not include anything that users
824 | can regenerate automatically from other parts of the Corresponding
825 | Source.
826 |
827 | The Corresponding Source for a work in source code form is that
828 | same work.
829 |
830 | 2. Basic Permissions.
831 |
832 | All rights granted under this License are granted for the term of
833 | copyright on the Program, and are irrevocable provided the stated
834 | conditions are met. This License explicitly affirms your unlimited
835 | permission to run the unmodified Program. The output from running a
836 | covered work is covered by this License only if the output, given its
837 | content, constitutes a covered work. This License acknowledges your
838 | rights of fair use or other equivalent, as provided by copyright law.
839 |
840 | You may make, run and propagate covered works that you do not
841 | convey, without conditions so long as your license otherwise remains
842 | in force. You may convey covered works to others for the sole purpose
843 | of having them make modifications exclusively for you, or provide you
844 | with facilities for running those works, provided that you comply with
845 | the terms of this License in conveying all material for which you do
846 | not control copyright. Those thus making or running the covered works
847 | for you must do so exclusively on your behalf, under your direction
848 | and control, on terms that prohibit them from making any copies of
849 | your copyrighted material outside their relationship with you.
850 |
851 | Conveying under any other circumstances is permitted solely under
852 | the conditions stated below. Sublicensing is not allowed; section 10
853 | makes it unnecessary.
854 |
855 | 3. Protecting Users' Legal Rights From Anti-Circumvention Law.
856 |
857 | No covered work shall be deemed part of an effective technological
858 | measure under any applicable law fulfilling obligations under article
859 | 11 of the WIPO copyright treaty adopted on 20 December 1996, or
860 | similar laws prohibiting or restricting circumvention of such
861 | measures.
862 |
863 | When you convey a covered work, you waive any legal power to forbid
864 | circumvention of technological measures to the extent such circumvention
865 | is effected by exercising rights under this License with respect to
866 | the covered work, and you disclaim any intention to limit operation or
867 | modification of the work as a means of enforcing, against the work's
868 | users, your or third parties' legal rights to forbid circumvention of
869 | technological measures.
870 |
871 | 4. Conveying Verbatim Copies.
872 |
873 | You may convey verbatim copies of the Program's source code as you
874 | receive it, in any medium, provided that you conspicuously and
875 | appropriately publish on each copy an appropriate copyright notice;
876 | keep intact all notices stating that this License and any
877 | non-permissive terms added in accord with section 7 apply to the code;
878 | keep intact all notices of the absence of any warranty; and give all
879 | recipients a copy of this License along with the Program.
880 |
881 | You may charge any price or no price for each copy that you convey,
882 | and you may offer support or warranty protection for a fee.
883 |
884 | 5. Conveying Modified Source Versions.
885 |
886 | You may convey a work based on the Program, or the modifications to
887 | produce it from the Program, in the form of source code under the
888 | terms of section 4, provided that you also meet all of these conditions:
889 |
890 | a) The work must carry prominent notices stating that you modified
891 | it, and giving a relevant date.
892 |
893 | b) The work must carry prominent notices stating that it is
894 | released under this License and any conditions added under section
895 | 7. This requirement modifies the requirement in section 4 to
896 | "keep intact all notices".
897 |
898 | c) You must license the entire work, as a whole, under this
899 | License to anyone who comes into possession of a copy. This
900 | License will therefore apply, along with any applicable section 7
901 | additional terms, to the whole of the work, and all its parts,
902 | regardless of how they are packaged. This License gives no
903 | permission to license the work in any other way, but it does not
904 | invalidate such permission if you have separately received it.
905 |
906 | d) If the work has interactive user interfaces, each must display
907 | Appropriate Legal Notices; however, if the Program has interactive
908 | interfaces that do not display Appropriate Legal Notices, your
909 | work need not make them do so.
910 |
911 | A compilation of a covered work with other separate and independent
912 | works, which are not by their nature extensions of the covered work,
913 | and which are not combined with it such as to form a larger program,
914 | in or on a volume of a storage or distribution medium, is called an
915 | "aggregate" if the compilation and its resulting copyright are not
916 | used to limit the access or legal rights of the compilation's users
917 | beyond what the individual works permit. Inclusion of a covered work
918 | in an aggregate does not cause this License to apply to the other
919 | parts of the aggregate.
920 |
921 | 6. Conveying Non-Source Forms.
922 |
923 | You may convey a covered work in object code form under the terms
924 | of sections 4 and 5, provided that you also convey the
925 | machine-readable Corresponding Source under the terms of this License,
926 | in one of these ways:
927 |
928 | a) Convey the object code in, or embodied in, a physical product
929 | (including a physical distribution medium), accompanied by the
930 | Corresponding Source fixed on a durable physical medium
931 | customarily used for software interchange.
932 |
933 | b) Convey the object code in, or embodied in, a physical product
934 | (including a physical distribution medium), accompanied by a
935 | written offer, valid for at least three years and valid for as
936 | long as you offer spare parts or customer support for that product
937 | model, to give anyone who possesses the object code either (1) a
938 | copy of the Corresponding Source for all the software in the
939 | product that is covered by this License, on a durable physical
940 | medium customarily used for software interchange, for a price no
941 | more than your reasonable cost of physically performing this
942 | conveying of source, or (2) access to copy the
943 | Corresponding Source from a network server at no charge.
944 |
945 | c) Convey individual copies of the object code with a copy of the
946 | written offer to provide the Corresponding Source. This
947 | alternative is allowed only occasionally and noncommercially, and
948 | only if you received the object code with such an offer, in accord
949 | with subsection 6b.
950 |
951 | d) Convey the object code by offering access from a designated
952 | place (gratis or for a charge), and offer equivalent access to the
953 | Corresponding Source in the same way through the same place at no
954 | further charge. You need not require recipients to copy the
955 | Corresponding Source along with the object code. If the place to
956 | copy the object code is a network server, the Corresponding Source
957 | may be on a different server (operated by you or a third party)
958 | that supports equivalent copying facilities, provided you maintain
959 | clear directions next to the object code saying where to find the
960 | Corresponding Source. Regardless of what server hosts the
961 | Corresponding Source, you remain obligated to ensure that it is
962 | available for as long as needed to satisfy these requirements.
963 |
964 | e) Convey the object code using peer-to-peer transmission, provided
965 | you inform other peers where the object code and Corresponding
966 | Source of the work are being offered to the general public at no
967 | charge under subsection 6d.
968 |
969 | A separable portion of the object code, whose source code is excluded
970 | from the Corresponding Source as a System Library, need not be
971 | included in conveying the object code work.
972 |
973 | A "User Product" is either (1) a "consumer product", which means any
974 | tangible personal property which is normally used for personal, family,
975 | or household purposes, or (2) anything designed or sold for incorporation
976 | into a dwelling. In determining whether a product is a consumer product,
977 | doubtful cases shall be resolved in favor of coverage. For a particular
978 | product received by a particular user, "normally used" refers to a
979 | typical or common use of that class of product, regardless of the status
980 | of the particular user or of the way in which the particular user
981 | actually uses, or expects or is expected to use, the product. A product
982 | is a consumer product regardless of whether the product has substantial
983 | commercial, industrial or non-consumer uses, unless such uses represent
984 | the only significant mode of use of the product.
985 |
986 | "Installation Information" for a User Product means any methods,
987 | procedures, authorization keys, or other information required to install
988 | and execute modified versions of a covered work in that User Product from
989 | a modified version of its Corresponding Source. The information must
990 | suffice to ensure that the continued functioning of the modified object
991 | code is in no case prevented or interfered with solely because
992 | modification has been made.
993 |
994 | If you convey an object code work under this section in, or with, or
995 | specifically for use in, a User Product, and the conveying occurs as
996 | part of a transaction in which the right of possession and use of the
997 | User Product is transferred to the recipient in perpetuity or for a
998 | fixed term (regardless of how the transaction is characterized), the
999 | Corresponding Source conveyed under this section must be accompanied
1000 | by the Installation Information. But this requirement does not apply
1001 | if neither you nor any third party retains the ability to install
1002 | modified object code on the User Product (for example, the work has
1003 | been installed in ROM).
1004 |
1005 | The requirement to provide Installation Information does not include a
1006 | requirement to continue to provide support service, warranty, or updates
1007 | for a work that has been modified or installed by the recipient, or for
1008 | the User Product in which it has been modified or installed. Access to a
1009 | network may be denied when the modification itself materially and
1010 | adversely affects the operation of the network or violates the rules and
1011 | protocols for communication across the network.
1012 |
1013 | Corresponding Source conveyed, and Installation Information provided,
1014 | in accord with this section must be in a format that is publicly
1015 | documented (and with an implementation available to the public in
1016 | source code form), and must require no special password or key for
1017 | unpacking, reading or copying.
1018 |
1019 | 7. Additional Terms.
1020 |
1021 | "Additional permissions" are terms that supplement the terms of this
1022 | License by making exceptions from one or more of its conditions.
1023 | Additional permissions that are applicable to the entire Program shall
1024 | be treated as though they were included in this License, to the extent
1025 | that they are valid under applicable law. If additional permissions
1026 | apply only to part of the Program, that part may be used separately
1027 | under those permissions, but the entire Program remains governed by
1028 | this License without regard to the additional permissions.
1029 |
1030 | When you convey a copy of a covered work, you may at your option
1031 | remove any additional permissions from that copy, or from any part of
1032 | it. (Additional permissions may be written to require their own
1033 | removal in certain cases when you modify the work.) You may place
1034 | additional permissions on material, added by you to a covered work,
1035 | for which you have or can give appropriate copyright permission.
1036 |
1037 | Notwithstanding any other provision of this License, for material you
1038 | add to a covered work, you may (if authorized by the copyright holders of
1039 | that material) supplement the terms of this License with terms:
1040 |
1041 | a) Disclaiming warranty or limiting liability differently from the
1042 | terms of sections 15 and 16 of this License; or
1043 |
1044 | b) Requiring preservation of specified reasonable legal notices or
1045 | author attributions in that material or in the Appropriate Legal
1046 | Notices displayed by works containing it; or
1047 |
1048 | c) Prohibiting misrepresentation of the origin of that material, or
1049 | requiring that modified versions of such material be marked in
1050 | reasonable ways as different from the original version; or
1051 |
1052 | d) Limiting the use for publicity purposes of names of licensors or
1053 | authors of the material; or
1054 |
1055 | e) Declining to grant rights under trademark law for use of some
1056 | trade names, trademarks, or service marks; or
1057 |
1058 | f) Requiring indemnification of licensors and authors of that
1059 | material by anyone who conveys the material (or modified versions of
1060 | it) with contractual assumptions of liability to the recipient, for
1061 | any liability that these contractual assumptions directly impose on
1062 | those licensors and authors.
1063 |
1064 | All other non-permissive additional terms are considered "further
1065 | restrictions" within the meaning of section 10. If the Program as you
1066 | received it, or any part of it, contains a notice stating that it is
1067 | governed by this License along with a term that is a further
1068 | restriction, you may remove that term. If a license document contains
1069 | a further restriction but permits relicensing or conveying under this
1070 | License, you may add to a covered work material governed by the terms
1071 | of that license document, provided that the further restriction does
1072 | not survive such relicensing or conveying.
1073 |
1074 | If you add terms to a covered work in accord with this section, you
1075 | must place, in the relevant source files, a statement of the
1076 | additional terms that apply to those files, or a notice indicating
1077 | where to find the applicable terms.
1078 |
1079 | Additional terms, permissive or non-permissive, may be stated in the
1080 | form of a separately written license, or stated as exceptions;
1081 | the above requirements apply either way.
1082 |
1083 | 8. Termination.
1084 |
1085 | You may not propagate or modify a covered work except as expressly
1086 | provided under this License. Any attempt otherwise to propagate or
1087 | modify it is void, and will automatically terminate your rights under
1088 | this License (including any patent licenses granted under the third
1089 | paragraph of section 11).
1090 |
1091 | However, if you cease all violation of this License, then your
1092 | license from a particular copyright holder is reinstated (a)
1093 | provisionally, unless and until the copyright holder explicitly and
1094 | finally terminates your license, and (b) permanently, if the copyright
1095 | holder fails to notify you of the violation by some reasonable means
1096 | prior to 60 days after the cessation.
1097 |
1098 | Moreover, your license from a particular copyright holder is
1099 | reinstated permanently if the copyright holder notifies you of the
1100 | violation by some reasonable means, this is the first time you have
1101 | received notice of violation of this License (for any work) from that
1102 | copyright holder, and you cure the violation prior to 30 days after
1103 | your receipt of the notice.
1104 |
1105 | Termination of your rights under this section does not terminate the
1106 | licenses of parties who have received copies or rights from you under
1107 | this License. If your rights have been terminated and not permanently
1108 | reinstated, you do not qualify to receive new licenses for the same
1109 | material under section 10.
1110 |
1111 | 9. Acceptance Not Required for Having Copies.
1112 |
1113 | You are not required to accept this License in order to receive or
1114 | run a copy of the Program. Ancillary propagation of a covered work
1115 | occurring solely as a consequence of using peer-to-peer transmission
1116 | to receive a copy likewise does not require acceptance. However,
1117 | nothing other than this License grants you permission to propagate or
1118 | modify any covered work. These actions infringe copyright if you do
1119 | not accept this License. Therefore, by modifying or propagating a
1120 | covered work, you indicate your acceptance of this License to do so.
1121 |
1122 | 10. Automatic Licensing of Downstream Recipients.
1123 |
1124 | Each time you convey a covered work, the recipient automatically
1125 | receives a license from the original licensors, to run, modify and
1126 | propagate that work, subject to this License. You are not responsible
1127 | for enforcing compliance by third parties with this License.
1128 |
1129 | An "entity transaction" is a transaction transferring control of an
1130 | organization, or substantially all assets of one, or subdividing an
1131 | organization, or merging organizations. If propagation of a covered
1132 | work results from an entity transaction, each party to that
1133 | transaction who receives a copy of the work also receives whatever
1134 | licenses to the work the party's predecessor in interest had or could
1135 | give under the previous paragraph, plus a right to possession of the
1136 | Corresponding Source of the work from the predecessor in interest, if
1137 | the predecessor has it or can get it with reasonable efforts.
1138 |
1139 | You may not impose any further restrictions on the exercise of the
1140 | rights granted or affirmed under this License. For example, you may
1141 | not impose a license fee, royalty, or other charge for exercise of
1142 | rights granted under this License, and you may not initiate litigation
1143 | (including a cross-claim or counterclaim in a lawsuit) alleging that
1144 | any patent claim is infringed by making, using, selling, offering for
1145 | sale, or importing the Program or any portion of it.
1146 |
1147 | 11. Patents.
1148 |
1149 | A "contributor" is a copyright holder who authorizes use under this
1150 | License of the Program or a work on which the Program is based. The
1151 | work thus licensed is called the contributor's "contributor version".
1152 |
1153 | A contributor's "essential patent claims" are all patent claims
1154 | owned or controlled by the contributor, whether already acquired or
1155 | hereafter acquired, that would be infringed by some manner, permitted
1156 | by this License, of making, using, or selling its contributor version,
1157 | but do not include claims that would be infringed only as a
1158 | consequence of further modification of the contributor version. For
1159 | purposes of this definition, "control" includes the right to grant
1160 | patent sublicenses in a manner consistent with the requirements of
1161 | this License.
1162 |
1163 | Each contributor grants you a non-exclusive, worldwide, royalty-free
1164 | patent license under the contributor's essential patent claims, to
1165 | make, use, sell, offer for sale, import and otherwise run, modify and
1166 | propagate the contents of its contributor version.
1167 |
1168 | In the following three paragraphs, a "patent license" is any express
1169 | agreement or commitment, however denominated, not to enforce a patent
1170 | (such as an express permission to practice a patent or covenant not to
1171 | sue for patent infringement). To "grant" such a patent license to a
1172 | party means to make such an agreement or commitment not to enforce a
1173 | patent against the party.
1174 |
1175 | If you convey a covered work, knowingly relying on a patent license,
1176 | and the Corresponding Source of the work is not available for anyone
1177 | to copy, free of charge and under the terms of this License, through a
1178 | publicly available network server or other readily accessible means,
1179 | then you must either (1) cause the Corresponding Source to be so
1180 | available, or (2) arrange to deprive yourself of the benefit of the
1181 | patent license for this particular work, or (3) arrange, in a manner
1182 | consistent with the requirements of this License, to extend the patent
1183 | license to downstream recipients. "Knowingly relying" means you have
1184 | actual knowledge that, but for the patent license, your conveying the
1185 | covered work in a country, or your recipient's use of the covered work
1186 | in a country, would infringe one or more identifiable patents in that
1187 | country that you have reason to believe are valid.
1188 |
1189 | If, pursuant to or in connection with a single transaction or
1190 | arrangement, you convey, or propagate by procuring conveyance of, a
1191 | covered work, and grant a patent license to some of the parties
1192 | receiving the covered work authorizing them to use, propagate, modify
1193 | or convey a specific copy of the covered work, then the patent license
1194 | you grant is automatically extended to all recipients of the covered
1195 | work and works based on it.
1196 |
1197 | A patent license is "discriminatory" if it does not include within
1198 | the scope of its coverage, prohibits the exercise of, or is
1199 | conditioned on the non-exercise of one or more of the rights that are
1200 | specifically granted under this License. You may not convey a covered
1201 | work if you are a party to an arrangement with a third party that is
1202 | in the business of distributing software, under which you make payment
1203 | to the third party based on the extent of your activity of conveying
1204 | the work, and under which the third party grants, to any of the
1205 | parties who would receive the covered work from you, a discriminatory
1206 | patent license (a) in connection with copies of the covered work
1207 | conveyed by you (or copies made from those copies), or (b) primarily
1208 | for and in connection with specific products or compilations that
1209 | contain the covered work, unless you entered into that arrangement,
1210 | or that patent license was granted, prior to 28 March 2007.
1211 |
1212 | Nothing in this License shall be construed as excluding or limiting
1213 | any implied license or other defenses to infringement that may
1214 | otherwise be available to you under applicable patent law.
1215 |
1216 | 12. No Surrender of Others' Freedom.
1217 |
1218 | If conditions are imposed on you (whether by court order, agreement or
1219 | otherwise) that contradict the conditions of this License, they do not
1220 | excuse you from the conditions of this License. If you cannot convey a
1221 | covered work so as to satisfy simultaneously your obligations under this
1222 | License and any other pertinent obligations, then as a consequence you may
1223 | not convey it at all. For example, if you agree to terms that obligate you
1224 | to collect a royalty for further conveying from those to whom you convey
1225 | the Program, the only way you could satisfy both those terms and this
1226 | License would be to refrain entirely from conveying the Program.
1227 |
1228 | 13. Use with the GNU Affero General Public License.
1229 |
1230 | Notwithstanding any other provision of this License, you have
1231 | permission to link or combine any covered work with a work licensed
1232 | under version 3 of the GNU Affero General Public License into a single
1233 | combined work, and to convey the resulting work. The terms of this
1234 | License will continue to apply to the part which is the covered work,
1235 | but the special requirements of the GNU Affero General Public License,
1236 | section 13, concerning interaction through a network will apply to the
1237 | combination as such.
1238 |
1239 | 14. Revised Versions of this License.
1240 |
1241 | The Free Software Foundation may publish revised and/or new versions of
1242 | the GNU General Public License from time to time. Such new versions will
1243 | be similar in spirit to the present version, but may differ in detail to
1244 | address new problems or concerns.
1245 |
1246 | Each version is given a distinguishing version number. If the
1247 | Program specifies that a certain numbered version of the GNU General
1248 | Public License "or any later version" applies to it, you have the
1249 | option of following the terms and conditions either of that numbered
1250 | version or of any later version published by the Free Software
1251 | Foundation. If the Program does not specify a version number of the
1252 | GNU General Public License, you may choose any version ever published
1253 | by the Free Software Foundation.
1254 |
1255 | If the Program specifies that a proxy can decide which future
1256 | versions of the GNU General Public License can be used, that proxy's
1257 | public statement of acceptance of a version permanently authorizes you
1258 | to choose that version for the Program.
1259 |
1260 | Later license versions may give you additional or different
1261 | permissions. However, no additional obligations are imposed on any
1262 | author or copyright holder as a result of your choosing to follow a
1263 | later version.
1264 |
1265 | 15. Disclaimer of Warranty.
1266 |
1267 | THERE IS NO WARRANTY FOR THE PROGRAM, TO THE EXTENT PERMITTED BY
1268 | APPLICABLE LAW. EXCEPT WHEN OTHERWISE STATED IN WRITING THE COPYRIGHT
1269 | HOLDERS AND/OR OTHER PARTIES PROVIDE THE PROGRAM "AS IS" WITHOUT WARRANTY
1270 | OF ANY KIND, EITHER EXPRESSED OR IMPLIED, INCLUDING, BUT NOT LIMITED TO,
1271 | THE IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR
1272 | PURPOSE. THE ENTIRE RISK AS TO THE QUALITY AND PERFORMANCE OF THE PROGRAM
1273 | IS WITH YOU. SHOULD THE PROGRAM PROVE DEFECTIVE, YOU ASSUME THE COST OF
1274 | ALL NECESSARY SERVICING, REPAIR OR CORRECTION.
1275 |
1276 | 16. Limitation of Liability.
1277 |
1278 | IN NO EVENT UNLESS REQUIRED BY APPLICABLE LAW OR AGREED TO IN WRITING
1279 | WILL ANY COPYRIGHT HOLDER, OR ANY OTHER PARTY WHO MODIFIES AND/OR CONVEYS
1280 | THE PROGRAM AS PERMITTED ABOVE, BE LIABLE TO YOU FOR DAMAGES, INCLUDING ANY
1281 | GENERAL, SPECIAL, INCIDENTAL OR CONSEQUENTIAL DAMAGES ARISING OUT OF THE
1282 | USE OR INABILITY TO USE THE PROGRAM (INCLUDING BUT NOT LIMITED TO LOSS OF
1283 | DATA OR DATA BEING RENDERED INACCURATE OR LOSSES SUSTAINED BY YOU OR THIRD
1284 | PARTIES OR A FAILURE OF THE PROGRAM TO OPERATE WITH ANY OTHER PROGRAMS),
1285 | EVEN IF SUCH HOLDER OR OTHER PARTY HAS BEEN ADVISED OF THE POSSIBILITY OF
1286 | SUCH DAMAGES.
1287 |
1288 | 17. Interpretation of Sections 15 and 16.
1289 |
1290 | If the disclaimer of warranty and limitation of liability provided
1291 | above cannot be given local legal effect according to their terms,
1292 | reviewing courts shall apply local law that most closely approximates
1293 | an absolute waiver of all civil liability in connection with the
1294 | Program, unless a warranty or assumption of liability accompanies a
1295 | copy of the Program in return for a fee.
1296 |
1297 | END OF TERMS AND CONDITIONS
1298 |
1299 | How to Apply These Terms to Your New Programs
1300 |
1301 | If you develop a new program, and you want it to be of the greatest
1302 | possible use to the public, the best way to achieve this is to make it
1303 | free software which everyone can redistribute and change under these terms.
1304 |
1305 | To do so, attach the following notices to the program. It is safest
1306 | to attach them to the start of each source file to most effectively
1307 | state the exclusion of warranty; and each file should have at least
1308 | the "copyright" line and a pointer to where the full notice is found.
1309 |
1310 |
1311 | Copyright (C)
1312 |
1313 | This program is free software: you can redistribute it and/or modify
1314 | it under the terms of the GNU General Public License as published by
1315 | the Free Software Foundation, either version 3 of the License, or
1316 | (at your option) any later version.
1317 |
1318 | This program is distributed in the hope that it will be useful,
1319 | but WITHOUT ANY WARRANTY; without even the implied warranty of
1320 | MERCHANTABILITY or FITNESS FOR A PARTICULAR PURPOSE. See the
1321 | GNU General Public License for more details.
1322 |
1323 | You should have received a copy of the GNU General Public License
1324 | along with this program. If not, see .
1325 |
1326 | Also add information on how to contact you by electronic and paper mail.
1327 |
1328 | If the program does terminal interaction, make it output a short
1329 | notice like this when it starts in an interactive mode:
1330 |
1331 | Copyright (C)
1332 | This program comes with ABSOLUTELY NO WARRANTY; for details type `show w'.
1333 | This is free software, and you are welcome to redistribute it
1334 | under certain conditions; type `show c' for details.
1335 |
1336 | The hypothetical commands `show w' and `show c' should show the appropriate
1337 | parts of the General Public License. Of course, your program's commands
1338 | might be different; for a GUI interface, you would use an "about box".
1339 |
1340 | You should also get your employer (if you work as a programmer) or school,
1341 | if any, to sign a "copyright disclaimer" for the program, if necessary.
1342 | For more information on this, and how to apply and follow the GNU GPL, see
1343 | .
1344 |
1345 | The GNU General Public License does not permit incorporating your program
1346 | into proprietary programs. If your program is a subroutine library, you
1347 | may consider it more useful to permit linking proprietary applications with
1348 | the library. If this is what you want to do, use the GNU Lesser General
1349 | Public License instead of this License. But first, please read
1350 | .
1351 | >>>>>>> c99cffb10ec82a36ff0fd53805b9022f6af0aee4
1352 |
--------------------------------------------------------------------------------
/README.md:
--------------------------------------------------------------------------------
1 | # vulscan - Vulnerability Scanning with Nmap
2 |
3 |
4 |  5 |
5 |
6 |
7 | ## Introduction
8 |
9 | Vulscan is a module which enhances nmap to a vulnerability scanner. The nmap option -sV enables version detection per service which is used to determine potential flaws according to the identified product. The data is looked up in an offline version of VulDB.
10 |
11 | 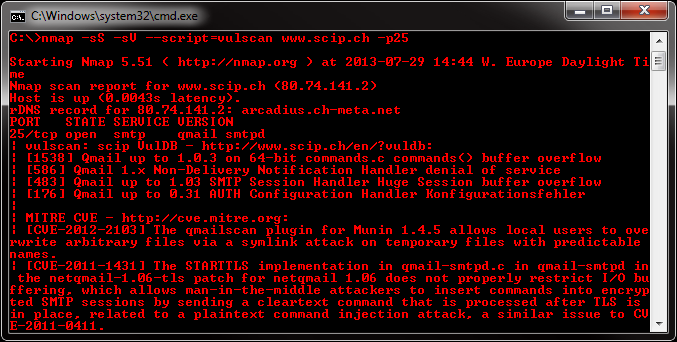
12 |
13 | ## Installation
14 |
15 | Please install the files into the following folder of your Nmap installation:
16 |
17 | Nmap\scripts\vulscan\*
18 |
19 | Clone the GitHub repository like this:
20 |
21 | git clone https://github.com/scipag/vulscan scipag_vulscan
22 | ln -s `pwd`/scipag_vulscan /usr/share/nmap/scripts/vulscan
23 |
24 | ## Usage
25 |
26 | You have to run the following minimal command to initiate a simple vulnerability scan:
27 |
28 | nmap -sV --script=vulscan/vulscan.nse www.example.com
29 |
30 | ## Vulnerability Database
31 |
32 | There are the following pre-installed databases available at the moment:
33 |
34 | * scipvuldb.csv - https://vuldb.com
35 | * cve.csv - https://cve.mitre.org
36 | * securityfocus.csv - https://www.securityfocus.com/bid/
37 | * xforce.csv - https://exchange.xforce.ibmcloud.com/
38 | * expliotdb.csv - https://www.exploit-db.com
39 | * openvas.csv - http://www.openvas.org
40 | * securitytracker.csv - https://www.securitytracker.com (end-of-life)
41 | * osvdb.csv - http://www.osvdb.org (end-of-life)
42 |
43 | ## Single Database Mode
44 |
45 | You may execute vulscan with the following argument to use a single database:
46 |
47 | --script-args vulscandb=your_own_database
48 |
49 | It is also possible to create and reference your own databases. This requires to create a database file, which has the following structure:
50 |
51 | ;
52 |
53 | Just execute vulscan like you would by refering to one of the pre-delivered databases. Feel free to share your own database and vulnerability connection with me, to add it to the official repository.
54 |
55 | ## Update Database
56 |
57 | The vulnerability databases are updated and assembled on a regularly basis. To support the latest disclosed vulnerabilities, keep your local vulnerability databases up-to-date.
58 |
59 | If you want to update your databases, go to the following web site and download these files:
60 |
61 | * https://www.computec.ch/projekte/vulscan/download/cve.csv
62 | * https://www.computec.ch/projekte/vulscan/download/exploitdb.csv
63 | * https://www.computec.ch/projekte/vulscan/download/openvas.csv
64 | * https://www.computec.ch/projekte/vulscan/download/osvdb.csv
65 | * https://www.computec.ch/projekte/vulscan/download/scipvuldb.csv
66 | * https://www.computec.ch/projekte/vulscan/download/securityfocus.csv
67 | * https://www.computec.ch/projekte/vulscan/download/securitytracker.csv
68 | * https://www.computec.ch/projekte/vulscan/download/xforce.csv
69 |
70 | Copy the files into your vulscan folder:
71 |
72 | /vulscan/
73 |
74 | ## Version Detection
75 |
76 | If the version detection was able to identify the software version and the vulnerability database is providing such details, also this data is matched.
77 |
78 | Disabling this feature might introduce false-positive but might also eliminate false-negatives and increase performance slighty. If you want to disable additional version matching, use the following argument:
79 |
80 | --script-args vulscanversiondetection=0
81 |
82 | Version detection of vulscan is only as good as Nmap version detection and the vulnerability database entries are. Some databases do not provide conclusive version information, which may lead to a lot of false-positives (as can be seen for Apache servers).
83 |
84 | ## Match Priority
85 |
86 | The script is trying to identify the best matches only. If no positive match could been found, the best possible match (with might be a false-positive) is put on display.
87 |
88 | If you want to show all matches, which might introduce a lot of false-positives but might be useful for further investigation, use the following argument:
89 |
90 | --script-args vulscanshowall=1
91 |
92 | ## Interactive Mode
93 |
94 | The interactive mode helps you to override version detection results for every port. Use the following argument to enable the interactive mode:
95 |
96 | --script-args vulscaninteractive=1
97 |
98 | ## Reporting
99 |
100 | All matching results are printed one by line. The default layout for this is:
101 |
102 | [{id}] {title}\n
103 |
104 | It is possible to use another pre-defined report structure with the following argument:
105 |
106 | --script-args vulscanoutput=details
107 | --script-args vulscanoutput=listid
108 | --script-args vulscanoutput=listlink
109 | --script-args vulscanoutput=listtitle
110 |
111 | You may enforce your own report structure by using the following argument (some examples):
112 |
113 | --script-args vulscanoutput='{link}\n{title}\n\n'
114 | --script-args vulscanoutput='ID: {id} - Title: {title} ({matches})\n'
115 | --script-args vulscanoutput='{id} | {product} | {version}\n'
116 |
117 | Supported are the following elements for a dynamic report template:
118 |
119 | * {id} - ID of the vulnerability
120 | * {title} - Title of the vulnerability
121 | * {matches} - Count of matches
122 | * {product} - Matched product string(s)
123 | * {version} - Matched version string(s)
124 | * {link} - Link to the vulnerability database entry
125 | * \n - Newline
126 | * \t - Tab
127 |
128 | Every default database comes with an url and a link, which is used during the scanning and might be accessed as {link} within the customized report template. To use custom database links, use the following argument:
129 |
130 | --script-args "vulscandblink=http://example.org/{id}"
131 |
132 | ## Disclaimer
133 |
134 | Keep in mind that this kind of derivative vulnerability scanning heavily relies on the confidence of the version detection of nmap, the amount of documented vulnerabilities and the accuracy of pattern matching. The existence of potential flaws is not verified with additional scanning nor exploiting techniques.
135 |
--------------------------------------------------------------------------------
/_config.yml:
--------------------------------------------------------------------------------
1 | theme: jekyll-theme-tactile
--------------------------------------------------------------------------------
/cve.csv:
--------------------------------------------------------------------------------
https://raw.githubusercontent.com/Gameye98/vulscan/8db27bb765af0f8c101e99afc8a3d9e12c123841/cve.csv
--------------------------------------------------------------------------------
/exploitdb.csv:
--------------------------------------------------------------------------------
https://raw.githubusercontent.com/Gameye98/vulscan/8db27bb765af0f8c101e99afc8a3d9e12c123841/exploitdb.csv
--------------------------------------------------------------------------------
/logo.png:
--------------------------------------------------------------------------------
https://raw.githubusercontent.com/Gameye98/vulscan/8db27bb765af0f8c101e99afc8a3d9e12c123841/logo.png
--------------------------------------------------------------------------------
/openvas.csv:
--------------------------------------------------------------------------------
https://raw.githubusercontent.com/Gameye98/vulscan/8db27bb765af0f8c101e99afc8a3d9e12c123841/openvas.csv
--------------------------------------------------------------------------------
/osvdb.csv:
--------------------------------------------------------------------------------
https://raw.githubusercontent.com/Gameye98/vulscan/8db27bb765af0f8c101e99afc8a3d9e12c123841/osvdb.csv
--------------------------------------------------------------------------------
/securityfocus.csv:
--------------------------------------------------------------------------------
https://raw.githubusercontent.com/Gameye98/vulscan/8db27bb765af0f8c101e99afc8a3d9e12c123841/securityfocus.csv
--------------------------------------------------------------------------------
/securitytracker.csv:
--------------------------------------------------------------------------------
https://raw.githubusercontent.com/Gameye98/vulscan/8db27bb765af0f8c101e99afc8a3d9e12c123841/securitytracker.csv
--------------------------------------------------------------------------------
/utilities/docker/Dockerfile:
--------------------------------------------------------------------------------
1 | FROM alpine:latest
2 |
3 | RUN apk --update add nmap \
4 | nmap-scripts \
5 | git \
6 | bash
7 |
8 | RUN git clone https://github.com/scipag/vulscan.git /usr/share/nmap/scripts/vulscan
9 |
10 | WORKDIR /usr/share/nmap/scripts/vulscan
11 |
12 | #Update CVE databases
13 | CMD ["/bin/bash","updateFiles.sh"]
14 |
15 | ENTRYPOINT ["nmap"]
16 | CMD ["-h"]
17 |
18 |
--------------------------------------------------------------------------------
/utilities/docker/Dockerfile_README.md:
--------------------------------------------------------------------------------
1 | # Nmap, nmap scripts, vulscan
2 |
3 | ## Abstract
4 | Comes fully equipped with
5 | the latest Nmap Scripting Engine (NSE) modules, as well as the [Vulscan](https://github.com/scipag/vulscan) NSE script.
6 | The databases used by Vulscan are pulled using the original updater script when image is built
7 |
8 | ## Source
9 |
10 | https://github.com/scipag/vulscan
11 |
12 | ## Usage
13 |
14 | ```bash
15 | docker build -t vulscan .
16 | docker run -it vulscan:latest
17 | ```
18 |
19 | ## Help:
20 |
21 | ```bash
22 | docker run -it nmap -sV --script=vulscan/vulscan.nse www.example.com
23 | ```
24 |
25 | ## Demo
26 | [](https://asciinema.org/a/141837)
27 |
28 |
--------------------------------------------------------------------------------
/utilities/updater/updateFiles.sh:
--------------------------------------------------------------------------------
1 | #!/bin/bash
2 | ##
3 | ## Declare all the sites that you want to download the cvs files from into an array.
4 | ## Error codes:
5 | ## 0 - Everything went fine, no updated files
6 | ## 1 - Everything went fine, at least one updated file
7 | ##
8 | ## The exit status can be used to help other scripts decide if it is time to update
9 | ## the files in the vulscan folder.
10 | ##
11 | declare -a FILES=(
12 | "https://raw.githubusercontent.com/scipag/vulscan/master/cve.csv"
13 | "https://raw.githubusercontent.com/scipag/vulscan/master/exploitdb.csv"
14 | "https://raw.githubusercontent.com/scipag/vulscan/master/openvas.csv"
15 | "https://raw.githubusercontent.com/scipag/vulscan/master/osvdb.csv"
16 | "https://raw.githubusercontent.com/scipag/vulscan/master/scipvuldb.csv"
17 | "https://raw.githubusercontent.com/scipag/vulscan/master/securityfocus.csv"
18 | "https://raw.githubusercontent.com/scipag/vulscan/master/securitytracker.csv"
19 | "https://raw.githubusercontent.com/scipag/vulscan/master/xforce.csv"
20 | )
21 |
22 | UPDATED=false
23 |
24 | ##
25 | ## Enable / Disable debug output.
26 | ##
27 | DEBUG=true
28 |
29 | ##
30 | ## Simple debug function, to help debug if debug is on.
31 | ## example use:
32 | ## logIfDebug "Hello world!"
33 | ##
34 | function logIfDebug(){
35 | if [ $DEBUG = true ]
36 | then
37 | echo "$1"
38 | fi
39 | }
40 |
41 | ##
42 | ## Create teporary download directory
43 | ##
44 | mkdir -p downloading
45 |
46 | ##
47 | ## Work from the temp directory
48 | ##
49 | cd downloading
50 |
51 | ##
52 | ## For each file, we want to download it, and see if it differs from old one.
53 | ## If it differs, we assume that it is new, and thus we want to replace the old one.
54 | ## Unfortunately GitHub is issuing the cert for www.github.com only and not for other
55 | ## domains which is why we need to ignore cert warnings
56 | ##
57 | for file in "${FILES[@]}"
58 | do
59 | logIfDebug "Downloading ${file}..."
60 | wget --quiet --no-check-certificate ${file}
61 | filename=$(echo ${file} | awk -F/ '{print $NF}')
62 | result=$(diff --suppress-common-lines --speed-large-files -y ${filename} ../../../${filename} | wc -l)
63 | if [ ${result} -ne 0 ]; then
64 | logIfDebug "Updating ${filename} as it differs"
65 | mv ${filename} ../../../
66 | UPDATED=true
67 | fi
68 | done
69 |
70 | ##
71 | ## Remove the temporary directory
72 | ##
73 | cd ..
74 | rm -rf downloading
75 |
76 | ##
77 | ## All is well, exit with error code 0.
78 | ##
79 | if [ $UPDATED = true ]
80 | then
81 | logIfDebug "Returning 1, as at least one file has been updated."
82 | exit 1;
83 | else
84 | logIfDebug "Returning 0, as no files have been updated, but script ran successfully"
85 | exit 0;
86 | fi
87 |
--------------------------------------------------------------------------------
/vulscan.nse:
--------------------------------------------------------------------------------
1 | description = [[
2 |
3 | INTRODUCTION
4 |
5 | Vulscan is a module which enhances nmap to a vulnerability scanner. The
6 | nmap option -sV enables version detection per service which is used to
7 | determine potential flaws according to the identified product. The data
8 | is looked up in an offline version of VulDB.
9 |
10 | INSTALLATION
11 |
12 | Please install the files into the following folder of your Nmap
13 | installation:
14 |
15 | Nmap\scripts\vulscan\*
16 |
17 | USAGE
18 |
19 | You have to run the following minimal command to initiate a simple
20 | vulnerability scan:
21 |
22 | nmap -sV --script=vulscan/vulscan.nse www.example.com
23 |
24 | VULNERABILITY DATABASE
25 |
26 | There are the following pre-installed databases available at the
27 | moment:
28 |
29 | scipvuldb.csv | https://vuldb.com
30 | cve.csv | https://cve.mitre.org
31 | securityfocus.csv | https://www.securityfocus.com/bid/
32 | xforce.csv | https://exchange.xforce.ibmcloud.com/
33 | expliotdb.csv | https://www.exploit-db.com
34 | openvas.csv | http://www.openvas.org
35 | securitytracker.csv | https://www.securitytracker.com (end-of-life)
36 | osvdb.csv | http://www.osvdb.org (end-of-life)
37 |
38 | SINGLE DATABASE MODE
39 |
40 | You may execute vulscan with the following argument to use a single
41 | database:
42 |
43 | --script-args vulscandb=your_own_database
44 |
45 | It is also possible to create and reference your own databases. This
46 | requires to create a database file, which has the following structure:
47 |
48 | <id>;<title>
49 |
50 | Just execute vulscan like you would by refering to one of the pre-
51 | delivered databases. Feel free to share your own database and
52 | vulnerability connection with me, to add it to the official
53 | repository.
54 |
55 | UPDATE DATABASE
56 |
57 | The vulnerability databases are updated and assembled on a regularly
58 | basis. To support the latest disclosed vulnerabilities, keep your local
59 | vulnerability databases up-to-date.
60 |
61 | If you want to update your databases, go to the following web site and
62 | download these files:
63 |
64 | https://www.computec.ch/mruef/software/nmap_nse_vulscan/cve.csv
65 | https://www.computec.ch/mruef/software/nmap_nse_vulscan/exploitdb.csv
66 | https://www.computec.ch/mruef/software/nmap_nse_vulscan/openvas.csv
67 | https://www.computec.ch/mruef/software/nmap_nse_vulscan/osvdb.csv
68 | https://www.computec.ch/mruef/software/nmap_nse_vulscan/scipvuldb.csv
69 | https://www.computec.ch/mruef/software/nmap_nse_vulscan/securityfocus.csv
70 | https://www.computec.ch/mruef/software/nmap_nse_vulscan/securitytracker.csv
71 | https://www.computec.ch/mruef/software/nmap_nse_vulscan/xforce.csv
72 |
73 | Copy the files into your vulscan folder:
74 |
75 | /vulscan/
76 |
77 | Clone the GitHub repository like this:
78 |
79 | git clone https://github.com/scipag/vulscan scipag_vulscan
80 | ln -s `pwd`/scipag_vulscan /usr/share/nmap/scripts/vulscan
81 |
82 | VERSION DETECTION
83 |
84 | If the version detection was able to identify the software version and
85 | the vulnerability database is providing such details, also this data
86 | is matched.
87 |
88 | Disabling this feature might introduce false-positive but might also
89 | eliminate false-negatives and increase performance slighty. If you want
90 | to disable additional version matching, use the following argument:
91 |
92 | --script-args vulscanversiondetection=0
93 |
94 | Version detection of vulscan is only as good as Nmap version detection
95 | and the vulnerability database entries are. Some databases do not
96 | provide conclusive version information, which may lead to a lot of
97 | false-positives (as can be seen for Apache servers).
98 |
99 | MATCH PRIORITY
100 |
101 | The script is trying to identify the best matches only. If no positive
102 | match could been found, the best possible match (with might be a false-
103 | positive) is put on display.
104 |
105 | If you want to show all matches, which might introduce a lot of false-
106 | positives but might be useful for further investigation, use the
107 | following argument:
108 |
109 | --script-args vulscanshowall=1
110 |
111 | INTERACTIVE MODE
112 |
113 | The interactive mode helps you to override version detection results
114 | for every port. Use the following argument to enable the interactive
115 | mode:
116 |
117 | --script-args vulscaninteractive=1
118 |
119 | REPORTING
120 |
121 | All matching results are printed one by line. The default layout for
122 | this is:
123 |
124 | [{id}] {title}\n
125 |
126 | It is possible to use another pre-defined report structure with the
127 | following argument:
128 |
129 | --script-args vulscanoutput=details
130 | --script-args vulscanoutput=listid
131 | --script-args vulscanoutput=listlink
132 | --script-args vulscanoutput=listtitle
133 |
134 | You may enforce your own report structure by using the following
135 | argument (some examples):
136 |
137 | --script-args vulscanoutput='{link}\n{title}\n\n'
138 | --script-args vulscanoutput='ID: {id} - Title: {title} ({matches})\n'
139 | --script-args vulscanoutput='{id} | {product} | {version}\n'
140 |
141 | Supported are the following elements for a dynamic report template:
142 |
143 | {id} ID of the vulnerability
144 | {title} Title of the vulnerability
145 | {matches} Count of matches
146 | {product} Matched product string(s)
147 | {version} Matched version string(s)
148 | {link} Link to the vulnerability database entry
149 | \n Newline
150 | \t Tab
151 |
152 | Every default database comes with an url and a link, which is used
153 | during the scanning and might be accessed as {link} within the
154 | customized report template. To use custom database links, use the
155 | following argument:
156 |
157 | --script-args "vulscandblink=http://example.org/{id}"
158 |
159 | DISCLAIMER
160 |
161 | Keep in mind that this kind of derivative vulnerability scanning
162 | heavily relies on the confidence of the version detection of nmap, the
163 | amount of documented vulnerebilities and the accuracy of pattern
164 | matching. The existence of potential flaws is not verified with
165 | additional scanning nor exploiting techniques.
166 |
167 | LINKS
168 |
169 | Download: https://www.computec.ch/mruef/?s=software&l=x
170 |
171 | ]]
172 |
173 | --@output
174 | -- PORT STATE SERVICE REASON VERSION
175 | -- 25/tcp open smtp syn-ack Exim smtpd 4.69
176 | -- | osvdb (22 findings):
177 | -- | [2440] qmailadmin autorespond Multiple Variable Remote Overflow
178 | -- | [3538] qmail Long SMTP Session DoS
179 | -- | [5850] qmail RCPT TO Command Remote Overflow DoS
180 | -- | [14176] MasqMail Piped Aliases Privilege Escalation
181 |
182 | --@changelog
183 | -- v2.2 | 09/20/2019 | Marc Ruef | Fixed support for Nmap 7.80 onwards
184 | -- v2.1 | 04/17/2019 | Marc Ruef | Minor fixes
185 | -- v2.0 | 08/14/2013 | Marc Ruef | Considering version data
186 | -- v1.0 | 06/18/2013 | Marc Ruef | Dynamic report structures
187 | -- v0.8 | 06/17/2013 | Marc Ruef | Multi-database support
188 | -- v0.7 | 06/14/2013 | Marc Ruef | Complete re-write of search engine
189 | -- v0.6 | 05/22/2010 | Marc Ruef | Added interactive mode for guided testing
190 | -- v0.5 | 05/21/2010 | Marc Ruef | Seperate functions for search engine
191 | -- v0.4 | 05/20/2010 | Marc Ruef | Tweaked analysis modules
192 | -- v0.3 | 05/19/2010 | Marc Ruef | Fuzzy search for product names included
193 | -- v0.2 | 05/18/2010 | Marc Ruef | Uniqueness of found vulnerabilities
194 | -- v0.1 | 05/17/2010 | Marc Ruef | First alpha running basic identification
195 |
196 | --@bugs
197 | -- Fuzzy search is sometimes catching wrong products
198 |
199 | --@todos
200 | -- Create product lookup table to match nmap<->db
201 | -- Enhance nmap/db to be CPE compliant (https://cpe.mitre.org)
202 | -- Display of identification confidence (e.g. +full_match, -partial_match)
203 | -- Add auto-update feature for databases (download & install)
204 |
205 | --@thanks
206 | -- I would like to thank a number of people which supported me in
207 | -- developing this script: Stefan Friedli, Simon Zumstein, Sean Rütschi,
208 | -- Pascal Schaufelberger, David Fifield, Nabil Ouchn, Doggy Dog, Matt
209 | -- Brown, Matthew Phillips, and Sebastian Brabetzl.
210 |
211 | author = "Marc Ruef, marc.ruef-at-computec.ch, https://www.computec.ch/mruef/"
212 | license = "Same as Nmap--See https://nmap.org/book/man-legal.html"
213 | categories = {"default", "safe", "vuln"}
214 |
215 | local stdnse = require("stdnse")
216 | local have_stringaux, stringaux = pcall(require, "stringaux")
217 | local strsplit = (have_stringaux and stringaux or stdnse).strsplit
218 |
219 | portrule = function(host, port)
220 | if port.version.product ~= nil and port.version.product ~= "" then
221 | return true
222 | else
223 | stdnse.print_debug(1, "vulscan: No version detection data available. Analysis not possible.")
224 | end
225 | end
226 |
227 | action = function(host, port)
228 | local prod = port.version.product -- product name
229 | local ver = port.version.version -- product version
230 | local struct = "[{id}] {title}\n" -- default report structure
231 | local db = {} -- vulnerability database
232 | local db_link = "" -- custom link for vulnerability databases
233 | local vul = {} -- details for the vulnerability
234 | local v_count = 0 -- counter for the vulnerabilities
235 | local s = "" -- the output string
236 |
237 | stdnse.print_debug(1, "vulscan: Found service " .. prod)
238 |
239 | -- Go into interactive mode
240 | if nmap.registry.args.vulscaninteractive == "1" then
241 | stdnse.print_debug(1, "vulscan: Enabling interactive mode ...")
242 | print("The scan has determined the following product:")
243 | print(prod)
244 | print("Press Enter to accept. Define new string to override.")
245 | local prod_override = io.stdin:read'*l'
246 |
247 | if string.len(prod_override) ~= 0 then
248 | prod = prod_override
249 | stdnse.print_debug(1, "vulscan: Product overwritten as " .. prod)
250 | end
251 | end
252 |
253 | -- Read custom report structure
254 | if nmap.registry.args.vulscanoutput ~= nil then
255 | if nmap.registry.args.vulscanoutput == "details" then
256 | struct = "[{id}] {title}\nMatches: {matches}, Prod: {product}, Ver: {version}\n{link}\n\n"
257 | elseif nmap.registry.args.vulscanoutput == "listid" then
258 | struct = "{id}\n"
259 | elseif nmap.registry.args.vulscanoutput == "listlink" then
260 | struct = "{link}\n"
261 | elseif nmap.registry.args.vulscanoutput == "listtitle" then
262 | struct = "{title}\n"
263 | else
264 | struct = nmap.registry.args.vulscanoutput
265 | end
266 |
267 | stdnse.print_debug(1, "vulscan: Custom output structure defined as " .. struct)
268 | end
269 |
270 | -- Read custom database link
271 | if nmap.registry.args.vulscandblink ~= nil then
272 | db_link = nmap.registry.args.vulscandblink
273 | stdnse.print_debug(1, "vulscan: Custom database link defined as " .. db_link)
274 | end
275 |
276 | if nmap.registry.args.vulscandb then
277 | stdnse.print_debug(1, "vulscan: Using single mode db " .. nmap.registry.args.vulscandb .. " ...")
278 | vul = find_vulnerabilities(prod, ver, nmap.registry.args.vulscandb)
279 | if #vul > 0 then
280 | s = s .. nmap.registry.args.vulscandb
281 | if db_link ~= "" then s = s .. " - " .. db_link end
282 | s = s .. ":\n" .. prepare_result(vul, struct, db_link) .. "\n\n"
283 | end
284 | else
285 | -- Add your own database, if you want to include it in the multi db mode
286 | db[1] = {name="VulDB", file="scipvuldb.csv", url="https://vuldb.com", link="https://vuldb.com/id.{id}"}
287 | db[2] = {name="MITRE CVE", file="cve.csv", url="https://cve.mitre.org", link="https://cve.mitre.org/cgi-bin/cvename.cgi?name={id}"}
288 | db[3] = {name="SecurityFocus", file="securityfocus.csv", url="https://www.securityfocus.com/bid/", link="https://www.securityfocus.com/bid/{id}"}
289 | db[4] = {name="IBM X-Force", file="xforce.csv", url="https://exchange.xforce.ibmcloud.com", link="https://exchange.xforce.ibmcloud.com/vulnerabilities/{id}"}
290 | db[5] = {name="Exploit-DB", file="exploitdb.csv", url="https://www.exploit-db.com", link="https://www.exploit-db.com/exploits/{id}"}
291 | db[6] = {name="OpenVAS (Nessus)", file="openvas.csv", url="http://www.openvas.org", link="https://www.tenable.com/plugins/nessus/{id}"}
292 | db[7] = {name="SecurityTracker", file="securitytracker.csv", url="https://www.securitytracker.com", link="https://www.securitytracker.com/id/{id}"}
293 | db[8] = {name="OSVDB", file="osvdb.csv", url="http://www.osvdb.org", link="http://www.osvdb.org/{id}"}
294 |
295 | stdnse.print_debug(1, "vulscan: Using multi db mode (" .. #db .. " databases) ...")
296 | for i,v in ipairs(db) do
297 | vul = find_vulnerabilities(prod, ver, v.file)
298 |
299 | s = s .. v.name .. " - " .. v.url .. ":\n"
300 | if #vul > 0 then
301 | v_count = v_count + #vul
302 | s = s .. prepare_result(vul, struct, v.link) .. "\n"
303 | else
304 | s = s .. "No findings\n\n"
305 | end
306 |
307 | stdnse.print_debug(1, "vulscan: " .. #vul .. " matches in " .. v.file)
308 | end
309 |
310 | stdnse.print_debug(1, "vulscan: " .. v_count .. " matches in total")
311 | end
312 |
313 | if s then
314 | return s
315 | end
316 | end
317 |
318 | -- Find the product matches in the vulnerability databases
319 | function find_vulnerabilities(prod, ver, db)
320 | local v = {} -- matching vulnerabilities
321 | local v_id -- id of vulnerability
322 | local v_title -- title of vulnerability
323 | local v_title_lower -- title of vulnerability in lowercase for speedup
324 | local v_found -- if a match could be found
325 |
326 | -- Load database
327 | local v_entries = read_from_file("scripts/vulscan/" .. db)
328 |
329 | -- Clean useless dataparts (speeds up search and improves accuracy)
330 | prod = string.gsub(prod, " httpd", "")
331 | prod = string.gsub(prod, " smtpd", "")
332 | prod = string.gsub(prod, " ftpd", "")
333 |
334 | local prod_words = strsplit(" ", prod)
335 |
336 | stdnse.print_debug(1, "vulscan: Starting search of " .. prod ..
337 | " in " .. db ..
338 | " (" .. #v_entries .. " entries) ...")
339 |
340 | -- Iterate through the vulnerabilities in the database
341 | for i=1, #v_entries, 1 do
342 | v_id = extract_from_table(v_entries[i], 1, ";")
343 | v_title = extract_from_table(v_entries[i], 2, ";")
344 |
345 | if type(v_title) == "string" then
346 | v_title_lower = string.lower(v_title)
347 |
348 | -- Find the matches for the database entry
349 | for j=1, #prod_words, 1 do
350 | v_found = string.find(v_title_lower, escape(string.lower(prod_words[j])), 1)
351 | if type(v_found) == "number" then
352 | if #v == 0 then
353 | -- Initiate table
354 | v[1] = {
355 | id = v_id,
356 | title = v_title,
357 | product = prod_words[j],
358 | version = "",
359 | matches = 1
360 | }
361 | elseif v[#v].id ~= v_id then
362 | -- Create new entry
363 | v[#v+1] = {
364 | id = v_id,
365 | title = v_title,
366 | product = prod_words[j],
367 | version = "",
368 | matches = 1
369 | }
370 | else
371 | -- Add to current entry
372 | v[#v].product = v[#v].product .. " " .. prod_words[j]
373 | v[#v].matches = v[#v].matches+1
374 | end
375 |
376 | stdnse.print_debug(2, "vulscan: Match v_id " .. v_id ..
377 | " -> v[" .. #v .. "] " ..
378 | "(" .. v[#v].matches .. " match) " ..
379 | "(Prod: " .. prod_words[j] .. ")")
380 | end
381 | end
382 |
383 | -- Additional version matching
384 | if nmap.registry.args.vulscanversiondetection ~= "0" and ver ~= nil and ver ~= "" then
385 | if v[#v] ~= nil and v[#v].id == v_id then
386 | for k=0, string.len(ver)-1, 1 do
387 | v_version = string.sub(ver, 1, string.len(ver)-k)
388 | v_found = string.find(string.lower(v_title), string.lower(" " .. v_version), 1)
389 |
390 | if type(v_found) == "number" then
391 | v[#v].version = v[#v].version .. v_version .. " "
392 | v[#v].matches = v[#v].matches+1
393 |
394 | stdnse.print_debug(2, "vulscan: Match v_id " .. v_id ..
395 | " -> v[" .. #v .. "] " ..
396 | "(" .. v[#v].matches .. " match) " ..
397 | "(Version: " .. v_version .. ")")
398 | end
399 | end
400 | end
401 | end
402 | end
403 | end
404 |
405 | return v
406 | end
407 |
408 | -- Prepare the resulting matches
409 | function prepare_result(v, struct, link)
410 | local grace = 0 -- grace trigger
411 | local match_max = 0 -- counter for maximum matches
412 | local match_max_title = "" -- title of the maximum match
413 | local s = "" -- the output string
414 |
415 | -- Search the entries with the best matches
416 | if #v > 0 then
417 | -- Find maximum matches
418 | for i=1, #v, 1 do
419 | if v[i].matches > match_max then
420 | match_max = v[i].matches
421 | match_max_title = v[i].title
422 | end
423 | end
424 |
425 | stdnse.print_debug(2, "vulscan: Maximum matches of a finding are " ..
426 | match_max .. " (" .. match_max_title .. ")")
427 |
428 | if match_max > 0 then
429 | for matchpoints=match_max, 1, -1 do
430 | for i=1, #v, 1 do
431 | if v[i].matches == matchpoints then
432 | stdnse.print_debug(2, "vulscan: Setting up result id " .. i)
433 | s = s .. report_parsing(v[i], struct, link)
434 | end
435 | end
436 |
437 | if nmap.registry.args.vulscanshowall ~= "1" and s ~= "" then
438 | -- If the next iteration shall be approached (increases matches)
439 | if grace == 0 then
440 | stdnse.print_debug(2, "vulscan: Best matches found in 1st pass. Going to use 2nd pass ...")
441 | grace = grace+1
442 | elseif nmap.registry.args.vulscanshowall ~= "1" then
443 | break
444 | end
445 | end
446 | end
447 | end
448 | end
449 |
450 | return s
451 | end
452 |
453 | -- Parse the report output structure
454 | function report_parsing(v, struct, link)
455 | local s = struct
456 |
457 | --database data (needs to be first)
458 | s = string.gsub(s, "{link}", escape(link))
459 |
460 | --layout elements (needs to be second)
461 | s = string.gsub(s, "\\n", "\n")
462 | s = string.gsub(s, "\\t", "\t")
463 |
464 | --vulnerability data (needs to be third)
465 | s = string.gsub(s, "{id}", escape(v.id))
466 | s = string.gsub(s, "{title}", escape(v.title))
467 | s = string.gsub(s, "{matches}", escape(v.matches))
468 | s = string.gsub(s, "{product}", escape(v.product))
469 | s = string.gsub(s, "{version}", escape(v.version))
470 |
471 | return s
472 | end
473 |
474 | -- Get the row of a CSV file
475 | function extract_from_table(line, col, del)
476 | local val = strsplit(del, line)
477 |
478 | if type(val[col]) == "string" then
479 | return val[col]
480 | end
481 | end
482 |
483 | -- Read a file
484 | function read_from_file(file)
485 | local filepath = nmap.fetchfile(file)
486 |
487 | if filepath then
488 | local f, err, _ = io.open(filepath, "r")
489 | if not f then
490 | stdnse.print_debug(1, "vulscan: Failed to open file" .. file)
491 | end
492 |
493 | local line, ret = nil, {}
494 | while true do
495 | line = f:read()
496 | if not line then break end
497 | ret[#ret+1] = line
498 | end
499 |
500 | f:close()
501 |
502 | return ret
503 | else
504 | stdnse.print_debug(1, "vulscan: File " .. file .. " not found")
505 | return ""
506 | end
507 | end
508 |
509 | -- We don't like unescaped things
510 | function escape(s)
511 | s = string.gsub(s, "%%", "%%%%")
512 | return s
513 | end
514 |
--------------------------------------------------------------------------------
/xforce.csv:
--------------------------------------------------------------------------------
https://raw.githubusercontent.com/Gameye98/vulscan/8db27bb765af0f8c101e99afc8a3d9e12c123841/xforce.csv
--------------------------------------------------------------------------------
 5 |
5 |  5 |
5 |