├── notebooks
├── 05. ML Models in DLT Pipelines.py
├── 04. Advanced DLT Concepts.py
├── 02. Building Delta Live Tables Pipelines-SQL.sql
├── 06. DLT Log Analysis.py
├── 01-Structured Streaming with Databricks Delta Tables.py
└── 03. Process Change Data Capture (CDC) data In DLT Pipeline.py
├── README.md
└── LICENSE
/notebooks/05. ML Models in DLT Pipelines.py:
--------------------------------------------------------------------------------
1 | # Databricks notebook source
2 | # MAGIC %pip install mlflow
3 | # MAGIC %pip install databricks
4 | # MAGIC %pip install cffi==1.14.5
5 | # MAGIC %pip install cloudpickle==1.6.0
6 | # MAGIC %pip install databricks-automl-runtime==0.1.0
7 | # MAGIC %pip install holidays==0.11.2
8 | # MAGIC %pip install koalas==1.8.1
9 | # MAGIC %pip install lightgbm==3.1.1
10 | # MAGIC %pip install matplotlib==3.4.2
11 | # MAGIC %pip install psutil==5.8.0
12 | # MAGIC %pip install scikit-learn==0.24.1
13 | # MAGIC %pip install simplejson==3.17.2
14 | # MAGIC %pip install typing-extensions==3.7.4.3
15 |
16 | # COMMAND ----------
17 |
18 | import dlt
19 | import mlflow
20 | from pyspark.sql.functions import struct
21 | from mlflow.store.artifact.models_artifact_repo import ModelsArtifactRepository
22 | import os
23 |
24 | # COMMAND ----------
25 |
26 | @dlt.table(
27 | name='sales_by_day_forecast'
28 | )
29 | def sales_by_day_forecast():
30 | import mlflow
31 | ## Get Model param
32 | model_name = "dlt_workshop_retail_forecast"
33 | model_uri = f"models:/{model_name}/2" ## New version developed on 9.1 LTS
34 |
35 | #logged_model = 'runs:/e4d61bc06e4b4b3fad5ce3709c457f6e/model'
36 |
37 | # Load model as a Spark UDF. Override result_type if the model does not return double values.
38 | loaded_model = mlflow.pyfunc.spark_udf(spark, model_uri=model_uri, result_type='double')
39 |
40 | source_table = dlt.read("sales_by_day")
41 | columns = list(source_table.columns)
42 |
43 | # Predict on a Spark DataFrame.
44 | output_df = source_table.withColumn('predictions', loaded_model(*columns))
45 |
46 | return output_df
47 |
--------------------------------------------------------------------------------
/README.md:
--------------------------------------------------------------------------------
1 | # Intorduction: Delta-Live-Tables-Hands-on-Workshop
2 | Welcome to the repository for the Databricks 1:M Delta Live Tables Workshop!
3 |
4 | This repository contains the notebooks that are used in the workshop to demonstrate the use of Delta Live Tables to build simple, scalable , production-ready pipelines that provides built-in data quality controls and monitoring, data pipeline logging, data lineage tracking, automated pipeline orchestration, automatic Error Handling, advanced auto-scaling, change data capture (CDC) and advanced data engineering concepts (window functions and meta-programming) into a simple pipeline.
5 |  6 |
7 |
8 |
9 | 
10 |
11 |
12 |
13 | # Reading Resources
14 |
15 | See below links for more documentation:
16 | * [How to Process IoT Device JSON Data Using Apache Spark Datasets and DataFrames](https://databricks.com/blog/2016/03/28/how-to-process-iot-device-json-data-using-apache-spark-datasets-and-dataframes.html)
17 | * [Spark Structure Streaming](https://databricks.com/blog/2016/07/28/structured-streaming-in-apache-spark.html)
18 | * [Beyond Lambda](https://databricks.com/discover/getting-started-with-delta-lake-tech-talks/beyond-lambda-introducing-delta-architecture)
19 | * [Delta Lake Docs](https://docs.databricks.com/delta/index.html)
20 | * [Medallion Architecture](https://databricks.com/solutions/data-pipelines)
21 | * [Cost Savings with the Medallion Architecture](https://techcommunity.microsoft.com/t5/analytics-on-azure/how-to-reduce-infrastructure-costs-by-up-to-80-with-azure/ba-p/1820280)
22 | * [Change Data Capture Streams with the Medallion Architecture](https://databricks.com/blog/2021/06/09/how-to-simplify-cdc-with-delta-lakes-change-data-feed.html)
23 |
24 |
25 |
26 | # Workshop Flow
27 |
28 | The workshop consists of 4 interactive sections that are separated by 4 notebooks located in the notebooks folder in this repository. Each is run sequentially as we explore the abilities of the lakehouse from data ingestion, data curation, and performance optimizations
29 | |Notebook|Summary|
30 | |--------|-------|
31 | |`01-Structured Streaming with Databricks Delta Tables`|Processing and ingesting data at scale utilizing databricks tunables and the medallion architecture|
32 | |`02-Orchestrating with Delta Live Tables`|Changing Spark Properties, Configuring Table Properties, Optimization of Tables, Combining Batch and Incremental Tables|
33 | |`03. Implement CDC In DLT Pipeline: Change Data Capture (Python)`|Implementing Change Data Capture in DLT pipelines for accessing to fresh data|
34 | |`04: Meta-programming`|Examples of metaprogramming in DLT When to use/problems is solved How to configure|
35 | |`05: ML Models in DLT Pipelines`|Example of integratation of ML models with DLT pipelines|
36 |
37 |
38 |
39 | # Setup / Requirements
40 |
41 | This workshop requires a running Databricks workspace. If you are an existing Databricks customer, you can use your existing Databricks workspace. Otherwise, the notebooks in this workshop have been tested to run on [Databricks Community Edition](https://databricks.com/product/faq/community-edition) as well.
42 |
43 | ## DBR Version
44 |
45 | The features used in this workshop require `DBR 9.1 LTS`+.
46 |
47 | ## Repos
48 |
49 | If you have repos enabled on your Databricks workspace. You can directly import this repo and run the notebooks as is and avoid the DBC archive step.
50 |
51 | ## DBC Archive
52 |
53 | Download the DBC archive from releases and import the archive into your Databricks workspace.
54 |
--------------------------------------------------------------------------------
/notebooks/04. Advanced DLT Concepts.py:
--------------------------------------------------------------------------------
1 | # Databricks notebook source
2 | # MAGIC %md
3 | # MAGIC When creating the pipeline:
4 | # MAGIC * add the following configuration to point to the data source `data_source_path` : `/databricks-datasets/online_retail/data-001/`
5 | # MAGIC * add the following configuration to read the country list from the correct schema/db : `dbName`: `username_workshop_db`
6 | # MAGIC * add notebook number 2 (`02. Building Delta Live Tables Pipelines-SQL`) to the notebook Paths
7 |
8 | # COMMAND ----------
9 |
10 | # MAGIC %md
11 | # MAGIC
12 | # MAGIC ## Making pipelines Configure-less-code with DLT
13 |
14 | # COMMAND ----------
15 |
16 | import dlt
17 |
18 | # COMMAND ----------
19 |
20 | from pyspark.sql.functions import *
21 | from pyspark.sql.types import *
22 |
23 | # COMMAND ----------
24 |
25 | # DBTITLE 1,Load Configs From Table or Files
26 | ## Loading Distinct Countries from DLT Table that is automatically managed and kept up to date
27 |
28 | ## Configs can be anything
29 | # 1. Mappings
30 | # 2. Optimizations
31 | # 3. Table/Env configs
32 | # 4. Table definitions
33 | # 5. SQL Expressions/Full logic
34 |
35 | dbName = spark.conf.get("dbName")
36 |
37 | ## Get all countries you want to make a separate table for -- then you can create DBSQL Dashboards, and share these tables
38 | countries_list = [i[0] for i in spark.table(f"{dbName}.distinct_countries_retail").select("Country").coalesce(1).collect()]
39 | print(countries_list)
40 |
41 | all_tbl_properties = {
42 | "quality":"silver",
43 | "delta.tuneFileSizesForRewrites":"true",
44 | "pipelines.autoOptimize.zOrderCols":"CustomerID, InvoiceNo"
45 | }
46 |
47 | expectations_configs = {"has_invoice_number":"CAST(InvoiceNo AS INTEGER) IS NOT NULL","has_customer_number":"CAST(CustomerID AS INTEGER) IS NOT NULL"}
48 |
49 | access_configs = {"accessible_via_pii_group": ['United Kingdom']}
50 |
51 | # COMMAND ----------
52 |
53 | # DBTITLE 1,Define Wrapper Function for Reproducible Operation(s)
54 | ### Use meta-programming model
55 |
56 | def generate_bronze_tables(call_table, filter):
57 | #@dlt.expect_all_or_drop(expectations_configs)
58 | @dlt.table(
59 | name=call_table,
60 | comment=f"Bronze Table {call_table} By for Country: {filter}",
61 | table_properties=all_tbl_properties,
62 | spark_conf={"pipelines.trigger.interval" : "1 day"}
63 | )
64 | def create_call_table():
65 |
66 | df = (dlt.read_stream("quality_retail_split_by_country")
67 | .filter(col("Country") == lit(filter))
68 | )
69 |
70 | return df
71 |
72 | # COMMAND ----------
73 |
74 | # DBTITLE 1,Declaratively Implement Function
75 | for country in countries_list:
76 | clean_name = country.replace(" ","_")
77 | table_name = "sales_for_" + clean_name + "_bronze"
78 | generate_bronze_tables(table_name, country)
79 |
80 | # COMMAND ----------
81 |
82 | # DBTITLE 1,Dynamic APPLY CHANGES function
83 | def generate_silver_tables(target_table, source_table, merge_keys, sequence_key):
84 |
85 | ### Auto-zorder by merge keys, and others by a config
86 | zorder_str = ",".join(merge_keys)
87 |
88 | ### Dynamically config target tables as little or as much as you want
89 | dlt.create_streaming_live_table(
90 | name = target_table,
91 | comment = "Silver Table",
92 | spark_conf={"pipelines.trigger.interval" : "1 hour"},
93 | table_properties= {"quality":"silver",
94 | "delta.autoOptimize.optimizeWrite":"true",
95 | "delta.tuneFileSizesForRewrites":"true",
96 | "pipelines.autoOptimize.zOrderCols":zorder_str}
97 | #partition_cols=["", ""],
98 | #path="",
99 | #schema="schema-definition"
100 | )
101 |
102 | ### Run Merge -- This includes CDC Data
103 | dlt.apply_changes(
104 | target = target_table,
105 | source = source_table,
106 | keys = merge_keys,
107 | sequence_by = sequence_key,
108 | ignore_null_updates = False,
109 | apply_as_deletes = None,
110 | column_list = None,
111 | except_column_list = None
112 | )
113 |
114 | return
115 |
116 | # COMMAND ----------
117 |
118 | # DBTITLE 1,This many tables to manage updates for is too much, lets do it all at once...
119 | for country in countries_list:
120 | clean_name = country.replace(" ","_")
121 | source_table_name = "sales_for_" + clean_name + "_bronze"
122 | target_table_name = "sales_for_" + clean_name + "_silver"
123 | merge_keys = ["InvoiceNo", "CustomerID"]
124 | sequence_key = "InvoiceDatetime"
125 | generate_silver_tables(target_table = target_table_name,
126 | source_table = source_table_name,
127 | merge_keys = merge_keys,
128 | sequence_key = sequence_key)
129 |
130 |
--------------------------------------------------------------------------------
/notebooks/02. Building Delta Live Tables Pipelines-SQL.sql:
--------------------------------------------------------------------------------
1 | -- Databricks notebook source
2 | -- MAGIC %md
3 | -- MAGIC When creating the pipeline add the following configuration to point to the data source:
4 | -- MAGIC
5 | -- MAGIC `data_source_path` : `/databricks-datasets/online_retail/data-001/`
6 |
7 | -- COMMAND ----------
8 |
9 | -- DBTITLE 1,Read in Raw Data via Autoloader in SQL
10 | CREATE STREAMING LIVE TABLE raw_retail
11 | COMMENT "This is the RAW bronze input data read in with Autoloader - no optimizations or expectations"
12 | PARTITIONED BY (Country)
13 | TBLPROPERTIES ("quality" = "bronze")
14 | AS (
15 | SELECT
16 | *,
17 | input_file_name() AS inputFileName
18 | FROM cloud_files( '${data_source_path}', 'csv',
19 | map("schema", "InvoiceNo STRING, StockCode STRING, Description STRING, Quantity FLOAT, InvoiceDate STRING, UnitPrice FLOAT, CustomerID STRING, Country STRING",
20 | "header", "true"))
21 | )
22 |
23 |
24 | -- COMMAND ----------
25 |
26 | -- DBTITLE 1,Optimize Data Layout for Performance
27 | -- SET pipelines.trigger.interval='1 hour';
28 |
29 | CREATE STREAMING LIVE TABLE cleaned_retail
30 | PARTITIONED BY (Country)
31 | COMMENT "This is the raw bronze table with data cleaned (dates, etc.), data partitioned, and optimized"
32 | TBLPROPERTIES --Can be spark, delta, or DLT confs
33 | ("quality"="bronze",
34 | "pipelines.autoOptimize.managed"="true",
35 | "pipelines.autoOptimize.zOrderCols"="CustomerID, InvoiceNo"
36 | )
37 | AS
38 | SELECT *
39 | FROM STREAM(LIVE.raw_retail)
40 |
41 | -- COMMAND ----------
42 |
43 | -- DBTITLE 1,Perform ETL & Enforce Quality Expectations
44 | -- SET pipelines.trigger.interval='1 hour';
45 |
46 | CREATE STREAMING LIVE TABLE quality_retail
47 | (
48 | CONSTRAINT has_customer EXPECT (CustomerID IS NOT NULL) ON VIOLATION DROP ROW,
49 | CONSTRAINT has_invoice EXPECT (InvoiceNo IS NOT NULL) ON VIOLATION DROP ROW,
50 | CONSTRAINT valid_date_time EXPECT (CAST(InvoiceDatetime AS TIMESTAMP) IS NOT NULL) ON VIOLATION DROP ROW
51 | )
52 | PARTITIONED BY (Country)
53 | COMMENT "This is the raw bronze table with data cleaned (dates, etc.), data partitioned, and optimized"
54 | TBLPROPERTIES
55 | ("quality"="silver",
56 | "pipelines.autoOptimize.zOrderCols"="CustomerID, InvoiceNo"
57 | )
58 | AS (
59 | WITH step1 AS
60 | (SELECT
61 | *,
62 | split(InvoiceDate, " ") AS Timestamp_Parts
63 | FROM STREAM(LIVE.cleaned_retail)
64 | ),
65 | step2 AS (
66 | SELECT
67 | *,
68 | split(Timestamp_Parts[0], "/") AS DateParts,
69 | Timestamp_Parts[1] AS RawTime
70 | FROM step1
71 | ),
72 | step3 AS (
73 | SELECT
74 | *,
75 | concat(lpad(DateParts[2], 4, "20"), "-", lpad(DateParts[0], 2, "0"),"-", lpad(DateParts[1], 2, "0")) AS CleanDate,
76 | lpad(RawTime, 5, '0') AS CleanTime
77 | FROM step2
78 | )
79 | SELECT
80 | InvoiceNo,
81 | StockCode,
82 | Description,
83 | Quantity,
84 | CleanDate AS InvoiceDate,
85 | CleanTime AS InvoiceTime,
86 | concat(CleanDate, " ", CleanTime)::timestamp AS InvoiceDatetime,
87 | UnitPrice,
88 | CustomerID,
89 | Country
90 | FROM step3
91 | )
92 |
93 | -- COMMAND ----------
94 |
95 | -- DBTITLE 1,Quarantine Data with Expectations
96 | -- SET pipelines.trigger.interval='1 hour';
97 |
98 | CREATE STREAMING LIVE TABLE quarantined_retail
99 | (
100 | CONSTRAINT has_customer EXPECT (CustomerID IS NULL) ON VIOLATION DROP ROW,
101 | CONSTRAINT has_invoice EXPECT (InvoiceNo IS NULL) ON VIOLATION DROP ROW,
102 | CONSTRAINT valid_date_time EXPECT (InvoiceDate IS NULL) ON VIOLATION DROP ROW
103 | )
104 | TBLPROPERTIES
105 | ("quality"="bronze",
106 | "pipelines.autoOptimize.zOrderCols"="CustomerID, InvoiceNo"
107 | )
108 | AS
109 | SELECT
110 | InvoiceNo,
111 | StockCode,
112 | Description,
113 | Quantity,
114 | InvoiceDate,
115 | UnitPrice,
116 | CustomerID,
117 | Country
118 | FROM STREAM(LIVE.cleaned_retail);
119 |
120 | -- COMMAND ----------
121 |
122 | -- DBTITLE 1,Create Complete Tables -- Use Case #1 -- for metadata downstream
123 | CREATE OR REFRESH LIVE TABLE distinct_countries_retail
124 | AS
125 | SELECT DISTINCT Country
126 | FROM LIVE.quality_retail;
127 |
128 | -- COMMAND ----------
129 |
130 | -- DBTITLE 1,Create Complete Tables -- Summary Analytics
131 | CREATE OR REFRESH LIVE TABLE sales_by_day
132 | AS
133 | SELECT
134 | date_trunc('day', InvoiceDatetime) AS Date,
135 | SUM(Quantity) AS TotalSales
136 | FROM (LIVE.retail_sales_all_countries)
137 | GROUP BY date_trunc('day', InvoiceDatetime)
138 | ORDER BY Date;
139 |
140 | -- COMMAND ----------
141 |
142 | CREATE OR REFRESH LIVE TABLE sales_by_country
143 | AS
144 | SELECT
145 | Country,
146 | SUM(Quantity) AS TotalSales
147 | FROM (LIVE.retail_sales_all_countries)
148 | GROUP BY Country
149 | ORDER BY TotalSales DESC;
150 |
151 | -- COMMAND ----------
152 |
153 | -- SET pipelines.trigger.interval='1 hour';
154 | CREATE OR REFRESH LIVE TABLE top_ten_customers
155 | AS
156 | SELECT
157 | CustomerID,
158 | SUM(Quantity) AS TotalSales
159 | FROM LIVE.retail_sales_all_countries
160 | GROUP BY CustomerID
161 | ORDER BY TotalSales DESC
162 | LIMIT 10;
163 |
164 | -- COMMAND ----------
165 |
166 | -- DBTITLE 1,Upsert New Data APPLY CHANGES INTO
167 | -- SET pipelines.trigger.interval='1 hour';
168 |
169 | CREATE STREAMING LIVE TABLE retail_sales_all_countries
170 | TBLPROPERTIES
171 | ("quality"="silver",
172 | "delta.tuneFileSizesForRewrites"="true",
173 | "pipelines.autoOptimize.zOrderCols"="CustomerID, InvoiceNo"
174 | );
175 |
176 | APPLY CHANGES INTO LIVE.retail_sales_all_countries
177 | FROM STREAM(LIVE.quality_retail)
178 | KEYS (CustomerID, InvoiceNo)
179 | SEQUENCE BY InvoiceDateTime
180 |
181 | -- COMMAND ----------
182 |
183 | -- DBTITLE 1,Just for Visuals -- Separate pipeline to split by country
184 | -- SET pipelines.trigger.interval='1 hour';
185 |
186 | CREATE STREAMING LIVE TABLE quality_retail_split_by_country
187 | (
188 | CONSTRAINT has_customer EXPECT (CustomerID IS NOT NULL) ON VIOLATION DROP ROW,
189 | CONSTRAINT has_invoice EXPECT (InvoiceNo IS NOT NULL) ON VIOLATION DROP ROW,
190 | CONSTRAINT valid_date_time EXPECT (CAST(InvoiceDatetime AS TIMESTAMP) IS NOT NULL) ON VIOLATION DROP ROW
191 | )
192 | PARTITIONED BY (Country)
193 | COMMENT "This is the raw bronze table with data cleaned (dates, etc.), data partitioned, and optimized"
194 | TBLPROPERTIES
195 | ("quality"="silver",
196 | "pipelines.autoOptimize.zOrderCols"="CustomerID, InvoiceNo"
197 | )
198 | AS
199 | SELECT * FROM STREAM(LIVE.quality_retail)
200 |
--------------------------------------------------------------------------------
/notebooks/06. DLT Log Analysis.py:
--------------------------------------------------------------------------------
1 | # Databricks notebook source
2 | # MAGIC %md
3 | # MAGIC # DLT pipeline log analysis
4 | # MAGIC
5 | # MAGIC Please make sure you specify your own Database and Storage location. You'll find this information in the configuration menu of your [Delta Live Table Pipeline](https://e2-demo-field-eng.cloud.databricks.com/?o=1444828305810485#joblist/pipelines/5b2ef462-558e-4f8d-8ad8-c80bce9da954).
6 | # MAGIC
7 | # MAGIC **NOTE:** Please use Databricks Runtime 9.1 or above when running this notebook
8 |
9 | # COMMAND ----------
10 |
11 | # Full username, e.g. ".@databricks.com"
12 | username = dbutils.notebook.entry_point.getDbutils().notebook().getContext().tags().apply('user')
13 |
14 | # Short form of username, suitable for use as part of a topic name.
15 | user = username.split("@")[0].replace(".","_")
16 |
17 | # Database name
18 | dbName = user+"_workshop_db"
19 |
20 | storage_location = f"/tmp/delta-stream-dltworkshop/{user}/dlt_storage"
21 |
22 | # COMMAND ----------
23 |
24 | dbutils.widgets.removeAll()
25 | dbutils.widgets.text('storage_location', storage_location)
26 | dbutils.widgets.text('latest_update_id', 'Update_ID_fromUpdateDetails')
27 |
28 | # COMMAND ----------
29 |
30 | # MAGIC %md
31 | # MAGIC Set correct `Update ID` and storage location
32 |
33 | # COMMAND ----------
34 |
35 | events_table_location = f"{dbutils.widgets.get('storage_location')}/system/events" #dbfs:/storage_location/system/events/
36 | latest_updateID = dbutils.widgets.get('latest_update_id')
37 |
38 | # COMMAND ----------
39 |
40 | # DBTITLE 1,Find the Metrics Table in DBFS
41 | display(dbutils.fs.ls(events_table_location))
42 |
43 | # COMMAND ----------
44 |
45 | # DBTITLE 1,Write the Metrics Table to our DLT Database
46 | df = spark.read.load(events_table_location)
47 | df.write.mode("overwrite").saveAsTable(f"{dbName}.metrics_table")
48 | display(df)
49 |
50 | # COMMAND ----------
51 |
52 | spark.sql(f"USE {dbName}")
53 |
54 | # COMMAND ----------
55 |
56 | # MAGIC %md
57 | # MAGIC
58 | # MAGIC ### Event Logs Analysis
59 | # MAGIC The `details` column contains metadata about each Event sent to the Event Log. There are different fields depending on what type of Event it is. Some examples include:
60 | # MAGIC
61 | # MAGIC | Type of event | behavior |
62 | # MAGIC | --- | --- |
63 | # MAGIC | `user_action` | Events occur when taking actions like creating the pipeline |
64 | # MAGIC | `flow_definition`| Events occur when a pipeline is deployed or updated and have lineage, schema, and execution plan information |
65 | # MAGIC | `output_dataset` and `input_datasets` | output table/view and its upstream table(s)/view(s) |
66 | # MAGIC | `flow_type` | whether this is a complete or append flow |
67 | # MAGIC | `explain_text` | the Spark explain plan |
68 | # MAGIC | `flow_progress`| Events occur when a data flow starts running or finishes processing a batch of data |
69 | # MAGIC | `metrics` | currently contains `num_output_rows` |
70 | # MAGIC | `data_quality` (`dropped_records`), (`expectations`: `name`, `dataset`, `passed_records`, `failed_records`)| contains an array of the results of the data quality rules for this particular dataset * `expectations`|
71 |
72 | # COMMAND ----------
73 |
74 | # DBTITLE 1,Monitor Data Quality Over All Runs
75 | # MAGIC %sql
76 | # MAGIC CREATE OR REPLACE TABLE dlt_dataquality
77 | # MAGIC SELECT
78 | # MAGIC id,
79 | # MAGIC timestamp,
80 | # MAGIC status_update,
81 | # MAGIC expectations.dataset,
82 | # MAGIC expectations.name,
83 | # MAGIC expectations.failed_records,
84 | # MAGIC expectations.passed_records
85 | # MAGIC FROM(
86 | # MAGIC SELECT
87 | # MAGIC id,
88 | # MAGIC timestamp,
89 | # MAGIC details:flow_progress.metrics.num_output_rows as output_records,
90 | # MAGIC details:flow_progress.data_quality.dropped_records,
91 | # MAGIC details:flow_progress.status as status_update,
92 | # MAGIC explode(from_json(details:flow_progress:data_quality:expectations
93 | # MAGIC , schema_of_json("[{'name':'str', 'dataset':'str', 'passed_records': 42, 'failed_records': 42}]"))) expectations
94 | # MAGIC FROM metrics_table
95 | # MAGIC WHERE details:flow_progress.metrics IS NOT NULL) data_quality;
96 | # MAGIC
97 | # MAGIC SELECT * FROM dlt_dataquality
98 |
99 | # COMMAND ----------
100 |
101 | # DBTITLE 1,Create Data Lineage Table
102 | # MAGIC %sql
103 | # MAGIC CREATE OR REPLACE TABLE dlt_lineage
104 | # MAGIC SELECT
105 | # MAGIC timestamp,
106 | # MAGIC details:flow_definition.output_dataset,
107 | # MAGIC details:flow_definition.input_datasets,
108 | # MAGIC details:flow_definition.flow_type,
109 | # MAGIC details:flow_definition.schema,
110 | # MAGIC details:flow_definition
111 | # MAGIC FROM metrics_table
112 | # MAGIC WHERE details:flow_definition IS NOT NULL
113 | # MAGIC ORDER BY timestamp;
114 | # MAGIC
115 | # MAGIC SELECT * FROM dlt_lineage
116 |
117 | # COMMAND ----------
118 |
119 | # MAGIC %md Let's head to our [Databricks SQL Dashboard](https://e2-demo-field-eng.cloud.databricks.com/sql/dashboards/88b89069-58f8-471f-9d60-a7943b93fa23-dlt-workshop--dlt-metrics?o=1444828305810485) where we can visualize our new tables.
120 |
121 | # COMMAND ----------
122 |
123 | # MAGIC %md These are the SQL Queries used to generate the visualizations on our dashboard:
124 |
125 | # COMMAND ----------
126 |
127 | # MAGIC %sql
128 | # MAGIC /* Failed Record Rate */
129 | # MAGIC SELECT sum(failed_records) / sum(failed_records + passed_records) * 100
130 | # MAGIC failure_rate,
131 | # MAGIC sum(failed_records + passed_records)
132 | # MAGIC output_records
133 | # MAGIC FROM dlt_workshop_retail.dlt_dataquality
134 |
135 | # COMMAND ----------
136 |
137 | # MAGIC %sql
138 | # MAGIC /* Number of Failed Records */
139 | # MAGIC SELECT avg(failed_records)
140 | # MAGIC FROM dlt_workshop_retail.dlt_dataquality
141 | # MAGIC WHERE failed_records > 0
142 |
143 | # COMMAND ----------
144 |
145 | # MAGIC %sql
146 | # MAGIC /* Failed and Passed Records Monthly */
147 | # MAGIC SELECT Sum(passed_records) AS passed_records,
148 | # MAGIC Sum(failed_records) AS failed_records,
149 | # MAGIC Sum(passed_records + failed_records) AS output_records,
150 | # MAGIC Sum(failed_records) / Sum(passed_records + failed_records) * 100 AS failure_rate,
151 | # MAGIC NAME,
152 | # MAGIC dataset,
153 | # MAGIC Date(timestamp) AS date
154 | # MAGIC FROM dlt_workshop_retail.dlt_dataquality
155 | # MAGIC GROUP BY date,
156 | # MAGIC dataset,
157 | # MAGIC NAME
158 |
159 | # COMMAND ----------
160 |
161 | # MAGIC %sql
162 | # MAGIC /* Records by Dataset */
163 | # MAGIC SELECT 'passed_records' AS type,
164 | # MAGIC Sum(passed_records) AS value,
165 | # MAGIC Sum(failed_records) / Sum(passed_records + failed_records) * 100 AS failure_rate,
166 | # MAGIC dataset
167 | # MAGIC FROM dlt_workshop_retail.dlt_dataquality
168 | # MAGIC GROUP BY dataset
169 | # MAGIC UNION
170 | # MAGIC SELECT 'failed_records' AS type,
171 | # MAGIC Sum(failed_records) AS value,
172 | # MAGIC Sum(failed_records) / Sum(passed_records + failed_records) * 100 AS failure_rate,
173 | # MAGIC dataset
174 | # MAGIC FROM dlt_workshop_retail.dlt_dataquality
175 | # MAGIC GROUP BY dataset
176 |
177 | # COMMAND ----------
178 |
179 | # MAGIC %sql
180 | # MAGIC /* Lineage Table */
181 | # MAGIC SELECT output_dataset AS dataset,
182 | # MAGIC input_datasets AS input
183 | # MAGIC FROM dlt_workshop_retail.dlt_lineage
184 | # MAGIC WHERE Date(timestamp) = "2022-12-09"
185 | # MAGIC AND flow_type = "incremental"
186 |
187 | # COMMAND ----------
188 |
189 |
190 |
--------------------------------------------------------------------------------
/notebooks/01-Structured Streaming with Databricks Delta Tables.py:
--------------------------------------------------------------------------------
1 | # Databricks notebook source
2 | # MAGIC %md
3 | # MAGIC
4 | # MAGIC # Structured Streaming with Databricks Delta Tables
5 | # MAGIC
6 | # MAGIC One of the hallmark innovations of Databricks and the Lakehouse vision is the establishing of a unified method for writing and reading data in a data lake. This unification of batch and streaming jobs has been called the post-lambda architecture for data warehousing. The flexibility, simplicity, and scalability of the new delta lake architecture has been pivotal towards addressing big data needs and has been gifted to the Linux Foundation. Fundamental to the lakehouse view of ETL/ELT is the usage of a multi-hop data architecture known as the medallion architecture.
7 | # MAGIC Delta Lake, the pillar of lakehouse platform, is an open-source storage layer that brings ACID transactions and increased performance to Apache Spark™ and big data workloads.
8 | # MAGIC
9 | # MAGIC
6 |
7 |
8 |
9 | 
10 |
11 |
12 |
13 | # Reading Resources
14 |
15 | See below links for more documentation:
16 | * [How to Process IoT Device JSON Data Using Apache Spark Datasets and DataFrames](https://databricks.com/blog/2016/03/28/how-to-process-iot-device-json-data-using-apache-spark-datasets-and-dataframes.html)
17 | * [Spark Structure Streaming](https://databricks.com/blog/2016/07/28/structured-streaming-in-apache-spark.html)
18 | * [Beyond Lambda](https://databricks.com/discover/getting-started-with-delta-lake-tech-talks/beyond-lambda-introducing-delta-architecture)
19 | * [Delta Lake Docs](https://docs.databricks.com/delta/index.html)
20 | * [Medallion Architecture](https://databricks.com/solutions/data-pipelines)
21 | * [Cost Savings with the Medallion Architecture](https://techcommunity.microsoft.com/t5/analytics-on-azure/how-to-reduce-infrastructure-costs-by-up-to-80-with-azure/ba-p/1820280)
22 | * [Change Data Capture Streams with the Medallion Architecture](https://databricks.com/blog/2021/06/09/how-to-simplify-cdc-with-delta-lakes-change-data-feed.html)
23 |
24 |
25 |
26 | # Workshop Flow
27 |
28 | The workshop consists of 4 interactive sections that are separated by 4 notebooks located in the notebooks folder in this repository. Each is run sequentially as we explore the abilities of the lakehouse from data ingestion, data curation, and performance optimizations
29 | |Notebook|Summary|
30 | |--------|-------|
31 | |`01-Structured Streaming with Databricks Delta Tables`|Processing and ingesting data at scale utilizing databricks tunables and the medallion architecture|
32 | |`02-Orchestrating with Delta Live Tables`|Changing Spark Properties, Configuring Table Properties, Optimization of Tables, Combining Batch and Incremental Tables|
33 | |`03. Implement CDC In DLT Pipeline: Change Data Capture (Python)`|Implementing Change Data Capture in DLT pipelines for accessing to fresh data|
34 | |`04: Meta-programming`|Examples of metaprogramming in DLT When to use/problems is solved How to configure|
35 | |`05: ML Models in DLT Pipelines`|Example of integratation of ML models with DLT pipelines|
36 |
37 |
38 |
39 | # Setup / Requirements
40 |
41 | This workshop requires a running Databricks workspace. If you are an existing Databricks customer, you can use your existing Databricks workspace. Otherwise, the notebooks in this workshop have been tested to run on [Databricks Community Edition](https://databricks.com/product/faq/community-edition) as well.
42 |
43 | ## DBR Version
44 |
45 | The features used in this workshop require `DBR 9.1 LTS`+.
46 |
47 | ## Repos
48 |
49 | If you have repos enabled on your Databricks workspace. You can directly import this repo and run the notebooks as is and avoid the DBC archive step.
50 |
51 | ## DBC Archive
52 |
53 | Download the DBC archive from releases and import the archive into your Databricks workspace.
54 |
--------------------------------------------------------------------------------
/notebooks/04. Advanced DLT Concepts.py:
--------------------------------------------------------------------------------
1 | # Databricks notebook source
2 | # MAGIC %md
3 | # MAGIC When creating the pipeline:
4 | # MAGIC * add the following configuration to point to the data source `data_source_path` : `/databricks-datasets/online_retail/data-001/`
5 | # MAGIC * add the following configuration to read the country list from the correct schema/db : `dbName`: `username_workshop_db`
6 | # MAGIC * add notebook number 2 (`02. Building Delta Live Tables Pipelines-SQL`) to the notebook Paths
7 |
8 | # COMMAND ----------
9 |
10 | # MAGIC %md
11 | # MAGIC
12 | # MAGIC ## Making pipelines Configure-less-code with DLT
13 |
14 | # COMMAND ----------
15 |
16 | import dlt
17 |
18 | # COMMAND ----------
19 |
20 | from pyspark.sql.functions import *
21 | from pyspark.sql.types import *
22 |
23 | # COMMAND ----------
24 |
25 | # DBTITLE 1,Load Configs From Table or Files
26 | ## Loading Distinct Countries from DLT Table that is automatically managed and kept up to date
27 |
28 | ## Configs can be anything
29 | # 1. Mappings
30 | # 2. Optimizations
31 | # 3. Table/Env configs
32 | # 4. Table definitions
33 | # 5. SQL Expressions/Full logic
34 |
35 | dbName = spark.conf.get("dbName")
36 |
37 | ## Get all countries you want to make a separate table for -- then you can create DBSQL Dashboards, and share these tables
38 | countries_list = [i[0] for i in spark.table(f"{dbName}.distinct_countries_retail").select("Country").coalesce(1).collect()]
39 | print(countries_list)
40 |
41 | all_tbl_properties = {
42 | "quality":"silver",
43 | "delta.tuneFileSizesForRewrites":"true",
44 | "pipelines.autoOptimize.zOrderCols":"CustomerID, InvoiceNo"
45 | }
46 |
47 | expectations_configs = {"has_invoice_number":"CAST(InvoiceNo AS INTEGER) IS NOT NULL","has_customer_number":"CAST(CustomerID AS INTEGER) IS NOT NULL"}
48 |
49 | access_configs = {"accessible_via_pii_group": ['United Kingdom']}
50 |
51 | # COMMAND ----------
52 |
53 | # DBTITLE 1,Define Wrapper Function for Reproducible Operation(s)
54 | ### Use meta-programming model
55 |
56 | def generate_bronze_tables(call_table, filter):
57 | #@dlt.expect_all_or_drop(expectations_configs)
58 | @dlt.table(
59 | name=call_table,
60 | comment=f"Bronze Table {call_table} By for Country: {filter}",
61 | table_properties=all_tbl_properties,
62 | spark_conf={"pipelines.trigger.interval" : "1 day"}
63 | )
64 | def create_call_table():
65 |
66 | df = (dlt.read_stream("quality_retail_split_by_country")
67 | .filter(col("Country") == lit(filter))
68 | )
69 |
70 | return df
71 |
72 | # COMMAND ----------
73 |
74 | # DBTITLE 1,Declaratively Implement Function
75 | for country in countries_list:
76 | clean_name = country.replace(" ","_")
77 | table_name = "sales_for_" + clean_name + "_bronze"
78 | generate_bronze_tables(table_name, country)
79 |
80 | # COMMAND ----------
81 |
82 | # DBTITLE 1,Dynamic APPLY CHANGES function
83 | def generate_silver_tables(target_table, source_table, merge_keys, sequence_key):
84 |
85 | ### Auto-zorder by merge keys, and others by a config
86 | zorder_str = ",".join(merge_keys)
87 |
88 | ### Dynamically config target tables as little or as much as you want
89 | dlt.create_streaming_live_table(
90 | name = target_table,
91 | comment = "Silver Table",
92 | spark_conf={"pipelines.trigger.interval" : "1 hour"},
93 | table_properties= {"quality":"silver",
94 | "delta.autoOptimize.optimizeWrite":"true",
95 | "delta.tuneFileSizesForRewrites":"true",
96 | "pipelines.autoOptimize.zOrderCols":zorder_str}
97 | #partition_cols=["", ""],
98 | #path="",
99 | #schema="schema-definition"
100 | )
101 |
102 | ### Run Merge -- This includes CDC Data
103 | dlt.apply_changes(
104 | target = target_table,
105 | source = source_table,
106 | keys = merge_keys,
107 | sequence_by = sequence_key,
108 | ignore_null_updates = False,
109 | apply_as_deletes = None,
110 | column_list = None,
111 | except_column_list = None
112 | )
113 |
114 | return
115 |
116 | # COMMAND ----------
117 |
118 | # DBTITLE 1,This many tables to manage updates for is too much, lets do it all at once...
119 | for country in countries_list:
120 | clean_name = country.replace(" ","_")
121 | source_table_name = "sales_for_" + clean_name + "_bronze"
122 | target_table_name = "sales_for_" + clean_name + "_silver"
123 | merge_keys = ["InvoiceNo", "CustomerID"]
124 | sequence_key = "InvoiceDatetime"
125 | generate_silver_tables(target_table = target_table_name,
126 | source_table = source_table_name,
127 | merge_keys = merge_keys,
128 | sequence_key = sequence_key)
129 |
130 |
--------------------------------------------------------------------------------
/notebooks/02. Building Delta Live Tables Pipelines-SQL.sql:
--------------------------------------------------------------------------------
1 | -- Databricks notebook source
2 | -- MAGIC %md
3 | -- MAGIC When creating the pipeline add the following configuration to point to the data source:
4 | -- MAGIC
5 | -- MAGIC `data_source_path` : `/databricks-datasets/online_retail/data-001/`
6 |
7 | -- COMMAND ----------
8 |
9 | -- DBTITLE 1,Read in Raw Data via Autoloader in SQL
10 | CREATE STREAMING LIVE TABLE raw_retail
11 | COMMENT "This is the RAW bronze input data read in with Autoloader - no optimizations or expectations"
12 | PARTITIONED BY (Country)
13 | TBLPROPERTIES ("quality" = "bronze")
14 | AS (
15 | SELECT
16 | *,
17 | input_file_name() AS inputFileName
18 | FROM cloud_files( '${data_source_path}', 'csv',
19 | map("schema", "InvoiceNo STRING, StockCode STRING, Description STRING, Quantity FLOAT, InvoiceDate STRING, UnitPrice FLOAT, CustomerID STRING, Country STRING",
20 | "header", "true"))
21 | )
22 |
23 |
24 | -- COMMAND ----------
25 |
26 | -- DBTITLE 1,Optimize Data Layout for Performance
27 | -- SET pipelines.trigger.interval='1 hour';
28 |
29 | CREATE STREAMING LIVE TABLE cleaned_retail
30 | PARTITIONED BY (Country)
31 | COMMENT "This is the raw bronze table with data cleaned (dates, etc.), data partitioned, and optimized"
32 | TBLPROPERTIES --Can be spark, delta, or DLT confs
33 | ("quality"="bronze",
34 | "pipelines.autoOptimize.managed"="true",
35 | "pipelines.autoOptimize.zOrderCols"="CustomerID, InvoiceNo"
36 | )
37 | AS
38 | SELECT *
39 | FROM STREAM(LIVE.raw_retail)
40 |
41 | -- COMMAND ----------
42 |
43 | -- DBTITLE 1,Perform ETL & Enforce Quality Expectations
44 | -- SET pipelines.trigger.interval='1 hour';
45 |
46 | CREATE STREAMING LIVE TABLE quality_retail
47 | (
48 | CONSTRAINT has_customer EXPECT (CustomerID IS NOT NULL) ON VIOLATION DROP ROW,
49 | CONSTRAINT has_invoice EXPECT (InvoiceNo IS NOT NULL) ON VIOLATION DROP ROW,
50 | CONSTRAINT valid_date_time EXPECT (CAST(InvoiceDatetime AS TIMESTAMP) IS NOT NULL) ON VIOLATION DROP ROW
51 | )
52 | PARTITIONED BY (Country)
53 | COMMENT "This is the raw bronze table with data cleaned (dates, etc.), data partitioned, and optimized"
54 | TBLPROPERTIES
55 | ("quality"="silver",
56 | "pipelines.autoOptimize.zOrderCols"="CustomerID, InvoiceNo"
57 | )
58 | AS (
59 | WITH step1 AS
60 | (SELECT
61 | *,
62 | split(InvoiceDate, " ") AS Timestamp_Parts
63 | FROM STREAM(LIVE.cleaned_retail)
64 | ),
65 | step2 AS (
66 | SELECT
67 | *,
68 | split(Timestamp_Parts[0], "/") AS DateParts,
69 | Timestamp_Parts[1] AS RawTime
70 | FROM step1
71 | ),
72 | step3 AS (
73 | SELECT
74 | *,
75 | concat(lpad(DateParts[2], 4, "20"), "-", lpad(DateParts[0], 2, "0"),"-", lpad(DateParts[1], 2, "0")) AS CleanDate,
76 | lpad(RawTime, 5, '0') AS CleanTime
77 | FROM step2
78 | )
79 | SELECT
80 | InvoiceNo,
81 | StockCode,
82 | Description,
83 | Quantity,
84 | CleanDate AS InvoiceDate,
85 | CleanTime AS InvoiceTime,
86 | concat(CleanDate, " ", CleanTime)::timestamp AS InvoiceDatetime,
87 | UnitPrice,
88 | CustomerID,
89 | Country
90 | FROM step3
91 | )
92 |
93 | -- COMMAND ----------
94 |
95 | -- DBTITLE 1,Quarantine Data with Expectations
96 | -- SET pipelines.trigger.interval='1 hour';
97 |
98 | CREATE STREAMING LIVE TABLE quarantined_retail
99 | (
100 | CONSTRAINT has_customer EXPECT (CustomerID IS NULL) ON VIOLATION DROP ROW,
101 | CONSTRAINT has_invoice EXPECT (InvoiceNo IS NULL) ON VIOLATION DROP ROW,
102 | CONSTRAINT valid_date_time EXPECT (InvoiceDate IS NULL) ON VIOLATION DROP ROW
103 | )
104 | TBLPROPERTIES
105 | ("quality"="bronze",
106 | "pipelines.autoOptimize.zOrderCols"="CustomerID, InvoiceNo"
107 | )
108 | AS
109 | SELECT
110 | InvoiceNo,
111 | StockCode,
112 | Description,
113 | Quantity,
114 | InvoiceDate,
115 | UnitPrice,
116 | CustomerID,
117 | Country
118 | FROM STREAM(LIVE.cleaned_retail);
119 |
120 | -- COMMAND ----------
121 |
122 | -- DBTITLE 1,Create Complete Tables -- Use Case #1 -- for metadata downstream
123 | CREATE OR REFRESH LIVE TABLE distinct_countries_retail
124 | AS
125 | SELECT DISTINCT Country
126 | FROM LIVE.quality_retail;
127 |
128 | -- COMMAND ----------
129 |
130 | -- DBTITLE 1,Create Complete Tables -- Summary Analytics
131 | CREATE OR REFRESH LIVE TABLE sales_by_day
132 | AS
133 | SELECT
134 | date_trunc('day', InvoiceDatetime) AS Date,
135 | SUM(Quantity) AS TotalSales
136 | FROM (LIVE.retail_sales_all_countries)
137 | GROUP BY date_trunc('day', InvoiceDatetime)
138 | ORDER BY Date;
139 |
140 | -- COMMAND ----------
141 |
142 | CREATE OR REFRESH LIVE TABLE sales_by_country
143 | AS
144 | SELECT
145 | Country,
146 | SUM(Quantity) AS TotalSales
147 | FROM (LIVE.retail_sales_all_countries)
148 | GROUP BY Country
149 | ORDER BY TotalSales DESC;
150 |
151 | -- COMMAND ----------
152 |
153 | -- SET pipelines.trigger.interval='1 hour';
154 | CREATE OR REFRESH LIVE TABLE top_ten_customers
155 | AS
156 | SELECT
157 | CustomerID,
158 | SUM(Quantity) AS TotalSales
159 | FROM LIVE.retail_sales_all_countries
160 | GROUP BY CustomerID
161 | ORDER BY TotalSales DESC
162 | LIMIT 10;
163 |
164 | -- COMMAND ----------
165 |
166 | -- DBTITLE 1,Upsert New Data APPLY CHANGES INTO
167 | -- SET pipelines.trigger.interval='1 hour';
168 |
169 | CREATE STREAMING LIVE TABLE retail_sales_all_countries
170 | TBLPROPERTIES
171 | ("quality"="silver",
172 | "delta.tuneFileSizesForRewrites"="true",
173 | "pipelines.autoOptimize.zOrderCols"="CustomerID, InvoiceNo"
174 | );
175 |
176 | APPLY CHANGES INTO LIVE.retail_sales_all_countries
177 | FROM STREAM(LIVE.quality_retail)
178 | KEYS (CustomerID, InvoiceNo)
179 | SEQUENCE BY InvoiceDateTime
180 |
181 | -- COMMAND ----------
182 |
183 | -- DBTITLE 1,Just for Visuals -- Separate pipeline to split by country
184 | -- SET pipelines.trigger.interval='1 hour';
185 |
186 | CREATE STREAMING LIVE TABLE quality_retail_split_by_country
187 | (
188 | CONSTRAINT has_customer EXPECT (CustomerID IS NOT NULL) ON VIOLATION DROP ROW,
189 | CONSTRAINT has_invoice EXPECT (InvoiceNo IS NOT NULL) ON VIOLATION DROP ROW,
190 | CONSTRAINT valid_date_time EXPECT (CAST(InvoiceDatetime AS TIMESTAMP) IS NOT NULL) ON VIOLATION DROP ROW
191 | )
192 | PARTITIONED BY (Country)
193 | COMMENT "This is the raw bronze table with data cleaned (dates, etc.), data partitioned, and optimized"
194 | TBLPROPERTIES
195 | ("quality"="silver",
196 | "pipelines.autoOptimize.zOrderCols"="CustomerID, InvoiceNo"
197 | )
198 | AS
199 | SELECT * FROM STREAM(LIVE.quality_retail)
200 |
--------------------------------------------------------------------------------
/notebooks/06. DLT Log Analysis.py:
--------------------------------------------------------------------------------
1 | # Databricks notebook source
2 | # MAGIC %md
3 | # MAGIC # DLT pipeline log analysis
4 | # MAGIC
5 | # MAGIC Please make sure you specify your own Database and Storage location. You'll find this information in the configuration menu of your [Delta Live Table Pipeline](https://e2-demo-field-eng.cloud.databricks.com/?o=1444828305810485#joblist/pipelines/5b2ef462-558e-4f8d-8ad8-c80bce9da954).
6 | # MAGIC
7 | # MAGIC **NOTE:** Please use Databricks Runtime 9.1 or above when running this notebook
8 |
9 | # COMMAND ----------
10 |
11 | # Full username, e.g. ".@databricks.com"
12 | username = dbutils.notebook.entry_point.getDbutils().notebook().getContext().tags().apply('user')
13 |
14 | # Short form of username, suitable for use as part of a topic name.
15 | user = username.split("@")[0].replace(".","_")
16 |
17 | # Database name
18 | dbName = user+"_workshop_db"
19 |
20 | storage_location = f"/tmp/delta-stream-dltworkshop/{user}/dlt_storage"
21 |
22 | # COMMAND ----------
23 |
24 | dbutils.widgets.removeAll()
25 | dbutils.widgets.text('storage_location', storage_location)
26 | dbutils.widgets.text('latest_update_id', 'Update_ID_fromUpdateDetails')
27 |
28 | # COMMAND ----------
29 |
30 | # MAGIC %md
31 | # MAGIC Set correct `Update ID` and storage location
32 |
33 | # COMMAND ----------
34 |
35 | events_table_location = f"{dbutils.widgets.get('storage_location')}/system/events" #dbfs:/storage_location/system/events/
36 | latest_updateID = dbutils.widgets.get('latest_update_id')
37 |
38 | # COMMAND ----------
39 |
40 | # DBTITLE 1,Find the Metrics Table in DBFS
41 | display(dbutils.fs.ls(events_table_location))
42 |
43 | # COMMAND ----------
44 |
45 | # DBTITLE 1,Write the Metrics Table to our DLT Database
46 | df = spark.read.load(events_table_location)
47 | df.write.mode("overwrite").saveAsTable(f"{dbName}.metrics_table")
48 | display(df)
49 |
50 | # COMMAND ----------
51 |
52 | spark.sql(f"USE {dbName}")
53 |
54 | # COMMAND ----------
55 |
56 | # MAGIC %md
57 | # MAGIC
58 | # MAGIC ### Event Logs Analysis
59 | # MAGIC The `details` column contains metadata about each Event sent to the Event Log. There are different fields depending on what type of Event it is. Some examples include:
60 | # MAGIC
61 | # MAGIC | Type of event | behavior |
62 | # MAGIC | --- | --- |
63 | # MAGIC | `user_action` | Events occur when taking actions like creating the pipeline |
64 | # MAGIC | `flow_definition`| Events occur when a pipeline is deployed or updated and have lineage, schema, and execution plan information |
65 | # MAGIC | `output_dataset` and `input_datasets` | output table/view and its upstream table(s)/view(s) |
66 | # MAGIC | `flow_type` | whether this is a complete or append flow |
67 | # MAGIC | `explain_text` | the Spark explain plan |
68 | # MAGIC | `flow_progress`| Events occur when a data flow starts running or finishes processing a batch of data |
69 | # MAGIC | `metrics` | currently contains `num_output_rows` |
70 | # MAGIC | `data_quality` (`dropped_records`), (`expectations`: `name`, `dataset`, `passed_records`, `failed_records`)| contains an array of the results of the data quality rules for this particular dataset * `expectations`|
71 |
72 | # COMMAND ----------
73 |
74 | # DBTITLE 1,Monitor Data Quality Over All Runs
75 | # MAGIC %sql
76 | # MAGIC CREATE OR REPLACE TABLE dlt_dataquality
77 | # MAGIC SELECT
78 | # MAGIC id,
79 | # MAGIC timestamp,
80 | # MAGIC status_update,
81 | # MAGIC expectations.dataset,
82 | # MAGIC expectations.name,
83 | # MAGIC expectations.failed_records,
84 | # MAGIC expectations.passed_records
85 | # MAGIC FROM(
86 | # MAGIC SELECT
87 | # MAGIC id,
88 | # MAGIC timestamp,
89 | # MAGIC details:flow_progress.metrics.num_output_rows as output_records,
90 | # MAGIC details:flow_progress.data_quality.dropped_records,
91 | # MAGIC details:flow_progress.status as status_update,
92 | # MAGIC explode(from_json(details:flow_progress:data_quality:expectations
93 | # MAGIC , schema_of_json("[{'name':'str', 'dataset':'str', 'passed_records': 42, 'failed_records': 42}]"))) expectations
94 | # MAGIC FROM metrics_table
95 | # MAGIC WHERE details:flow_progress.metrics IS NOT NULL) data_quality;
96 | # MAGIC
97 | # MAGIC SELECT * FROM dlt_dataquality
98 |
99 | # COMMAND ----------
100 |
101 | # DBTITLE 1,Create Data Lineage Table
102 | # MAGIC %sql
103 | # MAGIC CREATE OR REPLACE TABLE dlt_lineage
104 | # MAGIC SELECT
105 | # MAGIC timestamp,
106 | # MAGIC details:flow_definition.output_dataset,
107 | # MAGIC details:flow_definition.input_datasets,
108 | # MAGIC details:flow_definition.flow_type,
109 | # MAGIC details:flow_definition.schema,
110 | # MAGIC details:flow_definition
111 | # MAGIC FROM metrics_table
112 | # MAGIC WHERE details:flow_definition IS NOT NULL
113 | # MAGIC ORDER BY timestamp;
114 | # MAGIC
115 | # MAGIC SELECT * FROM dlt_lineage
116 |
117 | # COMMAND ----------
118 |
119 | # MAGIC %md Let's head to our [Databricks SQL Dashboard](https://e2-demo-field-eng.cloud.databricks.com/sql/dashboards/88b89069-58f8-471f-9d60-a7943b93fa23-dlt-workshop--dlt-metrics?o=1444828305810485) where we can visualize our new tables.
120 |
121 | # COMMAND ----------
122 |
123 | # MAGIC %md These are the SQL Queries used to generate the visualizations on our dashboard:
124 |
125 | # COMMAND ----------
126 |
127 | # MAGIC %sql
128 | # MAGIC /* Failed Record Rate */
129 | # MAGIC SELECT sum(failed_records) / sum(failed_records + passed_records) * 100
130 | # MAGIC failure_rate,
131 | # MAGIC sum(failed_records + passed_records)
132 | # MAGIC output_records
133 | # MAGIC FROM dlt_workshop_retail.dlt_dataquality
134 |
135 | # COMMAND ----------
136 |
137 | # MAGIC %sql
138 | # MAGIC /* Number of Failed Records */
139 | # MAGIC SELECT avg(failed_records)
140 | # MAGIC FROM dlt_workshop_retail.dlt_dataquality
141 | # MAGIC WHERE failed_records > 0
142 |
143 | # COMMAND ----------
144 |
145 | # MAGIC %sql
146 | # MAGIC /* Failed and Passed Records Monthly */
147 | # MAGIC SELECT Sum(passed_records) AS passed_records,
148 | # MAGIC Sum(failed_records) AS failed_records,
149 | # MAGIC Sum(passed_records + failed_records) AS output_records,
150 | # MAGIC Sum(failed_records) / Sum(passed_records + failed_records) * 100 AS failure_rate,
151 | # MAGIC NAME,
152 | # MAGIC dataset,
153 | # MAGIC Date(timestamp) AS date
154 | # MAGIC FROM dlt_workshop_retail.dlt_dataquality
155 | # MAGIC GROUP BY date,
156 | # MAGIC dataset,
157 | # MAGIC NAME
158 |
159 | # COMMAND ----------
160 |
161 | # MAGIC %sql
162 | # MAGIC /* Records by Dataset */
163 | # MAGIC SELECT 'passed_records' AS type,
164 | # MAGIC Sum(passed_records) AS value,
165 | # MAGIC Sum(failed_records) / Sum(passed_records + failed_records) * 100 AS failure_rate,
166 | # MAGIC dataset
167 | # MAGIC FROM dlt_workshop_retail.dlt_dataquality
168 | # MAGIC GROUP BY dataset
169 | # MAGIC UNION
170 | # MAGIC SELECT 'failed_records' AS type,
171 | # MAGIC Sum(failed_records) AS value,
172 | # MAGIC Sum(failed_records) / Sum(passed_records + failed_records) * 100 AS failure_rate,
173 | # MAGIC dataset
174 | # MAGIC FROM dlt_workshop_retail.dlt_dataquality
175 | # MAGIC GROUP BY dataset
176 |
177 | # COMMAND ----------
178 |
179 | # MAGIC %sql
180 | # MAGIC /* Lineage Table */
181 | # MAGIC SELECT output_dataset AS dataset,
182 | # MAGIC input_datasets AS input
183 | # MAGIC FROM dlt_workshop_retail.dlt_lineage
184 | # MAGIC WHERE Date(timestamp) = "2022-12-09"
185 | # MAGIC AND flow_type = "incremental"
186 |
187 | # COMMAND ----------
188 |
189 |
190 |
--------------------------------------------------------------------------------
/notebooks/01-Structured Streaming with Databricks Delta Tables.py:
--------------------------------------------------------------------------------
1 | # Databricks notebook source
2 | # MAGIC %md
3 | # MAGIC
4 | # MAGIC # Structured Streaming with Databricks Delta Tables
5 | # MAGIC
6 | # MAGIC One of the hallmark innovations of Databricks and the Lakehouse vision is the establishing of a unified method for writing and reading data in a data lake. This unification of batch and streaming jobs has been called the post-lambda architecture for data warehousing. The flexibility, simplicity, and scalability of the new delta lake architecture has been pivotal towards addressing big data needs and has been gifted to the Linux Foundation. Fundamental to the lakehouse view of ETL/ELT is the usage of a multi-hop data architecture known as the medallion architecture.
7 | # MAGIC Delta Lake, the pillar of lakehouse platform, is an open-source storage layer that brings ACID transactions and increased performance to Apache Spark™ and big data workloads.
8 | # MAGIC
9 | # MAGIC 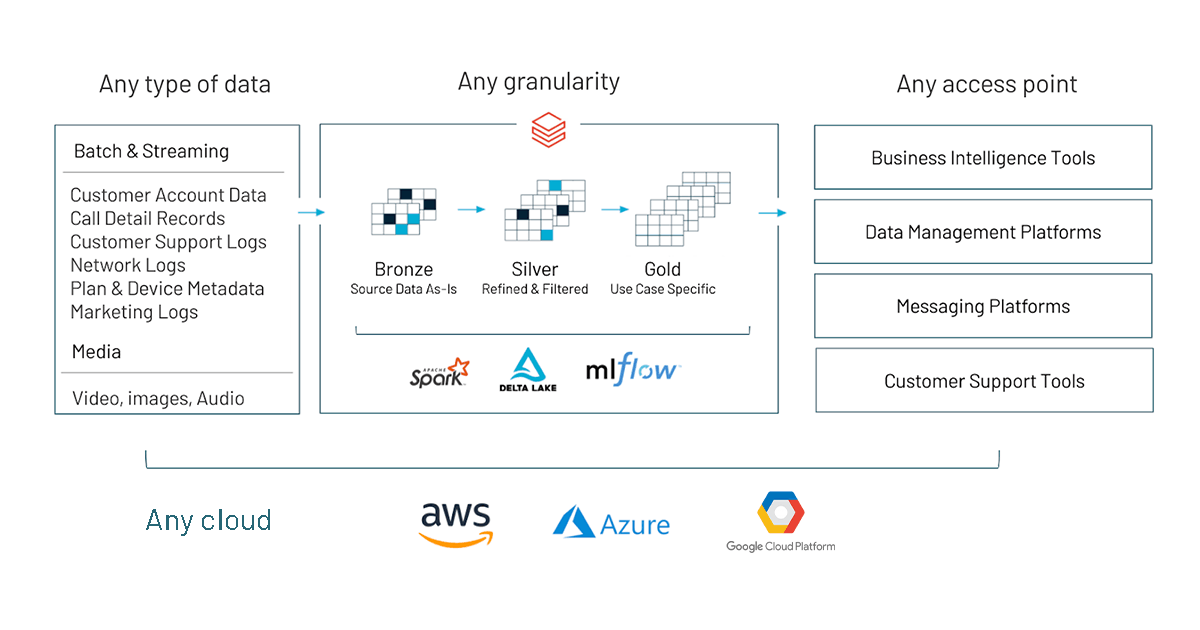 10 | # MAGIC
11 | # MAGIC See below links for more documentation:
12 | # MAGIC * [How to Process IoT Device JSON Data Using Apache Spark Datasets and DataFrames](https://databricks.com/blog/2016/03/28/how-to-process-iot-device-json-data-using-apache-spark-datasets-and-dataframes.html)
13 | # MAGIC * [Spark Structure Streaming](https://databricks.com/blog/2016/07/28/structured-streaming-in-apache-spark.html)
14 | # MAGIC * [Beyond Lambda](https://databricks.com/discover/getting-started-with-delta-lake-tech-talks/beyond-lambda-introducing-delta-architecture)
15 | # MAGIC * [Delta Lake Docs](https://docs.databricks.com/delta/index.html)
16 | # MAGIC * [Medallion Architecture](https://databricks.com/solutions/data-pipelines)
17 | # MAGIC * [Cost Savings with the Medallion Architecture](https://techcommunity.microsoft.com/t5/analytics-on-azure/how-to-reduce-infrastructure-costs-by-up-to-80-with-azure/ba-p/1820280)
18 | # MAGIC * [Change Data Capture Streams with the Medallion Architecture](https://databricks.com/blog/2021/06/09/how-to-simplify-cdc-with-delta-lakes-change-data-feed.html)
19 |
20 | # COMMAND ----------
21 |
22 | # MAGIC %md
23 | # MAGIC
24 | # MAGIC ## Schema
25 |
26 | # COMMAND ----------
27 |
28 | import time
29 | from pyspark.sql.functions import *
30 | from pyspark.sql.types import *
31 | from datetime import datetime, timezone
32 | import uuid
33 |
34 | # COMMAND ----------
35 |
36 | file_schema = (spark
37 | .read
38 | .format("csv")
39 | .option("header", True)
40 | .option("inferSchema", True)
41 | .load("/databricks-datasets/iot-stream/data-user/userData.csv")
42 | .limit(10)
43 | .schema)
44 |
45 | # COMMAND ----------
46 |
47 | print(file_schema)
48 |
49 | # COMMAND ----------
50 |
51 | # MAGIC %md
52 | # MAGIC
53 | # MAGIC ## Spark Structured Streaming
54 | # MAGIC
55 | # MAGIC
10 | # MAGIC
11 | # MAGIC See below links for more documentation:
12 | # MAGIC * [How to Process IoT Device JSON Data Using Apache Spark Datasets and DataFrames](https://databricks.com/blog/2016/03/28/how-to-process-iot-device-json-data-using-apache-spark-datasets-and-dataframes.html)
13 | # MAGIC * [Spark Structure Streaming](https://databricks.com/blog/2016/07/28/structured-streaming-in-apache-spark.html)
14 | # MAGIC * [Beyond Lambda](https://databricks.com/discover/getting-started-with-delta-lake-tech-talks/beyond-lambda-introducing-delta-architecture)
15 | # MAGIC * [Delta Lake Docs](https://docs.databricks.com/delta/index.html)
16 | # MAGIC * [Medallion Architecture](https://databricks.com/solutions/data-pipelines)
17 | # MAGIC * [Cost Savings with the Medallion Architecture](https://techcommunity.microsoft.com/t5/analytics-on-azure/how-to-reduce-infrastructure-costs-by-up-to-80-with-azure/ba-p/1820280)
18 | # MAGIC * [Change Data Capture Streams with the Medallion Architecture](https://databricks.com/blog/2021/06/09/how-to-simplify-cdc-with-delta-lakes-change-data-feed.html)
19 |
20 | # COMMAND ----------
21 |
22 | # MAGIC %md
23 | # MAGIC
24 | # MAGIC ## Schema
25 |
26 | # COMMAND ----------
27 |
28 | import time
29 | from pyspark.sql.functions import *
30 | from pyspark.sql.types import *
31 | from datetime import datetime, timezone
32 | import uuid
33 |
34 | # COMMAND ----------
35 |
36 | file_schema = (spark
37 | .read
38 | .format("csv")
39 | .option("header", True)
40 | .option("inferSchema", True)
41 | .load("/databricks-datasets/iot-stream/data-user/userData.csv")
42 | .limit(10)
43 | .schema)
44 |
45 | # COMMAND ----------
46 |
47 | print(file_schema)
48 |
49 | # COMMAND ----------
50 |
51 | # MAGIC %md
52 | # MAGIC
53 | # MAGIC ## Spark Structured Streaming
54 | # MAGIC
55 | # MAGIC 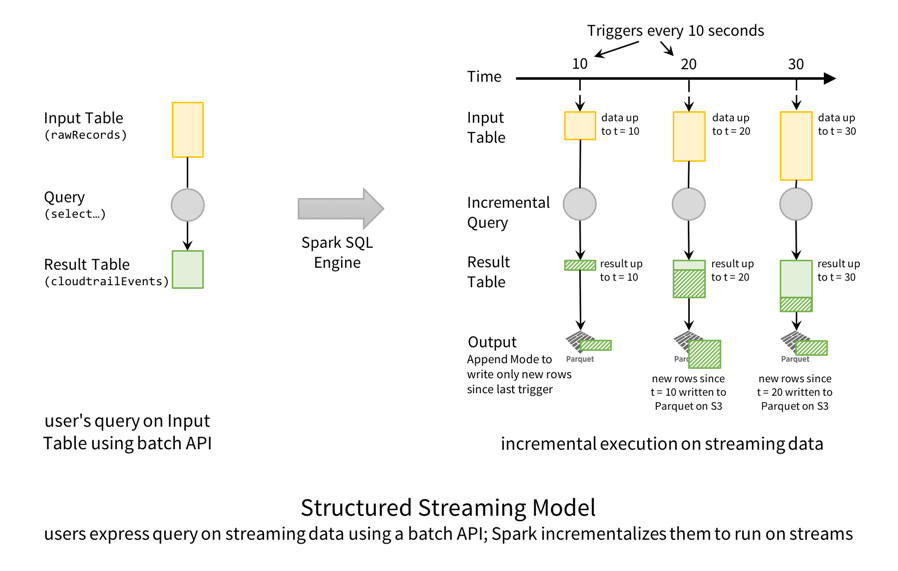 56 |
57 | # COMMAND ----------
58 |
59 | uuidUdf= udf(lambda : uuid.uuid4().hex,StringType())
60 |
61 | # Stream raw IOT Events from S3 bucket
62 | iot_event_stream = (spark
63 | .readStream
64 | .option( "maxFilesPerTrigger", 1 )
65 | .format("csv")
66 | .option("header", True)
67 | .schema(file_schema)
68 | .load("/databricks-datasets/iot-stream/data-user/*.csv")
69 | .withColumn( "id", uuidUdf() )
70 | .withColumn( "timestamp", lit(datetime.now().timestamp()).cast("timestamp") )
71 | .repartition(200)
72 | )
73 | display(iot_event_stream)
74 |
75 | # COMMAND ----------
76 |
77 | # DBTITLE 1,Housekeeping to make this idempotent
78 | # Full username, e.g. ".@databricks.com"
79 | username = dbutils.notebook.entry_point.getDbutils().notebook().getContext().tags().apply('user')
80 |
81 | # Short form of username, suitable for use as part of a topic name.
82 | user = username.split("@")[0].replace(".","_")
83 |
84 | # Database name
85 | dbName = user+"_workshop_db"
86 |
87 | spark.sql(f"CREATE SCHEMA IF NOT EXISTS {dbName}")
88 | spark.sql(f"USE {dbName}")
89 |
90 | # COMMAND ----------
91 |
92 | # MAGIC %md
93 | # MAGIC
94 | # MAGIC # Medallion Architecture
95 |
96 | # COMMAND ----------
97 |
98 | # MAGIC %sql
99 | # MAGIC
100 | # MAGIC --
101 | # MAGIC -- Drop streaming tables if they exist
102 | # MAGIC --
103 | # MAGIC
104 | # MAGIC Drop TABLE IF EXISTS iot_event_bronze;
105 | # MAGIC Drop TABLE IF EXISTS iot_event_silver;
106 | # MAGIC Drop TABLE IF EXISTS iot_event_gold;
107 |
108 | # COMMAND ----------
109 |
110 | # MAGIC %md
111 | # MAGIC
112 | # MAGIC ##Set up
113 |
114 | # COMMAND ----------
115 |
116 | # MAGIC %md
117 | # MAGIC ## Writing to Delta With Checkpointing
118 | # MAGIC
119 | # MAGIC
120 | # MAGIC
121 | # MAGIC
56 |
57 | # COMMAND ----------
58 |
59 | uuidUdf= udf(lambda : uuid.uuid4().hex,StringType())
60 |
61 | # Stream raw IOT Events from S3 bucket
62 | iot_event_stream = (spark
63 | .readStream
64 | .option( "maxFilesPerTrigger", 1 )
65 | .format("csv")
66 | .option("header", True)
67 | .schema(file_schema)
68 | .load("/databricks-datasets/iot-stream/data-user/*.csv")
69 | .withColumn( "id", uuidUdf() )
70 | .withColumn( "timestamp", lit(datetime.now().timestamp()).cast("timestamp") )
71 | .repartition(200)
72 | )
73 | display(iot_event_stream)
74 |
75 | # COMMAND ----------
76 |
77 | # DBTITLE 1,Housekeeping to make this idempotent
78 | # Full username, e.g. ".@databricks.com"
79 | username = dbutils.notebook.entry_point.getDbutils().notebook().getContext().tags().apply('user')
80 |
81 | # Short form of username, suitable for use as part of a topic name.
82 | user = username.split("@")[0].replace(".","_")
83 |
84 | # Database name
85 | dbName = user+"_workshop_db"
86 |
87 | spark.sql(f"CREATE SCHEMA IF NOT EXISTS {dbName}")
88 | spark.sql(f"USE {dbName}")
89 |
90 | # COMMAND ----------
91 |
92 | # MAGIC %md
93 | # MAGIC
94 | # MAGIC # Medallion Architecture
95 |
96 | # COMMAND ----------
97 |
98 | # MAGIC %sql
99 | # MAGIC
100 | # MAGIC --
101 | # MAGIC -- Drop streaming tables if they exist
102 | # MAGIC --
103 | # MAGIC
104 | # MAGIC Drop TABLE IF EXISTS iot_event_bronze;
105 | # MAGIC Drop TABLE IF EXISTS iot_event_silver;
106 | # MAGIC Drop TABLE IF EXISTS iot_event_gold;
107 |
108 | # COMMAND ----------
109 |
110 | # MAGIC %md
111 | # MAGIC
112 | # MAGIC ##Set up
113 |
114 | # COMMAND ----------
115 |
116 | # MAGIC %md
117 | # MAGIC ## Writing to Delta With Checkpointing
118 | # MAGIC
119 | # MAGIC
120 | # MAGIC
121 | # MAGIC  122 |
123 | # COMMAND ----------
124 |
125 | ######
126 | ## Setup checkpoint directory for writing out streaming workloads
127 | ######
128 |
129 | checkpoint_dir_bronze = f"/tmp/delta-stream-dltworkshop/{user}/bronze_check";
130 | checkpoint_dir_silver = f"/tmp/delta-stream-dltworkshop/{user}/silver_check"
131 | checkpoint_dir_gold = f"/tmp/delta-stream-dltworkshop/{user}/gold_check"
132 |
133 | # COMMAND ----------
134 |
135 | # MAGIC %md
136 | # MAGIC # Write IOT Events into a Bronze Delta Table
137 |
138 | # COMMAND ----------
139 |
140 | # Clear checkpoint location (for IDEMPOTENCY)
141 | dbutils.fs.rm(checkpoint_dir_bronze, True)
142 |
143 | iot_stream = iot_event_stream.writeStream\
144 | .format("delta")\
145 | .outputMode("append")\
146 | .option("header", True)\
147 | .option("checkpointLocation", checkpoint_dir_bronze)\
148 | .trigger(processingTime='10 seconds')\
149 | .table("iot_event_bronze")
150 |
151 | # COMMAND ----------
152 |
153 | # MAGIC %sql
154 | # MAGIC
155 | # MAGIC DESCRIBE TABLE EXTENDED iot_event_bronze;
156 |
157 | # COMMAND ----------
158 |
159 | # DBTITLE 1,Take a peak at delta lake files created
160 | display(dbutils.fs.ls(f"/user/hive/warehouse/{dbName}.db/iot_event_bronze/"))
161 |
162 | # COMMAND ----------
163 |
164 | # MAGIC %sql
165 | # MAGIC SELECT * FROM iot_event_bronze;
166 |
167 | # COMMAND ----------
168 |
169 | # MAGIC %md
170 | # MAGIC
171 | # MAGIC # Streaming ETL from Bronze to Silver
172 | # MAGIC
173 | # MAGIC Perform data cleanup and augmentation as we transform the Bronze data to Silver
174 |
175 | # COMMAND ----------
176 |
177 | """
178 | Deduplicate Bronze level data
179 | """
180 |
181 | # Clear checkpoint location (for IDEMPOTENCY)
182 | dbutils.fs.rm(checkpoint_dir_silver, True)
183 |
184 | # Drop terribly out-of-order events
185 | bronzeCleanDF = iot_event_stream.withWatermark( "timestamp", "1 day" )
186 |
187 | # Drop bad events
188 | bronzeCleanDF = bronzeCleanDF.dropna()
189 |
190 | silverStream = bronzeCleanDF.writeStream\
191 | .format("delta")\
192 | .outputMode("append")\
193 | .option( "checkpointLocation", checkpoint_dir_silver)\
194 | .trigger(processingTime='10 seconds')\
195 | .table("iot_event_silver")
196 | silverStream
197 |
198 | # COMMAND ----------
199 |
200 | # MAGIC %sql
201 | # MAGIC SELECT * FROM iot_event_silver;
202 |
203 | # COMMAND ----------
204 |
205 | # MAGIC %md
206 | # MAGIC
207 | # MAGIC ## Streaming Aggregation from Silver to Gold
208 |
209 | # COMMAND ----------
210 |
211 | silver_streamDF = spark.readStream.option( "maxFilesPerTrigger", 1 ).format( "delta" ).table("iot_event_silver")
212 |
213 | # Clear checkpoint location (for IDEMPOTENCY)
214 | dbutils.fs.rm(checkpoint_dir_gold, True)
215 |
216 | # def updateGold( batch, batchId ):
217 | # ( gold.alias("gold")
218 | # .merge( batch.alias("batch"),
219 | # "gold.date = batch.date AND gold.miles_walked = batch.miles_walked"
220 | # )
221 | # .whenMatchedUpdateAll()
222 | # .whenNotMatchedInsertAll()
223 | # .execute()
224 | # )
225 |
226 | ( (silver_streamDF.withWatermark("timestamp", "1 hour").groupBy("gender").agg(avg("weight").alias("avg_weight")))
227 | .writeStream
228 | .trigger(processingTime='12 seconds')
229 | .outputMode("complete")\
230 | .option( "checkpointLocation", checkpoint_dir_gold)\
231 | .table("iot_event_gold")
232 | )
233 |
234 | # COMMAND ----------
235 |
236 | # MAGIC %sql
237 | # MAGIC SELECT * FROM iot_event_gold;
238 |
239 | # COMMAND ----------
240 |
241 | # MAGIC %md
242 | # MAGIC
243 | # MAGIC ### Data Skipping and ZORDER
244 | # MAGIC
245 | # MAGIC Databricks Delta uses multiple mechanisms to speed up queries.
246 | # MAGIC
247 | # MAGIC
248 | # MAGIC Data Skipping is a performance optimization that aims at speeding up queries that contain filters (WHERE clauses).
249 | # MAGIC
250 | # MAGIC As new data is inserted into a Databricks Delta table, file-level min/max statistics are collected for all columns (including nested ones) of supported types. Then, when there’s a lookup query against the table, Databricks Delta first consults these statistics in order to determine which files can safely be skipped.
251 | # MAGIC
252 | # MAGIC ZOrdering Improve your query performance with `OPTIMIZE` and `ZORDER` using file compaction and a technique to co-locate related information in the same set of files. This co-locality is automatically used by Delta data-skipping algorithms to dramatically reduce the amount of data that needs to be read.
253 | # MAGIC
254 | # MAGIC Given a column that you want to perform ZORDER on, say `OrderColumn`, Delta
255 | # MAGIC * Takes existing parquet files within a partition.
256 | # MAGIC * Maps the rows within the parquet files according to `OrderColumn` using this algorithm.
257 | # MAGIC * In the case of only one column, the mapping above becomes a linear sort.
258 | # MAGIC * Rewrites the sorted data into new parquet files.
259 | # MAGIC
260 | # MAGIC Note: In streaming, where incoming events are inherently ordered (more or less) by event time, use `ZORDER` to sort by a different column, say 'userID'.
261 | # MAGIC
262 | # MAGIC Reference: [Processing Petabytes of Data in Seconds with Databricks Delta](https://databricks.com/blog/2018/07/31/processing-petabytes-of-data-in-seconds-with-databricks-delta.html)
263 |
264 | # COMMAND ----------
265 |
266 | # MAGIC %sql
267 | # MAGIC
268 | # MAGIC --
269 | # MAGIC -- Run a sample query
270 | # MAGIC --
271 | # MAGIC
272 | # MAGIC SELECT gender, avg(weight) as AVG_weight, avg(height) as AVG_height
273 | # MAGIC FROM iot_event_silver
274 | # MAGIC Group by gender
275 | # MAGIC ORDER by gender DESC, AVG_weight ASC;
276 |
277 | # COMMAND ----------
278 |
279 | # MAGIC %sql
280 | # MAGIC
281 | # MAGIC --
282 | # MAGIC -- Optimize and Z-order by
283 | # MAGIC --
284 | # MAGIC
285 | # MAGIC OPTIMIZE iot_event_silver
286 | # MAGIC ZORDER BY gender, height, weight;
287 |
288 | # COMMAND ----------
289 |
290 | # MAGIC %sql
291 | # MAGIC
292 | # MAGIC --
293 | # MAGIC -- Run the same select query at higher performance
294 | # MAGIC --
295 | # MAGIC
296 | # MAGIC SELECT gender, avg(weight) as AVG_weight, avg(height) as AVG_height
297 | # MAGIC FROM iot_event_silver
298 | # MAGIC Group by gender
299 | # MAGIC ORDER by gender DESC, AVG_weight ASC;
300 |
301 | # COMMAND ----------
302 |
303 | # DBTITLE 1,Stop all streams
304 | for s in spark.streams.active:
305 | s.stop()
306 |
307 | # COMMAND ----------
308 |
309 |
310 |
--------------------------------------------------------------------------------
/notebooks/03. Process Change Data Capture (CDC) data In DLT Pipeline.py:
--------------------------------------------------------------------------------
1 | # Databricks notebook source
2 | # MAGIC %pip install Faker
3 |
4 | # COMMAND ----------
5 |
6 | # MAGIC %md
7 | # MAGIC **When creating the pipeline add the following configuration to point to the data source:**
8 | # MAGIC
9 | # MAGIC `source` : `/tmp/delta-stream-dltworkshop/{your_user_name}/cdc_raw`
10 |
11 | # COMMAND ----------
12 |
13 | # MAGIC %md
14 | # MAGIC
15 | # MAGIC ## Importance of Change Data Capture (CDC)
16 | # MAGIC
17 | # MAGIC Change Data Capture (CDC) is the process that captures the changes in records made to a data storage like Database, Data Warehouse, etc. These changes usually refer to operations like data deletion, addition and updating.
18 | # MAGIC
19 | # MAGIC A straightforward way of Data Replication is to take a Database Dump that will export a Database and import it to a LakeHouse/DataWarehouse/Lake, but this is not a scalable approach.
20 | # MAGIC
21 | # MAGIC Change Data Capture, only capture the changes made to the Database and apply those changes to the target Database. CDC reduces the overhead, and supports real-time analytics. It enables incremental loading while eliminates the need for bulk load updating.
22 |
23 | # COMMAND ----------
24 |
25 | # MAGIC %md
26 | # MAGIC
27 | # MAGIC ### CDC Approaches
28 | # MAGIC
29 | # MAGIC **1- Develop in-house CDC process:**
30 | # MAGIC
31 | # MAGIC ***Complex Task:*** CDC Data Replication is not a one-time easy solution. Due to the differences between Database Providers, Varying Record Formats, and the inconvenience of accessing Log Records, CDC is challenging.
32 | # MAGIC
33 | # MAGIC ***Regular Maintainance:*** Writing a CDC process script is only the first step. You need to maintain a customized solution that can map to aformentioned changes regularly. This needs a lot of time and resources.
34 | # MAGIC
35 | # MAGIC ***Overburdening:*** Developers in companies already face the burden of public queries. Additional work for building customizes CDC solution will affect existing revenue-generating projects.
36 | # MAGIC
37 | # MAGIC **2- Using CDC tools** such as Debezium, Hevo Data, IBM Infosphere, Qlik Replicate, Talend, Oracle GoldenGate, StreamSets.
38 | # MAGIC
39 | # MAGIC In this demo repo we are using CDC data coming from a CDC tool.
40 | # MAGIC Since a CDC tool is reading database logs:
41 | # MAGIC We are no longer dependant on developers updating a certain column
42 | # MAGIC
43 | # MAGIC — A CDC tool like Debezium takes care of capturing every changed row. It records the history of data changes in Kafka logs, from where your application consumes them.
44 |
45 | # COMMAND ----------
46 |
47 | # MAGIC %md
48 | # MAGIC
49 | # MAGIC ### Implement CDC In DLT Pipeline: Change Data Capture (Python)
50 | # MAGIC
51 | # MAGIC
52 | # MAGIC
122 |
123 | # COMMAND ----------
124 |
125 | ######
126 | ## Setup checkpoint directory for writing out streaming workloads
127 | ######
128 |
129 | checkpoint_dir_bronze = f"/tmp/delta-stream-dltworkshop/{user}/bronze_check";
130 | checkpoint_dir_silver = f"/tmp/delta-stream-dltworkshop/{user}/silver_check"
131 | checkpoint_dir_gold = f"/tmp/delta-stream-dltworkshop/{user}/gold_check"
132 |
133 | # COMMAND ----------
134 |
135 | # MAGIC %md
136 | # MAGIC # Write IOT Events into a Bronze Delta Table
137 |
138 | # COMMAND ----------
139 |
140 | # Clear checkpoint location (for IDEMPOTENCY)
141 | dbutils.fs.rm(checkpoint_dir_bronze, True)
142 |
143 | iot_stream = iot_event_stream.writeStream\
144 | .format("delta")\
145 | .outputMode("append")\
146 | .option("header", True)\
147 | .option("checkpointLocation", checkpoint_dir_bronze)\
148 | .trigger(processingTime='10 seconds')\
149 | .table("iot_event_bronze")
150 |
151 | # COMMAND ----------
152 |
153 | # MAGIC %sql
154 | # MAGIC
155 | # MAGIC DESCRIBE TABLE EXTENDED iot_event_bronze;
156 |
157 | # COMMAND ----------
158 |
159 | # DBTITLE 1,Take a peak at delta lake files created
160 | display(dbutils.fs.ls(f"/user/hive/warehouse/{dbName}.db/iot_event_bronze/"))
161 |
162 | # COMMAND ----------
163 |
164 | # MAGIC %sql
165 | # MAGIC SELECT * FROM iot_event_bronze;
166 |
167 | # COMMAND ----------
168 |
169 | # MAGIC %md
170 | # MAGIC
171 | # MAGIC # Streaming ETL from Bronze to Silver
172 | # MAGIC
173 | # MAGIC Perform data cleanup and augmentation as we transform the Bronze data to Silver
174 |
175 | # COMMAND ----------
176 |
177 | """
178 | Deduplicate Bronze level data
179 | """
180 |
181 | # Clear checkpoint location (for IDEMPOTENCY)
182 | dbutils.fs.rm(checkpoint_dir_silver, True)
183 |
184 | # Drop terribly out-of-order events
185 | bronzeCleanDF = iot_event_stream.withWatermark( "timestamp", "1 day" )
186 |
187 | # Drop bad events
188 | bronzeCleanDF = bronzeCleanDF.dropna()
189 |
190 | silverStream = bronzeCleanDF.writeStream\
191 | .format("delta")\
192 | .outputMode("append")\
193 | .option( "checkpointLocation", checkpoint_dir_silver)\
194 | .trigger(processingTime='10 seconds')\
195 | .table("iot_event_silver")
196 | silverStream
197 |
198 | # COMMAND ----------
199 |
200 | # MAGIC %sql
201 | # MAGIC SELECT * FROM iot_event_silver;
202 |
203 | # COMMAND ----------
204 |
205 | # MAGIC %md
206 | # MAGIC
207 | # MAGIC ## Streaming Aggregation from Silver to Gold
208 |
209 | # COMMAND ----------
210 |
211 | silver_streamDF = spark.readStream.option( "maxFilesPerTrigger", 1 ).format( "delta" ).table("iot_event_silver")
212 |
213 | # Clear checkpoint location (for IDEMPOTENCY)
214 | dbutils.fs.rm(checkpoint_dir_gold, True)
215 |
216 | # def updateGold( batch, batchId ):
217 | # ( gold.alias("gold")
218 | # .merge( batch.alias("batch"),
219 | # "gold.date = batch.date AND gold.miles_walked = batch.miles_walked"
220 | # )
221 | # .whenMatchedUpdateAll()
222 | # .whenNotMatchedInsertAll()
223 | # .execute()
224 | # )
225 |
226 | ( (silver_streamDF.withWatermark("timestamp", "1 hour").groupBy("gender").agg(avg("weight").alias("avg_weight")))
227 | .writeStream
228 | .trigger(processingTime='12 seconds')
229 | .outputMode("complete")\
230 | .option( "checkpointLocation", checkpoint_dir_gold)\
231 | .table("iot_event_gold")
232 | )
233 |
234 | # COMMAND ----------
235 |
236 | # MAGIC %sql
237 | # MAGIC SELECT * FROM iot_event_gold;
238 |
239 | # COMMAND ----------
240 |
241 | # MAGIC %md
242 | # MAGIC
243 | # MAGIC ### Data Skipping and ZORDER
244 | # MAGIC
245 | # MAGIC Databricks Delta uses multiple mechanisms to speed up queries.
246 | # MAGIC
247 | # MAGIC
248 | # MAGIC Data Skipping is a performance optimization that aims at speeding up queries that contain filters (WHERE clauses).
249 | # MAGIC
250 | # MAGIC As new data is inserted into a Databricks Delta table, file-level min/max statistics are collected for all columns (including nested ones) of supported types. Then, when there’s a lookup query against the table, Databricks Delta first consults these statistics in order to determine which files can safely be skipped.
251 | # MAGIC
252 | # MAGIC ZOrdering Improve your query performance with `OPTIMIZE` and `ZORDER` using file compaction and a technique to co-locate related information in the same set of files. This co-locality is automatically used by Delta data-skipping algorithms to dramatically reduce the amount of data that needs to be read.
253 | # MAGIC
254 | # MAGIC Given a column that you want to perform ZORDER on, say `OrderColumn`, Delta
255 | # MAGIC * Takes existing parquet files within a partition.
256 | # MAGIC * Maps the rows within the parquet files according to `OrderColumn` using this algorithm.
257 | # MAGIC * In the case of only one column, the mapping above becomes a linear sort.
258 | # MAGIC * Rewrites the sorted data into new parquet files.
259 | # MAGIC
260 | # MAGIC Note: In streaming, where incoming events are inherently ordered (more or less) by event time, use `ZORDER` to sort by a different column, say 'userID'.
261 | # MAGIC
262 | # MAGIC Reference: [Processing Petabytes of Data in Seconds with Databricks Delta](https://databricks.com/blog/2018/07/31/processing-petabytes-of-data-in-seconds-with-databricks-delta.html)
263 |
264 | # COMMAND ----------
265 |
266 | # MAGIC %sql
267 | # MAGIC
268 | # MAGIC --
269 | # MAGIC -- Run a sample query
270 | # MAGIC --
271 | # MAGIC
272 | # MAGIC SELECT gender, avg(weight) as AVG_weight, avg(height) as AVG_height
273 | # MAGIC FROM iot_event_silver
274 | # MAGIC Group by gender
275 | # MAGIC ORDER by gender DESC, AVG_weight ASC;
276 |
277 | # COMMAND ----------
278 |
279 | # MAGIC %sql
280 | # MAGIC
281 | # MAGIC --
282 | # MAGIC -- Optimize and Z-order by
283 | # MAGIC --
284 | # MAGIC
285 | # MAGIC OPTIMIZE iot_event_silver
286 | # MAGIC ZORDER BY gender, height, weight;
287 |
288 | # COMMAND ----------
289 |
290 | # MAGIC %sql
291 | # MAGIC
292 | # MAGIC --
293 | # MAGIC -- Run the same select query at higher performance
294 | # MAGIC --
295 | # MAGIC
296 | # MAGIC SELECT gender, avg(weight) as AVG_weight, avg(height) as AVG_height
297 | # MAGIC FROM iot_event_silver
298 | # MAGIC Group by gender
299 | # MAGIC ORDER by gender DESC, AVG_weight ASC;
300 |
301 | # COMMAND ----------
302 |
303 | # DBTITLE 1,Stop all streams
304 | for s in spark.streams.active:
305 | s.stop()
306 |
307 | # COMMAND ----------
308 |
309 |
310 |
--------------------------------------------------------------------------------
/notebooks/03. Process Change Data Capture (CDC) data In DLT Pipeline.py:
--------------------------------------------------------------------------------
1 | # Databricks notebook source
2 | # MAGIC %pip install Faker
3 |
4 | # COMMAND ----------
5 |
6 | # MAGIC %md
7 | # MAGIC **When creating the pipeline add the following configuration to point to the data source:**
8 | # MAGIC
9 | # MAGIC `source` : `/tmp/delta-stream-dltworkshop/{your_user_name}/cdc_raw`
10 |
11 | # COMMAND ----------
12 |
13 | # MAGIC %md
14 | # MAGIC
15 | # MAGIC ## Importance of Change Data Capture (CDC)
16 | # MAGIC
17 | # MAGIC Change Data Capture (CDC) is the process that captures the changes in records made to a data storage like Database, Data Warehouse, etc. These changes usually refer to operations like data deletion, addition and updating.
18 | # MAGIC
19 | # MAGIC A straightforward way of Data Replication is to take a Database Dump that will export a Database and import it to a LakeHouse/DataWarehouse/Lake, but this is not a scalable approach.
20 | # MAGIC
21 | # MAGIC Change Data Capture, only capture the changes made to the Database and apply those changes to the target Database. CDC reduces the overhead, and supports real-time analytics. It enables incremental loading while eliminates the need for bulk load updating.
22 |
23 | # COMMAND ----------
24 |
25 | # MAGIC %md
26 | # MAGIC
27 | # MAGIC ### CDC Approaches
28 | # MAGIC
29 | # MAGIC **1- Develop in-house CDC process:**
30 | # MAGIC
31 | # MAGIC ***Complex Task:*** CDC Data Replication is not a one-time easy solution. Due to the differences between Database Providers, Varying Record Formats, and the inconvenience of accessing Log Records, CDC is challenging.
32 | # MAGIC
33 | # MAGIC ***Regular Maintainance:*** Writing a CDC process script is only the first step. You need to maintain a customized solution that can map to aformentioned changes regularly. This needs a lot of time and resources.
34 | # MAGIC
35 | # MAGIC ***Overburdening:*** Developers in companies already face the burden of public queries. Additional work for building customizes CDC solution will affect existing revenue-generating projects.
36 | # MAGIC
37 | # MAGIC **2- Using CDC tools** such as Debezium, Hevo Data, IBM Infosphere, Qlik Replicate, Talend, Oracle GoldenGate, StreamSets.
38 | # MAGIC
39 | # MAGIC In this demo repo we are using CDC data coming from a CDC tool.
40 | # MAGIC Since a CDC tool is reading database logs:
41 | # MAGIC We are no longer dependant on developers updating a certain column
42 | # MAGIC
43 | # MAGIC — A CDC tool like Debezium takes care of capturing every changed row. It records the history of data changes in Kafka logs, from where your application consumes them.
44 |
45 | # COMMAND ----------
46 |
47 | # MAGIC %md
48 | # MAGIC
49 | # MAGIC ### Implement CDC In DLT Pipeline: Change Data Capture (Python)
50 | # MAGIC
51 | # MAGIC
52 | # MAGIC 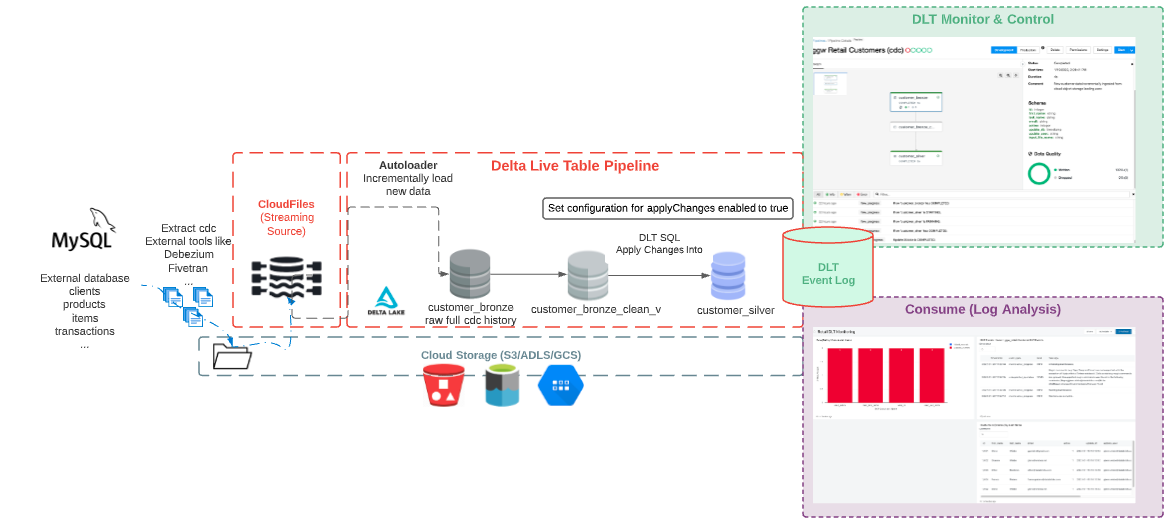 53 | # MAGIC
54 | # MAGIC
55 | # MAGIC ###### Resource [Change data capture with Delta Live Tables](https://docs.databricks.com/data-engineering/delta-live-tables/delta-live-tables-cdc.html)
56 |
57 | # COMMAND ----------
58 |
59 | # MAGIC %md
60 | # MAGIC
61 | # MAGIC ### Retail CDC Data Generator
62 |
63 | # COMMAND ----------
64 |
65 | # Full username, e.g. ".@databricks.com"
66 | username = dbutils.notebook.entry_point.getDbutils().notebook().getContext().tags().apply('user')
67 |
68 | # Short form of username, suitable for use as part of a topic name.
69 | user = username.split("@")[0].replace(".","_")
70 |
71 | # COMMAND ----------
72 |
73 | from pyspark.sql import functions as F
74 | from faker import Faker
75 | from collections import OrderedDict
76 | import uuid
77 |
78 | folder = f"/tmp/delta-stream-dltworkshop/{user}/cdc_raw"
79 | # dbutils.fs.rm(folder, True) # For Idempotency
80 |
81 | try:
82 | dbutils.fs.ls(folder)
83 | except:
84 | print("folder doesn't exists, generating the data...")
85 | fake = Faker()
86 | fake_firstname = F.udf(fake.first_name)
87 | fake_lastname = F.udf(fake.last_name)
88 | fake_email = F.udf(fake.ascii_company_email)
89 | fake_date = F.udf(lambda:fake.date_time_this_month().strftime("%m-%d-%Y %H:%M:%S"))
90 | fake_address = F.udf(fake.address)
91 | operations = OrderedDict([("APPEND", 0.5),("DELETE", 0.1),("UPDATE", 0.3),(None, 0.01)])
92 | fake_operation = F.udf(lambda:fake.random_elements(elements=operations, length=1)[0])
93 | fake_id = F.udf(lambda: str(uuid.uuid4()))
94 |
95 | df = spark.range(0, 100000)
96 | df = df.withColumn("id", fake_id())
97 | df = df.withColumn("firstname", fake_firstname())
98 | df = df.withColumn("lastname", fake_lastname())
99 | df = df.withColumn("email", fake_email())
100 | df = df.withColumn("address", fake_address())
101 | df = df.withColumn("operation", fake_operation())
102 | df = df.withColumn("operation_date", fake_date())
103 |
104 | df.repartition(100).write.format("json").mode("overwrite").save(folder+"/customers")
105 |
106 | df = spark.range(0, 10000)
107 | df = df.withColumn("id", fake_id())
108 | df = df.withColumn("transaction_date", fake_date())
109 | df = df.withColumn("amount", F.round(F.rand()*1000))
110 | df = df.withColumn("item_count", F.round(F.rand()*10))
111 | df = df.withColumn("operation", fake_operation())
112 | df = df.withColumn("operation_date", fake_date())
113 | #Join with the customer to get the same IDs generated.
114 | df = df.withColumn("t_id", F.monotonically_increasing_id()).join(spark.read.json(folder+"/customers").select("id").withColumnRenamed("id", "customer_id").withColumn("t_id", F.monotonically_increasing_id()), "t_id").drop("t_id")
115 | df.repartition(10).write.format("json").mode("overwrite").save(folder+"/transactions")
116 |
117 | # COMMAND ----------
118 |
119 | spark.read.json(folder+"/customers").display()
120 |
121 | # COMMAND ----------
122 |
123 | # MAGIC %md
124 | # MAGIC ## How to synchronize your SQL Database with your Lakehouse?
125 | # MAGIC CDC flow with a CDC tool, autoloader and DLT pipeline:
126 | # MAGIC
127 | # MAGIC - A CDC tool reads database logs, produces json messages that includes the changes, and streams the records with changes description to Kafka
128 | # MAGIC - Kafka streams the messages which holds INSERT, UPDATE and DELETE operations, and stores them in cloud object storage (S3 folder, ADLS, etc).
129 | # MAGIC - Using Autoloader we incrementally load the messages from cloud object storage, and stores them in Bronze table as it stores the raw messages
130 | # MAGIC - Next we can perform APPLY CHANGES INTO on the cleaned Bronze layer table to propagate the most updated data downstream to the Silver Table
131 | # MAGIC
132 | # MAGIC Here is the flow we'll implement, consuming CDC data from an external database. Note that the incoming could be any format, including message queue such as Kafka.
133 | # MAGIC
53 | # MAGIC
54 | # MAGIC
55 | # MAGIC ###### Resource [Change data capture with Delta Live Tables](https://docs.databricks.com/data-engineering/delta-live-tables/delta-live-tables-cdc.html)
56 |
57 | # COMMAND ----------
58 |
59 | # MAGIC %md
60 | # MAGIC
61 | # MAGIC ### Retail CDC Data Generator
62 |
63 | # COMMAND ----------
64 |
65 | # Full username, e.g. ".@databricks.com"
66 | username = dbutils.notebook.entry_point.getDbutils().notebook().getContext().tags().apply('user')
67 |
68 | # Short form of username, suitable for use as part of a topic name.
69 | user = username.split("@")[0].replace(".","_")
70 |
71 | # COMMAND ----------
72 |
73 | from pyspark.sql import functions as F
74 | from faker import Faker
75 | from collections import OrderedDict
76 | import uuid
77 |
78 | folder = f"/tmp/delta-stream-dltworkshop/{user}/cdc_raw"
79 | # dbutils.fs.rm(folder, True) # For Idempotency
80 |
81 | try:
82 | dbutils.fs.ls(folder)
83 | except:
84 | print("folder doesn't exists, generating the data...")
85 | fake = Faker()
86 | fake_firstname = F.udf(fake.first_name)
87 | fake_lastname = F.udf(fake.last_name)
88 | fake_email = F.udf(fake.ascii_company_email)
89 | fake_date = F.udf(lambda:fake.date_time_this_month().strftime("%m-%d-%Y %H:%M:%S"))
90 | fake_address = F.udf(fake.address)
91 | operations = OrderedDict([("APPEND", 0.5),("DELETE", 0.1),("UPDATE", 0.3),(None, 0.01)])
92 | fake_operation = F.udf(lambda:fake.random_elements(elements=operations, length=1)[0])
93 | fake_id = F.udf(lambda: str(uuid.uuid4()))
94 |
95 | df = spark.range(0, 100000)
96 | df = df.withColumn("id", fake_id())
97 | df = df.withColumn("firstname", fake_firstname())
98 | df = df.withColumn("lastname", fake_lastname())
99 | df = df.withColumn("email", fake_email())
100 | df = df.withColumn("address", fake_address())
101 | df = df.withColumn("operation", fake_operation())
102 | df = df.withColumn("operation_date", fake_date())
103 |
104 | df.repartition(100).write.format("json").mode("overwrite").save(folder+"/customers")
105 |
106 | df = spark.range(0, 10000)
107 | df = df.withColumn("id", fake_id())
108 | df = df.withColumn("transaction_date", fake_date())
109 | df = df.withColumn("amount", F.round(F.rand()*1000))
110 | df = df.withColumn("item_count", F.round(F.rand()*10))
111 | df = df.withColumn("operation", fake_operation())
112 | df = df.withColumn("operation_date", fake_date())
113 | #Join with the customer to get the same IDs generated.
114 | df = df.withColumn("t_id", F.monotonically_increasing_id()).join(spark.read.json(folder+"/customers").select("id").withColumnRenamed("id", "customer_id").withColumn("t_id", F.monotonically_increasing_id()), "t_id").drop("t_id")
115 | df.repartition(10).write.format("json").mode("overwrite").save(folder+"/transactions")
116 |
117 | # COMMAND ----------
118 |
119 | spark.read.json(folder+"/customers").display()
120 |
121 | # COMMAND ----------
122 |
123 | # MAGIC %md
124 | # MAGIC ## How to synchronize your SQL Database with your Lakehouse?
125 | # MAGIC CDC flow with a CDC tool, autoloader and DLT pipeline:
126 | # MAGIC
127 | # MAGIC - A CDC tool reads database logs, produces json messages that includes the changes, and streams the records with changes description to Kafka
128 | # MAGIC - Kafka streams the messages which holds INSERT, UPDATE and DELETE operations, and stores them in cloud object storage (S3 folder, ADLS, etc).
129 | # MAGIC - Using Autoloader we incrementally load the messages from cloud object storage, and stores them in Bronze table as it stores the raw messages
130 | # MAGIC - Next we can perform APPLY CHANGES INTO on the cleaned Bronze layer table to propagate the most updated data downstream to the Silver Table
131 | # MAGIC
132 | # MAGIC Here is the flow we'll implement, consuming CDC data from an external database. Note that the incoming could be any format, including message queue such as Kafka.
133 | # MAGIC 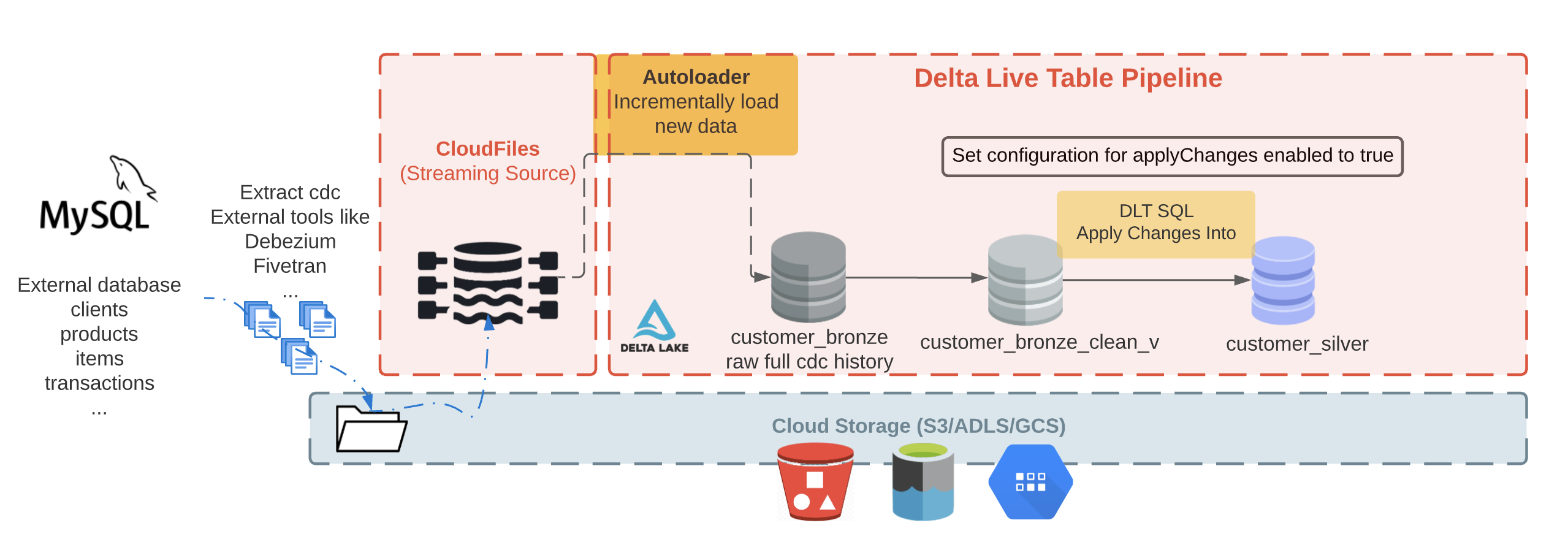 134 |
135 | # COMMAND ----------
136 |
137 | # MAGIC %md
138 | # MAGIC
139 | # MAGIC ###How does CDC tools like Debezium output looks like?
140 | # MAGIC
141 | # MAGIC A json message describing the changed data has interesting fields similar to the list below:
142 | # MAGIC
143 | # MAGIC - operation: an operation code (DELETE, APPEND, UPDATE, CREATE)
144 | # MAGIC - operation_date: the date and timestamp for the record came for each operation action
145 | # MAGIC
146 | # MAGIC Some other fields that you may see in Debezium output (not included in this demo):
147 | # MAGIC - before: the row before the change
148 | # MAGIC - after: the row after the change
149 | # MAGIC
150 | # MAGIC To learn more about the expected fields check out [this reference](https://debezium.io/documentation/reference/stable/connectors/postgresql.html#postgresql-update-events)
151 |
152 | # COMMAND ----------
153 |
154 | # MAGIC %md-sandbox
155 | # MAGIC ### Incremental data loading using Auto Loader (cloud_files)
156 | # MAGIC
157 | # MAGIC
158 | # MAGIC Working with external system can be challenging due to schema update. The external database can have schema update, adding or modifying columns, and our system must be robust against these changes.
159 | # MAGIC Databricks Autoloader (`cloudFiles`) handles schema inference and evolution out of the box.
160 | # MAGIC
161 | # MAGIC Autoloader allow us to efficiently ingest millions of files from a cloud storage, and support efficient schema inference and evolution at scale. In this notebook we leverage Autoloader to handle streaming (and batch) data.
162 | # MAGIC
134 |
135 | # COMMAND ----------
136 |
137 | # MAGIC %md
138 | # MAGIC
139 | # MAGIC ###How does CDC tools like Debezium output looks like?
140 | # MAGIC
141 | # MAGIC A json message describing the changed data has interesting fields similar to the list below:
142 | # MAGIC
143 | # MAGIC - operation: an operation code (DELETE, APPEND, UPDATE, CREATE)
144 | # MAGIC - operation_date: the date and timestamp for the record came for each operation action
145 | # MAGIC
146 | # MAGIC Some other fields that you may see in Debezium output (not included in this demo):
147 | # MAGIC - before: the row before the change
148 | # MAGIC - after: the row after the change
149 | # MAGIC
150 | # MAGIC To learn more about the expected fields check out [this reference](https://debezium.io/documentation/reference/stable/connectors/postgresql.html#postgresql-update-events)
151 |
152 | # COMMAND ----------
153 |
154 | # MAGIC %md-sandbox
155 | # MAGIC ### Incremental data loading using Auto Loader (cloud_files)
156 | # MAGIC
157 | # MAGIC
158 | # MAGIC Working with external system can be challenging due to schema update. The external database can have schema update, adding or modifying columns, and our system must be robust against these changes.
159 | # MAGIC Databricks Autoloader (`cloudFiles`) handles schema inference and evolution out of the box.
160 | # MAGIC
161 | # MAGIC Autoloader allow us to efficiently ingest millions of files from a cloud storage, and support efficient schema inference and evolution at scale. In this notebook we leverage Autoloader to handle streaming (and batch) data.
162 | # MAGIC
163 | # MAGIC

164 | # MAGIC
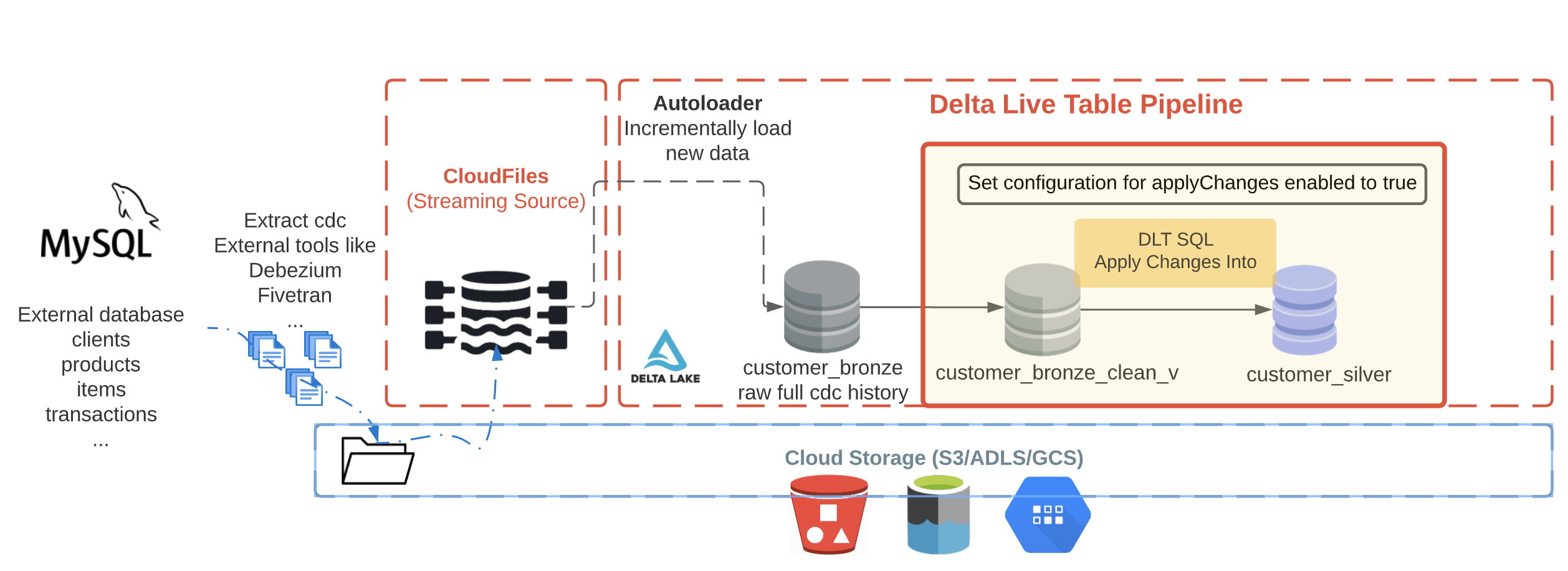 248 | # MAGIC
249 | # MAGIC The silver `customer_silver` table will contains the most up to date view. It'll be a replicate of the original table.
250 | # MAGIC
251 | # MAGIC To propagate the `Apply Changes Into` operations downstream to the `Silver` layer, we must explicitly enable the feature in pipeline by adding and enabling the applyChanges configuration to the DLT pipeline settings.
252 |
253 | # COMMAND ----------
254 |
255 | # DBTITLE 1,Delete unwanted clients records - Silver Table - DLT Python
256 | """
257 | ##Create the target table
258 | """
259 |
260 | dlt.create_streaming_live_table(name="customer_silver",
261 | comment="Clean, merged customers",
262 | table_properties={
263 | "quality": "silver"
264 | }
265 | )
266 |
267 | # COMMAND ----------
268 |
269 | """
270 | ##APPLY CHANGES the target table
271 | """
272 |
273 | dlt.apply_changes(
274 | target = "customer_silver", #The customer table being materilized
275 | source = "customer_bronze_clean_v", #the incoming CDC
276 | keys = ["id"], #Primary key to match the rows to upsert/delete
277 | sequence_by = col("operation_date"), #deduplicate by operation date getting the most recent value
278 | apply_as_deletes = expr("operation = 'DELETE'"), #DELETE condition
279 | except_column_list = ["operation", "operation_date", "_rescued_data"], # drop metadata columns
280 | stored_as_scd_type = 2
281 | )
282 |
283 | # COMMAND ----------
284 |
285 | # MAGIC %md
286 | # MAGIC
287 | # MAGIC Next step, create DLT pipeline, add a path to this notebook and **add configuration with enabling applychanges to true**.
288 |
--------------------------------------------------------------------------------
/LICENSE:
--------------------------------------------------------------------------------
1 | GNU GENERAL PUBLIC LICENSE
2 | Version 3, 29 June 2007
3 |
4 | Copyright (C) 2007 Free Software Foundation, Inc.
5 | Everyone is permitted to copy and distribute verbatim copies
6 | of this license document, but changing it is not allowed.
7 |
8 | Preamble
9 |
10 | The GNU General Public License is a free, copyleft license for
11 | software and other kinds of works.
12 |
13 | The licenses for most software and other practical works are designed
14 | to take away your freedom to share and change the works. By contrast,
15 | the GNU General Public License is intended to guarantee your freedom to
16 | share and change all versions of a program--to make sure it remains free
17 | software for all its users. We, the Free Software Foundation, use the
18 | GNU General Public License for most of our software; it applies also to
19 | any other work released this way by its authors. You can apply it to
20 | your programs, too.
21 |
22 | When we speak of free software, we are referring to freedom, not
23 | price. Our General Public Licenses are designed to make sure that you
24 | have the freedom to distribute copies of free software (and charge for
25 | them if you wish), that you receive source code or can get it if you
26 | want it, that you can change the software or use pieces of it in new
27 | free programs, and that you know you can do these things.
28 |
29 | To protect your rights, we need to prevent others from denying you
30 | these rights or asking you to surrender the rights. Therefore, you have
31 | certain responsibilities if you distribute copies of the software, or if
32 | you modify it: responsibilities to respect the freedom of others.
33 |
34 | For example, if you distribute copies of such a program, whether
35 | gratis or for a fee, you must pass on to the recipients the same
36 | freedoms that you received. You must make sure that they, too, receive
37 | or can get the source code. And you must show them these terms so they
38 | know their rights.
39 |
40 | Developers that use the GNU GPL protect your rights with two steps:
41 | (1) assert copyright on the software, and (2) offer you this License
42 | giving you legal permission to copy, distribute and/or modify it.
43 |
44 | For the developers' and authors' protection, the GPL clearly explains
45 | that there is no warranty for this free software. For both users' and
46 | authors' sake, the GPL requires that modified versions be marked as
47 | changed, so that their problems will not be attributed erroneously to
48 | authors of previous versions.
49 |
50 | Some devices are designed to deny users access to install or run
51 | modified versions of the software inside them, although the manufacturer
52 | can do so. This is fundamentally incompatible with the aim of
53 | protecting users' freedom to change the software. The systematic
54 | pattern of such abuse occurs in the area of products for individuals to
55 | use, which is precisely where it is most unacceptable. Therefore, we
56 | have designed this version of the GPL to prohibit the practice for those
57 | products. If such problems arise substantially in other domains, we
58 | stand ready to extend this provision to those domains in future versions
59 | of the GPL, as needed to protect the freedom of users.
60 |
61 | Finally, every program is threatened constantly by software patents.
62 | States should not allow patents to restrict development and use of
63 | software on general-purpose computers, but in those that do, we wish to
64 | avoid the special danger that patents applied to a free program could
65 | make it effectively proprietary. To prevent this, the GPL assures that
66 | patents cannot be used to render the program non-free.
67 |
68 | The precise terms and conditions for copying, distribution and
69 | modification follow.
70 |
71 | TERMS AND CONDITIONS
72 |
73 | 0. Definitions.
74 |
75 | "This License" refers to version 3 of the GNU General Public License.
76 |
77 | "Copyright" also means copyright-like laws that apply to other kinds of
78 | works, such as semiconductor masks.
79 |
80 | "The Program" refers to any copyrightable work licensed under this
81 | License. Each licensee is addressed as "you". "Licensees" and
82 | "recipients" may be individuals or organizations.
83 |
84 | To "modify" a work means to copy from or adapt all or part of the work
85 | in a fashion requiring copyright permission, other than the making of an
86 | exact copy. The resulting work is called a "modified version" of the
87 | earlier work or a work "based on" the earlier work.
88 |
89 | A "covered work" means either the unmodified Program or a work based
90 | on the Program.
91 |
92 | To "propagate" a work means to do anything with it that, without
93 | permission, would make you directly or secondarily liable for
94 | infringement under applicable copyright law, except executing it on a
95 | computer or modifying a private copy. Propagation includes copying,
96 | distribution (with or without modification), making available to the
97 | public, and in some countries other activities as well.
98 |
99 | To "convey" a work means any kind of propagation that enables other
100 | parties to make or receive copies. Mere interaction with a user through
101 | a computer network, with no transfer of a copy, is not conveying.
102 |
103 | An interactive user interface displays "Appropriate Legal Notices"
104 | to the extent that it includes a convenient and prominently visible
105 | feature that (1) displays an appropriate copyright notice, and (2)
106 | tells the user that there is no warranty for the work (except to the
107 | extent that warranties are provided), that licensees may convey the
108 | work under this License, and how to view a copy of this License. If
109 | the interface presents a list of user commands or options, such as a
110 | menu, a prominent item in the list meets this criterion.
111 |
112 | 1. Source Code.
113 |
114 | The "source code" for a work means the preferred form of the work
115 | for making modifications to it. "Object code" means any non-source
116 | form of a work.
117 |
118 | A "Standard Interface" means an interface that either is an official
119 | standard defined by a recognized standards body, or, in the case of
120 | interfaces specified for a particular programming language, one that
121 | is widely used among developers working in that language.
122 |
123 | The "System Libraries" of an executable work include anything, other
124 | than the work as a whole, that (a) is included in the normal form of
125 | packaging a Major Component, but which is not part of that Major
126 | Component, and (b) serves only to enable use of the work with that
127 | Major Component, or to implement a Standard Interface for which an
128 | implementation is available to the public in source code form. A
129 | "Major Component", in this context, means a major essential component
130 | (kernel, window system, and so on) of the specific operating system
131 | (if any) on which the executable work runs, or a compiler used to
132 | produce the work, or an object code interpreter used to run it.
133 |
134 | The "Corresponding Source" for a work in object code form means all
135 | the source code needed to generate, install, and (for an executable
136 | work) run the object code and to modify the work, including scripts to
137 | control those activities. However, it does not include the work's
138 | System Libraries, or general-purpose tools or generally available free
139 | programs which are used unmodified in performing those activities but
140 | which are not part of the work. For example, Corresponding Source
141 | includes interface definition files associated with source files for
142 | the work, and the source code for shared libraries and dynamically
143 | linked subprograms that the work is specifically designed to require,
144 | such as by intimate data communication or control flow between those
145 | subprograms and other parts of the work.
146 |
147 | The Corresponding Source need not include anything that users
148 | can regenerate automatically from other parts of the Corresponding
149 | Source.
150 |
151 | The Corresponding Source for a work in source code form is that
152 | same work.
153 |
154 | 2. Basic Permissions.
155 |
156 | All rights granted under this License are granted for the term of
157 | copyright on the Program, and are irrevocable provided the stated
158 | conditions are met. This License explicitly affirms your unlimited
159 | permission to run the unmodified Program. The output from running a
160 | covered work is covered by this License only if the output, given its
161 | content, constitutes a covered work. This License acknowledges your
162 | rights of fair use or other equivalent, as provided by copyright law.
163 |
164 | You may make, run and propagate covered works that you do not
165 | convey, without conditions so long as your license otherwise remains
166 | in force. You may convey covered works to others for the sole purpose
167 | of having them make modifications exclusively for you, or provide you
168 | with facilities for running those works, provided that you comply with
169 | the terms of this License in conveying all material for which you do
170 | not control copyright. Those thus making or running the covered works
171 | for you must do so exclusively on your behalf, under your direction
172 | and control, on terms that prohibit them from making any copies of
173 | your copyrighted material outside their relationship with you.
174 |
175 | Conveying under any other circumstances is permitted solely under
176 | the conditions stated below. Sublicensing is not allowed; section 10
177 | makes it unnecessary.
178 |
179 | 3. Protecting Users' Legal Rights From Anti-Circumvention Law.
180 |
181 | No covered work shall be deemed part of an effective technological
182 | measure under any applicable law fulfilling obligations under article
183 | 11 of the WIPO copyright treaty adopted on 20 December 1996, or
184 | similar laws prohibiting or restricting circumvention of such
185 | measures.
186 |
187 | When you convey a covered work, you waive any legal power to forbid
188 | circumvention of technological measures to the extent such circumvention
189 | is effected by exercising rights under this License with respect to
190 | the covered work, and you disclaim any intention to limit operation or
191 | modification of the work as a means of enforcing, against the work's
192 | users, your or third parties' legal rights to forbid circumvention of
193 | technological measures.
194 |
195 | 4. Conveying Verbatim Copies.
196 |
197 | You may convey verbatim copies of the Program's source code as you
198 | receive it, in any medium, provided that you conspicuously and
199 | appropriately publish on each copy an appropriate copyright notice;
200 | keep intact all notices stating that this License and any
201 | non-permissive terms added in accord with section 7 apply to the code;
202 | keep intact all notices of the absence of any warranty; and give all
203 | recipients a copy of this License along with the Program.
204 |
205 | You may charge any price or no price for each copy that you convey,
206 | and you may offer support or warranty protection for a fee.
207 |
208 | 5. Conveying Modified Source Versions.
209 |
210 | You may convey a work based on the Program, or the modifications to
211 | produce it from the Program, in the form of source code under the
212 | terms of section 4, provided that you also meet all of these conditions:
213 |
214 | a) The work must carry prominent notices stating that you modified
215 | it, and giving a relevant date.
216 |
217 | b) The work must carry prominent notices stating that it is
218 | released under this License and any conditions added under section
219 | 7. This requirement modifies the requirement in section 4 to
220 | "keep intact all notices".
221 |
222 | c) You must license the entire work, as a whole, under this
223 | License to anyone who comes into possession of a copy. This
224 | License will therefore apply, along with any applicable section 7
225 | additional terms, to the whole of the work, and all its parts,
226 | regardless of how they are packaged. This License gives no
227 | permission to license the work in any other way, but it does not
228 | invalidate such permission if you have separately received it.
229 |
230 | d) If the work has interactive user interfaces, each must display
231 | Appropriate Legal Notices; however, if the Program has interactive
232 | interfaces that do not display Appropriate Legal Notices, your
233 | work need not make them do so.
234 |
235 | A compilation of a covered work with other separate and independent
236 | works, which are not by their nature extensions of the covered work,
237 | and which are not combined with it such as to form a larger program,
238 | in or on a volume of a storage or distribution medium, is called an
239 | "aggregate" if the compilation and its resulting copyright are not
240 | used to limit the access or legal rights of the compilation's users
241 | beyond what the individual works permit. Inclusion of a covered work
242 | in an aggregate does not cause this License to apply to the other
243 | parts of the aggregate.
244 |
245 | 6. Conveying Non-Source Forms.
246 |
247 | You may convey a covered work in object code form under the terms
248 | of sections 4 and 5, provided that you also convey the
249 | machine-readable Corresponding Source under the terms of this License,
250 | in one of these ways:
251 |
252 | a) Convey the object code in, or embodied in, a physical product
253 | (including a physical distribution medium), accompanied by the
254 | Corresponding Source fixed on a durable physical medium
255 | customarily used for software interchange.
256 |
257 | b) Convey the object code in, or embodied in, a physical product
258 | (including a physical distribution medium), accompanied by a
259 | written offer, valid for at least three years and valid for as
260 | long as you offer spare parts or customer support for that product
261 | model, to give anyone who possesses the object code either (1) a
262 | copy of the Corresponding Source for all the software in the
263 | product that is covered by this License, on a durable physical
264 | medium customarily used for software interchange, for a price no
265 | more than your reasonable cost of physically performing this
266 | conveying of source, or (2) access to copy the
267 | Corresponding Source from a network server at no charge.
268 |
269 | c) Convey individual copies of the object code with a copy of the
270 | written offer to provide the Corresponding Source. This
271 | alternative is allowed only occasionally and noncommercially, and
272 | only if you received the object code with such an offer, in accord
273 | with subsection 6b.
274 |
275 | d) Convey the object code by offering access from a designated
276 | place (gratis or for a charge), and offer equivalent access to the
277 | Corresponding Source in the same way through the same place at no
278 | further charge. You need not require recipients to copy the
279 | Corresponding Source along with the object code. If the place to
280 | copy the object code is a network server, the Corresponding Source
281 | may be on a different server (operated by you or a third party)
282 | that supports equivalent copying facilities, provided you maintain
283 | clear directions next to the object code saying where to find the
284 | Corresponding Source. Regardless of what server hosts the
285 | Corresponding Source, you remain obligated to ensure that it is
286 | available for as long as needed to satisfy these requirements.
287 |
288 | e) Convey the object code using peer-to-peer transmission, provided
289 | you inform other peers where the object code and Corresponding
290 | Source of the work are being offered to the general public at no
291 | charge under subsection 6d.
292 |
293 | A separable portion of the object code, whose source code is excluded
294 | from the Corresponding Source as a System Library, need not be
295 | included in conveying the object code work.
296 |
297 | A "User Product" is either (1) a "consumer product", which means any
298 | tangible personal property which is normally used for personal, family,
299 | or household purposes, or (2) anything designed or sold for incorporation
300 | into a dwelling. In determining whether a product is a consumer product,
301 | doubtful cases shall be resolved in favor of coverage. For a particular
302 | product received by a particular user, "normally used" refers to a
303 | typical or common use of that class of product, regardless of the status
304 | of the particular user or of the way in which the particular user
305 | actually uses, or expects or is expected to use, the product. A product
306 | is a consumer product regardless of whether the product has substantial
307 | commercial, industrial or non-consumer uses, unless such uses represent
308 | the only significant mode of use of the product.
309 |
310 | "Installation Information" for a User Product means any methods,
311 | procedures, authorization keys, or other information required to install
312 | and execute modified versions of a covered work in that User Product from
313 | a modified version of its Corresponding Source. The information must
314 | suffice to ensure that the continued functioning of the modified object
315 | code is in no case prevented or interfered with solely because
316 | modification has been made.
317 |
318 | If you convey an object code work under this section in, or with, or
319 | specifically for use in, a User Product, and the conveying occurs as
320 | part of a transaction in which the right of possession and use of the
321 | User Product is transferred to the recipient in perpetuity or for a
322 | fixed term (regardless of how the transaction is characterized), the
323 | Corresponding Source conveyed under this section must be accompanied
324 | by the Installation Information. But this requirement does not apply
325 | if neither you nor any third party retains the ability to install
326 | modified object code on the User Product (for example, the work has
327 | been installed in ROM).
328 |
329 | The requirement to provide Installation Information does not include a
330 | requirement to continue to provide support service, warranty, or updates
331 | for a work that has been modified or installed by the recipient, or for
332 | the User Product in which it has been modified or installed. Access to a
333 | network may be denied when the modification itself materially and
334 | adversely affects the operation of the network or violates the rules and
335 | protocols for communication across the network.
336 |
337 | Corresponding Source conveyed, and Installation Information provided,
338 | in accord with this section must be in a format that is publicly
339 | documented (and with an implementation available to the public in
340 | source code form), and must require no special password or key for
341 | unpacking, reading or copying.
342 |
343 | 7. Additional Terms.
344 |
345 | "Additional permissions" are terms that supplement the terms of this
346 | License by making exceptions from one or more of its conditions.
347 | Additional permissions that are applicable to the entire Program shall
348 | be treated as though they were included in this License, to the extent
349 | that they are valid under applicable law. If additional permissions
350 | apply only to part of the Program, that part may be used separately
351 | under those permissions, but the entire Program remains governed by
352 | this License without regard to the additional permissions.
353 |
354 | When you convey a copy of a covered work, you may at your option
355 | remove any additional permissions from that copy, or from any part of
356 | it. (Additional permissions may be written to require their own
357 | removal in certain cases when you modify the work.) You may place
358 | additional permissions on material, added by you to a covered work,
359 | for which you have or can give appropriate copyright permission.
360 |
361 | Notwithstanding any other provision of this License, for material you
362 | add to a covered work, you may (if authorized by the copyright holders of
363 | that material) supplement the terms of this License with terms:
364 |
365 | a) Disclaiming warranty or limiting liability differently from the
366 | terms of sections 15 and 16 of this License; or
367 |
368 | b) Requiring preservation of specified reasonable legal notices or
369 | author attributions in that material or in the Appropriate Legal
370 | Notices displayed by works containing it; or
371 |
372 | c) Prohibiting misrepresentation of the origin of that material, or
373 | requiring that modified versions of such material be marked in
374 | reasonable ways as different from the original version; or
375 |
376 | d) Limiting the use for publicity purposes of names of licensors or
377 | authors of the material; or
378 |
379 | e) Declining to grant rights under trademark law for use of some
380 | trade names, trademarks, or service marks; or
381 |
382 | f) Requiring indemnification of licensors and authors of that
383 | material by anyone who conveys the material (or modified versions of
384 | it) with contractual assumptions of liability to the recipient, for
385 | any liability that these contractual assumptions directly impose on
386 | those licensors and authors.
387 |
388 | All other non-permissive additional terms are considered "further
389 | restrictions" within the meaning of section 10. If the Program as you
390 | received it, or any part of it, contains a notice stating that it is
391 | governed by this License along with a term that is a further
392 | restriction, you may remove that term. If a license document contains
393 | a further restriction but permits relicensing or conveying under this
394 | License, you may add to a covered work material governed by the terms
395 | of that license document, provided that the further restriction does
396 | not survive such relicensing or conveying.
397 |
398 | If you add terms to a covered work in accord with this section, you
399 | must place, in the relevant source files, a statement of the
400 | additional terms that apply to those files, or a notice indicating
401 | where to find the applicable terms.
402 |
403 | Additional terms, permissive or non-permissive, may be stated in the
404 | form of a separately written license, or stated as exceptions;
405 | the above requirements apply either way.
406 |
407 | 8. Termination.
408 |
409 | You may not propagate or modify a covered work except as expressly
410 | provided under this License. Any attempt otherwise to propagate or
411 | modify it is void, and will automatically terminate your rights under
412 | this License (including any patent licenses granted under the third
413 | paragraph of section 11).
414 |
415 | However, if you cease all violation of this License, then your
416 | license from a particular copyright holder is reinstated (a)
417 | provisionally, unless and until the copyright holder explicitly and
418 | finally terminates your license, and (b) permanently, if the copyright
419 | holder fails to notify you of the violation by some reasonable means
420 | prior to 60 days after the cessation.
421 |
422 | Moreover, your license from a particular copyright holder is
423 | reinstated permanently if the copyright holder notifies you of the
424 | violation by some reasonable means, this is the first time you have
425 | received notice of violation of this License (for any work) from that
426 | copyright holder, and you cure the violation prior to 30 days after
427 | your receipt of the notice.
428 |
429 | Termination of your rights under this section does not terminate the
430 | licenses of parties who have received copies or rights from you under
431 | this License. If your rights have been terminated and not permanently
432 | reinstated, you do not qualify to receive new licenses for the same
433 | material under section 10.
434 |
435 | 9. Acceptance Not Required for Having Copies.
436 |
437 | You are not required to accept this License in order to receive or
438 | run a copy of the Program. Ancillary propagation of a covered work
439 | occurring solely as a consequence of using peer-to-peer transmission
440 | to receive a copy likewise does not require acceptance. However,
441 | nothing other than this License grants you permission to propagate or
442 | modify any covered work. These actions infringe copyright if you do
443 | not accept this License. Therefore, by modifying or propagating a
444 | covered work, you indicate your acceptance of this License to do so.
445 |
446 | 10. Automatic Licensing of Downstream Recipients.
447 |
448 | Each time you convey a covered work, the recipient automatically
449 | receives a license from the original licensors, to run, modify and
450 | propagate that work, subject to this License. You are not responsible
451 | for enforcing compliance by third parties with this License.
452 |
453 | An "entity transaction" is a transaction transferring control of an
454 | organization, or substantially all assets of one, or subdividing an
455 | organization, or merging organizations. If propagation of a covered
456 | work results from an entity transaction, each party to that
457 | transaction who receives a copy of the work also receives whatever
458 | licenses to the work the party's predecessor in interest had or could
459 | give under the previous paragraph, plus a right to possession of the
460 | Corresponding Source of the work from the predecessor in interest, if
461 | the predecessor has it or can get it with reasonable efforts.
462 |
463 | You may not impose any further restrictions on the exercise of the
464 | rights granted or affirmed under this License. For example, you may
465 | not impose a license fee, royalty, or other charge for exercise of
466 | rights granted under this License, and you may not initiate litigation
467 | (including a cross-claim or counterclaim in a lawsuit) alleging that
468 | any patent claim is infringed by making, using, selling, offering for
469 | sale, or importing the Program or any portion of it.
470 |
471 | 11. Patents.
472 |
473 | A "contributor" is a copyright holder who authorizes use under this
474 | License of the Program or a work on which the Program is based. The
475 | work thus licensed is called the contributor's "contributor version".
476 |
477 | A contributor's "essential patent claims" are all patent claims
478 | owned or controlled by the contributor, whether already acquired or
479 | hereafter acquired, that would be infringed by some manner, permitted
480 | by this License, of making, using, or selling its contributor version,
481 | but do not include claims that would be infringed only as a
482 | consequence of further modification of the contributor version. For
483 | purposes of this definition, "control" includes the right to grant
484 | patent sublicenses in a manner consistent with the requirements of
485 | this License.
486 |
487 | Each contributor grants you a non-exclusive, worldwide, royalty-free
488 | patent license under the contributor's essential patent claims, to
489 | make, use, sell, offer for sale, import and otherwise run, modify and
490 | propagate the contents of its contributor version.
491 |
492 | In the following three paragraphs, a "patent license" is any express
493 | agreement or commitment, however denominated, not to enforce a patent
494 | (such as an express permission to practice a patent or covenant not to
495 | sue for patent infringement). To "grant" such a patent license to a
496 | party means to make such an agreement or commitment not to enforce a
497 | patent against the party.
498 |
499 | If you convey a covered work, knowingly relying on a patent license,
500 | and the Corresponding Source of the work is not available for anyone
501 | to copy, free of charge and under the terms of this License, through a
502 | publicly available network server or other readily accessible means,
503 | then you must either (1) cause the Corresponding Source to be so
504 | available, or (2) arrange to deprive yourself of the benefit of the
505 | patent license for this particular work, or (3) arrange, in a manner
506 | consistent with the requirements of this License, to extend the patent
507 | license to downstream recipients. "Knowingly relying" means you have
508 | actual knowledge that, but for the patent license, your conveying the
509 | covered work in a country, or your recipient's use of the covered work
510 | in a country, would infringe one or more identifiable patents in that
511 | country that you have reason to believe are valid.
512 |
513 | If, pursuant to or in connection with a single transaction or
514 | arrangement, you convey, or propagate by procuring conveyance of, a
515 | covered work, and grant a patent license to some of the parties
516 | receiving the covered work authorizing them to use, propagate, modify
517 | or convey a specific copy of the covered work, then the patent license
518 | you grant is automatically extended to all recipients of the covered
519 | work and works based on it.
520 |
521 | A patent license is "discriminatory" if it does not include within
522 | the scope of its coverage, prohibits the exercise of, or is
523 | conditioned on the non-exercise of one or more of the rights that are
524 | specifically granted under this License. You may not convey a covered
525 | work if you are a party to an arrangement with a third party that is
526 | in the business of distributing software, under which you make payment
527 | to the third party based on the extent of your activity of conveying
528 | the work, and under which the third party grants, to any of the
529 | parties who would receive the covered work from you, a discriminatory
530 | patent license (a) in connection with copies of the covered work
531 | conveyed by you (or copies made from those copies), or (b) primarily
532 | for and in connection with specific products or compilations that
533 | contain the covered work, unless you entered into that arrangement,
534 | or that patent license was granted, prior to 28 March 2007.
535 |
536 | Nothing in this License shall be construed as excluding or limiting
537 | any implied license or other defenses to infringement that may
538 | otherwise be available to you under applicable patent law.
539 |
540 | 12. No Surrender of Others' Freedom.
541 |
542 | If conditions are imposed on you (whether by court order, agreement or
543 | otherwise) that contradict the conditions of this License, they do not
544 | excuse you from the conditions of this License. If you cannot convey a
545 | covered work so as to satisfy simultaneously your obligations under this
546 | License and any other pertinent obligations, then as a consequence you may
547 | not convey it at all. For example, if you agree to terms that obligate you
548 | to collect a royalty for further conveying from those to whom you convey
549 | the Program, the only way you could satisfy both those terms and this
550 | License would be to refrain entirely from conveying the Program.
551 |
552 | 13. Use with the GNU Affero General Public License.
553 |
554 | Notwithstanding any other provision of this License, you have
555 | permission to link or combine any covered work with a work licensed
556 | under version 3 of the GNU Affero General Public License into a single
557 | combined work, and to convey the resulting work. The terms of this
558 | License will continue to apply to the part which is the covered work,
559 | but the special requirements of the GNU Affero General Public License,
560 | section 13, concerning interaction through a network will apply to the
561 | combination as such.
562 |
563 | 14. Revised Versions of this License.
564 |
565 | The Free Software Foundation may publish revised and/or new versions of
566 | the GNU General Public License from time to time. Such new versions will
567 | be similar in spirit to the present version, but may differ in detail to
568 | address new problems or concerns.
569 |
570 | Each version is given a distinguishing version number. If the
571 | Program specifies that a certain numbered version of the GNU General
572 | Public License "or any later version" applies to it, you have the
573 | option of following the terms and conditions either of that numbered
574 | version or of any later version published by the Free Software
575 | Foundation. If the Program does not specify a version number of the
576 | GNU General Public License, you may choose any version ever published
577 | by the Free Software Foundation.
578 |
579 | If the Program specifies that a proxy can decide which future
580 | versions of the GNU General Public License can be used, that proxy's
581 | public statement of acceptance of a version permanently authorizes you
582 | to choose that version for the Program.
583 |
584 | Later license versions may give you additional or different
585 | permissions. However, no additional obligations are imposed on any
586 | author or copyright holder as a result of your choosing to follow a
587 | later version.
588 |
589 | 15. Disclaimer of Warranty.
590 |
591 | THERE IS NO WARRANTY FOR THE PROGRAM, TO THE EXTENT PERMITTED BY
592 | APPLICABLE LAW. EXCEPT WHEN OTHERWISE STATED IN WRITING THE COPYRIGHT
593 | HOLDERS AND/OR OTHER PARTIES PROVIDE THE PROGRAM "AS IS" WITHOUT WARRANTY
594 | OF ANY KIND, EITHER EXPRESSED OR IMPLIED, INCLUDING, BUT NOT LIMITED TO,
595 | THE IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR
596 | PURPOSE. THE ENTIRE RISK AS TO THE QUALITY AND PERFORMANCE OF THE PROGRAM
597 | IS WITH YOU. SHOULD THE PROGRAM PROVE DEFECTIVE, YOU ASSUME THE COST OF
598 | ALL NECESSARY SERVICING, REPAIR OR CORRECTION.
599 |
600 | 16. Limitation of Liability.
601 |
602 | IN NO EVENT UNLESS REQUIRED BY APPLICABLE LAW OR AGREED TO IN WRITING
603 | WILL ANY COPYRIGHT HOLDER, OR ANY OTHER PARTY WHO MODIFIES AND/OR CONVEYS
604 | THE PROGRAM AS PERMITTED ABOVE, BE LIABLE TO YOU FOR DAMAGES, INCLUDING ANY
605 | GENERAL, SPECIAL, INCIDENTAL OR CONSEQUENTIAL DAMAGES ARISING OUT OF THE
606 | USE OR INABILITY TO USE THE PROGRAM (INCLUDING BUT NOT LIMITED TO LOSS OF
607 | DATA OR DATA BEING RENDERED INACCURATE OR LOSSES SUSTAINED BY YOU OR THIRD
608 | PARTIES OR A FAILURE OF THE PROGRAM TO OPERATE WITH ANY OTHER PROGRAMS),
609 | EVEN IF SUCH HOLDER OR OTHER PARTY HAS BEEN ADVISED OF THE POSSIBILITY OF
610 | SUCH DAMAGES.
611 |
612 | 17. Interpretation of Sections 15 and 16.
613 |
614 | If the disclaimer of warranty and limitation of liability provided
615 | above cannot be given local legal effect according to their terms,
616 | reviewing courts shall apply local law that most closely approximates
617 | an absolute waiver of all civil liability in connection with the
618 | Program, unless a warranty or assumption of liability accompanies a
619 | copy of the Program in return for a fee.
620 |
621 | END OF TERMS AND CONDITIONS
622 |
623 | How to Apply These Terms to Your New Programs
624 |
625 | If you develop a new program, and you want it to be of the greatest
626 | possible use to the public, the best way to achieve this is to make it
627 | free software which everyone can redistribute and change under these terms.
628 |
629 | To do so, attach the following notices to the program. It is safest
630 | to attach them to the start of each source file to most effectively
631 | state the exclusion of warranty; and each file should have at least
632 | the "copyright" line and a pointer to where the full notice is found.
633 |
634 |
635 | Copyright (C)
636 |
637 | This program is free software: you can redistribute it and/or modify
638 | it under the terms of the GNU General Public License as published by
639 | the Free Software Foundation, either version 3 of the License, or
640 | (at your option) any later version.
641 |
642 | This program is distributed in the hope that it will be useful,
643 | but WITHOUT ANY WARRANTY; without even the implied warranty of
644 | MERCHANTABILITY or FITNESS FOR A PARTICULAR PURPOSE. See the
645 | GNU General Public License for more details.
646 |
647 | You should have received a copy of the GNU General Public License
648 | along with this program. If not, see .
649 |
650 | Also add information on how to contact you by electronic and paper mail.
651 |
652 | If the program does terminal interaction, make it output a short
653 | notice like this when it starts in an interactive mode:
654 |
655 | Copyright (C)
656 | This program comes with ABSOLUTELY NO WARRANTY; for details type `show w'.
657 | This is free software, and you are welcome to redistribute it
658 | under certain conditions; type `show c' for details.
659 |
660 | The hypothetical commands `show w' and `show c' should show the appropriate
661 | parts of the General Public License. Of course, your program's commands
662 | might be different; for a GUI interface, you would use an "about box".
663 |
664 | You should also get your employer (if you work as a programmer) or school,
665 | if any, to sign a "copyright disclaimer" for the program, if necessary.
666 | For more information on this, and how to apply and follow the GNU GPL, see
667 | .
668 |
669 | The GNU General Public License does not permit incorporating your program
670 | into proprietary programs. If your program is a subroutine library, you
671 | may consider it more useful to permit linking proprietary applications with
672 | the library. If this is what you want to do, use the GNU Lesser General
673 | Public License instead of this License. But first, please read
674 | .
675 |
--------------------------------------------------------------------------------
248 | # MAGIC
249 | # MAGIC The silver `customer_silver` table will contains the most up to date view. It'll be a replicate of the original table.
250 | # MAGIC
251 | # MAGIC To propagate the `Apply Changes Into` operations downstream to the `Silver` layer, we must explicitly enable the feature in pipeline by adding and enabling the applyChanges configuration to the DLT pipeline settings.
252 |
253 | # COMMAND ----------
254 |
255 | # DBTITLE 1,Delete unwanted clients records - Silver Table - DLT Python
256 | """
257 | ##Create the target table
258 | """
259 |
260 | dlt.create_streaming_live_table(name="customer_silver",
261 | comment="Clean, merged customers",
262 | table_properties={
263 | "quality": "silver"
264 | }
265 | )
266 |
267 | # COMMAND ----------
268 |
269 | """
270 | ##APPLY CHANGES the target table
271 | """
272 |
273 | dlt.apply_changes(
274 | target = "customer_silver", #The customer table being materilized
275 | source = "customer_bronze_clean_v", #the incoming CDC
276 | keys = ["id"], #Primary key to match the rows to upsert/delete
277 | sequence_by = col("operation_date"), #deduplicate by operation date getting the most recent value
278 | apply_as_deletes = expr("operation = 'DELETE'"), #DELETE condition
279 | except_column_list = ["operation", "operation_date", "_rescued_data"], # drop metadata columns
280 | stored_as_scd_type = 2
281 | )
282 |
283 | # COMMAND ----------
284 |
285 | # MAGIC %md
286 | # MAGIC
287 | # MAGIC Next step, create DLT pipeline, add a path to this notebook and **add configuration with enabling applychanges to true**.
288 |
--------------------------------------------------------------------------------
/LICENSE:
--------------------------------------------------------------------------------
1 | GNU GENERAL PUBLIC LICENSE
2 | Version 3, 29 June 2007
3 |
4 | Copyright (C) 2007 Free Software Foundation, Inc.
5 | Everyone is permitted to copy and distribute verbatim copies
6 | of this license document, but changing it is not allowed.
7 |
8 | Preamble
9 |
10 | The GNU General Public License is a free, copyleft license for
11 | software and other kinds of works.
12 |
13 | The licenses for most software and other practical works are designed
14 | to take away your freedom to share and change the works. By contrast,
15 | the GNU General Public License is intended to guarantee your freedom to
16 | share and change all versions of a program--to make sure it remains free
17 | software for all its users. We, the Free Software Foundation, use the
18 | GNU General Public License for most of our software; it applies also to
19 | any other work released this way by its authors. You can apply it to
20 | your programs, too.
21 |
22 | When we speak of free software, we are referring to freedom, not
23 | price. Our General Public Licenses are designed to make sure that you
24 | have the freedom to distribute copies of free software (and charge for
25 | them if you wish), that you receive source code or can get it if you
26 | want it, that you can change the software or use pieces of it in new
27 | free programs, and that you know you can do these things.
28 |
29 | To protect your rights, we need to prevent others from denying you
30 | these rights or asking you to surrender the rights. Therefore, you have
31 | certain responsibilities if you distribute copies of the software, or if
32 | you modify it: responsibilities to respect the freedom of others.
33 |
34 | For example, if you distribute copies of such a program, whether
35 | gratis or for a fee, you must pass on to the recipients the same
36 | freedoms that you received. You must make sure that they, too, receive
37 | or can get the source code. And you must show them these terms so they
38 | know their rights.
39 |
40 | Developers that use the GNU GPL protect your rights with two steps:
41 | (1) assert copyright on the software, and (2) offer you this License
42 | giving you legal permission to copy, distribute and/or modify it.
43 |
44 | For the developers' and authors' protection, the GPL clearly explains
45 | that there is no warranty for this free software. For both users' and
46 | authors' sake, the GPL requires that modified versions be marked as
47 | changed, so that their problems will not be attributed erroneously to
48 | authors of previous versions.
49 |
50 | Some devices are designed to deny users access to install or run
51 | modified versions of the software inside them, although the manufacturer
52 | can do so. This is fundamentally incompatible with the aim of
53 | protecting users' freedom to change the software. The systematic
54 | pattern of such abuse occurs in the area of products for individuals to
55 | use, which is precisely where it is most unacceptable. Therefore, we
56 | have designed this version of the GPL to prohibit the practice for those
57 | products. If such problems arise substantially in other domains, we
58 | stand ready to extend this provision to those domains in future versions
59 | of the GPL, as needed to protect the freedom of users.
60 |
61 | Finally, every program is threatened constantly by software patents.
62 | States should not allow patents to restrict development and use of
63 | software on general-purpose computers, but in those that do, we wish to
64 | avoid the special danger that patents applied to a free program could
65 | make it effectively proprietary. To prevent this, the GPL assures that
66 | patents cannot be used to render the program non-free.
67 |
68 | The precise terms and conditions for copying, distribution and
69 | modification follow.
70 |
71 | TERMS AND CONDITIONS
72 |
73 | 0. Definitions.
74 |
75 | "This License" refers to version 3 of the GNU General Public License.
76 |
77 | "Copyright" also means copyright-like laws that apply to other kinds of
78 | works, such as semiconductor masks.
79 |
80 | "The Program" refers to any copyrightable work licensed under this
81 | License. Each licensee is addressed as "you". "Licensees" and
82 | "recipients" may be individuals or organizations.
83 |
84 | To "modify" a work means to copy from or adapt all or part of the work
85 | in a fashion requiring copyright permission, other than the making of an
86 | exact copy. The resulting work is called a "modified version" of the
87 | earlier work or a work "based on" the earlier work.
88 |
89 | A "covered work" means either the unmodified Program or a work based
90 | on the Program.
91 |
92 | To "propagate" a work means to do anything with it that, without
93 | permission, would make you directly or secondarily liable for
94 | infringement under applicable copyright law, except executing it on a
95 | computer or modifying a private copy. Propagation includes copying,
96 | distribution (with or without modification), making available to the
97 | public, and in some countries other activities as well.
98 |
99 | To "convey" a work means any kind of propagation that enables other
100 | parties to make or receive copies. Mere interaction with a user through
101 | a computer network, with no transfer of a copy, is not conveying.
102 |
103 | An interactive user interface displays "Appropriate Legal Notices"
104 | to the extent that it includes a convenient and prominently visible
105 | feature that (1) displays an appropriate copyright notice, and (2)
106 | tells the user that there is no warranty for the work (except to the
107 | extent that warranties are provided), that licensees may convey the
108 | work under this License, and how to view a copy of this License. If
109 | the interface presents a list of user commands or options, such as a
110 | menu, a prominent item in the list meets this criterion.
111 |
112 | 1. Source Code.
113 |
114 | The "source code" for a work means the preferred form of the work
115 | for making modifications to it. "Object code" means any non-source
116 | form of a work.
117 |
118 | A "Standard Interface" means an interface that either is an official
119 | standard defined by a recognized standards body, or, in the case of
120 | interfaces specified for a particular programming language, one that
121 | is widely used among developers working in that language.
122 |
123 | The "System Libraries" of an executable work include anything, other
124 | than the work as a whole, that (a) is included in the normal form of
125 | packaging a Major Component, but which is not part of that Major
126 | Component, and (b) serves only to enable use of the work with that
127 | Major Component, or to implement a Standard Interface for which an
128 | implementation is available to the public in source code form. A
129 | "Major Component", in this context, means a major essential component
130 | (kernel, window system, and so on) of the specific operating system
131 | (if any) on which the executable work runs, or a compiler used to
132 | produce the work, or an object code interpreter used to run it.
133 |
134 | The "Corresponding Source" for a work in object code form means all
135 | the source code needed to generate, install, and (for an executable
136 | work) run the object code and to modify the work, including scripts to
137 | control those activities. However, it does not include the work's
138 | System Libraries, or general-purpose tools or generally available free
139 | programs which are used unmodified in performing those activities but
140 | which are not part of the work. For example, Corresponding Source
141 | includes interface definition files associated with source files for
142 | the work, and the source code for shared libraries and dynamically
143 | linked subprograms that the work is specifically designed to require,
144 | such as by intimate data communication or control flow between those
145 | subprograms and other parts of the work.
146 |
147 | The Corresponding Source need not include anything that users
148 | can regenerate automatically from other parts of the Corresponding
149 | Source.
150 |
151 | The Corresponding Source for a work in source code form is that
152 | same work.
153 |
154 | 2. Basic Permissions.
155 |
156 | All rights granted under this License are granted for the term of
157 | copyright on the Program, and are irrevocable provided the stated
158 | conditions are met. This License explicitly affirms your unlimited
159 | permission to run the unmodified Program. The output from running a
160 | covered work is covered by this License only if the output, given its
161 | content, constitutes a covered work. This License acknowledges your
162 | rights of fair use or other equivalent, as provided by copyright law.
163 |
164 | You may make, run and propagate covered works that you do not
165 | convey, without conditions so long as your license otherwise remains
166 | in force. You may convey covered works to others for the sole purpose
167 | of having them make modifications exclusively for you, or provide you
168 | with facilities for running those works, provided that you comply with
169 | the terms of this License in conveying all material for which you do
170 | not control copyright. Those thus making or running the covered works
171 | for you must do so exclusively on your behalf, under your direction
172 | and control, on terms that prohibit them from making any copies of
173 | your copyrighted material outside their relationship with you.
174 |
175 | Conveying under any other circumstances is permitted solely under
176 | the conditions stated below. Sublicensing is not allowed; section 10
177 | makes it unnecessary.
178 |
179 | 3. Protecting Users' Legal Rights From Anti-Circumvention Law.
180 |
181 | No covered work shall be deemed part of an effective technological
182 | measure under any applicable law fulfilling obligations under article
183 | 11 of the WIPO copyright treaty adopted on 20 December 1996, or
184 | similar laws prohibiting or restricting circumvention of such
185 | measures.
186 |
187 | When you convey a covered work, you waive any legal power to forbid
188 | circumvention of technological measures to the extent such circumvention
189 | is effected by exercising rights under this License with respect to
190 | the covered work, and you disclaim any intention to limit operation or
191 | modification of the work as a means of enforcing, against the work's
192 | users, your or third parties' legal rights to forbid circumvention of
193 | technological measures.
194 |
195 | 4. Conveying Verbatim Copies.
196 |
197 | You may convey verbatim copies of the Program's source code as you
198 | receive it, in any medium, provided that you conspicuously and
199 | appropriately publish on each copy an appropriate copyright notice;
200 | keep intact all notices stating that this License and any
201 | non-permissive terms added in accord with section 7 apply to the code;
202 | keep intact all notices of the absence of any warranty; and give all
203 | recipients a copy of this License along with the Program.
204 |
205 | You may charge any price or no price for each copy that you convey,
206 | and you may offer support or warranty protection for a fee.
207 |
208 | 5. Conveying Modified Source Versions.
209 |
210 | You may convey a work based on the Program, or the modifications to
211 | produce it from the Program, in the form of source code under the
212 | terms of section 4, provided that you also meet all of these conditions:
213 |
214 | a) The work must carry prominent notices stating that you modified
215 | it, and giving a relevant date.
216 |
217 | b) The work must carry prominent notices stating that it is
218 | released under this License and any conditions added under section
219 | 7. This requirement modifies the requirement in section 4 to
220 | "keep intact all notices".
221 |
222 | c) You must license the entire work, as a whole, under this
223 | License to anyone who comes into possession of a copy. This
224 | License will therefore apply, along with any applicable section 7
225 | additional terms, to the whole of the work, and all its parts,
226 | regardless of how they are packaged. This License gives no
227 | permission to license the work in any other way, but it does not
228 | invalidate such permission if you have separately received it.
229 |
230 | d) If the work has interactive user interfaces, each must display
231 | Appropriate Legal Notices; however, if the Program has interactive
232 | interfaces that do not display Appropriate Legal Notices, your
233 | work need not make them do so.
234 |
235 | A compilation of a covered work with other separate and independent
236 | works, which are not by their nature extensions of the covered work,
237 | and which are not combined with it such as to form a larger program,
238 | in or on a volume of a storage or distribution medium, is called an
239 | "aggregate" if the compilation and its resulting copyright are not
240 | used to limit the access or legal rights of the compilation's users
241 | beyond what the individual works permit. Inclusion of a covered work
242 | in an aggregate does not cause this License to apply to the other
243 | parts of the aggregate.
244 |
245 | 6. Conveying Non-Source Forms.
246 |
247 | You may convey a covered work in object code form under the terms
248 | of sections 4 and 5, provided that you also convey the
249 | machine-readable Corresponding Source under the terms of this License,
250 | in one of these ways:
251 |
252 | a) Convey the object code in, or embodied in, a physical product
253 | (including a physical distribution medium), accompanied by the
254 | Corresponding Source fixed on a durable physical medium
255 | customarily used for software interchange.
256 |
257 | b) Convey the object code in, or embodied in, a physical product
258 | (including a physical distribution medium), accompanied by a
259 | written offer, valid for at least three years and valid for as
260 | long as you offer spare parts or customer support for that product
261 | model, to give anyone who possesses the object code either (1) a
262 | copy of the Corresponding Source for all the software in the
263 | product that is covered by this License, on a durable physical
264 | medium customarily used for software interchange, for a price no
265 | more than your reasonable cost of physically performing this
266 | conveying of source, or (2) access to copy the
267 | Corresponding Source from a network server at no charge.
268 |
269 | c) Convey individual copies of the object code with a copy of the
270 | written offer to provide the Corresponding Source. This
271 | alternative is allowed only occasionally and noncommercially, and
272 | only if you received the object code with such an offer, in accord
273 | with subsection 6b.
274 |
275 | d) Convey the object code by offering access from a designated
276 | place (gratis or for a charge), and offer equivalent access to the
277 | Corresponding Source in the same way through the same place at no
278 | further charge. You need not require recipients to copy the
279 | Corresponding Source along with the object code. If the place to
280 | copy the object code is a network server, the Corresponding Source
281 | may be on a different server (operated by you or a third party)
282 | that supports equivalent copying facilities, provided you maintain
283 | clear directions next to the object code saying where to find the
284 | Corresponding Source. Regardless of what server hosts the
285 | Corresponding Source, you remain obligated to ensure that it is
286 | available for as long as needed to satisfy these requirements.
287 |
288 | e) Convey the object code using peer-to-peer transmission, provided
289 | you inform other peers where the object code and Corresponding
290 | Source of the work are being offered to the general public at no
291 | charge under subsection 6d.
292 |
293 | A separable portion of the object code, whose source code is excluded
294 | from the Corresponding Source as a System Library, need not be
295 | included in conveying the object code work.
296 |
297 | A "User Product" is either (1) a "consumer product", which means any
298 | tangible personal property which is normally used for personal, family,
299 | or household purposes, or (2) anything designed or sold for incorporation
300 | into a dwelling. In determining whether a product is a consumer product,
301 | doubtful cases shall be resolved in favor of coverage. For a particular
302 | product received by a particular user, "normally used" refers to a
303 | typical or common use of that class of product, regardless of the status
304 | of the particular user or of the way in which the particular user
305 | actually uses, or expects or is expected to use, the product. A product
306 | is a consumer product regardless of whether the product has substantial
307 | commercial, industrial or non-consumer uses, unless such uses represent
308 | the only significant mode of use of the product.
309 |
310 | "Installation Information" for a User Product means any methods,
311 | procedures, authorization keys, or other information required to install
312 | and execute modified versions of a covered work in that User Product from
313 | a modified version of its Corresponding Source. The information must
314 | suffice to ensure that the continued functioning of the modified object
315 | code is in no case prevented or interfered with solely because
316 | modification has been made.
317 |
318 | If you convey an object code work under this section in, or with, or
319 | specifically for use in, a User Product, and the conveying occurs as
320 | part of a transaction in which the right of possession and use of the
321 | User Product is transferred to the recipient in perpetuity or for a
322 | fixed term (regardless of how the transaction is characterized), the
323 | Corresponding Source conveyed under this section must be accompanied
324 | by the Installation Information. But this requirement does not apply
325 | if neither you nor any third party retains the ability to install
326 | modified object code on the User Product (for example, the work has
327 | been installed in ROM).
328 |
329 | The requirement to provide Installation Information does not include a
330 | requirement to continue to provide support service, warranty, or updates
331 | for a work that has been modified or installed by the recipient, or for
332 | the User Product in which it has been modified or installed. Access to a
333 | network may be denied when the modification itself materially and
334 | adversely affects the operation of the network or violates the rules and
335 | protocols for communication across the network.
336 |
337 | Corresponding Source conveyed, and Installation Information provided,
338 | in accord with this section must be in a format that is publicly
339 | documented (and with an implementation available to the public in
340 | source code form), and must require no special password or key for
341 | unpacking, reading or copying.
342 |
343 | 7. Additional Terms.
344 |
345 | "Additional permissions" are terms that supplement the terms of this
346 | License by making exceptions from one or more of its conditions.
347 | Additional permissions that are applicable to the entire Program shall
348 | be treated as though they were included in this License, to the extent
349 | that they are valid under applicable law. If additional permissions
350 | apply only to part of the Program, that part may be used separately
351 | under those permissions, but the entire Program remains governed by
352 | this License without regard to the additional permissions.
353 |
354 | When you convey a copy of a covered work, you may at your option
355 | remove any additional permissions from that copy, or from any part of
356 | it. (Additional permissions may be written to require their own
357 | removal in certain cases when you modify the work.) You may place
358 | additional permissions on material, added by you to a covered work,
359 | for which you have or can give appropriate copyright permission.
360 |
361 | Notwithstanding any other provision of this License, for material you
362 | add to a covered work, you may (if authorized by the copyright holders of
363 | that material) supplement the terms of this License with terms:
364 |
365 | a) Disclaiming warranty or limiting liability differently from the
366 | terms of sections 15 and 16 of this License; or
367 |
368 | b) Requiring preservation of specified reasonable legal notices or
369 | author attributions in that material or in the Appropriate Legal
370 | Notices displayed by works containing it; or
371 |
372 | c) Prohibiting misrepresentation of the origin of that material, or
373 | requiring that modified versions of such material be marked in
374 | reasonable ways as different from the original version; or
375 |
376 | d) Limiting the use for publicity purposes of names of licensors or
377 | authors of the material; or
378 |
379 | e) Declining to grant rights under trademark law for use of some
380 | trade names, trademarks, or service marks; or
381 |
382 | f) Requiring indemnification of licensors and authors of that
383 | material by anyone who conveys the material (or modified versions of
384 | it) with contractual assumptions of liability to the recipient, for
385 | any liability that these contractual assumptions directly impose on
386 | those licensors and authors.
387 |
388 | All other non-permissive additional terms are considered "further
389 | restrictions" within the meaning of section 10. If the Program as you
390 | received it, or any part of it, contains a notice stating that it is
391 | governed by this License along with a term that is a further
392 | restriction, you may remove that term. If a license document contains
393 | a further restriction but permits relicensing or conveying under this
394 | License, you may add to a covered work material governed by the terms
395 | of that license document, provided that the further restriction does
396 | not survive such relicensing or conveying.
397 |
398 | If you add terms to a covered work in accord with this section, you
399 | must place, in the relevant source files, a statement of the
400 | additional terms that apply to those files, or a notice indicating
401 | where to find the applicable terms.
402 |
403 | Additional terms, permissive or non-permissive, may be stated in the
404 | form of a separately written license, or stated as exceptions;
405 | the above requirements apply either way.
406 |
407 | 8. Termination.
408 |
409 | You may not propagate or modify a covered work except as expressly
410 | provided under this License. Any attempt otherwise to propagate or
411 | modify it is void, and will automatically terminate your rights under
412 | this License (including any patent licenses granted under the third
413 | paragraph of section 11).
414 |
415 | However, if you cease all violation of this License, then your
416 | license from a particular copyright holder is reinstated (a)
417 | provisionally, unless and until the copyright holder explicitly and
418 | finally terminates your license, and (b) permanently, if the copyright
419 | holder fails to notify you of the violation by some reasonable means
420 | prior to 60 days after the cessation.
421 |
422 | Moreover, your license from a particular copyright holder is
423 | reinstated permanently if the copyright holder notifies you of the
424 | violation by some reasonable means, this is the first time you have
425 | received notice of violation of this License (for any work) from that
426 | copyright holder, and you cure the violation prior to 30 days after
427 | your receipt of the notice.
428 |
429 | Termination of your rights under this section does not terminate the
430 | licenses of parties who have received copies or rights from you under
431 | this License. If your rights have been terminated and not permanently
432 | reinstated, you do not qualify to receive new licenses for the same
433 | material under section 10.
434 |
435 | 9. Acceptance Not Required for Having Copies.
436 |
437 | You are not required to accept this License in order to receive or
438 | run a copy of the Program. Ancillary propagation of a covered work
439 | occurring solely as a consequence of using peer-to-peer transmission
440 | to receive a copy likewise does not require acceptance. However,
441 | nothing other than this License grants you permission to propagate or
442 | modify any covered work. These actions infringe copyright if you do
443 | not accept this License. Therefore, by modifying or propagating a
444 | covered work, you indicate your acceptance of this License to do so.
445 |
446 | 10. Automatic Licensing of Downstream Recipients.
447 |
448 | Each time you convey a covered work, the recipient automatically
449 | receives a license from the original licensors, to run, modify and
450 | propagate that work, subject to this License. You are not responsible
451 | for enforcing compliance by third parties with this License.
452 |
453 | An "entity transaction" is a transaction transferring control of an
454 | organization, or substantially all assets of one, or subdividing an
455 | organization, or merging organizations. If propagation of a covered
456 | work results from an entity transaction, each party to that
457 | transaction who receives a copy of the work also receives whatever
458 | licenses to the work the party's predecessor in interest had or could
459 | give under the previous paragraph, plus a right to possession of the
460 | Corresponding Source of the work from the predecessor in interest, if
461 | the predecessor has it or can get it with reasonable efforts.
462 |
463 | You may not impose any further restrictions on the exercise of the
464 | rights granted or affirmed under this License. For example, you may
465 | not impose a license fee, royalty, or other charge for exercise of
466 | rights granted under this License, and you may not initiate litigation
467 | (including a cross-claim or counterclaim in a lawsuit) alleging that
468 | any patent claim is infringed by making, using, selling, offering for
469 | sale, or importing the Program or any portion of it.
470 |
471 | 11. Patents.
472 |
473 | A "contributor" is a copyright holder who authorizes use under this
474 | License of the Program or a work on which the Program is based. The
475 | work thus licensed is called the contributor's "contributor version".
476 |
477 | A contributor's "essential patent claims" are all patent claims
478 | owned or controlled by the contributor, whether already acquired or
479 | hereafter acquired, that would be infringed by some manner, permitted
480 | by this License, of making, using, or selling its contributor version,
481 | but do not include claims that would be infringed only as a
482 | consequence of further modification of the contributor version. For
483 | purposes of this definition, "control" includes the right to grant
484 | patent sublicenses in a manner consistent with the requirements of
485 | this License.
486 |
487 | Each contributor grants you a non-exclusive, worldwide, royalty-free
488 | patent license under the contributor's essential patent claims, to
489 | make, use, sell, offer for sale, import and otherwise run, modify and
490 | propagate the contents of its contributor version.
491 |
492 | In the following three paragraphs, a "patent license" is any express
493 | agreement or commitment, however denominated, not to enforce a patent
494 | (such as an express permission to practice a patent or covenant not to
495 | sue for patent infringement). To "grant" such a patent license to a
496 | party means to make such an agreement or commitment not to enforce a
497 | patent against the party.
498 |
499 | If you convey a covered work, knowingly relying on a patent license,
500 | and the Corresponding Source of the work is not available for anyone
501 | to copy, free of charge and under the terms of this License, through a
502 | publicly available network server or other readily accessible means,
503 | then you must either (1) cause the Corresponding Source to be so
504 | available, or (2) arrange to deprive yourself of the benefit of the
505 | patent license for this particular work, or (3) arrange, in a manner
506 | consistent with the requirements of this License, to extend the patent
507 | license to downstream recipients. "Knowingly relying" means you have
508 | actual knowledge that, but for the patent license, your conveying the
509 | covered work in a country, or your recipient's use of the covered work
510 | in a country, would infringe one or more identifiable patents in that
511 | country that you have reason to believe are valid.
512 |
513 | If, pursuant to or in connection with a single transaction or
514 | arrangement, you convey, or propagate by procuring conveyance of, a
515 | covered work, and grant a patent license to some of the parties
516 | receiving the covered work authorizing them to use, propagate, modify
517 | or convey a specific copy of the covered work, then the patent license
518 | you grant is automatically extended to all recipients of the covered
519 | work and works based on it.
520 |
521 | A patent license is "discriminatory" if it does not include within
522 | the scope of its coverage, prohibits the exercise of, or is
523 | conditioned on the non-exercise of one or more of the rights that are
524 | specifically granted under this License. You may not convey a covered
525 | work if you are a party to an arrangement with a third party that is
526 | in the business of distributing software, under which you make payment
527 | to the third party based on the extent of your activity of conveying
528 | the work, and under which the third party grants, to any of the
529 | parties who would receive the covered work from you, a discriminatory
530 | patent license (a) in connection with copies of the covered work
531 | conveyed by you (or copies made from those copies), or (b) primarily
532 | for and in connection with specific products or compilations that
533 | contain the covered work, unless you entered into that arrangement,
534 | or that patent license was granted, prior to 28 March 2007.
535 |
536 | Nothing in this License shall be construed as excluding or limiting
537 | any implied license or other defenses to infringement that may
538 | otherwise be available to you under applicable patent law.
539 |
540 | 12. No Surrender of Others' Freedom.
541 |
542 | If conditions are imposed on you (whether by court order, agreement or
543 | otherwise) that contradict the conditions of this License, they do not
544 | excuse you from the conditions of this License. If you cannot convey a
545 | covered work so as to satisfy simultaneously your obligations under this
546 | License and any other pertinent obligations, then as a consequence you may
547 | not convey it at all. For example, if you agree to terms that obligate you
548 | to collect a royalty for further conveying from those to whom you convey
549 | the Program, the only way you could satisfy both those terms and this
550 | License would be to refrain entirely from conveying the Program.
551 |
552 | 13. Use with the GNU Affero General Public License.
553 |
554 | Notwithstanding any other provision of this License, you have
555 | permission to link or combine any covered work with a work licensed
556 | under version 3 of the GNU Affero General Public License into a single
557 | combined work, and to convey the resulting work. The terms of this
558 | License will continue to apply to the part which is the covered work,
559 | but the special requirements of the GNU Affero General Public License,
560 | section 13, concerning interaction through a network will apply to the
561 | combination as such.
562 |
563 | 14. Revised Versions of this License.
564 |
565 | The Free Software Foundation may publish revised and/or new versions of
566 | the GNU General Public License from time to time. Such new versions will
567 | be similar in spirit to the present version, but may differ in detail to
568 | address new problems or concerns.
569 |
570 | Each version is given a distinguishing version number. If the
571 | Program specifies that a certain numbered version of the GNU General
572 | Public License "or any later version" applies to it, you have the
573 | option of following the terms and conditions either of that numbered
574 | version or of any later version published by the Free Software
575 | Foundation. If the Program does not specify a version number of the
576 | GNU General Public License, you may choose any version ever published
577 | by the Free Software Foundation.
578 |
579 | If the Program specifies that a proxy can decide which future
580 | versions of the GNU General Public License can be used, that proxy's
581 | public statement of acceptance of a version permanently authorizes you
582 | to choose that version for the Program.
583 |
584 | Later license versions may give you additional or different
585 | permissions. However, no additional obligations are imposed on any
586 | author or copyright holder as a result of your choosing to follow a
587 | later version.
588 |
589 | 15. Disclaimer of Warranty.
590 |
591 | THERE IS NO WARRANTY FOR THE PROGRAM, TO THE EXTENT PERMITTED BY
592 | APPLICABLE LAW. EXCEPT WHEN OTHERWISE STATED IN WRITING THE COPYRIGHT
593 | HOLDERS AND/OR OTHER PARTIES PROVIDE THE PROGRAM "AS IS" WITHOUT WARRANTY
594 | OF ANY KIND, EITHER EXPRESSED OR IMPLIED, INCLUDING, BUT NOT LIMITED TO,
595 | THE IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR
596 | PURPOSE. THE ENTIRE RISK AS TO THE QUALITY AND PERFORMANCE OF THE PROGRAM
597 | IS WITH YOU. SHOULD THE PROGRAM PROVE DEFECTIVE, YOU ASSUME THE COST OF
598 | ALL NECESSARY SERVICING, REPAIR OR CORRECTION.
599 |
600 | 16. Limitation of Liability.
601 |
602 | IN NO EVENT UNLESS REQUIRED BY APPLICABLE LAW OR AGREED TO IN WRITING
603 | WILL ANY COPYRIGHT HOLDER, OR ANY OTHER PARTY WHO MODIFIES AND/OR CONVEYS
604 | THE PROGRAM AS PERMITTED ABOVE, BE LIABLE TO YOU FOR DAMAGES, INCLUDING ANY
605 | GENERAL, SPECIAL, INCIDENTAL OR CONSEQUENTIAL DAMAGES ARISING OUT OF THE
606 | USE OR INABILITY TO USE THE PROGRAM (INCLUDING BUT NOT LIMITED TO LOSS OF
607 | DATA OR DATA BEING RENDERED INACCURATE OR LOSSES SUSTAINED BY YOU OR THIRD
608 | PARTIES OR A FAILURE OF THE PROGRAM TO OPERATE WITH ANY OTHER PROGRAMS),
609 | EVEN IF SUCH HOLDER OR OTHER PARTY HAS BEEN ADVISED OF THE POSSIBILITY OF
610 | SUCH DAMAGES.
611 |
612 | 17. Interpretation of Sections 15 and 16.
613 |
614 | If the disclaimer of warranty and limitation of liability provided
615 | above cannot be given local legal effect according to their terms,
616 | reviewing courts shall apply local law that most closely approximates
617 | an absolute waiver of all civil liability in connection with the
618 | Program, unless a warranty or assumption of liability accompanies a
619 | copy of the Program in return for a fee.
620 |
621 | END OF TERMS AND CONDITIONS
622 |
623 | How to Apply These Terms to Your New Programs
624 |
625 | If you develop a new program, and you want it to be of the greatest
626 | possible use to the public, the best way to achieve this is to make it
627 | free software which everyone can redistribute and change under these terms.
628 |
629 | To do so, attach the following notices to the program. It is safest
630 | to attach them to the start of each source file to most effectively
631 | state the exclusion of warranty; and each file should have at least
632 | the "copyright" line and a pointer to where the full notice is found.
633 |
634 |
635 | Copyright (C)
636 |
637 | This program is free software: you can redistribute it and/or modify
638 | it under the terms of the GNU General Public License as published by
639 | the Free Software Foundation, either version 3 of the License, or
640 | (at your option) any later version.
641 |
642 | This program is distributed in the hope that it will be useful,
643 | but WITHOUT ANY WARRANTY; without even the implied warranty of
644 | MERCHANTABILITY or FITNESS FOR A PARTICULAR PURPOSE. See the
645 | GNU General Public License for more details.
646 |
647 | You should have received a copy of the GNU General Public License
648 | along with this program. If not, see .
649 |
650 | Also add information on how to contact you by electronic and paper mail.
651 |
652 | If the program does terminal interaction, make it output a short
653 | notice like this when it starts in an interactive mode:
654 |
655 | Copyright (C)
656 | This program comes with ABSOLUTELY NO WARRANTY; for details type `show w'.
657 | This is free software, and you are welcome to redistribute it
658 | under certain conditions; type `show c' for details.
659 |
660 | The hypothetical commands `show w' and `show c' should show the appropriate
661 | parts of the General Public License. Of course, your program's commands
662 | might be different; for a GUI interface, you would use an "about box".
663 |
664 | You should also get your employer (if you work as a programmer) or school,
665 | if any, to sign a "copyright disclaimer" for the program, if necessary.
666 | For more information on this, and how to apply and follow the GNU GPL, see
667 | .
668 |
669 | The GNU General Public License does not permit incorporating your program
670 | into proprietary programs. If your program is a subroutine library, you
671 | may consider it more useful to permit linking proprietary applications with
672 | the library. If this is what you want to do, use the GNU Lesser General
673 | Public License instead of this License. But first, please read
674 | .
675 |
--------------------------------------------------------------------------------
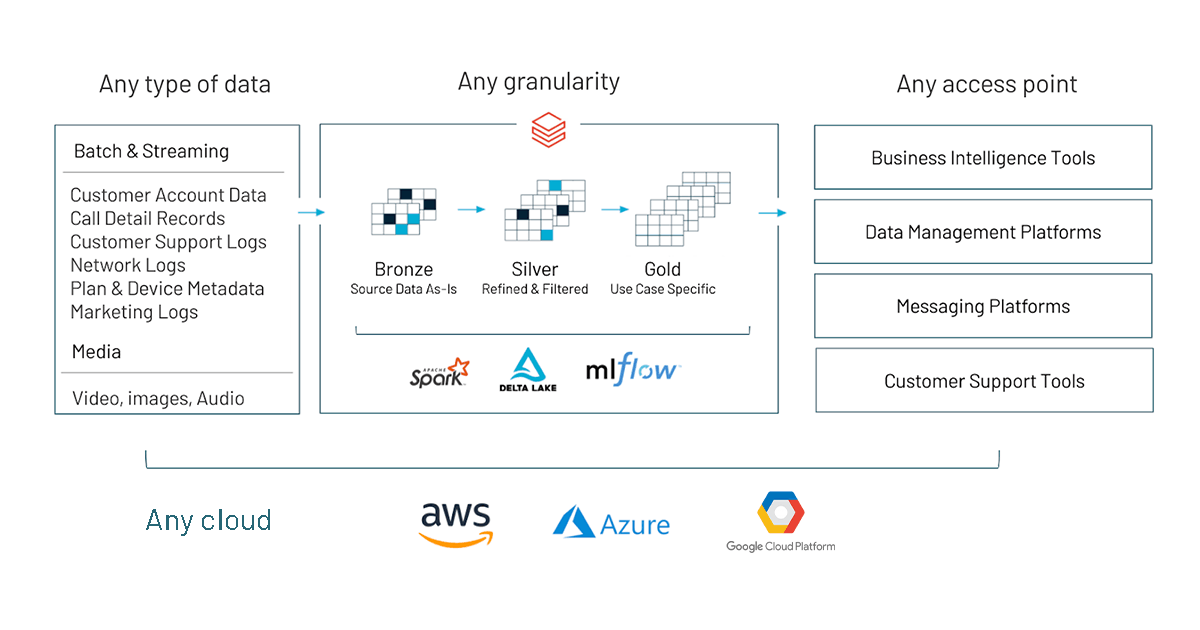 10 | # MAGIC
11 | # MAGIC See below links for more documentation:
12 | # MAGIC * [How to Process IoT Device JSON Data Using Apache Spark Datasets and DataFrames](https://databricks.com/blog/2016/03/28/how-to-process-iot-device-json-data-using-apache-spark-datasets-and-dataframes.html)
13 | # MAGIC * [Spark Structure Streaming](https://databricks.com/blog/2016/07/28/structured-streaming-in-apache-spark.html)
14 | # MAGIC * [Beyond Lambda](https://databricks.com/discover/getting-started-with-delta-lake-tech-talks/beyond-lambda-introducing-delta-architecture)
15 | # MAGIC * [Delta Lake Docs](https://docs.databricks.com/delta/index.html)
16 | # MAGIC * [Medallion Architecture](https://databricks.com/solutions/data-pipelines)
17 | # MAGIC * [Cost Savings with the Medallion Architecture](https://techcommunity.microsoft.com/t5/analytics-on-azure/how-to-reduce-infrastructure-costs-by-up-to-80-with-azure/ba-p/1820280)
18 | # MAGIC * [Change Data Capture Streams with the Medallion Architecture](https://databricks.com/blog/2021/06/09/how-to-simplify-cdc-with-delta-lakes-change-data-feed.html)
19 |
20 | # COMMAND ----------
21 |
22 | # MAGIC %md
23 | # MAGIC
24 | # MAGIC ## Schema
25 |
26 | # COMMAND ----------
27 |
28 | import time
29 | from pyspark.sql.functions import *
30 | from pyspark.sql.types import *
31 | from datetime import datetime, timezone
32 | import uuid
33 |
34 | # COMMAND ----------
35 |
36 | file_schema = (spark
37 | .read
38 | .format("csv")
39 | .option("header", True)
40 | .option("inferSchema", True)
41 | .load("/databricks-datasets/iot-stream/data-user/userData.csv")
42 | .limit(10)
43 | .schema)
44 |
45 | # COMMAND ----------
46 |
47 | print(file_schema)
48 |
49 | # COMMAND ----------
50 |
51 | # MAGIC %md
52 | # MAGIC
53 | # MAGIC ## Spark Structured Streaming
54 | # MAGIC
55 | # MAGIC
10 | # MAGIC
11 | # MAGIC See below links for more documentation:
12 | # MAGIC * [How to Process IoT Device JSON Data Using Apache Spark Datasets and DataFrames](https://databricks.com/blog/2016/03/28/how-to-process-iot-device-json-data-using-apache-spark-datasets-and-dataframes.html)
13 | # MAGIC * [Spark Structure Streaming](https://databricks.com/blog/2016/07/28/structured-streaming-in-apache-spark.html)
14 | # MAGIC * [Beyond Lambda](https://databricks.com/discover/getting-started-with-delta-lake-tech-talks/beyond-lambda-introducing-delta-architecture)
15 | # MAGIC * [Delta Lake Docs](https://docs.databricks.com/delta/index.html)
16 | # MAGIC * [Medallion Architecture](https://databricks.com/solutions/data-pipelines)
17 | # MAGIC * [Cost Savings with the Medallion Architecture](https://techcommunity.microsoft.com/t5/analytics-on-azure/how-to-reduce-infrastructure-costs-by-up-to-80-with-azure/ba-p/1820280)
18 | # MAGIC * [Change Data Capture Streams with the Medallion Architecture](https://databricks.com/blog/2021/06/09/how-to-simplify-cdc-with-delta-lakes-change-data-feed.html)
19 |
20 | # COMMAND ----------
21 |
22 | # MAGIC %md
23 | # MAGIC
24 | # MAGIC ## Schema
25 |
26 | # COMMAND ----------
27 |
28 | import time
29 | from pyspark.sql.functions import *
30 | from pyspark.sql.types import *
31 | from datetime import datetime, timezone
32 | import uuid
33 |
34 | # COMMAND ----------
35 |
36 | file_schema = (spark
37 | .read
38 | .format("csv")
39 | .option("header", True)
40 | .option("inferSchema", True)
41 | .load("/databricks-datasets/iot-stream/data-user/userData.csv")
42 | .limit(10)
43 | .schema)
44 |
45 | # COMMAND ----------
46 |
47 | print(file_schema)
48 |
49 | # COMMAND ----------
50 |
51 | # MAGIC %md
52 | # MAGIC
53 | # MAGIC ## Spark Structured Streaming
54 | # MAGIC
55 | # MAGIC 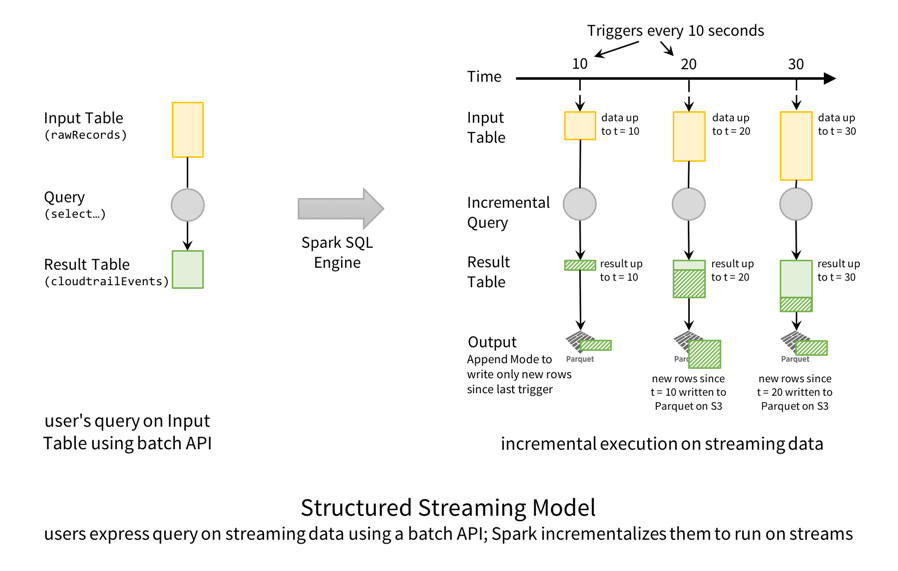 56 |
57 | # COMMAND ----------
58 |
59 | uuidUdf= udf(lambda : uuid.uuid4().hex,StringType())
60 |
61 | # Stream raw IOT Events from S3 bucket
62 | iot_event_stream = (spark
63 | .readStream
64 | .option( "maxFilesPerTrigger", 1 )
65 | .format("csv")
66 | .option("header", True)
67 | .schema(file_schema)
68 | .load("/databricks-datasets/iot-stream/data-user/*.csv")
69 | .withColumn( "id", uuidUdf() )
70 | .withColumn( "timestamp", lit(datetime.now().timestamp()).cast("timestamp") )
71 | .repartition(200)
72 | )
73 | display(iot_event_stream)
74 |
75 | # COMMAND ----------
76 |
77 | # DBTITLE 1,Housekeeping to make this idempotent
78 | # Full username, e.g. "
56 |
57 | # COMMAND ----------
58 |
59 | uuidUdf= udf(lambda : uuid.uuid4().hex,StringType())
60 |
61 | # Stream raw IOT Events from S3 bucket
62 | iot_event_stream = (spark
63 | .readStream
64 | .option( "maxFilesPerTrigger", 1 )
65 | .format("csv")
66 | .option("header", True)
67 | .schema(file_schema)
68 | .load("/databricks-datasets/iot-stream/data-user/*.csv")
69 | .withColumn( "id", uuidUdf() )
70 | .withColumn( "timestamp", lit(datetime.now().timestamp()).cast("timestamp") )
71 | .repartition(200)
72 | )
73 | display(iot_event_stream)
74 |
75 | # COMMAND ----------
76 |
77 | # DBTITLE 1,Housekeeping to make this idempotent
78 | # Full username, e.g. " 122 |
123 | # COMMAND ----------
124 |
125 | ######
126 | ## Setup checkpoint directory for writing out streaming workloads
127 | ######
128 |
129 | checkpoint_dir_bronze = f"/tmp/delta-stream-dltworkshop/{user}/bronze_check";
130 | checkpoint_dir_silver = f"/tmp/delta-stream-dltworkshop/{user}/silver_check"
131 | checkpoint_dir_gold = f"/tmp/delta-stream-dltworkshop/{user}/gold_check"
132 |
133 | # COMMAND ----------
134 |
135 | # MAGIC %md
136 | # MAGIC # Write IOT Events into a Bronze Delta Table
137 |
138 | # COMMAND ----------
139 |
140 | # Clear checkpoint location (for IDEMPOTENCY)
141 | dbutils.fs.rm(checkpoint_dir_bronze, True)
142 |
143 | iot_stream = iot_event_stream.writeStream\
144 | .format("delta")\
145 | .outputMode("append")\
146 | .option("header", True)\
147 | .option("checkpointLocation", checkpoint_dir_bronze)\
148 | .trigger(processingTime='10 seconds')\
149 | .table("iot_event_bronze")
150 |
151 | # COMMAND ----------
152 |
153 | # MAGIC %sql
154 | # MAGIC
155 | # MAGIC DESCRIBE TABLE EXTENDED iot_event_bronze;
156 |
157 | # COMMAND ----------
158 |
159 | # DBTITLE 1,Take a peak at delta lake files created
160 | display(dbutils.fs.ls(f"/user/hive/warehouse/{dbName}.db/iot_event_bronze/"))
161 |
162 | # COMMAND ----------
163 |
164 | # MAGIC %sql
165 | # MAGIC SELECT * FROM iot_event_bronze;
166 |
167 | # COMMAND ----------
168 |
169 | # MAGIC %md
170 | # MAGIC
171 | # MAGIC # Streaming ETL from Bronze to Silver
172 | # MAGIC
173 | # MAGIC Perform data cleanup and augmentation as we transform the Bronze data to Silver
174 |
175 | # COMMAND ----------
176 |
177 | """
178 | Deduplicate Bronze level data
179 | """
180 |
181 | # Clear checkpoint location (for IDEMPOTENCY)
182 | dbutils.fs.rm(checkpoint_dir_silver, True)
183 |
184 | # Drop terribly out-of-order events
185 | bronzeCleanDF = iot_event_stream.withWatermark( "timestamp", "1 day" )
186 |
187 | # Drop bad events
188 | bronzeCleanDF = bronzeCleanDF.dropna()
189 |
190 | silverStream = bronzeCleanDF.writeStream\
191 | .format("delta")\
192 | .outputMode("append")\
193 | .option( "checkpointLocation", checkpoint_dir_silver)\
194 | .trigger(processingTime='10 seconds')\
195 | .table("iot_event_silver")
196 | silverStream
197 |
198 | # COMMAND ----------
199 |
200 | # MAGIC %sql
201 | # MAGIC SELECT * FROM iot_event_silver;
202 |
203 | # COMMAND ----------
204 |
205 | # MAGIC %md
206 | # MAGIC
207 | # MAGIC ## Streaming Aggregation from Silver to Gold
208 |
209 | # COMMAND ----------
210 |
211 | silver_streamDF = spark.readStream.option( "maxFilesPerTrigger", 1 ).format( "delta" ).table("iot_event_silver")
212 |
213 | # Clear checkpoint location (for IDEMPOTENCY)
214 | dbutils.fs.rm(checkpoint_dir_gold, True)
215 |
216 | # def updateGold( batch, batchId ):
217 | # ( gold.alias("gold")
218 | # .merge( batch.alias("batch"),
219 | # "gold.date = batch.date AND gold.miles_walked = batch.miles_walked"
220 | # )
221 | # .whenMatchedUpdateAll()
222 | # .whenNotMatchedInsertAll()
223 | # .execute()
224 | # )
225 |
226 | ( (silver_streamDF.withWatermark("timestamp", "1 hour").groupBy("gender").agg(avg("weight").alias("avg_weight")))
227 | .writeStream
228 | .trigger(processingTime='12 seconds')
229 | .outputMode("complete")\
230 | .option( "checkpointLocation", checkpoint_dir_gold)\
231 | .table("iot_event_gold")
232 | )
233 |
234 | # COMMAND ----------
235 |
236 | # MAGIC %sql
237 | # MAGIC SELECT * FROM iot_event_gold;
238 |
239 | # COMMAND ----------
240 |
241 | # MAGIC %md
242 | # MAGIC
243 | # MAGIC ### Data Skipping and ZORDER
244 | # MAGIC
245 | # MAGIC Databricks Delta uses multiple mechanisms to speed up queries.
246 | # MAGIC
247 | # MAGIC
248 | # MAGIC Data Skipping is a performance optimization that aims at speeding up queries that contain filters (WHERE clauses).
249 | # MAGIC
250 | # MAGIC As new data is inserted into a Databricks Delta table, file-level min/max statistics are collected for all columns (including nested ones) of supported types. Then, when there’s a lookup query against the table, Databricks Delta first consults these statistics in order to determine which files can safely be skipped.
251 | # MAGIC
252 | # MAGIC ZOrdering Improve your query performance with `OPTIMIZE` and `ZORDER` using file compaction and a technique to co-locate related information in the same set of files. This co-locality is automatically used by Delta data-skipping algorithms to dramatically reduce the amount of data that needs to be read.
253 | # MAGIC
254 | # MAGIC Given a column that you want to perform ZORDER on, say `OrderColumn`, Delta
255 | # MAGIC * Takes existing parquet files within a partition.
256 | # MAGIC * Maps the rows within the parquet files according to `OrderColumn` using this algorithm.
257 | # MAGIC * In the case of only one column, the mapping above becomes a linear sort.
258 | # MAGIC * Rewrites the sorted data into new parquet files.
259 | # MAGIC
260 | # MAGIC Note: In streaming, where incoming events are inherently ordered (more or less) by event time, use `ZORDER` to sort by a different column, say 'userID'.
261 | # MAGIC
262 | # MAGIC Reference: [Processing Petabytes of Data in Seconds with Databricks Delta](https://databricks.com/blog/2018/07/31/processing-petabytes-of-data-in-seconds-with-databricks-delta.html)
263 |
264 | # COMMAND ----------
265 |
266 | # MAGIC %sql
267 | # MAGIC
268 | # MAGIC --
269 | # MAGIC -- Run a sample query
270 | # MAGIC --
271 | # MAGIC
272 | # MAGIC SELECT gender, avg(weight) as AVG_weight, avg(height) as AVG_height
273 | # MAGIC FROM iot_event_silver
274 | # MAGIC Group by gender
275 | # MAGIC ORDER by gender DESC, AVG_weight ASC;
276 |
277 | # COMMAND ----------
278 |
279 | # MAGIC %sql
280 | # MAGIC
281 | # MAGIC --
282 | # MAGIC -- Optimize and Z-order by
283 | # MAGIC --
284 | # MAGIC
285 | # MAGIC OPTIMIZE iot_event_silver
286 | # MAGIC ZORDER BY gender, height, weight;
287 |
288 | # COMMAND ----------
289 |
290 | # MAGIC %sql
291 | # MAGIC
292 | # MAGIC --
293 | # MAGIC -- Run the same select query at higher performance
294 | # MAGIC --
295 | # MAGIC
296 | # MAGIC SELECT gender, avg(weight) as AVG_weight, avg(height) as AVG_height
297 | # MAGIC FROM iot_event_silver
298 | # MAGIC Group by gender
299 | # MAGIC ORDER by gender DESC, AVG_weight ASC;
300 |
301 | # COMMAND ----------
302 |
303 | # DBTITLE 1,Stop all streams
304 | for s in spark.streams.active:
305 | s.stop()
306 |
307 | # COMMAND ----------
308 |
309 |
310 |
--------------------------------------------------------------------------------
/notebooks/03. Process Change Data Capture (CDC) data In DLT Pipeline.py:
--------------------------------------------------------------------------------
1 | # Databricks notebook source
2 | # MAGIC %pip install Faker
3 |
4 | # COMMAND ----------
5 |
6 | # MAGIC %md
7 | # MAGIC **When creating the pipeline add the following configuration to point to the data source:**
8 | # MAGIC
9 | # MAGIC `source` : `/tmp/delta-stream-dltworkshop/{your_user_name}/cdc_raw`
10 |
11 | # COMMAND ----------
12 |
13 | # MAGIC %md
14 | # MAGIC
15 | # MAGIC ## Importance of Change Data Capture (CDC)
16 | # MAGIC
17 | # MAGIC Change Data Capture (CDC) is the process that captures the changes in records made to a data storage like Database, Data Warehouse, etc. These changes usually refer to operations like data deletion, addition and updating.
18 | # MAGIC
19 | # MAGIC A straightforward way of Data Replication is to take a Database Dump that will export a Database and import it to a LakeHouse/DataWarehouse/Lake, but this is not a scalable approach.
20 | # MAGIC
21 | # MAGIC Change Data Capture, only capture the changes made to the Database and apply those changes to the target Database. CDC reduces the overhead, and supports real-time analytics. It enables incremental loading while eliminates the need for bulk load updating.
22 |
23 | # COMMAND ----------
24 |
25 | # MAGIC %md
26 | # MAGIC
27 | # MAGIC ### CDC Approaches
28 | # MAGIC
29 | # MAGIC **1- Develop in-house CDC process:**
30 | # MAGIC
31 | # MAGIC ***Complex Task:*** CDC Data Replication is not a one-time easy solution. Due to the differences between Database Providers, Varying Record Formats, and the inconvenience of accessing Log Records, CDC is challenging.
32 | # MAGIC
33 | # MAGIC ***Regular Maintainance:*** Writing a CDC process script is only the first step. You need to maintain a customized solution that can map to aformentioned changes regularly. This needs a lot of time and resources.
34 | # MAGIC
35 | # MAGIC ***Overburdening:*** Developers in companies already face the burden of public queries. Additional work for building customizes CDC solution will affect existing revenue-generating projects.
36 | # MAGIC
37 | # MAGIC **2- Using CDC tools** such as Debezium, Hevo Data, IBM Infosphere, Qlik Replicate, Talend, Oracle GoldenGate, StreamSets.
38 | # MAGIC
39 | # MAGIC In this demo repo we are using CDC data coming from a CDC tool.
40 | # MAGIC Since a CDC tool is reading database logs:
41 | # MAGIC We are no longer dependant on developers updating a certain column
42 | # MAGIC
43 | # MAGIC — A CDC tool like Debezium takes care of capturing every changed row. It records the history of data changes in Kafka logs, from where your application consumes them.
44 |
45 | # COMMAND ----------
46 |
47 | # MAGIC %md
48 | # MAGIC
49 | # MAGIC ### Implement CDC In DLT Pipeline: Change Data Capture (Python)
50 | # MAGIC
51 | # MAGIC
52 | # MAGIC
122 |
123 | # COMMAND ----------
124 |
125 | ######
126 | ## Setup checkpoint directory for writing out streaming workloads
127 | ######
128 |
129 | checkpoint_dir_bronze = f"/tmp/delta-stream-dltworkshop/{user}/bronze_check";
130 | checkpoint_dir_silver = f"/tmp/delta-stream-dltworkshop/{user}/silver_check"
131 | checkpoint_dir_gold = f"/tmp/delta-stream-dltworkshop/{user}/gold_check"
132 |
133 | # COMMAND ----------
134 |
135 | # MAGIC %md
136 | # MAGIC # Write IOT Events into a Bronze Delta Table
137 |
138 | # COMMAND ----------
139 |
140 | # Clear checkpoint location (for IDEMPOTENCY)
141 | dbutils.fs.rm(checkpoint_dir_bronze, True)
142 |
143 | iot_stream = iot_event_stream.writeStream\
144 | .format("delta")\
145 | .outputMode("append")\
146 | .option("header", True)\
147 | .option("checkpointLocation", checkpoint_dir_bronze)\
148 | .trigger(processingTime='10 seconds')\
149 | .table("iot_event_bronze")
150 |
151 | # COMMAND ----------
152 |
153 | # MAGIC %sql
154 | # MAGIC
155 | # MAGIC DESCRIBE TABLE EXTENDED iot_event_bronze;
156 |
157 | # COMMAND ----------
158 |
159 | # DBTITLE 1,Take a peak at delta lake files created
160 | display(dbutils.fs.ls(f"/user/hive/warehouse/{dbName}.db/iot_event_bronze/"))
161 |
162 | # COMMAND ----------
163 |
164 | # MAGIC %sql
165 | # MAGIC SELECT * FROM iot_event_bronze;
166 |
167 | # COMMAND ----------
168 |
169 | # MAGIC %md
170 | # MAGIC
171 | # MAGIC # Streaming ETL from Bronze to Silver
172 | # MAGIC
173 | # MAGIC Perform data cleanup and augmentation as we transform the Bronze data to Silver
174 |
175 | # COMMAND ----------
176 |
177 | """
178 | Deduplicate Bronze level data
179 | """
180 |
181 | # Clear checkpoint location (for IDEMPOTENCY)
182 | dbutils.fs.rm(checkpoint_dir_silver, True)
183 |
184 | # Drop terribly out-of-order events
185 | bronzeCleanDF = iot_event_stream.withWatermark( "timestamp", "1 day" )
186 |
187 | # Drop bad events
188 | bronzeCleanDF = bronzeCleanDF.dropna()
189 |
190 | silverStream = bronzeCleanDF.writeStream\
191 | .format("delta")\
192 | .outputMode("append")\
193 | .option( "checkpointLocation", checkpoint_dir_silver)\
194 | .trigger(processingTime='10 seconds')\
195 | .table("iot_event_silver")
196 | silverStream
197 |
198 | # COMMAND ----------
199 |
200 | # MAGIC %sql
201 | # MAGIC SELECT * FROM iot_event_silver;
202 |
203 | # COMMAND ----------
204 |
205 | # MAGIC %md
206 | # MAGIC
207 | # MAGIC ## Streaming Aggregation from Silver to Gold
208 |
209 | # COMMAND ----------
210 |
211 | silver_streamDF = spark.readStream.option( "maxFilesPerTrigger", 1 ).format( "delta" ).table("iot_event_silver")
212 |
213 | # Clear checkpoint location (for IDEMPOTENCY)
214 | dbutils.fs.rm(checkpoint_dir_gold, True)
215 |
216 | # def updateGold( batch, batchId ):
217 | # ( gold.alias("gold")
218 | # .merge( batch.alias("batch"),
219 | # "gold.date = batch.date AND gold.miles_walked = batch.miles_walked"
220 | # )
221 | # .whenMatchedUpdateAll()
222 | # .whenNotMatchedInsertAll()
223 | # .execute()
224 | # )
225 |
226 | ( (silver_streamDF.withWatermark("timestamp", "1 hour").groupBy("gender").agg(avg("weight").alias("avg_weight")))
227 | .writeStream
228 | .trigger(processingTime='12 seconds')
229 | .outputMode("complete")\
230 | .option( "checkpointLocation", checkpoint_dir_gold)\
231 | .table("iot_event_gold")
232 | )
233 |
234 | # COMMAND ----------
235 |
236 | # MAGIC %sql
237 | # MAGIC SELECT * FROM iot_event_gold;
238 |
239 | # COMMAND ----------
240 |
241 | # MAGIC %md
242 | # MAGIC
243 | # MAGIC ### Data Skipping and ZORDER
244 | # MAGIC
245 | # MAGIC Databricks Delta uses multiple mechanisms to speed up queries.
246 | # MAGIC
247 | # MAGIC
248 | # MAGIC Data Skipping is a performance optimization that aims at speeding up queries that contain filters (WHERE clauses).
249 | # MAGIC
250 | # MAGIC As new data is inserted into a Databricks Delta table, file-level min/max statistics are collected for all columns (including nested ones) of supported types. Then, when there’s a lookup query against the table, Databricks Delta first consults these statistics in order to determine which files can safely be skipped.
251 | # MAGIC
252 | # MAGIC ZOrdering Improve your query performance with `OPTIMIZE` and `ZORDER` using file compaction and a technique to co-locate related information in the same set of files. This co-locality is automatically used by Delta data-skipping algorithms to dramatically reduce the amount of data that needs to be read.
253 | # MAGIC
254 | # MAGIC Given a column that you want to perform ZORDER on, say `OrderColumn`, Delta
255 | # MAGIC * Takes existing parquet files within a partition.
256 | # MAGIC * Maps the rows within the parquet files according to `OrderColumn` using this algorithm.
257 | # MAGIC * In the case of only one column, the mapping above becomes a linear sort.
258 | # MAGIC * Rewrites the sorted data into new parquet files.
259 | # MAGIC
260 | # MAGIC Note: In streaming, where incoming events are inherently ordered (more or less) by event time, use `ZORDER` to sort by a different column, say 'userID'.
261 | # MAGIC
262 | # MAGIC Reference: [Processing Petabytes of Data in Seconds with Databricks Delta](https://databricks.com/blog/2018/07/31/processing-petabytes-of-data-in-seconds-with-databricks-delta.html)
263 |
264 | # COMMAND ----------
265 |
266 | # MAGIC %sql
267 | # MAGIC
268 | # MAGIC --
269 | # MAGIC -- Run a sample query
270 | # MAGIC --
271 | # MAGIC
272 | # MAGIC SELECT gender, avg(weight) as AVG_weight, avg(height) as AVG_height
273 | # MAGIC FROM iot_event_silver
274 | # MAGIC Group by gender
275 | # MAGIC ORDER by gender DESC, AVG_weight ASC;
276 |
277 | # COMMAND ----------
278 |
279 | # MAGIC %sql
280 | # MAGIC
281 | # MAGIC --
282 | # MAGIC -- Optimize and Z-order by
283 | # MAGIC --
284 | # MAGIC
285 | # MAGIC OPTIMIZE iot_event_silver
286 | # MAGIC ZORDER BY gender, height, weight;
287 |
288 | # COMMAND ----------
289 |
290 | # MAGIC %sql
291 | # MAGIC
292 | # MAGIC --
293 | # MAGIC -- Run the same select query at higher performance
294 | # MAGIC --
295 | # MAGIC
296 | # MAGIC SELECT gender, avg(weight) as AVG_weight, avg(height) as AVG_height
297 | # MAGIC FROM iot_event_silver
298 | # MAGIC Group by gender
299 | # MAGIC ORDER by gender DESC, AVG_weight ASC;
300 |
301 | # COMMAND ----------
302 |
303 | # DBTITLE 1,Stop all streams
304 | for s in spark.streams.active:
305 | s.stop()
306 |
307 | # COMMAND ----------
308 |
309 |
310 |
--------------------------------------------------------------------------------
/notebooks/03. Process Change Data Capture (CDC) data In DLT Pipeline.py:
--------------------------------------------------------------------------------
1 | # Databricks notebook source
2 | # MAGIC %pip install Faker
3 |
4 | # COMMAND ----------
5 |
6 | # MAGIC %md
7 | # MAGIC **When creating the pipeline add the following configuration to point to the data source:**
8 | # MAGIC
9 | # MAGIC `source` : `/tmp/delta-stream-dltworkshop/{your_user_name}/cdc_raw`
10 |
11 | # COMMAND ----------
12 |
13 | # MAGIC %md
14 | # MAGIC
15 | # MAGIC ## Importance of Change Data Capture (CDC)
16 | # MAGIC
17 | # MAGIC Change Data Capture (CDC) is the process that captures the changes in records made to a data storage like Database, Data Warehouse, etc. These changes usually refer to operations like data deletion, addition and updating.
18 | # MAGIC
19 | # MAGIC A straightforward way of Data Replication is to take a Database Dump that will export a Database and import it to a LakeHouse/DataWarehouse/Lake, but this is not a scalable approach.
20 | # MAGIC
21 | # MAGIC Change Data Capture, only capture the changes made to the Database and apply those changes to the target Database. CDC reduces the overhead, and supports real-time analytics. It enables incremental loading while eliminates the need for bulk load updating.
22 |
23 | # COMMAND ----------
24 |
25 | # MAGIC %md
26 | # MAGIC
27 | # MAGIC ### CDC Approaches
28 | # MAGIC
29 | # MAGIC **1- Develop in-house CDC process:**
30 | # MAGIC
31 | # MAGIC ***Complex Task:*** CDC Data Replication is not a one-time easy solution. Due to the differences between Database Providers, Varying Record Formats, and the inconvenience of accessing Log Records, CDC is challenging.
32 | # MAGIC
33 | # MAGIC ***Regular Maintainance:*** Writing a CDC process script is only the first step. You need to maintain a customized solution that can map to aformentioned changes regularly. This needs a lot of time and resources.
34 | # MAGIC
35 | # MAGIC ***Overburdening:*** Developers in companies already face the burden of public queries. Additional work for building customizes CDC solution will affect existing revenue-generating projects.
36 | # MAGIC
37 | # MAGIC **2- Using CDC tools** such as Debezium, Hevo Data, IBM Infosphere, Qlik Replicate, Talend, Oracle GoldenGate, StreamSets.
38 | # MAGIC
39 | # MAGIC In this demo repo we are using CDC data coming from a CDC tool.
40 | # MAGIC Since a CDC tool is reading database logs:
41 | # MAGIC We are no longer dependant on developers updating a certain column
42 | # MAGIC
43 | # MAGIC — A CDC tool like Debezium takes care of capturing every changed row. It records the history of data changes in Kafka logs, from where your application consumes them.
44 |
45 | # COMMAND ----------
46 |
47 | # MAGIC %md
48 | # MAGIC
49 | # MAGIC ### Implement CDC In DLT Pipeline: Change Data Capture (Python)
50 | # MAGIC
51 | # MAGIC
52 | # MAGIC 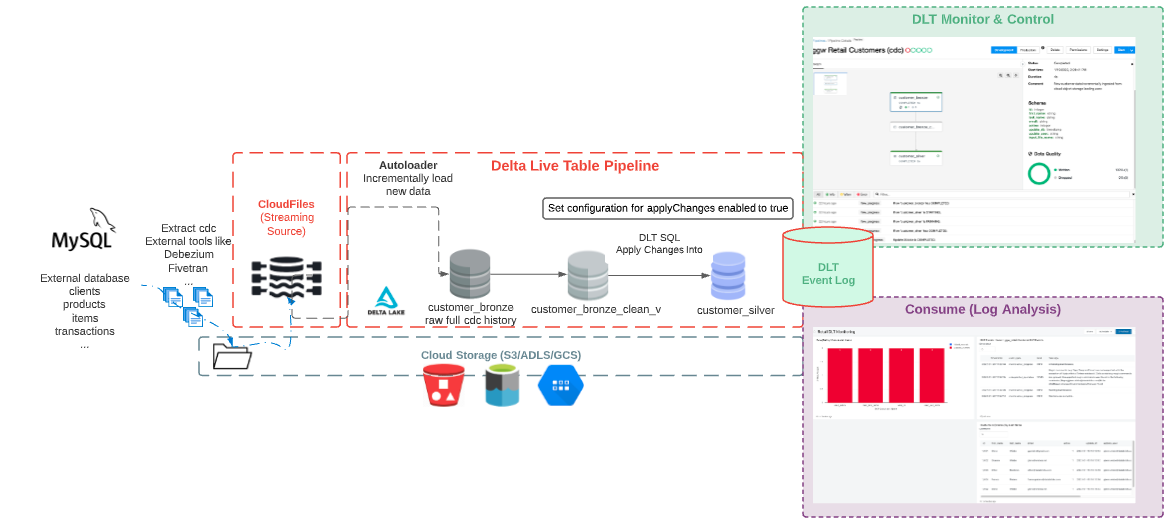 53 | # MAGIC
54 | # MAGIC
55 | # MAGIC ###### Resource [Change data capture with Delta Live Tables](https://docs.databricks.com/data-engineering/delta-live-tables/delta-live-tables-cdc.html)
56 |
57 | # COMMAND ----------
58 |
59 | # MAGIC %md
60 | # MAGIC
61 | # MAGIC ### Retail CDC Data Generator
62 |
63 | # COMMAND ----------
64 |
65 | # Full username, e.g. "
53 | # MAGIC
54 | # MAGIC
55 | # MAGIC ###### Resource [Change data capture with Delta Live Tables](https://docs.databricks.com/data-engineering/delta-live-tables/delta-live-tables-cdc.html)
56 |
57 | # COMMAND ----------
58 |
59 | # MAGIC %md
60 | # MAGIC
61 | # MAGIC ### Retail CDC Data Generator
62 |
63 | # COMMAND ----------
64 |
65 | # Full username, e.g. "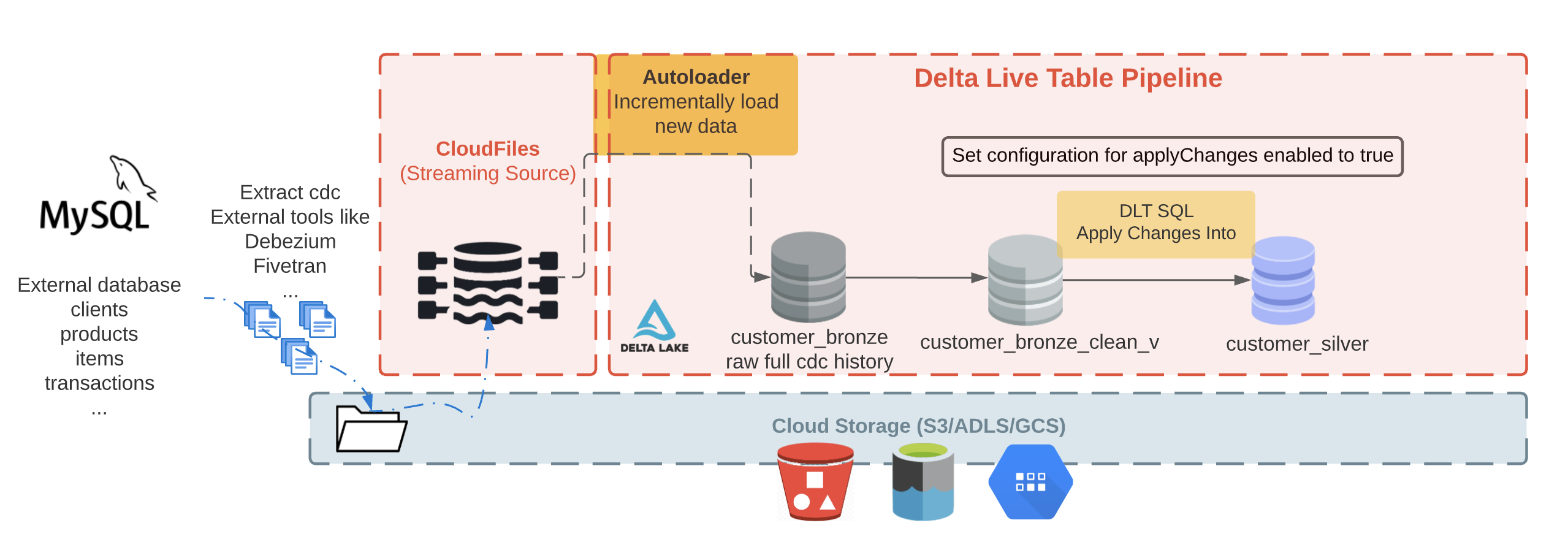 134 |
135 | # COMMAND ----------
136 |
137 | # MAGIC %md
138 | # MAGIC
139 | # MAGIC ###How does CDC tools like Debezium output looks like?
140 | # MAGIC
141 | # MAGIC A json message describing the changed data has interesting fields similar to the list below:
142 | # MAGIC
143 | # MAGIC - operation: an operation code (DELETE, APPEND, UPDATE, CREATE)
144 | # MAGIC - operation_date: the date and timestamp for the record came for each operation action
145 | # MAGIC
146 | # MAGIC Some other fields that you may see in Debezium output (not included in this demo):
147 | # MAGIC - before: the row before the change
148 | # MAGIC - after: the row after the change
149 | # MAGIC
150 | # MAGIC To learn more about the expected fields check out [this reference](https://debezium.io/documentation/reference/stable/connectors/postgresql.html#postgresql-update-events)
151 |
152 | # COMMAND ----------
153 |
154 | # MAGIC %md-sandbox
155 | # MAGIC ### Incremental data loading using Auto Loader (cloud_files)
156 | # MAGIC
157 | # MAGIC
158 | # MAGIC Working with external system can be challenging due to schema update. The external database can have schema update, adding or modifying columns, and our system must be robust against these changes.
159 | # MAGIC Databricks Autoloader (`cloudFiles`) handles schema inference and evolution out of the box.
160 | # MAGIC
161 | # MAGIC Autoloader allow us to efficiently ingest millions of files from a cloud storage, and support efficient schema inference and evolution at scale. In this notebook we leverage Autoloader to handle streaming (and batch) data.
162 | # MAGIC
134 |
135 | # COMMAND ----------
136 |
137 | # MAGIC %md
138 | # MAGIC
139 | # MAGIC ###How does CDC tools like Debezium output looks like?
140 | # MAGIC
141 | # MAGIC A json message describing the changed data has interesting fields similar to the list below:
142 | # MAGIC
143 | # MAGIC - operation: an operation code (DELETE, APPEND, UPDATE, CREATE)
144 | # MAGIC - operation_date: the date and timestamp for the record came for each operation action
145 | # MAGIC
146 | # MAGIC Some other fields that you may see in Debezium output (not included in this demo):
147 | # MAGIC - before: the row before the change
148 | # MAGIC - after: the row after the change
149 | # MAGIC
150 | # MAGIC To learn more about the expected fields check out [this reference](https://debezium.io/documentation/reference/stable/connectors/postgresql.html#postgresql-update-events)
151 |
152 | # COMMAND ----------
153 |
154 | # MAGIC %md-sandbox
155 | # MAGIC ### Incremental data loading using Auto Loader (cloud_files)
156 | # MAGIC
157 | # MAGIC
158 | # MAGIC Working with external system can be challenging due to schema update. The external database can have schema update, adding or modifying columns, and our system must be robust against these changes.
159 | # MAGIC Databricks Autoloader (`cloudFiles`) handles schema inference and evolution out of the box.
160 | # MAGIC
161 | # MAGIC Autoloader allow us to efficiently ingest millions of files from a cloud storage, and support efficient schema inference and evolution at scale. In this notebook we leverage Autoloader to handle streaming (and batch) data.
162 | # MAGIC  164 | # MAGIC
164 | # MAGIC  164 | # MAGIC
164 | # MAGIC 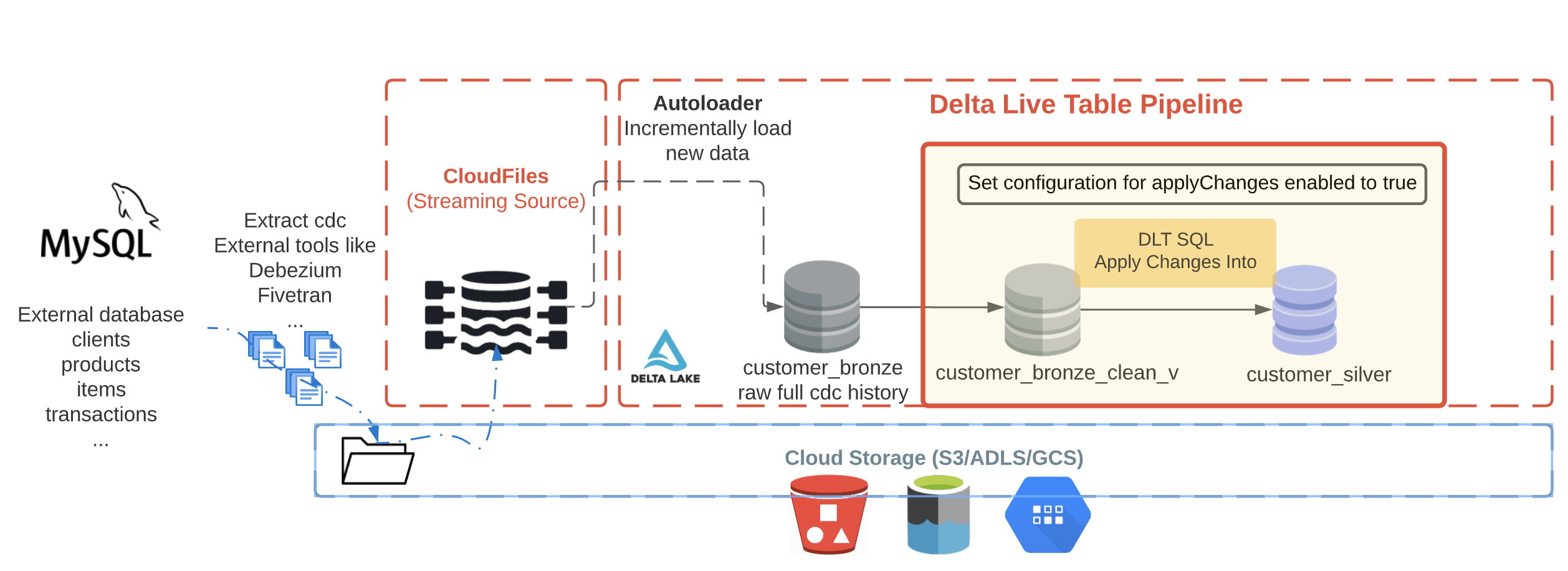 248 | # MAGIC
249 | # MAGIC The silver `customer_silver` table will contains the most up to date view. It'll be a replicate of the original table.
250 | # MAGIC
251 | # MAGIC To propagate the `Apply Changes Into` operations downstream to the `Silver` layer, we must explicitly enable the feature in pipeline by adding and enabling the applyChanges configuration to the DLT pipeline settings.
252 |
253 | # COMMAND ----------
254 |
255 | # DBTITLE 1,Delete unwanted clients records - Silver Table - DLT Python
256 | """
257 | ##Create the target table
258 | """
259 |
260 | dlt.create_streaming_live_table(name="customer_silver",
261 | comment="Clean, merged customers",
262 | table_properties={
263 | "quality": "silver"
264 | }
265 | )
266 |
267 | # COMMAND ----------
268 |
269 | """
270 | ##APPLY CHANGES the target table
271 | """
272 |
273 | dlt.apply_changes(
274 | target = "customer_silver", #The customer table being materilized
275 | source = "customer_bronze_clean_v", #the incoming CDC
276 | keys = ["id"], #Primary key to match the rows to upsert/delete
277 | sequence_by = col("operation_date"), #deduplicate by operation date getting the most recent value
278 | apply_as_deletes = expr("operation = 'DELETE'"), #DELETE condition
279 | except_column_list = ["operation", "operation_date", "_rescued_data"], # drop metadata columns
280 | stored_as_scd_type = 2
281 | )
282 |
283 | # COMMAND ----------
284 |
285 | # MAGIC %md
286 | # MAGIC
287 | # MAGIC Next step, create DLT pipeline, add a path to this notebook and **add configuration with enabling applychanges to true**.
288 |
--------------------------------------------------------------------------------
/LICENSE:
--------------------------------------------------------------------------------
1 | GNU GENERAL PUBLIC LICENSE
2 | Version 3, 29 June 2007
3 |
4 | Copyright (C) 2007 Free Software Foundation, Inc.
248 | # MAGIC
249 | # MAGIC The silver `customer_silver` table will contains the most up to date view. It'll be a replicate of the original table.
250 | # MAGIC
251 | # MAGIC To propagate the `Apply Changes Into` operations downstream to the `Silver` layer, we must explicitly enable the feature in pipeline by adding and enabling the applyChanges configuration to the DLT pipeline settings.
252 |
253 | # COMMAND ----------
254 |
255 | # DBTITLE 1,Delete unwanted clients records - Silver Table - DLT Python
256 | """
257 | ##Create the target table
258 | """
259 |
260 | dlt.create_streaming_live_table(name="customer_silver",
261 | comment="Clean, merged customers",
262 | table_properties={
263 | "quality": "silver"
264 | }
265 | )
266 |
267 | # COMMAND ----------
268 |
269 | """
270 | ##APPLY CHANGES the target table
271 | """
272 |
273 | dlt.apply_changes(
274 | target = "customer_silver", #The customer table being materilized
275 | source = "customer_bronze_clean_v", #the incoming CDC
276 | keys = ["id"], #Primary key to match the rows to upsert/delete
277 | sequence_by = col("operation_date"), #deduplicate by operation date getting the most recent value
278 | apply_as_deletes = expr("operation = 'DELETE'"), #DELETE condition
279 | except_column_list = ["operation", "operation_date", "_rescued_data"], # drop metadata columns
280 | stored_as_scd_type = 2
281 | )
282 |
283 | # COMMAND ----------
284 |
285 | # MAGIC %md
286 | # MAGIC
287 | # MAGIC Next step, create DLT pipeline, add a path to this notebook and **add configuration with enabling applychanges to true**.
288 |
--------------------------------------------------------------------------------
/LICENSE:
--------------------------------------------------------------------------------
1 | GNU GENERAL PUBLIC LICENSE
2 | Version 3, 29 June 2007
3 |
4 | Copyright (C) 2007 Free Software Foundation, Inc.  6 |
7 |
8 |
9 | 
10 |
11 |
12 |
13 | # Reading Resources
14 |
15 | See below links for more documentation:
16 | * [How to Process IoT Device JSON Data Using Apache Spark Datasets and DataFrames](https://databricks.com/blog/2016/03/28/how-to-process-iot-device-json-data-using-apache-spark-datasets-and-dataframes.html)
17 | * [Spark Structure Streaming](https://databricks.com/blog/2016/07/28/structured-streaming-in-apache-spark.html)
18 | * [Beyond Lambda](https://databricks.com/discover/getting-started-with-delta-lake-tech-talks/beyond-lambda-introducing-delta-architecture)
19 | * [Delta Lake Docs](https://docs.databricks.com/delta/index.html)
20 | * [Medallion Architecture](https://databricks.com/solutions/data-pipelines)
21 | * [Cost Savings with the Medallion Architecture](https://techcommunity.microsoft.com/t5/analytics-on-azure/how-to-reduce-infrastructure-costs-by-up-to-80-with-azure/ba-p/1820280)
22 | * [Change Data Capture Streams with the Medallion Architecture](https://databricks.com/blog/2021/06/09/how-to-simplify-cdc-with-delta-lakes-change-data-feed.html)
23 |
24 |
25 |
26 | # Workshop Flow
27 |
28 | The workshop consists of 4 interactive sections that are separated by 4 notebooks located in the notebooks folder in this repository. Each is run sequentially as we explore the abilities of the lakehouse from data ingestion, data curation, and performance optimizations
29 | |Notebook|Summary|
30 | |--------|-------|
31 | |`01-Structured Streaming with Databricks Delta Tables`|Processing and ingesting data at scale utilizing databricks tunables and the medallion architecture|
32 | |`02-Orchestrating with Delta Live Tables`|Changing Spark Properties, Configuring Table Properties, Optimization of Tables, Combining Batch and Incremental Tables|
33 | |`03. Implement CDC In DLT Pipeline: Change Data Capture (Python)`|Implementing Change Data Capture in DLT pipelines for accessing to fresh data|
34 | |`04: Meta-programming`|Examples of metaprogramming in DLT When to use/problems is solved How to configure|
35 | |`05: ML Models in DLT Pipelines`|Example of integratation of ML models with DLT pipelines|
36 |
37 |
38 |
39 | # Setup / Requirements
40 |
41 | This workshop requires a running Databricks workspace. If you are an existing Databricks customer, you can use your existing Databricks workspace. Otherwise, the notebooks in this workshop have been tested to run on [Databricks Community Edition](https://databricks.com/product/faq/community-edition) as well.
42 |
43 | ## DBR Version
44 |
45 | The features used in this workshop require `DBR 9.1 LTS`+.
46 |
47 | ## Repos
48 |
49 | If you have repos enabled on your Databricks workspace. You can directly import this repo and run the notebooks as is and avoid the DBC archive step.
50 |
51 | ## DBC Archive
52 |
53 | Download the DBC archive from releases and import the archive into your Databricks workspace.
54 |
--------------------------------------------------------------------------------
/notebooks/04. Advanced DLT Concepts.py:
--------------------------------------------------------------------------------
1 | # Databricks notebook source
2 | # MAGIC %md
3 | # MAGIC When creating the pipeline:
4 | # MAGIC * add the following configuration to point to the data source `data_source_path` : `/databricks-datasets/online_retail/data-001/`
5 | # MAGIC * add the following configuration to read the country list from the correct schema/db : `dbName`: `username_workshop_db`
6 | # MAGIC * add notebook number 2 (`02. Building Delta Live Tables Pipelines-SQL`) to the notebook Paths
7 |
8 | # COMMAND ----------
9 |
10 | # MAGIC %md
11 | # MAGIC
12 | # MAGIC ## Making pipelines Configure-less-code with DLT
13 |
14 | # COMMAND ----------
15 |
16 | import dlt
17 |
18 | # COMMAND ----------
19 |
20 | from pyspark.sql.functions import *
21 | from pyspark.sql.types import *
22 |
23 | # COMMAND ----------
24 |
25 | # DBTITLE 1,Load Configs From Table or Files
26 | ## Loading Distinct Countries from DLT Table that is automatically managed and kept up to date
27 |
28 | ## Configs can be anything
29 | # 1. Mappings
30 | # 2. Optimizations
31 | # 3. Table/Env configs
32 | # 4. Table definitions
33 | # 5. SQL Expressions/Full logic
34 |
35 | dbName = spark.conf.get("dbName")
36 |
37 | ## Get all countries you want to make a separate table for -- then you can create DBSQL Dashboards, and share these tables
38 | countries_list = [i[0] for i in spark.table(f"{dbName}.distinct_countries_retail").select("Country").coalesce(1).collect()]
39 | print(countries_list)
40 |
41 | all_tbl_properties = {
42 | "quality":"silver",
43 | "delta.tuneFileSizesForRewrites":"true",
44 | "pipelines.autoOptimize.zOrderCols":"CustomerID, InvoiceNo"
45 | }
46 |
47 | expectations_configs = {"has_invoice_number":"CAST(InvoiceNo AS INTEGER) IS NOT NULL","has_customer_number":"CAST(CustomerID AS INTEGER) IS NOT NULL"}
48 |
49 | access_configs = {"accessible_via_pii_group": ['United Kingdom']}
50 |
51 | # COMMAND ----------
52 |
53 | # DBTITLE 1,Define Wrapper Function for Reproducible Operation(s)
54 | ### Use meta-programming model
55 |
56 | def generate_bronze_tables(call_table, filter):
57 | #@dlt.expect_all_or_drop(expectations_configs)
58 | @dlt.table(
59 | name=call_table,
60 | comment=f"Bronze Table {call_table} By for Country: {filter}",
61 | table_properties=all_tbl_properties,
62 | spark_conf={"pipelines.trigger.interval" : "1 day"}
63 | )
64 | def create_call_table():
65 |
66 | df = (dlt.read_stream("quality_retail_split_by_country")
67 | .filter(col("Country") == lit(filter))
68 | )
69 |
70 | return df
71 |
72 | # COMMAND ----------
73 |
74 | # DBTITLE 1,Declaratively Implement Function
75 | for country in countries_list:
76 | clean_name = country.replace(" ","_")
77 | table_name = "sales_for_" + clean_name + "_bronze"
78 | generate_bronze_tables(table_name, country)
79 |
80 | # COMMAND ----------
81 |
82 | # DBTITLE 1,Dynamic APPLY CHANGES function
83 | def generate_silver_tables(target_table, source_table, merge_keys, sequence_key):
84 |
85 | ### Auto-zorder by merge keys, and others by a config
86 | zorder_str = ",".join(merge_keys)
87 |
88 | ### Dynamically config target tables as little or as much as you want
89 | dlt.create_streaming_live_table(
90 | name = target_table,
91 | comment = "Silver Table",
92 | spark_conf={"pipelines.trigger.interval" : "1 hour"},
93 | table_properties= {"quality":"silver",
94 | "delta.autoOptimize.optimizeWrite":"true",
95 | "delta.tuneFileSizesForRewrites":"true",
96 | "pipelines.autoOptimize.zOrderCols":zorder_str}
97 | #partition_cols=["
6 |
7 |
8 |
9 | 
10 |
11 |
12 |
13 | # Reading Resources
14 |
15 | See below links for more documentation:
16 | * [How to Process IoT Device JSON Data Using Apache Spark Datasets and DataFrames](https://databricks.com/blog/2016/03/28/how-to-process-iot-device-json-data-using-apache-spark-datasets-and-dataframes.html)
17 | * [Spark Structure Streaming](https://databricks.com/blog/2016/07/28/structured-streaming-in-apache-spark.html)
18 | * [Beyond Lambda](https://databricks.com/discover/getting-started-with-delta-lake-tech-talks/beyond-lambda-introducing-delta-architecture)
19 | * [Delta Lake Docs](https://docs.databricks.com/delta/index.html)
20 | * [Medallion Architecture](https://databricks.com/solutions/data-pipelines)
21 | * [Cost Savings with the Medallion Architecture](https://techcommunity.microsoft.com/t5/analytics-on-azure/how-to-reduce-infrastructure-costs-by-up-to-80-with-azure/ba-p/1820280)
22 | * [Change Data Capture Streams with the Medallion Architecture](https://databricks.com/blog/2021/06/09/how-to-simplify-cdc-with-delta-lakes-change-data-feed.html)
23 |
24 |
25 |
26 | # Workshop Flow
27 |
28 | The workshop consists of 4 interactive sections that are separated by 4 notebooks located in the notebooks folder in this repository. Each is run sequentially as we explore the abilities of the lakehouse from data ingestion, data curation, and performance optimizations
29 | |Notebook|Summary|
30 | |--------|-------|
31 | |`01-Structured Streaming with Databricks Delta Tables`|Processing and ingesting data at scale utilizing databricks tunables and the medallion architecture|
32 | |`02-Orchestrating with Delta Live Tables`|Changing Spark Properties, Configuring Table Properties, Optimization of Tables, Combining Batch and Incremental Tables|
33 | |`03. Implement CDC In DLT Pipeline: Change Data Capture (Python)`|Implementing Change Data Capture in DLT pipelines for accessing to fresh data|
34 | |`04: Meta-programming`|Examples of metaprogramming in DLT When to use/problems is solved How to configure|
35 | |`05: ML Models in DLT Pipelines`|Example of integratation of ML models with DLT pipelines|
36 |
37 |
38 |
39 | # Setup / Requirements
40 |
41 | This workshop requires a running Databricks workspace. If you are an existing Databricks customer, you can use your existing Databricks workspace. Otherwise, the notebooks in this workshop have been tested to run on [Databricks Community Edition](https://databricks.com/product/faq/community-edition) as well.
42 |
43 | ## DBR Version
44 |
45 | The features used in this workshop require `DBR 9.1 LTS`+.
46 |
47 | ## Repos
48 |
49 | If you have repos enabled on your Databricks workspace. You can directly import this repo and run the notebooks as is and avoid the DBC archive step.
50 |
51 | ## DBC Archive
52 |
53 | Download the DBC archive from releases and import the archive into your Databricks workspace.
54 |
--------------------------------------------------------------------------------
/notebooks/04. Advanced DLT Concepts.py:
--------------------------------------------------------------------------------
1 | # Databricks notebook source
2 | # MAGIC %md
3 | # MAGIC When creating the pipeline:
4 | # MAGIC * add the following configuration to point to the data source `data_source_path` : `/databricks-datasets/online_retail/data-001/`
5 | # MAGIC * add the following configuration to read the country list from the correct schema/db : `dbName`: `username_workshop_db`
6 | # MAGIC * add notebook number 2 (`02. Building Delta Live Tables Pipelines-SQL`) to the notebook Paths
7 |
8 | # COMMAND ----------
9 |
10 | # MAGIC %md
11 | # MAGIC
12 | # MAGIC ## Making pipelines Configure-less-code with DLT
13 |
14 | # COMMAND ----------
15 |
16 | import dlt
17 |
18 | # COMMAND ----------
19 |
20 | from pyspark.sql.functions import *
21 | from pyspark.sql.types import *
22 |
23 | # COMMAND ----------
24 |
25 | # DBTITLE 1,Load Configs From Table or Files
26 | ## Loading Distinct Countries from DLT Table that is automatically managed and kept up to date
27 |
28 | ## Configs can be anything
29 | # 1. Mappings
30 | # 2. Optimizations
31 | # 3. Table/Env configs
32 | # 4. Table definitions
33 | # 5. SQL Expressions/Full logic
34 |
35 | dbName = spark.conf.get("dbName")
36 |
37 | ## Get all countries you want to make a separate table for -- then you can create DBSQL Dashboards, and share these tables
38 | countries_list = [i[0] for i in spark.table(f"{dbName}.distinct_countries_retail").select("Country").coalesce(1).collect()]
39 | print(countries_list)
40 |
41 | all_tbl_properties = {
42 | "quality":"silver",
43 | "delta.tuneFileSizesForRewrites":"true",
44 | "pipelines.autoOptimize.zOrderCols":"CustomerID, InvoiceNo"
45 | }
46 |
47 | expectations_configs = {"has_invoice_number":"CAST(InvoiceNo AS INTEGER) IS NOT NULL","has_customer_number":"CAST(CustomerID AS INTEGER) IS NOT NULL"}
48 |
49 | access_configs = {"accessible_via_pii_group": ['United Kingdom']}
50 |
51 | # COMMAND ----------
52 |
53 | # DBTITLE 1,Define Wrapper Function for Reproducible Operation(s)
54 | ### Use meta-programming model
55 |
56 | def generate_bronze_tables(call_table, filter):
57 | #@dlt.expect_all_or_drop(expectations_configs)
58 | @dlt.table(
59 | name=call_table,
60 | comment=f"Bronze Table {call_table} By for Country: {filter}",
61 | table_properties=all_tbl_properties,
62 | spark_conf={"pipelines.trigger.interval" : "1 day"}
63 | )
64 | def create_call_table():
65 |
66 | df = (dlt.read_stream("quality_retail_split_by_country")
67 | .filter(col("Country") == lit(filter))
68 | )
69 |
70 | return df
71 |
72 | # COMMAND ----------
73 |
74 | # DBTITLE 1,Declaratively Implement Function
75 | for country in countries_list:
76 | clean_name = country.replace(" ","_")
77 | table_name = "sales_for_" + clean_name + "_bronze"
78 | generate_bronze_tables(table_name, country)
79 |
80 | # COMMAND ----------
81 |
82 | # DBTITLE 1,Dynamic APPLY CHANGES function
83 | def generate_silver_tables(target_table, source_table, merge_keys, sequence_key):
84 |
85 | ### Auto-zorder by merge keys, and others by a config
86 | zorder_str = ",".join(merge_keys)
87 |
88 | ### Dynamically config target tables as little or as much as you want
89 | dlt.create_streaming_live_table(
90 | name = target_table,
91 | comment = "Silver Table",
92 | spark_conf={"pipelines.trigger.interval" : "1 hour"},
93 | table_properties= {"quality":"silver",
94 | "delta.autoOptimize.optimizeWrite":"true",
95 | "delta.tuneFileSizesForRewrites":"true",
96 | "pipelines.autoOptimize.zOrderCols":zorder_str}
97 | #partition_cols=["