├── LICENSE
├── README.md
├── bin
└── proxmox-update
├── pbs
├── LICENSE
├── README.md
├── filter.d
│ └── proxmox-backup-server.conf
└── jail.d
│ └── proxmox-backup-server.conf
├── proxmox_toolbox.sh
├── pve
├── filter.d
│ └── proxmox-virtual-environement.conf
└── jail.d
│ └── proxmox-virtual-environement.conf
└── snmp
└── snmpd.conf
/LICENSE:
--------------------------------------------------------------------------------
1 | GNU GENERAL PUBLIC LICENSE
2 | Version 3, 29 June 2007
3 |
4 | Copyright (C) 2007 Free Software Foundation, Inc.
5 | Everyone is permitted to copy and distribute verbatim copies
6 | of this license document, but changing it is not allowed.
7 |
8 | Preamble
9 |
10 | The GNU General Public License is a free, copyleft license for
11 | software and other kinds of works.
12 |
13 | The licenses for most software and other practical works are designed
14 | to take away your freedom to share and change the works. By contrast,
15 | the GNU General Public License is intended to guarantee your freedom to
16 | share and change all versions of a program--to make sure it remains free
17 | software for all its users. We, the Free Software Foundation, use the
18 | GNU General Public License for most of our software; it applies also to
19 | any other work released this way by its authors. You can apply it to
20 | your programs, too.
21 |
22 | When we speak of free software, we are referring to freedom, not
23 | price. Our General Public Licenses are designed to make sure that you
24 | have the freedom to distribute copies of free software (and charge for
25 | them if you wish), that you receive source code or can get it if you
26 | want it, that you can change the software or use pieces of it in new
27 | free programs, and that you know you can do these things.
28 |
29 | To protect your rights, we need to prevent others from denying you
30 | these rights or asking you to surrender the rights. Therefore, you have
31 | certain responsibilities if you distribute copies of the software, or if
32 | you modify it: responsibilities to respect the freedom of others.
33 |
34 | For example, if you distribute copies of such a program, whether
35 | gratis or for a fee, you must pass on to the recipients the same
36 | freedoms that you received. You must make sure that they, too, receive
37 | or can get the source code. And you must show them these terms so they
38 | know their rights.
39 |
40 | Developers that use the GNU GPL protect your rights with two steps:
41 | (1) assert copyright on the software, and (2) offer you this License
42 | giving you legal permission to copy, distribute and/or modify it.
43 |
44 | For the developers' and authors' protection, the GPL clearly explains
45 | that there is no warranty for this free software. For both users' and
46 | authors' sake, the GPL requires that modified versions be marked as
47 | changed, so that their problems will not be attributed erroneously to
48 | authors of previous versions.
49 |
50 | Some devices are designed to deny users access to install or run
51 | modified versions of the software inside them, although the manufacturer
52 | can do so. This is fundamentally incompatible with the aim of
53 | protecting users' freedom to change the software. The systematic
54 | pattern of such abuse occurs in the area of products for individuals to
55 | use, which is precisely where it is most unacceptable. Therefore, we
56 | have designed this version of the GPL to prohibit the practice for those
57 | products. If such problems arise substantially in other domains, we
58 | stand ready to extend this provision to those domains in future versions
59 | of the GPL, as needed to protect the freedom of users.
60 |
61 | Finally, every program is threatened constantly by software patents.
62 | States should not allow patents to restrict development and use of
63 | software on general-purpose computers, but in those that do, we wish to
64 | avoid the special danger that patents applied to a free program could
65 | make it effectively proprietary. To prevent this, the GPL assures that
66 | patents cannot be used to render the program non-free.
67 |
68 | The precise terms and conditions for copying, distribution and
69 | modification follow.
70 |
71 | TERMS AND CONDITIONS
72 |
73 | 0. Definitions.
74 |
75 | "This License" refers to version 3 of the GNU General Public License.
76 |
77 | "Copyright" also means copyright-like laws that apply to other kinds of
78 | works, such as semiconductor masks.
79 |
80 | "The Program" refers to any copyrightable work licensed under this
81 | License. Each licensee is addressed as "you". "Licensees" and
82 | "recipients" may be individuals or organizations.
83 |
84 | To "modify" a work means to copy from or adapt all or part of the work
85 | in a fashion requiring copyright permission, other than the making of an
86 | exact copy. The resulting work is called a "modified version" of the
87 | earlier work or a work "based on" the earlier work.
88 |
89 | A "covered work" means either the unmodified Program or a work based
90 | on the Program.
91 |
92 | To "propagate" a work means to do anything with it that, without
93 | permission, would make you directly or secondarily liable for
94 | infringement under applicable copyright law, except executing it on a
95 | computer or modifying a private copy. Propagation includes copying,
96 | distribution (with or without modification), making available to the
97 | public, and in some countries other activities as well.
98 |
99 | To "convey" a work means any kind of propagation that enables other
100 | parties to make or receive copies. Mere interaction with a user through
101 | a computer network, with no transfer of a copy, is not conveying.
102 |
103 | An interactive user interface displays "Appropriate Legal Notices"
104 | to the extent that it includes a convenient and prominently visible
105 | feature that (1) displays an appropriate copyright notice, and (2)
106 | tells the user that there is no warranty for the work (except to the
107 | extent that warranties are provided), that licensees may convey the
108 | work under this License, and how to view a copy of this License. If
109 | the interface presents a list of user commands or options, such as a
110 | menu, a prominent item in the list meets this criterion.
111 |
112 | 1. Source Code.
113 |
114 | The "source code" for a work means the preferred form of the work
115 | for making modifications to it. "Object code" means any non-source
116 | form of a work.
117 |
118 | A "Standard Interface" means an interface that either is an official
119 | standard defined by a recognized standards body, or, in the case of
120 | interfaces specified for a particular programming language, one that
121 | is widely used among developers working in that language.
122 |
123 | The "System Libraries" of an executable work include anything, other
124 | than the work as a whole, that (a) is included in the normal form of
125 | packaging a Major Component, but which is not part of that Major
126 | Component, and (b) serves only to enable use of the work with that
127 | Major Component, or to implement a Standard Interface for which an
128 | implementation is available to the public in source code form. A
129 | "Major Component", in this context, means a major essential component
130 | (kernel, window system, and so on) of the specific operating system
131 | (if any) on which the executable work runs, or a compiler used to
132 | produce the work, or an object code interpreter used to run it.
133 |
134 | The "Corresponding Source" for a work in object code form means all
135 | the source code needed to generate, install, and (for an executable
136 | work) run the object code and to modify the work, including scripts to
137 | control those activities. However, it does not include the work's
138 | System Libraries, or general-purpose tools or generally available free
139 | programs which are used unmodified in performing those activities but
140 | which are not part of the work. For example, Corresponding Source
141 | includes interface definition files associated with source files for
142 | the work, and the source code for shared libraries and dynamically
143 | linked subprograms that the work is specifically designed to require,
144 | such as by intimate data communication or control flow between those
145 | subprograms and other parts of the work.
146 |
147 | The Corresponding Source need not include anything that users
148 | can regenerate automatically from other parts of the Corresponding
149 | Source.
150 |
151 | The Corresponding Source for a work in source code form is that
152 | same work.
153 |
154 | 2. Basic Permissions.
155 |
156 | All rights granted under this License are granted for the term of
157 | copyright on the Program, and are irrevocable provided the stated
158 | conditions are met. This License explicitly affirms your unlimited
159 | permission to run the unmodified Program. The output from running a
160 | covered work is covered by this License only if the output, given its
161 | content, constitutes a covered work. This License acknowledges your
162 | rights of fair use or other equivalent, as provided by copyright law.
163 |
164 | You may make, run and propagate covered works that you do not
165 | convey, without conditions so long as your license otherwise remains
166 | in force. You may convey covered works to others for the sole purpose
167 | of having them make modifications exclusively for you, or provide you
168 | with facilities for running those works, provided that you comply with
169 | the terms of this License in conveying all material for which you do
170 | not control copyright. Those thus making or running the covered works
171 | for you must do so exclusively on your behalf, under your direction
172 | and control, on terms that prohibit them from making any copies of
173 | your copyrighted material outside their relationship with you.
174 |
175 | Conveying under any other circumstances is permitted solely under
176 | the conditions stated below. Sublicensing is not allowed; section 10
177 | makes it unnecessary.
178 |
179 | 3. Protecting Users' Legal Rights From Anti-Circumvention Law.
180 |
181 | No covered work shall be deemed part of an effective technological
182 | measure under any applicable law fulfilling obligations under article
183 | 11 of the WIPO copyright treaty adopted on 20 December 1996, or
184 | similar laws prohibiting or restricting circumvention of such
185 | measures.
186 |
187 | When you convey a covered work, you waive any legal power to forbid
188 | circumvention of technological measures to the extent such circumvention
189 | is effected by exercising rights under this License with respect to
190 | the covered work, and you disclaim any intention to limit operation or
191 | modification of the work as a means of enforcing, against the work's
192 | users, your or third parties' legal rights to forbid circumvention of
193 | technological measures.
194 |
195 | 4. Conveying Verbatim Copies.
196 |
197 | You may convey verbatim copies of the Program's source code as you
198 | receive it, in any medium, provided that you conspicuously and
199 | appropriately publish on each copy an appropriate copyright notice;
200 | keep intact all notices stating that this License and any
201 | non-permissive terms added in accord with section 7 apply to the code;
202 | keep intact all notices of the absence of any warranty; and give all
203 | recipients a copy of this License along with the Program.
204 |
205 | You may charge any price or no price for each copy that you convey,
206 | and you may offer support or warranty protection for a fee.
207 |
208 | 5. Conveying Modified Source Versions.
209 |
210 | You may convey a work based on the Program, or the modifications to
211 | produce it from the Program, in the form of source code under the
212 | terms of section 4, provided that you also meet all of these conditions:
213 |
214 | a) The work must carry prominent notices stating that you modified
215 | it, and giving a relevant date.
216 |
217 | b) The work must carry prominent notices stating that it is
218 | released under this License and any conditions added under section
219 | 7. This requirement modifies the requirement in section 4 to
220 | "keep intact all notices".
221 |
222 | c) You must license the entire work, as a whole, under this
223 | License to anyone who comes into possession of a copy. This
224 | License will therefore apply, along with any applicable section 7
225 | additional terms, to the whole of the work, and all its parts,
226 | regardless of how they are packaged. This License gives no
227 | permission to license the work in any other way, but it does not
228 | invalidate such permission if you have separately received it.
229 |
230 | d) If the work has interactive user interfaces, each must display
231 | Appropriate Legal Notices; however, if the Program has interactive
232 | interfaces that do not display Appropriate Legal Notices, your
233 | work need not make them do so.
234 |
235 | A compilation of a covered work with other separate and independent
236 | works, which are not by their nature extensions of the covered work,
237 | and which are not combined with it such as to form a larger program,
238 | in or on a volume of a storage or distribution medium, is called an
239 | "aggregate" if the compilation and its resulting copyright are not
240 | used to limit the access or legal rights of the compilation's users
241 | beyond what the individual works permit. Inclusion of a covered work
242 | in an aggregate does not cause this License to apply to the other
243 | parts of the aggregate.
244 |
245 | 6. Conveying Non-Source Forms.
246 |
247 | You may convey a covered work in object code form under the terms
248 | of sections 4 and 5, provided that you also convey the
249 | machine-readable Corresponding Source under the terms of this License,
250 | in one of these ways:
251 |
252 | a) Convey the object code in, or embodied in, a physical product
253 | (including a physical distribution medium), accompanied by the
254 | Corresponding Source fixed on a durable physical medium
255 | customarily used for software interchange.
256 |
257 | b) Convey the object code in, or embodied in, a physical product
258 | (including a physical distribution medium), accompanied by a
259 | written offer, valid for at least three years and valid for as
260 | long as you offer spare parts or customer support for that product
261 | model, to give anyone who possesses the object code either (1) a
262 | copy of the Corresponding Source for all the software in the
263 | product that is covered by this License, on a durable physical
264 | medium customarily used for software interchange, for a price no
265 | more than your reasonable cost of physically performing this
266 | conveying of source, or (2) access to copy the
267 | Corresponding Source from a network server at no charge.
268 |
269 | c) Convey individual copies of the object code with a copy of the
270 | written offer to provide the Corresponding Source. This
271 | alternative is allowed only occasionally and noncommercially, and
272 | only if you received the object code with such an offer, in accord
273 | with subsection 6b.
274 |
275 | d) Convey the object code by offering access from a designated
276 | place (gratis or for a charge), and offer equivalent access to the
277 | Corresponding Source in the same way through the same place at no
278 | further charge. You need not require recipients to copy the
279 | Corresponding Source along with the object code. If the place to
280 | copy the object code is a network server, the Corresponding Source
281 | may be on a different server (operated by you or a third party)
282 | that supports equivalent copying facilities, provided you maintain
283 | clear directions next to the object code saying where to find the
284 | Corresponding Source. Regardless of what server hosts the
285 | Corresponding Source, you remain obligated to ensure that it is
286 | available for as long as needed to satisfy these requirements.
287 |
288 | e) Convey the object code using peer-to-peer transmission, provided
289 | you inform other peers where the object code and Corresponding
290 | Source of the work are being offered to the general public at no
291 | charge under subsection 6d.
292 |
293 | A separable portion of the object code, whose source code is excluded
294 | from the Corresponding Source as a System Library, need not be
295 | included in conveying the object code work.
296 |
297 | A "User Product" is either (1) a "consumer product", which means any
298 | tangible personal property which is normally used for personal, family,
299 | or household purposes, or (2) anything designed or sold for incorporation
300 | into a dwelling. In determining whether a product is a consumer product,
301 | doubtful cases shall be resolved in favor of coverage. For a particular
302 | product received by a particular user, "normally used" refers to a
303 | typical or common use of that class of product, regardless of the status
304 | of the particular user or of the way in which the particular user
305 | actually uses, or expects or is expected to use, the product. A product
306 | is a consumer product regardless of whether the product has substantial
307 | commercial, industrial or non-consumer uses, unless such uses represent
308 | the only significant mode of use of the product.
309 |
310 | "Installation Information" for a User Product means any methods,
311 | procedures, authorization keys, or other information required to install
312 | and execute modified versions of a covered work in that User Product from
313 | a modified version of its Corresponding Source. The information must
314 | suffice to ensure that the continued functioning of the modified object
315 | code is in no case prevented or interfered with solely because
316 | modification has been made.
317 |
318 | If you convey an object code work under this section in, or with, or
319 | specifically for use in, a User Product, and the conveying occurs as
320 | part of a transaction in which the right of possession and use of the
321 | User Product is transferred to the recipient in perpetuity or for a
322 | fixed term (regardless of how the transaction is characterized), the
323 | Corresponding Source conveyed under this section must be accompanied
324 | by the Installation Information. But this requirement does not apply
325 | if neither you nor any third party retains the ability to install
326 | modified object code on the User Product (for example, the work has
327 | been installed in ROM).
328 |
329 | The requirement to provide Installation Information does not include a
330 | requirement to continue to provide support service, warranty, or updates
331 | for a work that has been modified or installed by the recipient, or for
332 | the User Product in which it has been modified or installed. Access to a
333 | network may be denied when the modification itself materially and
334 | adversely affects the operation of the network or violates the rules and
335 | protocols for communication across the network.
336 |
337 | Corresponding Source conveyed, and Installation Information provided,
338 | in accord with this section must be in a format that is publicly
339 | documented (and with an implementation available to the public in
340 | source code form), and must require no special password or key for
341 | unpacking, reading or copying.
342 |
343 | 7. Additional Terms.
344 |
345 | "Additional permissions" are terms that supplement the terms of this
346 | License by making exceptions from one or more of its conditions.
347 | Additional permissions that are applicable to the entire Program shall
348 | be treated as though they were included in this License, to the extent
349 | that they are valid under applicable law. If additional permissions
350 | apply only to part of the Program, that part may be used separately
351 | under those permissions, but the entire Program remains governed by
352 | this License without regard to the additional permissions.
353 |
354 | When you convey a copy of a covered work, you may at your option
355 | remove any additional permissions from that copy, or from any part of
356 | it. (Additional permissions may be written to require their own
357 | removal in certain cases when you modify the work.) You may place
358 | additional permissions on material, added by you to a covered work,
359 | for which you have or can give appropriate copyright permission.
360 |
361 | Notwithstanding any other provision of this License, for material you
362 | add to a covered work, you may (if authorized by the copyright holders of
363 | that material) supplement the terms of this License with terms:
364 |
365 | a) Disclaiming warranty or limiting liability differently from the
366 | terms of sections 15 and 16 of this License; or
367 |
368 | b) Requiring preservation of specified reasonable legal notices or
369 | author attributions in that material or in the Appropriate Legal
370 | Notices displayed by works containing it; or
371 |
372 | c) Prohibiting misrepresentation of the origin of that material, or
373 | requiring that modified versions of such material be marked in
374 | reasonable ways as different from the original version; or
375 |
376 | d) Limiting the use for publicity purposes of names of licensors or
377 | authors of the material; or
378 |
379 | e) Declining to grant rights under trademark law for use of some
380 | trade names, trademarks, or service marks; or
381 |
382 | f) Requiring indemnification of licensors and authors of that
383 | material by anyone who conveys the material (or modified versions of
384 | it) with contractual assumptions of liability to the recipient, for
385 | any liability that these contractual assumptions directly impose on
386 | those licensors and authors.
387 |
388 | All other non-permissive additional terms are considered "further
389 | restrictions" within the meaning of section 10. If the Program as you
390 | received it, or any part of it, contains a notice stating that it is
391 | governed by this License along with a term that is a further
392 | restriction, you may remove that term. If a license document contains
393 | a further restriction but permits relicensing or conveying under this
394 | License, you may add to a covered work material governed by the terms
395 | of that license document, provided that the further restriction does
396 | not survive such relicensing or conveying.
397 |
398 | If you add terms to a covered work in accord with this section, you
399 | must place, in the relevant source files, a statement of the
400 | additional terms that apply to those files, or a notice indicating
401 | where to find the applicable terms.
402 |
403 | Additional terms, permissive or non-permissive, may be stated in the
404 | form of a separately written license, or stated as exceptions;
405 | the above requirements apply either way.
406 |
407 | 8. Termination.
408 |
409 | You may not propagate or modify a covered work except as expressly
410 | provided under this License. Any attempt otherwise to propagate or
411 | modify it is void, and will automatically terminate your rights under
412 | this License (including any patent licenses granted under the third
413 | paragraph of section 11).
414 |
415 | However, if you cease all violation of this License, then your
416 | license from a particular copyright holder is reinstated (a)
417 | provisionally, unless and until the copyright holder explicitly and
418 | finally terminates your license, and (b) permanently, if the copyright
419 | holder fails to notify you of the violation by some reasonable means
420 | prior to 60 days after the cessation.
421 |
422 | Moreover, your license from a particular copyright holder is
423 | reinstated permanently if the copyright holder notifies you of the
424 | violation by some reasonable means, this is the first time you have
425 | received notice of violation of this License (for any work) from that
426 | copyright holder, and you cure the violation prior to 30 days after
427 | your receipt of the notice.
428 |
429 | Termination of your rights under this section does not terminate the
430 | licenses of parties who have received copies or rights from you under
431 | this License. If your rights have been terminated and not permanently
432 | reinstated, you do not qualify to receive new licenses for the same
433 | material under section 10.
434 |
435 | 9. Acceptance Not Required for Having Copies.
436 |
437 | You are not required to accept this License in order to receive or
438 | run a copy of the Program. Ancillary propagation of a covered work
439 | occurring solely as a consequence of using peer-to-peer transmission
440 | to receive a copy likewise does not require acceptance. However,
441 | nothing other than this License grants you permission to propagate or
442 | modify any covered work. These actions infringe copyright if you do
443 | not accept this License. Therefore, by modifying or propagating a
444 | covered work, you indicate your acceptance of this License to do so.
445 |
446 | 10. Automatic Licensing of Downstream Recipients.
447 |
448 | Each time you convey a covered work, the recipient automatically
449 | receives a license from the original licensors, to run, modify and
450 | propagate that work, subject to this License. You are not responsible
451 | for enforcing compliance by third parties with this License.
452 |
453 | An "entity transaction" is a transaction transferring control of an
454 | organization, or substantially all assets of one, or subdividing an
455 | organization, or merging organizations. If propagation of a covered
456 | work results from an entity transaction, each party to that
457 | transaction who receives a copy of the work also receives whatever
458 | licenses to the work the party's predecessor in interest had or could
459 | give under the previous paragraph, plus a right to possession of the
460 | Corresponding Source of the work from the predecessor in interest, if
461 | the predecessor has it or can get it with reasonable efforts.
462 |
463 | You may not impose any further restrictions on the exercise of the
464 | rights granted or affirmed under this License. For example, you may
465 | not impose a license fee, royalty, or other charge for exercise of
466 | rights granted under this License, and you may not initiate litigation
467 | (including a cross-claim or counterclaim in a lawsuit) alleging that
468 | any patent claim is infringed by making, using, selling, offering for
469 | sale, or importing the Program or any portion of it.
470 |
471 | 11. Patents.
472 |
473 | A "contributor" is a copyright holder who authorizes use under this
474 | License of the Program or a work on which the Program is based. The
475 | work thus licensed is called the contributor's "contributor version".
476 |
477 | A contributor's "essential patent claims" are all patent claims
478 | owned or controlled by the contributor, whether already acquired or
479 | hereafter acquired, that would be infringed by some manner, permitted
480 | by this License, of making, using, or selling its contributor version,
481 | but do not include claims that would be infringed only as a
482 | consequence of further modification of the contributor version. For
483 | purposes of this definition, "control" includes the right to grant
484 | patent sublicenses in a manner consistent with the requirements of
485 | this License.
486 |
487 | Each contributor grants you a non-exclusive, worldwide, royalty-free
488 | patent license under the contributor's essential patent claims, to
489 | make, use, sell, offer for sale, import and otherwise run, modify and
490 | propagate the contents of its contributor version.
491 |
492 | In the following three paragraphs, a "patent license" is any express
493 | agreement or commitment, however denominated, not to enforce a patent
494 | (such as an express permission to practice a patent or covenant not to
495 | sue for patent infringement). To "grant" such a patent license to a
496 | party means to make such an agreement or commitment not to enforce a
497 | patent against the party.
498 |
499 | If you convey a covered work, knowingly relying on a patent license,
500 | and the Corresponding Source of the work is not available for anyone
501 | to copy, free of charge and under the terms of this License, through a
502 | publicly available network server or other readily accessible means,
503 | then you must either (1) cause the Corresponding Source to be so
504 | available, or (2) arrange to deprive yourself of the benefit of the
505 | patent license for this particular work, or (3) arrange, in a manner
506 | consistent with the requirements of this License, to extend the patent
507 | license to downstream recipients. "Knowingly relying" means you have
508 | actual knowledge that, but for the patent license, your conveying the
509 | covered work in a country, or your recipient's use of the covered work
510 | in a country, would infringe one or more identifiable patents in that
511 | country that you have reason to believe are valid.
512 |
513 | If, pursuant to or in connection with a single transaction or
514 | arrangement, you convey, or propagate by procuring conveyance of, a
515 | covered work, and grant a patent license to some of the parties
516 | receiving the covered work authorizing them to use, propagate, modify
517 | or convey a specific copy of the covered work, then the patent license
518 | you grant is automatically extended to all recipients of the covered
519 | work and works based on it.
520 |
521 | A patent license is "discriminatory" if it does not include within
522 | the scope of its coverage, prohibits the exercise of, or is
523 | conditioned on the non-exercise of one or more of the rights that are
524 | specifically granted under this License. You may not convey a covered
525 | work if you are a party to an arrangement with a third party that is
526 | in the business of distributing software, under which you make payment
527 | to the third party based on the extent of your activity of conveying
528 | the work, and under which the third party grants, to any of the
529 | parties who would receive the covered work from you, a discriminatory
530 | patent license (a) in connection with copies of the covered work
531 | conveyed by you (or copies made from those copies), or (b) primarily
532 | for and in connection with specific products or compilations that
533 | contain the covered work, unless you entered into that arrangement,
534 | or that patent license was granted, prior to 28 March 2007.
535 |
536 | Nothing in this License shall be construed as excluding or limiting
537 | any implied license or other defenses to infringement that may
538 | otherwise be available to you under applicable patent law.
539 |
540 | 12. No Surrender of Others' Freedom.
541 |
542 | If conditions are imposed on you (whether by court order, agreement or
543 | otherwise) that contradict the conditions of this License, they do not
544 | excuse you from the conditions of this License. If you cannot convey a
545 | covered work so as to satisfy simultaneously your obligations under this
546 | License and any other pertinent obligations, then as a consequence you may
547 | not convey it at all. For example, if you agree to terms that obligate you
548 | to collect a royalty for further conveying from those to whom you convey
549 | the Program, the only way you could satisfy both those terms and this
550 | License would be to refrain entirely from conveying the Program.
551 |
552 | 13. Use with the GNU Affero General Public License.
553 |
554 | Notwithstanding any other provision of this License, you have
555 | permission to link or combine any covered work with a work licensed
556 | under version 3 of the GNU Affero General Public License into a single
557 | combined work, and to convey the resulting work. The terms of this
558 | License will continue to apply to the part which is the covered work,
559 | but the special requirements of the GNU Affero General Public License,
560 | section 13, concerning interaction through a network will apply to the
561 | combination as such.
562 |
563 | 14. Revised Versions of this License.
564 |
565 | The Free Software Foundation may publish revised and/or new versions of
566 | the GNU General Public License from time to time. Such new versions will
567 | be similar in spirit to the present version, but may differ in detail to
568 | address new problems or concerns.
569 |
570 | Each version is given a distinguishing version number. If the
571 | Program specifies that a certain numbered version of the GNU General
572 | Public License "or any later version" applies to it, you have the
573 | option of following the terms and conditions either of that numbered
574 | version or of any later version published by the Free Software
575 | Foundation. If the Program does not specify a version number of the
576 | GNU General Public License, you may choose any version ever published
577 | by the Free Software Foundation.
578 |
579 | If the Program specifies that a proxy can decide which future
580 | versions of the GNU General Public License can be used, that proxy's
581 | public statement of acceptance of a version permanently authorizes you
582 | to choose that version for the Program.
583 |
584 | Later license versions may give you additional or different
585 | permissions. However, no additional obligations are imposed on any
586 | author or copyright holder as a result of your choosing to follow a
587 | later version.
588 |
589 | 15. Disclaimer of Warranty.
590 |
591 | THERE IS NO WARRANTY FOR THE PROGRAM, TO THE EXTENT PERMITTED BY
592 | APPLICABLE LAW. EXCEPT WHEN OTHERWISE STATED IN WRITING THE COPYRIGHT
593 | HOLDERS AND/OR OTHER PARTIES PROVIDE THE PROGRAM "AS IS" WITHOUT WARRANTY
594 | OF ANY KIND, EITHER EXPRESSED OR IMPLIED, INCLUDING, BUT NOT LIMITED TO,
595 | THE IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR
596 | PURPOSE. THE ENTIRE RISK AS TO THE QUALITY AND PERFORMANCE OF THE PROGRAM
597 | IS WITH YOU. SHOULD THE PROGRAM PROVE DEFECTIVE, YOU ASSUME THE COST OF
598 | ALL NECESSARY SERVICING, REPAIR OR CORRECTION.
599 |
600 | 16. Limitation of Liability.
601 |
602 | IN NO EVENT UNLESS REQUIRED BY APPLICABLE LAW OR AGREED TO IN WRITING
603 | WILL ANY COPYRIGHT HOLDER, OR ANY OTHER PARTY WHO MODIFIES AND/OR CONVEYS
604 | THE PROGRAM AS PERMITTED ABOVE, BE LIABLE TO YOU FOR DAMAGES, INCLUDING ANY
605 | GENERAL, SPECIAL, INCIDENTAL OR CONSEQUENTIAL DAMAGES ARISING OUT OF THE
606 | USE OR INABILITY TO USE THE PROGRAM (INCLUDING BUT NOT LIMITED TO LOSS OF
607 | DATA OR DATA BEING RENDERED INACCURATE OR LOSSES SUSTAINED BY YOU OR THIRD
608 | PARTIES OR A FAILURE OF THE PROGRAM TO OPERATE WITH ANY OTHER PROGRAMS),
609 | EVEN IF SUCH HOLDER OR OTHER PARTY HAS BEEN ADVISED OF THE POSSIBILITY OF
610 | SUCH DAMAGES.
611 |
612 | 17. Interpretation of Sections 15 and 16.
613 |
614 | If the disclaimer of warranty and limitation of liability provided
615 | above cannot be given local legal effect according to their terms,
616 | reviewing courts shall apply local law that most closely approximates
617 | an absolute waiver of all civil liability in connection with the
618 | Program, unless a warranty or assumption of liability accompanies a
619 | copy of the Program in return for a fee.
620 |
621 | END OF TERMS AND CONDITIONS
622 |
623 | How to Apply These Terms to Your New Programs
624 |
625 | If you develop a new program, and you want it to be of the greatest
626 | possible use to the public, the best way to achieve this is to make it
627 | free software which everyone can redistribute and change under these terms.
628 |
629 | To do so, attach the following notices to the program. It is safest
630 | to attach them to the start of each source file to most effectively
631 | state the exclusion of warranty; and each file should have at least
632 | the "copyright" line and a pointer to where the full notice is found.
633 |
634 |
635 | Copyright (C)
636 |
637 | This program is free software: you can redistribute it and/or modify
638 | it under the terms of the GNU General Public License as published by
639 | the Free Software Foundation, either version 3 of the License, or
640 | (at your option) any later version.
641 |
642 | This program is distributed in the hope that it will be useful,
643 | but WITHOUT ANY WARRANTY; without even the implied warranty of
644 | MERCHANTABILITY or FITNESS FOR A PARTICULAR PURPOSE. See the
645 | GNU General Public License for more details.
646 |
647 | You should have received a copy of the GNU General Public License
648 | along with this program. If not, see .
649 |
650 | Also add information on how to contact you by electronic and paper mail.
651 |
652 | If the program does terminal interaction, make it output a short
653 | notice like this when it starts in an interactive mode:
654 |
655 | Copyright (C)
656 | This program comes with ABSOLUTELY NO WARRANTY; for details type `show w'.
657 | This is free software, and you are welcome to redistribute it
658 | under certain conditions; type `show c' for details.
659 |
660 | The hypothetical commands `show w' and `show c' should show the appropriate
661 | parts of the General Public License. Of course, your program's commands
662 | might be different; for a GUI interface, you would use an "about box".
663 |
664 | You should also get your employer (if you work as a programmer) or school,
665 | if any, to sign a "copyright disclaimer" for the program, if necessary.
666 | For more information on this, and how to apply and follow the GNU GPL, see
667 | .
668 |
669 | The GNU General Public License does not permit incorporating your program
670 | into proprietary programs. If your program is a subroutine library, you
671 | may consider it more useful to permit linking proprietary applications with
672 | the library. If this is what you want to do, use the GNU Lesser General
673 | Public License instead of this License. But first, please read
674 | .
675 |
--------------------------------------------------------------------------------
/README.md:
--------------------------------------------------------------------------------
1 | # Proxmox Toolbox
2 | ## Toolbox to setup Proxmox Virtual Environment and Backup Server
3 |
4 | 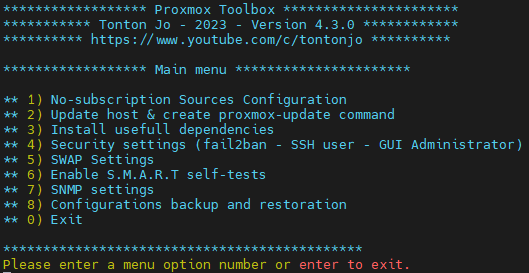
5 |
6 |
7 | ## Tonton Jo
8 | ### Rejoint la trame - Join the community & Support my work
9 | [Click Here!](https://linktr.ee/tontonjo)
10 |
11 | ## Informations:
12 |
13 | This little tool aim to get smalls one-time configurations for Proxmox Virtual environement and backup server hosts in no time.
14 | It automatically will find if the host is a pve or a pbs host and setup accordingly.
15 |
16 | ### Demonstration:
17 | You can watch a demonstration of the tool [in this playlist](https://www.youtube.com/playlist?list=PLU73OWQhDzsTpLpVNspJ14rVrXAmo2Biu)
18 |
19 | ### Prerequisits:
20 | - Up-to-date PVE 7 / 8 or PBS server
21 | - Internet connexion
22 |
23 | ## Features are:
24 | - Automatic PVE / PBS host detection
25 | - Hide enterprise repo and set no-subscription repository
26 | - - when no-enterprise source is set, disable no-subscription message
27 | - Update host and create a new command "proxmox-update"
28 | - Install usefull dependencies: ifupdown2 - git - sudo - libsasl2-modules - snmp
29 | - Security settings:
30 | - - Enable fail2ban with default configuration for sshd, Proxmox virtual environement and Proxmox backup server
31 | (credits to [inettgmbh](https://github.com/inettgmbh/fail2ban-proxmox-backup-server))
32 | - - Create another debian user with sudo rights
33 | - - Disable root ssh login
34 | - - Create another Proxmox GUI administrator (login with Proxmox VE Realm)
35 | - - Disabling root@pam user !!! root@pam is needed to update from GUI - update can still be done trough SSH if disabled !!!
36 | - SWAP value change or disable
37 | - Enable S.M.A.R.T self-tests on all supported drives
38 | - - short: every sunday@22h - Long: every 1st of month @22h
39 | - Enable SNMP V2 or v3
40 | - Backup and restore Proxmox Virtual Environment and Backup Server configurations
41 | - - Automatic remount of directories and zpools using previously existing configurations
42 | - - Please find more informations below
43 |
44 | ## Legacy hidden function:
45 | - Configure email service to send system and proxmox notifications (postfix)
46 |
47 | ## News
48 | 2023.11.24: Proxmox 8.1 - Emails Notifications - Proxmox VE now supports email configurations very well from the GUI, the toolbox wont get any update related to this function anymore.
49 |
50 | ## Usage and arguments:
51 | ### Get and execute:
52 | ```shell
53 | wget -qO proxmox_toolbox.sh https://raw.githubusercontent.com/Tontonjo/proxmox_toolbox/main/proxmox_toolbox.sh && bash proxmox_toolbox.sh
54 | ```
55 |
56 | ### Updating host & remove subscription message
57 | The script will update your host and detect if the no-enterprise source is configured, if so, remove the subscription message.
58 | - If you still encounter it after, clear your broswer cache.
59 | - If you update your host directly within the system, the no subscribtion message may reappear when the file gets updated.
60 | - In order to nerver see this again, you have to update Proxmox with one of the following options:
61 |
62 | To start an update only, without menu or prompt:
63 | ```shell
64 | bash proxmox_toolbox.sh -u
65 | ```
66 | Once the tool has been used to update host, you can execute this command to fully update your host - kind of an alias of bash proxmox_toolbox.sh -u
67 | ```shell
68 | proxmox-update
69 | ```
70 |
71 | ### Backup configuration
72 | To start a configuration backup only:
73 | ```shell
74 | bash proxmox_toolbox.sh -b
75 | ```
76 | ## Fail2ban:
77 | If you enable fail2ban, i guess you know what you're doing, if you dont: here's some usefull informations and commands:
78 | - ban are for 1 hour
79 | - ssh and web interface logins are monitored
80 | #### List of $jailname:
81 | ```ssh
82 | fail2ban-client status
83 | ```
84 | #### get status of a jails - display banned IP's
85 | ```ssh
86 | fail2ban-client status $jailname
87 | ```
88 | #### Unband an IP:
89 | ```ssh
90 | fail2ban-client set $jailname unbanip $ipaddress
91 | ```
92 |
93 |
94 | ## Backup and Restoration:
95 | - Be carefull as this was not extensively tested - especially not with cluster configurations
96 | - The following folders and configurations are backuped by default:
97 | ```/etc/ssh/sshd_config /root/.ssh/ /etc/fail2ban/ /etc/systemd/system/*.mount /etc/network/interfaces /etc/sysctl.conf /etc/resolv.conf /etc/hosts /etc/hostname /etc/cron* /etc/aliases /etc/snmp/ /etc/smartd.conf /usr/share/snmp/snmpd.conf /etc/postfix/ /etc/pve/ /etc/lvm/ /etc/modprobe.d/ /var/lib/pve-firewall/ /var/lib/pve-cluster/ /etc/vzdump.conf /etc/ksmtuned.conf /etc/proxmox-backup/```
98 |
99 | ### Backup
100 | The script will put every folder listed in backup_content in a tar.gz archive.
101 | - You cand add /remove folder trough the edit of backup_content= line in the script
102 | - You can change the target folder to use for backup and restoration in the script env. variables at: backupdir="/root/"
103 |
104 | Once the backup is done, a tar.gz archive is located at backupdir="/root/".
105 |
106 | ### Restauration:
107 | The script looks for tar.gz files located in backupdir="/root/" and will list all the available archives for you to choose one.
108 | Warning: The restauration will overwrite any existing file with the one in archive
109 |
110 | The restauration process will:
111 | - Reinstall missing dependencies for snmp and fail2ban if config were existing
112 | - Restore Proxmox configurations (proxmox configs, certificates, vm configs, storages configs, proxmox users)
113 | - Automatically remount the following storages: dir and zpools
114 |
115 | ## Directory mountpoint and zpool
116 |
117 | In case of need, here's how you can manually mount storages:
118 |
119 | #### Directory:
120 | Mount configurations are located in /etc/systemd/system/mnt-datastore-$datastorename.mount
121 | - run the following commands:
122 | ```shell
123 | source /etc/systemd/system/mnt-datastore-$datastorename.mount
124 | mkdir -p "$Where"
125 | echo "$What $Where $Type $Options 0 2" >> /etc/fstab
126 | mount -a
127 | ```
128 | - Control if the drives are now correctly mounted
129 | - Add a new Directory storage in pve/pbs using "where" as directory path
130 | #### Zpool:
131 | - run
132 | ```shell
133 | zpool import
134 | ```
135 | - Take note of the "pool" name and run
136 | ```shell
137 | zpool import -f $poolname
138 | ```
139 | - Add a new ZFS storage in pve/pbs
140 | ## SOURCES:
141 | https://pve.proxmox.com/wiki/Fail2ban
142 | https://github.com/inettgmbh/fail2ban-proxmox-backup-server
143 | https://forum.proxmox.com/threads/how-do-i-set-the-mail-server-to-be-used-in-proxmox.23669/
144 | https://linuxscriptshub.com/configure-smtp-with-gmail-using-postfix/
145 | https://suoption_pickedpport.google.com/accounts/answer/6010255
146 | https://www.howtoforge.com/community/threads/solved-problem-with-outgoing-mail-from-server.53920/
147 | http://mhawthorne.net/posts/2011-postfix-configuring-gmail-as-relay/
148 | https://docs.oracle.com/en/cloud/cloud-at-customer/occ-get-started/add-ssh-enabled-user.html
149 | https://www.noobunbox.net/serveur/monitoring/configurer-snmp-v3-sous-debian
150 | https://github.com/DeadlockState/Proxmox-prepare
151 | https://blog.lbdg.me/proxmox-best-performance-disable-swappiness/
152 | https://gist.github.com/mrpeardotnet/6bdc4b504f43ce57fa7eaee96d376edf
153 | https://github.com/DerDanilo/proxmox-stuff/blob/master/prox_config_backup.sh
154 | https://pve.proxmox.com/wiki/Upgrade_from_6.x_to_7.0
155 | https://wiki.debian.org/SSDOptimization
156 | https://www.linuxtricks.fr/wiki/proxmox-quelques-infos
157 | https://bobcares.com/blog/fail2ban-unban-ip/
158 |
159 | ## TODO:
160 | settings for zram -> https://pve.proxmox.com/wiki/Zram
161 | PBS: add support for user creation and backup / restoration
162 | user creation fro PBS when available
163 | make things stupid-proof (deny characters when numbers expected and so on)
164 |
--------------------------------------------------------------------------------
/bin/proxmox-update:
--------------------------------------------------------------------------------
1 | #!/bin/bash
2 |
3 | # Tonton Jo - 2022
4 | # Join me on Youtube: https://www.youtube.com/c/tontonjo
5 |
6 | # Version:
7 | # 1.0: Initial file version
8 | # 1.1: add echo to inform in case execution get stuck
9 | # 1.2: force to read whole script in case it get overwritten by an update
10 |
11 | # file is intended to be in /usr/bin/proxmox-update
12 | # This command retreive the latest version of proxmox-toolbox and execute it with update argument
13 |
14 | proxmox-update() {
15 | echo "- Retreiving ressources"
16 | wget -qO - https://raw.githubusercontent.com/Tontonjo/proxmox_toolbox/main/proxmox_toolbox.sh | bash /dev/stdin -u
17 | }
18 | proxmox-update "$@"; exit
19 |
--------------------------------------------------------------------------------
/pbs/LICENSE:
--------------------------------------------------------------------------------
1 | GNU AFFERO GENERAL PUBLIC LICENSE
2 | Version 3, 19 November 2007
3 |
4 | Copyright (C) 2007 Free Software Foundation, Inc.
5 | Everyone is permitted to copy and distribute verbatim copies
6 | of this license document, but changing it is not allowed.
7 |
8 | Preamble
9 |
10 | The GNU Affero General Public License is a free, copyleft license for
11 | software and other kinds of works, specifically designed to ensure
12 | cooperation with the community in the case of network server software.
13 |
14 | The licenses for most software and other practical works are designed
15 | to take away your freedom to share and change the works. By contrast,
16 | our General Public Licenses are intended to guarantee your freedom to
17 | share and change all versions of a program--to make sure it remains free
18 | software for all its users.
19 |
20 | When we speak of free software, we are referring to freedom, not
21 | price. Our General Public Licenses are designed to make sure that you
22 | have the freedom to distribute copies of free software (and charge for
23 | them if you wish), that you receive source code or can get it if you
24 | want it, that you can change the software or use pieces of it in new
25 | free programs, and that you know you can do these things.
26 |
27 | Developers that use our General Public Licenses protect your rights
28 | with two steps: (1) assert copyright on the software, and (2) offer
29 | you this License which gives you legal permission to copy, distribute
30 | and/or modify the software.
31 |
32 | A secondary benefit of defending all users' freedom is that
33 | improvements made in alternate versions of the program, if they
34 | receive widespread use, become available for other developers to
35 | incorporate. Many developers of free software are heartened and
36 | encouraged by the resulting cooperation. However, in the case of
37 | software used on network servers, this result may fail to come about.
38 | The GNU General Public License permits making a modified version and
39 | letting the public access it on a server without ever releasing its
40 | source code to the public.
41 |
42 | The GNU Affero General Public License is designed specifically to
43 | ensure that, in such cases, the modified source code becomes available
44 | to the community. It requires the operator of a network server to
45 | provide the source code of the modified version running there to the
46 | users of that server. Therefore, public use of a modified version, on
47 | a publicly accessible server, gives the public access to the source
48 | code of the modified version.
49 |
50 | An older license, called the Affero General Public License and
51 | published by Affero, was designed to accomplish similar goals. This is
52 | a different license, not a version of the Affero GPL, but Affero has
53 | released a new version of the Affero GPL which permits relicensing under
54 | this license.
55 |
56 | The precise terms and conditions for copying, distribution and
57 | modification follow.
58 |
59 | TERMS AND CONDITIONS
60 |
61 | 0. Definitions.
62 |
63 | "This License" refers to version 3 of the GNU Affero General Public License.
64 |
65 | "Copyright" also means copyright-like laws that apply to other kinds of
66 | works, such as semiconductor masks.
67 |
68 | "The Program" refers to any copyrightable work licensed under this
69 | License. Each licensee is addressed as "you". "Licensees" and
70 | "recipients" may be individuals or organizations.
71 |
72 | To "modify" a work means to copy from or adapt all or part of the work
73 | in a fashion requiring copyright permission, other than the making of an
74 | exact copy. The resulting work is called a "modified version" of the
75 | earlier work or a work "based on" the earlier work.
76 |
77 | A "covered work" means either the unmodified Program or a work based
78 | on the Program.
79 |
80 | To "propagate" a work means to do anything with it that, without
81 | permission, would make you directly or secondarily liable for
82 | infringement under applicable copyright law, except executing it on a
83 | computer or modifying a private copy. Propagation includes copying,
84 | distribution (with or without modification), making available to the
85 | public, and in some countries other activities as well.
86 |
87 | To "convey" a work means any kind of propagation that enables other
88 | parties to make or receive copies. Mere interaction with a user through
89 | a computer network, with no transfer of a copy, is not conveying.
90 |
91 | An interactive user interface displays "Appropriate Legal Notices"
92 | to the extent that it includes a convenient and prominently visible
93 | feature that (1) displays an appropriate copyright notice, and (2)
94 | tells the user that there is no warranty for the work (except to the
95 | extent that warranties are provided), that licensees may convey the
96 | work under this License, and how to view a copy of this License. If
97 | the interface presents a list of user commands or options, such as a
98 | menu, a prominent item in the list meets this criterion.
99 |
100 | 1. Source Code.
101 |
102 | The "source code" for a work means the preferred form of the work
103 | for making modifications to it. "Object code" means any non-source
104 | form of a work.
105 |
106 | A "Standard Interface" means an interface that either is an official
107 | standard defined by a recognized standards body, or, in the case of
108 | interfaces specified for a particular programming language, one that
109 | is widely used among developers working in that language.
110 |
111 | The "System Libraries" of an executable work include anything, other
112 | than the work as a whole, that (a) is included in the normal form of
113 | packaging a Major Component, but which is not part of that Major
114 | Component, and (b) serves only to enable use of the work with that
115 | Major Component, or to implement a Standard Interface for which an
116 | implementation is available to the public in source code form. A
117 | "Major Component", in this context, means a major essential component
118 | (kernel, window system, and so on) of the specific operating system
119 | (if any) on which the executable work runs, or a compiler used to
120 | produce the work, or an object code interpreter used to run it.
121 |
122 | The "Corresponding Source" for a work in object code form means all
123 | the source code needed to generate, install, and (for an executable
124 | work) run the object code and to modify the work, including scripts to
125 | control those activities. However, it does not include the work's
126 | System Libraries, or general-purpose tools or generally available free
127 | programs which are used unmodified in performing those activities but
128 | which are not part of the work. For example, Corresponding Source
129 | includes interface definition files associated with source files for
130 | the work, and the source code for shared libraries and dynamically
131 | linked subprograms that the work is specifically designed to require,
132 | such as by intimate data communication or control flow between those
133 | subprograms and other parts of the work.
134 |
135 | The Corresponding Source need not include anything that users
136 | can regenerate automatically from other parts of the Corresponding
137 | Source.
138 |
139 | The Corresponding Source for a work in source code form is that
140 | same work.
141 |
142 | 2. Basic Permissions.
143 |
144 | All rights granted under this License are granted for the term of
145 | copyright on the Program, and are irrevocable provided the stated
146 | conditions are met. This License explicitly affirms your unlimited
147 | permission to run the unmodified Program. The output from running a
148 | covered work is covered by this License only if the output, given its
149 | content, constitutes a covered work. This License acknowledges your
150 | rights of fair use or other equivalent, as provided by copyright law.
151 |
152 | You may make, run and propagate covered works that you do not
153 | convey, without conditions so long as your license otherwise remains
154 | in force. You may convey covered works to others for the sole purpose
155 | of having them make modifications exclusively for you, or provide you
156 | with facilities for running those works, provided that you comply with
157 | the terms of this License in conveying all material for which you do
158 | not control copyright. Those thus making or running the covered works
159 | for you must do so exclusively on your behalf, under your direction
160 | and control, on terms that prohibit them from making any copies of
161 | your copyrighted material outside their relationship with you.
162 |
163 | Conveying under any other circumstances is permitted solely under
164 | the conditions stated below. Sublicensing is not allowed; section 10
165 | makes it unnecessary.
166 |
167 | 3. Protecting Users' Legal Rights From Anti-Circumvention Law.
168 |
169 | No covered work shall be deemed part of an effective technological
170 | measure under any applicable law fulfilling obligations under article
171 | 11 of the WIPO copyright treaty adopted on 20 December 1996, or
172 | similar laws prohibiting or restricting circumvention of such
173 | measures.
174 |
175 | When you convey a covered work, you waive any legal power to forbid
176 | circumvention of technological measures to the extent such circumvention
177 | is effected by exercising rights under this License with respect to
178 | the covered work, and you disclaim any intention to limit operation or
179 | modification of the work as a means of enforcing, against the work's
180 | users, your or third parties' legal rights to forbid circumvention of
181 | technological measures.
182 |
183 | 4. Conveying Verbatim Copies.
184 |
185 | You may convey verbatim copies of the Program's source code as you
186 | receive it, in any medium, provided that you conspicuously and
187 | appropriately publish on each copy an appropriate copyright notice;
188 | keep intact all notices stating that this License and any
189 | non-permissive terms added in accord with section 7 apply to the code;
190 | keep intact all notices of the absence of any warranty; and give all
191 | recipients a copy of this License along with the Program.
192 |
193 | You may charge any price or no price for each copy that you convey,
194 | and you may offer support or warranty protection for a fee.
195 |
196 | 5. Conveying Modified Source Versions.
197 |
198 | You may convey a work based on the Program, or the modifications to
199 | produce it from the Program, in the form of source code under the
200 | terms of section 4, provided that you also meet all of these conditions:
201 |
202 | a) The work must carry prominent notices stating that you modified
203 | it, and giving a relevant date.
204 |
205 | b) The work must carry prominent notices stating that it is
206 | released under this License and any conditions added under section
207 | 7. This requirement modifies the requirement in section 4 to
208 | "keep intact all notices".
209 |
210 | c) You must license the entire work, as a whole, under this
211 | License to anyone who comes into possession of a copy. This
212 | License will therefore apply, along with any applicable section 7
213 | additional terms, to the whole of the work, and all its parts,
214 | regardless of how they are packaged. This License gives no
215 | permission to license the work in any other way, but it does not
216 | invalidate such permission if you have separately received it.
217 |
218 | d) If the work has interactive user interfaces, each must display
219 | Appropriate Legal Notices; however, if the Program has interactive
220 | interfaces that do not display Appropriate Legal Notices, your
221 | work need not make them do so.
222 |
223 | A compilation of a covered work with other separate and independent
224 | works, which are not by their nature extensions of the covered work,
225 | and which are not combined with it such as to form a larger program,
226 | in or on a volume of a storage or distribution medium, is called an
227 | "aggregate" if the compilation and its resulting copyright are not
228 | used to limit the access or legal rights of the compilation's users
229 | beyond what the individual works permit. Inclusion of a covered work
230 | in an aggregate does not cause this License to apply to the other
231 | parts of the aggregate.
232 |
233 | 6. Conveying Non-Source Forms.
234 |
235 | You may convey a covered work in object code form under the terms
236 | of sections 4 and 5, provided that you also convey the
237 | machine-readable Corresponding Source under the terms of this License,
238 | in one of these ways:
239 |
240 | a) Convey the object code in, or embodied in, a physical product
241 | (including a physical distribution medium), accompanied by the
242 | Corresponding Source fixed on a durable physical medium
243 | customarily used for software interchange.
244 |
245 | b) Convey the object code in, or embodied in, a physical product
246 | (including a physical distribution medium), accompanied by a
247 | written offer, valid for at least three years and valid for as
248 | long as you offer spare parts or customer support for that product
249 | model, to give anyone who possesses the object code either (1) a
250 | copy of the Corresponding Source for all the software in the
251 | product that is covered by this License, on a durable physical
252 | medium customarily used for software interchange, for a price no
253 | more than your reasonable cost of physically performing this
254 | conveying of source, or (2) access to copy the
255 | Corresponding Source from a network server at no charge.
256 |
257 | c) Convey individual copies of the object code with a copy of the
258 | written offer to provide the Corresponding Source. This
259 | alternative is allowed only occasionally and noncommercially, and
260 | only if you received the object code with such an offer, in accord
261 | with subsection 6b.
262 |
263 | d) Convey the object code by offering access from a designated
264 | place (gratis or for a charge), and offer equivalent access to the
265 | Corresponding Source in the same way through the same place at no
266 | further charge. You need not require recipients to copy the
267 | Corresponding Source along with the object code. If the place to
268 | copy the object code is a network server, the Corresponding Source
269 | may be on a different server (operated by you or a third party)
270 | that supports equivalent copying facilities, provided you maintain
271 | clear directions next to the object code saying where to find the
272 | Corresponding Source. Regardless of what server hosts the
273 | Corresponding Source, you remain obligated to ensure that it is
274 | available for as long as needed to satisfy these requirements.
275 |
276 | e) Convey the object code using peer-to-peer transmission, provided
277 | you inform other peers where the object code and Corresponding
278 | Source of the work are being offered to the general public at no
279 | charge under subsection 6d.
280 |
281 | A separable portion of the object code, whose source code is excluded
282 | from the Corresponding Source as a System Library, need not be
283 | included in conveying the object code work.
284 |
285 | A "User Product" is either (1) a "consumer product", which means any
286 | tangible personal property which is normally used for personal, family,
287 | or household purposes, or (2) anything designed or sold for incorporation
288 | into a dwelling. In determining whether a product is a consumer product,
289 | doubtful cases shall be resolved in favor of coverage. For a particular
290 | product received by a particular user, "normally used" refers to a
291 | typical or common use of that class of product, regardless of the status
292 | of the particular user or of the way in which the particular user
293 | actually uses, or expects or is expected to use, the product. A product
294 | is a consumer product regardless of whether the product has substantial
295 | commercial, industrial or non-consumer uses, unless such uses represent
296 | the only significant mode of use of the product.
297 |
298 | "Installation Information" for a User Product means any methods,
299 | procedures, authorization keys, or other information required to install
300 | and execute modified versions of a covered work in that User Product from
301 | a modified version of its Corresponding Source. The information must
302 | suffice to ensure that the continued functioning of the modified object
303 | code is in no case prevented or interfered with solely because
304 | modification has been made.
305 |
306 | If you convey an object code work under this section in, or with, or
307 | specifically for use in, a User Product, and the conveying occurs as
308 | part of a transaction in which the right of possession and use of the
309 | User Product is transferred to the recipient in perpetuity or for a
310 | fixed term (regardless of how the transaction is characterized), the
311 | Corresponding Source conveyed under this section must be accompanied
312 | by the Installation Information. But this requirement does not apply
313 | if neither you nor any third party retains the ability to install
314 | modified object code on the User Product (for example, the work has
315 | been installed in ROM).
316 |
317 | The requirement to provide Installation Information does not include a
318 | requirement to continue to provide support service, warranty, or updates
319 | for a work that has been modified or installed by the recipient, or for
320 | the User Product in which it has been modified or installed. Access to a
321 | network may be denied when the modification itself materially and
322 | adversely affects the operation of the network or violates the rules and
323 | protocols for communication across the network.
324 |
325 | Corresponding Source conveyed, and Installation Information provided,
326 | in accord with this section must be in a format that is publicly
327 | documented (and with an implementation available to the public in
328 | source code form), and must require no special password or key for
329 | unpacking, reading or copying.
330 |
331 | 7. Additional Terms.
332 |
333 | "Additional permissions" are terms that supplement the terms of this
334 | License by making exceptions from one or more of its conditions.
335 | Additional permissions that are applicable to the entire Program shall
336 | be treated as though they were included in this License, to the extent
337 | that they are valid under applicable law. If additional permissions
338 | apply only to part of the Program, that part may be used separately
339 | under those permissions, but the entire Program remains governed by
340 | this License without regard to the additional permissions.
341 |
342 | When you convey a copy of a covered work, you may at your option
343 | remove any additional permissions from that copy, or from any part of
344 | it. (Additional permissions may be written to require their own
345 | removal in certain cases when you modify the work.) You may place
346 | additional permissions on material, added by you to a covered work,
347 | for which you have or can give appropriate copyright permission.
348 |
349 | Notwithstanding any other provision of this License, for material you
350 | add to a covered work, you may (if authorized by the copyright holders of
351 | that material) supplement the terms of this License with terms:
352 |
353 | a) Disclaiming warranty or limiting liability differently from the
354 | terms of sections 15 and 16 of this License; or
355 |
356 | b) Requiring preservation of specified reasonable legal notices or
357 | author attributions in that material or in the Appropriate Legal
358 | Notices displayed by works containing it; or
359 |
360 | c) Prohibiting misrepresentation of the origin of that material, or
361 | requiring that modified versions of such material be marked in
362 | reasonable ways as different from the original version; or
363 |
364 | d) Limiting the use for publicity purposes of names of licensors or
365 | authors of the material; or
366 |
367 | e) Declining to grant rights under trademark law for use of some
368 | trade names, trademarks, or service marks; or
369 |
370 | f) Requiring indemnification of licensors and authors of that
371 | material by anyone who conveys the material (or modified versions of
372 | it) with contractual assumptions of liability to the recipient, for
373 | any liability that these contractual assumptions directly impose on
374 | those licensors and authors.
375 |
376 | All other non-permissive additional terms are considered "further
377 | restrictions" within the meaning of section 10. If the Program as you
378 | received it, or any part of it, contains a notice stating that it is
379 | governed by this License along with a term that is a further
380 | restriction, you may remove that term. If a license document contains
381 | a further restriction but permits relicensing or conveying under this
382 | License, you may add to a covered work material governed by the terms
383 | of that license document, provided that the further restriction does
384 | not survive such relicensing or conveying.
385 |
386 | If you add terms to a covered work in accord with this section, you
387 | must place, in the relevant source files, a statement of the
388 | additional terms that apply to those files, or a notice indicating
389 | where to find the applicable terms.
390 |
391 | Additional terms, permissive or non-permissive, may be stated in the
392 | form of a separately written license, or stated as exceptions;
393 | the above requirements apply either way.
394 |
395 | 8. Termination.
396 |
397 | You may not propagate or modify a covered work except as expressly
398 | provided under this License. Any attempt otherwise to propagate or
399 | modify it is void, and will automatically terminate your rights under
400 | this License (including any patent licenses granted under the third
401 | paragraph of section 11).
402 |
403 | However, if you cease all violation of this License, then your
404 | license from a particular copyright holder is reinstated (a)
405 | provisionally, unless and until the copyright holder explicitly and
406 | finally terminates your license, and (b) permanently, if the copyright
407 | holder fails to notify you of the violation by some reasonable means
408 | prior to 60 days after the cessation.
409 |
410 | Moreover, your license from a particular copyright holder is
411 | reinstated permanently if the copyright holder notifies you of the
412 | violation by some reasonable means, this is the first time you have
413 | received notice of violation of this License (for any work) from that
414 | copyright holder, and you cure the violation prior to 30 days after
415 | your receipt of the notice.
416 |
417 | Termination of your rights under this section does not terminate the
418 | licenses of parties who have received copies or rights from you under
419 | this License. If your rights have been terminated and not permanently
420 | reinstated, you do not qualify to receive new licenses for the same
421 | material under section 10.
422 |
423 | 9. Acceptance Not Required for Having Copies.
424 |
425 | You are not required to accept this License in order to receive or
426 | run a copy of the Program. Ancillary propagation of a covered work
427 | occurring solely as a consequence of using peer-to-peer transmission
428 | to receive a copy likewise does not require acceptance. However,
429 | nothing other than this License grants you permission to propagate or
430 | modify any covered work. These actions infringe copyright if you do
431 | not accept this License. Therefore, by modifying or propagating a
432 | covered work, you indicate your acceptance of this License to do so.
433 |
434 | 10. Automatic Licensing of Downstream Recipients.
435 |
436 | Each time you convey a covered work, the recipient automatically
437 | receives a license from the original licensors, to run, modify and
438 | propagate that work, subject to this License. You are not responsible
439 | for enforcing compliance by third parties with this License.
440 |
441 | An "entity transaction" is a transaction transferring control of an
442 | organization, or substantially all assets of one, or subdividing an
443 | organization, or merging organizations. If propagation of a covered
444 | work results from an entity transaction, each party to that
445 | transaction who receives a copy of the work also receives whatever
446 | licenses to the work the party's predecessor in interest had or could
447 | give under the previous paragraph, plus a right to possession of the
448 | Corresponding Source of the work from the predecessor in interest, if
449 | the predecessor has it or can get it with reasonable efforts.
450 |
451 | You may not impose any further restrictions on the exercise of the
452 | rights granted or affirmed under this License. For example, you may
453 | not impose a license fee, royalty, or other charge for exercise of
454 | rights granted under this License, and you may not initiate litigation
455 | (including a cross-claim or counterclaim in a lawsuit) alleging that
456 | any patent claim is infringed by making, using, selling, offering for
457 | sale, or importing the Program or any portion of it.
458 |
459 | 11. Patents.
460 |
461 | A "contributor" is a copyright holder who authorizes use under this
462 | License of the Program or a work on which the Program is based. The
463 | work thus licensed is called the contributor's "contributor version".
464 |
465 | A contributor's "essential patent claims" are all patent claims
466 | owned or controlled by the contributor, whether already acquired or
467 | hereafter acquired, that would be infringed by some manner, permitted
468 | by this License, of making, using, or selling its contributor version,
469 | but do not include claims that would be infringed only as a
470 | consequence of further modification of the contributor version. For
471 | purposes of this definition, "control" includes the right to grant
472 | patent sublicenses in a manner consistent with the requirements of
473 | this License.
474 |
475 | Each contributor grants you a non-exclusive, worldwide, royalty-free
476 | patent license under the contributor's essential patent claims, to
477 | make, use, sell, offer for sale, import and otherwise run, modify and
478 | propagate the contents of its contributor version.
479 |
480 | In the following three paragraphs, a "patent license" is any express
481 | agreement or commitment, however denominated, not to enforce a patent
482 | (such as an express permission to practice a patent or covenant not to
483 | sue for patent infringement). To "grant" such a patent license to a
484 | party means to make such an agreement or commitment not to enforce a
485 | patent against the party.
486 |
487 | If you convey a covered work, knowingly relying on a patent license,
488 | and the Corresponding Source of the work is not available for anyone
489 | to copy, free of charge and under the terms of this License, through a
490 | publicly available network server or other readily accessible means,
491 | then you must either (1) cause the Corresponding Source to be so
492 | available, or (2) arrange to deprive yourself of the benefit of the
493 | patent license for this particular work, or (3) arrange, in a manner
494 | consistent with the requirements of this License, to extend the patent
495 | license to downstream recipients. "Knowingly relying" means you have
496 | actual knowledge that, but for the patent license, your conveying the
497 | covered work in a country, or your recipient's use of the covered work
498 | in a country, would infringe one or more identifiable patents in that
499 | country that you have reason to believe are valid.
500 |
501 | If, pursuant to or in connection with a single transaction or
502 | arrangement, you convey, or propagate by procuring conveyance of, a
503 | covered work, and grant a patent license to some of the parties
504 | receiving the covered work authorizing them to use, propagate, modify
505 | or convey a specific copy of the covered work, then the patent license
506 | you grant is automatically extended to all recipients of the covered
507 | work and works based on it.
508 |
509 | A patent license is "discriminatory" if it does not include within
510 | the scope of its coverage, prohibits the exercise of, or is
511 | conditioned on the non-exercise of one or more of the rights that are
512 | specifically granted under this License. You may not convey a covered
513 | work if you are a party to an arrangement with a third party that is
514 | in the business of distributing software, under which you make payment
515 | to the third party based on the extent of your activity of conveying
516 | the work, and under which the third party grants, to any of the
517 | parties who would receive the covered work from you, a discriminatory
518 | patent license (a) in connection with copies of the covered work
519 | conveyed by you (or copies made from those copies), or (b) primarily
520 | for and in connection with specific products or compilations that
521 | contain the covered work, unless you entered into that arrangement,
522 | or that patent license was granted, prior to 28 March 2007.
523 |
524 | Nothing in this License shall be construed as excluding or limiting
525 | any implied license or other defenses to infringement that may
526 | otherwise be available to you under applicable patent law.
527 |
528 | 12. No Surrender of Others' Freedom.
529 |
530 | If conditions are imposed on you (whether by court order, agreement or
531 | otherwise) that contradict the conditions of this License, they do not
532 | excuse you from the conditions of this License. If you cannot convey a
533 | covered work so as to satisfy simultaneously your obligations under this
534 | License and any other pertinent obligations, then as a consequence you may
535 | not convey it at all. For example, if you agree to terms that obligate you
536 | to collect a royalty for further conveying from those to whom you convey
537 | the Program, the only way you could satisfy both those terms and this
538 | License would be to refrain entirely from conveying the Program.
539 |
540 | 13. Remote Network Interaction; Use with the GNU General Public License.
541 |
542 | Notwithstanding any other provision of this License, if you modify the
543 | Program, your modified version must prominently offer all users
544 | interacting with it remotely through a computer network (if your version
545 | supports such interaction) an opportunity to receive the Corresponding
546 | Source of your version by providing access to the Corresponding Source
547 | from a network server at no charge, through some standard or customary
548 | means of facilitating copying of software. This Corresponding Source
549 | shall include the Corresponding Source for any work covered by version 3
550 | of the GNU General Public License that is incorporated pursuant to the
551 | following paragraph.
552 |
553 | Notwithstanding any other provision of this License, you have
554 | permission to link or combine any covered work with a work licensed
555 | under version 3 of the GNU General Public License into a single
556 | combined work, and to convey the resulting work. The terms of this
557 | License will continue to apply to the part which is the covered work,
558 | but the work with which it is combined will remain governed by version
559 | 3 of the GNU General Public License.
560 |
561 | 14. Revised Versions of this License.
562 |
563 | The Free Software Foundation may publish revised and/or new versions of
564 | the GNU Affero General Public License from time to time. Such new versions
565 | will be similar in spirit to the present version, but may differ in detail to
566 | address new problems or concerns.
567 |
568 | Each version is given a distinguishing version number. If the
569 | Program specifies that a certain numbered version of the GNU Affero General
570 | Public License "or any later version" applies to it, you have the
571 | option of following the terms and conditions either of that numbered
572 | version or of any later version published by the Free Software
573 | Foundation. If the Program does not specify a version number of the
574 | GNU Affero General Public License, you may choose any version ever published
575 | by the Free Software Foundation.
576 |
577 | If the Program specifies that a proxy can decide which future
578 | versions of the GNU Affero General Public License can be used, that proxy's
579 | public statement of acceptance of a version permanently authorizes you
580 | to choose that version for the Program.
581 |
582 | Later license versions may give you additional or different
583 | permissions. However, no additional obligations are imposed on any
584 | author or copyright holder as a result of your choosing to follow a
585 | later version.
586 |
587 | 15. Disclaimer of Warranty.
588 |
589 | THERE IS NO WARRANTY FOR THE PROGRAM, TO THE EXTENT PERMITTED BY
590 | APPLICABLE LAW. EXCEPT WHEN OTHERWISE STATED IN WRITING THE COPYRIGHT
591 | HOLDERS AND/OR OTHER PARTIES PROVIDE THE PROGRAM "AS IS" WITHOUT WARRANTY
592 | OF ANY KIND, EITHER EXPRESSED OR IMPLIED, INCLUDING, BUT NOT LIMITED TO,
593 | THE IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR
594 | PURPOSE. THE ENTIRE RISK AS TO THE QUALITY AND PERFORMANCE OF THE PROGRAM
595 | IS WITH YOU. SHOULD THE PROGRAM PROVE DEFECTIVE, YOU ASSUME THE COST OF
596 | ALL NECESSARY SERVICING, REPAIR OR CORRECTION.
597 |
598 | 16. Limitation of Liability.
599 |
600 | IN NO EVENT UNLESS REQUIRED BY APPLICABLE LAW OR AGREED TO IN WRITING
601 | WILL ANY COPYRIGHT HOLDER, OR ANY OTHER PARTY WHO MODIFIES AND/OR CONVEYS
602 | THE PROGRAM AS PERMITTED ABOVE, BE LIABLE TO YOU FOR DAMAGES, INCLUDING ANY
603 | GENERAL, SPECIAL, INCIDENTAL OR CONSEQUENTIAL DAMAGES ARISING OUT OF THE
604 | USE OR INABILITY TO USE THE PROGRAM (INCLUDING BUT NOT LIMITED TO LOSS OF
605 | DATA OR DATA BEING RENDERED INACCURATE OR LOSSES SUSTAINED BY YOU OR THIRD
606 | PARTIES OR A FAILURE OF THE PROGRAM TO OPERATE WITH ANY OTHER PROGRAMS),
607 | EVEN IF SUCH HOLDER OR OTHER PARTY HAS BEEN ADVISED OF THE POSSIBILITY OF
608 | SUCH DAMAGES.
609 |
610 | 17. Interpretation of Sections 15 and 16.
611 |
612 | If the disclaimer of warranty and limitation of liability provided
613 | above cannot be given local legal effect according to their terms,
614 | reviewing courts shall apply local law that most closely approximates
615 | an absolute waiver of all civil liability in connection with the
616 | Program, unless a warranty or assumption of liability accompanies a
617 | copy of the Program in return for a fee.
618 |
619 | END OF TERMS AND CONDITIONS
620 |
621 | How to Apply These Terms to Your New Programs
622 |
623 | If you develop a new program, and you want it to be of the greatest
624 | possible use to the public, the best way to achieve this is to make it
625 | free software which everyone can redistribute and change under these terms.
626 |
627 | To do so, attach the following notices to the program. It is safest
628 | to attach them to the start of each source file to most effectively
629 | state the exclusion of warranty; and each file should have at least
630 | the "copyright" line and a pointer to where the full notice is found.
631 |
632 |
633 | Copyright (C)
634 |
635 | This program is free software: you can redistribute it and/or modify
636 | it under the terms of the GNU Affero General Public License as published
637 | by the Free Software Foundation, either version 3 of the License, or
638 | (at your option) any later version.
639 |
640 | This program is distributed in the hope that it will be useful,
641 | but WITHOUT ANY WARRANTY; without even the implied warranty of
642 | MERCHANTABILITY or FITNESS FOR A PARTICULAR PURPOSE. See the
643 | GNU Affero General Public License for more details.
644 |
645 | You should have received a copy of the GNU Affero General Public License
646 | along with this program. If not, see .
647 |
648 | Also add information on how to contact you by electronic and paper mail.
649 |
650 | If your software can interact with users remotely through a computer
651 | network, you should also make sure that it provides a way for users to
652 | get its source. For example, if your program is a web application, its
653 | interface could display a "Source" link that leads users to an archive
654 | of the code. There are many ways you could offer source, and different
655 | solutions will be better for different programs; see section 13 for the
656 | specific requirements.
657 |
658 | You should also get your employer (if you work as a programmer) or school,
659 | if any, to sign a "copyright disclaimer" for the program, if necessary.
660 | For more information on this, and how to apply and follow the GNU AGPL, see
661 | .
662 |
--------------------------------------------------------------------------------
/pbs/README.md:
--------------------------------------------------------------------------------
1 | # fail2ban-proxmox-backup-server
2 |
3 | Fail2Ban for Proxmox Backup Server (PBS)
4 | https://github.com/inettgmbh/fail2ban-proxmox-backup-server
5 |
6 | filter and jail for fail2ban protecting a Proxmox Backup Server (PBS) from brute force attacks to the API/WebGUI
7 |
8 | # Installation
9 |
10 | ## Install fail2ban on a Proxmox Backup Server
11 |
12 | ```
13 | apt -y update; apt -y install fail2ban
14 | ```
15 |
16 | ## Add the configs from this repository
17 |
18 | ```
19 | # Download or clone this repository
20 | git clone https://github.com/inettgmbh/fail2ban-proxmox-backup-server.git
21 |
22 | # Put filter.d/proxmox-backup-server.conf contents to /etc/fail2ban/filter.d/proxmox-backup-server.conf
23 | cp filter.d/proxmox-backup-server.conf /etc/fail2ban/filter.d/proxmox-backup-server.conf
24 |
25 | # Put jail.d/proxmox-backup-server.conf to /etc/fail2ban/jail.d/proxmox-backup-server.conf
26 | cp jail.d/proxmox-backup-server.conf /etc/fail2ban/jail.d/proxmox-backup-server.conf
27 |
28 | # Restart Fail2Ban Service
29 | systemctl restart fail2ban.service
30 | ```
31 |
32 | ## Check if new jail is active
33 |
34 | ```
35 | fail2ban-client status
36 |
37 | Status
38 | |- Number of jail: 2
39 | `- Jail list: proxmox-backup-server, sshd
40 | ```
41 |
42 | ```
43 | fail2ban-client status proxmox-backup-server
44 |
45 | Status for the jail: proxmox-backup-server
46 | |- Filter
47 | | |- Currently failed: 0
48 | | |- Total failed: 0
49 | | `- File list: /var/log/proxmox-backup/api/auth.log
50 | `- Actions
51 | |- Currently banned: 0
52 | |- Total banned: 0
53 | `- Banned IP list:
54 | ```
55 |
--------------------------------------------------------------------------------
/pbs/filter.d/proxmox-backup-server.conf:
--------------------------------------------------------------------------------
1 | # proxmox-backup-server api brute force auth filter: /etc/fail2ban/filter.d/proxmox-backup-server.conf:
2 | #
3 | # Block IPs trying to auth by web or rest api at proxmox-backup-server api
4 | #
5 | # Matches e.g.
6 | # 2020-11-24T13:17:27+01:00: authentication failure; rhost=::ffff:17.225.71.15 user=root@pam msg=AUTH_ERR (7)
7 | # Should not match:
8 | # 2020-11-24T13:17:27+01:00: authentication failure; rhost=::ffff:77.205.51.62 msg=invalid ticket - expired
9 |
10 | [INCLUDES]
11 |
12 | before = common.conf
13 |
14 | [Definition]
15 |
16 | __suffix_failed_login = (AUTH_ERR|invalid credentials).?
17 |
18 | failregex = authentication failure; rhost=.*msg=%(__suffix_failed_login)s
19 |
20 | ignoreregex =
21 |
22 | # Author: Marco Gabriel, inett GmbH
23 |
--------------------------------------------------------------------------------
/pbs/jail.d/proxmox-backup-server.conf:
--------------------------------------------------------------------------------
1 | [proxmox-backup-server]
2 | bantime = 60m
3 | filter = proxmox-backup-server
4 | findtime = 60m
5 | maxretry = 3
6 | enabled = true
7 | port = 8007
8 | backend = systemd
9 | logpath = /var/log/proxmox-backup/api/auth.log
10 |
11 |
--------------------------------------------------------------------------------
/proxmox_toolbox.sh:
--------------------------------------------------------------------------------
1 | #!/bin/bash
2 |
3 | # Tonton Jo - 2024
4 | # Join me on Youtube: https://www.youtube.com/c/tontonjo
5 |
6 | # This little tool is aimed to set some default configurations up and running in not time
7 |
8 | # DISCLAIMER
9 | # I assume you know what you are doing have a backup and have a default configuration.
10 | # I'm responsible in no way if something get broken - even if there's likely no chance to happen:-)
11 | # I am no programmer - just tying to get some begginers life a bit easier
12 | # There will be bugs or things i did not thinked about - sorry - if so, try to solve-it yourself, let me kindly know and PR
13 | # Backup and restore has not been extensivly tested - and has never been tested on cluster configurations - Dont count on it too much
14 |
15 | # USAGE
16 | # You can download and execute this script using:
17 | # wget -qO proxmox_toolbox.sh https://raw.githubusercontent.com/Tontonjo/proxmox_toolbox/main/proxmox_toolbox.sh && bash proxmox_toolbox.sh
18 |
19 | # SOURCES:
20 | # https://pve.proxmox.com/wiki/Fail2ban
21 | # https://pve.proxmox.com/wiki/System_Software_Updates
22 | # https://forum.proxmox.com/threads/how-do-i-set-the-mail-server-to-be-used-in-proxmox.23669/
23 | # https://pve.proxmox.com/wiki/Upgrade_from_6.x_to_7.0
24 |
25 | # https://www.linuxtricks.fr/wiki/proxmox-quelques-infos
26 |
27 | # https://github.com/inettgmbh/fail2ban-proxmox-backup-server
28 | # https://linuxscriptshub.com/configure-smtp-with-gmail-using-postfix/
29 | # https://suoption_pickedpport.google.com/accounts/answer/6010255
30 | # https://www.howtoforge.com/community/threads/solved-problem-with-outgoing-mail-from-server.53920/
31 | # http://mhawthorne.net/posts/2011-postfix-configuring-gmail-as-relay/
32 | # https://docs.oracle.com/en/cloud/cloud-at-customer/occ-get-started/add-ssh-enabled-user.html
33 | # https://www.noobunbox.net/serveur/monitoring/configurer-snmp-v3-sous-debian
34 | # https://blog.lbdg.me/proxmox-best-performance-disable-swappiness/
35 | # https://gist.github.com/mrpeardotnet/6bdc4b504f43ce57fa7eaee96d376edf
36 | # https://github.com/DerDanilo/proxmox-stuff/blob/master/prox_config_backup.sh
37 |
38 |
39 | # TODO:
40 | # settings for zram -> https://pve.proxmox.com/wiki/Zram
41 | # PBS: add support for user creation and backup / restoration
42 | # make things stupid-proof (deny characters when numbers expected ans so on)
43 | # Cosmetic corrections
44 |
45 | # Proxmox_toolbox
46 | version=4.3.2
47 |
48 | # V1.0: Initial Release
49 | # V1.1: correct detecition of subscription message removal
50 | # V2.0: Add backup and restore - reworked menu order - lots of small changes
51 | # V2.2: add confirmation to disable root@pam which is required to update from web UI - add more choices in security settings
52 | # V2.3: Add check of swap existence to allow swap setting configuration
53 | # V2.4: Add check of root rights
54 | # V2.5: Ensure swap setting resist reboot
55 | # V2.6: Much better and smarter way to remove subscription message (credits to @adrien Linuxtricks)
56 | # V2.7: Fix remove subscription message detection
57 | # V3.0: Remove useless mutiple versions for better clarity
58 | # V3.1: Merge backup folder in case there's pve and pbs on the same host - useless to have 2 content list
59 | # V3.2: Restauration now automatically remount directories and reimport existant zpools
60 | # V3.3: Add echo when restarting proxy services
61 | # V3.4: Add proxmox bashrc command to invoke update script usinge "proxmox-update"
62 | # V3.4.1: reverted.
63 | # V3.5: In order to have 1 tool and be able to simply update with ease, now it can be triggered using the -u flag
64 | # V3.6: reworked a bit the snmp menu for better clarity & use systemctl everywhere
65 | # V3.7: Add check when restoring "dir" to ensure the original drive still resides in system to avoid problems at boot
66 | # V3.8: Use /usr/bin instead of .bashrc edit - way better
67 | # V3.8.1: Little enhancement for updates
68 | # V3.9.0: Fix update who happend to not work on first run for no apparent reasons and remove ping in mail menu
69 | # V3.9.1: Add more logic when creating new admin user
70 | # V3.9.2: Specify more clearly the realm to use when creating an alternate admin user
71 | # V3.9.3: Add check for .mount file to avoid error trying to remount
72 | # V3.9.4: Fix detection of enterprise source status in order to not reapply
73 | # V3.9.5: Fix snmp file retreiving - add a success validation befor continuing.
74 | # V3.9.6: add choice to restore the network configuration usefull in case of other network configuration / hardware
75 | # V3.9.7: Add a first run backup for people who rekt their installation and blame the toolbox :) - add some enhancements
76 | # V3.9.8: Uninstall fail2ban when restoring if no config exist in backup content
77 | # V3.9.9: Small cosmetic changes and enhancements, now check for update bin version
78 | # V4.0.0: Some cosmetic changes
79 | # V4.0.1: Small enhancement for backup / restore function - bump bin version to 1.2
80 | # V4.0.2: Small enhancements
81 | # V4.0.3: Update sources before attempt to install packages and ensure git is installed before trying to clone
82 | # V4.1.0: Correction and optimisations in fail2ban setup
83 | # V4.1.1: Important fix in permissions for ssh keys
84 | # V4.1.2: Add Ceph enterprise list to ignored sources when using no-subcription
85 | # V4.1.3: Add a function to restore a working self-signed certificate in case of mistake, replace sleep with a more permissive method
86 | # V4.1.4: reworked menu a bit
87 | # V4.1.5: Fixed fail2ban in proxmox V8 - needed to add "backend = systemd" in every jail
88 | # V4.1.6: Small add to pbs in order to support case where the source.list file is missing (docker container)
89 | # V4.2.0: Add argument to run backup directly
90 | # V4.2.1: Notifications now use hostname in from instead of "root"
91 | # V4.2.2: Add a corosync file to backup content as it appear to be necessary to restore a node in a cluster -> https://github.com/Tontonjo/proxmox_toolbox/issues/19
92 | # V4.2.3: fixed snmpd dependencies installation check to be more reliable
93 | # V4.2.4: Added Rsyslog as it's missing in pve8 and can be usefull to check logs (merci l'ami)
94 | # V4.3.0: Removed email options as pve8 has now a gui configuration tool that is way better. hidden in menu 9 in case :)
95 | # V4.3.1: Removed apt-get upgrade in update as it's useless and less safe thant apt-get dist-upgrade
96 | # V4.3.2: Getting snmp ready for ipv6
97 |
98 | # check if root
99 | if [[ $(id -u) -ne 0 ]] ; then echo "- Please run as root / sudo" ; exit 1 ; fi
100 |
101 | # -----------------User variables----------------------
102 | backupdir="/root/proxmox_config_backups" # NO trailing slash is mandatory
103 | backup_content="/etc/ssh/sshd_config /root/.ssh/ /etc/fail2ban/ /etc/systemd/system/*.mount /etc/network/interfaces /etc/sysctl.conf /etc/resolv.conf /etc/hosts /etc/hostname /etc/cron* /etc/aliases /etc/snmp/ /etc/smartd.conf /usr/share/snmp/snmpd.conf /etc/postfix/ /etc/pve/ /etc/lvm/ /etc/modprobe.d/ /var/lib/pve-firewall/ /var/lib/pve-cluster/ /etc/corosync/authkey /etc/vzdump.conf /etc/ksmtuned.conf /etc/proxmox-backup/"
104 |
105 | # ----------------- System variables----------------------
106 | updatebinversion=1.2
107 | pve_log_folder="/var/log/pve/tasks/"
108 | proxmoxlib="/usr/share/javascript/proxmox-widget-toolkit/proxmoxlib.js"
109 | distribution=$(. /etc/*-release;echo $VERSION_CODENAME)
110 | execdir=$(dirname $0)
111 | hostname=$(hostname)
112 | date=$(date +%Y_%m_%d-%H_%M_%S)
113 | # ---------------END OF VARIABLES-----------------
114 |
115 |
116 |
117 | if [ ! -f /root/proxmox_config_backups/$hostname-firstrun.tar.gz ]; then
118 | echo "- Creating a backup at first run - dont delete it :-)"
119 | mkdir -p /root/proxmox_config_backups/
120 | tar -czf /root/proxmox_config_backups/$hostname-firstrun.tar.gz --absolute-names $backup_content
121 | echo "- First run: a backup of the actual configurations has been created at /root/proxmox_config_backups/$hostname-firstrun.tar.gz"
122 | wait_or_input
123 | fi
124 |
125 | ## Functions
126 | # Function to wait an amount of time or a key press
127 | wait_or_input() {
128 | local timeout=30 # timeout
129 | local input
130 |
131 | if read -t "$timeout" -n 1 -p "- Continue: press any key or wait $timeout seconds... " input; then
132 | echo "Key pressed: continuing"
133 | else
134 | echo "- No key pressed until $timeout tiemout. continuing..."
135 | fi
136 | }
137 | # Update
138 | update () {
139 | # Check if the /usr/bin/proxmox-update entry for update is already created
140 | if ! grep -Fqs "$updatebinversion" /usr/bin/proxmox-update; then
141 | echo "- Downloading / Updating update binary to version $updatebinversion"
142 | wget -qO "/usr/bin/proxmox-update" https://raw.githubusercontent.com/Tontonjo/proxmox_toolbox/main/bin/proxmox-update && chmod +x "/usr/bin/proxmox-update"
143 | update
144 | else
145 | echo "- Updating System using proxmox_toolbox version: $version"
146 | apt-get update -y -qq
147 | apt-get dist-upgrade -y -qq
148 | if grep -Ewqi "no-subscription" /etc/apt/sources.list; then
149 | if grep -q ".data.status.toLowerCase() == 'active') {" $proxmoxlib; then
150 | echo "- Subscription Message already removed - Skipping"
151 | else
152 | if [ -d "$pve_log_folder" ]; then
153 | echo "- Removing No Valid Subscription Message for PVE"
154 | sed -Ezi.bak "s/!== 'active'/== 'active'/" $proxmoxlib && echo "- Restarting proxy service" && systemctl restart pveproxy.service
155 | else
156 | echo "- Removing No Valid Subscription Message for PBS"
157 | sed -Ezi.bak "s/!== 'active'/== 'active'/" $proxmoxlib && echo "- Restarting proxy service" && systemctl restart proxmox-backup-proxy.service
158 | fi
159 | fi
160 | fi
161 | fi
162 | }
163 | # get the snmp configurations
164 | snmpconfig() {
165 | wget -qO /etc/snmp/snmpd.conf https://github.com/Tontonjo/proxmox_toolbox/raw/main/snmp/snmpd.conf
166 | }
167 |
168 | # Display the banner in menu
169 | banner() {
170 | echo -e "${MENU}****************** Proxmox Toolbox **********************${NORMAL}"
171 | echo -e "${MENU}*********** Tonton Jo - 2023 - Version $version ************${NORMAL}"
172 | echo -e "${MENU}********** https://www.youtube.com/c/tontonjo **********${NORMAL}"
173 | echo -e "${MENU} " "${NORMAL}"
174 | }
175 |
176 | # Validate that a content retreiving was successfull
177 | getcontentcheck() {
178 | exitcode=$?
179 | if [ $exitcode -ne 0 ]; then
180 | echo "- Error retreiving ressources - control your internet connexion"
181 | wait_or_input
182 | main_menu
183 | fi
184 | }
185 | # backup the configurations
186 | backup() {
187 | mkdir -p $backupdir
188 | echo "- Creating backup"
189 | tar -czf $backupdir/$hostname-$(date +%Y_%m_%d-%H_%M_%S).tar.gz --absolute-names $backup_content
190 | clear
191 | echo "- Backup done - please control and test it"
192 | echo "- Archive is located in $backupdir"
193 | }
194 | # Arguments
195 | # Thoses are argument that directly trigger specific toolbox functions
196 | if [[ $1 = "-u" ]]; then
197 | update
198 | exit
199 | fi
200 |
201 | if [[ $1 = "-b" ]]; then
202 | backup
203 | exit
204 | fi
205 | # End of arguments
206 |
207 | main_menu(){
208 | clear
209 | NORMAL=`echo "\033[m"`
210 | MENU=`echo "\033[36m"` #Blue
211 | NUMBER=`echo "\033[33m"` #yellow
212 | FGRED=`echo "\033[41m"`
213 | RED_TEXT=`echo "\033[31m"`
214 | ENTER_LINE=`echo "\033[33m"`
215 | banner
216 | echo -e "${MENU}****************** Main menu **********************${NORMAL}"
217 | echo " "
218 | echo -e "${MENU}**${NUMBER} 1)${MENU} No-subscription Sources Configuration ${NORMAL}"
219 | echo -e "${MENU}**${NUMBER} 2)${MENU} Update host & create proxmox-update command ${NORMAL}"
220 | echo -e "${MENU}**${NUMBER} 3)${MENU} Install usefull dependencies ${NORMAL}"
221 | echo -e "${MENU}**${NUMBER} 4)${MENU} Security settings (fail2ban - SSH user - GUI Administrator) ${NORMAL}"
222 | echo -e "${MENU}**${NUMBER} 5)${MENU} SWAP Settings ${NORMAL}"
223 | echo -e "${MENU}**${NUMBER} 6)${MENU} Enable S.M.A.R.T self-tests ${NORMAL}"
224 | echo -e "${MENU}**${NUMBER} 7)${MENU} SNMP settings ${NORMAL}"
225 | echo -e "${MENU}**${NUMBER} 8)${MENU} Configurations backup and restoration ${NORMAL}"
226 | echo -e "${MENU}**${NUMBER} 0)${MENU} Exit ${NORMAL}"
227 | echo " "
228 | echo -e "${MENU}*********************************************${NORMAL}"
229 | echo -e "${ENTER_LINE}Please enter a menu option number or ${RED_TEXT}enter to exit. ${NORMAL}"
230 | read -rsn1 opt
231 | while [ opt != '' ]
232 | do
233 | if [[ $opt = "" ]]; then
234 | exit;
235 | else
236 | case $opt in
237 |
238 | 1) clear;
239 | read -p "This will configure sources for no-enterprise repository - Continue? y = yes / anything = no: " -n 1 -r
240 | if [[ $REPLY =~ ^[Yy]$ ]]; then
241 | if [ -d "$pve_log_folder" ]; then
242 | echo "- Server is a PVE host"
243 | #2: Edit sources list:
244 | echo "- Checking Sources lists"
245 | if grep -Fq "deb http://download.proxmox.com/debian/pve" /etc/apt/sources.list; then
246 | echo "-- Source looks alredy configured - Skipping"
247 | else
248 | echo "-- Adding new entry to sources.list"
249 | sed -i "\$adeb http://download.proxmox.com/debian/pve $distribution pve-no-subscription" /etc/apt/sources.list
250 | fi
251 | echo "- Checking Enterprise Source list"
252 | if grep -Fq "#deb https://enterprise.proxmox.com/debian/pve" "/etc/apt/sources.list.d/pve-enterprise.list"; then
253 | echo "-- Entreprise repo looks already commented - Skipping"
254 | else
255 | echo "-- Hiding Enterprise sources list"
256 | sed -i 's/^/#/' /etc/apt/sources.list.d/pve-enterprise.list
257 | fi
258 | echo "- Checking Ceph Enterprise Source list"
259 | # Checking that source list file exist
260 | if [[ -f "/etc/apt/sources.list.d/ceph.list" ]]; then
261 | # Checking if it source is already commented or not
262 | if grep -Fq "#deb https://enterprise.proxmox.com/debian/ceph-quincy" "/etc/apt/sources.list.d/ceph.list"; then
263 | # If so do nothing
264 | echo "-- Ceph Entreprise repo looks already commented - Skipping"
265 | else
266 | # else comment it
267 | echo "-- Hiding Ceph Enterprise sources list"
268 | sed -i 's/^/#/' /etc/apt/sources.list.d/ceph.list
269 | fi
270 | fi
271 | else
272 | echo "- Server is a PBS host"
273 | echo "- Checking Sources list"
274 | if grep -Fq "deb http://download.proxmox.com/debian/pbs" /etc/apt/sources.list; then
275 | echo "-- Source looks alredy configured - Skipping"
276 | else
277 | echo "-- Adding new entry to sources.list"
278 | sed -i "\$adeb http://download.proxmox.com/debian/pbs $distribution pbs-no-subscription" /etc/apt/sources.list
279 | exitcode=$?
280 | if [ $exitcode -ne 0 ]; then
281 | echo "-- Sources.list seems to be missing as sed failed: creating it in /etc/apt/sources.list"
282 | if [ -f "/etc/apt/sources.list" ]; then
283 | echo "-- Source.list appear to exist but an error was encountered. please report this case on github"
284 | else
285 | echo "-- Creating source.list"
286 | echo "deb http://download.proxmox.com/debian/pbs $distribution pbs-no-subscription" >> /etc/apt/sources.list
287 | wget -q https://enterprise.proxmox.com/debian/proxmox-release-$distribution.gpg -O /etc/apt/trusted.gpg.d/proxmox-release-bookworm.gpg
288 | fi
289 | fi
290 |
291 | fi
292 | echo "- Checking Enterprise Source list"
293 | if grep -Fq "#deb https://enterprise.proxmox.com/debian/pbs" /etc/apt/sources.list.d/pbs-enterprise.list; then
294 | echo "-- Entreprise repo looks already commented - Skipping"
295 | else
296 | echo "-- Hiding Enterprise sources list"
297 | sed -i 's/^/#/' /etc/apt/sources.list.d/pbs-enterprise.list
298 | fi
299 | fi
300 | wait_or_input
301 | fi
302 | main_menu
303 | ;;
304 | 2) clear;
305 | update
306 | wait_or_input
307 | main_menu
308 | ;;
309 | 3) clear;
310 | read -p "- This will install thoses libraries if missing: ifupdown2 - git - sudo - libsasl2-modules - lshw - lm-sensors - Continue? y = yes / anything = no: " -n 1 -r
311 | if [[ $REPLY =~ ^[Yy]$ ]]; then
312 | echo " "
313 | echo "- Updating sources"
314 | apt-get update -y -qq
315 | if [ $(dpkg-query -W -f='${Status}' ifupdown2 2>/dev/null | grep -c "ok installed") -eq 0 ]; then
316 | apt-get install -y ifupdown2;
317 | else
318 | echo "- ifupdown2 already installed"
319 | fi
320 | if [ $(dpkg-query -W -f='${Status}' git 2>/dev/null | grep -c "ok installed") -eq 0 ]; then
321 | apt-get install -y git;
322 | else
323 | echo "- git already installed"
324 | fi
325 | if [ $(dpkg-query -W -f='${Status}' sudo 2>/dev/null | grep -c "ok installed") -eq 0 ]; then
326 | apt-get install -y sudo;
327 | else
328 | echo "- sudo already installed"
329 | fi
330 | if [ $(dpkg-query -W -f='${Status}' libsasl2-modules 2>/dev/null | grep -c "ok installed") -eq 0 ]; then
331 | apt-get install -y libsasl2-modules;.
332 | else
333 | echo "- libsasl2-modules already installed"
334 | fi
335 | if [ $(dpkg-query -W -f='${Status}' lshw 2>/dev/null | grep -c "ok installed") -eq 0 ]; then
336 | apt-get install -y lshw;.
337 | else
338 | echo "- lshw already installed"
339 | fi
340 | if [ $(dpkg-query -W -f='${Status}' lm-sensors 2>/dev/null | grep -c "ok installed") -eq 0 ]; then
341 | apt-get install -y lm-sensors;.
342 | else
343 | echo "- lm-sensors already installed"
344 | fi
345 | if [ $(dpkg-query -W -f='${Status}' rsyslog 2>/dev/null | grep -c "ok installed") -eq 0 ]; then
346 | apt-get install -y rsyslog;
347 | else
348 | echo "- rsyslog already installed"
349 | fi
350 | wait_or_input
351 | fi
352 | main_menu
353 | ;;
354 | 4) clear;
355 | read -p "Do you want to enable fail2ban? y = yes / anything = no: " -n 1 -r
356 | if [[ $REPLY =~ ^[Yy]$ ]]; then
357 | echo " "
358 | echo "- Updating sources"
359 | apt-get update -y -qq
360 | if [ $(dpkg-query -W -f='${Status}' fail2ban 2>/dev/null | grep -c "ok installed") -eq 0 ]; then
361 | apt-get install -y fail2ban;
362 | getcontentcheck
363 | else
364 | echo "- fail2ban already installed"
365 | fi
366 | echo "- Ensuring Git is installed"
367 | if [ $(dpkg-query -W -f='${Status}' git 2>/dev/null | grep -c "ok installed") -eq 0 ]; then
368 | apt-get install -y git;
369 | getcontentcheck
370 | else
371 | echo "- git already installed"
372 | fi
373 | echo "- Retreiving fail2ban Proxmox jails from github"
374 | git clone -q https://github.com/Tontonjo/proxmox_toolbox.git
375 | getcontentcheck
376 | if [ -d "$pve_log_folder" ]; then
377 | echo "- Host is a PVE Host"
378 | # Put filter.d/proxmox-backup-server.conf contents to /etc/fail2ban/filter.d/proxmox-backup-server.conf
379 | cp -f proxmox_toolbox/pve/filter.d/proxmox-virtual-environement.conf /etc/fail2ban/filter.d/proxmox-virtual-environement.conf
380 | # Put jail.d/proxmox-backup-server.conf to /etc/fail2ban/jail.d/proxmox-backup-server.conf
381 | cp -f proxmox_toolbox/pve/jail.d/proxmox-virtual-environement.conf /etc/fail2ban/jail.d/proxmox-virtual-environement.conf
382 | else
383 | echo "- Host is a PBS Host"
384 | # Put filter.d/proxmox-backup-server.conf contents to /etc/fail2ban/filter.d/proxmox-backup-server.conf
385 | cp -f proxmox_toolbox/pbs/filter.d/proxmox-backup-server.conf /etc/fail2ban/filter.d/proxmox-backup-server.conf
386 | # Put jail.d/proxmox-backup-server.conf to /etc/fail2ban/jail.d/proxmox-backup-server.conf
387 | cp -f proxmox_toolbox/pbs/jail.d/proxmox-backup-server.conf /etc/fail2ban/jail.d/proxmox-backup-server.conf
388 | fi
389 | # Adding the right backend to fail2ban sshd configuration
390 | if ! grep -Fqs "systemd" /etc/fail2ban/jail.d/defaults-debian.conf; then
391 | echo "- Backend missing in defaults-debian.conf"
392 | echo -e "\nbackend = systemd" >> /etc/fail2ban/jail.d/defaults-debian.conf
393 | else
394 | echo "- Backend already setted-up in defaults-debian.conf"
395 | fi
396 | # if [ -d "$pve_log_folder" ]; then
397 | # if ! grep -Fqs "systemd" /etc/fail2ban/jail.d/proxmox-virtual-environement.conf; then
398 | # echo "- Backend missing in proxmox-virtual-environement.conf"
399 | # echo -e "\nbackend = systemd" >> /etc/fail2ban/jail.d/proxmox-virtual-environement.conf
400 | # else
401 | # echo "- Backend already setted-up in proxmox-virtual-environement.conf"
402 | # fi
403 | # else
404 | # if ! grep -Fqs "systemd" /etc/fail2ban/jail.d/proxmox-backup-server.conf; then
405 | # echo "- Backend missing in proxmox-backup-server.conf"
406 | # echo -e "\nackend = systemd" >> /etc/fail2ban/jail.d/proxmox-backup-server.conf
407 | # else
408 | # echo "- Backend already setted-up in proxmox-backup-server.conf"
409 | # fi
410 | # fi
411 | # Restart Fail2Ban Service
412 | echo "- Restarting fail2ban service"
413 | systemctl restart fail2ban.service
414 | if systemctl is-active fail2ban | grep -q 'active'; then
415 | echo "- Fail2ban started correctly"
416 | else
417 | echo "- Fail2ban failed to start"
418 | systemctl status fail2ban
419 | fi
420 | echo "- Cleaning git ressources"
421 | rm -rf ./proxmox_toolbox/
422 | wait_or_input
423 | fi
424 | clear
425 | echo "- Do you want to create another SSH user ?"
426 | echo "- This will guide you to create another user, add it as a sudo user and allow sudo users to connect trough ssh"
427 | read -p "- Press: y = yes / anything = no: " -n 1 -r
428 | if [[ $REPLY =~ ^[Yy]$ ]]; then
429 | clear
430 | if [ $(dpkg-query -W -f='${Status}' sudo 2>/dev/null | grep -c "ok installed") -eq 0 ]; then
431 | apt-get install -y sudo
432 | getcontentcheck
433 | else
434 | echo "- sudo already installed"
435 | fi
436 | echo "- What is the new debian user username?: "
437 | read username
438 | clear
439 | useradd -m $username
440 | passwd $username
441 | mkdir /home/$username/.ssh/
442 | ssh-keygen -t rsa -b 4096 -f /home/$username/.ssh/id_rsa -q -N ""
443 | cp /home/$username/.ssh/id_rsa.pub /home/$username/.ssh/authorized_keys
444 | chown -R $username:$username /home/$username/.ssh/
445 | echo "- New user $username created"
446 | echo "- Adding user to sudo users"
447 | adduser $username sudo
448 | echo "AllowGroups sudo" >> "/etc/ssh/sshd_config"
449 | read -p "- Do you want to deny root SSH login? y = yes / anything = no: " -n 1 -r
450 | if [[ $REPLY =~ ^[Yy]$ ]]; then
451 | if grep -qF "PermitRootLogin yes" /etc/ssh/sshd_config; then
452 | sed -i 's/PermitRootLogin yes/PermitRootLogin no/g' /etc/ssh/sshd_config
453 | else
454 | main_menu
455 | fi
456 | systemctl restart ssh sshd
457 | fi
458 | clear
459 | fi
460 | clear
461 | if [ -d "$pve_log_folder" ]; then
462 | read -p "- Do you want to create an alternate PVE admin user? y = yes / anything = no: " -n 1 -r
463 | if [[ $REPLY =~ ^[Yy]$ ]]; then
464 | clear
465 | echo "- What is the new pve username: "
466 | read pveusername
467 | echo "- Creating PVE user $pveusername"
468 | pveum user add $pveusername@pve
469 | pveum passwd $pveusername@pve
470 | clear
471 | echo "- What is the new admin group name: "
472 | read admingroup
473 | clear
474 | echo "- Creating PVE admin group $admingroup"
475 | pveum group add $admingroup -comment "System Administrators"
476 | echo "- Defining administrators right"
477 | pveum acl modify / -group $admingroup -role Administrator
478 | echo "- adding $pveusername to $admingroup"
479 | pveum user modify $pveusername@pve -group $admingroup
480 | clear
481 | echo "- You can now login on GUI with $pveusername@Proxmox VE authenticaton Realm"
482 | wait_or_input
483 | echo " "
484 | echo "!! Warning - root@pam is required to update host from Proxmox web ui !!"
485 | read -p "- Do you want to disable "root@pam"? y = yes / anything = no: " -n 1 -r
486 | if [[ $REPLY =~ ^[Yy]$ ]]; then
487 | clear
488 | read -p "- Are you sure you want to disable root@pam? y = yes / anything = no: " -n 1 -r
489 | if [[ $REPLY =~ ^[Yy]$ ]]; then
490 | echo "- Removing root user from PVE"
491 | pveum user modify root@pam -enable 0
492 | fi
493 | fi
494 | fi
495 | clear
496 |
497 | else
498 | echo "- Host is a PBS host - user management not implemented ATM"
499 | fi
500 | main_menu
501 | ;;
502 | 5) clear;
503 | lsblk | grep -qi swap
504 | swapenabled=$?
505 | if [ $swapenabled -eq 0 ]; then
506 | echo ""
507 | swapvalue=$(cat /proc/sys/vm/swappiness)
508 | echo "- SWAP is actually set on $swapvalue"
509 | echo "- Recommanded value: 1 - The lower the value - the less SWAP will be used - 0 to use SWAP only when out of memory"
510 | read -p "- Do you want to edit swappiness value or disable SWAP? y = yes / anything = no: " -n 1 -r
511 | if [[ $REPLY =~ ^[Yy]$ ]]; then
512 | echo ""
513 | echo "- What is the new swapiness value? 0 to 100 "
514 | read newswapvalue
515 | echo "- Setting swapiness to $newswapvalue"
516 | sysctl vm.swappiness=$newswapvalue
517 | echo "vm.swappiness=$newswapvalue" > /etc/sysctl.d/swappiness.conf
518 | echo "- Emptying swap - This may take some time"
519 | swapoff -a
520 | echo "- Re-enabling with a swapiness of: $newswapvalue"
521 | swapon -a
522 | wait_or_input
523 | fi
524 | else
525 | echo " - System has no swap - Nothing to do"
526 | wait_or_input
527 | fi
528 | main_menu
529 | ;;
530 | 6) clear;
531 | read -p "- Do you want to enable short and long S.M.A.R.T self-tests? y = yes / anything = no: " -n 1 -r
532 | clear
533 | if [[ $REPLY =~ ^[Yy]$ ]]; then
534 | if grep -Ewqi "(S/../../7/22|L/../01/./22)" /etc/smartd.conf; then
535 | echo "- Self tests looks already configured"
536 | echo "- Short smart test will occure every sunday at 22H and long smart tests every 1 of month at 22H"
537 | else
538 | cp /etc/smartd.conf /etc/smartd.conf.BCK
539 | echo "- Enabling short and long self-tests"
540 | echo "- Short smart test will occure every sunday at 22H and long smart tests every 1 of month at 22H"
541 | echo "DEVICESCAN -d auto -n never -a -s (S/../../7/22|L/../01/./22) -m root -M exec /usr/share/smartmontools/smartd-runner" > "/etc/smartd.conf"
542 | fi
543 | wait_or_input
544 | fi
545 | main_menu
546 | ;;
547 | 7) clear;
548 | read -p "- Install and configure SNMP? y = yes / anything = no: " -n 1 -r
549 | if [[ $REPLY =~ ^[Yy]$ ]]; then
550 | echo " "
551 | if [ $(dpkg-query -W -f='${Status}' git 2>/dev/null | grep -c "ok installed") -eq 0 ]; then
552 | apt-get install -y git;
553 | else
554 | echo "- git already installed"
555 | fi
556 | git clone -q https://github.com/Tontonjo/proxmox_toolbox.git
557 | if [ $(dpkg-query -W -f='${Status}' snmpd 2>/dev/null | grep -c "ok installed") -eq 0 ]; then
558 | apt-get install -y snmpd;
559 | else
560 | echo "- snmpd already installed"
561 | fi
562 | if [ $(dpkg-query -W -f='${Status}' libsnmp-dev 2>/dev/null | grep -c "ok installed") -eq 0 ]; then
563 | apt-get install -y libsnmp-dev;
564 | else
565 | echo "- libsnmp-dev already installed"
566 | fi
567 | clear
568 | read -p "- Press 2 for snmpv2 or 3 for SNMP V3 (ReadOnly) or anything to return to menu: " -n 1 -r
569 | if [[ $REPLY =~ ^[2]$ ]]; then
570 | clear
571 | cp -n /etc/snmp/snmpd.conf /etc/snmp/snmpd.conf.backup
572 | snmpconfig
573 | getcontentcheck
574 | echo "- Read only community name? (ex: ro_tontonjo): "
575 | read rocommunity
576 | echo "- Allowed subnet? Enter for none (x.x.x.x/xx): "
577 | read allowedsubnet
578 | echo "- Allowed subnet for IPV6? Enter for none (xx::xx/xx): "
579 | read allowedsubnet6
580 | echo "- Setting SNMP"
581 | echo "rocommunity $rocommunity $allowedsubnet" >> /etc/snmp/snmpd.conf
582 | echo "rocommunity6 $rocommunity" >> /etc/snmp/snmpd.conf
583 | elif [[ $REPLY =~ ^[3]$ ]]; then
584 | clear
585 | cp -n /etc/snmp/snmpd.conf /etc/snmp/snmpd.conf.backup
586 | snmpconfig
587 | getcontentcheck
588 | echo "- Encryption will be MD5 and DES"
589 | systemctl stop snmpd
590 | echo "- Deleting old SNMPv3 users in /usr/share/snmp/snmpd.conf"
591 | rm -f /usr/share/snmp/snmpd.conf
592 | echo "!! min 8 charachters password !!"
593 | net-snmp-config --create-snmpv3-user -ro -a MD5 -x DES
594 | else
595 | clear
596 | echo "- Returning to menu - no valid choice selected"
597 | wait_or_input
598 | main_menu
599 | fi
600 | systemctl restart snmpd
601 | wait_or_input
602 | fi
603 | main_menu
604 | ;;
605 | 8) clear;
606 | backup_menu
607 |
608 | ;;
609 | 9) clear;
610 | mail_menu
611 | ;;
612 |
613 | 0)
614 | clear
615 | exit
616 | ;;
617 | esac
618 | fi
619 | done
620 | main_menu
621 | }
622 |
623 | mail_menu(){
624 | if [ $(dpkg-query -W -f='${Status}' libsasl2-modules 2>/dev/null | grep -c "ok installed") -eq 0 ]; then
625 | apt-get install -yqq libsasl2-modules;
626 | fi
627 | if [ $(dpkg-query -W -f='${Status}' mailutils 2>/dev/null | grep -c "ok installed") -eq 0 ]; then
628 | apt-get install -yqq mailutils;
629 | fi
630 | clear
631 | ALIASESBCK=/etc/aliases.BCK
632 | if test -f "$ALIASESBCK"; then
633 | echo "backup OK"
634 | else
635 | cp -n /etc/aliases /etc/aliases.BCK
636 | fi
637 | MAINCFBCK=/etc/postfix/main.cf.BCK
638 | if test -f "$MAINCFBCK"; then
639 | echo "backup OK"
640 | else
641 | cp -n /etc/postfix/main.cf /etc/postfix/main.cf.BCK
642 | fi
643 | clear
644 | NORMAL=`echo "\033[m"`
645 | MENU=`echo "\033[36m"` #Blue
646 | NUMBER=`echo "\033[33m"` #yellow
647 | FGRED=`echo "\033[41m"`
648 | RED_TEXT=`echo "\033[31m"`
649 | ENTER_LINE=`echo "\033[33m"`
650 | banner
651 | echo -e "${MENU}****************** Mail Menu (LEGACY) **********************${NORMAL}"
652 | echo " "
653 | echo -e "${MENU}**${NUMBER} 1)${MENU} Configure ${NORMAL}"
654 | echo -e "${MENU}**${NUMBER} 2)${MENU} Test ${NORMAL}"
655 | echo -e "${MENU}**${NUMBER} 3)${MENU} Check logs for known errors - attempt to correct ${NORMAL}"
656 | echo -e "${MENU}**${NUMBER} 4)${MENU} Restore original conf ${NORMAL}"
657 | echo -e "${MENU}**${NUMBER} 0)${MENU} Back ${NORMAL}"
658 | echo " "
659 | echo -e "${MENU}*********************************************${NORMAL}"
660 | echo -e "${ENTER_LINE}Please enter a menu option number or ${RED_TEXT}enter to exit. ${NORMAL}"
661 | read -rsn1 opt
662 | while [ opt != '' ]
663 | do
664 | if [[ $opt = "" ]]; then
665 | exit;
666 | else
667 | case $opt in
668 | 1) clear;
669 | echo "- System administrator recipient mail address (user@domain.tld) (root alias): "
670 | read 'rootaddressalias'
671 | echo "- What is the mail server hostname? (smtp.gmail.com): "
672 | read 'mailserverhostname'
673 | echo "- What is the mail SMTP port? (Usually 587 - can be 25 (no tls)): "
674 | read 'smtpport'
675 | read -p "- Does the server require TLS? y = yes / anything = no: " -n 1 -r
676 | if [[ $REPLY =~ ^[Yy]$ ]]; then
677 | vartls=yes
678 | else
679 | vartls=no
680 | fi
681 | echo " "
682 | echo "- What is the AUTHENTIFICATION USERNAME? (user@domain.tld or username): "
683 | read 'authusername'
684 | echo "- What is the AUTHENTIFICATION PASSWORD?: "
685 | read 'authpassword'
686 | echo "- Is the SENDER mail address the same as the AUTHENTIFICATION USERNAME?"
687 | read -p " y to use $authusername / Enter to set something else: " -n 1 -r
688 | if [[ $REPLY =~ ^[Yy]$ ]]; then
689 | senderaddress=$authusername
690 | else
691 | echo " "
692 | echo "- What is the sender email address?: "
693 | read 'senderaddress'
694 | fi
695 | echo " "
696 | echo "- Working on it!"
697 | echo " "
698 | echo "- Setting Aliases"
699 | if grep "root:" /etc/aliases
700 | then
701 | echo "- Alias entry was found: editing for $rootaddressalias"
702 | sed -i "s/^root:.*$/root: $rootaddressalias/" /etc/aliases
703 | else
704 | echo "- No root alias found: Adding"
705 | echo "root: $rootaddressalias" >> /etc/aliases
706 | fi
707 |
708 | #Setting canonical file for sender - :
709 | echo "root $senderaddress" > /etc/postfix/canonical
710 | chmod 600 /etc/postfix/canonical
711 |
712 | # Preparing for password hash
713 | echo [$mailserverhostname]:$smtpport $authusername:$authpassword > /etc/postfix/sasl_passwd
714 | chmod 600 /etc/postfix/sasl_passwd
715 |
716 | # Add mailserver in main.cf
717 | sed -i "/#/!s/\(relayhost[[:space:]]*=[[:space:]]*\)\(.*\)/\1"[$mailserverhostname]:"$smtpport""/" /etc/postfix/main.cf
718 |
719 | # Checking TLS settings
720 | echo "- Setting correct TLS Settings: $vartls"
721 | postconf smtp_use_tls=$vartls
722 |
723 | # Checking for password hash entry
724 | if grep "smtp_sasl_password_maps" /etc/postfix/main.cf
725 | then
726 | echo "- Password hash already setted-up"
727 | else
728 | echo "- Adding password hash entry"
729 | postconf smtp_sasl_password_maps=hash:/etc/postfix/sasl_passwd
730 | fi
731 | #checking for certificate
732 | if grep "smtp_tls_CAfile" /etc/postfix/main.cf
733 | then
734 | echo "- TLS CA File looks setted-up"
735 | else
736 | postconf smtp_tls_CAfile=/etc/ssl/certs/ca-certificates.crt
737 | fi
738 | # Adding sasl security options
739 | # eliminates default security options which are imcompatible with gmail
740 | if grep "smtp_sasl_security_options" /etc/postfix/main.cf
741 | then
742 | echo "- Google smtp_sasl_security_options setted-up"
743 | else
744 | postconf smtp_sasl_security_options=noanonymous
745 | fi
746 | if grep "smtp_sasl_auth_enable" /etc/postfix/main.cf
747 | then
748 | echo "- Authentification already enabled"
749 | else
750 | postconf smtp_sasl_auth_enable=yes
751 | fi
752 | if grep "sender_canonical_maps" /etc/postfix/main.cf
753 | then
754 | echo "- Canonical entry already existing"
755 | else
756 | postconf sender_canonical_maps=hash:/etc/postfix/canonical
757 | fi
758 | if grep "smtp_header_checks" /etc/postfix/main.cf
759 | then
760 | echo "- smtp_header_checks entry already existing"
761 | else
762 | postconf -e 'smtp_header_checks = regexp:/etc/postfix/header_checks'
763 | echo "/^From:(.*)/ REPLACE From: $hostname <$senderaddress>" > /etc/postfix/header_checks
764 | fi
765 | echo "- Encrypting password and canonical entry"
766 | postmap /etc/postfix/sasl_passwd
767 | postmap /etc/postfix/canonical
768 | postmap /etc/postfix/header_checks
769 | echo "- Restarting postfix and enable automatic startup"
770 | systemctl restart postfix && systemctl enable postfix
771 | echo "- Cleaning file used to generate password hash"
772 | rm -rf "/etc/postfix/sasl_passwd"
773 | echo "- Files cleaned"
774 | wait_or_input
775 | mail_menu;
776 | ;;
777 |
778 | 2) clear;
779 | echo "- What is the recipient email address? :"
780 | read vardestaddress
781 | echo "- An email will be sent to: $vardestaddress"
782 | echo “If you receive this, it means your email configurations looks correct. Yay!” | mail -s "test mail - $hostname - $date" $vardestaddress
783 | echo "- Email should have been sent - If none received, you may want to check for errors in menu 3"
784 | wait_or_input
785 |
786 | mail_menu;
787 | ;;
788 | 3) clear;
789 | echo "- Checking for known errors that may be found in logs"
790 | if grep "SMTPUTF8 is required" "/var/log/mail.log"
791 | then
792 | echo "- Errors im log found - SMTPUTF8 is required"
793 | if grep "smtputf8_enable = no" /etc/postfix/main.cf
794 | then
795 | echo "- Fix looks already applied!"
796 | else
797 | echo " "
798 | echo "- Setting "smtputf8_enable=no" to correct "SMTPUTF8 was required but not supported""
799 | postconf smtputf8_enable=no
800 | postfix reload
801 | fi
802 |
803 | elif grep "Network is unreachable" "/var/log/mail.log"; then
804 | read -p "- Are you on IPv4 AND your host can resolve and access public adresses? y = yes / anything = no: " -n 1 -r
805 | if [[ $REPLY =~ ^[Yy]$ ]]; then
806 | if grep "inet_protocols = ipv4" /etc/postfix/main.cf
807 | then
808 | echo "- Fix looks already applied!"
809 | else
810 | echo " "
811 | echo "- Setting "inet_protocols = ipv4 " to correct ""Network is unreachable" caused by ipv6 resolution""
812 | postconf inet_protocols=ipv4
813 | postfix reload
814 | fi
815 | fi
816 | elif grep "smtp_tls_security_level = encrypt" "/var/log/mail.log"; then
817 | echo "- Errors im log found - smtp_tls_security_level = encrypt is required"
818 | if grep "smtp_tls_security_level = encrypt" /etc/postfix/main.cf; then
819 | echo "- Fix looks already applied!"
820 | else
821 | echo " "
822 | echo "- Setting "smtp_tls_security_level = encrypt" to correct"
823 | postconf inet_protocols=ipv4
824 | postfix reload
825 | fi
826 | elif grep "smtp_tls_wrappermode = yes" "/var/log/mail.log"; then
827 | echo "- Errors im log found - smtp_tls_wrappermode = yes is required"
828 | if grep "smtp_tls_wrappermode = yes" /etc/postfix/main.cf; then
829 | echo "- Fix looks already applied!"
830 | else
831 | echo " "
832 | echo "- Setting "smtp_tls_wrappermode = yes" to correct"
833 | postconf smtp_tls_wrappermode=yes
834 | postfix reload
835 | fi
836 | else
837 | echo "- No configured error found - nothing to do!"
838 | wait_or_input
839 | fi
840 | mail_menu;
841 | ;;
842 | 4) clear;
843 | read -p "- Do you really want to restore? y = yes / anything = no: " -n 1 -r
844 | if [[ $REPLY =~ ^[Yy]$ ]]; then
845 | echo " "
846 | echo "- Restoring default configuration files"
847 | cp -rf /etc/aliases.BCK /etc/aliases
848 | cp -rf /etc/postfix/main.cf.BCK /etc/postfix/main.cf
849 | echo "- Restarting services "
850 | systemctl restart postfix
851 | echo "- Restoration done"
852 | wait_or_input
853 | fi
854 | mail_menu;
855 | ;;
856 |
857 | 0) clear;
858 | main_menu;
859 | ;;
860 |
861 | x)exit;
862 | ;;
863 |
864 | \n)exit;
865 | ;;
866 |
867 | *)clear;
868 | main_menu;
869 | ;;
870 | esac
871 | fi
872 | done
873 | }
874 |
875 | backup_menu(){
876 | clear
877 | NORMAL=`echo "\033[m"`
878 | MENU=`echo "\033[36m"` #Blue
879 | NUMBER=`echo "\033[33m"` #yellow
880 | FGRED=`echo "\033[41m"`
881 | RED_TEXT=`echo "\033[31m"`
882 | ENTER_LINE=`echo "\033[33m"`
883 | banner
884 | echo -e "${MENU}************ Backup and restoration Menu ****************${NORMAL}"
885 | echo " "
886 | echo -e "${MENU}**${NUMBER} 1)${MENU} Backup configuration ${NORMAL}"
887 | echo -e "${MENU}**${NUMBER} 2)${MENU} Restore configuration ${NORMAL}"
888 | echo -e "${MENU}**${NUMBER} 3)${MENU} Restore a Self signed certificate ${NORMAL}"
889 | echo -e "${MENU}**${NUMBER} 0)${MENU} Back ${NORMAL}"
890 | echo " "
891 | echo -e "${MENU}*********************************************${NORMAL}"
892 | echo -e "${ENTER_LINE}Please enter a menu option number or ${RED_TEXT}enter to exit. ${NORMAL}"
893 | read -rsn1 opt
894 | while [ opt != '' ]
895 | do
896 | if [[ $opt = "" ]]; then
897 | exit;
898 | else
899 | case $opt in
900 | 1) clear;
901 | backup
902 | wait_or_input
903 | clear
904 | backup_menu
905 | ;;
906 | 2) clear;
907 | unset options i
908 | while IFS= read -r -d $'\0' f; do
909 | options[i++]="$f"
910 | done < <(find $backupdir -maxdepth 1 -type f -name "*.tar.gz" -print0 )
911 | select opt in "${options[@]}" "- Return to backup menu"; do
912 | case "$opt" in
913 | *.tar.gz)
914 | echo "- Backup $opt selected"
915 | read -p "- Proceed with the restoration? y = yes / anything = no: " -n 1 -r
916 | if [[ $REPLY =~ ^[Yy]$ ]]; then
917 | echo " "
918 | read -p "- Do you want to restore the network configuration aswell? y = yes / anything = no: " -n 1 -r
919 | if [[ $REPLY =~ ^[Yy]$ ]]; then
920 | tar -xf "$opt" -C /
921 |
922 | else
923 | tar -xf "$opt" --exclude='/etc/network/interfaces' -C /
924 | fi
925 | clear
926 | echo "- File restauration done"
927 | echo "- Installing missing dependencies if missing"
928 | if [ -d "/etc/snmp/" ]; then
929 | echo "- snmp config found - installing snmpd"
930 | apt-get -yqq install snmpd libsnmp-dev
931 | fi
932 | archivecontent=$(tar -tvf $opt)
933 | if cat $archivecontent | grep -qi fail2ban; then
934 | echo "- fail2ban config found - installing fail2ban"
935 | apt-get -yqq install fail2ban
936 | else
937 | echo "- fail2ban config NOT found - uninstalling fail2ban if existing"
938 | apt-get -yqq remove --purge fail2ban
939 | fi
940 | echo "- Remounting previously existing storages if any"
941 | if find /etc/systemd/system/*.mount; then
942 | echo "- .mount file found - trying to remount"
943 | for mount in /etc/systemd/system/*.mount; do
944 | source $mount >/dev/null 2>&1
945 | echo "- Checking if $mount is still present in system"
946 | if find /dev/disk/by-uuid/ | grep -w $What; then
947 | echo "- Remountig using configuration $mount"
948 | mkdir -p "$Where"
949 | echo "$What $Where $Type $Options 0 2" >> /etc/fstab
950 | else
951 | echo "- The drive for $mount was not found and will not be mounted back"
952 | fi
953 | done
954 | mount -a
955 | else
956 | echo "- No .mount file found"
957 | fi
958 | for pool in $(zpool import | grep pool: | awk '{print $2}'); do
959 | echo "- Importing pool $pool"
960 | zpool import -f $pool
961 | done
962 | wait_or_input
963 | read -p "- Do you want to reboot host now? y = yes / anything = no: " -n 1 -r
964 | if [[ $REPLY =~ ^[Yy]$ ]]; then
965 | reboot now
966 | else
967 | main_menu
968 | fi
969 | else
970 | clear
971 | backup_menu
972 | fi
973 | ;;
974 | "- Return to backup menu")
975 | backup_menu
976 | ;;
977 | *)
978 | echo "- Please choose using an number"
979 | ;;
980 | esac
981 | done
982 | ;;
983 | 3) clear;
984 | echo "- Removing old certificates "
985 | rm -f /etc/pve/pve-root-ca.pem
986 | rm -f /etc/pve/priv/pve-root-ca.key
987 | rm -f /etc/pve/nodes/$hostname/pve-ssl.pem
988 | rm -f /etc/pve/nodes/$hostname/pve-ssl.key
989 | echo "- Generating new certificates"
990 | pvecm updatecerts -f
991 | wait_or_input
992 | clear
993 | backup_menu
994 | ;;
995 | 0) clear;
996 | main_menu;
997 | ;;
998 |
999 | x)exit;
1000 | ;;
1001 |
1002 | \n)exit;
1003 | ;;
1004 |
1005 | *)clear;
1006 | main_menu;
1007 | ;;
1008 | esac
1009 | fi
1010 | done
1011 | }
1012 |
1013 | main_menu
1014 |
--------------------------------------------------------------------------------
/pve/filter.d/proxmox-virtual-environement.conf:
--------------------------------------------------------------------------------
1 | [Definition]
2 | failregex = pvedaemon\[.*authentication failure; rhost= user=.* msg=.*
3 | ignoreregex =
4 |
--------------------------------------------------------------------------------
/pve/jail.d/proxmox-virtual-environement.conf:
--------------------------------------------------------------------------------
1 | [proxmox]
2 | enabled = true
3 | port = https,http,8006
4 | filter = proxmox-virtual-environement
5 | logpath = /var/log/daemon.log
6 | backend = systemd
7 | maxretry = 3
8 | # 1 hour
9 | bantime = 3600
10 |
--------------------------------------------------------------------------------
/snmp/snmpd.conf:
--------------------------------------------------------------------------------
1 | # Default config
2 | # Tonton Jo - 2021
3 |
4 | # open up
5 | agentAddress udp:161,udp6:161
6 | # run as
7 | agentuser root
8 | # dont log connection from UDP:
9 | dontLogTCPWrappersConnects yes
10 | # fix for disks larger then 2TB
11 | realStorageUnits 0
12 | includeFile /usr/share/snmp/snmpd.conf
13 |
14 | # User settings
15 |
--------------------------------------------------------------------------------