├── .gitignore
├── LICENSE
├── README.md
├── build.darwin.amd64.cmd
├── build.linux.amd64.cmd
├── build.linux.i386.cmd
├── build.windows.amd64.cmd
├── build.windows.i386.cmd
├── client.go
├── echarts.custom.min.js
├── echarts.go
├── echarts.min.js
├── htmltpl.go
├── main.go
├── sample.focus.min.png
├── sample.min.png
├── sample.zoom.min.png
└── utils.go
/.gitignore:
--------------------------------------------------------------------------------
1 | debug
2 | debug~
3 | *.upx
4 | *.zip
5 | *.html
6 | dns-dependency-go-darwin-amd64.bin
7 | dns-dependency-go-linux-amd64.bin
8 | dns-dependency-go-linux-i386.bin
9 | dns-dependency-go-windows-amd64.exe
10 | dns-dependency-go-windows-i386.exe
11 | dns-dependency-go.exe
--------------------------------------------------------------------------------
/LICENSE:
--------------------------------------------------------------------------------
1 | GNU GENERAL PUBLIC LICENSE
2 | Version 3, 29 June 2007
3 |
4 | Copyright (C) 2007 Free Software Foundation, Inc.
5 | Everyone is permitted to copy and distribute verbatim copies
6 | of this license document, but changing it is not allowed.
7 |
8 | Preamble
9 |
10 | The GNU General Public License is a free, copyleft license for
11 | software and other kinds of works.
12 |
13 | The licenses for most software and other practical works are designed
14 | to take away your freedom to share and change the works. By contrast,
15 | the GNU General Public License is intended to guarantee your freedom to
16 | share and change all versions of a program--to make sure it remains free
17 | software for all its users. We, the Free Software Foundation, use the
18 | GNU General Public License for most of our software; it applies also to
19 | any other work released this way by its authors. You can apply it to
20 | your programs, too.
21 |
22 | When we speak of free software, we are referring to freedom, not
23 | price. Our General Public Licenses are designed to make sure that you
24 | have the freedom to distribute copies of free software (and charge for
25 | them if you wish), that you receive source code or can get it if you
26 | want it, that you can change the software or use pieces of it in new
27 | free programs, and that you know you can do these things.
28 |
29 | To protect your rights, we need to prevent others from denying you
30 | these rights or asking you to surrender the rights. Therefore, you have
31 | certain responsibilities if you distribute copies of the software, or if
32 | you modify it: responsibilities to respect the freedom of others.
33 |
34 | For example, if you distribute copies of such a program, whether
35 | gratis or for a fee, you must pass on to the recipients the same
36 | freedoms that you received. You must make sure that they, too, receive
37 | or can get the source code. And you must show them these terms so they
38 | know their rights.
39 |
40 | Developers that use the GNU GPL protect your rights with two steps:
41 | (1) assert copyright on the software, and (2) offer you this License
42 | giving you legal permission to copy, distribute and/or modify it.
43 |
44 | For the developers' and authors' protection, the GPL clearly explains
45 | that there is no warranty for this free software. For both users' and
46 | authors' sake, the GPL requires that modified versions be marked as
47 | changed, so that their problems will not be attributed erroneously to
48 | authors of previous versions.
49 |
50 | Some devices are designed to deny users access to install or run
51 | modified versions of the software inside them, although the manufacturer
52 | can do so. This is fundamentally incompatible with the aim of
53 | protecting users' freedom to change the software. The systematic
54 | pattern of such abuse occurs in the area of products for individuals to
55 | use, which is precisely where it is most unacceptable. Therefore, we
56 | have designed this version of the GPL to prohibit the practice for those
57 | products. If such problems arise substantially in other domains, we
58 | stand ready to extend this provision to those domains in future versions
59 | of the GPL, as needed to protect the freedom of users.
60 |
61 | Finally, every program is threatened constantly by software patents.
62 | States should not allow patents to restrict development and use of
63 | software on general-purpose computers, but in those that do, we wish to
64 | avoid the special danger that patents applied to a free program could
65 | make it effectively proprietary. To prevent this, the GPL assures that
66 | patents cannot be used to render the program non-free.
67 |
68 | The precise terms and conditions for copying, distribution and
69 | modification follow.
70 |
71 | TERMS AND CONDITIONS
72 |
73 | 0. Definitions.
74 |
75 | "This License" refers to version 3 of the GNU General Public License.
76 |
77 | "Copyright" also means copyright-like laws that apply to other kinds of
78 | works, such as semiconductor masks.
79 |
80 | "The Program" refers to any copyrightable work licensed under this
81 | License. Each licensee is addressed as "you". "Licensees" and
82 | "recipients" may be individuals or organizations.
83 |
84 | To "modify" a work means to copy from or adapt all or part of the work
85 | in a fashion requiring copyright permission, other than the making of an
86 | exact copy. The resulting work is called a "modified version" of the
87 | earlier work or a work "based on" the earlier work.
88 |
89 | A "covered work" means either the unmodified Program or a work based
90 | on the Program.
91 |
92 | To "propagate" a work means to do anything with it that, without
93 | permission, would make you directly or secondarily liable for
94 | infringement under applicable copyright law, except executing it on a
95 | computer or modifying a private copy. Propagation includes copying,
96 | distribution (with or without modification), making available to the
97 | public, and in some countries other activities as well.
98 |
99 | To "convey" a work means any kind of propagation that enables other
100 | parties to make or receive copies. Mere interaction with a user through
101 | a computer network, with no transfer of a copy, is not conveying.
102 |
103 | An interactive user interface displays "Appropriate Legal Notices"
104 | to the extent that it includes a convenient and prominently visible
105 | feature that (1) displays an appropriate copyright notice, and (2)
106 | tells the user that there is no warranty for the work (except to the
107 | extent that warranties are provided), that licensees may convey the
108 | work under this License, and how to view a copy of this License. If
109 | the interface presents a list of user commands or options, such as a
110 | menu, a prominent item in the list meets this criterion.
111 |
112 | 1. Source Code.
113 |
114 | The "source code" for a work means the preferred form of the work
115 | for making modifications to it. "Object code" means any non-source
116 | form of a work.
117 |
118 | A "Standard Interface" means an interface that either is an official
119 | standard defined by a recognized standards body, or, in the case of
120 | interfaces specified for a particular programming language, one that
121 | is widely used among developers working in that language.
122 |
123 | The "System Libraries" of an executable work include anything, other
124 | than the work as a whole, that (a) is included in the normal form of
125 | packaging a Major Component, but which is not part of that Major
126 | Component, and (b) serves only to enable use of the work with that
127 | Major Component, or to implement a Standard Interface for which an
128 | implementation is available to the public in source code form. A
129 | "Major Component", in this context, means a major essential component
130 | (kernel, window system, and so on) of the specific operating system
131 | (if any) on which the executable work runs, or a compiler used to
132 | produce the work, or an object code interpreter used to run it.
133 |
134 | The "Corresponding Source" for a work in object code form means all
135 | the source code needed to generate, install, and (for an executable
136 | work) run the object code and to modify the work, including scripts to
137 | control those activities. However, it does not include the work's
138 | System Libraries, or general-purpose tools or generally available free
139 | programs which are used unmodified in performing those activities but
140 | which are not part of the work. For example, Corresponding Source
141 | includes interface definition files associated with source files for
142 | the work, and the source code for shared libraries and dynamically
143 | linked subprograms that the work is specifically designed to require,
144 | such as by intimate data communication or control flow between those
145 | subprograms and other parts of the work.
146 |
147 | The Corresponding Source need not include anything that users
148 | can regenerate automatically from other parts of the Corresponding
149 | Source.
150 |
151 | The Corresponding Source for a work in source code form is that
152 | same work.
153 |
154 | 2. Basic Permissions.
155 |
156 | All rights granted under this License are granted for the term of
157 | copyright on the Program, and are irrevocable provided the stated
158 | conditions are met. This License explicitly affirms your unlimited
159 | permission to run the unmodified Program. The output from running a
160 | covered work is covered by this License only if the output, given its
161 | content, constitutes a covered work. This License acknowledges your
162 | rights of fair use or other equivalent, as provided by copyright law.
163 |
164 | You may make, run and propagate covered works that you do not
165 | convey, without conditions so long as your license otherwise remains
166 | in force. You may convey covered works to others for the sole purpose
167 | of having them make modifications exclusively for you, or provide you
168 | with facilities for running those works, provided that you comply with
169 | the terms of this License in conveying all material for which you do
170 | not control copyright. Those thus making or running the covered works
171 | for you must do so exclusively on your behalf, under your direction
172 | and control, on terms that prohibit them from making any copies of
173 | your copyrighted material outside their relationship with you.
174 |
175 | Conveying under any other circumstances is permitted solely under
176 | the conditions stated below. Sublicensing is not allowed; section 10
177 | makes it unnecessary.
178 |
179 | 3. Protecting Users' Legal Rights From Anti-Circumvention Law.
180 |
181 | No covered work shall be deemed part of an effective technological
182 | measure under any applicable law fulfilling obligations under article
183 | 11 of the WIPO copyright treaty adopted on 20 December 1996, or
184 | similar laws prohibiting or restricting circumvention of such
185 | measures.
186 |
187 | When you convey a covered work, you waive any legal power to forbid
188 | circumvention of technological measures to the extent such circumvention
189 | is effected by exercising rights under this License with respect to
190 | the covered work, and you disclaim any intention to limit operation or
191 | modification of the work as a means of enforcing, against the work's
192 | users, your or third parties' legal rights to forbid circumvention of
193 | technological measures.
194 |
195 | 4. Conveying Verbatim Copies.
196 |
197 | You may convey verbatim copies of the Program's source code as you
198 | receive it, in any medium, provided that you conspicuously and
199 | appropriately publish on each copy an appropriate copyright notice;
200 | keep intact all notices stating that this License and any
201 | non-permissive terms added in accord with section 7 apply to the code;
202 | keep intact all notices of the absence of any warranty; and give all
203 | recipients a copy of this License along with the Program.
204 |
205 | You may charge any price or no price for each copy that you convey,
206 | and you may offer support or warranty protection for a fee.
207 |
208 | 5. Conveying Modified Source Versions.
209 |
210 | You may convey a work based on the Program, or the modifications to
211 | produce it from the Program, in the form of source code under the
212 | terms of section 4, provided that you also meet all of these conditions:
213 |
214 | a) The work must carry prominent notices stating that you modified
215 | it, and giving a relevant date.
216 |
217 | b) The work must carry prominent notices stating that it is
218 | released under this License and any conditions added under section
219 | 7. This requirement modifies the requirement in section 4 to
220 | "keep intact all notices".
221 |
222 | c) You must license the entire work, as a whole, under this
223 | License to anyone who comes into possession of a copy. This
224 | License will therefore apply, along with any applicable section 7
225 | additional terms, to the whole of the work, and all its parts,
226 | regardless of how they are packaged. This License gives no
227 | permission to license the work in any other way, but it does not
228 | invalidate such permission if you have separately received it.
229 |
230 | d) If the work has interactive user interfaces, each must display
231 | Appropriate Legal Notices; however, if the Program has interactive
232 | interfaces that do not display Appropriate Legal Notices, your
233 | work need not make them do so.
234 |
235 | A compilation of a covered work with other separate and independent
236 | works, which are not by their nature extensions of the covered work,
237 | and which are not combined with it such as to form a larger program,
238 | in or on a volume of a storage or distribution medium, is called an
239 | "aggregate" if the compilation and its resulting copyright are not
240 | used to limit the access or legal rights of the compilation's users
241 | beyond what the individual works permit. Inclusion of a covered work
242 | in an aggregate does not cause this License to apply to the other
243 | parts of the aggregate.
244 |
245 | 6. Conveying Non-Source Forms.
246 |
247 | You may convey a covered work in object code form under the terms
248 | of sections 4 and 5, provided that you also convey the
249 | machine-readable Corresponding Source under the terms of this License,
250 | in one of these ways:
251 |
252 | a) Convey the object code in, or embodied in, a physical product
253 | (including a physical distribution medium), accompanied by the
254 | Corresponding Source fixed on a durable physical medium
255 | customarily used for software interchange.
256 |
257 | b) Convey the object code in, or embodied in, a physical product
258 | (including a physical distribution medium), accompanied by a
259 | written offer, valid for at least three years and valid for as
260 | long as you offer spare parts or customer support for that product
261 | model, to give anyone who possesses the object code either (1) a
262 | copy of the Corresponding Source for all the software in the
263 | product that is covered by this License, on a durable physical
264 | medium customarily used for software interchange, for a price no
265 | more than your reasonable cost of physically performing this
266 | conveying of source, or (2) access to copy the
267 | Corresponding Source from a network server at no charge.
268 |
269 | c) Convey individual copies of the object code with a copy of the
270 | written offer to provide the Corresponding Source. This
271 | alternative is allowed only occasionally and noncommercially, and
272 | only if you received the object code with such an offer, in accord
273 | with subsection 6b.
274 |
275 | d) Convey the object code by offering access from a designated
276 | place (gratis or for a charge), and offer equivalent access to the
277 | Corresponding Source in the same way through the same place at no
278 | further charge. You need not require recipients to copy the
279 | Corresponding Source along with the object code. If the place to
280 | copy the object code is a network server, the Corresponding Source
281 | may be on a different server (operated by you or a third party)
282 | that supports equivalent copying facilities, provided you maintain
283 | clear directions next to the object code saying where to find the
284 | Corresponding Source. Regardless of what server hosts the
285 | Corresponding Source, you remain obligated to ensure that it is
286 | available for as long as needed to satisfy these requirements.
287 |
288 | e) Convey the object code using peer-to-peer transmission, provided
289 | you inform other peers where the object code and Corresponding
290 | Source of the work are being offered to the general public at no
291 | charge under subsection 6d.
292 |
293 | A separable portion of the object code, whose source code is excluded
294 | from the Corresponding Source as a System Library, need not be
295 | included in conveying the object code work.
296 |
297 | A "User Product" is either (1) a "consumer product", which means any
298 | tangible personal property which is normally used for personal, family,
299 | or household purposes, or (2) anything designed or sold for incorporation
300 | into a dwelling. In determining whether a product is a consumer product,
301 | doubtful cases shall be resolved in favor of coverage. For a particular
302 | product received by a particular user, "normally used" refers to a
303 | typical or common use of that class of product, regardless of the status
304 | of the particular user or of the way in which the particular user
305 | actually uses, or expects or is expected to use, the product. A product
306 | is a consumer product regardless of whether the product has substantial
307 | commercial, industrial or non-consumer uses, unless such uses represent
308 | the only significant mode of use of the product.
309 |
310 | "Installation Information" for a User Product means any methods,
311 | procedures, authorization keys, or other information required to install
312 | and execute modified versions of a covered work in that User Product from
313 | a modified version of its Corresponding Source. The information must
314 | suffice to ensure that the continued functioning of the modified object
315 | code is in no case prevented or interfered with solely because
316 | modification has been made.
317 |
318 | If you convey an object code work under this section in, or with, or
319 | specifically for use in, a User Product, and the conveying occurs as
320 | part of a transaction in which the right of possession and use of the
321 | User Product is transferred to the recipient in perpetuity or for a
322 | fixed term (regardless of how the transaction is characterized), the
323 | Corresponding Source conveyed under this section must be accompanied
324 | by the Installation Information. But this requirement does not apply
325 | if neither you nor any third party retains the ability to install
326 | modified object code on the User Product (for example, the work has
327 | been installed in ROM).
328 |
329 | The requirement to provide Installation Information does not include a
330 | requirement to continue to provide support service, warranty, or updates
331 | for a work that has been modified or installed by the recipient, or for
332 | the User Product in which it has been modified or installed. Access to a
333 | network may be denied when the modification itself materially and
334 | adversely affects the operation of the network or violates the rules and
335 | protocols for communication across the network.
336 |
337 | Corresponding Source conveyed, and Installation Information provided,
338 | in accord with this section must be in a format that is publicly
339 | documented (and with an implementation available to the public in
340 | source code form), and must require no special password or key for
341 | unpacking, reading or copying.
342 |
343 | 7. Additional Terms.
344 |
345 | "Additional permissions" are terms that supplement the terms of this
346 | License by making exceptions from one or more of its conditions.
347 | Additional permissions that are applicable to the entire Program shall
348 | be treated as though they were included in this License, to the extent
349 | that they are valid under applicable law. If additional permissions
350 | apply only to part of the Program, that part may be used separately
351 | under those permissions, but the entire Program remains governed by
352 | this License without regard to the additional permissions.
353 |
354 | When you convey a copy of a covered work, you may at your option
355 | remove any additional permissions from that copy, or from any part of
356 | it. (Additional permissions may be written to require their own
357 | removal in certain cases when you modify the work.) You may place
358 | additional permissions on material, added by you to a covered work,
359 | for which you have or can give appropriate copyright permission.
360 |
361 | Notwithstanding any other provision of this License, for material you
362 | add to a covered work, you may (if authorized by the copyright holders of
363 | that material) supplement the terms of this License with terms:
364 |
365 | a) Disclaiming warranty or limiting liability differently from the
366 | terms of sections 15 and 16 of this License; or
367 |
368 | b) Requiring preservation of specified reasonable legal notices or
369 | author attributions in that material or in the Appropriate Legal
370 | Notices displayed by works containing it; or
371 |
372 | c) Prohibiting misrepresentation of the origin of that material, or
373 | requiring that modified versions of such material be marked in
374 | reasonable ways as different from the original version; or
375 |
376 | d) Limiting the use for publicity purposes of names of licensors or
377 | authors of the material; or
378 |
379 | e) Declining to grant rights under trademark law for use of some
380 | trade names, trademarks, or service marks; or
381 |
382 | f) Requiring indemnification of licensors and authors of that
383 | material by anyone who conveys the material (or modified versions of
384 | it) with contractual assumptions of liability to the recipient, for
385 | any liability that these contractual assumptions directly impose on
386 | those licensors and authors.
387 |
388 | All other non-permissive additional terms are considered "further
389 | restrictions" within the meaning of section 10. If the Program as you
390 | received it, or any part of it, contains a notice stating that it is
391 | governed by this License along with a term that is a further
392 | restriction, you may remove that term. If a license document contains
393 | a further restriction but permits relicensing or conveying under this
394 | License, you may add to a covered work material governed by the terms
395 | of that license document, provided that the further restriction does
396 | not survive such relicensing or conveying.
397 |
398 | If you add terms to a covered work in accord with this section, you
399 | must place, in the relevant source files, a statement of the
400 | additional terms that apply to those files, or a notice indicating
401 | where to find the applicable terms.
402 |
403 | Additional terms, permissive or non-permissive, may be stated in the
404 | form of a separately written license, or stated as exceptions;
405 | the above requirements apply either way.
406 |
407 | 8. Termination.
408 |
409 | You may not propagate or modify a covered work except as expressly
410 | provided under this License. Any attempt otherwise to propagate or
411 | modify it is void, and will automatically terminate your rights under
412 | this License (including any patent licenses granted under the third
413 | paragraph of section 11).
414 |
415 | However, if you cease all violation of this License, then your
416 | license from a particular copyright holder is reinstated (a)
417 | provisionally, unless and until the copyright holder explicitly and
418 | finally terminates your license, and (b) permanently, if the copyright
419 | holder fails to notify you of the violation by some reasonable means
420 | prior to 60 days after the cessation.
421 |
422 | Moreover, your license from a particular copyright holder is
423 | reinstated permanently if the copyright holder notifies you of the
424 | violation by some reasonable means, this is the first time you have
425 | received notice of violation of this License (for any work) from that
426 | copyright holder, and you cure the violation prior to 30 days after
427 | your receipt of the notice.
428 |
429 | Termination of your rights under this section does not terminate the
430 | licenses of parties who have received copies or rights from you under
431 | this License. If your rights have been terminated and not permanently
432 | reinstated, you do not qualify to receive new licenses for the same
433 | material under section 10.
434 |
435 | 9. Acceptance Not Required for Having Copies.
436 |
437 | You are not required to accept this License in order to receive or
438 | run a copy of the Program. Ancillary propagation of a covered work
439 | occurring solely as a consequence of using peer-to-peer transmission
440 | to receive a copy likewise does not require acceptance. However,
441 | nothing other than this License grants you permission to propagate or
442 | modify any covered work. These actions infringe copyright if you do
443 | not accept this License. Therefore, by modifying or propagating a
444 | covered work, you indicate your acceptance of this License to do so.
445 |
446 | 10. Automatic Licensing of Downstream Recipients.
447 |
448 | Each time you convey a covered work, the recipient automatically
449 | receives a license from the original licensors, to run, modify and
450 | propagate that work, subject to this License. You are not responsible
451 | for enforcing compliance by third parties with this License.
452 |
453 | An "entity transaction" is a transaction transferring control of an
454 | organization, or substantially all assets of one, or subdividing an
455 | organization, or merging organizations. If propagation of a covered
456 | work results from an entity transaction, each party to that
457 | transaction who receives a copy of the work also receives whatever
458 | licenses to the work the party's predecessor in interest had or could
459 | give under the previous paragraph, plus a right to possession of the
460 | Corresponding Source of the work from the predecessor in interest, if
461 | the predecessor has it or can get it with reasonable efforts.
462 |
463 | You may not impose any further restrictions on the exercise of the
464 | rights granted or affirmed under this License. For example, you may
465 | not impose a license fee, royalty, or other charge for exercise of
466 | rights granted under this License, and you may not initiate litigation
467 | (including a cross-claim or counterclaim in a lawsuit) alleging that
468 | any patent claim is infringed by making, using, selling, offering for
469 | sale, or importing the Program or any portion of it.
470 |
471 | 11. Patents.
472 |
473 | A "contributor" is a copyright holder who authorizes use under this
474 | License of the Program or a work on which the Program is based. The
475 | work thus licensed is called the contributor's "contributor version".
476 |
477 | A contributor's "essential patent claims" are all patent claims
478 | owned or controlled by the contributor, whether already acquired or
479 | hereafter acquired, that would be infringed by some manner, permitted
480 | by this License, of making, using, or selling its contributor version,
481 | but do not include claims that would be infringed only as a
482 | consequence of further modification of the contributor version. For
483 | purposes of this definition, "control" includes the right to grant
484 | patent sublicenses in a manner consistent with the requirements of
485 | this License.
486 |
487 | Each contributor grants you a non-exclusive, worldwide, royalty-free
488 | patent license under the contributor's essential patent claims, to
489 | make, use, sell, offer for sale, import and otherwise run, modify and
490 | propagate the contents of its contributor version.
491 |
492 | In the following three paragraphs, a "patent license" is any express
493 | agreement or commitment, however denominated, not to enforce a patent
494 | (such as an express permission to practice a patent or covenant not to
495 | sue for patent infringement). To "grant" such a patent license to a
496 | party means to make such an agreement or commitment not to enforce a
497 | patent against the party.
498 |
499 | If you convey a covered work, knowingly relying on a patent license,
500 | and the Corresponding Source of the work is not available for anyone
501 | to copy, free of charge and under the terms of this License, through a
502 | publicly available network server or other readily accessible means,
503 | then you must either (1) cause the Corresponding Source to be so
504 | available, or (2) arrange to deprive yourself of the benefit of the
505 | patent license for this particular work, or (3) arrange, in a manner
506 | consistent with the requirements of this License, to extend the patent
507 | license to downstream recipients. "Knowingly relying" means you have
508 | actual knowledge that, but for the patent license, your conveying the
509 | covered work in a country, or your recipient's use of the covered work
510 | in a country, would infringe one or more identifiable patents in that
511 | country that you have reason to believe are valid.
512 |
513 | If, pursuant to or in connection with a single transaction or
514 | arrangement, you convey, or propagate by procuring conveyance of, a
515 | covered work, and grant a patent license to some of the parties
516 | receiving the covered work authorizing them to use, propagate, modify
517 | or convey a specific copy of the covered work, then the patent license
518 | you grant is automatically extended to all recipients of the covered
519 | work and works based on it.
520 |
521 | A patent license is "discriminatory" if it does not include within
522 | the scope of its coverage, prohibits the exercise of, or is
523 | conditioned on the non-exercise of one or more of the rights that are
524 | specifically granted under this License. You may not convey a covered
525 | work if you are a party to an arrangement with a third party that is
526 | in the business of distributing software, under which you make payment
527 | to the third party based on the extent of your activity of conveying
528 | the work, and under which the third party grants, to any of the
529 | parties who would receive the covered work from you, a discriminatory
530 | patent license (a) in connection with copies of the covered work
531 | conveyed by you (or copies made from those copies), or (b) primarily
532 | for and in connection with specific products or compilations that
533 | contain the covered work, unless you entered into that arrangement,
534 | or that patent license was granted, prior to 28 March 2007.
535 |
536 | Nothing in this License shall be construed as excluding or limiting
537 | any implied license or other defenses to infringement that may
538 | otherwise be available to you under applicable patent law.
539 |
540 | 12. No Surrender of Others' Freedom.
541 |
542 | If conditions are imposed on you (whether by court order, agreement or
543 | otherwise) that contradict the conditions of this License, they do not
544 | excuse you from the conditions of this License. If you cannot convey a
545 | covered work so as to satisfy simultaneously your obligations under this
546 | License and any other pertinent obligations, then as a consequence you may
547 | not convey it at all. For example, if you agree to terms that obligate you
548 | to collect a royalty for further conveying from those to whom you convey
549 | the Program, the only way you could satisfy both those terms and this
550 | License would be to refrain entirely from conveying the Program.
551 |
552 | 13. Use with the GNU Affero General Public License.
553 |
554 | Notwithstanding any other provision of this License, you have
555 | permission to link or combine any covered work with a work licensed
556 | under version 3 of the GNU Affero General Public License into a single
557 | combined work, and to convey the resulting work. The terms of this
558 | License will continue to apply to the part which is the covered work,
559 | but the special requirements of the GNU Affero General Public License,
560 | section 13, concerning interaction through a network will apply to the
561 | combination as such.
562 |
563 | 14. Revised Versions of this License.
564 |
565 | The Free Software Foundation may publish revised and/or new versions of
566 | the GNU General Public License from time to time. Such new versions will
567 | be similar in spirit to the present version, but may differ in detail to
568 | address new problems or concerns.
569 |
570 | Each version is given a distinguishing version number. If the
571 | Program specifies that a certain numbered version of the GNU General
572 | Public License "or any later version" applies to it, you have the
573 | option of following the terms and conditions either of that numbered
574 | version or of any later version published by the Free Software
575 | Foundation. If the Program does not specify a version number of the
576 | GNU General Public License, you may choose any version ever published
577 | by the Free Software Foundation.
578 |
579 | If the Program specifies that a proxy can decide which future
580 | versions of the GNU General Public License can be used, that proxy's
581 | public statement of acceptance of a version permanently authorizes you
582 | to choose that version for the Program.
583 |
584 | Later license versions may give you additional or different
585 | permissions. However, no additional obligations are imposed on any
586 | author or copyright holder as a result of your choosing to follow a
587 | later version.
588 |
589 | 15. Disclaimer of Warranty.
590 |
591 | THERE IS NO WARRANTY FOR THE PROGRAM, TO THE EXTENT PERMITTED BY
592 | APPLICABLE LAW. EXCEPT WHEN OTHERWISE STATED IN WRITING THE COPYRIGHT
593 | HOLDERS AND/OR OTHER PARTIES PROVIDE THE PROGRAM "AS IS" WITHOUT WARRANTY
594 | OF ANY KIND, EITHER EXPRESSED OR IMPLIED, INCLUDING, BUT NOT LIMITED TO,
595 | THE IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR
596 | PURPOSE. THE ENTIRE RISK AS TO THE QUALITY AND PERFORMANCE OF THE PROGRAM
597 | IS WITH YOU. SHOULD THE PROGRAM PROVE DEFECTIVE, YOU ASSUME THE COST OF
598 | ALL NECESSARY SERVICING, REPAIR OR CORRECTION.
599 |
600 | 16. Limitation of Liability.
601 |
602 | IN NO EVENT UNLESS REQUIRED BY APPLICABLE LAW OR AGREED TO IN WRITING
603 | WILL ANY COPYRIGHT HOLDER, OR ANY OTHER PARTY WHO MODIFIES AND/OR CONVEYS
604 | THE PROGRAM AS PERMITTED ABOVE, BE LIABLE TO YOU FOR DAMAGES, INCLUDING ANY
605 | GENERAL, SPECIAL, INCIDENTAL OR CONSEQUENTIAL DAMAGES ARISING OUT OF THE
606 | USE OR INABILITY TO USE THE PROGRAM (INCLUDING BUT NOT LIMITED TO LOSS OF
607 | DATA OR DATA BEING RENDERED INACCURATE OR LOSSES SUSTAINED BY YOU OR THIRD
608 | PARTIES OR A FAILURE OF THE PROGRAM TO OPERATE WITH ANY OTHER PROGRAMS),
609 | EVEN IF SUCH HOLDER OR OTHER PARTY HAS BEEN ADVISED OF THE POSSIBILITY OF
610 | SUCH DAMAGES.
611 |
612 | 17. Interpretation of Sections 15 and 16.
613 |
614 | If the disclaimer of warranty and limitation of liability provided
615 | above cannot be given local legal effect according to their terms,
616 | reviewing courts shall apply local law that most closely approximates
617 | an absolute waiver of all civil liability in connection with the
618 | Program, unless a warranty or assumption of liability accompanies a
619 | copy of the Program in return for a fee.
620 |
621 | END OF TERMS AND CONDITIONS
622 |
623 | How to Apply These Terms to Your New Programs
624 |
625 | If you develop a new program, and you want it to be of the greatest
626 | possible use to the public, the best way to achieve this is to make it
627 | free software which everyone can redistribute and change under these terms.
628 |
629 | To do so, attach the following notices to the program. It is safest
630 | to attach them to the start of each source file to most effectively
631 | state the exclusion of warranty; and each file should have at least
632 | the "copyright" line and a pointer to where the full notice is found.
633 |
634 | <<<<<<< HEAD
635 | {one line to give the program's name and a brief idea of what it does.}
636 | Copyright (C) {year} {fullname}
637 | =======
638 |
639 | Copyright (C)
640 | >>>>>>> 82c2ec74e6650fb8ea08f7ad9ba162acb9449865
641 |
642 | This program is free software: you can redistribute it and/or modify
643 | it under the terms of the GNU General Public License as published by
644 | the Free Software Foundation, either version 3 of the License, or
645 | (at your option) any later version.
646 |
647 | This program is distributed in the hope that it will be useful,
648 | but WITHOUT ANY WARRANTY; without even the implied warranty of
649 | MERCHANTABILITY or FITNESS FOR A PARTICULAR PURPOSE. See the
650 | GNU General Public License for more details.
651 |
652 | You should have received a copy of the GNU General Public License
653 | <<<<<<< HEAD
654 | along with this program. If not, see [http://www.gnu.org/licenses/].
655 | =======
656 | along with this program. If not, see .
657 | >>>>>>> 82c2ec74e6650fb8ea08f7ad9ba162acb9449865
658 |
659 | Also add information on how to contact you by electronic and paper mail.
660 |
661 | If the program does terminal interaction, make it output a short
662 | notice like this when it starts in an interactive mode:
663 |
664 | <<<<<<< HEAD
665 | dns-dependency-go Copyright (C) 2018 mchtech
666 | =======
667 | Copyright (C)
668 | >>>>>>> 82c2ec74e6650fb8ea08f7ad9ba162acb9449865
669 | This program comes with ABSOLUTELY NO WARRANTY; for details type `show w'.
670 | This is free software, and you are welcome to redistribute it
671 | under certain conditions; type `show c' for details.
672 |
673 | The hypothetical commands `show w' and `show c' should show the appropriate
674 | parts of the General Public License. Of course, your program's commands
675 | might be different; for a GUI interface, you would use an "about box".
676 |
677 | You should also get your employer (if you work as a programmer) or school,
678 | if any, to sign a "copyright disclaimer" for the program, if necessary.
679 | For more information on this, and how to apply and follow the GNU GPL, see
680 | <<<<<<< HEAD
681 | [http://www.gnu.org/licenses/].
682 | =======
683 | .
684 | >>>>>>> 82c2ec74e6650fb8ea08f7ad9ba162acb9449865
685 |
686 | The GNU General Public License does not permit incorporating your program
687 | into proprietary programs. If your program is a subroutine library, you
688 | may consider it more useful to permit linking proprietary applications with
689 | the library. If this is what you want to do, use the GNU Lesser General
690 | Public License instead of this License. But first, please read
691 | <<<<<<< HEAD
692 | [http://www.gnu.org/philosophy/why-not-lgpl.html].
693 | =======
694 | .
695 | >>>>>>> 82c2ec74e6650fb8ea08f7ad9ba162acb9449865
696 |
--------------------------------------------------------------------------------
/README.md:
--------------------------------------------------------------------------------
1 | # domain-dependency-tool
2 | # 一个能画出域名与其它DNS域的依赖关系/拓扑图的工具
3 | # A dependency graph/topology tool that can draw domain names with other DNS domains/zones
4 | ## 二进制(Binary): [Windows, Linux, Darwin](https://github.com/mchtech/domain-dependency-tool/releases/tag/v1.1)
5 | ## 效果(Result):
6 | ### github.com
7 | 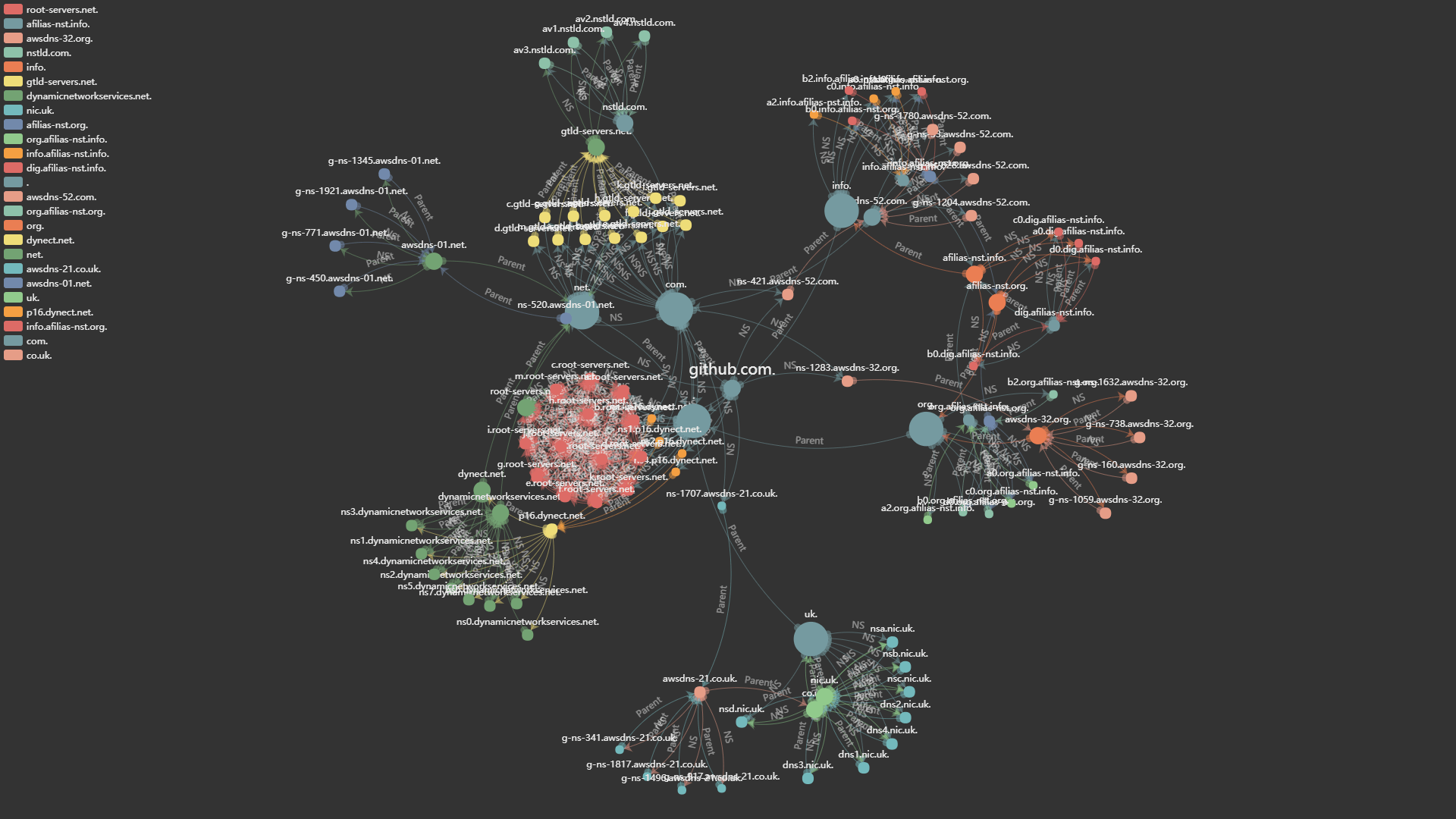
8 | 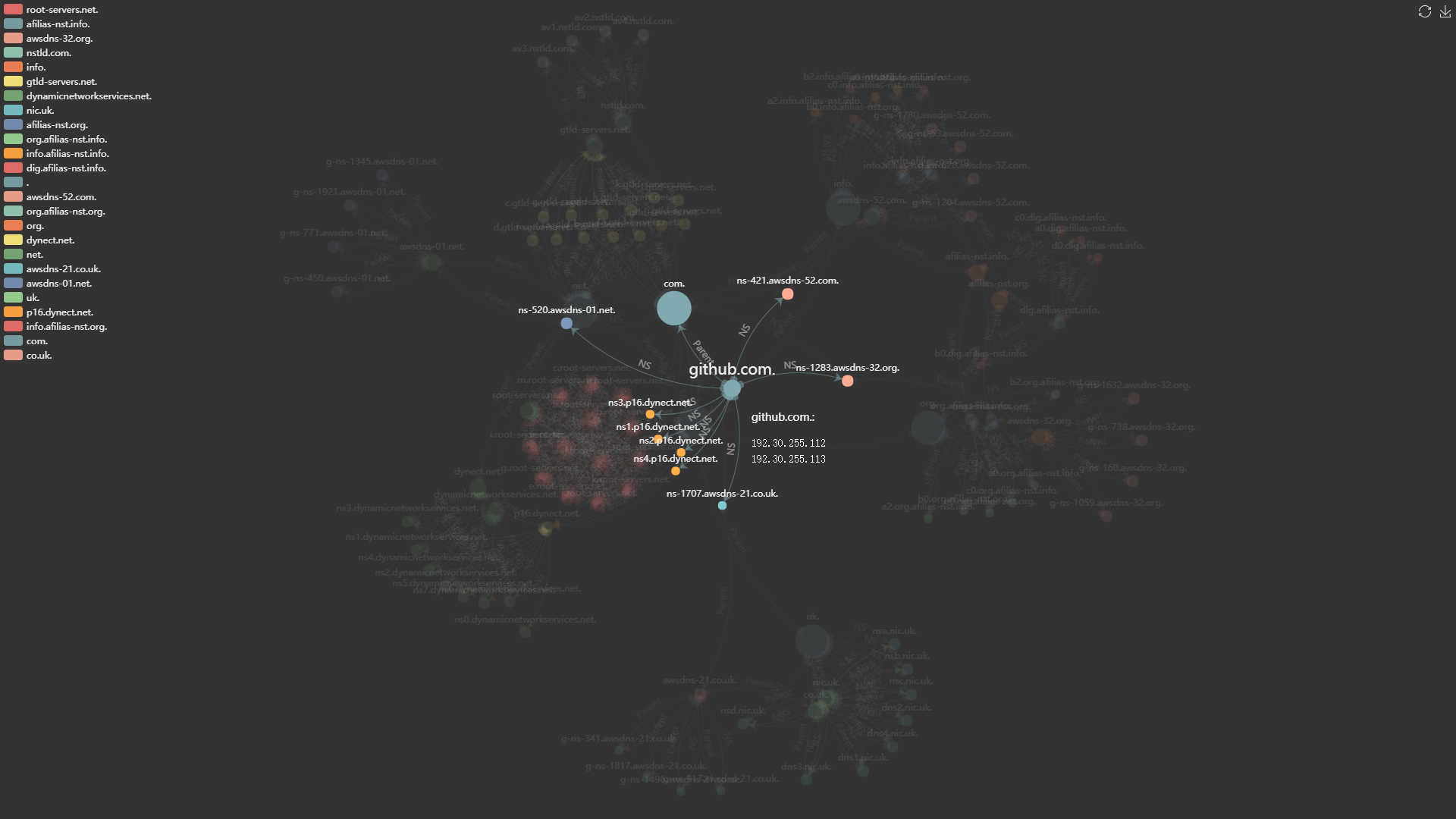
9 | ### 图缩放:滚轮(Zoom: use the wheel):
10 | 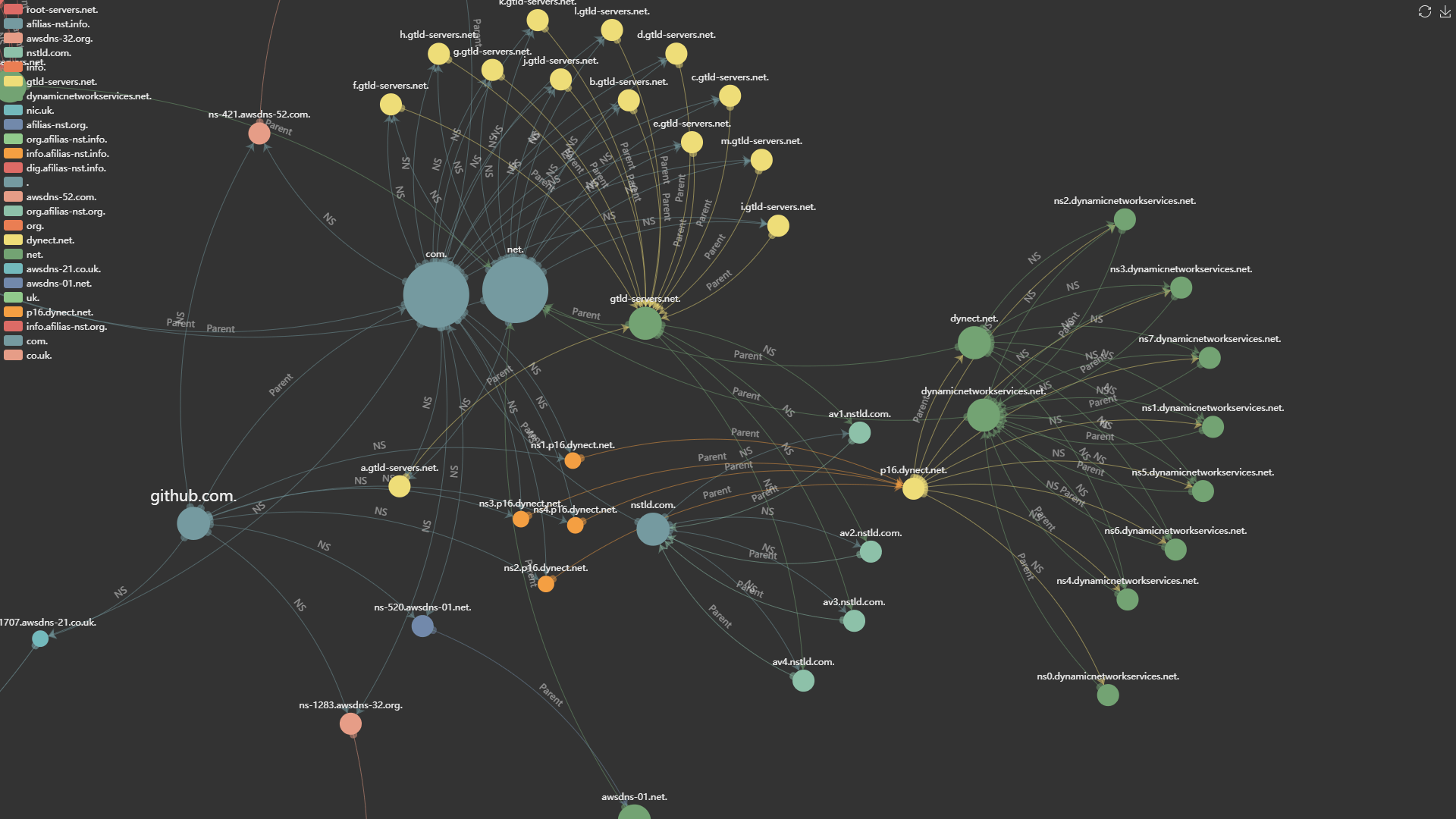
11 | ## 用法(Usage):
12 | > dns-dependency-go [-t timeout] [-c retry_count] [-eip clientip] [-nv] [-root] 域名/domain_name_or_FQDN
13 | ## 参数(Parameters):
14 | > -t 指定DNS解析超时时间(秒,默认为2秒) [Specify DNS resoving timeout (in second, default is 2 seconds)]
15 |
16 | > -c 指定DNS解析超时重试次数(默认为4) [Specify DNS resoving timeout retry times (default is 4)]
17 |
18 | > -eip 指定 EDNS-Client-Subnet 的 IPv4 或 IPv6 地址 [Specify the IPv4 or IPv6 address for EDNS-Client-Subnet]
19 |
20 | > -nv 不验证权威NS记录 [Do not verify authoritative NS records]
21 |
22 | > -root 解析根域名服务器记录 [Resolve the root-servers records]
23 | ## 例子(Examples):
24 |
25 | > dns-dependency-go github.com
26 |
27 | > dns-dependency-go -t 2 -c 4 -eip 192.0.2.0 -root github.com
28 |
29 | > dns-dependency-go -t 2 -c 4 -eip 2001:db8::1 -root github.com
30 | ## 依赖(Library Dependency):
31 | ### echarts http://echarts.baidu.com/
32 |
--------------------------------------------------------------------------------
/build.darwin.amd64.cmd:
--------------------------------------------------------------------------------
1 | @echo off
2 | set GOOS=darwin
3 | set GOARCH=amd64
4 | go build -o dns-dependency-go-darwin-amd64.bin -v -ldflags="-s -w"
5 | upx -9 dns-dependency-go-darwin-amd64.bin
--------------------------------------------------------------------------------
/build.linux.amd64.cmd:
--------------------------------------------------------------------------------
1 | @echo off
2 | set GOOS=linux
3 | set GOARCH=amd64
4 | go build -o dns-dependency-go-linux-amd64.bin -v -ldflags="-s -w"
5 | upx -9 dns-dependency-go-linux-amd64.bin
--------------------------------------------------------------------------------
/build.linux.i386.cmd:
--------------------------------------------------------------------------------
1 | @echo off
2 | set GOOS=linux
3 | set GOARCH=386
4 | go build -o dns-dependency-go-linux-i386.bin -v -ldflags="-s -w"
5 | upx -9 dns-dependency-go-linux-i386.bin
--------------------------------------------------------------------------------
/build.windows.amd64.cmd:
--------------------------------------------------------------------------------
1 | @echo off
2 | set GOOS=windows
3 | set GOARCH=amd64
4 | go build -o dns-dependency-go-windows-amd64.exe -v -ldflags="-s -w"
5 | upx -9 dns-dependency-go-windows-amd64.exe
6 | dns-dependency-go-windows-amd64.exe
--------------------------------------------------------------------------------
/build.windows.i386.cmd:
--------------------------------------------------------------------------------
1 | @echo off
2 | set GOOS=windows
3 | set GOARCH=386
4 | go build -o dns-dependency-go-windows-i386.exe -v -ldflags="-s -w"
5 | upx -9 dns-dependency-go-windows-i386.exe
6 | dns-dependency-go-windows-i386.exe
--------------------------------------------------------------------------------
/client.go:
--------------------------------------------------------------------------------
1 | package main
2 |
3 | import (
4 | "fmt"
5 | "strings"
6 | "time"
7 |
8 | "github.com/miekg/dns"
9 | )
10 |
11 | func querydns(servers []string, name string, qtype uint16, qclass uint16) querydnsresult {
12 | var ret querydnsresult
13 | for _, server := range servers {
14 | if strings.Index(server, ":") != -1 && len(server) > 0 && server[0] != '[' {
15 | server = "[" + server + "]"
16 | }
17 | ok := false
18 | proto := "udp"
19 | for i := 0; i < cfg.TimeoutRetry+1; i++ {
20 | //time.Sleep(100 * time.Millisecond)
21 | m1 := new(dns.Msg)
22 | m1.Compress = true
23 | m1.Id = dns.Id()
24 | m1.RecursionDesired = false
25 | m1.Question = []dns.Question{
26 | dns.Question{
27 | Name: dns.Fqdn(name),
28 | Qtype: qtype,
29 | Qclass: qclass}}
30 |
31 | if cfg.EDNSClient != "" {
32 | subnet := dns.EDNS0_SUBNET{
33 | Code: dns.EDNS0SUBNET,
34 | Family: cfg.EDNSClientFamily,
35 | SourceNetmask: cfg.EDNSClientMask,
36 | SourceScope: 0,
37 | Address: cfg.eDNSClientBin,
38 | }
39 | opt := new(dns.OPT)
40 | opt.Hdr.Name = "."
41 | opt.Hdr.Rrtype = dns.TypeOPT
42 | opt.Option = append(opt.Option, &subnet)
43 | m1.Extra = append(m1.Extra, opt)
44 | }
45 |
46 | var ans1 *dns.Msg
47 | var err1 error
48 |
49 | var conn *dns.Conn
50 |
51 | conn, err1 = dns.DialTimeout(proto, server+":53", cfg.Timeout)
52 |
53 | if err1 == nil && conn != nil {
54 | co := new(dns.Conn)
55 | co.Conn = conn
56 | co.SetDeadline(time.Now().Add(cfg.Timeout))
57 | co.WriteMsg(m1)
58 | ans1, err1 = co.ReadMsg()
59 | defer co.Close()
60 | }
61 | // return result
62 | if err1 == nil {
63 | ret = querydnsresult{
64 | ans: ans1,
65 | err: err1,
66 | }
67 | ok = true
68 | break
69 | } else {
70 | ret.err = err1
71 | if err1.Error() == "dns: failed to unpack truncated message" {
72 | proto = "tcp"
73 | } else {
74 | fmt.Println("error:", err1)
75 | }
76 | }
77 | }
78 | if ok {
79 | break
80 | }
81 | }
82 | if ret.ans == nil {
83 | fmt.Println("[FATAL ERROR]", ret.err, name, dns.TypeToString[qtype], servers)
84 | }
85 | return ret
86 | }
87 |
88 | type querydnsresult struct {
89 | ans *dns.Msg
90 | err error
91 | }
92 |
--------------------------------------------------------------------------------
/echarts.go:
--------------------------------------------------------------------------------
1 | package main
2 |
3 | import (
4 | "encoding/json"
5 | "fmt"
6 | "io/ioutil"
7 | "strings"
8 | )
9 |
10 | type EData struct {
11 | Name string `json:"name"`
12 | Draggable bool `json:"draggable"`
13 | Category string `json:"category"`
14 | Value string `json:"value"`
15 | SymbolSize float32 `json:"symbolSize"`
16 | }
17 | type ECategory struct {
18 | Name string `json:"name"`
19 | }
20 | type ELink struct {
21 | Source string `json:"source"`
22 | Target string `json:"target"`
23 | Value string `json:"value"`
24 | LineStyle ELineStyle `json:"lineStyle"`
25 | }
26 |
27 | type ELineStyle struct {
28 | Normal ELineStyleNormal `json:"normal"`
29 | }
30 | type ELineStyleNormal struct {
31 | Curveness float32 `json:"curveness"`
32 | }
33 |
34 | func genjs(name string, mp map[string]*dnsrecord, fname string) {
35 | var datas []EData
36 | var links []ELink
37 | var categories []ECategory
38 | var categoriesname []string
39 |
40 | catamap := make(map[string]int)
41 |
42 | for _, v := range mp {
43 | upname := "."
44 | if v.name != "." {
45 | // Upper Name
46 | upname = getuplevelname(v.name)
47 | if _, ok := catamap[upname]; !ok {
48 | catamap[upname] = 0
49 | categoriesname = append(categoriesname, upname)
50 | categories = append(categories, ECategory{
51 | Name: upname,
52 | })
53 | }
54 | //CNAME
55 | if v.cname != "" {
56 | catamap[v.cname] = 0
57 | categoriesname = append(categoriesname, v.cname)
58 | categories = append(categories, ECategory{
59 | Name: v.cname,
60 | })
61 | }
62 | //CNAME Link
63 | if v.cname != "" {
64 | links = append(links, ELink{
65 | Source: v.name,
66 | Target: v.cname,
67 | Value: "CNAME",
68 | LineStyle: ELineStyle{
69 | Normal: ELineStyleNormal{
70 | Curveness: 0.2,
71 | },
72 | },
73 | })
74 | }
75 |
76 | // //SOA Link
77 | // if v.soa != "" {
78 | // links = append(links, ELink{
79 | // Source: v.name,
80 | // Target: v.soa,
81 | // Value: "SOA",
82 | // LineStyle: ELineStyle{
83 | // Normal: ELineStyleNormal{
84 | // Curveness: 0.2,
85 | // },
86 | // },
87 | // })
88 | // }
89 | }
90 |
91 | //Data
92 | dotcount := float32(strings.Count(v.name, "."))
93 | cnss := float32(48.00)
94 | cnss = cnss / dotcount
95 |
96 | data := EData{
97 | Name: v.name,
98 | Draggable: true,
99 | Category: upname,
100 | Value: strings.Join(v.ip, "\n"),
101 | SymbolSize: cnss,
102 | }
103 | datas = append(datas, data)
104 |
105 | //NS Link
106 | for _, ns := range v.ns {
107 | links = append(links, ELink{
108 | Source: v.name,
109 | Target: ns,
110 | Value: "NS",
111 | LineStyle: ELineStyle{
112 | Normal: ELineStyleNormal{
113 | Curveness: 0.2,
114 | },
115 | },
116 | })
117 | }
118 | }
119 |
120 | for _, v := range mp {
121 | ln := v.name
122 | for {
123 | if ln == "." {
124 | break
125 | }
126 | //Upper Name Link
127 | un := getuplevelname(ln)
128 | links = append(links, ELink{
129 | Source: ln,
130 | Target: un,
131 | Value: "Parent",
132 | LineStyle: ELineStyle{
133 | Normal: ELineStyleNormal{
134 | Curveness: 0.2,
135 | },
136 | },
137 | })
138 | ln = un
139 | }
140 | }
141 |
142 | // categories = make([]string, len(catamap))
143 | // for i, v := range catamap {
144 | // categories[v] = i
145 | // }
146 |
147 | cataarrjsonbin, _ := json.Marshal(categoriesname)
148 | catajsonbin, _ := json.Marshal(categories)
149 | datajsonbin, _ := json.Marshal(datas)
150 | linkjsonbin, _ := json.Marshal(links)
151 |
152 | cataarrjson := string(cataarrjsonbin)
153 | catajson := string(catajsonbin)
154 | datajson := string(datajsonbin)
155 | linkjson := string(linkjsonbin)
156 |
157 | jsonstr := fmt.Sprintf(tpl, cataarrjson, datajson, linkjson, catajson, name)
158 | ioutil.WriteFile(fname, []byte(jsonstr), 0666)
159 | }
160 |
--------------------------------------------------------------------------------
/main.go:
--------------------------------------------------------------------------------
1 | package main
2 |
3 | import (
4 | "flag"
5 | "fmt"
6 | "net"
7 | "os/exec"
8 | "runtime"
9 | "strings"
10 | "time"
11 |
12 | "github.com/miekg/dns"
13 | )
14 |
15 | type dnsrecord struct {
16 | name string
17 | ip []string
18 | ns []string
19 | cname string
20 | verifyed bool
21 | //soa string
22 | }
23 |
24 | var mp = make(map[string]*dnsrecord)
25 | var cla = uint16(dns.ClassINET)
26 |
27 | //得到域名的第nsindex的权威DNS的IP 和 权威DNS的个数
28 | // return IPs, NS count
29 | func getnsip(nm string, nsindex int) ([]string, int) {
30 | var ret []string
31 | var nslen int
32 | // 获取 name 的 NS记录
33 | record := mp[nm]
34 |
35 | if record != nil && len(record.ns) > 0 {
36 | nslen = len(record.ns)
37 | for i := nsindex; i < nslen; i++ {
38 | ns := record.ns[i]
39 | // 获取 ns 的 IP地址
40 | record2 := mp[ns]
41 | // IP 存在
42 | if record2 != nil && len(record2.ip) > 0 {
43 | ret = record2.ip
44 | break
45 | } else {
46 | ret = analyze(ns, false)
47 | }
48 | }
49 |
50 | } else { // 如果 nm (ccc.bbb.aaa) 的 NS记录 不存在
51 | // uplevelnm (bbb.aaa)
52 | uplevelnm := getuplevelname(nm)
53 | var nsip []string
54 | maxloop := 1
55 | for i := 0; i < maxloop; i++ {
56 | fmt.Println("--Loop", i, "for getting NS of", uplevelnm)
57 | // nsip: 得到 bbb.aaa 的 NS
58 | nsip, maxloop = getnsip(uplevelnm, i)
59 | if len(nsip) > 0 {
60 | // 向 nsip (bbb.aaa 的 NS) 查询 nm (ccc.bbb.aaa) 的 NS (nsres)
61 | nsres := querydns(nsip, nm, dns.TypeNS, cla)
62 | if nsres.ans != nil {
63 | if len(nsres.ans.Ns) == 0 {
64 | //使用上级name的NS
65 | uplevelrecord := mp[uplevelnm]
66 | if uplevelrecord != nil {
67 | mergenstodnsrecord(nm, uplevelrecord.ns)
68 | //fmt.Println("get result", mp[nm])
69 | ret = nsip
70 | //是指针不用重取
71 | nslen = len(uplevelrecord.ns)
72 | } else {
73 | //bug
74 | fmt.Println("bug 1!")
75 | }
76 | } else {
77 | fmt.Println("---Using NS records in answer of", nm)
78 | // nm(ccc.bbb.aaa) 的 NS (nsrecords)
79 | nsrecords := searchnsfromns(nm, nsres.ans.Ns)
80 | nslen = len(nsrecords)
81 | if nslen > 0 {
82 | var mergednamefromns []string
83 | for _, nsrecord := range nsrecords {
84 | nsrecord = strings.ToLower(nsrecord)
85 | nsi := searchipfromextra(nsrecord, nsres.ans.Extra)
86 | if len(nsi) > 0 {
87 | mergeaaaaatodnsrecord(nsrecord, nsi)
88 | } else {
89 | //fmt.Println("bug3")
90 | }
91 | mergednamefromns = append(mergednamefromns, nsrecord)
92 | appendnstodnsrecord(nm, nsrecord)
93 | fmt.Println("---Loop", i, "Get results(from Authority RRs)", mp[nm])
94 | ip := analyze(nsrecord, false)
95 | ret = dupmerge(ret, ip)
96 | }
97 | //验证每一个NS
98 | if cfg.VerifyNS {
99 | for _, mname := range mergednamefromns {
100 | mname = strings.ToLower(mname)
101 | if stat, ok := mp[mname]; !ok || !stat.verifyed {
102 | fmt.Println("----Loop", i, "Verify NS of", mname)
103 | //重新验证
104 | analyze(mname, true)
105 | if stat, ok = mp[mname]; ok {
106 | stat.verifyed = true
107 | }
108 | }
109 | }
110 | }
111 | } else { // NS record 查找失败
112 | fmt.Println("---Loop", i, "NS Record 查找失败")
113 | //return ret
114 | }
115 | }
116 | }
117 | break
118 | } else { // 本级 NS 查找失败
119 | //fmt.Println("here 4")
120 | //return ret
121 | continue
122 | }
123 | }
124 | }
125 | return ret, nslen
126 | }
127 |
128 | //reserved : must false
129 | func analyze(nm string, reserved bool) []string {
130 |
131 | nm = strings.ToLower(nm)
132 | var res []string
133 |
134 | fmt.Println("-Analyze", nm)
135 | record := mp[nm]
136 |
137 | var nsip []string
138 | // 得到域名的权威DNS IP
139 | // nm = ns1.aaa.com.
140 | //upname = aaa.com.
141 | upname := getuplevelname(nm)
142 | uprecord := mp[upname]
143 | //uprecord.ns = ns1.aaa.com.
144 | //nsip = record.ip
145 | if record != nil && (!reserved || (reserved && uprecord != nil && len(uprecord.ns) > 0 && uprecord.ns[0] == nm)) {
146 | //if record != nil && (!reserved || (reserved && record.soa == nm)) {
147 | if len(record.ip) > 0 {
148 | res = record.ip
149 | fmt.Println("-Analyze Results (from cache)", res)
150 | return res
151 | }
152 | }
153 |
154 | maxloop := 1
155 | for i := 0; i < maxloop; i++ {
156 | fmt.Println("--Begin Analyze Loop", i, "Name", nm)
157 | nsip, maxloop = getnsip(upname, i)
158 |
159 | if len(nsip) > 0 {
160 | ok := true
161 | //使用权威DNS解析
162 | qtypes := []uint16{dns.TypeA, dns.TypeAAAA}
163 | //qtypes := []uint16{dns.TypeA}
164 |
165 | for _, qtype := range qtypes {
166 | nmip := querydns(nsip, nm, qtype, cla)
167 | if nmip.ans != nil && len(nmip.ans.Answer) > 0 {
168 | if nmip.ans.Answer[0].Header().Rrtype == dns.TypeA || nmip.ans.Answer[0].Header().Rrtype == dns.TypeAAAA {
169 | ips := searchaaaaafromansver(nmip.ans.Answer)
170 | mergeaaaaatodnsrecord(nm, ips)
171 | res = dupmerge(res, ips)
172 | //fmt.Println("analyze result", mp[nm])
173 | } else if nmip.ans.Answer[0].Header().Rrtype == dns.TypeCNAME {
174 | cname := nmip.ans.Answer[0].(*dns.CNAME).Target
175 | res = dupmerge(res, analyze(cname, false))
176 | mergeaaaaatodnsrecord(nm, res)
177 | mp[nm].cname = cname
178 | } else {
179 | // mal package
180 | fmt.Println("mal package")
181 | }
182 | } else {
183 | if nmip.ans == nil {
184 | ok = false
185 | break
186 | } else if nmip.ans != nil && !nmip.ans.Authoritative {
187 | //非权威应答
188 | fmt.Println("!! non-authoritive answer !!")
189 | nsrecords := searchnsfromns(nm, nmip.ans.Ns)
190 | nsrecordslen := len(nsrecords)
191 | if nsrecordslen > 0 {
192 | mergenstodnsrecord(upname, nsrecords)
193 | for _, nsrecord := range nsrecords {
194 | nsrecord = strings.ToLower(nsrecord)
195 | //同源
196 | if strings.Index(nsrecord, upname) != -1 {
197 | nsi := searchipfromextra(nsrecord, nmip.ans.Extra)
198 | nsiplen := len(nsi)
199 | if nsiplen > 0 {
200 | mergeaaaaatodnsrecord(nsrecord, nsi)
201 | }
202 | }
203 | if strings.Count(nsrecord, ".")-strings.Count(upname, ".") > 1 {
204 | getnsip(getuplevelname(nsrecord), 0)
205 | }
206 | }
207 | maxloop += nsrecordslen
208 | i = maxloop - nsrecordslen - 1
209 | }
210 | ok = false
211 | break
212 | } else {
213 | // OK
214 | }
215 | }
216 | }
217 | if !ok {
218 | continue
219 | }
220 | } else {
221 | fmt.Println("bug2!", nsip)
222 | }
223 | break
224 | }
225 | fmt.Println("-Analyze Results", res)
226 | return res
227 | }
228 |
229 | type Config struct {
230 | Name string
231 | EDNSClient string
232 | eDNSClientBin net.IP
233 | EDNSClientMask uint8
234 | EDNSClientFamily uint16
235 | timeout int
236 | Timeout time.Duration
237 | TimeoutRetry int
238 | VerifyNS bool
239 | ResolveRootServer bool
240 | }
241 |
242 | var cfg Config
243 |
244 | func main() {
245 | start := time.Now()
246 |
247 | flag.BoolVar(&cfg.VerifyNS, "nv", false, "No not verify NS records in Authority Records (will take a short time and get less relationships)")
248 | flag.BoolVar(&cfg.ResolveRootServer, "root", false, "Resolve root-servers Records")
249 | flag.StringVar(&cfg.EDNSClient, "eip", "", "IPv4 or IPv6 address for EDNS-Client-Subnet")
250 | flag.IntVar(&cfg.timeout, "t", 2, "timeout of resolving domain (in second)")
251 | flag.IntVar(&cfg.TimeoutRetry, "c", 4, "retry count (timeout)")
252 | flag.Parse()
253 |
254 | cfg.VerifyNS = !cfg.VerifyNS
255 | cfg.Timeout = time.Duration(cfg.timeout) * time.Second
256 | cfg.Name = flag.Arg(0)
257 |
258 | //cfg.Name = "www.amazon.com."
259 | // cfg.VerifyNS = true
260 |
261 | if cfg.Name == "" {
262 | flag.Usage()
263 | fmt.Println(" DomainName string\n\na domain name is required.\n")
264 | return
265 | }
266 | // fqdn format
267 | if !strings.HasSuffix(cfg.Name, ".") {
268 | cfg.Name += "."
269 | }
270 | //edns
271 | if cfg.EDNSClient != "" {
272 | if strings.Index(cfg.EDNSClient, ":") != -1 {
273 | cfg.EDNSClientFamily = 2
274 | cfg.EDNSClientMask = 128
275 | cfg.eDNSClientBin = net.ParseIP(cfg.EDNSClient)
276 | } else {
277 | cfg.EDNSClientFamily = 1
278 | cfg.EDNSClientMask = 32
279 | cfg.eDNSClientBin = net.ParseIP(cfg.EDNSClient).To4()
280 | }
281 | }
282 | // setup root-servers
283 |
284 | rootservers := []string{}
285 | for i := 'a'; i <= 'm'; i++ {
286 | rootserver := string(i) + ".root-servers.net."
287 | rootservers = append(rootservers, rootserver)
288 | mp[rootserver] = &dnsrecord{
289 | name: rootserver,
290 | }
291 | }
292 | mp["a.root-servers.net."] = &dnsrecord{
293 | name: "a.root-servers.net.",
294 | ip: []string{"198.41.0.4", "2001:503:ba3e::2:30"},
295 | }
296 | for i := 'a'; i <= 'm'; i++ {
297 | rootserver := string(i) + ".root-servers.net."
298 | mp[rootserver].ns = rootservers
299 | }
300 |
301 | mp["."] = &dnsrecord{
302 | name: ".",
303 | ns: rootservers,
304 | }
305 |
306 | if cfg.ResolveRootServer {
307 | for i := 'a'; i <= 'm'; i++ {
308 | analyze(string(i)+".root-servers.net.", true)
309 | }
310 | }
311 | //process
312 | result := analyze(cfg.Name, false)
313 | getnsip(cfg.Name, 0)
314 |
315 | //dump
316 | fmt.Println("----------------------------------------------------------------------------------------------------")
317 | for i, data := range mp {
318 | //fmt.Println(i, "Fqdn", data.name, "SOA", data.soa, "NS", data.ns, "CNAME", data.cname, "IP", data.ip)
319 | fmt.Println(i, "Fqdn", data.name, "NS", data.ns, "CNAME", data.cname, "IP", data.ip)
320 | }
321 | fmt.Println("----------------------------------------------------------------------------------------------------")
322 | fmt.Println(result)
323 |
324 | //gen map html
325 | fname := cfg.Name
326 | if !cfg.VerifyNS {
327 | fname += "-noverifyns"
328 | }
329 | if cfg.EDNSClient != "" {
330 | ip := strings.Replace(cfg.EDNSClient, ":", "-", -1)
331 | fname += "-edns-" + ip
332 | }
333 | fname += ".html"
334 |
335 | genjs(cfg.Name, mp, fname)
336 | fmt.Println(fname + " generated")
337 | OpenURL(fname)
338 | fmt.Println("Spent", time.Now().Sub(start))
339 | }
340 |
341 | var commands = map[string][]string{
342 | "windows": []string{"cmd", " /c start "},
343 | "darwin": []string{"open", ""},
344 | "linux": []string{"xdg-open", ""},
345 | }
346 |
347 | // Open calls the OS default program for uri
348 | func OpenURL(uri string) error {
349 | run, ok := commands[runtime.GOOS]
350 | if !ok {
351 | return fmt.Errorf("don't know how to open things on %s platform", runtime.GOOS)
352 | }
353 |
354 | cmd := exec.Command(run[0], run[1]+uri)
355 | return cmd.Start()
356 | }
357 |
--------------------------------------------------------------------------------
/sample.focus.min.png:
--------------------------------------------------------------------------------
https://raw.githubusercontent.com/mchtech/domain-dependency-tool/9be15ac2eea77b3f9d5a291541ce22c219dbeacb/sample.focus.min.png
--------------------------------------------------------------------------------
/sample.min.png:
--------------------------------------------------------------------------------
https://raw.githubusercontent.com/mchtech/domain-dependency-tool/9be15ac2eea77b3f9d5a291541ce22c219dbeacb/sample.min.png
--------------------------------------------------------------------------------
/sample.zoom.min.png:
--------------------------------------------------------------------------------
https://raw.githubusercontent.com/mchtech/domain-dependency-tool/9be15ac2eea77b3f9d5a291541ce22c219dbeacb/sample.zoom.min.png
--------------------------------------------------------------------------------
/utils.go:
--------------------------------------------------------------------------------
1 | package main
2 |
3 | import (
4 | "strings"
5 |
6 | "github.com/miekg/dns"
7 | )
8 |
9 | func inarray(arr []string, str string) bool {
10 | for _, a := range arr {
11 | if a == str {
12 | return true
13 | }
14 | }
15 | return false
16 | }
17 |
18 | func searchipfromextra(name string, exrr []dns.RR) []string {
19 | name = strings.ToLower(name)
20 | var res []string
21 | for _, v := range exrr {
22 | if strings.ToLower(v.Header().Name) == name {
23 | if v.Header().Rrtype == dns.TypeA {
24 | res = append(res, v.(*dns.A).A.String())
25 | } else if v.Header().Rrtype == dns.TypeAAAA {
26 | res = append(res, v.(*dns.AAAA).AAAA.String())
27 | }
28 | }
29 | }
30 | return res
31 | }
32 |
33 | func dupmerge(src []string, dst []string) []string {
34 | for _, d := range dst {
35 | dup := false
36 | for _, s := range src {
37 | if s == d {
38 | dup = true
39 | break
40 | }
41 | }
42 | if !dup {
43 | src = append(src, d)
44 | }
45 | }
46 | return src
47 | }
48 |
49 | func searchnsfromns(name string, nss []dns.RR) []string {
50 | name = strings.ToLower(name)
51 | var res []string
52 | for _, v := range nss {
53 | if v.Header().Rrtype == dns.TypeNS {
54 | res = append(res, strings.ToLower(v.(*dns.NS).Ns))
55 | } else if v.Header().Rrtype == dns.TypeSOA {
56 | soaname := v.(*dns.SOA).Hdr.Name
57 | soaname = strings.ToLower(soaname)
58 | if soaname != name {
59 | //getnsip(soaname, 0)
60 | //analyze(soaname)
61 | soarecord := mp[soaname]
62 | if soarecord != nil {
63 | res = dupmerge(res, soarecord.ns)
64 | }
65 | // if sv, ok := mp[name]; ok {
66 | // sv.soa = soaname
67 | // } else {
68 | // mp[name] = &dnsrecord{
69 | // name: name,
70 | // ns: []string{},
71 | // soa: soaname,
72 | // ip: []string{},
73 | // }
74 | // }
75 | }
76 | res = dupmerge(res, []string{strings.ToLower(v.(*dns.SOA).Ns)})
77 | }
78 | }
79 | return res
80 | }
81 |
82 | func searchaaaaafromansver(ans []dns.RR) []string {
83 | var res []string
84 | for _, v := range ans {
85 | if v.Header().Rrtype == dns.TypeA {
86 | res = append(res, v.(*dns.A).A.String())
87 | } else if v.Header().Rrtype == dns.TypeAAAA {
88 | res = append(res, v.(*dns.AAAA).AAAA.String())
89 | }
90 | }
91 | return res
92 | }
93 |
94 | func appendnstodnsrecord(name string, nsrecord string) {
95 | name = strings.ToLower(name)
96 | nsrecord = strings.ToLower(nsrecord)
97 | record := mp[name]
98 | if record == nil {
99 | mp[name] = &dnsrecord{
100 | name: name,
101 | ns: []string{nsrecord},
102 | ip: []string{},
103 | }
104 | } else {
105 | for _, ns := range record.ns {
106 | if ns == nsrecord {
107 | return
108 | }
109 | }
110 | record.ns = append(record.ns, nsrecord)
111 | }
112 | }
113 |
114 | func mergeaaaaatodnsrecord(name string, aaaaa []string) {
115 | name = strings.ToLower(name)
116 | record := mp[name]
117 | if record == nil {
118 | mp[name] = &dnsrecord{
119 | name: name,
120 | ip: aaaaa,
121 | ns: []string{},
122 | }
123 | } else {
124 | for _, aaa := range aaaaa {
125 | exist := false
126 | for _, ip := range record.ip {
127 | if ip == aaa {
128 | exist = true
129 | }
130 | }
131 | if !exist {
132 | record.ip = append(record.ip, aaa)
133 | }
134 | }
135 | }
136 | }
137 |
138 | func mergenstodnsrecord(name string, aaaaa []string) {
139 | name = strings.ToLower(name)
140 | for i, v := range aaaaa {
141 | aaaaa[i] = strings.ToLower(v)
142 | }
143 |
144 | record := mp[name]
145 | if record == nil {
146 | mp[name] = &dnsrecord{
147 | name: name,
148 | ns: aaaaa,
149 | ip: []string{},
150 | }
151 | } else {
152 | for _, aaa := range aaaaa {
153 |
154 | exist := false
155 | for _, ns := range record.ns {
156 | if ns == aaa {
157 | exist = true
158 | }
159 | }
160 | if !exist {
161 | record.ns = append(record.ns, aaa)
162 | }
163 | }
164 | }
165 | }
166 |
167 | func getuplevelname(name string) string {
168 | idx := strings.Index(name, ".")
169 | ret := name[idx+1:]
170 | if ret == "" {
171 | ret = "."
172 | }
173 | return ret
174 | }
175 |
--------------------------------------------------------------------------------