 3 |
3 | 4 | Kubernetes Guide 5 |
 3 |
3 |
84 |  85 |
85 |
86 |
 94 |
95 | **Building Highly-Availability(HA) Clusters with kubeadm. Source: [Kubernetes.io](https://kubernetes.io/docs/setup/production-environment/tools/kubeadm/high-availability/)**
96 |
97 | ### Developer Resources
98 | [Back to the Top](#table-of-contents)
99 |
100 | - [Kubernetes Certifications](https://kubernetes.io/training/)
101 |
102 | - [Getting started with Kubernetes on AWS](https://aws.amazon.com/kubernetes/)
103 |
104 | - [Kubernetes on Microsoft Azure](https://azure.microsoft.com/en-us/topic/what-is-kubernetes/)
105 |
106 | - [Intro to Azure Kubernetes Service](https://docs.microsoft.com/en-us/azure/aks/kubernetes-dashboard)
107 |
108 | - [Getting started with Google Cloud](https://cloud.google.com/learn/what-is-kubernetes)
109 |
110 | - [Azure Red Hat OpenShift ](https://azure.microsoft.com/en-us/services/openshift/)
111 |
112 | - [Getting started with Kubernetes on Red Hat](https://www.redhat.com/en/topics/containers/what-is-kubernetes)
113 |
114 | - [Getting started with Kubernetes on IBM](https://www.ibm.com/cloud/learn/kubernetes)
115 |
116 | - [Red Hat OpenShift on IBM Cloud](https://www.ibm.com/cloud/openshift)
117 |
118 | - [Kubernetes Contributors](https://www.kubernetes.dev/)
119 |
120 | - [Kubernetes Tutorials from Pulumi](https://www.pulumi.com/docs/tutorials/kubernetes/)
121 |
122 | - [Enable OpenShift Virtualization on Red Hat OpenShift](https://developers.redhat.com/blog/2020/08/28/enable-openshift-virtualization-on-red-hat-openshift/)
123 |
124 | - [YAML basics in Kubernetes](https://developer.ibm.com/technologies/containers/tutorials/yaml-basics-and-usage-in-kubernetes/)
125 |
126 | - [Elastic Cloud on Kubernetes](https://www.elastic.co/elastic-cloud-kubernetes)
127 |
128 | - [Docker and Kubernetes](https://www.docker.com/products/kubernetes)
129 |
130 | - [Running Apache Spark on Kubernetes](http://spark.apache.org/docs/latest/running-on-kubernetes.html)
131 |
132 | - [Kubernetes Across VMware vRealize Automation](https://blogs.vmware.com/management/2019/06/kubernetes-across-vmware-cloud-automation-services.html)
133 |
134 | - [VMware Tanzu Kubernetes Grid](https://tanzu.vmware.com/kubernetes-grid)
135 |
136 | - [All the Ways VMware Tanzu Works with AWS](https://tanzu.vmware.com/content/blog/all-the-ways-vmware-tanzutm-works-with-aws)
137 |
138 | - [Using Ansible in a Cloud-Native Kubernetes Environment](https://www.ansible.com/blog/how-useful-is-ansible-in-a-cloud-native-kubernetes-environment)
139 |
140 | - [Managing Kubernetes (K8s) objects with Ansible](https://docs.ansible.com/ansible/latest/collections/community/kubernetes/k8s_module.html)
141 |
142 | - [Setting up a Kubernetes cluster using Vagrant and Ansible](https://kubernetes.io/blog/2019/03/15/kubernetes-setup-using-ansible-and-vagrant/)
143 |
144 | - [Running MongoDB with Kubernetes](https://www.mongodb.com/kubernetes)
145 |
146 | - [Kubernetes Fluentd](https://docs.fluentd.org/v/0.12/articles/kubernetes-fluentd)
147 |
148 | - [Understanding the new GitLab Kubernetes Agent](https://about.gitlab.com/blog/2020/09/22/introducing-the-gitlab-kubernetes-agent/)
149 |
150 | - [Intro Local Process with Kubernetes for Visual Studio 2019](https://devblogs.microsoft.com/visualstudio/introducing-local-process-with-kubernetes-for-visual-studio%E2%80%AF2019/)
151 |
152 | - [Kubernetes Playground by Katacoda](https://www.katacoda.com/courses/kubernetes/playground)
153 |
154 | ### Kubernetes Courses & Certifications
155 | [Back to the Top](#table-of-contents)
156 |
157 | - [Kubernetes Training & Certifications](https://kubernetes.io/training/)
158 |
159 | - [Top Kubernetes Courses Online | Coursera](https://www.coursera.org/courses?query=kubernetes)
160 |
161 | - [Top Kubernetes Courses Online | Udemy](https://www.udemy.com/topic/kubernetes/)
162 |
163 | - [Kubernetes Courses - IBM Developer](https://developer.ibm.com/components/kubernetes/courses/)
164 |
165 | - [Introduction to Kubernetes Courses | edX](https://www.edx.org/course/introduction-to-kubernetes)
166 |
167 | - [VMware Tanzu Education](https://tanzu.vmware.com/education)
168 |
169 | - [KubeAcademy from VMware](https://kube.academy/)
170 |
171 | - [Online Kubernetes Course: Beginners Guide to Kubernetes | Pluralsight](https://www.pluralsight.com/courses/getting-started-kubernetes)
172 |
173 | - [Getting Started with Google Kubernetes Engine | Pluralsight](https://www.pluralsight.com/courses/getting-started-google-kubernetes-engine-8)
174 |
175 | - [Scalable Microservices with Kubernetes course from Udacity](https://www.udacity.com/course/scalable-microservices-with-kubernetes--ud615)
176 |
177 | ### Kubernetes Books
178 | [Back to the Top](#table-of-contents)
179 |
180 | - [Kubernetes for Full-Stack Developers by Digital Ocean](https://assets.digitalocean.com/books/kubernetes-for-full-stack-developers.pdf)
181 |
182 | - [Kubernetes Patterns - Red Hat](https://www.redhat.com/cms/managed-files/cm-oreilly-kubernetes-patterns-ebook-f19824-201910-en.pdf)
183 |
184 | - [The Ultimate Guide to Kubernetes Deployments with Octopus](https://i.octopus.com/books/kubernetes-book.pdf)
185 |
186 | - [Learng Kubernetes (PDF)](https://riptutorial.com/Download/kubernetes.pdf)
187 |
188 | - [Certified Kubernetes Administrator (CKA) Study Guide: In-Depth Guidance and Practice](https://www.amazon.com/Certified-Kubernetes-Administrator-Study-Depth/dp/1098107225/ref=sr_1_29?crid=15963283P4C0V&keywords=kubernetes&qid=1653935057&s=books&sprefix=kubernetes%2Cstripbooks%2C174&sr=1-29)
189 |
190 | - [Quick Start Kubernetes by Nigel Poulton (2022)](https://www.amazon.com/Quick-Start-Kubernetes-Nigel-Poulton-ebook/dp/B08T21NW4Z/ref=sr_1_18?crid=15963283P4C0V&keywords=kubernetes&qid=1653935057&s=books&sprefix=kubernetes%2Cstripbooks%2C174&sr=1-18)
191 |
192 | - [The Kubernetes Book by Nigel Poulton (2022)](https://www.amazon.com/Kubernetes-Book-Version-November-2018-ebook/dp/B072TS9ZQZ/ref=sr_1_4?crid=15963283P4C0V&keywords=kubernetes&qid=1653935057&s=books&sprefix=kubernetes%2Cstripbooks%2C174&sr=1-4)
193 |
194 | - [Kubernetes: Up and Running: Dive into the Future of Infrastructure](https://www.amazon.com/Kubernetes-Running-Dive-Future-Infrastructure/dp/1492046531/ref=sr_1_5?crid=15963283P4C0V&keywords=kubernetes&qid=1653935057&s=books&sprefix=kubernetes%2Cstripbooks%2C174&sr=1-5)
195 |
196 | - [Kubernetes and Docker - An Enterprise Guide: Effectively containerize applications, integrate enterprise systems, and scale applications in your enterprise](https://www.amazon.com/Kubernetes-Docker-Effectively-containerize-applications/dp/183921340X/ref=sr_1_24?crid=15963283P4C0V&keywords=kubernetes&qid=1653935057&s=books&sprefix=kubernetes%2Cstripbooks%2C174&sr=1-24)
197 |
198 | - [Kubernetes in Action](https://www.amazon.com/Kubernetes-Action-Marko-Luksa/dp/1617293725/ref=sr_1_7?crid=15963283P4C0V&keywords=kubernetes&qid=1653935057&s=books&sprefix=kubernetes%2Cstripbooks%2C174&sr=1-7)
199 |
200 | - [Kubernetes – An Enterprise Guide: Effectively containerize applications, integrate enterprise systems, and scale](https://www.amazon.com/Kubernetes-Enterprise-Effectively-containerize-applications/dp/1803230037/ref=sr_1_6?crid=15963283P4C0V&keywords=kubernetes&qid=1653935057&s=books&sprefix=kubernetes%2Cstripbooks%2C174&sr=1-6)
201 |
202 | - [Production Kubernetes: Building Successful Application Platforms](https://www.amazon.com/Production-Kubernetes-Successful-Application-Platforms/dp/1492092304/ref=sr_1_8?crid=15963283P4C0V&keywords=kubernetes&qid=1653935057&s=books&sprefix=kubernetes%2Cstripbooks%2C174&sr=1-8)
203 |
204 | - [The Kubernetes Bible: The definitive guide to deploying and managing Kubernetes across major cloud platforms](https://www.amazon.com/Kubernetes-Bible-definitive-deploying-platforms/dp/1838827692/ref=sr_1_16?crid=15963283P4C0V&keywords=kubernetes&qid=1653935057&s=books&sprefix=kubernetes%2Cstripbooks%2C174&sr=1-16)
205 |
206 | - [Networking and Kubernetes: A Layered Approach](https://www.amazon.com/Networking-Kubernetes-Approach-James-Strong/dp/1492081655/ref=sr_1_12?crid=15963283P4C0V&keywords=kubernetes&qid=1653935057&s=books&sprefix=kubernetes%2Cstripbooks%2C174&sr=1-12)
207 |
208 | - [Kubernetes Best Practices: Blueprints for Building Successful Applications on Kubernetes](https://www.amazon.com/Kubernetes-Best-Practices-Blueprints-Applications/dp/1492056472/ref=sr_1_19?crid=15963283P4C0V&keywords=kubernetes&qid=1653935057&s=books&sprefix=kubernetes%2Cstripbooks%2C174&sr=1-19)
209 |
210 | - [Kubernetes Security and Observability: A Holistic Approach to Securing Containers and Cloud Native Apps](https://www.amazon.com/Kubernetes-Security-Observability-Containers-Applications/dp/1098107101/ref=sr_1_26?crid=15963283P4C0V&keywords=kubernetes&qid=1653935057&s=books&sprefix=kubernetes%2Cstripbooks%2C174&sr=1-26)
211 |
212 | - [Hands-on Kubernetes on Azure: Use Azure Kubernetes Service to automate management, scaling, and deployment of containerized apps](https://www.amazon.com/Hands-Kubernetes-Azure-containerized-applications-ebook/dp/B095H26VFY/ref=sr_1_11?crid=15963283P4C0V&keywords=kubernetes&qid=1653935057&s=books&sprefix=kubernetes%2Cstripbooks%2C174&sr=1-11)
213 |
214 | ### YouTube Tutorials
215 | [Back to the Top](#table-of-contents)
216 |
217 | [](https://www.youtube.com/watch?v=kGrpLKNi4ZI)
218 | [](https://www.youtube.com/watch?v=Oe_mhDtb22M)
219 | [](https://www.youtube.com/watch?v=vxtq_pJp7_A)
220 | [](https://www.youtube.com/watch?v=S8eX0MxfnB4)
221 | [")](https://www.youtube.com/watch?v=d6WC5n9G_sM)
222 | [](https://www.youtube.com/watch?v=VnvRFRk_51k)
223 | [](https://www.youtube.com/watch?v=wXuSqFJVNQA)
224 | [](https://www.youtube.com/watch?v=kTp5xUtcalw)
225 | [](https://www.youtube.com/watch?v=PziYflu8cB8)
226 | [](https://www.youtube.com/watch?v=n-fAf2mte6M)
227 |
228 | ### Red Hat CodeReady Containers (CRC) on WSL
229 |
230 | [Back to the Top](#table-of-contents)
231 |
232 | [Red Hat CodeReady Containers (CRC)](https://developers.redhat.com/content-gateway/rest/mirror/pub/openshift-v4/clients/crc/2.9.0) is a tool that provides a minimal, preconfigured OpenShift 4 cluster on a laptop or desktop machine for development and testing purposes. CRC is delivered as a platform inside of the VM.
233 |
234 | * **odo (OpenShift Do)**, a CLI tool for developers, to manage application components on the OpenShift Container Platform.
235 |
236 |
94 |
95 | **Building Highly-Availability(HA) Clusters with kubeadm. Source: [Kubernetes.io](https://kubernetes.io/docs/setup/production-environment/tools/kubeadm/high-availability/)**
96 |
97 | ### Developer Resources
98 | [Back to the Top](#table-of-contents)
99 |
100 | - [Kubernetes Certifications](https://kubernetes.io/training/)
101 |
102 | - [Getting started with Kubernetes on AWS](https://aws.amazon.com/kubernetes/)
103 |
104 | - [Kubernetes on Microsoft Azure](https://azure.microsoft.com/en-us/topic/what-is-kubernetes/)
105 |
106 | - [Intro to Azure Kubernetes Service](https://docs.microsoft.com/en-us/azure/aks/kubernetes-dashboard)
107 |
108 | - [Getting started with Google Cloud](https://cloud.google.com/learn/what-is-kubernetes)
109 |
110 | - [Azure Red Hat OpenShift ](https://azure.microsoft.com/en-us/services/openshift/)
111 |
112 | - [Getting started with Kubernetes on Red Hat](https://www.redhat.com/en/topics/containers/what-is-kubernetes)
113 |
114 | - [Getting started with Kubernetes on IBM](https://www.ibm.com/cloud/learn/kubernetes)
115 |
116 | - [Red Hat OpenShift on IBM Cloud](https://www.ibm.com/cloud/openshift)
117 |
118 | - [Kubernetes Contributors](https://www.kubernetes.dev/)
119 |
120 | - [Kubernetes Tutorials from Pulumi](https://www.pulumi.com/docs/tutorials/kubernetes/)
121 |
122 | - [Enable OpenShift Virtualization on Red Hat OpenShift](https://developers.redhat.com/blog/2020/08/28/enable-openshift-virtualization-on-red-hat-openshift/)
123 |
124 | - [YAML basics in Kubernetes](https://developer.ibm.com/technologies/containers/tutorials/yaml-basics-and-usage-in-kubernetes/)
125 |
126 | - [Elastic Cloud on Kubernetes](https://www.elastic.co/elastic-cloud-kubernetes)
127 |
128 | - [Docker and Kubernetes](https://www.docker.com/products/kubernetes)
129 |
130 | - [Running Apache Spark on Kubernetes](http://spark.apache.org/docs/latest/running-on-kubernetes.html)
131 |
132 | - [Kubernetes Across VMware vRealize Automation](https://blogs.vmware.com/management/2019/06/kubernetes-across-vmware-cloud-automation-services.html)
133 |
134 | - [VMware Tanzu Kubernetes Grid](https://tanzu.vmware.com/kubernetes-grid)
135 |
136 | - [All the Ways VMware Tanzu Works with AWS](https://tanzu.vmware.com/content/blog/all-the-ways-vmware-tanzutm-works-with-aws)
137 |
138 | - [Using Ansible in a Cloud-Native Kubernetes Environment](https://www.ansible.com/blog/how-useful-is-ansible-in-a-cloud-native-kubernetes-environment)
139 |
140 | - [Managing Kubernetes (K8s) objects with Ansible](https://docs.ansible.com/ansible/latest/collections/community/kubernetes/k8s_module.html)
141 |
142 | - [Setting up a Kubernetes cluster using Vagrant and Ansible](https://kubernetes.io/blog/2019/03/15/kubernetes-setup-using-ansible-and-vagrant/)
143 |
144 | - [Running MongoDB with Kubernetes](https://www.mongodb.com/kubernetes)
145 |
146 | - [Kubernetes Fluentd](https://docs.fluentd.org/v/0.12/articles/kubernetes-fluentd)
147 |
148 | - [Understanding the new GitLab Kubernetes Agent](https://about.gitlab.com/blog/2020/09/22/introducing-the-gitlab-kubernetes-agent/)
149 |
150 | - [Intro Local Process with Kubernetes for Visual Studio 2019](https://devblogs.microsoft.com/visualstudio/introducing-local-process-with-kubernetes-for-visual-studio%E2%80%AF2019/)
151 |
152 | - [Kubernetes Playground by Katacoda](https://www.katacoda.com/courses/kubernetes/playground)
153 |
154 | ### Kubernetes Courses & Certifications
155 | [Back to the Top](#table-of-contents)
156 |
157 | - [Kubernetes Training & Certifications](https://kubernetes.io/training/)
158 |
159 | - [Top Kubernetes Courses Online | Coursera](https://www.coursera.org/courses?query=kubernetes)
160 |
161 | - [Top Kubernetes Courses Online | Udemy](https://www.udemy.com/topic/kubernetes/)
162 |
163 | - [Kubernetes Courses - IBM Developer](https://developer.ibm.com/components/kubernetes/courses/)
164 |
165 | - [Introduction to Kubernetes Courses | edX](https://www.edx.org/course/introduction-to-kubernetes)
166 |
167 | - [VMware Tanzu Education](https://tanzu.vmware.com/education)
168 |
169 | - [KubeAcademy from VMware](https://kube.academy/)
170 |
171 | - [Online Kubernetes Course: Beginners Guide to Kubernetes | Pluralsight](https://www.pluralsight.com/courses/getting-started-kubernetes)
172 |
173 | - [Getting Started with Google Kubernetes Engine | Pluralsight](https://www.pluralsight.com/courses/getting-started-google-kubernetes-engine-8)
174 |
175 | - [Scalable Microservices with Kubernetes course from Udacity](https://www.udacity.com/course/scalable-microservices-with-kubernetes--ud615)
176 |
177 | ### Kubernetes Books
178 | [Back to the Top](#table-of-contents)
179 |
180 | - [Kubernetes for Full-Stack Developers by Digital Ocean](https://assets.digitalocean.com/books/kubernetes-for-full-stack-developers.pdf)
181 |
182 | - [Kubernetes Patterns - Red Hat](https://www.redhat.com/cms/managed-files/cm-oreilly-kubernetes-patterns-ebook-f19824-201910-en.pdf)
183 |
184 | - [The Ultimate Guide to Kubernetes Deployments with Octopus](https://i.octopus.com/books/kubernetes-book.pdf)
185 |
186 | - [Learng Kubernetes (PDF)](https://riptutorial.com/Download/kubernetes.pdf)
187 |
188 | - [Certified Kubernetes Administrator (CKA) Study Guide: In-Depth Guidance and Practice](https://www.amazon.com/Certified-Kubernetes-Administrator-Study-Depth/dp/1098107225/ref=sr_1_29?crid=15963283P4C0V&keywords=kubernetes&qid=1653935057&s=books&sprefix=kubernetes%2Cstripbooks%2C174&sr=1-29)
189 |
190 | - [Quick Start Kubernetes by Nigel Poulton (2022)](https://www.amazon.com/Quick-Start-Kubernetes-Nigel-Poulton-ebook/dp/B08T21NW4Z/ref=sr_1_18?crid=15963283P4C0V&keywords=kubernetes&qid=1653935057&s=books&sprefix=kubernetes%2Cstripbooks%2C174&sr=1-18)
191 |
192 | - [The Kubernetes Book by Nigel Poulton (2022)](https://www.amazon.com/Kubernetes-Book-Version-November-2018-ebook/dp/B072TS9ZQZ/ref=sr_1_4?crid=15963283P4C0V&keywords=kubernetes&qid=1653935057&s=books&sprefix=kubernetes%2Cstripbooks%2C174&sr=1-4)
193 |
194 | - [Kubernetes: Up and Running: Dive into the Future of Infrastructure](https://www.amazon.com/Kubernetes-Running-Dive-Future-Infrastructure/dp/1492046531/ref=sr_1_5?crid=15963283P4C0V&keywords=kubernetes&qid=1653935057&s=books&sprefix=kubernetes%2Cstripbooks%2C174&sr=1-5)
195 |
196 | - [Kubernetes and Docker - An Enterprise Guide: Effectively containerize applications, integrate enterprise systems, and scale applications in your enterprise](https://www.amazon.com/Kubernetes-Docker-Effectively-containerize-applications/dp/183921340X/ref=sr_1_24?crid=15963283P4C0V&keywords=kubernetes&qid=1653935057&s=books&sprefix=kubernetes%2Cstripbooks%2C174&sr=1-24)
197 |
198 | - [Kubernetes in Action](https://www.amazon.com/Kubernetes-Action-Marko-Luksa/dp/1617293725/ref=sr_1_7?crid=15963283P4C0V&keywords=kubernetes&qid=1653935057&s=books&sprefix=kubernetes%2Cstripbooks%2C174&sr=1-7)
199 |
200 | - [Kubernetes – An Enterprise Guide: Effectively containerize applications, integrate enterprise systems, and scale](https://www.amazon.com/Kubernetes-Enterprise-Effectively-containerize-applications/dp/1803230037/ref=sr_1_6?crid=15963283P4C0V&keywords=kubernetes&qid=1653935057&s=books&sprefix=kubernetes%2Cstripbooks%2C174&sr=1-6)
201 |
202 | - [Production Kubernetes: Building Successful Application Platforms](https://www.amazon.com/Production-Kubernetes-Successful-Application-Platforms/dp/1492092304/ref=sr_1_8?crid=15963283P4C0V&keywords=kubernetes&qid=1653935057&s=books&sprefix=kubernetes%2Cstripbooks%2C174&sr=1-8)
203 |
204 | - [The Kubernetes Bible: The definitive guide to deploying and managing Kubernetes across major cloud platforms](https://www.amazon.com/Kubernetes-Bible-definitive-deploying-platforms/dp/1838827692/ref=sr_1_16?crid=15963283P4C0V&keywords=kubernetes&qid=1653935057&s=books&sprefix=kubernetes%2Cstripbooks%2C174&sr=1-16)
205 |
206 | - [Networking and Kubernetes: A Layered Approach](https://www.amazon.com/Networking-Kubernetes-Approach-James-Strong/dp/1492081655/ref=sr_1_12?crid=15963283P4C0V&keywords=kubernetes&qid=1653935057&s=books&sprefix=kubernetes%2Cstripbooks%2C174&sr=1-12)
207 |
208 | - [Kubernetes Best Practices: Blueprints for Building Successful Applications on Kubernetes](https://www.amazon.com/Kubernetes-Best-Practices-Blueprints-Applications/dp/1492056472/ref=sr_1_19?crid=15963283P4C0V&keywords=kubernetes&qid=1653935057&s=books&sprefix=kubernetes%2Cstripbooks%2C174&sr=1-19)
209 |
210 | - [Kubernetes Security and Observability: A Holistic Approach to Securing Containers and Cloud Native Apps](https://www.amazon.com/Kubernetes-Security-Observability-Containers-Applications/dp/1098107101/ref=sr_1_26?crid=15963283P4C0V&keywords=kubernetes&qid=1653935057&s=books&sprefix=kubernetes%2Cstripbooks%2C174&sr=1-26)
211 |
212 | - [Hands-on Kubernetes on Azure: Use Azure Kubernetes Service to automate management, scaling, and deployment of containerized apps](https://www.amazon.com/Hands-Kubernetes-Azure-containerized-applications-ebook/dp/B095H26VFY/ref=sr_1_11?crid=15963283P4C0V&keywords=kubernetes&qid=1653935057&s=books&sprefix=kubernetes%2Cstripbooks%2C174&sr=1-11)
213 |
214 | ### YouTube Tutorials
215 | [Back to the Top](#table-of-contents)
216 |
217 | [](https://www.youtube.com/watch?v=kGrpLKNi4ZI)
218 | [](https://www.youtube.com/watch?v=Oe_mhDtb22M)
219 | [](https://www.youtube.com/watch?v=vxtq_pJp7_A)
220 | [](https://www.youtube.com/watch?v=S8eX0MxfnB4)
221 | [")](https://www.youtube.com/watch?v=d6WC5n9G_sM)
222 | [](https://www.youtube.com/watch?v=VnvRFRk_51k)
223 | [](https://www.youtube.com/watch?v=wXuSqFJVNQA)
224 | [](https://www.youtube.com/watch?v=kTp5xUtcalw)
225 | [](https://www.youtube.com/watch?v=PziYflu8cB8)
226 | [](https://www.youtube.com/watch?v=n-fAf2mte6M)
227 |
228 | ### Red Hat CodeReady Containers (CRC) on WSL
229 |
230 | [Back to the Top](#table-of-contents)
231 |
232 | [Red Hat CodeReady Containers (CRC)](https://developers.redhat.com/content-gateway/rest/mirror/pub/openshift-v4/clients/crc/2.9.0) is a tool that provides a minimal, preconfigured OpenShift 4 cluster on a laptop or desktop machine for development and testing purposes. CRC is delivered as a platform inside of the VM.
233 |
234 | * **odo (OpenShift Do)**, a CLI tool for developers, to manage application components on the OpenShift Container Platform.
235 |
236 |
237 |  238 |
238 |
239 |
320 |  321 |
321 |
322 |
337 |  338 |
338 |
339 | Podman
340 |
355 |  356 |
356 |
357 | Buildah
358 |
375 |  376 |
376 |
377 | Rancher Desktop
378 |
381 |  382 |
382 |
383 | Rancher Desktop Kubernetes Settings
384 |
413 |  414 |
414 |
415 | Rancher Desktop Architecture Overview
416 |
423 |  424 |
424 |
425 | Enable the WSL 2 base engine in Docker Desktop
426 |
431 |  432 |
432 |
433 |
629 |  630 |
630 |
631 |
638 |  639 |
639 |
640 |
731 |  732 |
732 |
733 |
740 |  741 |
741 |
742 |
749 |  750 |
750 |
751 |
758 |  759 |
759 |
760 |
767 |  768 |
768 |
769 |
776 |  777 |
777 |
778 |
785 |  786 |
786 |
787 |
794 |  795 |
795 |
796 |
807 |  808 |
808 |
809 |
816 |  817 |
817 |
818 |
825 |  826 |
826 |
827 |
834 |  835 |
835 |
836 |
843 |  844 |
844 |
845 |
854 |  855 |
855 |
856 |
908 |  909 |
909 |
910 |
915 |  916 |
916 |
917 |
1012 |  1013 |
1013 |
1014 |
1043 |
1044 |
1045 |
1050 |
1051 |
1052 |
1090 |  1091 |
1091 |
1092 |
1100 |  1101 |
1101 |
1102 | Installing Red Hat OpenShift Data Science
1103 |
1106 |  1107 |
1107 |
1108 | Opening Red Hat OpenShift Data Science
1109 |
1112 |  1113 |
1113 |
1114 | JuypterHub on Red Hat OpenShift Data Science
1115 |
1118 |  1119 |
1119 |
1120 | Exploring Tools on Red Hat OpenShift Data Science
1121 |
1124 |  1125 |
1125 |
1126 | Setting up JupyterHub Notebook Server
1127 |
1130 |  1131 |
1131 |
1132 | Creating a new Python 3 Notebook
1133 |
1136 |  1137 |
1137 |
1138 | Python 3 JupyterHub Notebook
1139 |
1142 |  1143 |
1143 |
1144 | JupyterHub Notebook Sample Demo
1145 |
1148 |  1149 |
1149 |
1150 | OpenShift Project Models
1151 |
1154 |  1155 |
1155 |
1156 | How OpenShift integrates with JupyterHub using Python - Source-to-Image (S2I)
1157 |
1168 |  1169 |
1169 |
1170 |
1251 |  1252 |
1252 |
1253 |
1275 |  1276 |
1276 |
1277 | Podman Desktop
1278 |
1281 |  1282 |
1282 |
1283 | Podman
1284 |
1300 |  1301 |
1301 |
1302 | Buildah
1303 |
1312 |  1313 |
1313 |
1314 |
 1688 |
1689 | ## ML Learning Resources
1690 |
1691 | [Kubernetes for Machine Learning on Platform9](https://platform9.com/blog/kubernetes-for-machine-learning/)
1692 |
1693 | [Introducing Amazon SageMaker Operators for Kubernetes](https://aws.amazon.com/blogs/machine-learning/introducing-amazon-sagemaker-operators-for-kubernetes/)
1694 |
1695 | [Deploying machine learning models on Kubernetes with Google Cloud](https://cloud.google.com/community/tutorials/kubernetes-ml-ops)
1696 |
1697 | [Create and attach Azure Kubernetes Service with Azure Machine Learning](https://docs.microsoft.com/en-us/azure/machine-learning/how-to-create-attach-kubernetes)
1698 |
1699 | [Kubernetes for MLOps: Scaling Enterprise Machine Learning, Deep Learning, AI with HPE](https://www.hpe.com/us/en/resources/solutions/kubernetes-mlops.html)
1700 |
1701 | [Machine Learning by Stanford University from Coursera](https://www.coursera.org/learn/machine-learning)
1702 |
1703 | [Machine Learning Courses Online from Coursera](https://www.coursera.org/courses?query=machine%20learning&)
1704 |
1705 | [Machine Learning Courses Online from Udemy](https://www.udemy.com/topic/machine-learning/)
1706 |
1707 | [Learn Machine Learning with Online Courses and Classes from edX](https://www.edx.org/learn/machine-learning)
1708 |
1709 | ## ML frameworks & applications
1710 |
1711 | [TensorFlow](https://www.tensorflow.org) is an end-to-end open source platform for machine learning. It has a comprehensive, flexible ecosystem of tools, libraries and community resources that lets researchers push the state-of-the-art in ML and developers easily build and deploy ML powered applications.
1712 |
1713 | [Tensorman](https://github.com/pop-os/tensorman) is a utility for easy management of Tensorflow containers by developed by [System76]( https://system76.com).Tensorman allows Tensorflow to operate in an isolated environment that is contained from the rest of the system. This virtual environment can operate independent of the base system, allowing you to use any version of Tensorflow on any version of a Linux distribution that supports the Docker runtime.
1714 |
1715 | [Keras](https://keras.io) is a high-level neural networks API, written in Python and capable of running on top of TensorFlow, CNTK, or Theano.It was developed with a focus on enabling fast experimentation. It is capable of running on top of TensorFlow, Microsoft Cognitive Toolkit, R, Theano, or PlaidML.
1716 |
1717 | [PyTorch](https://pytorch.org) is a library for deep learning on irregular input data such as graphs, point clouds, and manifolds. Primarily developed by Facebook's AI Research lab.
1718 |
1719 | [Amazon SageMaker](https://aws.amazon.com/sagemaker/) is a fully managed service that provides every developer and data scientist with the ability to build, train, and deploy machine learning (ML) models quickly. SageMaker removes the heavy lifting from each step of the machine learning process to make it easier to develop high quality models.
1720 |
1721 | [Azure Databricks](https://azure.microsoft.com/en-us/services/databricks/) is a fast and collaborative Apache Spark-based big data analytics service designed for data science and data engineering. Azure Databricks, sets up your Apache Spark environment in minutes, autoscale, and collaborate on shared projects in an interactive workspace. Azure Databricks supports Python, Scala, R, Java, and SQL, as well as data science frameworks and libraries including TensorFlow, PyTorch, and scikit-learn.
1722 |
1723 | [Microsoft Cognitive Toolkit (CNTK)](https://docs.microsoft.com/en-us/cognitive-toolkit/) is an open-source toolkit for commercial-grade distributed deep learning. It describes neural networks as a series of computational steps via a directed graph. CNTK allows the user to easily realize and combine popular model types such as feed-forward DNNs, convolutional neural networks (CNNs) and recurrent neural networks (RNNs/LSTMs). CNTK implements stochastic gradient descent (SGD, error backpropagation) learning with automatic differentiation and parallelization across multiple GPUs and servers.
1724 |
1725 | [Apache Airflow](https://airflow.apache.org) is an open-source workflow management platform created by the community to programmatically author, schedule and monitor workflows. Install. Principles. Scalable. Airflow has a modular architecture and uses a message queue to orchestrate an arbitrary number of workers. Airflow is ready to scale to infinity.
1726 |
1727 | [Open Neural Network Exchange(ONNX)](https://github.com/onnx) is an open ecosystem that empowers AI developers to choose the right tools as their project evolves. ONNX provides an open source format for AI models, both deep learning and traditional ML. It defines an extensible computation graph model, as well as definitions of built-in operators and standard data types.
1728 |
1729 | [Apache MXNet](https://mxnet.apache.org/) is a deep learning framework designed for both efficiency and flexibility. It allows you to mix symbolic and imperative programming to maximize efficiency and productivity. At its core, MXNet contains a dynamic dependency scheduler that automatically parallelizes both symbolic and imperative operations on the fly. A graph optimization layer on top of that makes symbolic execution fast and memory efficient. MXNet is portable and lightweight, scaling effectively to multiple GPUs and multiple machines. Support for Python, R, Julia, Scala, Go, Javascript and more.
1730 |
1731 | [AutoGluon](https://autogluon.mxnet.io/index.html) is toolkit for Deep learning that automates machine learning tasks enabling you to easily achieve strong predictive performance in your applications. With just a few lines of code, you can train and deploy high-accuracy deep learning models on tabular, image, and text data.
1732 |
1733 | [Anaconda](https://www.anaconda.com/) is a very popular Data Science platform for machine learning and deep learning that enables users to develop models, train them, and deploy them.
1734 |
1735 | [PlaidML](https://github.com/plaidml/plaidml) is an advanced and portable tensor compiler for enabling deep learning on laptops, embedded devices, or other devices where the available computing hardware is not well supported or the available software stack contains unpalatable license restrictions.
1736 |
1737 | [OpenCV](https://opencv.org) is a highly optimized library with focus on real-time computer vision applications. The C++, Python, and Java interfaces support Linux, MacOS, Windows, iOS, and Android.
1738 |
1739 | [Scikit-Learn](https://scikit-learn.org/stable/index.html) is a Python module for machine learning built on top of SciPy, NumPy, and matplotlib, making it easier to apply robust and simple implementations of many popular machine learning algorithms.
1740 |
1741 | [Weka](https://www.cs.waikato.ac.nz/ml/weka/) is an open source machine learning software that can be accessed through a graphical user interface, standard terminal applications, or a Java API. It is widely used for teaching, research, and industrial applications, contains a plethora of built-in tools for standard machine learning tasks, and additionally gives transparent access to well-known toolboxes such as scikit-learn, R, and Deeplearning4j.
1742 |
1743 | [Caffe](https://github.com/BVLC/caffe) is a deep learning framework made with expression, speed, and modularity in mind. It is developed by Berkeley AI Research (BAIR)/The Berkeley Vision and Learning Center (BVLC) and community contributors.
1744 |
1745 | [Theano](https://github.com/Theano/Theano) is a Python library that allows you to define, optimize, and evaluate mathematical expressions involving multi-dimensional arrays efficiently including tight integration with NumPy.
1746 |
1747 | [nGraph](https://github.com/NervanaSystems/ngraph) is an open source C++ library, compiler and runtime for Deep Learning. The nGraph Compiler aims to accelerate developing AI workloads using any deep learning framework and deploying to a variety of hardware targets.It provides the freedom, performance, and ease-of-use to AI developers.
1748 |
1749 | [NVIDIA cuDNN](https://developer.nvidia.com/cudnn) is a GPU-accelerated library of primitives for [deep neural networks](https://developer.nvidia.com/deep-learning). cuDNN provides highly tuned implementations for standard routines such as forward and backward convolution, pooling, normalization, and activation layers. cuDNN accelerates widely used deep learning frameworks, including [Caffe2](https://caffe2.ai/), [Chainer](https://chainer.org/), [Keras](https://keras.io/), [MATLAB](https://www.mathworks.com/solutions/deep-learning.html), [MxNet](https://mxnet.incubator.apache.org/), [PyTorch](https://pytorch.org/), and [TensorFlow](https://www.tensorflow.org/).
1750 |
1751 | [Jupyter Notebook](https://jupyter.org/) is an open-source web application that allows you to create and share documents that contain live code, equations, visualizations and narrative text. Jupyter is used widely in industries that do data cleaning and transformation, numerical simulation, statistical modeling, data visualization, data science, and machine learning.
1752 |
1753 | [Apache Spark](https://spark.apache.org/) is a unified analytics engine for large-scale data processing. It provides high-level APIs in Scala, Java, Python, and R, and an optimized engine that supports general computation graphs for data analysis. It also supports a rich set of higher-level tools including Spark SQL for SQL and DataFrames, MLlib for machine learning, GraphX for graph processing, and Structured Streaming for stream processing.
1754 |
1755 | [Apache Spark Connector for SQL Server and Azure SQL](https://github.com/microsoft/sql-spark-connector) is a high-performance connector that enables you to use transactional data in big data analytics and persists results for ad-hoc queries or reporting. The connector allows you to use any SQL database, on-premises or in the cloud, as an input data source or output data sink for Spark jobs.
1756 |
1757 | [Apache PredictionIO](https://predictionio.apache.org/) is an open source machine learning framework for developers, data scientists, and end users. It supports event collection, deployment of algorithms, evaluation, querying predictive results via REST APIs. It is based on scalable open source services like Hadoop, HBase (and other DBs), Elasticsearch, Spark and implements what is called a Lambda Architecture.
1758 |
1759 | [Cluster Manager for Apache Kafka(CMAK)](https://github.com/yahoo/CMAK) is a tool for managing [Apache Kafka](https://kafka.apache.org/) clusters.
1760 |
1761 | [BigDL](https://bigdl-project.github.io/) is a distributed deep learning library for Apache Spark. With BigDL, users can write their deep learning applications as standard Spark programs, which can directly run on top of existing Spark or Hadoop clusters.
1762 |
1763 | [Koalas](https://pypi.org/project/koalas/) is project makes data scientists more productive when interacting with big data, by implementing the pandas DataFrame API on top of Apache Spark.
1764 |
1765 | [Apache Spark™ MLflow](https://mlflow.org/) is an open source platform to manage the ML lifecycle, including experimentation, reproducibility, deployment, and a central model registry. MLflow currently offers four components:
1766 |
1767 | **[MLflow Tracking](https://mlflow.org/docs/latest/tracking.html)**: Record and query experiments: code, data, config, and results.
1768 |
1769 | **[MLflow Projects](https://mlflow.org/docs/latest/projects.html)**: Package data science code in a format to reproduce runs on any platform.
1770 |
1771 | **[MLflow Models](https://mlflow.org/docs/latest/models.html)**: Deploy machine learning models in diverse serving environments.
1772 |
1773 | **[Model Registry](https://mlflow.org/docs/latest/model-registry.html)**: Store, annotate, discover, and manage models in a central repository.
1774 |
1775 | [Eclipse Deeplearning4J (DL4J)](https://deeplearning4j.konduit.ai/) is a set of projects intended to support all the needs of a JVM-based(Scala, Kotlin, Clojure, and Groovy) deep learning application. This means starting with the raw data, loading and preprocessing it from wherever and whatever format it is in to building and tuning a wide variety of simple and complex deep learning networks.
1776 |
1777 | [Numba](https://github.com/numba/numba) is an open source, NumPy-aware optimizing compiler for Python sponsored by Anaconda, Inc. It uses the LLVM compiler project to generate machine code from Python syntax. Numba can compile a large subset of numerically-focused Python, including many NumPy functions. Additionally, Numba has support for automatic parallelization of loops, generation of GPU-accelerated code, and creation of ufuncs and C callbacks.
1778 |
1779 | [Chainer](https://chainer.org/) is a Python-based deep learning framework aiming at flexibility. It provides automatic differentiation APIs based on the define-by-run approach (dynamic computational graphs) as well as object-oriented high-level APIs to build and train neural networks. It also supports CUDA/cuDNN using [CuPy](https://github.com/cupy/cupy) for high performance training and inference.
1780 |
1781 | [cuML](https://github.com/rapidsai/cuml) is a suite of libraries that implement machine learning algorithms and mathematical primitives functions that share compatible APIs with other RAPIDS projects. cuML enables data scientists, researchers, and software engineers to run traditional tabular ML tasks on GPUs without going into the details of CUDA programming. In most cases, cuML's Python API matches the API from scikit-learn.
1782 |
1783 | # Networking
1784 |
1785 | [Back to the Top](https://github.com/mikeroyal/kubernetes-Guide/blob/main/README.md#table-of-contents)
1786 |
1787 |
1688 |
1689 | ## ML Learning Resources
1690 |
1691 | [Kubernetes for Machine Learning on Platform9](https://platform9.com/blog/kubernetes-for-machine-learning/)
1692 |
1693 | [Introducing Amazon SageMaker Operators for Kubernetes](https://aws.amazon.com/blogs/machine-learning/introducing-amazon-sagemaker-operators-for-kubernetes/)
1694 |
1695 | [Deploying machine learning models on Kubernetes with Google Cloud](https://cloud.google.com/community/tutorials/kubernetes-ml-ops)
1696 |
1697 | [Create and attach Azure Kubernetes Service with Azure Machine Learning](https://docs.microsoft.com/en-us/azure/machine-learning/how-to-create-attach-kubernetes)
1698 |
1699 | [Kubernetes for MLOps: Scaling Enterprise Machine Learning, Deep Learning, AI with HPE](https://www.hpe.com/us/en/resources/solutions/kubernetes-mlops.html)
1700 |
1701 | [Machine Learning by Stanford University from Coursera](https://www.coursera.org/learn/machine-learning)
1702 |
1703 | [Machine Learning Courses Online from Coursera](https://www.coursera.org/courses?query=machine%20learning&)
1704 |
1705 | [Machine Learning Courses Online from Udemy](https://www.udemy.com/topic/machine-learning/)
1706 |
1707 | [Learn Machine Learning with Online Courses and Classes from edX](https://www.edx.org/learn/machine-learning)
1708 |
1709 | ## ML frameworks & applications
1710 |
1711 | [TensorFlow](https://www.tensorflow.org) is an end-to-end open source platform for machine learning. It has a comprehensive, flexible ecosystem of tools, libraries and community resources that lets researchers push the state-of-the-art in ML and developers easily build and deploy ML powered applications.
1712 |
1713 | [Tensorman](https://github.com/pop-os/tensorman) is a utility for easy management of Tensorflow containers by developed by [System76]( https://system76.com).Tensorman allows Tensorflow to operate in an isolated environment that is contained from the rest of the system. This virtual environment can operate independent of the base system, allowing you to use any version of Tensorflow on any version of a Linux distribution that supports the Docker runtime.
1714 |
1715 | [Keras](https://keras.io) is a high-level neural networks API, written in Python and capable of running on top of TensorFlow, CNTK, or Theano.It was developed with a focus on enabling fast experimentation. It is capable of running on top of TensorFlow, Microsoft Cognitive Toolkit, R, Theano, or PlaidML.
1716 |
1717 | [PyTorch](https://pytorch.org) is a library for deep learning on irregular input data such as graphs, point clouds, and manifolds. Primarily developed by Facebook's AI Research lab.
1718 |
1719 | [Amazon SageMaker](https://aws.amazon.com/sagemaker/) is a fully managed service that provides every developer and data scientist with the ability to build, train, and deploy machine learning (ML) models quickly. SageMaker removes the heavy lifting from each step of the machine learning process to make it easier to develop high quality models.
1720 |
1721 | [Azure Databricks](https://azure.microsoft.com/en-us/services/databricks/) is a fast and collaborative Apache Spark-based big data analytics service designed for data science and data engineering. Azure Databricks, sets up your Apache Spark environment in minutes, autoscale, and collaborate on shared projects in an interactive workspace. Azure Databricks supports Python, Scala, R, Java, and SQL, as well as data science frameworks and libraries including TensorFlow, PyTorch, and scikit-learn.
1722 |
1723 | [Microsoft Cognitive Toolkit (CNTK)](https://docs.microsoft.com/en-us/cognitive-toolkit/) is an open-source toolkit for commercial-grade distributed deep learning. It describes neural networks as a series of computational steps via a directed graph. CNTK allows the user to easily realize and combine popular model types such as feed-forward DNNs, convolutional neural networks (CNNs) and recurrent neural networks (RNNs/LSTMs). CNTK implements stochastic gradient descent (SGD, error backpropagation) learning with automatic differentiation and parallelization across multiple GPUs and servers.
1724 |
1725 | [Apache Airflow](https://airflow.apache.org) is an open-source workflow management platform created by the community to programmatically author, schedule and monitor workflows. Install. Principles. Scalable. Airflow has a modular architecture and uses a message queue to orchestrate an arbitrary number of workers. Airflow is ready to scale to infinity.
1726 |
1727 | [Open Neural Network Exchange(ONNX)](https://github.com/onnx) is an open ecosystem that empowers AI developers to choose the right tools as their project evolves. ONNX provides an open source format for AI models, both deep learning and traditional ML. It defines an extensible computation graph model, as well as definitions of built-in operators and standard data types.
1728 |
1729 | [Apache MXNet](https://mxnet.apache.org/) is a deep learning framework designed for both efficiency and flexibility. It allows you to mix symbolic and imperative programming to maximize efficiency and productivity. At its core, MXNet contains a dynamic dependency scheduler that automatically parallelizes both symbolic and imperative operations on the fly. A graph optimization layer on top of that makes symbolic execution fast and memory efficient. MXNet is portable and lightweight, scaling effectively to multiple GPUs and multiple machines. Support for Python, R, Julia, Scala, Go, Javascript and more.
1730 |
1731 | [AutoGluon](https://autogluon.mxnet.io/index.html) is toolkit for Deep learning that automates machine learning tasks enabling you to easily achieve strong predictive performance in your applications. With just a few lines of code, you can train and deploy high-accuracy deep learning models on tabular, image, and text data.
1732 |
1733 | [Anaconda](https://www.anaconda.com/) is a very popular Data Science platform for machine learning and deep learning that enables users to develop models, train them, and deploy them.
1734 |
1735 | [PlaidML](https://github.com/plaidml/plaidml) is an advanced and portable tensor compiler for enabling deep learning on laptops, embedded devices, or other devices where the available computing hardware is not well supported or the available software stack contains unpalatable license restrictions.
1736 |
1737 | [OpenCV](https://opencv.org) is a highly optimized library with focus on real-time computer vision applications. The C++, Python, and Java interfaces support Linux, MacOS, Windows, iOS, and Android.
1738 |
1739 | [Scikit-Learn](https://scikit-learn.org/stable/index.html) is a Python module for machine learning built on top of SciPy, NumPy, and matplotlib, making it easier to apply robust and simple implementations of many popular machine learning algorithms.
1740 |
1741 | [Weka](https://www.cs.waikato.ac.nz/ml/weka/) is an open source machine learning software that can be accessed through a graphical user interface, standard terminal applications, or a Java API. It is widely used for teaching, research, and industrial applications, contains a plethora of built-in tools for standard machine learning tasks, and additionally gives transparent access to well-known toolboxes such as scikit-learn, R, and Deeplearning4j.
1742 |
1743 | [Caffe](https://github.com/BVLC/caffe) is a deep learning framework made with expression, speed, and modularity in mind. It is developed by Berkeley AI Research (BAIR)/The Berkeley Vision and Learning Center (BVLC) and community contributors.
1744 |
1745 | [Theano](https://github.com/Theano/Theano) is a Python library that allows you to define, optimize, and evaluate mathematical expressions involving multi-dimensional arrays efficiently including tight integration with NumPy.
1746 |
1747 | [nGraph](https://github.com/NervanaSystems/ngraph) is an open source C++ library, compiler and runtime for Deep Learning. The nGraph Compiler aims to accelerate developing AI workloads using any deep learning framework and deploying to a variety of hardware targets.It provides the freedom, performance, and ease-of-use to AI developers.
1748 |
1749 | [NVIDIA cuDNN](https://developer.nvidia.com/cudnn) is a GPU-accelerated library of primitives for [deep neural networks](https://developer.nvidia.com/deep-learning). cuDNN provides highly tuned implementations for standard routines such as forward and backward convolution, pooling, normalization, and activation layers. cuDNN accelerates widely used deep learning frameworks, including [Caffe2](https://caffe2.ai/), [Chainer](https://chainer.org/), [Keras](https://keras.io/), [MATLAB](https://www.mathworks.com/solutions/deep-learning.html), [MxNet](https://mxnet.incubator.apache.org/), [PyTorch](https://pytorch.org/), and [TensorFlow](https://www.tensorflow.org/).
1750 |
1751 | [Jupyter Notebook](https://jupyter.org/) is an open-source web application that allows you to create and share documents that contain live code, equations, visualizations and narrative text. Jupyter is used widely in industries that do data cleaning and transformation, numerical simulation, statistical modeling, data visualization, data science, and machine learning.
1752 |
1753 | [Apache Spark](https://spark.apache.org/) is a unified analytics engine for large-scale data processing. It provides high-level APIs in Scala, Java, Python, and R, and an optimized engine that supports general computation graphs for data analysis. It also supports a rich set of higher-level tools including Spark SQL for SQL and DataFrames, MLlib for machine learning, GraphX for graph processing, and Structured Streaming for stream processing.
1754 |
1755 | [Apache Spark Connector for SQL Server and Azure SQL](https://github.com/microsoft/sql-spark-connector) is a high-performance connector that enables you to use transactional data in big data analytics and persists results for ad-hoc queries or reporting. The connector allows you to use any SQL database, on-premises or in the cloud, as an input data source or output data sink for Spark jobs.
1756 |
1757 | [Apache PredictionIO](https://predictionio.apache.org/) is an open source machine learning framework for developers, data scientists, and end users. It supports event collection, deployment of algorithms, evaluation, querying predictive results via REST APIs. It is based on scalable open source services like Hadoop, HBase (and other DBs), Elasticsearch, Spark and implements what is called a Lambda Architecture.
1758 |
1759 | [Cluster Manager for Apache Kafka(CMAK)](https://github.com/yahoo/CMAK) is a tool for managing [Apache Kafka](https://kafka.apache.org/) clusters.
1760 |
1761 | [BigDL](https://bigdl-project.github.io/) is a distributed deep learning library for Apache Spark. With BigDL, users can write their deep learning applications as standard Spark programs, which can directly run on top of existing Spark or Hadoop clusters.
1762 |
1763 | [Koalas](https://pypi.org/project/koalas/) is project makes data scientists more productive when interacting with big data, by implementing the pandas DataFrame API on top of Apache Spark.
1764 |
1765 | [Apache Spark™ MLflow](https://mlflow.org/) is an open source platform to manage the ML lifecycle, including experimentation, reproducibility, deployment, and a central model registry. MLflow currently offers four components:
1766 |
1767 | **[MLflow Tracking](https://mlflow.org/docs/latest/tracking.html)**: Record and query experiments: code, data, config, and results.
1768 |
1769 | **[MLflow Projects](https://mlflow.org/docs/latest/projects.html)**: Package data science code in a format to reproduce runs on any platform.
1770 |
1771 | **[MLflow Models](https://mlflow.org/docs/latest/models.html)**: Deploy machine learning models in diverse serving environments.
1772 |
1773 | **[Model Registry](https://mlflow.org/docs/latest/model-registry.html)**: Store, annotate, discover, and manage models in a central repository.
1774 |
1775 | [Eclipse Deeplearning4J (DL4J)](https://deeplearning4j.konduit.ai/) is a set of projects intended to support all the needs of a JVM-based(Scala, Kotlin, Clojure, and Groovy) deep learning application. This means starting with the raw data, loading and preprocessing it from wherever and whatever format it is in to building and tuning a wide variety of simple and complex deep learning networks.
1776 |
1777 | [Numba](https://github.com/numba/numba) is an open source, NumPy-aware optimizing compiler for Python sponsored by Anaconda, Inc. It uses the LLVM compiler project to generate machine code from Python syntax. Numba can compile a large subset of numerically-focused Python, including many NumPy functions. Additionally, Numba has support for automatic parallelization of loops, generation of GPU-accelerated code, and creation of ufuncs and C callbacks.
1778 |
1779 | [Chainer](https://chainer.org/) is a Python-based deep learning framework aiming at flexibility. It provides automatic differentiation APIs based on the define-by-run approach (dynamic computational graphs) as well as object-oriented high-level APIs to build and train neural networks. It also supports CUDA/cuDNN using [CuPy](https://github.com/cupy/cupy) for high performance training and inference.
1780 |
1781 | [cuML](https://github.com/rapidsai/cuml) is a suite of libraries that implement machine learning algorithms and mathematical primitives functions that share compatible APIs with other RAPIDS projects. cuML enables data scientists, researchers, and software engineers to run traditional tabular ML tasks on GPUs without going into the details of CUDA programming. In most cases, cuML's Python API matches the API from scikit-learn.
1782 |
1783 | # Networking
1784 |
1785 | [Back to the Top](https://github.com/mikeroyal/kubernetes-Guide/blob/main/README.md#table-of-contents)
1786 |
1787 |
1788 |  1789 |
1789 |
1790 |
 2080 |
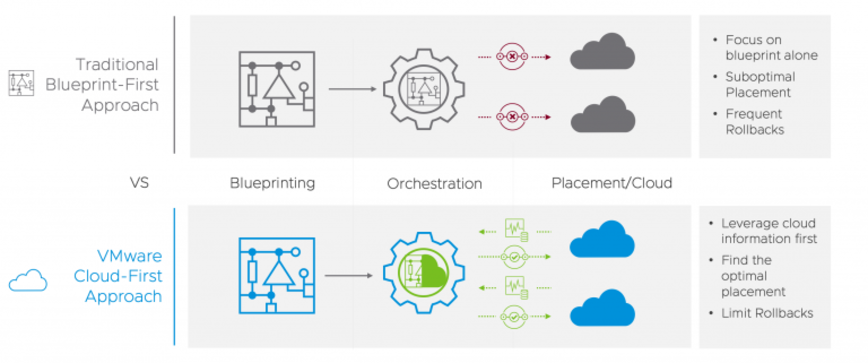
2081 | **VMware Cloud First Approach. Source: [VMware](https://www.vmware.com/products/telco-cloud-automation.html).**
2082 |
2083 |
2084 |
2080 |
2081 | **VMware Cloud First Approach. Source: [VMware](https://www.vmware.com/products/telco-cloud-automation.html).**
2082 |
2083 |
2084 |  2085 |
2086 | **VMware Telco Cloud Automation Components. Source: [VMware](https://www.vmware.com/products/telco-cloud-automation.html).**
2087 |
2088 |
2089 | ## Telco Learning Resources
2090 |
2091 | [HPE(Hewlett Packard Enterprise) Telco Blueprints overview](https://techhub.hpe.com/eginfolib/servers/docs/Telco/Blueprints/infocenter/index.html#GUID-9906A227-C1FB-4FD5-A3C3-F3B72EC81CAB.html)
2092 |
2093 | [Network Functions Virtualization Infrastructure (NFVI) by Cisco](https://www.cisco.com/c/en/us/solutions/service-provider/network-functions-virtualization-nfv-infrastructure/index.html)
2094 |
2095 | [Introduction to vCloud NFV Telco Edge from VMware](https://docs.vmware.com/en/VMware-vCloud-NFV-OpenStack-Edition/3.1/vloud-nfv-edge-reference-arch-31/GUID-744C45F1-A8D5-4523-9E5E-EAF6336EE3A0.html)
2096 |
2097 | [VMware Telco Cloud Automation(TCA) Architecture Overview](https://docs.vmware.com/en/VMware-Telco-Cloud-Platform-5G-Edition/1.0/telco-cloud-platform-5G-edition-reference-architecture/GUID-C19566B3-F42D-4351-BA55-DE70D55FB0DD.html)
2098 |
2099 | [5G Telco Cloud from VMware](https://telco.vmware.com/)
2100 |
2101 | [Maturing OpenStack Together To Solve Telco Needs from Red Hat](https://www.redhat.com/cms/managed-files/4.Nokia%20CloudBand%20&%20Red%20Hat%20-%20Maturing%20Openstack%20together%20to%20solve%20Telco%20needs%20Ehud%20Malik,%20Senior%20PLM,%20Nokia%20CloudBand.pdf)
2102 |
2103 | [Red Hat telco ecosystem program](https://connect.redhat.com/en/programs/telco-ecosystem)
2104 |
2105 | [OpenStack for Telcos by Canonical](https://ubuntu.com/blog/openstack-for-telcos-by-canonical)
2106 |
2107 | [Open source NFV platform for 5G from Ubuntu](https://ubuntu.com/telco)
2108 |
2109 | [Understanding 5G Technology from Verizon](https://www.verizon.com/5g/)
2110 |
2111 | [Verizon and Unity partner to enable 5G & MEC gaming and enterprise applications](https://www.verizon.com/about/news/verizon-unity-partner-5g-mec-gaming-enterprise)
2112 |
2113 | [Understanding 5G Technology from Intel](https://www.intel.com/content/www/us/en/wireless-network/what-is-5g.html)
2114 |
2115 | [Understanding 5G Technology from Qualcomm](https://www.qualcomm.com/invention/5g/what-is-5g)
2116 |
2117 | [Telco Acceleration with Xilinx](https://www.xilinx.com/applications/wired-wireless/telco.html)
2118 |
2119 | [VIMs on OSM Public Wiki](https://osm.etsi.org/wikipub/index.php/VIMs)
2120 |
2121 | [Amazon EC2 Overview and Networking Introduction for Telecom Companies](https://docs.aws.amazon.com/whitepapers/latest/ec2-networking-for-telecom/ec2-networking-for-telecom.pdf)
2122 |
2123 | [Citrix Certified Associate – Networking(CCA-N)](http://training.citrix.com/cms/index.php/certification/networking/)
2124 |
2125 | [Citrix Certified Professional – Virtualization(CCP-V)](https://www.globalknowledge.com/us-en/training/certification-prep/brands/citrix/section/virtualization/citrix-certified-professional-virtualization-ccp-v/)
2126 |
2127 | [CCNP Routing and Switching](https://learningnetwork.cisco.com/s/ccnp-enterprise)
2128 |
2129 | [Certified Information Security Manager(CISM)](https://www.isaca.org/credentialing/cism)
2130 |
2131 | [Wireshark Certified Network Analyst (WCNA)](https://www.wiresharktraining.com/certification.html)
2132 |
2133 | [Juniper Networks Certification Program Enterprise (JNCP)](https://www.juniper.net/us/en/training/certification/)
2134 |
2135 | [Cloud Native Computing Foundation Training and Certification Program](https://www.cncf.io/certification/training/)
2136 |
2137 |
2138 | ## Tools
2139 |
2140 | [Open Stack](https://www.openstack.org/) is an open source cloud platform, deployed as infrastructure-as-a-service (IaaS) to orchestrate data center operations on bare metal, private cloud hardware, public cloud resources, or both (hybrid/multi-cloud architecture). OpenStack includes advance use of virtualization & SDN for network traffic optimization to handle the core cloud-computing services of compute, networking, storage, identity, and image services.
2141 |
2142 | [StarlingX](https://www.starlingx.io/) is a complete cloud infrastructure software stack for the edge used by the most demanding applications in industrial IOT, telecom, video delivery and other ultra-low latency use cases.
2143 |
2144 | [Airship](https://www.airshipit.org/) is a collection of open source tools for automating cloud provisioning and management. Airship provides a declarative framework for defining and managing the life cycle of open infrastructure tools and the underlying hardware.
2145 |
2146 | [Network functions virtualization (NFV)](https://www.vmware.com/topics/glossary/content/network-functions-virtualization-nfv) is the replacement of network appliance hardware with virtual machines. The virtual machines use a hypervisor to run networking software and processes such as routing and load balancing. NFV allows for the separation of communication services from dedicated hardware, such as routers and firewalls. This separation means network operations can provide new services dynamically and without installing new hardware. Deploying network components with network functions virtualization only takes hours compared to months like with traditional networking solutions.
2147 |
2148 | [Software Defined Networking (SDN)](https://www.vmware.com/topics/glossary/content/software-defined-networking) is an approach to networking that uses software-based controllers or application programming interfaces (APIs) to communicate with underlying hardware infrastructure and direct traffic on a network. This model differs from that of traditional networks, which use dedicated hardware devices (routers and switches) to control network traffic.
2149 |
2150 | [Virtualized Infrastructure Manager (VIM)](https://www.cisco.com/c/en/us/td/docs/net_mgmt/network_function_virtualization_Infrastructure/3_2_2/install_guide/Cisco_VIM_Install_Guide_3_2_2/Cisco_VIM_Install_Guide_3_2_2_chapter_00.html) is a service delivery and reduce costs with high performance lifecycle management Manage the full lifecycle of the software and hardware comprising your NFV infrastructure (NFVI), and maintaining a live inventory and allocation plan of both physical and virtual resources.
2151 |
2152 | [Management and Orchestration(MANO)](https://www.etsi.org/technologies/open-source-mano) is an ETSI-hosted initiative to develop an Open Source NFV Management and Orchestration (MANO) software stack aligned with ETSI NFV. Two of the key components of the ETSI NFV architectural framework are the NFV Orchestrator and VNF Manager, known as NFV MANO.
2153 |
2154 | [Magma](https://www.magmacore.org/) is an open source software platform that gives network operators an open, flexible and extendable mobile core network solution. Their mission is to connect the world to a faster network by enabling service providers to build cost-effective and extensible carrier-grade networks. Magma is 3GPP generation (2G, 3G, 4G or upcoming 5G networks) and access network agnostic (cellular or WiFi). It can flexibly support a radio access network with minimal development and deployment effort.
2155 |
2156 | [OpenRAN](https://open-ran.org/) is an intelligent Radio Access Network(RAN) integrated on general purpose platforms with open interface between software defined functions. Open RANecosystem enables enormous flexibility and interoperability with a complete openess to multi-vendor deployments.
2157 |
2158 | [Open vSwitch(OVS)](https://www.openvswitch.org/)is an open source production quality, multilayer virtual switch licensed under the open source Apache 2.0 license. It is designed to enable massive network automation through programmatic extension, while still supporting standard management interfaces and protocols (NetFlow, sFlow, IPFIX, RSPAN, CLI, LACP, 802.1ag).
2159 |
2160 | [Edge](https://www.ibm.com/cloud/what-is-edge-computing) is a distributed computing framework that brings enterprise applications closer to data sources such as IoT devices or local edge servers. This proximity to data at its source can deliver strong business benefits, including faster insights, improved response times and better bandwidth availability.
2161 |
2162 | [Multi-access edge computing (MEC)](https://www.etsi.org/technologies/multi-access-edge-computing) is an Industry Specification Group (ISG) within ETSI to create a standardized, open environment which will allow the efficient and seamless integration of applications from vendors, service providers, and third-parties across multi-vendor Multi-access Edge Computing platforms.
2163 |
2164 | [Virtualized network functions(VNFs)](https://www.juniper.net/documentation/en_US/cso4.1/topics/concept/nsd-vnf-overview.html) is a software application used in a Network Functions Virtualization (NFV) implementation that has well defined interfaces, and provides one or more component networking functions in a defined way. For example, a security VNF provides Network Address Translation (NAT) and firewall component functions.
2165 |
2166 | [Cloud-Native Network Functions(CNF)](https://www.cncf.io/announcements/2020/11/18/cloud-native-network-functions-conformance-launched-by-cncf/) is a network function designed and implemented to run inside containers. CNFs inherit all the cloud native architectural and operational principles including Kubernetes(K8s) lifecycle management, agility, resilience, and observability.
2167 |
2168 | [Physical Network Function(PNF)](https://www.mpirical.com/glossary/pnf-physical-network-function) is a physical network node which has not undergone virtualization. Both PNFs and VNFs (Virtualized Network Functions) can be used to form an overall Network Service.
2169 |
2170 | [Network functions virtualization infrastructure(NFVI)](https://docs.vmware.com/en/VMware-vCloud-NFV/2.0/vmware-vcloud-nfv-reference-architecture-20/GUID-FBEA6C6B-54D8-4A37-87B1-D825F9E0DBC7.html) is the foundation of the overall NFV architecture. It provides the physical compute, storage, and networking hardware that hosts the VNFs. Each NFVI block can be thought of as an NFVI node and many nodes can be deployed and controlled geographically.
2171 |
2172 | # Open Source Security
2173 |
2174 | [Back to the Top](https://github.com/mikeroyal/Kubernetes-Guide/blob/main/README.md#table-of-contents)
2175 |
2176 |
2177 | [Open Source Security Foundation (OpenSSF)](https://openssf.org/) is a cross-industry collaboration that brings together leaders to improve the security of open source software by building a broader community, targeted initiatives, and best practices. The OpenSSF brings together open source security initiatives under one foundation to accelerate work through cross-industry support. Along with the Core Infrastructure Initiative and the Open Source Security Coalition, and will include new working groups that address vulnerability disclosures, security tooling and more.
2178 |
2179 | ## Security Standards, Frameworks and Benchmarks
2180 |
2181 | [STIGs Benchmarks - Security Technical Implementation Guides](https://public.cyber.mil/stigs/)
2182 |
2183 | [CIS Benchmarks - CIS Center for Internet Security](https://www.cisecurity.org/cis-benchmarks/)
2184 |
2185 | [CIS Top 18 Critical Security Controls](https://www.cisecurity.org/controls/cis-controls-list)
2186 |
2187 | [OSSTMM (Open Source Security Testing Methodology Manual) PDF](https://github.com/mikeroyal/Open-Source-Security-Guide/files/8834704/osstmm.en.2.1.pdf)
2188 |
2189 | [NIST Technical Guide to Information Security Testing and Assessment (PDF)](https://github.com/mikeroyal/Open-Source-Security-Guide/files/8834705/nistspecialpublication800-115.pdf)
2190 |
2191 | [NIST - Current FIPS](https://www.nist.gov/itl/current-fips)
2192 |
2193 | [ISO Standards Catalogue](https://www.iso.org/standards.html)
2194 |
2195 | [Common Criteria for Information Technology Security Evaluation (CC)](https://www.commoncriteriaportal.org/cc/) is an international standard (ISO / IEC 15408) for computer security. It allows an objective evaluation to validate that a particular product satisfies a defined set of security requirements.
2196 |
2197 | [ISO 22301](https://www.iso.org/en/contents/data/standard/07/51/75106.html) is the international standard that provides a best-practice framework for implementing an optimised BCMS (business continuity management system).
2198 |
2199 | [ISO27001](https://www.iso.org/isoiec-27001-information-security.html) is the international standard that describes the requirements for an ISMS (information security management system). The framework is designed to help organizations manage their security practices in one place, consistently and cost-effectively.
2200 |
2201 | [ISO 27701](https://www.iso.org/en/contents/data/standard/07/16/71670.html) specifies the requirements for a PIMS (privacy information management system) based on the requirements of ISO 27001.
2202 | It is extended by a set of privacy-specific requirements, control objectives and controls. Companies that have implemented ISO 27001 will be able to use ISO 27701 to extend their security efforts to cover privacy management.
2203 |
2204 | [EU GDPR (General Data Protection Regulation)](https://gdpr.eu/) is a privacy and data protection law that supersedes existing national data protection laws across the EU, bringing uniformity by introducing just one main data protection law for companies/organizations to comply with.
2205 |
2206 | [CCPA (California Consumer Privacy Act)](https://www.oag.ca.gov/privacy/ccpa) is a data privacy law that took effect on January 1, 2020 in the State of California. It applies to businesses that collect California residents’ personal information, and its privacy requirements are similar to those of the EU’s GDPR (General Data Protection Regulation).
2207 |
2208 | [Payment Card Industry (PCI) Data Security Standards (DSS)](https://docs.microsoft.com/en-us/microsoft-365/compliance/offering-pci-dss) is a global information security standard designed to prevent fraud through increased control of credit card data.
2209 |
2210 | [SOC 2](https://www.aicpa.org/interestareas/frc/assuranceadvisoryservices/aicpasoc2report.html) is an auditing procedure that ensures your service providers securely manage your data to protect the interests of your comapny/organization and the privacy of their clients.
2211 |
2212 | [NIST CSF](https://www.nist.gov/national-security-standards) is a voluntary framework primarily intended for critical infrastructure organizations to manage and mitigate cybersecurity risk based on existing best practice.
2213 |
2214 | ## Security Tools
2215 |
2216 | [AppArmor](https://www.apparmor.net/) is an effective and easy-to-use Linux application security system. AppArmor proactively protects the operating system and applications from external or internal threats, even zero-day attacks, by enforcing good behavior and preventing both known and unknown application flaws from being exploited. AppArmor supplements the traditional Unix discretionary access control (DAC) model by providing mandatory access control (MAC). It has been included in the mainline Linux kernel since version 2.6.36 and its development has been supported by Canonical since 2009.
2217 |
2218 | [SELinux](https://github.com/SELinuxProject/selinux) is a security enhancement to Linux which allows users and administrators more control over access control. Access can be constrained on such variables as which users and applications can access which resources. These resources may take the form of files. Standard Linux access controls, such as file modes (-rwxr-xr-x) are modifiable by the user and the applications which the user runs. Conversely, SELinux access controls are determined by a policy loaded on the system which may not be changed by careless users or misbehaving applications.
2219 |
2220 | [Control Groups(Cgroups)](https://www.redhat.com/sysadmin/cgroups-part-one) is a Linux kernel feature that allows you to allocate resources such as CPU time, system memory, network bandwidth, or any combination of these resources for user-defined groups of tasks (processes) running on a system.
2221 |
2222 | [EarlyOOM](https://github.com/rfjakob/earlyoom) is a daemon for Linux that enables users to more quickly recover and regain control over their system in low-memory situations with heavy swap usage.
2223 |
2224 | [Libgcrypt](https://www.gnupg.org/related_software/libgcrypt/) is a general purpose cryptographic library originally based on code from GnuPG.
2225 |
2226 | [Pi-hole](https://pi-hole.net/) is a [DNS sinkhole](https://en.wikipedia.org/wiki/DNS_Sinkhole) that protects your devices from unwanted content, without installing any client-side software, intended for use on a private network. It is designed for use on embedded devices with network capability, such as the Raspberry Pi, but it can be used on other machines running Linux and cloud implementations.
2227 |
2228 | [Aircrack-ng](https://www.aircrack-ng.org/) is a network software suite consisting of a detector, packet sniffer, WEP and WPA/WPA2-PSK cracker and analysis tool for 802.11 wireless LANs. It works with any wireless network interface controller whose driver supports raw monitoring mode and can sniff 802.11a, 802.11b and 802.11g traffic.
2229 |
2230 | [Acra](https://cossacklabs.com/acra) is a single database security suite with 9 strong security controls: application level encryption, searchable encryption, data masking, data tokenization, secure authentication, data leakage prevention, database request firewall, cryptographically signed audit logging, security events automation. It is designed to cover the most important data security requirements with SQL and NoSQL databases and distributed apps in a fast, convenient, and reliable way.
2231 |
2232 | [Netdata](https://github.com/netdata/netdata) is high-fidelity infrastructure monitoring and troubleshooting, real-time monitoring Agent collects thousands of metrics from systems, hardware, containers, and applications with zero configuration. It runs permanently on all your physical/virtual servers, containers, cloud deployments, and edge/IoT devices, and is perfectly safe to install on your systems mid-incident without any preparation.
2233 |
2234 | [Trivy](https://aquasecurity.github.io/trivy/) is a comprehensive security scanner for vulnerabilities in container images, file systems, and Git repositories, as well as for configuration issues and hard-coded secrets.
2235 |
2236 | [Lynis](https://cisofy.com/lynis/) is a security auditing tool for Linux, macOS, and UNIX-based systems. Assists with compliance testing (HIPAA/ISO27001/PCI DSS) and system hardening. Agentless, and installation optional.
2237 |
2238 | [OWASP Nettacker](https://github.com/OWASP/Nettacker) is a project created to automate information gathering, vulnerability scanning and eventually generating a report for networks, including services, bugs, vulnerabilities, misconfigurations, and other information. This software will utilize TCP SYN, ACK, ICMP, and many other protocols in order to detect and bypass Firewall/IDS/IPS devices.
2239 |
2240 | [Terrascan](https://runterrascan.io/) is a static code analyzer for Infrastructure as Code to mitigate risk before provisioning cloud native infrastructure.
2241 |
2242 | [Sliver](https://github.com/BishopFox/sliver) is an open source cross-platform adversary emulation/red team framework, it can be used by organizations of all sizes to perform security testing. Sliver's implants support C2 over Mutual TLS (mTLS), WireGuard, HTTP(S), and DNS and are dynamically compiled with per-binary asymmetric encryption keys.
2243 |
2244 | [Attack Surface Analyzer](https://github.com/microsoft/AttackSurfaceAnalyzer) is a [Microsoft](https://github.com/microsoft/) developed open source security tool that analyzes the attack surface of a target system and reports on potential security vulnerabilities introduced during the installation of software or system misconfiguration.
2245 |
2246 | [Intel Owl](https://intelowl.readthedocs.io/) is an Open Source Intelligence, or OSINT solution to get threat intelligence data about a specific file, an IP or a domain from a single API at scale. It integrates a number of analyzers available online and a lot of cutting-edge malware analysis tools.
2247 |
2248 | [Deepfence ThreatMapper](https://deepfence.io/) is a runtime tool that hunts for vulnerabilities in your cloud native production platforms(Linux, K8s, AWS Fargate and more.), and ranks these vulnerabilities based on their risk-of-exploit.
2249 |
2250 | [Dockle](https://containers.goodwith.tech/) is a Container Image Linter for Security and helping build the Best-Practice Docker Image.
2251 |
2252 | [RustScan](https://github.com/RustScan/RustScan) is a Modern Port Scanner.
2253 |
2254 | [gosec](https://github.com/securego/gosec) is a Golang Security Checker that inspects source code for security problems by scanning the Go AST.
2255 |
2256 | [Prowler](https://github.com/prowler-cloud/prowler) is an Open Source security tool to perform AWS security best practices assessments, audits, incident response, continuous monitoring, hardening and forensics readiness. It contains more than 240 controls covering CIS, PCI-DSS, ISO27001, GDPR, HIPAA, FFIEC, SOC2, AWS FTR, ENS and custom security frameworks.
2257 |
2258 | [Burp Suite](https://portswigger.net/burp) is a leading range of cybersecurity tools.
2259 |
2260 | [KernelCI](https://foundation.kernelci.org/) is a community-based open source distributed test automation system focused on upstream kernel development. The primary goal of KernelCI is to use an open testing philosophy to ensure the quality, stability and long-term maintenance of the Linux kernel.
2261 |
2262 | [Continuous Kernel Integration project](https://github.com/cki-project) helps find bugs in kernel patches before they are commited to an upstram kernel tree. We are team of kernel developers, kernel testers, and automation engineers.
2263 |
2264 | [eBPF](https://ebpf.io) is a revolutionary technology that can run sandboxed programs in the Linux kernel without changing kernel source code or loading kernel modules. By making the Linux kernel programmable, infrastructure software can leverage existing layers, making them more intelligent and feature-rich without continuing to add additional layers of complexity to the system.
2265 |
2266 | [Cilium](https://cilium.io/) uses eBPF to accelerate getting data in and out of L7 proxies such as Envoy, enabling efficient visibility into API protocols like HTTP, gRPC, and Kafka.
2267 |
2268 | [Hubble](https://github.com/cilium/hubble) is a Network, Service & Security Observability for Kubernetes using eBPF.
2269 |
2270 | [Istio](https://istio.io/) is an open platform to connect, manage, and secure microservices. Istio's control plane provides an abstraction layer over the underlying cluster management platform, such as Kubernetes and Mesos.
2271 |
2272 | [Certgen](https://github.com/cilium/certgen) is a convenience tool to generate and store certificates for Hubble Relay mTLS.
2273 |
2274 | [Scapy](https://scapy.net/) is a python-based interactive packet manipulation program & library.
2275 |
2276 | [syzkaller](https://github.com/google/syzkaller) is an unsupervised, coverage-guided kernel fuzzer.
2277 |
2278 | [SchedViz](https://github.com/google/schedviz) is a tool for gathering and visualizing kernel scheduling traces on Linux machines.
2279 |
2280 | [oss-fuzz](https://google.github.io/oss-fuzz/) aims to make common open source software more secure and stable by combining modern fuzzing techniques with scalable, distributed execution.
2281 |
2282 | [OSSEC](https://www.ossec.net/) is a free, open-source host-based intrusion detection system. It performs log analysis, integrity checking, Windows registry monitoring, rootkit detection, time-based alerting, and active response.
2283 |
2284 | [Metasploit Project](https://www.metasploit.com/) is a computer security project that provides information about security vulnerabilities and aids in penetration testing and IDS signature development.
2285 |
2286 | [Wfuzz](https://github.com/xmendez/wfuzz) was created to facilitate the task in web applications assessments and it is based on a simple concept: it replaces any reference to the FUZZ keyword by the value of a given payload.
2287 |
2288 | [Nmap](https://nmap.org/) is a security scanner used to discover hosts and services on a computer network, thus building a "map" of the network.
2289 |
2290 | [Patchwork](https://github.com/getpatchwork/patchwork) is a web-based patch tracking system designed to facilitate the contribution and management of contributions to an open-source project.
2291 |
2292 | [pfSense](https://www.pfsense.org/) is a free and open source firewall and router that also features unified threat management, load balancing, multi WAN, and more.
2293 |
2294 | [Snowpatch](https://github.com/ruscur/snowpatch) is a continuous integration tool for projects using a patch-based, mailing-list-centric git workflow. This workflow is used by a number of well-known open source projects such as the Linux kernel.
2295 |
2296 | [Snort](https://www.snort.org/) is an open-source, free and lightweight network intrusion detection system (NIDS) software for Linux and Windows to detect emerging threats.
2297 |
2298 | [Wireshark](https://www.wireshark.org/) is a free and open-source packet analyzer. It is used for network troubleshooting, analysis, software and communications protocol development, and education.
2299 |
2300 | [OpenSCAP](https://www.open-scap.org/) is U.S. standard maintained by [National Institute of Standards and Technology (NIST)](https://www.nist.gov/). It provides multiple tools to assist administrators and auditors with assessment, measurement, and enforcement of security baselines. OpenSCAP maintains great flexibility and interoperability by reducing the costs of performing security audits. Whether you want to evaluate DISA STIGs, NIST‘s USGCB, or Red Hat’s Security Response Team’s content, all are supported by OpenSCAP.
2301 |
2302 | [Tink](https://github.com/google/tink) is a multi-language, cross-platform, open source library that provides cryptographic APIs that are secure, easy to use correctly, and harder to misuse.
2303 |
2304 | [OWASP](https://www.owasp.org/index.php/Main_Page) is an online community, produces freely-available articles, methodologies, documentation, tools, and technologies in the field of web application security.
2305 |
2306 | [Open Vulnerability and Assessment Language](https://oval.mitre.org/) is a community effort to standardize how to assess and report upon the machine state of computer systems. OVAL includes a language to encode system details, and community repositories of content. Tools and services that use OVAL provide enterprises with accurate, consistent, and actionable information to improve their security.
2307 |
2308 | [ClamAV](https://www.clamav.net/) is an open source antivirus engine for detecting trojans, viruses, malware & other malicious threats.
2309 |
2310 | ### Security Tutorials & Resources
2311 |
2312 | - [Microsoft Open Source Software Security](https://www.microsoft.com/en-us/securityengineering/opensource)
2313 |
2314 | - [Cloudflare Open Source Security](https://cloudflare.github.io)
2315 |
2316 | - [The Seven Properties of Highly Secure Devices](https://www.microsoft.com/en-us/research/publication/seven-properties-highly-secure-devices/)
2317 |
2318 | - [How Layer 7 of the Internet Works](https://www.cloudflare.com/learning/ddos/what-is-layer-7/)
2319 |
2320 | - [The 7 Kinds of Security](https://www.veracode.com/sites/default/files/Resources/eBooks/7-kinds-of-security.pdf)
2321 |
2322 | - [The Libgcrypt Reference Manual](https://www.gnupg.org/documentation/manuals/gcrypt/)
2323 |
2324 | - [The Open Web Application Security Project(OWASP) Foundation Top 10](https://owasp.org/www-project-top-ten/)
2325 |
2326 | - [Best Practices for Using Open Source Code from The Linux Foundation](https://www.linuxfoundation.org/blog/2017/11/best-practices-using-open-source-code/)
2327 |
2328 | ### Security Certifications
2329 |
2330 | - [AWS Certified Security - Specialty Certification](https://aws.amazon.com/certification/certified-security-specialty/)
2331 |
2332 | - [Microsoft Certified: Azure Security Engineer Associate](https://docs.microsoft.com/en-us/learn/certifications/azure-security-engineer)
2333 |
2334 | - [Google Cloud Certified Professional Cloud Security Engineer](https://cloud.google.com/certification/cloud-security-engineer)
2335 |
2336 | - [Cisco Security Certifications](https://www.cisco.com/c/en/us/training-events/training-certifications/certifications/security.html)
2337 |
2338 | - [The Red Hat Certified Specialist in Security: Linux](https://www.redhat.com/en/services/training/ex415-red-hat-certified-specialist-security-linux-exam)
2339 |
2340 | - [Linux Professional Institute LPIC-3 Enterprise Security Certification](https://www.lpi.org/our-certifications/lpic-3-303-overview)
2341 |
2342 | - [Cybersecurity Training and Courses from IBM Skills](https://www.ibm.com/skills/topics/cybersecurity/)
2343 |
2344 | - [Cybersecurity Courses and Certifications by Offensive Security](https://www.offensive-security.com/courses-and-certifications/)
2345 |
2346 | - [RSA Certification Program](https://community.rsa.com/community/training/certification)
2347 |
2348 | - [Check Point Certified Security Expert(CCSE) Certification](https://training-certifications.checkpoint.com/#/courses/Check%20Point%20Certified%20Expert%20(CCSE)%20R80.x)
2349 |
2350 | - [Check Point Certified Security Administrator(CCSA) Certification](https://training-certifications.checkpoint.com/#/courses/Check%20Point%20Certified%20Admin%20(CCSA)%20R80.x)
2351 |
2352 | - [Check Point Certified Security Master (CCSM) Certification](https://training-certifications.checkpoint.com/#/courses/Check%20Point%20Certified%20Master%20(CCSM)%20R80.x)
2353 |
2354 | - [Certified Cloud Security Professional(CCSP) Certification](https://www.isc2.org/Certifications/CCSP)
2355 |
2356 | - [Certified Information Systems Security Professional (CISSP) Certification](https://www.isc2.org/Certifications/CISSP)
2357 |
2358 | - [CCNP Routing and Switching](https://learningnetwork.cisco.com/s/ccnp-enterprise)
2359 |
2360 | - [Certified Information Security Manager(CISM)](https://www.isaca.org/credentialing/cism)
2361 |
2362 | - [Wireshark Certified Network Analyst (WCNA)](https://www.wiresharktraining.com/certification.html)
2363 |
2364 | - [Juniper Networks Certification Program Enterprise (JNCP)](https://www.juniper.net/us/en/training/certification/)
2365 |
2366 | - [Security Training Certifications and Courses from Udemy](https://www.udemy.com/courses/search/?src=ukw&q=secuirty)
2367 |
2368 | - [Security Training Certifications and Courses from Coursera](https://www.coursera.org/search?query=security&)
2369 |
2370 | - [Security Certifications Training from Pluarlsight](https://www.pluralsight.com/browse/information-cyber-security/security-certifications)
2371 |
2372 |
2373 | ## Contribute
2374 |
2375 | - [x] If would you like to contribute to this guide simply make a [Pull Request](https://github.com/mikeroyal/Kubernetes-Guide/pulls).
2376 |
2377 |
2378 | ## License
2379 | [Back to the Top](https://github.com/mikeroyal/Kubernetes-Guide/blob/main/README.md#table-of-contents)
2380 |
2381 | Distributed under the [Creative Commons Attribution 4.0 International (CC BY 4.0) Public License](https://creativecommons.org/licenses/by/4.0/).
2382 |
--------------------------------------------------------------------------------
/Security Glossary.md:
--------------------------------------------------------------------------------
1 | A list of Key Information Security Terms for Software and Hardware. **Sources:** [NIST Federal Information Processing Standards (FIPS)](https://csrc.nist.gov/publications/fips), the [Special Publication (SP) 800 series](https://csrc.nist.gov/publications/sp), [NIST Interagency Reports (NISTIRs)](https://csrc.nist.gov/publications/nistir), and from the [Committee for National Security Systems Instruction 4009 (CNSSI-4009)](https://www.cnss.gov/CNSS/issuances/Instructions.cfm).
2 |
3 |
4 | A
5 |
6 | Access – Ability and means to communicate with or otherwise interact with a system, to use system resources to handle information, to gain knowledge of the information the system contains, or to control system components and functions.
7 | SOURCE: CNSSI-4009
8 |
9 | Access Authority – An entity responsible for monitoring and granting access privileges for other authorized entities.
10 | SOURCE: CNSSI-4009
11 |
12 | Access Control – The process of granting or denying specific requests to: 1) obtain and use information and related information processing services; and 2) enter specific physical facilities (e.g., federal buildings, military establishments, border crossing entrances).
13 | SOURCE: FIPS 201; CNSSI-4009
14 |
15 | Access Control List (ACL) –
16 | * 1. A list of permissions associated with an object. The list specifies who or what is allowed to access the object and what operations are allowed to be performed on the object.
17 | * 2. A mechanism that implements access control for a system resource by enumerating the system entities that are permitted to access the resource and stating, either implicitly or explicitly, the access modes granted to each entity.
18 | SOURCE: CNSSI-4009
19 |
20 | Access Control Lists (ACLs) – A register of:
21 | * 1. users (including groups, machines, processes) who have been given permission to use a particular system resource, and
22 | * 2. the types of access they have been permitted.
23 | SOURCE: SP 800-12
24 |
25 | Access Control Mechanism – Security safeguards (i.e., hardware and software features, physical controls, operating procedures, management procedures, and various combinations of these) designed to detect and deny unauthorized
26 | access and permit authorized access to an information system.
27 | SOURCE: CNSSI-4009
28 |
29 | Access Level – A category within a given security classification limiting entry or
30 | system connectivity to only authorized persons.
31 | SOURCE: CNSSI-4009
32 |
33 | Access List – Roster of individuals authorized admittance to a controlled area.
34 | SOURCE: CNSSI-4009
35 |
36 | Access Point – A device that logically connects wireless client devices operating in infrastructure to one another and provides access to a distribution system, if connected, which is typically an organization’s enterprise wired network.
37 | SOURCE: SP 800-48; SP 800-121
38 |
39 | Access Profile – Association of a user with a list of protected objects the user may access.
40 | SOURCE: CNSSI-4009
41 |
42 | Access Type – Privilege to perform action on an object. Read, write, execute, append, modify, delete, and create are examples of access types.
43 | SOURCE: CNSSI-4009
44 |
45 | Activation Data – Private data, other than keys, that are required to access cryptographic modules.
46 | SOURCE: SP 800-32
47 |
48 | Active Attack – An attack that alters a system or data.
49 | SOURCE: CNSSI-4009
50 |
51 | Active Content – Software in various forms that is able to automatically carry out or trigger actions on a computer platform without the intervention of a user.
52 | SOURCE: CNSSI-4009
53 |
54 | Active Security Testing – Security testing that involves direct interaction with a target, such as sending packets to a target.
55 | SOURCE: SP 800-115
56 |
57 | Advanced Encryption Standard – (AES) The Advanced Encryption Standard specifies a U.S. government-approved cryptographic algorithm that can be used to protect electronic data. The AES algorithm is a symmetric block cipher that can encrypt (encipher) and decrypt (decipher) information. This standard specifies the Rijndael algorithm, a symmetric block cipher that can process data blocks of 128 bits, using cipher keys with lengths of 128, 192, and 256 bits.
58 | SOURCE: FIPS 197
59 |
60 | B
61 |
62 | Blacklisting – The process of the system invalidating a user ID based on the user’s inappropriate actions. A blacklisted user ID cannot be used to log on to the system, even with the correct authenticator. Blacklisting and lifting of a blacklisting are both security-relevant events. Blacklisting also applies to blocks placed against IP addresses to prevent inappropriate or unauthorized use of Internet resources.
63 | SOURCE: CNSSI-4009
64 |
65 | Blue Team –
66 | * 1. The group responsible for defending an enterprise’s use of
67 | information systems by maintaining its security posture against a
68 | group of mock attackers (i.e., the Red Team). Typically the Blue
69 | Team and its supporters must defend against real or simulated
70 | attacks 1) over a significant period of time, 2) in a representative
71 | operational context (e.g., as part of an operational exercise), and 3)
72 | according to rules established and monitored with the help of a
73 | neutral group refereeing the simulation or exercise (i.e., the White
74 | Team).
75 | * 2. The term Blue Team is also used for defining a group of
76 | individuals that conduct operational network vulnerability
77 | evaluations and provide mitigation techniques to customers who have
78 | a need for an independent technical review of their network security
79 | posture. The Blue Team identifies security threats and risks in the
80 | operating environment, and in cooperation with the customer,
81 | analyzes the network environment and its current state of security
82 | readiness. Based on the Blue Team findings and expertise,
83 | they provide recommendations that integrate into an overall
84 | community security solution to increase the customer's cyber security
85 | readiness posture. Often times a Blue Team is employed by itself or
86 | prior to a Red Team employment to ensure that the customer's
87 | networks are as secure as possible before having the Red Team test
88 | the systems.
89 | SOURCE: CNSSI-4009
90 |
91 | Body of Evidence (BoE) – The set of data that documents the information system’s adherence to the security controls applied. The BoE will include a Requirements Verification Traceability Matrix (RVTM) delineating where the selected security controls are met and evidence to that fact can be found. The BoE content required by an Authorizing Official will be adjusted according to the impact levels selected.
92 | SOURCE: CNSSI-4009
93 |
94 | Boundary – Physical or logical perimeter of a system.
95 | SOURCE: CNSSI-4009
96 |
97 | C
98 |
99 | Capstone Policies – Those policies that are developed by governing or coordinating institutions of Health Information Exchanges (HIEs). They provide overall requirements and guidance for protecting health information within those HIEs. Capstone Policies must address the requirements imposed by: (1) all laws, regulations, and guidelines at the federal, state, and local levels; (2) business needs; and (3) policies at the institutional and HIE levels.
100 | SOURCE: NISTIR-7497
101 |
102 | Capture – The method of taking a biometric sample from an end user.
103 | Source: FIPS 201
104 |
105 | Certificate Management – Process whereby certificates (as defined above) are generated, stored, protected, transferred, loaded, used, and destroyed.
106 | SOURCE: CNSSI-4009
107 |
108 | Certificate Management Authority – A Certification Authority (CA) or a Registration Authority (RA).
109 | SOURCE: SP 800-32
110 |
111 | Certificate Policy (CP) – A specialized form of administrative policy tuned to electronic transactions performed during certificate management. A Certificate Policy addresses all aspects associated with the generation, production, distribution, accounting, compromise recovery, and administration of digital certificates. Indirectly, a certificate policy can also govern the transactions conducted using a communications system protected by a certificate-based security system. By controlling critical certificate extensions, such policies and associated enforcement technology can support provision of the security services required by particular applications.
112 | SOURCE: CNSSI-4009; SP 800-32
113 |
114 | Certification Practice Statement – A statement of the practices that a Certification Authority employs in issuing, suspending, revoking, and renewing certificates and providing access to them, in accordance with specific requirements (i.e., requirements specified in this Certificate Policy, or requirements specified in a contract for services).
115 | SOURCE: SP 800-32; CNSSI-4009
116 |
117 | Certification Test and Evaluation – Software and hardware security tests conducted during development of an information system.
118 | SOURCE: CNSSI-4009
119 |
120 | Checksum – Value computed on data to detect error or manipulation.
121 | SOURCE: CNSSI-4009
122 |
123 | Cloud Computing - A model for enabling ubiquitous, convenient, on-demand network access to a shared pool of configurable computing resources (e.g., networks, servers, storage, applications, and services) that can be rapidly provisioned and released with minimal management effort or service Provider interaction. This cloud model is composed of five essential characteristics, three service models, and four deployment models
124 | SOURCE(s): NISTIR 8006 under Cloud computing from NIST SP 800-145 - Adapted
125 |
126 | Cryptographic Initialization – Function used to set the state of a cryptographic logic prior to key generation, encryption, or other operating mode.
127 | SOURCE: CNSSI-4009
128 |
129 | Cryptographic Key – A value used to control cryptographic operations, such as decryption, encryption, signature generation, or signature verification.
130 | SOURCE: SP 800-63
131 |
132 | D
133 |
134 | Data – A subset of information in an electronic format that allows it to be retrieved or transmitted.
135 | SOURCE: CNSSI-4009
136 |
137 | Data Aggregation – Compilation of individual data systems and data that could result in the totality of the information being classified, or classified at a higher level, or of beneficial use to an adversary.
138 | SOURCE: CNSSI-4009
139 |
140 | Data Origin Authentication – The process of verifying that the source of the data is as claimed and that the data has not been modified.
141 | SOURCE: CNSSI-4009
142 |
143 | Data Security – Protection of data from unauthorized (accidental or intentional) modification, destruction, or disclosure.
144 | SOURCE: CNSSI-4009
145 |
146 | Data Transfer Device (DTD) – Fill device designed to securely store, transport, and transfer electronically both COMSEC and TRANSEC key, designed to be backward compatible with the previous generation of COMSEC common fill devices, and programmable to support modern mission systems.
147 | SOURCE: CNSSI-4009
148 |
149 | Denial of Service (DoS) – The prevention of authorized access to resources or the delaying of time-critical operations. (Time-critical may be milliseconds or it may be hours, depending upon the service provided.)
150 | SOURCE: CNSSI-4009
151 |
152 | Differential Power Analysis – An analysis of the variations of the electrical power consumption of a cryptographic module, using advanced statistical methods and/or other techniques, for the purpose of extracting information correlated to cryptographic keys used in a cryptographic algorithm.
153 | SOURCE: FIPS 140-2
154 |
155 | Digital Evidence – Electronic information stored or transferred in digital form.
156 | SOURCE: SP 800-72
157 |
158 | Digital Forensics – The application of science to the identification, collection, examination, and analysis of data while preserving the integrity of the information and maintaining a strict chain of custody for the data.
159 | SOURCE: SP 800-86
160 |
161 | Digital Signature – An asymmetric key operation where the private key is used to digitally sign data and the public key is used to verify the signature. Digital signatures provide authenticity protection, integrity protection, and non-repudiation.
162 | SOURCE: SP 800-63
163 |
164 | Disaster Recovery Plan (DRP) – A written plan for recovering one or more information systems at an alternate facility in response to a major hardware or software failure or destruction of facilities.
165 | SOURCE: SP 800-34
166 |
167 | E
168 |
169 | Embedded Cryptographic System – Cryptosystem performing or controlling a function as an integral element of a larger system or subsystem.
170 | SOURCE: CNSSI-4009
171 |
172 | Embedded Cryptography - Cryptography engineered into an equipment or system whose basic function is not cryptographic.
173 | SOURCE: CNSSI-4009
174 |
175 | Encipher – Convert plain text to cipher text by means of a cryptographic system.
176 | SOURCE: CNSSI-4009
177 |
178 | Encode – Convert plain text to cipher text by means of a code.
179 | SOURCE: CNSSI-4009
180 |
181 | Encrypt – Generic term encompassing encipher and encode.
182 | SOURCE: CNSSI-4009
183 |
184 | Encrypted Key – A cryptographic key that has been encrypted using an Approved security function with a key encrypting key, a PIN, or a password in order to disguise the value of the underlying plaintext key.
185 | SOURCE: FIPS 140-2
186 |
187 | Encrypted Network – A network on which messages are encrypted (e.g., using DES, AES, or other appropriate algorithms) to prevent reading by unauthorized parties.
188 | SOURCE: SP 800-32
189 |
190 | Encryption – Conversion of plaintext to ciphertext through the use of a cryptographic algorithm.
191 | SOURCE: FIPS 185
192 |
193 | End-to-End Encryption – Encryption of information at its origin and decryption at its intended destination without intermediate decryption.
194 | SOURCE: CNSSI-4009
195 |
196 | End-to-End Security – Safeguarding information in an information system from point of origin to point of destination.
197 | SOURCE: CNSSI-4009
198 |
199 | F
200 |
201 | [Federal Risk and Authorization Management Program (FedRAMP)](https://www.gsa.gov/technology/government-it-initiatives/fedramp) is a government-wide program that provides a standardized approach to security assessment, authorization, and continuous monitoring for cloud products and services. FedRAMP empowers agencies to use modern cloud technologies, with emphasis on security and protection of federal information, and helps accelerate the adoption of secure, cloud solutions.
202 |
203 | [Federal Information Security Management Act (FISMA)](https://csrc.nist.gov/topics/laws-and-regulations/laws/fisma) is a United States federal law that defines a comprehensive framework to protect government information, operations, and assets against natural and manmade threats. This risk management framework was signed into law as part of the Electronic Government Act of 2002. Since 2002, FISMA's scope has widened to apply to state agencies that administer federal programs, or private businesses and service providers that hold a contract with the U.S. government.
204 |
205 | False Positive – An alert that incorrectly indicates that malicious activity is occurring.
206 | SOURCE: SP 800-61
207 |
208 | False Rejection – In biometrics, the instance of a security system failing to verify or identify an authorized person. It does not necessarily indicate a flaw in the biometric system; for example, in a fingerprint-based system, an incorrectly aligned finger on the scanner or dirt on the scanner can result in the scanner misreading the fingerprint, causing a false rejection of the authorized user.
209 | SOURCE: CNSSI-4009
210 |
211 | Federal Information Processing Standard (FIPS) – A standard for adoption and use by federal departments and agencies that has been developed within the Information Technology Laboratory and published by the National Institute of Standards and Technology, a part of the U.S. Department of Commerce. A FIPS covers some topic in information technology in order to achieve a common level of quality or some level of interoperability.
212 | SOURCE: FIPS 201
213 |
214 | File Encryption – The process of encrypting individual files on a storage medium and permitting access to the encrypted data only after proper authentication is provided.
215 | SOURCE: SP 800-111
216 |
217 | File Name Anomaly –
218 | * 1. A mismatch between the internal file header and its external
219 | extension.
220 | * 2. A file name inconsistent with the content of the file (e.g., renaming
221 | a graphics file with a non-graphical extension.
222 | SOURCE: SP 800-72
223 |
224 | File Protection – Aggregate of processes and procedures designed to inhibit unauthorized access, contamination, elimination, modification, or destruction of a file or any of its contents.
225 | SOURCE: CNSSI-4009
226 |
227 | File Security – Means by which access to computer files is limited to authorized users only.
228 | SOURCE: CNSSI-4009
229 |
230 | Firewall – A gateway that limits access between networks in accordance with local security policy.
231 | SOURCE: SP 800-32
232 |
233 | Forensics – The practice of gathering, retaining, and analyzing computer-related data for investigative purposes in a manner that maintains the integrity of the data.
234 | SOURCE: CNSSI-4009
235 |
236 | G
237 |
238 | Gateway – Interface providing compatibility between networks by converting transmission speeds, protocols, codes, or security measures.
239 | SOURCE: CNSSI-4009
240 |
241 | H
242 |
243 | Handshaking Procedures – Dialogue between two information systems for synchronizing, identifying, and authenticating themselves to one another.
244 | SOURCE: CNSSI-4009
245 |
246 | Hard Copy Key – Physical keying material, such as printed key lists, punched or printed key tapes, or programmable, read-only memories (PROM).
247 | SOURCE: CNSSI-4009
248 |
249 | Hardening – Configuring a host’s operating systems and applications to reduce the host’s security weaknesses.
250 | SOURCE: SP 800-123
251 |
252 | Hardware – The physical components of an information system.
253 | SOURCE: CNSSI-4009
254 |
255 | High Availability – A failover feature to ensure availability during device or component interruptions.
256 | SOURCE: SP 800-113
257 |
258 | I
259 |
260 | Identification – The process of verifying the identity of a user, process, or device, usually as a prerequisite for granting access to resources in an IT system.
261 | SOURCE: SP 800-47
262 |
263 | Identifier – Unique data used to represent a person’s identity and associated attributes. A name or a card number are examples of identifiers.
264 | SOURCE: FIPS 201
265 |
266 | Identity – A set of attributes that uniquely describe a person within a given context.
267 | SOURCE: SP 800-63
268 |
269 | Identity – The set of physical and behavioral characteristics by which an individual is uniquely recognizable.
270 | SOURCE: FIPS 201
271 |
272 | Identity Token – Smart card, metal key, or other physical object used to authenticate identity.
273 | SOURCE: CNSSI-4009
274 |
275 | Identity Validation – Tests enabling an information system to authenticate users or resources.
276 | SOURCE: CNSSI-4009
277 |
278 | Incident – A violation or imminent threat of violation of computer security policies, acceptable use policies, or standard security practices.
279 | SOURCE: SP 800-61
280 |
281 | Intellectual Property – Creations of the mind such as musical, literary, and artistic works; inventions; and symbols, names, images, and designs used in commerce, including copyrights, trademarks, patents, and related rights. Under intellectual property law, the holder of one of these abstract “properties” has certain exclusive rights to the creative work, commercial symbol, or invention by which it is covered.
282 | SOURCE: CNSSI-4009
283 |
284 | Internet Protocol (IP) – Standard protocol for transmission of data from source to destinations in packet-switched communications networks and interconnected systems of such networks.
285 | SOURCE: CNSSI-4009
286 |
287 | Intranet – A private network that is employed within the confines of a given enterprise (e.g., internal to a business or agency).
288 | SOURCE: CNSSI-4009
289 |
290 | Intrusion – Unauthorized act of bypassing the security mechanisms of a system.
291 | SOURCE: CNSSI-4009
292 |
293 | Intrusion Detection Systems (IDS) – Hardware or software product that gathers and analyzes information from various areas within a computer or a network to identify possible security breaches, which include both intrusions (attacks from outside the organizations) and misuse (attacks from within the organizations.)
294 | SOURCE: CNSSI-4009
295 |
296 | J
297 |
298 | Jamming – An attack in which a device is used to emit electromagnetic energy on a wireless network’s frequency to make it unusable.
299 | SOURCE: SP 800-48
300 |
301 | K
302 |
303 | Kerberos – A means of verifying the identities of principals on an open network. It accomplishes this without relying on the authentication, trustworthiness, or physical security of hosts while assuming all packets can be read, modified and inserted at will. It uses a trust broker model and symmetric cryptography to provide authentication and authorization of users and systems on the network.
304 | SOURCE: SP 800-95
305 |
306 | Key – A value used to control cryptographic operations, such as decryption, encryption, signature generation, or signature verification.
307 | SOURCE: SP 800-63
308 |
309 | Key Logger – A program designed to record which keys are pressed on a computer keyboard used to obtain passwords or encryption keys and thus bypass other security measures.
310 | SOURCE: SP 800-82
311 |
312 | L
313 |
314 | Least Privilege – The security objective of granting users only those accesses they need to perform their official duties.
315 | SOURCE: SP 800-12
316 |
317 | Level of Protection – Extent to which protective measures, techniques, and procedures must be applied to information systems and networks based on risk, threat, vulnerability, system interconnectivity considerations, and information assurance needs. Levels of protection are:
318 | * 1. Basic: information systems and networks requiring implementation of standard minimum security countermeasures.
319 | * 2. Medium: information systems and networks requiring layering of additional safeguards above the standard minimum security countermeasures.
320 | * 3. High: information systems and networks requiring the most stringent protection and rigorous security countermeasures.
321 | SOURCE: CNSSI-4009
322 |
323 | Likelihood of Occurrence – In Information Assurance risk analysis, a weighted factor based on a subjective analysis of the probability that a given threat is capable of exploiting a given vulnerability.
324 | SOURCE: CNSSI-4009
325 |
326 | M
327 |
328 | Malicious Code – Software or firmware intended to perform an unauthorized process that will have adverse impact on the confidentiality, integrity, or availability of an information system. A virus, worm, Trojan horse, or other code-based entity that infects a host. Spyware and some forms of adware are also examples of malicious code.
329 | SOURCE: SP 800-53; CNSSI-4009
330 |
331 | Malware – A program that is inserted into a system, usually covertly, with the intent of compromising the confidentiality, integrity, or availability of the victim’s data, applications, or operating system or of otherwise annoying or disrupting the victim.
332 | SOURCE: SP 800-83
333 |
334 | Man-in-the-middle Attack (MitM) – A form of active wiretapping attack in which the attacker intercepts and selectively modifies communicated data to masquerade as one or more of the entities involved in a communication association.
335 | SOURCE: CNSSI-4009
336 |
337 | Mandatory Access Control (MAC) – A means of restricting access to system resources based on the sensitivity (as represented by a label) of the information contained in the system resource and the formal authorization (i.e., clearance) of users to access information of such sensitivity.
338 | SOURCE: SP 800-44
339 |
340 | Mandatory Access Control – Access controls (which) are driven by the results of a comparison between the user’s trust level or clearance and the sensitivity designation of the information.
341 | SOURCE: FIPS 191
342 |
343 | Masquerading –When an unauthorized agent claims the identity of another agent, it is said to be masquerading.
344 | SOURCE: SP 800-19
345 |
346 | Multilevel Security (MLS) – A concept of processing information with different classifications and categories that simultaneously permits access by users with different security clearances and denies access to users who lack authorization.
347 | SOURCE: CNSSI-4009
348 |
349 | N
350 |
351 | Needs Assessment (IT Security Awareness and Training) – A process that can be used to determine an organization’s awareness and training needs. The results of a needs assessment can provide justification to convince management to allocate adequate resources
352 | to meet the identified awareness and training needs.
353 | SOURCE: SP 800-50
354 |
355 | Network – Information system(s) implemented with a collection of interconnected components. Such components may include routers,
356 | hubs, cabling, telecommunications controllers, key distribution centers, and technical control devices.
357 | SOURCE: SP 800-53; CNSSI-4009
358 |
359 | Network Access – Access to an organizational information system by a user (or a process acting on behalf of a user) communicating through a network (e.g., local area network, wide area network, Internet).
360 | SOURCE: SP 800-53; CNSSI-4009
361 |
362 | Network Access Control (NAC) – A feature provided by some firewalls that allows access based on a user’s credentials and the results of health checks performed on the telework client device.
363 | SOURCE: SP 800-41
364 |
365 | Network Address Translation (NAT) – A routing technology used by many firewalls to hide internal system addresses from an external network through use of an addressing schema.
366 | SOURCE: SP 800-41
367 |
368 | O
369 |
370 | Object Identifier – A specialized formatted number that is registered with an internationally recognized standards organization. The unique alphanumeric/numeric identifier registered under the ISO registration standard to reference a specific object or object class. In the federal government PKI, they are used to uniquely identify each of the four policies and cryptographic algorithms supported.
371 | SOURCE: SP 800-32
372 |
373 | Open Storage – Any storage of classified national security information outside of approved containers. This includes classified information that is resident on information systems media and outside of an approved storage container, regardless of whether or not that media is in use (i.e., unattended operations).
374 | SOURCE: CNSSI-4009
375 |
376 | Operating System (OS) Fingerprinting – Analyzing characteristics of packets sent by a target, such as packet headers or listening ports, to identify the operating system in use on the target.
377 | SOURCE: SP 800-115
378 |
379 | Operations Code – Code composed largely of words and phrases suitable for general communications use.
380 | SOURCE: CNSSI-4009
381 |
382 | Organization – A federal agency, or, as appropriate, any of its operational elements.
383 | SOURCE: FIPS 200
384 |
385 | Overwrite Procedure – A software process that replaces data previously stored on storage media with a predetermined set of meaningless data or random patterns.
386 | SOURCE: CNSSI-4009
387 |
388 | P
389 |
390 | Packet Filter – A routing device that provides access control functionality for host addresses and communication sessions.
391 | SOURCE: SP 800-41
392 |
393 | Packet Sniffer – Software that observes and records network traffic.
394 | SOURCE: CNSSI-4009
395 |
396 | Password – A protected character string used to authenticate the identity of a computer system user or to authorize access to system resources.
397 | SOURCE: FIPS 181
398 |
399 | Password Cracking – The process of recovering secret passwords stored in a computer system or transmitted over a network.
400 | SOURCE: SP 800-115
401 |
402 | Password Protected – The ability to protect a file using a password access control, protecting the data contents from being viewed with the appropriate viewer unless the proper password is entered.
403 | SOURCE: SP 800-72
404 |
405 | Patch – An update to an operating system, application, or other software issued specifically to correct particular problems with the software.
406 | SOURCE: SP 800-123
407 |
408 | Payload – The input data to the CCM generation-encryption process that is both authenticated and encrypted.
409 | SOURCE: SP 800-38C
410 |
411 | Penetration Testing – A test methodology in which assessors, using all available documentation (e.g., system design, source code, manuals) and working under specific constraints, attempt to circumvent the security features of an information system.
412 | SOURCE: SP 800-53A
413 |
414 | Personal Identification Number (PIN) – A secret that a claimant memorizes and uses to authenticate his or her identity. PINs are generally only decimal digits.
415 | SOURCE: FIPS 201
416 |
417 | Phishing - A digital form of social engineering that uses authentic looking but bogus emails to request information from users or direct them to a fake Web site that requests information.
418 | SOURCE: SP 800-115
419 |
420 | Plaintext – Data input to the Cipher or output from the Inverse Cipher.
421 | SOURCE: FIPS 197
422 |
423 | Policy Mapping – Recognizing that, when a CA in one domain certifies a CA in another domain, a particular certificate policy in the second domain may be considered by the authority of the first domain to be equivalent (but not necessarily identical in all respects) to a particular certificate policy in the first domain.
424 | SOURCE: SP 800-15
425 |
426 | Port – A physical entry or exit point of a cryptographic module that provides access to the module for physical signals, represented by logical information flows (physically separated ports do not share the same physical pin or wire).
427 | SOURCE: FIPS 140-2
428 |
429 | Port Scanning – Using a program to remotely determine which ports on a system are open (e.g., whether systems allow connections through those ports).
430 | SOURCE: CNSSI-4009
431 |
432 | Portal – A high-level remote access architecture that is based on a server that offers teleworkers access to one or more applications through a single centralized interface.
433 | SOURCE: SP 800-46
434 |
435 | Privilege – A right granted to an individual, a program, or a process.
436 | SOURCE: CNSSI-4009
437 |
438 | Privileged Accounts – Individuals who have access to set “access rights” for users on a given system. Sometimes referred to as system or network administrative accounts.
439 | SOURCE: SP 800-12
440 |
441 | Probe – A technique that attempts to access a system to learn something about the system.
442 | SOURCE: CNSSI-4009
443 |
444 | Profiling – Measuring the characteristics of expected activity so that changes to it can be more easily identified.
445 | SOURCE: SP 800-61; CNSSI-4009
446 |
447 | Protocol – Set of rules and formats, semantic and syntactic, permitting information systems to exchange information.
448 | SOURCE: CNSSI-4009
449 |
450 | Protocol Data Unit – A unit of data specified in a protocol and consisting of protocol information and, possibly, user data.
451 | SOURCE: FIPS 188
452 |
453 | Protocol Entity – Entity that follows a set of rules and formats (semantic and syntactic) that determines the communication behavior of other entities.
454 | SOURCE: FIPS 188
455 |
456 | Proxy – A proxy is an application that “breaks” the connection between client and server. The proxy accepts certain types of traffic entering or leaving a network and processes it and forwards it. This effectively closes the straight path between the internal and external networks making it more difficult for an attacker to obtain internal addresses and other details of the organization’s internal network. Proxy servers are available for common Internet services; for example, a Hyper Text Transfer Protocol (HTTP) proxy used for Web access, and a Simple Mail Transfer Protocol (SMTP) proxy used for email.
457 | SOURCE: SP 800-44
458 |
459 | Proxy Server – A server that services the requests of its clients by forwarding those requests to other servers.
460 | SOURCE: CNSSI-4009
461 |
462 | Public Domain Software – Software not protected by copyright laws of any nation that may be freely used without permission of, or payment to, the creator, and that carries no warranties from, or liabilities to the creator.
463 | SOURCE: CNSSI-4009
464 |
465 | Public Key - A cryptographic key used with a public key cryptographic algorithm, uniquely associated with an entity, and which may be made public; it is used to verify a digital signature; this key is mathematically linked with a corresponding private key.
466 | SOURCE: FIPS 196
467 |
468 | Q
469 |
470 | Qualitative Assessment – Use of a set of methods, principles, or rules for assessing risk based on nonnumeric categories or levels.
471 | SOURCE: SP 800-30
472 |
473 | Quality of Service – The measurable end-to-end performance properties of a network service, which can be guaranteed in advance by a Service-Level Agreement between a user and a service provider, so as to satisfy specific customer application requirements. Note: These properties may include throughput (bandwidth), transit delay (latency), error rates, priority, security, packet loss, packet jitter, etc.
474 | SOURCE: CNSSI-4009
475 |
476 | Quantitative Assessment – Use of a set of methods, principles, or rules for assessing risks based on the use of numbers where the meanings and proportionality of values are maintained inside and outside the context of the assessment.
477 | SOURCE: SP 800-30
478 |
479 | Quarantine – Store files containing malware in isolation for future disinfection or examination.
480 | SOURCE: SP 800-69
481 |
482 | R
483 |
484 | Radio Frequency Identification (RFID) – A form of automatic identification and data capture (AIDC) that uses electric or magnetic fields at radio frequencies to transmit information.
485 | SOURCE: SP 800-98
486 |
487 | Read – Fundamental operation in an information system that results only in the flow of information from an object to a subject.
488 | SOURCE: CNSSI-4009
489 |
490 | Read Access – Permission to read information in an information system.
491 | SOURCE: CNSSI-4009
492 |
493 | Real-Time Reaction – Immediate response to a penetration attempt that is detected and diagnosed in time to prevent access.
494 | SOURCE: CNSSI-4009
495 |
496 | Red Team – A group of people authorized and organized to emulate a potential adversary’s attack or exploitation capabilities against an enterprise’s security posture. The Red Team’s objective is to improve enterprise Information Assurance by demonstrating the impacts of successful attacks and by demonstrating what works for the defenders (i.e., the Blue Team) in an operational environment.
497 | SOURCE: CNSSI-4009
498 |
499 | Red Team Exercise – An exercise, reflecting real-world conditions, that is conducted as a simulated adversarial attempt to compromise organizational missions and/or business processes to provide a comprehensive assessment of the security capability of the information system and organization.
500 | SOURCE: SP 800-53
501 |
502 | Remote Access – Access to an organizational information system by a user (or an information system acting on behalf of a user) communicating through an external network (e.g., the Internet).
503 | SOURCE: SP 800-53
504 |
505 | Repository – A database containing information and data relating to certificates as specified in a CP; may also be referred to as a directory.
506 | SOURCE: SP 800-32
507 |
508 | Risk Assessment – The process of identifying risks to organizational operations (including mission, functions, image, or reputation), organizational assets, individuals, other organizations, and the Nation, arising through the operation of an information system. Part of risk management, incorporates threat and vulnerability analyses and considers mitigations provided by security controls planned or in place. Synonymous with risk analysis.
509 | SOURCE: SP 800-53; SP 800-53A; SP 800-37
510 |
511 | Risk Assessment Methodology – A risk assessment process, together with a risk model, assessment approach, and analysis approach.
512 | SOURCE: SP 800-30
513 |
514 | Risk Assessment Report – The report which contains the results of performing a risk assessment or the formal output from the process of assessing risk.
515 | SOURCE: SP 800-30
516 |
517 | Root Certification Authority – In a hierarchical Public Key Infrastructure, the Certification Authority whose public key serves as the most trusted datum (i.e., the beginning of trust paths) for a security domain.
518 | SOURCE: SP 800-32; CNSSI-4009
519 |
520 | Rootkit – A set of tools used by an attacker after gaining root-level access to a host to conceal the attacker’s activities on the host and permit the attacker to maintain root-level access to the host through covert means.
521 | SOURCE: CNSSI-4009
522 |
523 | S
524 | Safeguards – Protective measures prescribed to meet the security requirements (i.e., confidentiality, integrity, and availability) specified for an information system. Safeguards may include security features, management constraints, personnel security, and security of physical structures, areas, and devices. Synonymous with security controls and countermeasures.
525 | SOURCE: SP 800-53; SP 800-37; FIPS 200; CNSSI-4009
526 |
527 | Sandboxing- A restricted, controlled execution environment that prevents potentially malicious software, such as mobile code, from accessing any system resources except those for which the software is authorized.
528 | SOURCE: CNSSI-4009
529 |
530 | Scanning – Sending packets or requests to another system to gain information to be used in a subsequent attack.
531 | SOURCE: CNSSI-4009
532 |
533 | Secure Socket Layer (SSL) – A protocol used for protecting private information during transmission via the Internet.
534 | * **Note:** SSL works by using a public key to encrypt data that's transferred over the SSL connection. Most Web browsers support
535 | SSL, and many Web sites use the protocol to obtain confidential user information, such as credit card numbers. By convention, URLs that require an SSL connection start with “https:” instead of “http:.”
536 | SOURCE: CNSSI-4009
537 |
538 | Security Content Automation Protocol (SCAP) – A method for using specific standardized testing methods to enable automated vulnerability management, measurement, and policy compliance evaluation against a standardized set of security requirements.
539 | SOURCE: CNSSI-4009
540 |
541 | Signature – A recognizable, distinguishing pattern associated with an attack, such as a binary string in a virus or a particular set of keystrokes used to gain unauthorized access to a system.
542 | SOURCE: SP 800-61
543 |
544 | Signature Certificate – A public key certificate that contains a public key intended for verifying digital signatures rather than encrypting data or performing any other cryptographic functions.
545 | SOURCE: SP 800-32; CNSSI-4009
546 |
547 | Smart Card – A credit card-sized card with embedded integrated circuits that can store, process, and communicate information.
548 | SOURCE: CNSSI-4009
549 |
550 | Social Engineering – An attempt to trick someone into revealing information (e.g., a password) that can be used to attack systems or networks.
551 | SOURCE: SP 800-61
552 |
553 | Spam - Electronic junk mail or the abuse of electronic messaging systems to indiscriminately send unsolicited bulk messages.
554 | SOURCE: CNSSI-4009
555 |
556 | Spoofing – “IP spoofing” refers to sending a network packet that appears to come from a source other than its actual source.
557 | SOURCE: SP 800-48
558 |
559 | Spyware – Software that is secretly or surreptitiously installed into an information system to gather information on individuals or
560 | organizations without their knowledge; a type of malicious code.
561 | SOURCE: SP 800-53; CNSSI-4009
562 |
563 | Steganography – The art and science of communicating in a way that hides the existence of the communication. For example, a child pornography image can be hidden inside another graphic image file, audio file, or other file format.
564 | SOURCE: SP 800-72; SP 800-101
565 |
566 | Supply Chain Attack – Attacks that allow the adversary to utilize implants or other vulnerabilities inserted prior to installation in order to infiltrate data, or manipulate information technology hardware, software, operating systems, peripherals (information technology products) or services at any point during the life cycle.
567 | SOURCE: CNSSI-4009
568 |
569 | System Development Life Cycle (SDLC) – The scope of activities associated with a system, encompassing the system’s initiation, development and acquisition, implementation, operation and maintenance, and ultimately its disposal that instigates another system initiation.
570 | SOURCE: SP 800-34; CNSSI-4009
571 |
572 | System Development Methodologies – Methodologies developed through software engineering to manage the complexity of system development. Development methodologies include software engineering aids and high-level design analysis tools.
573 | SOURCE: CNSSI-4009
574 |
575 | System Integrity – The quality that a system has when it performs its intended function in an unimpaired manner, free from unauthorized manipulation of the system, whether intentional or accidental.
576 | SOURCE: SP 800-27
577 |
578 | T
579 |
580 | Tailoring – The process by which a security control baseline is modified based on: (i) the application of scoping guidance; (ii) the specification of compensating security controls, if needed; and (iii) the specification of organization-defined parameters in the security controls via explicit assignment and selection statements.
581 | SOURCE: SP 800-37; SP 800-53; SP 800-53A; CNSSI-4009
582 |
583 | Tampering – An intentional event resulting in modification of a system, its intended behavior, or data.
584 | SOURCE: CNSSI-4009
585 |
586 | Telecommunications – Preparation, transmission, communication, or related processing of information (writing, images, sounds, or other data) by electrical, electromagnetic, electromechanical, electro-optical, or electronic means.
587 | SOURCE: CNSSI-4009
588 |
589 | Threat – Any circumstance or event with the potential to adversely impact organizational operations (including mission, functions, image, or reputation), organizational assets, individuals, other organizations, or the Nation through an information system via unauthorized access, destruction, disclosure, modification of information, and/or denial of service.
590 | SOURCE: SP 800-53; SP 800-53A; SP 800-27; SP 800-60; SP 800-
591 | 37; CNSSI-4009
592 |
593 | Threat Analysis – The examination of threat sources against system vulnerabilities to determine the threats for a particular system in a particular operational environment.
594 | SOURCE: SP 800-27
595 |
596 | Threat Assessment – Formal description and evaluation of threat to an information system.
597 | SOURCE: SP 800-53; SP 800-18
598 |
599 | Threat Monitoring – Analysis, assessment, and review of audit trails and other information collected for the purpose of searching out system events that may constitute violations of system security.
600 | SOURCE: CNSSI-4009
601 |
602 | Token – Something that the Claimant possesses and controls (typically a key or password) that is used to authenticate the Claimant’s identity.
603 | SOURCE: SP 800-63
604 |
605 | Tracking Cookie – A cookie placed on a user’s computer to track the user’s activity on different Web sites, creating a detailed profile of the user’s behavior.
606 | SOURCE: SP 800-83
607 |
608 | Traffic Analysis – A form of passive attack in which an intruder observes information about calls (although not necessarily the contents of the messages) and makes inferences, e.g., from the source and destination numbers, or frequency and length of the messages.
609 | SOURCE: SP 800-24
610 |
611 | Trojan Horse – A computer program that appears to have a useful function, but also has a hidden and potentially malicious function that evades security mechanisms, sometimes by exploiting legitimate authorizations of a system entity that invokes the program.
612 | SOURCE: CNSSI-4009
613 |
614 | U
615 |
616 | Unauthorized Access – Unauthorized Occurs when a user, legitimate or unauthorized, accesses a resource that the user is not permitted to use.
617 | SOURCE: FIPS 191
618 |
619 | Unauthorized Disclosure – An event involving the exposure of information to entities not authorized access to the information.
620 | SOURCE: SP 800-57 Part 1; CNSSI-4009
621 |
622 | User – Individual or (system) process authorized to access an information system.
623 | SOURCE: FIPS 200
624 |
625 | User Initialization – A function in the life cycle of keying material; the process whereby a user initializes its cryptographic application (e.g., installing and initializing software and hardware).
626 | SOURCE: SP 800-57 Part 1
627 |
628 | V
629 |
630 | Validation – The process of demonstrating that the system under consideration meets in all respects the specification of that system.
631 | SOURCE: FIPS 201
632 |
633 | Verification – Confirmation, through the provision of objective evidence, that specified requirements have been fulfilled (e.g., an entity’s requirements have been correctly defined, or an entity’s attributes have been correctly presented; or a procedure or function performs as intended and leads to the expected outcome).
634 | SOURCE: CNSSI-4009
635 |
636 | Virtual Machine (VM) – Software that allows a single host to run one or more guest operating systems.
637 | SOURCE: SP 800-115
638 |
639 | Virtual Private Network (VPN) – A virtual network, built on top of existing physical networks, that provides a secure communications tunnel for data and other information transmitted between networks.
640 | SOURCE: SP 800-46
641 |
642 | Virus – A computer program that can copy itself and infect a computer without permission or knowledge of the user. A virus might corrupt
643 | or delete data on a computer, use email programs to spread itself to other computers, or even erase everything on a hard disk.
644 | SOURCE: CNSSI-4009
645 |
646 | Vulnerability – Weakness in an information system, system security procedures, internal controls, or implementation that could be exploited or triggered by a threat source.
647 | SOURCE: SP 800-53; SP 800-53A; SP 800-37; SP 800-60; SP 800-115; FIPS 200
648 |
649 | Vulnerability Assessment –Formal description and evaluation of the vulnerabilities in an information system.
650 | SOURCE: SP 800-53; SP 800-37
651 |
652 | W
653 |
654 | Web Content Filtering Software – A program that prevents access to undesirable Web sites, typically by comparing a requested Web site address to a list of known bad Web sites.
655 | SOURCE: SP 800-69
656 |
657 | Web Risk Assessment – Processes for ensuring Web sites are in compliance with applicable policies.
658 | SOURCE: CNSSI-4009
659 |
660 | Whitelist – A list of discrete entities, such as hosts or applications that are known to be benign and are approved for use within an organization and/or information system.
661 | SOURCE: SP 800-128
662 |
663 | Wi-Fi Protected Access-2 (WPA2) – The approved Wi-Fi Alliance interoperable implementation of the IEEE 802.11i security standard. For federal government use, the implementation must use FIPS-approved encryption, such as AES.
664 | SOURCE: CNSSI-4009
665 |
666 | Wireless Local Area Network (WLAN) – A group of wireless networking devices within a limited geographic area, such as an office building, that exchange data through radio communications. The security of each WLAN is heavily dependent on how well each WLAN component—including client devices, APs, and wireless switches—is secured throughout the WLAN lifecycle, from initial WLAN design and deployment through ongoing maintenance and monitoring.
667 | SOURCE: SP 800-153
668 |
669 | Write – Fundamental operation in an information system that results only in the flow of information from a subject to an object. See Access Type.
670 | SOURCE: CNSSI-4009
671 |
672 | Write Access – Permission to write to an object in an information system.
673 | SOURCE: CNSSI-4009
674 |
675 | Z
676 |
677 | Zeroize – To remove or eliminate the key from a cryptographic equipment or fill device.
678 | SOURCE: CNSSI-4009
679 |
680 | Zombie – A program that is installed on a system to cause it to attack other systems.
681 | SOURCE: SP 800-83
682 |
--------------------------------------------------------------------------------
2085 |
2086 | **VMware Telco Cloud Automation Components. Source: [VMware](https://www.vmware.com/products/telco-cloud-automation.html).**
2087 |
2088 |
2089 | ## Telco Learning Resources
2090 |
2091 | [HPE(Hewlett Packard Enterprise) Telco Blueprints overview](https://techhub.hpe.com/eginfolib/servers/docs/Telco/Blueprints/infocenter/index.html#GUID-9906A227-C1FB-4FD5-A3C3-F3B72EC81CAB.html)
2092 |
2093 | [Network Functions Virtualization Infrastructure (NFVI) by Cisco](https://www.cisco.com/c/en/us/solutions/service-provider/network-functions-virtualization-nfv-infrastructure/index.html)
2094 |
2095 | [Introduction to vCloud NFV Telco Edge from VMware](https://docs.vmware.com/en/VMware-vCloud-NFV-OpenStack-Edition/3.1/vloud-nfv-edge-reference-arch-31/GUID-744C45F1-A8D5-4523-9E5E-EAF6336EE3A0.html)
2096 |
2097 | [VMware Telco Cloud Automation(TCA) Architecture Overview](https://docs.vmware.com/en/VMware-Telco-Cloud-Platform-5G-Edition/1.0/telco-cloud-platform-5G-edition-reference-architecture/GUID-C19566B3-F42D-4351-BA55-DE70D55FB0DD.html)
2098 |
2099 | [5G Telco Cloud from VMware](https://telco.vmware.com/)
2100 |
2101 | [Maturing OpenStack Together To Solve Telco Needs from Red Hat](https://www.redhat.com/cms/managed-files/4.Nokia%20CloudBand%20&%20Red%20Hat%20-%20Maturing%20Openstack%20together%20to%20solve%20Telco%20needs%20Ehud%20Malik,%20Senior%20PLM,%20Nokia%20CloudBand.pdf)
2102 |
2103 | [Red Hat telco ecosystem program](https://connect.redhat.com/en/programs/telco-ecosystem)
2104 |
2105 | [OpenStack for Telcos by Canonical](https://ubuntu.com/blog/openstack-for-telcos-by-canonical)
2106 |
2107 | [Open source NFV platform for 5G from Ubuntu](https://ubuntu.com/telco)
2108 |
2109 | [Understanding 5G Technology from Verizon](https://www.verizon.com/5g/)
2110 |
2111 | [Verizon and Unity partner to enable 5G & MEC gaming and enterprise applications](https://www.verizon.com/about/news/verizon-unity-partner-5g-mec-gaming-enterprise)
2112 |
2113 | [Understanding 5G Technology from Intel](https://www.intel.com/content/www/us/en/wireless-network/what-is-5g.html)
2114 |
2115 | [Understanding 5G Technology from Qualcomm](https://www.qualcomm.com/invention/5g/what-is-5g)
2116 |
2117 | [Telco Acceleration with Xilinx](https://www.xilinx.com/applications/wired-wireless/telco.html)
2118 |
2119 | [VIMs on OSM Public Wiki](https://osm.etsi.org/wikipub/index.php/VIMs)
2120 |
2121 | [Amazon EC2 Overview and Networking Introduction for Telecom Companies](https://docs.aws.amazon.com/whitepapers/latest/ec2-networking-for-telecom/ec2-networking-for-telecom.pdf)
2122 |
2123 | [Citrix Certified Associate – Networking(CCA-N)](http://training.citrix.com/cms/index.php/certification/networking/)
2124 |
2125 | [Citrix Certified Professional – Virtualization(CCP-V)](https://www.globalknowledge.com/us-en/training/certification-prep/brands/citrix/section/virtualization/citrix-certified-professional-virtualization-ccp-v/)
2126 |
2127 | [CCNP Routing and Switching](https://learningnetwork.cisco.com/s/ccnp-enterprise)
2128 |
2129 | [Certified Information Security Manager(CISM)](https://www.isaca.org/credentialing/cism)
2130 |
2131 | [Wireshark Certified Network Analyst (WCNA)](https://www.wiresharktraining.com/certification.html)
2132 |
2133 | [Juniper Networks Certification Program Enterprise (JNCP)](https://www.juniper.net/us/en/training/certification/)
2134 |
2135 | [Cloud Native Computing Foundation Training and Certification Program](https://www.cncf.io/certification/training/)
2136 |
2137 |
2138 | ## Tools
2139 |
2140 | [Open Stack](https://www.openstack.org/) is an open source cloud platform, deployed as infrastructure-as-a-service (IaaS) to orchestrate data center operations on bare metal, private cloud hardware, public cloud resources, or both (hybrid/multi-cloud architecture). OpenStack includes advance use of virtualization & SDN for network traffic optimization to handle the core cloud-computing services of compute, networking, storage, identity, and image services.
2141 |
2142 | [StarlingX](https://www.starlingx.io/) is a complete cloud infrastructure software stack for the edge used by the most demanding applications in industrial IOT, telecom, video delivery and other ultra-low latency use cases.
2143 |
2144 | [Airship](https://www.airshipit.org/) is a collection of open source tools for automating cloud provisioning and management. Airship provides a declarative framework for defining and managing the life cycle of open infrastructure tools and the underlying hardware.
2145 |
2146 | [Network functions virtualization (NFV)](https://www.vmware.com/topics/glossary/content/network-functions-virtualization-nfv) is the replacement of network appliance hardware with virtual machines. The virtual machines use a hypervisor to run networking software and processes such as routing and load balancing. NFV allows for the separation of communication services from dedicated hardware, such as routers and firewalls. This separation means network operations can provide new services dynamically and without installing new hardware. Deploying network components with network functions virtualization only takes hours compared to months like with traditional networking solutions.
2147 |
2148 | [Software Defined Networking (SDN)](https://www.vmware.com/topics/glossary/content/software-defined-networking) is an approach to networking that uses software-based controllers or application programming interfaces (APIs) to communicate with underlying hardware infrastructure and direct traffic on a network. This model differs from that of traditional networks, which use dedicated hardware devices (routers and switches) to control network traffic.
2149 |
2150 | [Virtualized Infrastructure Manager (VIM)](https://www.cisco.com/c/en/us/td/docs/net_mgmt/network_function_virtualization_Infrastructure/3_2_2/install_guide/Cisco_VIM_Install_Guide_3_2_2/Cisco_VIM_Install_Guide_3_2_2_chapter_00.html) is a service delivery and reduce costs with high performance lifecycle management Manage the full lifecycle of the software and hardware comprising your NFV infrastructure (NFVI), and maintaining a live inventory and allocation plan of both physical and virtual resources.
2151 |
2152 | [Management and Orchestration(MANO)](https://www.etsi.org/technologies/open-source-mano) is an ETSI-hosted initiative to develop an Open Source NFV Management and Orchestration (MANO) software stack aligned with ETSI NFV. Two of the key components of the ETSI NFV architectural framework are the NFV Orchestrator and VNF Manager, known as NFV MANO.
2153 |
2154 | [Magma](https://www.magmacore.org/) is an open source software platform that gives network operators an open, flexible and extendable mobile core network solution. Their mission is to connect the world to a faster network by enabling service providers to build cost-effective and extensible carrier-grade networks. Magma is 3GPP generation (2G, 3G, 4G or upcoming 5G networks) and access network agnostic (cellular or WiFi). It can flexibly support a radio access network with minimal development and deployment effort.
2155 |
2156 | [OpenRAN](https://open-ran.org/) is an intelligent Radio Access Network(RAN) integrated on general purpose platforms with open interface between software defined functions. Open RANecosystem enables enormous flexibility and interoperability with a complete openess to multi-vendor deployments.
2157 |
2158 | [Open vSwitch(OVS)](https://www.openvswitch.org/)is an open source production quality, multilayer virtual switch licensed under the open source Apache 2.0 license. It is designed to enable massive network automation through programmatic extension, while still supporting standard management interfaces and protocols (NetFlow, sFlow, IPFIX, RSPAN, CLI, LACP, 802.1ag).
2159 |
2160 | [Edge](https://www.ibm.com/cloud/what-is-edge-computing) is a distributed computing framework that brings enterprise applications closer to data sources such as IoT devices or local edge servers. This proximity to data at its source can deliver strong business benefits, including faster insights, improved response times and better bandwidth availability.
2161 |
2162 | [Multi-access edge computing (MEC)](https://www.etsi.org/technologies/multi-access-edge-computing) is an Industry Specification Group (ISG) within ETSI to create a standardized, open environment which will allow the efficient and seamless integration of applications from vendors, service providers, and third-parties across multi-vendor Multi-access Edge Computing platforms.
2163 |
2164 | [Virtualized network functions(VNFs)](https://www.juniper.net/documentation/en_US/cso4.1/topics/concept/nsd-vnf-overview.html) is a software application used in a Network Functions Virtualization (NFV) implementation that has well defined interfaces, and provides one or more component networking functions in a defined way. For example, a security VNF provides Network Address Translation (NAT) and firewall component functions.
2165 |
2166 | [Cloud-Native Network Functions(CNF)](https://www.cncf.io/announcements/2020/11/18/cloud-native-network-functions-conformance-launched-by-cncf/) is a network function designed and implemented to run inside containers. CNFs inherit all the cloud native architectural and operational principles including Kubernetes(K8s) lifecycle management, agility, resilience, and observability.
2167 |
2168 | [Physical Network Function(PNF)](https://www.mpirical.com/glossary/pnf-physical-network-function) is a physical network node which has not undergone virtualization. Both PNFs and VNFs (Virtualized Network Functions) can be used to form an overall Network Service.
2169 |
2170 | [Network functions virtualization infrastructure(NFVI)](https://docs.vmware.com/en/VMware-vCloud-NFV/2.0/vmware-vcloud-nfv-reference-architecture-20/GUID-FBEA6C6B-54D8-4A37-87B1-D825F9E0DBC7.html) is the foundation of the overall NFV architecture. It provides the physical compute, storage, and networking hardware that hosts the VNFs. Each NFVI block can be thought of as an NFVI node and many nodes can be deployed and controlled geographically.
2171 |
2172 | # Open Source Security
2173 |
2174 | [Back to the Top](https://github.com/mikeroyal/Kubernetes-Guide/blob/main/README.md#table-of-contents)
2175 |
2176 |
2177 | [Open Source Security Foundation (OpenSSF)](https://openssf.org/) is a cross-industry collaboration that brings together leaders to improve the security of open source software by building a broader community, targeted initiatives, and best practices. The OpenSSF brings together open source security initiatives under one foundation to accelerate work through cross-industry support. Along with the Core Infrastructure Initiative and the Open Source Security Coalition, and will include new working groups that address vulnerability disclosures, security tooling and more.
2178 |
2179 | ## Security Standards, Frameworks and Benchmarks
2180 |
2181 | [STIGs Benchmarks - Security Technical Implementation Guides](https://public.cyber.mil/stigs/)
2182 |
2183 | [CIS Benchmarks - CIS Center for Internet Security](https://www.cisecurity.org/cis-benchmarks/)
2184 |
2185 | [CIS Top 18 Critical Security Controls](https://www.cisecurity.org/controls/cis-controls-list)
2186 |
2187 | [OSSTMM (Open Source Security Testing Methodology Manual) PDF](https://github.com/mikeroyal/Open-Source-Security-Guide/files/8834704/osstmm.en.2.1.pdf)
2188 |
2189 | [NIST Technical Guide to Information Security Testing and Assessment (PDF)](https://github.com/mikeroyal/Open-Source-Security-Guide/files/8834705/nistspecialpublication800-115.pdf)
2190 |
2191 | [NIST - Current FIPS](https://www.nist.gov/itl/current-fips)
2192 |
2193 | [ISO Standards Catalogue](https://www.iso.org/standards.html)
2194 |
2195 | [Common Criteria for Information Technology Security Evaluation (CC)](https://www.commoncriteriaportal.org/cc/) is an international standard (ISO / IEC 15408) for computer security. It allows an objective evaluation to validate that a particular product satisfies a defined set of security requirements.
2196 |
2197 | [ISO 22301](https://www.iso.org/en/contents/data/standard/07/51/75106.html) is the international standard that provides a best-practice framework for implementing an optimised BCMS (business continuity management system).
2198 |
2199 | [ISO27001](https://www.iso.org/isoiec-27001-information-security.html) is the international standard that describes the requirements for an ISMS (information security management system). The framework is designed to help organizations manage their security practices in one place, consistently and cost-effectively.
2200 |
2201 | [ISO 27701](https://www.iso.org/en/contents/data/standard/07/16/71670.html) specifies the requirements for a PIMS (privacy information management system) based on the requirements of ISO 27001.
2202 | It is extended by a set of privacy-specific requirements, control objectives and controls. Companies that have implemented ISO 27001 will be able to use ISO 27701 to extend their security efforts to cover privacy management.
2203 |
2204 | [EU GDPR (General Data Protection Regulation)](https://gdpr.eu/) is a privacy and data protection law that supersedes existing national data protection laws across the EU, bringing uniformity by introducing just one main data protection law for companies/organizations to comply with.
2205 |
2206 | [CCPA (California Consumer Privacy Act)](https://www.oag.ca.gov/privacy/ccpa) is a data privacy law that took effect on January 1, 2020 in the State of California. It applies to businesses that collect California residents’ personal information, and its privacy requirements are similar to those of the EU’s GDPR (General Data Protection Regulation).
2207 |
2208 | [Payment Card Industry (PCI) Data Security Standards (DSS)](https://docs.microsoft.com/en-us/microsoft-365/compliance/offering-pci-dss) is a global information security standard designed to prevent fraud through increased control of credit card data.
2209 |
2210 | [SOC 2](https://www.aicpa.org/interestareas/frc/assuranceadvisoryservices/aicpasoc2report.html) is an auditing procedure that ensures your service providers securely manage your data to protect the interests of your comapny/organization and the privacy of their clients.
2211 |
2212 | [NIST CSF](https://www.nist.gov/national-security-standards) is a voluntary framework primarily intended for critical infrastructure organizations to manage and mitigate cybersecurity risk based on existing best practice.
2213 |
2214 | ## Security Tools
2215 |
2216 | [AppArmor](https://www.apparmor.net/) is an effective and easy-to-use Linux application security system. AppArmor proactively protects the operating system and applications from external or internal threats, even zero-day attacks, by enforcing good behavior and preventing both known and unknown application flaws from being exploited. AppArmor supplements the traditional Unix discretionary access control (DAC) model by providing mandatory access control (MAC). It has been included in the mainline Linux kernel since version 2.6.36 and its development has been supported by Canonical since 2009.
2217 |
2218 | [SELinux](https://github.com/SELinuxProject/selinux) is a security enhancement to Linux which allows users and administrators more control over access control. Access can be constrained on such variables as which users and applications can access which resources. These resources may take the form of files. Standard Linux access controls, such as file modes (-rwxr-xr-x) are modifiable by the user and the applications which the user runs. Conversely, SELinux access controls are determined by a policy loaded on the system which may not be changed by careless users or misbehaving applications.
2219 |
2220 | [Control Groups(Cgroups)](https://www.redhat.com/sysadmin/cgroups-part-one) is a Linux kernel feature that allows you to allocate resources such as CPU time, system memory, network bandwidth, or any combination of these resources for user-defined groups of tasks (processes) running on a system.
2221 |
2222 | [EarlyOOM](https://github.com/rfjakob/earlyoom) is a daemon for Linux that enables users to more quickly recover and regain control over their system in low-memory situations with heavy swap usage.
2223 |
2224 | [Libgcrypt](https://www.gnupg.org/related_software/libgcrypt/) is a general purpose cryptographic library originally based on code from GnuPG.
2225 |
2226 | [Pi-hole](https://pi-hole.net/) is a [DNS sinkhole](https://en.wikipedia.org/wiki/DNS_Sinkhole) that protects your devices from unwanted content, without installing any client-side software, intended for use on a private network. It is designed for use on embedded devices with network capability, such as the Raspberry Pi, but it can be used on other machines running Linux and cloud implementations.
2227 |
2228 | [Aircrack-ng](https://www.aircrack-ng.org/) is a network software suite consisting of a detector, packet sniffer, WEP and WPA/WPA2-PSK cracker and analysis tool for 802.11 wireless LANs. It works with any wireless network interface controller whose driver supports raw monitoring mode and can sniff 802.11a, 802.11b and 802.11g traffic.
2229 |
2230 | [Acra](https://cossacklabs.com/acra) is a single database security suite with 9 strong security controls: application level encryption, searchable encryption, data masking, data tokenization, secure authentication, data leakage prevention, database request firewall, cryptographically signed audit logging, security events automation. It is designed to cover the most important data security requirements with SQL and NoSQL databases and distributed apps in a fast, convenient, and reliable way.
2231 |
2232 | [Netdata](https://github.com/netdata/netdata) is high-fidelity infrastructure monitoring and troubleshooting, real-time monitoring Agent collects thousands of metrics from systems, hardware, containers, and applications with zero configuration. It runs permanently on all your physical/virtual servers, containers, cloud deployments, and edge/IoT devices, and is perfectly safe to install on your systems mid-incident without any preparation.
2233 |
2234 | [Trivy](https://aquasecurity.github.io/trivy/) is a comprehensive security scanner for vulnerabilities in container images, file systems, and Git repositories, as well as for configuration issues and hard-coded secrets.
2235 |
2236 | [Lynis](https://cisofy.com/lynis/) is a security auditing tool for Linux, macOS, and UNIX-based systems. Assists with compliance testing (HIPAA/ISO27001/PCI DSS) and system hardening. Agentless, and installation optional.
2237 |
2238 | [OWASP Nettacker](https://github.com/OWASP/Nettacker) is a project created to automate information gathering, vulnerability scanning and eventually generating a report for networks, including services, bugs, vulnerabilities, misconfigurations, and other information. This software will utilize TCP SYN, ACK, ICMP, and many other protocols in order to detect and bypass Firewall/IDS/IPS devices.
2239 |
2240 | [Terrascan](https://runterrascan.io/) is a static code analyzer for Infrastructure as Code to mitigate risk before provisioning cloud native infrastructure.
2241 |
2242 | [Sliver](https://github.com/BishopFox/sliver) is an open source cross-platform adversary emulation/red team framework, it can be used by organizations of all sizes to perform security testing. Sliver's implants support C2 over Mutual TLS (mTLS), WireGuard, HTTP(S), and DNS and are dynamically compiled with per-binary asymmetric encryption keys.
2243 |
2244 | [Attack Surface Analyzer](https://github.com/microsoft/AttackSurfaceAnalyzer) is a [Microsoft](https://github.com/microsoft/) developed open source security tool that analyzes the attack surface of a target system and reports on potential security vulnerabilities introduced during the installation of software or system misconfiguration.
2245 |
2246 | [Intel Owl](https://intelowl.readthedocs.io/) is an Open Source Intelligence, or OSINT solution to get threat intelligence data about a specific file, an IP or a domain from a single API at scale. It integrates a number of analyzers available online and a lot of cutting-edge malware analysis tools.
2247 |
2248 | [Deepfence ThreatMapper](https://deepfence.io/) is a runtime tool that hunts for vulnerabilities in your cloud native production platforms(Linux, K8s, AWS Fargate and more.), and ranks these vulnerabilities based on their risk-of-exploit.
2249 |
2250 | [Dockle](https://containers.goodwith.tech/) is a Container Image Linter for Security and helping build the Best-Practice Docker Image.
2251 |
2252 | [RustScan](https://github.com/RustScan/RustScan) is a Modern Port Scanner.
2253 |
2254 | [gosec](https://github.com/securego/gosec) is a Golang Security Checker that inspects source code for security problems by scanning the Go AST.
2255 |
2256 | [Prowler](https://github.com/prowler-cloud/prowler) is an Open Source security tool to perform AWS security best practices assessments, audits, incident response, continuous monitoring, hardening and forensics readiness. It contains more than 240 controls covering CIS, PCI-DSS, ISO27001, GDPR, HIPAA, FFIEC, SOC2, AWS FTR, ENS and custom security frameworks.
2257 |
2258 | [Burp Suite](https://portswigger.net/burp) is a leading range of cybersecurity tools.
2259 |
2260 | [KernelCI](https://foundation.kernelci.org/) is a community-based open source distributed test automation system focused on upstream kernel development. The primary goal of KernelCI is to use an open testing philosophy to ensure the quality, stability and long-term maintenance of the Linux kernel.
2261 |
2262 | [Continuous Kernel Integration project](https://github.com/cki-project) helps find bugs in kernel patches before they are commited to an upstram kernel tree. We are team of kernel developers, kernel testers, and automation engineers.
2263 |
2264 | [eBPF](https://ebpf.io) is a revolutionary technology that can run sandboxed programs in the Linux kernel without changing kernel source code or loading kernel modules. By making the Linux kernel programmable, infrastructure software can leverage existing layers, making them more intelligent and feature-rich without continuing to add additional layers of complexity to the system.
2265 |
2266 | [Cilium](https://cilium.io/) uses eBPF to accelerate getting data in and out of L7 proxies such as Envoy, enabling efficient visibility into API protocols like HTTP, gRPC, and Kafka.
2267 |
2268 | [Hubble](https://github.com/cilium/hubble) is a Network, Service & Security Observability for Kubernetes using eBPF.
2269 |
2270 | [Istio](https://istio.io/) is an open platform to connect, manage, and secure microservices. Istio's control plane provides an abstraction layer over the underlying cluster management platform, such as Kubernetes and Mesos.
2271 |
2272 | [Certgen](https://github.com/cilium/certgen) is a convenience tool to generate and store certificates for Hubble Relay mTLS.
2273 |
2274 | [Scapy](https://scapy.net/) is a python-based interactive packet manipulation program & library.
2275 |
2276 | [syzkaller](https://github.com/google/syzkaller) is an unsupervised, coverage-guided kernel fuzzer.
2277 |
2278 | [SchedViz](https://github.com/google/schedviz) is a tool for gathering and visualizing kernel scheduling traces on Linux machines.
2279 |
2280 | [oss-fuzz](https://google.github.io/oss-fuzz/) aims to make common open source software more secure and stable by combining modern fuzzing techniques with scalable, distributed execution.
2281 |
2282 | [OSSEC](https://www.ossec.net/) is a free, open-source host-based intrusion detection system. It performs log analysis, integrity checking, Windows registry monitoring, rootkit detection, time-based alerting, and active response.
2283 |
2284 | [Metasploit Project](https://www.metasploit.com/) is a computer security project that provides information about security vulnerabilities and aids in penetration testing and IDS signature development.
2285 |
2286 | [Wfuzz](https://github.com/xmendez/wfuzz) was created to facilitate the task in web applications assessments and it is based on a simple concept: it replaces any reference to the FUZZ keyword by the value of a given payload.
2287 |
2288 | [Nmap](https://nmap.org/) is a security scanner used to discover hosts and services on a computer network, thus building a "map" of the network.
2289 |
2290 | [Patchwork](https://github.com/getpatchwork/patchwork) is a web-based patch tracking system designed to facilitate the contribution and management of contributions to an open-source project.
2291 |
2292 | [pfSense](https://www.pfsense.org/) is a free and open source firewall and router that also features unified threat management, load balancing, multi WAN, and more.
2293 |
2294 | [Snowpatch](https://github.com/ruscur/snowpatch) is a continuous integration tool for projects using a patch-based, mailing-list-centric git workflow. This workflow is used by a number of well-known open source projects such as the Linux kernel.
2295 |
2296 | [Snort](https://www.snort.org/) is an open-source, free and lightweight network intrusion detection system (NIDS) software for Linux and Windows to detect emerging threats.
2297 |
2298 | [Wireshark](https://www.wireshark.org/) is a free and open-source packet analyzer. It is used for network troubleshooting, analysis, software and communications protocol development, and education.
2299 |
2300 | [OpenSCAP](https://www.open-scap.org/) is U.S. standard maintained by [National Institute of Standards and Technology (NIST)](https://www.nist.gov/). It provides multiple tools to assist administrators and auditors with assessment, measurement, and enforcement of security baselines. OpenSCAP maintains great flexibility and interoperability by reducing the costs of performing security audits. Whether you want to evaluate DISA STIGs, NIST‘s USGCB, or Red Hat’s Security Response Team’s content, all are supported by OpenSCAP.
2301 |
2302 | [Tink](https://github.com/google/tink) is a multi-language, cross-platform, open source library that provides cryptographic APIs that are secure, easy to use correctly, and harder to misuse.
2303 |
2304 | [OWASP](https://www.owasp.org/index.php/Main_Page) is an online community, produces freely-available articles, methodologies, documentation, tools, and technologies in the field of web application security.
2305 |
2306 | [Open Vulnerability and Assessment Language](https://oval.mitre.org/) is a community effort to standardize how to assess and report upon the machine state of computer systems. OVAL includes a language to encode system details, and community repositories of content. Tools and services that use OVAL provide enterprises with accurate, consistent, and actionable information to improve their security.
2307 |
2308 | [ClamAV](https://www.clamav.net/) is an open source antivirus engine for detecting trojans, viruses, malware & other malicious threats.
2309 |
2310 | ### Security Tutorials & Resources
2311 |
2312 | - [Microsoft Open Source Software Security](https://www.microsoft.com/en-us/securityengineering/opensource)
2313 |
2314 | - [Cloudflare Open Source Security](https://cloudflare.github.io)
2315 |
2316 | - [The Seven Properties of Highly Secure Devices](https://www.microsoft.com/en-us/research/publication/seven-properties-highly-secure-devices/)
2317 |
2318 | - [How Layer 7 of the Internet Works](https://www.cloudflare.com/learning/ddos/what-is-layer-7/)
2319 |
2320 | - [The 7 Kinds of Security](https://www.veracode.com/sites/default/files/Resources/eBooks/7-kinds-of-security.pdf)
2321 |
2322 | - [The Libgcrypt Reference Manual](https://www.gnupg.org/documentation/manuals/gcrypt/)
2323 |
2324 | - [The Open Web Application Security Project(OWASP) Foundation Top 10](https://owasp.org/www-project-top-ten/)
2325 |
2326 | - [Best Practices for Using Open Source Code from The Linux Foundation](https://www.linuxfoundation.org/blog/2017/11/best-practices-using-open-source-code/)
2327 |
2328 | ### Security Certifications
2329 |
2330 | - [AWS Certified Security - Specialty Certification](https://aws.amazon.com/certification/certified-security-specialty/)
2331 |
2332 | - [Microsoft Certified: Azure Security Engineer Associate](https://docs.microsoft.com/en-us/learn/certifications/azure-security-engineer)
2333 |
2334 | - [Google Cloud Certified Professional Cloud Security Engineer](https://cloud.google.com/certification/cloud-security-engineer)
2335 |
2336 | - [Cisco Security Certifications](https://www.cisco.com/c/en/us/training-events/training-certifications/certifications/security.html)
2337 |
2338 | - [The Red Hat Certified Specialist in Security: Linux](https://www.redhat.com/en/services/training/ex415-red-hat-certified-specialist-security-linux-exam)
2339 |
2340 | - [Linux Professional Institute LPIC-3 Enterprise Security Certification](https://www.lpi.org/our-certifications/lpic-3-303-overview)
2341 |
2342 | - [Cybersecurity Training and Courses from IBM Skills](https://www.ibm.com/skills/topics/cybersecurity/)
2343 |
2344 | - [Cybersecurity Courses and Certifications by Offensive Security](https://www.offensive-security.com/courses-and-certifications/)
2345 |
2346 | - [RSA Certification Program](https://community.rsa.com/community/training/certification)
2347 |
2348 | - [Check Point Certified Security Expert(CCSE) Certification](https://training-certifications.checkpoint.com/#/courses/Check%20Point%20Certified%20Expert%20(CCSE)%20R80.x)
2349 |
2350 | - [Check Point Certified Security Administrator(CCSA) Certification](https://training-certifications.checkpoint.com/#/courses/Check%20Point%20Certified%20Admin%20(CCSA)%20R80.x)
2351 |
2352 | - [Check Point Certified Security Master (CCSM) Certification](https://training-certifications.checkpoint.com/#/courses/Check%20Point%20Certified%20Master%20(CCSM)%20R80.x)
2353 |
2354 | - [Certified Cloud Security Professional(CCSP) Certification](https://www.isc2.org/Certifications/CCSP)
2355 |
2356 | - [Certified Information Systems Security Professional (CISSP) Certification](https://www.isc2.org/Certifications/CISSP)
2357 |
2358 | - [CCNP Routing and Switching](https://learningnetwork.cisco.com/s/ccnp-enterprise)
2359 |
2360 | - [Certified Information Security Manager(CISM)](https://www.isaca.org/credentialing/cism)
2361 |
2362 | - [Wireshark Certified Network Analyst (WCNA)](https://www.wiresharktraining.com/certification.html)
2363 |
2364 | - [Juniper Networks Certification Program Enterprise (JNCP)](https://www.juniper.net/us/en/training/certification/)
2365 |
2366 | - [Security Training Certifications and Courses from Udemy](https://www.udemy.com/courses/search/?src=ukw&q=secuirty)
2367 |
2368 | - [Security Training Certifications and Courses from Coursera](https://www.coursera.org/search?query=security&)
2369 |
2370 | - [Security Certifications Training from Pluarlsight](https://www.pluralsight.com/browse/information-cyber-security/security-certifications)
2371 |
2372 |
2373 | ## Contribute
2374 |
2375 | - [x] If would you like to contribute to this guide simply make a [Pull Request](https://github.com/mikeroyal/Kubernetes-Guide/pulls).
2376 |
2377 |
2378 | ## License
2379 | [Back to the Top](https://github.com/mikeroyal/Kubernetes-Guide/blob/main/README.md#table-of-contents)
2380 |
2381 | Distributed under the [Creative Commons Attribution 4.0 International (CC BY 4.0) Public License](https://creativecommons.org/licenses/by/4.0/).
2382 |
--------------------------------------------------------------------------------
/Security Glossary.md:
--------------------------------------------------------------------------------
1 | A list of Key Information Security Terms for Software and Hardware. **Sources:** [NIST Federal Information Processing Standards (FIPS)](https://csrc.nist.gov/publications/fips), the [Special Publication (SP) 800 series](https://csrc.nist.gov/publications/sp), [NIST Interagency Reports (NISTIRs)](https://csrc.nist.gov/publications/nistir), and from the [Committee for National Security Systems Instruction 4009 (CNSSI-4009)](https://www.cnss.gov/CNSS/issuances/Instructions.cfm).
2 |
3 |
4 | A
5 |
6 | Access – Ability and means to communicate with or otherwise interact with a system, to use system resources to handle information, to gain knowledge of the information the system contains, or to control system components and functions.
7 | SOURCE: CNSSI-4009
8 |
9 | Access Authority – An entity responsible for monitoring and granting access privileges for other authorized entities.
10 | SOURCE: CNSSI-4009
11 |
12 | Access Control – The process of granting or denying specific requests to: 1) obtain and use information and related information processing services; and 2) enter specific physical facilities (e.g., federal buildings, military establishments, border crossing entrances).
13 | SOURCE: FIPS 201; CNSSI-4009
14 |
15 | Access Control List (ACL) –
16 | * 1. A list of permissions associated with an object. The list specifies who or what is allowed to access the object and what operations are allowed to be performed on the object.
17 | * 2. A mechanism that implements access control for a system resource by enumerating the system entities that are permitted to access the resource and stating, either implicitly or explicitly, the access modes granted to each entity.
18 | SOURCE: CNSSI-4009
19 |
20 | Access Control Lists (ACLs) – A register of:
21 | * 1. users (including groups, machines, processes) who have been given permission to use a particular system resource, and
22 | * 2. the types of access they have been permitted.
23 | SOURCE: SP 800-12
24 |
25 | Access Control Mechanism – Security safeguards (i.e., hardware and software features, physical controls, operating procedures, management procedures, and various combinations of these) designed to detect and deny unauthorized
26 | access and permit authorized access to an information system.
27 | SOURCE: CNSSI-4009
28 |
29 | Access Level – A category within a given security classification limiting entry or
30 | system connectivity to only authorized persons.
31 | SOURCE: CNSSI-4009
32 |
33 | Access List – Roster of individuals authorized admittance to a controlled area.
34 | SOURCE: CNSSI-4009
35 |
36 | Access Point – A device that logically connects wireless client devices operating in infrastructure to one another and provides access to a distribution system, if connected, which is typically an organization’s enterprise wired network.
37 | SOURCE: SP 800-48; SP 800-121
38 |
39 | Access Profile – Association of a user with a list of protected objects the user may access.
40 | SOURCE: CNSSI-4009
41 |
42 | Access Type – Privilege to perform action on an object. Read, write, execute, append, modify, delete, and create are examples of access types.
43 | SOURCE: CNSSI-4009
44 |
45 | Activation Data – Private data, other than keys, that are required to access cryptographic modules.
46 | SOURCE: SP 800-32
47 |
48 | Active Attack – An attack that alters a system or data.
49 | SOURCE: CNSSI-4009
50 |
51 | Active Content – Software in various forms that is able to automatically carry out or trigger actions on a computer platform without the intervention of a user.
52 | SOURCE: CNSSI-4009
53 |
54 | Active Security Testing – Security testing that involves direct interaction with a target, such as sending packets to a target.
55 | SOURCE: SP 800-115
56 |
57 | Advanced Encryption Standard – (AES) The Advanced Encryption Standard specifies a U.S. government-approved cryptographic algorithm that can be used to protect electronic data. The AES algorithm is a symmetric block cipher that can encrypt (encipher) and decrypt (decipher) information. This standard specifies the Rijndael algorithm, a symmetric block cipher that can process data blocks of 128 bits, using cipher keys with lengths of 128, 192, and 256 bits.
58 | SOURCE: FIPS 197
59 |
60 | B
61 |
62 | Blacklisting – The process of the system invalidating a user ID based on the user’s inappropriate actions. A blacklisted user ID cannot be used to log on to the system, even with the correct authenticator. Blacklisting and lifting of a blacklisting are both security-relevant events. Blacklisting also applies to blocks placed against IP addresses to prevent inappropriate or unauthorized use of Internet resources.
63 | SOURCE: CNSSI-4009
64 |
65 | Blue Team –
66 | * 1. The group responsible for defending an enterprise’s use of
67 | information systems by maintaining its security posture against a
68 | group of mock attackers (i.e., the Red Team). Typically the Blue
69 | Team and its supporters must defend against real or simulated
70 | attacks 1) over a significant period of time, 2) in a representative
71 | operational context (e.g., as part of an operational exercise), and 3)
72 | according to rules established and monitored with the help of a
73 | neutral group refereeing the simulation or exercise (i.e., the White
74 | Team).
75 | * 2. The term Blue Team is also used for defining a group of
76 | individuals that conduct operational network vulnerability
77 | evaluations and provide mitigation techniques to customers who have
78 | a need for an independent technical review of their network security
79 | posture. The Blue Team identifies security threats and risks in the
80 | operating environment, and in cooperation with the customer,
81 | analyzes the network environment and its current state of security
82 | readiness. Based on the Blue Team findings and expertise,
83 | they provide recommendations that integrate into an overall
84 | community security solution to increase the customer's cyber security
85 | readiness posture. Often times a Blue Team is employed by itself or
86 | prior to a Red Team employment to ensure that the customer's
87 | networks are as secure as possible before having the Red Team test
88 | the systems.
89 | SOURCE: CNSSI-4009
90 |
91 | Body of Evidence (BoE) – The set of data that documents the information system’s adherence to the security controls applied. The BoE will include a Requirements Verification Traceability Matrix (RVTM) delineating where the selected security controls are met and evidence to that fact can be found. The BoE content required by an Authorizing Official will be adjusted according to the impact levels selected.
92 | SOURCE: CNSSI-4009
93 |
94 | Boundary – Physical or logical perimeter of a system.
95 | SOURCE: CNSSI-4009
96 |
97 | C
98 |
99 | Capstone Policies – Those policies that are developed by governing or coordinating institutions of Health Information Exchanges (HIEs). They provide overall requirements and guidance for protecting health information within those HIEs. Capstone Policies must address the requirements imposed by: (1) all laws, regulations, and guidelines at the federal, state, and local levels; (2) business needs; and (3) policies at the institutional and HIE levels.
100 | SOURCE: NISTIR-7497
101 |
102 | Capture – The method of taking a biometric sample from an end user.
103 | Source: FIPS 201
104 |
105 | Certificate Management – Process whereby certificates (as defined above) are generated, stored, protected, transferred, loaded, used, and destroyed.
106 | SOURCE: CNSSI-4009
107 |
108 | Certificate Management Authority – A Certification Authority (CA) or a Registration Authority (RA).
109 | SOURCE: SP 800-32
110 |
111 | Certificate Policy (CP) – A specialized form of administrative policy tuned to electronic transactions performed during certificate management. A Certificate Policy addresses all aspects associated with the generation, production, distribution, accounting, compromise recovery, and administration of digital certificates. Indirectly, a certificate policy can also govern the transactions conducted using a communications system protected by a certificate-based security system. By controlling critical certificate extensions, such policies and associated enforcement technology can support provision of the security services required by particular applications.
112 | SOURCE: CNSSI-4009; SP 800-32
113 |
114 | Certification Practice Statement – A statement of the practices that a Certification Authority employs in issuing, suspending, revoking, and renewing certificates and providing access to them, in accordance with specific requirements (i.e., requirements specified in this Certificate Policy, or requirements specified in a contract for services).
115 | SOURCE: SP 800-32; CNSSI-4009
116 |
117 | Certification Test and Evaluation – Software and hardware security tests conducted during development of an information system.
118 | SOURCE: CNSSI-4009
119 |
120 | Checksum – Value computed on data to detect error or manipulation.
121 | SOURCE: CNSSI-4009
122 |
123 | Cloud Computing - A model for enabling ubiquitous, convenient, on-demand network access to a shared pool of configurable computing resources (e.g., networks, servers, storage, applications, and services) that can be rapidly provisioned and released with minimal management effort or service Provider interaction. This cloud model is composed of five essential characteristics, three service models, and four deployment models
124 | SOURCE(s): NISTIR 8006 under Cloud computing from NIST SP 800-145 - Adapted
125 |
126 | Cryptographic Initialization – Function used to set the state of a cryptographic logic prior to key generation, encryption, or other operating mode.
127 | SOURCE: CNSSI-4009
128 |
129 | Cryptographic Key – A value used to control cryptographic operations, such as decryption, encryption, signature generation, or signature verification.
130 | SOURCE: SP 800-63
131 |
132 | D
133 |
134 | Data – A subset of information in an electronic format that allows it to be retrieved or transmitted.
135 | SOURCE: CNSSI-4009
136 |
137 | Data Aggregation – Compilation of individual data systems and data that could result in the totality of the information being classified, or classified at a higher level, or of beneficial use to an adversary.
138 | SOURCE: CNSSI-4009
139 |
140 | Data Origin Authentication – The process of verifying that the source of the data is as claimed and that the data has not been modified.
141 | SOURCE: CNSSI-4009
142 |
143 | Data Security – Protection of data from unauthorized (accidental or intentional) modification, destruction, or disclosure.
144 | SOURCE: CNSSI-4009
145 |
146 | Data Transfer Device (DTD) – Fill device designed to securely store, transport, and transfer electronically both COMSEC and TRANSEC key, designed to be backward compatible with the previous generation of COMSEC common fill devices, and programmable to support modern mission systems.
147 | SOURCE: CNSSI-4009
148 |
149 | Denial of Service (DoS) – The prevention of authorized access to resources or the delaying of time-critical operations. (Time-critical may be milliseconds or it may be hours, depending upon the service provided.)
150 | SOURCE: CNSSI-4009
151 |
152 | Differential Power Analysis – An analysis of the variations of the electrical power consumption of a cryptographic module, using advanced statistical methods and/or other techniques, for the purpose of extracting information correlated to cryptographic keys used in a cryptographic algorithm.
153 | SOURCE: FIPS 140-2
154 |
155 | Digital Evidence – Electronic information stored or transferred in digital form.
156 | SOURCE: SP 800-72
157 |
158 | Digital Forensics – The application of science to the identification, collection, examination, and analysis of data while preserving the integrity of the information and maintaining a strict chain of custody for the data.
159 | SOURCE: SP 800-86
160 |
161 | Digital Signature – An asymmetric key operation where the private key is used to digitally sign data and the public key is used to verify the signature. Digital signatures provide authenticity protection, integrity protection, and non-repudiation.
162 | SOURCE: SP 800-63
163 |
164 | Disaster Recovery Plan (DRP) – A written plan for recovering one or more information systems at an alternate facility in response to a major hardware or software failure or destruction of facilities.
165 | SOURCE: SP 800-34
166 |
167 | E
168 |
169 | Embedded Cryptographic System – Cryptosystem performing or controlling a function as an integral element of a larger system or subsystem.
170 | SOURCE: CNSSI-4009
171 |
172 | Embedded Cryptography - Cryptography engineered into an equipment or system whose basic function is not cryptographic.
173 | SOURCE: CNSSI-4009
174 |
175 | Encipher – Convert plain text to cipher text by means of a cryptographic system.
176 | SOURCE: CNSSI-4009
177 |
178 | Encode – Convert plain text to cipher text by means of a code.
179 | SOURCE: CNSSI-4009
180 |
181 | Encrypt – Generic term encompassing encipher and encode.
182 | SOURCE: CNSSI-4009
183 |
184 | Encrypted Key – A cryptographic key that has been encrypted using an Approved security function with a key encrypting key, a PIN, or a password in order to disguise the value of the underlying plaintext key.
185 | SOURCE: FIPS 140-2
186 |
187 | Encrypted Network – A network on which messages are encrypted (e.g., using DES, AES, or other appropriate algorithms) to prevent reading by unauthorized parties.
188 | SOURCE: SP 800-32
189 |
190 | Encryption – Conversion of plaintext to ciphertext through the use of a cryptographic algorithm.
191 | SOURCE: FIPS 185
192 |
193 | End-to-End Encryption – Encryption of information at its origin and decryption at its intended destination without intermediate decryption.
194 | SOURCE: CNSSI-4009
195 |
196 | End-to-End Security – Safeguarding information in an information system from point of origin to point of destination.
197 | SOURCE: CNSSI-4009
198 |
199 | F
200 |
201 | [Federal Risk and Authorization Management Program (FedRAMP)](https://www.gsa.gov/technology/government-it-initiatives/fedramp) is a government-wide program that provides a standardized approach to security assessment, authorization, and continuous monitoring for cloud products and services. FedRAMP empowers agencies to use modern cloud technologies, with emphasis on security and protection of federal information, and helps accelerate the adoption of secure, cloud solutions.
202 |
203 | [Federal Information Security Management Act (FISMA)](https://csrc.nist.gov/topics/laws-and-regulations/laws/fisma) is a United States federal law that defines a comprehensive framework to protect government information, operations, and assets against natural and manmade threats. This risk management framework was signed into law as part of the Electronic Government Act of 2002. Since 2002, FISMA's scope has widened to apply to state agencies that administer federal programs, or private businesses and service providers that hold a contract with the U.S. government.
204 |
205 | False Positive – An alert that incorrectly indicates that malicious activity is occurring.
206 | SOURCE: SP 800-61
207 |
208 | False Rejection – In biometrics, the instance of a security system failing to verify or identify an authorized person. It does not necessarily indicate a flaw in the biometric system; for example, in a fingerprint-based system, an incorrectly aligned finger on the scanner or dirt on the scanner can result in the scanner misreading the fingerprint, causing a false rejection of the authorized user.
209 | SOURCE: CNSSI-4009
210 |
211 | Federal Information Processing Standard (FIPS) – A standard for adoption and use by federal departments and agencies that has been developed within the Information Technology Laboratory and published by the National Institute of Standards and Technology, a part of the U.S. Department of Commerce. A FIPS covers some topic in information technology in order to achieve a common level of quality or some level of interoperability.
212 | SOURCE: FIPS 201
213 |
214 | File Encryption – The process of encrypting individual files on a storage medium and permitting access to the encrypted data only after proper authentication is provided.
215 | SOURCE: SP 800-111
216 |
217 | File Name Anomaly –
218 | * 1. A mismatch between the internal file header and its external
219 | extension.
220 | * 2. A file name inconsistent with the content of the file (e.g., renaming
221 | a graphics file with a non-graphical extension.
222 | SOURCE: SP 800-72
223 |
224 | File Protection – Aggregate of processes and procedures designed to inhibit unauthorized access, contamination, elimination, modification, or destruction of a file or any of its contents.
225 | SOURCE: CNSSI-4009
226 |
227 | File Security – Means by which access to computer files is limited to authorized users only.
228 | SOURCE: CNSSI-4009
229 |
230 | Firewall – A gateway that limits access between networks in accordance with local security policy.
231 | SOURCE: SP 800-32
232 |
233 | Forensics – The practice of gathering, retaining, and analyzing computer-related data for investigative purposes in a manner that maintains the integrity of the data.
234 | SOURCE: CNSSI-4009
235 |
236 | G
237 |
238 | Gateway – Interface providing compatibility between networks by converting transmission speeds, protocols, codes, or security measures.
239 | SOURCE: CNSSI-4009
240 |
241 | H
242 |
243 | Handshaking Procedures – Dialogue between two information systems for synchronizing, identifying, and authenticating themselves to one another.
244 | SOURCE: CNSSI-4009
245 |
246 | Hard Copy Key – Physical keying material, such as printed key lists, punched or printed key tapes, or programmable, read-only memories (PROM).
247 | SOURCE: CNSSI-4009
248 |
249 | Hardening – Configuring a host’s operating systems and applications to reduce the host’s security weaknesses.
250 | SOURCE: SP 800-123
251 |
252 | Hardware – The physical components of an information system.
253 | SOURCE: CNSSI-4009
254 |
255 | High Availability – A failover feature to ensure availability during device or component interruptions.
256 | SOURCE: SP 800-113
257 |
258 | I
259 |
260 | Identification – The process of verifying the identity of a user, process, or device, usually as a prerequisite for granting access to resources in an IT system.
261 | SOURCE: SP 800-47
262 |
263 | Identifier – Unique data used to represent a person’s identity and associated attributes. A name or a card number are examples of identifiers.
264 | SOURCE: FIPS 201
265 |
266 | Identity – A set of attributes that uniquely describe a person within a given context.
267 | SOURCE: SP 800-63
268 |
269 | Identity – The set of physical and behavioral characteristics by which an individual is uniquely recognizable.
270 | SOURCE: FIPS 201
271 |
272 | Identity Token – Smart card, metal key, or other physical object used to authenticate identity.
273 | SOURCE: CNSSI-4009
274 |
275 | Identity Validation – Tests enabling an information system to authenticate users or resources.
276 | SOURCE: CNSSI-4009
277 |
278 | Incident – A violation or imminent threat of violation of computer security policies, acceptable use policies, or standard security practices.
279 | SOURCE: SP 800-61
280 |
281 | Intellectual Property – Creations of the mind such as musical, literary, and artistic works; inventions; and symbols, names, images, and designs used in commerce, including copyrights, trademarks, patents, and related rights. Under intellectual property law, the holder of one of these abstract “properties” has certain exclusive rights to the creative work, commercial symbol, or invention by which it is covered.
282 | SOURCE: CNSSI-4009
283 |
284 | Internet Protocol (IP) – Standard protocol for transmission of data from source to destinations in packet-switched communications networks and interconnected systems of such networks.
285 | SOURCE: CNSSI-4009
286 |
287 | Intranet – A private network that is employed within the confines of a given enterprise (e.g., internal to a business or agency).
288 | SOURCE: CNSSI-4009
289 |
290 | Intrusion – Unauthorized act of bypassing the security mechanisms of a system.
291 | SOURCE: CNSSI-4009
292 |
293 | Intrusion Detection Systems (IDS) – Hardware or software product that gathers and analyzes information from various areas within a computer or a network to identify possible security breaches, which include both intrusions (attacks from outside the organizations) and misuse (attacks from within the organizations.)
294 | SOURCE: CNSSI-4009
295 |
296 | J
297 |
298 | Jamming – An attack in which a device is used to emit electromagnetic energy on a wireless network’s frequency to make it unusable.
299 | SOURCE: SP 800-48
300 |
301 | K
302 |
303 | Kerberos – A means of verifying the identities of principals on an open network. It accomplishes this without relying on the authentication, trustworthiness, or physical security of hosts while assuming all packets can be read, modified and inserted at will. It uses a trust broker model and symmetric cryptography to provide authentication and authorization of users and systems on the network.
304 | SOURCE: SP 800-95
305 |
306 | Key – A value used to control cryptographic operations, such as decryption, encryption, signature generation, or signature verification.
307 | SOURCE: SP 800-63
308 |
309 | Key Logger – A program designed to record which keys are pressed on a computer keyboard used to obtain passwords or encryption keys and thus bypass other security measures.
310 | SOURCE: SP 800-82
311 |
312 | L
313 |
314 | Least Privilege – The security objective of granting users only those accesses they need to perform their official duties.
315 | SOURCE: SP 800-12
316 |
317 | Level of Protection – Extent to which protective measures, techniques, and procedures must be applied to information systems and networks based on risk, threat, vulnerability, system interconnectivity considerations, and information assurance needs. Levels of protection are:
318 | * 1. Basic: information systems and networks requiring implementation of standard minimum security countermeasures.
319 | * 2. Medium: information systems and networks requiring layering of additional safeguards above the standard minimum security countermeasures.
320 | * 3. High: information systems and networks requiring the most stringent protection and rigorous security countermeasures.
321 | SOURCE: CNSSI-4009
322 |
323 | Likelihood of Occurrence – In Information Assurance risk analysis, a weighted factor based on a subjective analysis of the probability that a given threat is capable of exploiting a given vulnerability.
324 | SOURCE: CNSSI-4009
325 |
326 | M
327 |
328 | Malicious Code – Software or firmware intended to perform an unauthorized process that will have adverse impact on the confidentiality, integrity, or availability of an information system. A virus, worm, Trojan horse, or other code-based entity that infects a host. Spyware and some forms of adware are also examples of malicious code.
329 | SOURCE: SP 800-53; CNSSI-4009
330 |
331 | Malware – A program that is inserted into a system, usually covertly, with the intent of compromising the confidentiality, integrity, or availability of the victim’s data, applications, or operating system or of otherwise annoying or disrupting the victim.
332 | SOURCE: SP 800-83
333 |
334 | Man-in-the-middle Attack (MitM) – A form of active wiretapping attack in which the attacker intercepts and selectively modifies communicated data to masquerade as one or more of the entities involved in a communication association.
335 | SOURCE: CNSSI-4009
336 |
337 | Mandatory Access Control (MAC) – A means of restricting access to system resources based on the sensitivity (as represented by a label) of the information contained in the system resource and the formal authorization (i.e., clearance) of users to access information of such sensitivity.
338 | SOURCE: SP 800-44
339 |
340 | Mandatory Access Control – Access controls (which) are driven by the results of a comparison between the user’s trust level or clearance and the sensitivity designation of the information.
341 | SOURCE: FIPS 191
342 |
343 | Masquerading –When an unauthorized agent claims the identity of another agent, it is said to be masquerading.
344 | SOURCE: SP 800-19
345 |
346 | Multilevel Security (MLS) – A concept of processing information with different classifications and categories that simultaneously permits access by users with different security clearances and denies access to users who lack authorization.
347 | SOURCE: CNSSI-4009
348 |
349 | N
350 |
351 | Needs Assessment (IT Security Awareness and Training) – A process that can be used to determine an organization’s awareness and training needs. The results of a needs assessment can provide justification to convince management to allocate adequate resources
352 | to meet the identified awareness and training needs.
353 | SOURCE: SP 800-50
354 |
355 | Network – Information system(s) implemented with a collection of interconnected components. Such components may include routers,
356 | hubs, cabling, telecommunications controllers, key distribution centers, and technical control devices.
357 | SOURCE: SP 800-53; CNSSI-4009
358 |
359 | Network Access – Access to an organizational information system by a user (or a process acting on behalf of a user) communicating through a network (e.g., local area network, wide area network, Internet).
360 | SOURCE: SP 800-53; CNSSI-4009
361 |
362 | Network Access Control (NAC) – A feature provided by some firewalls that allows access based on a user’s credentials and the results of health checks performed on the telework client device.
363 | SOURCE: SP 800-41
364 |
365 | Network Address Translation (NAT) – A routing technology used by many firewalls to hide internal system addresses from an external network through use of an addressing schema.
366 | SOURCE: SP 800-41
367 |
368 | O
369 |
370 | Object Identifier – A specialized formatted number that is registered with an internationally recognized standards organization. The unique alphanumeric/numeric identifier registered under the ISO registration standard to reference a specific object or object class. In the federal government PKI, they are used to uniquely identify each of the four policies and cryptographic algorithms supported.
371 | SOURCE: SP 800-32
372 |
373 | Open Storage – Any storage of classified national security information outside of approved containers. This includes classified information that is resident on information systems media and outside of an approved storage container, regardless of whether or not that media is in use (i.e., unattended operations).
374 | SOURCE: CNSSI-4009
375 |
376 | Operating System (OS) Fingerprinting – Analyzing characteristics of packets sent by a target, such as packet headers or listening ports, to identify the operating system in use on the target.
377 | SOURCE: SP 800-115
378 |
379 | Operations Code – Code composed largely of words and phrases suitable for general communications use.
380 | SOURCE: CNSSI-4009
381 |
382 | Organization – A federal agency, or, as appropriate, any of its operational elements.
383 | SOURCE: FIPS 200
384 |
385 | Overwrite Procedure – A software process that replaces data previously stored on storage media with a predetermined set of meaningless data or random patterns.
386 | SOURCE: CNSSI-4009
387 |
388 | P
389 |
390 | Packet Filter – A routing device that provides access control functionality for host addresses and communication sessions.
391 | SOURCE: SP 800-41
392 |
393 | Packet Sniffer – Software that observes and records network traffic.
394 | SOURCE: CNSSI-4009
395 |
396 | Password – A protected character string used to authenticate the identity of a computer system user or to authorize access to system resources.
397 | SOURCE: FIPS 181
398 |
399 | Password Cracking – The process of recovering secret passwords stored in a computer system or transmitted over a network.
400 | SOURCE: SP 800-115
401 |
402 | Password Protected – The ability to protect a file using a password access control, protecting the data contents from being viewed with the appropriate viewer unless the proper password is entered.
403 | SOURCE: SP 800-72
404 |
405 | Patch – An update to an operating system, application, or other software issued specifically to correct particular problems with the software.
406 | SOURCE: SP 800-123
407 |
408 | Payload – The input data to the CCM generation-encryption process that is both authenticated and encrypted.
409 | SOURCE: SP 800-38C
410 |
411 | Penetration Testing – A test methodology in which assessors, using all available documentation (e.g., system design, source code, manuals) and working under specific constraints, attempt to circumvent the security features of an information system.
412 | SOURCE: SP 800-53A
413 |
414 | Personal Identification Number (PIN) – A secret that a claimant memorizes and uses to authenticate his or her identity. PINs are generally only decimal digits.
415 | SOURCE: FIPS 201
416 |
417 | Phishing - A digital form of social engineering that uses authentic looking but bogus emails to request information from users or direct them to a fake Web site that requests information.
418 | SOURCE: SP 800-115
419 |
420 | Plaintext – Data input to the Cipher or output from the Inverse Cipher.
421 | SOURCE: FIPS 197
422 |
423 | Policy Mapping – Recognizing that, when a CA in one domain certifies a CA in another domain, a particular certificate policy in the second domain may be considered by the authority of the first domain to be equivalent (but not necessarily identical in all respects) to a particular certificate policy in the first domain.
424 | SOURCE: SP 800-15
425 |
426 | Port – A physical entry or exit point of a cryptographic module that provides access to the module for physical signals, represented by logical information flows (physically separated ports do not share the same physical pin or wire).
427 | SOURCE: FIPS 140-2
428 |
429 | Port Scanning – Using a program to remotely determine which ports on a system are open (e.g., whether systems allow connections through those ports).
430 | SOURCE: CNSSI-4009
431 |
432 | Portal – A high-level remote access architecture that is based on a server that offers teleworkers access to one or more applications through a single centralized interface.
433 | SOURCE: SP 800-46
434 |
435 | Privilege – A right granted to an individual, a program, or a process.
436 | SOURCE: CNSSI-4009
437 |
438 | Privileged Accounts – Individuals who have access to set “access rights” for users on a given system. Sometimes referred to as system or network administrative accounts.
439 | SOURCE: SP 800-12
440 |
441 | Probe – A technique that attempts to access a system to learn something about the system.
442 | SOURCE: CNSSI-4009
443 |
444 | Profiling – Measuring the characteristics of expected activity so that changes to it can be more easily identified.
445 | SOURCE: SP 800-61; CNSSI-4009
446 |
447 | Protocol – Set of rules and formats, semantic and syntactic, permitting information systems to exchange information.
448 | SOURCE: CNSSI-4009
449 |
450 | Protocol Data Unit – A unit of data specified in a protocol and consisting of protocol information and, possibly, user data.
451 | SOURCE: FIPS 188
452 |
453 | Protocol Entity – Entity that follows a set of rules and formats (semantic and syntactic) that determines the communication behavior of other entities.
454 | SOURCE: FIPS 188
455 |
456 | Proxy – A proxy is an application that “breaks” the connection between client and server. The proxy accepts certain types of traffic entering or leaving a network and processes it and forwards it. This effectively closes the straight path between the internal and external networks making it more difficult for an attacker to obtain internal addresses and other details of the organization’s internal network. Proxy servers are available for common Internet services; for example, a Hyper Text Transfer Protocol (HTTP) proxy used for Web access, and a Simple Mail Transfer Protocol (SMTP) proxy used for email.
457 | SOURCE: SP 800-44
458 |
459 | Proxy Server – A server that services the requests of its clients by forwarding those requests to other servers.
460 | SOURCE: CNSSI-4009
461 |
462 | Public Domain Software – Software not protected by copyright laws of any nation that may be freely used without permission of, or payment to, the creator, and that carries no warranties from, or liabilities to the creator.
463 | SOURCE: CNSSI-4009
464 |
465 | Public Key - A cryptographic key used with a public key cryptographic algorithm, uniquely associated with an entity, and which may be made public; it is used to verify a digital signature; this key is mathematically linked with a corresponding private key.
466 | SOURCE: FIPS 196
467 |
468 | Q
469 |
470 | Qualitative Assessment – Use of a set of methods, principles, or rules for assessing risk based on nonnumeric categories or levels.
471 | SOURCE: SP 800-30
472 |
473 | Quality of Service – The measurable end-to-end performance properties of a network service, which can be guaranteed in advance by a Service-Level Agreement between a user and a service provider, so as to satisfy specific customer application requirements. Note: These properties may include throughput (bandwidth), transit delay (latency), error rates, priority, security, packet loss, packet jitter, etc.
474 | SOURCE: CNSSI-4009
475 |
476 | Quantitative Assessment – Use of a set of methods, principles, or rules for assessing risks based on the use of numbers where the meanings and proportionality of values are maintained inside and outside the context of the assessment.
477 | SOURCE: SP 800-30
478 |
479 | Quarantine – Store files containing malware in isolation for future disinfection or examination.
480 | SOURCE: SP 800-69
481 |
482 | R
483 |
484 | Radio Frequency Identification (RFID) – A form of automatic identification and data capture (AIDC) that uses electric or magnetic fields at radio frequencies to transmit information.
485 | SOURCE: SP 800-98
486 |
487 | Read – Fundamental operation in an information system that results only in the flow of information from an object to a subject.
488 | SOURCE: CNSSI-4009
489 |
490 | Read Access – Permission to read information in an information system.
491 | SOURCE: CNSSI-4009
492 |
493 | Real-Time Reaction – Immediate response to a penetration attempt that is detected and diagnosed in time to prevent access.
494 | SOURCE: CNSSI-4009
495 |
496 | Red Team – A group of people authorized and organized to emulate a potential adversary’s attack or exploitation capabilities against an enterprise’s security posture. The Red Team’s objective is to improve enterprise Information Assurance by demonstrating the impacts of successful attacks and by demonstrating what works for the defenders (i.e., the Blue Team) in an operational environment.
497 | SOURCE: CNSSI-4009
498 |
499 | Red Team Exercise – An exercise, reflecting real-world conditions, that is conducted as a simulated adversarial attempt to compromise organizational missions and/or business processes to provide a comprehensive assessment of the security capability of the information system and organization.
500 | SOURCE: SP 800-53
501 |
502 | Remote Access – Access to an organizational information system by a user (or an information system acting on behalf of a user) communicating through an external network (e.g., the Internet).
503 | SOURCE: SP 800-53
504 |
505 | Repository – A database containing information and data relating to certificates as specified in a CP; may also be referred to as a directory.
506 | SOURCE: SP 800-32
507 |
508 | Risk Assessment – The process of identifying risks to organizational operations (including mission, functions, image, or reputation), organizational assets, individuals, other organizations, and the Nation, arising through the operation of an information system. Part of risk management, incorporates threat and vulnerability analyses and considers mitigations provided by security controls planned or in place. Synonymous with risk analysis.
509 | SOURCE: SP 800-53; SP 800-53A; SP 800-37
510 |
511 | Risk Assessment Methodology – A risk assessment process, together with a risk model, assessment approach, and analysis approach.
512 | SOURCE: SP 800-30
513 |
514 | Risk Assessment Report – The report which contains the results of performing a risk assessment or the formal output from the process of assessing risk.
515 | SOURCE: SP 800-30
516 |
517 | Root Certification Authority – In a hierarchical Public Key Infrastructure, the Certification Authority whose public key serves as the most trusted datum (i.e., the beginning of trust paths) for a security domain.
518 | SOURCE: SP 800-32; CNSSI-4009
519 |
520 | Rootkit – A set of tools used by an attacker after gaining root-level access to a host to conceal the attacker’s activities on the host and permit the attacker to maintain root-level access to the host through covert means.
521 | SOURCE: CNSSI-4009
522 |
523 | S
524 | Safeguards – Protective measures prescribed to meet the security requirements (i.e., confidentiality, integrity, and availability) specified for an information system. Safeguards may include security features, management constraints, personnel security, and security of physical structures, areas, and devices. Synonymous with security controls and countermeasures.
525 | SOURCE: SP 800-53; SP 800-37; FIPS 200; CNSSI-4009
526 |
527 | Sandboxing- A restricted, controlled execution environment that prevents potentially malicious software, such as mobile code, from accessing any system resources except those for which the software is authorized.
528 | SOURCE: CNSSI-4009
529 |
530 | Scanning – Sending packets or requests to another system to gain information to be used in a subsequent attack.
531 | SOURCE: CNSSI-4009
532 |
533 | Secure Socket Layer (SSL) – A protocol used for protecting private information during transmission via the Internet.
534 | * **Note:** SSL works by using a public key to encrypt data that's transferred over the SSL connection. Most Web browsers support
535 | SSL, and many Web sites use the protocol to obtain confidential user information, such as credit card numbers. By convention, URLs that require an SSL connection start with “https:” instead of “http:.”
536 | SOURCE: CNSSI-4009
537 |
538 | Security Content Automation Protocol (SCAP) – A method for using specific standardized testing methods to enable automated vulnerability management, measurement, and policy compliance evaluation against a standardized set of security requirements.
539 | SOURCE: CNSSI-4009
540 |
541 | Signature – A recognizable, distinguishing pattern associated with an attack, such as a binary string in a virus or a particular set of keystrokes used to gain unauthorized access to a system.
542 | SOURCE: SP 800-61
543 |
544 | Signature Certificate – A public key certificate that contains a public key intended for verifying digital signatures rather than encrypting data or performing any other cryptographic functions.
545 | SOURCE: SP 800-32; CNSSI-4009
546 |
547 | Smart Card – A credit card-sized card with embedded integrated circuits that can store, process, and communicate information.
548 | SOURCE: CNSSI-4009
549 |
550 | Social Engineering – An attempt to trick someone into revealing information (e.g., a password) that can be used to attack systems or networks.
551 | SOURCE: SP 800-61
552 |
553 | Spam - Electronic junk mail or the abuse of electronic messaging systems to indiscriminately send unsolicited bulk messages.
554 | SOURCE: CNSSI-4009
555 |
556 | Spoofing – “IP spoofing” refers to sending a network packet that appears to come from a source other than its actual source.
557 | SOURCE: SP 800-48
558 |
559 | Spyware – Software that is secretly or surreptitiously installed into an information system to gather information on individuals or
560 | organizations without their knowledge; a type of malicious code.
561 | SOURCE: SP 800-53; CNSSI-4009
562 |
563 | Steganography – The art and science of communicating in a way that hides the existence of the communication. For example, a child pornography image can be hidden inside another graphic image file, audio file, or other file format.
564 | SOURCE: SP 800-72; SP 800-101
565 |
566 | Supply Chain Attack – Attacks that allow the adversary to utilize implants or other vulnerabilities inserted prior to installation in order to infiltrate data, or manipulate information technology hardware, software, operating systems, peripherals (information technology products) or services at any point during the life cycle.
567 | SOURCE: CNSSI-4009
568 |
569 | System Development Life Cycle (SDLC) – The scope of activities associated with a system, encompassing the system’s initiation, development and acquisition, implementation, operation and maintenance, and ultimately its disposal that instigates another system initiation.
570 | SOURCE: SP 800-34; CNSSI-4009
571 |
572 | System Development Methodologies – Methodologies developed through software engineering to manage the complexity of system development. Development methodologies include software engineering aids and high-level design analysis tools.
573 | SOURCE: CNSSI-4009
574 |
575 | System Integrity – The quality that a system has when it performs its intended function in an unimpaired manner, free from unauthorized manipulation of the system, whether intentional or accidental.
576 | SOURCE: SP 800-27
577 |
578 | T
579 |
580 | Tailoring – The process by which a security control baseline is modified based on: (i) the application of scoping guidance; (ii) the specification of compensating security controls, if needed; and (iii) the specification of organization-defined parameters in the security controls via explicit assignment and selection statements.
581 | SOURCE: SP 800-37; SP 800-53; SP 800-53A; CNSSI-4009
582 |
583 | Tampering – An intentional event resulting in modification of a system, its intended behavior, or data.
584 | SOURCE: CNSSI-4009
585 |
586 | Telecommunications – Preparation, transmission, communication, or related processing of information (writing, images, sounds, or other data) by electrical, electromagnetic, electromechanical, electro-optical, or electronic means.
587 | SOURCE: CNSSI-4009
588 |
589 | Threat – Any circumstance or event with the potential to adversely impact organizational operations (including mission, functions, image, or reputation), organizational assets, individuals, other organizations, or the Nation through an information system via unauthorized access, destruction, disclosure, modification of information, and/or denial of service.
590 | SOURCE: SP 800-53; SP 800-53A; SP 800-27; SP 800-60; SP 800-
591 | 37; CNSSI-4009
592 |
593 | Threat Analysis – The examination of threat sources against system vulnerabilities to determine the threats for a particular system in a particular operational environment.
594 | SOURCE: SP 800-27
595 |
596 | Threat Assessment – Formal description and evaluation of threat to an information system.
597 | SOURCE: SP 800-53; SP 800-18
598 |
599 | Threat Monitoring – Analysis, assessment, and review of audit trails and other information collected for the purpose of searching out system events that may constitute violations of system security.
600 | SOURCE: CNSSI-4009
601 |
602 | Token – Something that the Claimant possesses and controls (typically a key or password) that is used to authenticate the Claimant’s identity.
603 | SOURCE: SP 800-63
604 |
605 | Tracking Cookie – A cookie placed on a user’s computer to track the user’s activity on different Web sites, creating a detailed profile of the user’s behavior.
606 | SOURCE: SP 800-83
607 |
608 | Traffic Analysis – A form of passive attack in which an intruder observes information about calls (although not necessarily the contents of the messages) and makes inferences, e.g., from the source and destination numbers, or frequency and length of the messages.
609 | SOURCE: SP 800-24
610 |
611 | Trojan Horse – A computer program that appears to have a useful function, but also has a hidden and potentially malicious function that evades security mechanisms, sometimes by exploiting legitimate authorizations of a system entity that invokes the program.
612 | SOURCE: CNSSI-4009
613 |
614 | U
615 |
616 | Unauthorized Access – Unauthorized Occurs when a user, legitimate or unauthorized, accesses a resource that the user is not permitted to use.
617 | SOURCE: FIPS 191
618 |
619 | Unauthorized Disclosure – An event involving the exposure of information to entities not authorized access to the information.
620 | SOURCE: SP 800-57 Part 1; CNSSI-4009
621 |
622 | User – Individual or (system) process authorized to access an information system.
623 | SOURCE: FIPS 200
624 |
625 | User Initialization – A function in the life cycle of keying material; the process whereby a user initializes its cryptographic application (e.g., installing and initializing software and hardware).
626 | SOURCE: SP 800-57 Part 1
627 |
628 | V
629 |
630 | Validation – The process of demonstrating that the system under consideration meets in all respects the specification of that system.
631 | SOURCE: FIPS 201
632 |
633 | Verification – Confirmation, through the provision of objective evidence, that specified requirements have been fulfilled (e.g., an entity’s requirements have been correctly defined, or an entity’s attributes have been correctly presented; or a procedure or function performs as intended and leads to the expected outcome).
634 | SOURCE: CNSSI-4009
635 |
636 | Virtual Machine (VM) – Software that allows a single host to run one or more guest operating systems.
637 | SOURCE: SP 800-115
638 |
639 | Virtual Private Network (VPN) – A virtual network, built on top of existing physical networks, that provides a secure communications tunnel for data and other information transmitted between networks.
640 | SOURCE: SP 800-46
641 |
642 | Virus – A computer program that can copy itself and infect a computer without permission or knowledge of the user. A virus might corrupt
643 | or delete data on a computer, use email programs to spread itself to other computers, or even erase everything on a hard disk.
644 | SOURCE: CNSSI-4009
645 |
646 | Vulnerability – Weakness in an information system, system security procedures, internal controls, or implementation that could be exploited or triggered by a threat source.
647 | SOURCE: SP 800-53; SP 800-53A; SP 800-37; SP 800-60; SP 800-115; FIPS 200
648 |
649 | Vulnerability Assessment –Formal description and evaluation of the vulnerabilities in an information system.
650 | SOURCE: SP 800-53; SP 800-37
651 |
652 | W
653 |
654 | Web Content Filtering Software – A program that prevents access to undesirable Web sites, typically by comparing a requested Web site address to a list of known bad Web sites.
655 | SOURCE: SP 800-69
656 |
657 | Web Risk Assessment – Processes for ensuring Web sites are in compliance with applicable policies.
658 | SOURCE: CNSSI-4009
659 |
660 | Whitelist – A list of discrete entities, such as hosts or applications that are known to be benign and are approved for use within an organization and/or information system.
661 | SOURCE: SP 800-128
662 |
663 | Wi-Fi Protected Access-2 (WPA2) – The approved Wi-Fi Alliance interoperable implementation of the IEEE 802.11i security standard. For federal government use, the implementation must use FIPS-approved encryption, such as AES.
664 | SOURCE: CNSSI-4009
665 |
666 | Wireless Local Area Network (WLAN) – A group of wireless networking devices within a limited geographic area, such as an office building, that exchange data through radio communications. The security of each WLAN is heavily dependent on how well each WLAN component—including client devices, APs, and wireless switches—is secured throughout the WLAN lifecycle, from initial WLAN design and deployment through ongoing maintenance and monitoring.
667 | SOURCE: SP 800-153
668 |
669 | Write – Fundamental operation in an information system that results only in the flow of information from a subject to an object. See Access Type.
670 | SOURCE: CNSSI-4009
671 |
672 | Write Access – Permission to write to an object in an information system.
673 | SOURCE: CNSSI-4009
674 |
675 | Z
676 |
677 | Zeroize – To remove or eliminate the key from a cryptographic equipment or fill device.
678 | SOURCE: CNSSI-4009
679 |
680 | Zombie – A program that is installed on a system to cause it to attack other systems.
681 | SOURCE: SP 800-83
682 |
--------------------------------------------------------------------------------